wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]
#16
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #16](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 April 2008 - 03:40 PM
Posted 09 April 2008 - 03:40 PM

#17
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #17](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 April 2008 - 03:46 PM
Posted 09 April 2008 - 03:46 PM

I am going to try taking all those antis out of the startup, and see if it could be one of them causing any or all.
The startup process is definitely not as it was before any of this, I am going to fool with some stuff, and see if I can figure out why.
#18
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #18](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 April 2008 - 04:20 PM
Posted 09 April 2008 - 04:20 PM

Something is still trying to get at my host file when I boot up, according to my ancient version (4.75) of SpyBlocker.
By dint of random and blind clicking, I have resolved some of the cosmetic bootup issues, however, in addition to the host file attempt by some unknown entity, I can tell there is something cranking up.
I will relate more as I continue to scan and click and mash buttons, but my immediate question is, how can I tell what is trying to get at my hosts file on startup?
And a thousand thanks for your untiring patience and help. Your parents made a very wise reproductive choice.
Edited by MoonBloo, 09 April 2008 - 07:29 PM.
#19
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #19](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 April 2008 - 02:47 AM
Posted 10 April 2008 - 02:47 AM

Download SDFix and save it to your Desktop.
Double click SDFix.exe and it will extract the files to %systemdrive%
(Drive that contains the Windows Directory, typically C:\SDFix)
Please then reboot your computer in Safe Mode by doing the following :
- Restart your computer
- After hearing your computer beep once during startup, but before the Windows icon appears, tap the F8 key continually;
- Instead of Windows loading as normal, the Advanced Options Menu should appear;
- Select the first option, to run Windows in Safe Mode, then press Enter.
- Choose your usual account.
- Open the extracted SDFix folder and double click RunThis.bat to start the script.
- Type Y to begin the cleanup process.
- It will remove any Trojan Services and Registry Entries that it finds then prompt you to press any key to Reboot.
- Press any Key and it will restart the PC.
- When the PC restarts the Fixtool will run again and complete the removal process then display Finished, press any key to end the script and load your desktop icons.
- Once the desktop icons load the SDFix report will open on screen and also save into the SDFix folder as Report.txt
(Report.txt will also be copied to Clipboard ready for posting back on the forum). - Finally paste the contents of the Report.txt back on the forum with a new HijackThis log
#20
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #20](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 April 2008 - 02:47 PM
Posted 10 April 2008 - 02:47 PM

