1) Below here is the Combofix Log:-
ComboFix 08-02-25.3 - Administrator 2008-02-27 10:44:18.4 - FAT32x86
Microsoft Windows XP Professional 5.1.2600.1.1252.1.1033.18.148 [GMT 8:00]
Running from: C:\Documents and Settings\Administrator\Desktop\ComboFix.exe
Command switches used :: C:\Documents and Settings\Administrator\Desktop\CFScript.txt
* Created a new restore point
WARNING -THIS MACHINE DOES NOT HAVE THE RECOVERY CONSOLE INSTALLED !!
.
((((((((((((((((((((((((( Files Created from 2008-01-27 to 2008-02-27 )))))))))))))))))))))))))))))))
.
2008-02-27 01:40 . 2008-02-27 01:40 <DIR> d-------- C:\fixwareout
2008-02-26 23:00 . 2008-02-26 23:00 <DIR> d-------- C:\WINDOWS\system32\Kaspersky Lab
2008-02-26 23:00 . 2008-02-26 23:00 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\Kaspersky Lab
2008-02-26 21:56 . 2008-02-26 21:56 <DIR> d-------- C:\WINDOWS\ERUNT
2008-02-26 21:51 . 2008-02-25 15:14 <DIR> d-------- C:\SDFix
2008-02-26 12:35 . 2008-02-26 12:35 <DIR> d-------- C:\Program Files\Trend Micro
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2007-10-07 09:40 34,904 ----a-w C:\Documents and Settings\Administrator\Application Data\GDIPFONTCACHEV1.DAT
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ctfmon.exe"="C:\WINDOWS\System32\ctfmon.exe" [2002-08-28 19:41 13312]
"BitComet"="C:\Program Files\BitComet\BitComet.exe" [ ]
"BitTorrent"="C:\Program Files\BitTorrent\bittorrent.exe" [ ]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"RAM Idle"="C:\Program Files\Customizer XP\RAMIdle.exe" [2002-05-01 12:29 104960]
"SbUsb AudCtrl"="sbusbdll.dll" [2005-05-26 17:52 128000 C:\WINDOWS\system32\sbusbdll.dll]
"WMC_AutoUpdate"="" []
"AVG7_CC"="C:\PROGRA~1\Grisoft\AVG7\avgcc.exe" [2005-12-26 08:20 579072]
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run]
"AVG7_Run"="C:\PROGRA~1\Grisoft\AVG7\avgw.exe" [2005-12-25 16:27 219136]
C:\Documents and Settings\All Users\Start Menu\Programs\Startup\
Microsoft Office.lnk - C:\Program Files\Microsoft Office\Office10\OSA.EXE [2001-02-13 01:01:04 83360]
R3 ati2mtaa;ati2mtaa;C:\WINDOWS\System32\DRIVERS\ati2mtaa.sys [2002-08-28 23:16]
S2 MSDCOMClient16;DCOM Service Process Manager;C:\WINDOWS\System32\svchost.exe [2001-08-23 04:00]
S3 sbusb;Sound Blaster USB Audio Driver;C:\WINDOWS\System32\DRIVERS\sbusb.sys [2005-06-10 09:39]
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Svchost - NetSvcs
MSDCOMClient16
enqe
MSDCOMClient32
.
**************************************************************************
catchme 0.3.1344 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2008-02-27 10:46:18
Windows 5.1.2600 Service Pack 1 FAT NTAPI
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
Completion time: 2008-02-27 10:47:23
ComboFix-quarantined-files.txt 2008-02-27 02:47:20
ComboFix4.txt 2008-02-26 04:51:16
ComboFix3.txt 2008-02-26 14:16:22
ComboFix2.txt 2008-02-26 17:30:58
2) This the Malwarebytes' Anti-MalWare log :-
Malwarebytes' Anti-Malware 1.05
Database version: 414
Scan type: Full Scan (A:\|C:\|D:\|)
Objects scanned: 37688
Time elapsed: 10 minute(s), 37 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 4
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 1
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
HKEY_CLASSES_ROOT\newsadvpusher.brlogic (Adware.CPush) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\newsadvpusher.brlogic.1 (Adware.CPush) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\newscocomediumspop.popcoco (Adware.CPush) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\newscocomediumspop.popcoco.1 (Adware.CPush) -> Quarantined and deleted successfully.
