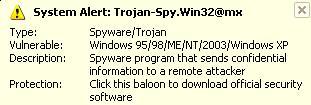
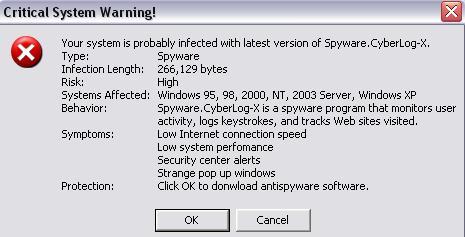
My younger cousin was surfing the net when a pop up came up about computer having a virus and my homepage got taken over by securitynetpage.net i dont have a antivirus or firewall for something to come up telling me i got a virus. also i popup comes up in the corner.(see attechment). so i have a feeling i have spyware or a virus may you please help. also i am running on dial up 25kb.
Logfile of HijackThis v1.99.1
Scan saved at 7:22:46 PM, on 8/22/2006
Platform: Windows XP SP1 (WinNT 5.01.2600)
MSIE: Internet Explorer v6.00 SP1 (6.00.2800.1106)
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\system32\spoolsv.exe
C:\WINDOWS\System32\nvsvc32.exe
C:\WINDOWS\Explorer.EXE
C:\WINDOWS\SOUNDMAN.EXE
C:\PROGRA~1\Nokia\NOKIAP~1\LAUNCH~1.EXE
C:\Program Files\iTunes\iTunesHelper.exe
C:\Program Files\QuickTime\qttask.exe
C:\Program Files\iPod\bin\iPodService.exe
C:\WINDOWS\System32\ctfmon.exe
C:\Program Files\Nokia\Nokia PC Suite 6\PcSync2.exe
C:\Program Files\Messenger\msmsgs.exe
C:\Program Files\Common Files\PCSuite\Services\ServiceLayer.exe
C:\PROGRA~1\COMMON~1\Nokia\MPAPI\MPAPI3s.exe
C:\Program Files\Internet Explorer\IEXPLORE.EXE
C:\Program Files\Internet Explorer\IEXPLORE.EXE
C:\WINDOWS\System32\svchost.exe
C:\Documents and Settings\F.bondok\Desktop\hijackthis\HijackThis.exe
O1 - Hosts: 82.146.56.35 personal.barclays.co.uk
O1 - Hosts: 82.146.56.35 barclays.co.uk
O1 - Hosts: 82.146.56.35 ibank.barclays.co.uk
O1 - Hosts: 82.146.56.35 www.barclays.co.uk
O1 - Hosts: 82.146.56.35 hsbc.co.uk
O1 - Hosts: 82.146.56.35 www.hsbc.co.uk
O1 - Hosts: 82.146.56.35 personal.hsbc.co.uk
O1 - Hosts: 82.146.56.35 abbey.com
O1 - Hosts: 82.146.56.35 www.abbey.com
O1 - Hosts: 82.146.56.35 www.abbey.co.uk
O1 - Hosts: 82.146.56.35 abbey.co.uk
O1 - Hosts: 82.146.56.35 www.banesto.es
O1 - Hosts: 82.146.56.35 banesto.es
O1 - Hosts: 82.146.56.35 www.bbvanet.com
O1 - Hosts: 82.146.56.35 bbvanet.com
O1 - Hosts: 82.146.56.35 www.halifax.co.uk
O1 - Hosts: 82.146.56.35 halifax.co.uk
O1 - Hosts: 82.146.56.35 bankofscotlandhalifax.co.uk
O1 - Hosts: 82.146.56.35 www.bankofscotlandhalifax-online.co.uk
O1 - Hosts: 82.146.56.35 www.co-operativebank.co.uk
O1 - Hosts: 82.146.56.35 co-operativebank.co.uk
O1 - Hosts: 82.146.56.35 www.co-operativebank.com
O1 - Hosts: 82.146.56.35 co-operativebank.com
O1 - Hosts: 82.146.56.35 welcome2.co-operativebankonline.co.uk
O1 - Hosts: 82.146.56.35 welcome6.co-operativebankonline.co.uk
O1 - Hosts: 82.146.56.35 welcome8.co-operativebankonline.co.uk
O1 - Hosts: 82.146.56.35 welcome10.co-operativebankonline.co.uk
O1 - Hosts: 82.146.56.35 www.woolwich.co.uk
O1 - Hosts: 82.146.56.35 woolwich.co.uk
O1 - Hosts: 82.146.56.35 cahoot.com