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
C:\QooBox\Quarantine\C\Program Files\Common Files\CPUSH\Uninst.exe.vir (Malware.Trace) -> Quarantined and deleted successfully.
3) For the Ice Sword application , I did not find any messages or words red in colour? Is that good news? By theway ,below here are the indivual results of each category:-
a) Processes
Process:
System Idle Process
System
C:\Documents and Settings\Administrator\Desktop\IceSword.exe
C:\WINDOWS\System32\SMSS.EXE
C:\WINDOWS\System32\CSRSS.EXE
C:\WINDOWS\System32\WINLOGON.EXE
C:\WINDOWS\System32\SERVICES.EXE
C:\WINDOWS\System32\LSASS.EXE
C:\WINDOWS\System32\SVCHOST.EXE
C:\WINDOWS\System32\SVCHOST.EXE
C:\WINDOWS\System32\SVCHOST.EXE
C:\WINDOWS\System32\SVCHOST.EXE
C:\WINDOWS\System32\SPOOLSV.EXE
C:\WINDOWS\EXPLORER.EXE
C:\Program Files\Customizer XP\RAMIdle.exe
C:\WINDOWS\System32\RUNDLL32.EXE
C:\WINDOWS\System32\CTFMON.EXE
C:\Program Files\Grisoft\AVG7\AVGAMSVR.EXE
C:\Program Files\Grisoft\AVG7\AVGUPSVC.EXE
C:\Program Files\Grisoft\AVG7\AVGEMC.EXE
C:\Program Files\Common Files\Microsoft Shared\VS7Debug\MDM.EXE
C:\WINDOWS\System32\DEVLDR32.EXE
C:\WINDOWS\System32\SVCHOST.EXE
C:\WINDOWS\System32\WDFMGR.EXE
B)Services
Started Service:
Service Name:AudioSrv Display Name:Windows Audio
Service Name:Avg7Alrt Display Name:AVG7 Alert Manager Server
Service Name:Avg7UpdSvc Display Name:AVG7 Update Service
Service Name:AVGEMS Display Name:AVG E-mail Scanner
Service Name:Browser Display Name:Computer Browser
Service Name:CryptSvc Display Name:Cryptographic Services
Service Name:Dhcp Display Name:DHCP Client
Service Name:dmserver Display Name:Logical Disk Manager
Service Name:Dnscache Display Name:DNS Client
Service Name:ERSvc Display Name:Error Reporting Service
Service Name:Eventlog Display Name:Event Log
Service Name:EventSystem Display Name:COM+ Event System
Service Name:helpsvc Display Name:Help and Support
Service Name:lanmanserver Display Name:Server
Service Name:lanmanworkstation Display Name:Workstation
Service Name:LmHosts Display Name:TCP/IP NetBIOS Helper
Service Name:MDM Display Name:Machine Debug Manager
Service Name:Messenger Display Name:Messenger
Service Name:Netman Display Name:Network Connections
Service Name:Nla Display Name:Network Location Awareness (NLA)
Service Name:PlugPlay Display Name:Plug and Play
Service Name:PolicyAgent Display Name:IPSEC Services
Service Name:ProtectedStorage Display Name:Protected Storage
Service Name:RasMan Display Name:Remote Access Connection Manager
Service Name:RemoteRegistry Display Name:Remote Registry
Service Name:RpcSs Display Name:Remote Procedure Call (RPC)
Service Name:SamSs Display Name:Security Accounts Manager
Service Name:Schedule Display Name:Task Scheduler
Service Name:seclogon Display Name:Secondary Logon
Service Name:SENS Display Name:System Event Notification
Service Name:ShellHWDetection Display Name:Shell Hardware Detection
Service Name:Spooler Display Name:Print Spooler
Service Name:srservice Display Name:System Restore Service
Service Name:SSDPSRV Display Name:SSDP Discovery Service
Service Name:stisvc Display Name:Windows Image Acquisition (WIA)
Service Name:TapiSrv Display Name:Telephony
Service Name:TermService Display Name:Terminal Services
Service Name:Themes Display Name:Themes
Service Name:TrkWks Display Name:Distributed Link Tracking Client
Service Name:UMWdf Display Name:Windows User Mode Driver Framework
Service Name:uploadmgr Display Name:Upload Manager
Service Name:W32Time Display Name:Windows Time
Service Name:WebClient Display Name:WebClient
Service Name:winmgmt Display Name:Windows Management Instrumentation
Service Name:wuauserv Display Name:Automatic Updates
Service Name:WZCSVC Display Name:Wireless Zero Configuration
C) Start up
Startup:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
RAM Idle
C:\Program Files\Customizer XP\RAMIdle.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
SbUsb AudCtrl
RunDll32 sbusbdll.dll,RCMonitor
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
WMC_AutoUpdate
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
AVG7_CC
C:\PROGRA~1\Grisoft\AVG7\avgcc.exe /STARTUP
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
ctfmon.exe
C:\WINDOWS\System32\ctfmon.exe
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
BitComet
"C:\Program Files\BitComet\BitComet.exe"
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
BitTorrent
"C:\Program Files\BitTorrent\bittorrent.exe" --force_start_minimized
C:\Documents and Settings\All Users\Start Menu\Programs\Startup
desktop.ini
C:\Documents and Settings\All Users\Start Menu\Programs\Startup
Microsoft Office.lnk
C:\Program Files\Microsoft Office\Office10\OSA.EXE (Remark£ºMicrosoft Office StartUp)
C:\Documents and Settings\Administrator\Start Menu\Programs\Startup
desktop.ini
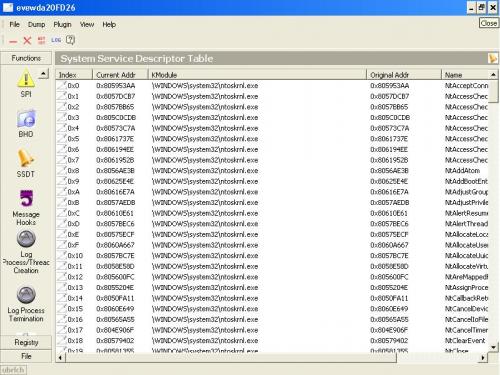
4) SSDT -there are no red highlighted words, and I could not create a log file (don't know why).By the way, I have a screenshot of this category ,please have a look...
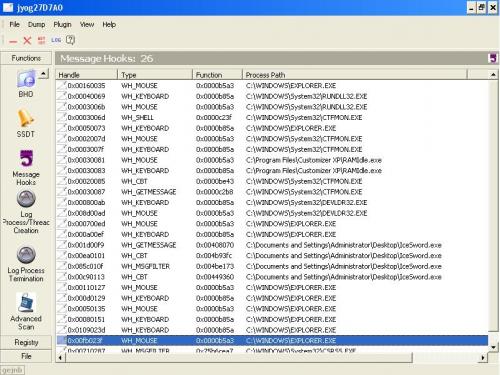
5) Message Hook -same as SSDt ,there are re entries. I could not create alog as well. So, I did another screenshot just for your information.There are some Process Paths that are labelledWH_KEYBOARD under Type column .They are....
C/WINDOWS/EXPLORER.EXE
C/WINDOWS/System32/RUNDLL32.exe
C/WINDOWS/System32/CTFMON.exe
C/Program Files/Customizer XP/RAMIdle.exe
C/WINDOWS/System32/DEVLDR32.exe
What's next , i really hope to solve this matter by today ,if possible!
Thanks again ,your continous effort to help me!
Kuihkociboy

 This topic is locked
This topic is locked













 Sign In
Sign In Create Account
Create Account