O1 - Hosts: 82.146.56.35 www.cahoot.com
O1 - Hosts: 82.146.56.35 www.cahoot.co.uk
O1 - Hosts: 82.146.56.35 cahoot.co.uk
O1 - Hosts: 82.146.56.35 www.smile.co.uk
O1 - Hosts: 82.146.56.35 smile.co.uk
O1 - Hosts: 82.146.56.35 www.volksbank.de
O1 - Hosts: 82.146.56.35 volksbank.de
O1 - Hosts: 82.146.56.35 www.berliner-volksbank.de
O1 - Hosts: 82.146.56.35 postbank.de
O1 - Hosts: 82.146.56.35 www.postbank.de
O1 - Hosts: 82.146.56.35 banking.postbank.de
O1 - Hosts: 82.146.56.35 direkt.postbank.de
O2 - BHO: (no name) - {873eb32d-ae1a-4183-89bd-45a77f761be4} - C:\WINDOWS\System32\ixt1.dll
O3 - Toolbar: &Radio - {8E718888-423F-11D2-876E-00A0C9082467} - C:\WINDOWS\System32\msdxm.ocx
O4 - HKLM\..\Run: [SoundMan] SOUNDMAN.EXE
O4 - HKLM\..\Run: [Nemesis4] C:\Documents and Settings\F.bondok\Desktop\Program Hack Msn\Pro.exe
O4 - HKLM\..\Run: [PCSuiteTrayApplication] C:\PROGRA~1\Nokia\NOKIAP~1\LAUNCH~1.EXE -startup
O4 - HKLM\..\Run: [iTunesHelper] "C:\Program Files\iTunes\iTunesHelper.exe"
O4 - HKLM\..\Run: [QuickTime Task] "C:\Program Files\QuickTime\qttask.exe" -atboottime
O4 - HKLM\..\Run: [SMSERIAL] sm56hlpr.exe
O4 - HKLM\..\Run: [Microsoft Network Services Controller] C:\WINDOWS\System32\mmsvc32.exe
O4 - HKCU\..\Run: [ctfmon.exe] C:\WINDOWS\System32\ctfmon.exe
O4 - HKCU\..\Run: [PcSync] C:\Program Files\Nokia\Nokia PC Suite 6\PcSync2.exe /NoDialog
O4 - HKCU\..\Run: [MSMSGS] "C:\Program Files\Messenger\msmsgs.exe" /background
O8 - Extra context menu item: E&xport to Microsoft Excel - res://C:\PROGRA~1\MICROS~2\OFFICE11\EXCEL.EXE/3000
O9 - Extra button: Research - {92780B25-18CC-41C8-B9BE-3C9C571A8263} - C:\PROGRA~1\MICROS~2\OFFICE11\REFIEBAR.DLL
O9 - Extra button: Related - {c95fe080-8f5d-11d2-a20b-00aa003c157a} - C:\WINDOWS\web\related.htm
O9 - Extra 'Tools' menuitem: Show &Related Links - {c95fe080-8f5d-11d2-a20b-00aa003c157a} - C:\WINDOWS\web\related.htm
O16 - DPF: {88D969C0-F192-11D4-A65F-0040963251E5} (XML DOM Document 4.0) - file://C:\TempEI4\EI40_\msxml4.cab
O17 - HKLM\System\CCS\Services\Tcpip\..\{F07EEF05-D653-4062-93AD-23BC1565AB69}: NameServer = 217.139.192.10 217.139.145.10
O21 - SSODL: hubbsi - {7b1eeccd-0a6d-4ad5-8ac1-4af5722b3885} - C:\WINDOWS\System32\vwlummc.dll
O23 - Service: InstallDriver Table Manager (IDriverT) - Macrovision Corporation - C:\Program Files\Common Files\InstallShield\Driver\11\Intel 32\IDriverT.exe
O23 - Service: iPodService - Apple Computer, Inc. - C:\Program Files\iPod\bin\iPodService.exe
O23 - Service: NVIDIA Driver Helper Service (NVSvc) - NVIDIA Corporation - C:\WINDOWS\System32\nvsvc32.exe
O23 - Service: ServiceLayer - Nokia. - C:\Program Files\Common Files\PCSuite\Services\ServiceLayer.exe
thank you
Edited by biggam, 21 August 2006 - 10:45 AM.














 Sign In
Sign In Create Account
Create Account