(Which, when it rebooted, did so into normal, and not safe mode, just in case that is relevant. Getting into safe mode on this computer is no mean feat, let me tell you! Before discovering this oasis of humanitarian activity, I had done all kinds of things that required safe mode, and it takes roughly 6 tries for every successful landing on that airstrip. I also discovered that the Dell company apparently does not believe in reset buttons.)
It appears, and more importantly, feels, as if the computer is essentially back to its pre-"incident" state, the only thing I noticed after invoking the awesome wrath of SDFix, my AVG anti-spyware was back in the system tray (In my efforts to find the culprit, I had pruned startup down to nothing but AVG antivirus and my antique SpyBlocker).
I am naturally quite paranoid now, and have a gazillion questions, such as:
Should I keep system restore disabled?
I'm not sure what benefit it provides, since the only time I would need it would be in a case of malware, and every malware worth its salt appears to head for system restore like a tween to a Miley Cyrus concert.
And is there just ONE program that will do it all? After running so many antis so many times, it seems that one finds this, the other finds that and misses this, how can I know which one is "best?"
Can I just delete PSEXESVC.EXE? Nothing I have read indicates that it is something I would ever use, but it seems that the same cannot be said of the Bad Things.
As you may imagine, I am especially terrified of keyloggers. Not because I fear the publication of private emails containing scathing criticism of Old Aunt Mina's fashion choices, but because I do not wish to share things like the ftp logins of clients, or data related to my online purchase of those IBM mousepads I like so much and can't find in the stores.
So I want that one program that does it ALL to prevent those, too. Am I asking too much?
And am I now asking my questions in the wrong place?
I do not want to take you away, for even a minute, from those who are in the same desolate valley from which, thanks to your perserverance, generosity and general genius I am now - I can scarcely believe it, and so whisper it, lest I tempt the evil spirits - rescued by my most Gallant and Good Knight, so if I should ask all this in a different forum, please tell me which one, and I will go there immediately, but not before at least attempting to express my gratitude, my admiration, and my awe.
Thank you. There! I knew I could not do it. Words will only do so much, may all applicable deities, djinns and spirits rain blessings and munificence upon your house and head unto all generations, and likewise to your comrades-at-mouse, and all the program authors who so generously share their gifts with all earth residents.
Behold! The SDFix Log!
=================
SDFix: Version 1.168
Run by Administrator on Thu 04/10/2008 at 03:37 PM
Microsoft Windows XP [Version 5.1.2600]
Running From: C:\SDFix\SDFix
Checking Services :
Restoring Windows Registry Values
Restoring Windows Default Hosts File
Restoring Default Desktop Wallpaper
Rebooting
Checking Files :
No Trojan Files Found
Removing Temp Files
ADS Check :
Final Check :
catchme 0.3.1351.2 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2008-04-10 15:41:28
Windows 5.1.2600 Service Pack 2 NTFS
scanning hidden processes ...
scanning hidden services & system hive ...
scanning hidden registry entries ...
scanning hidden files ...
scan completed successfully
hidden processes: 0
hidden services: 0
hidden files: 0
Remaining Services :
Authorized Application Key Export:
[HKEY_LOCAL_MACHINE\system\currentcontrolset\services\sharedaccess\parameters\firewallpolicy\standardprofile\authorizedapplications\list]
"%windir%\\system32\\sessmgr.exe"="%windir%\\system32\\sessmgr.exe:*:enabled:@xpsp2res.dll,-22019"
"C:\\Program Files\\Microsoft Office\\Office12\\OUTLOOK.EXE"="C:\\Program Files\\Microsoft Office\\Office12\\OUTLOOK.EXE:*:Enabled:Microsoft Office Outlook"
"C:\\Program Files\\SpyBlocker Software\\spyblocker.exe"="C:\\Program Files\\SpyBlocker Software\\spyblocker.exe:*:Enabled:SpyBlocker"
"C:\\Program Files\\WS_FTP Pro\\ftp95pro.exe"="C:\\Program Files\\WS_FTP Pro\\ftp95pro.exe:*:Enabled:WS_FTP 95"
"C:\\Program Files\\Grisoft\\AVG7\\avginet.exe"="C:\\Program Files\\Grisoft\\AVG7\\avginet.exe:*:Enabled:avginet.exe"
"C:\\Program Files\\Grisoft\\AVG7\\avgamsvr.exe"="C:\\Program Files\\Grisoft\\AVG7\\avgamsvr.exe:*:Enabled:avgamsvr.exe"
"C:\\Program Files\\Grisoft\\AVG7\\avgcc.exe"="C:\\Program Files\\Grisoft\\AVG7\\avgcc.exe:*:Enabled:avgcc.exe"
"C:\\Program Files\\BitTyrant\\Azureus.exe"="C:\\Program Files\\BitTyrant\\Azureus.exe:*:Enabled:Azureus"
"C:\\Program Files\\uTorrent\\uTorrent.exe"="C:\\Program Files\\uTorrent\\uTorrent.exe:*:Enabled:æTorrent"
"C:\\Program Files\\Azureus\\Azureus.exe"="C:\\Program Files\\Azureus\\Azureus.exe:*:Enabled:Azureus Vuze"
"C:\\Program Files\\UltraEdit\\UEDIT32.EXE"="C:\\Program Files\\UltraEdit\\UEDIT32.EXE:*:Enabled:UltraEdit-32 Professional Text/Hex Editor"
[HKEY_LOCAL_MACHINE\system\currentcontrolset\services\sharedaccess\parameters\firewallpolicy\domainprofile\authorizedapplications\list]
"%windir%\\system32\\sessmgr.exe"="%windir%\\system32\\sessmgr.exe:*:enabled:@xpsp2res.dll,-22019"
Remaining Files :
File Backups: - C:\SDFix\SDFix\backups\backups.zip
Files with Hidden Attributes :
Fri 20 Oct 2006 108 A.SHR --- "C:\WINDOWS\neoqaz2.dll"
Wed 31 Jul 2002 108 ..SH. --- "C:\WINDOWS\WSYS049.SYS"
Mon 28 Jan 2008 1,404,240 A.SHR --- "C:\Program Files\Spybot - Search & Destroy\SDUpdate.exe"
Mon 28 Jan 2008 5,146,448 A.SHR --- "C:\Program Files\Spybot - Search & Destroy\SpybotSD.exe"
Mon 28 Jan 2008 2,097,488 A.SHR --- "C:\Program Files\Spybot - Search & Destroy\TeaTimer.exe"
Fri 10 Mar 2000 84,992 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\14_43260.DLL"
Fri 10 Mar 2000 44,032 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\28_83260.DLL"
Fri 10 Mar 2000 30,208 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\AUTH3260.DLL"
Fri 10 Mar 2000 23,552 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\BASC3260.DLL"
Fri 10 Mar 2000 23,552 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\COKR3260.DLL"
Fri 10 Mar 2000 25,088 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\COOK3260.DLL"
Fri 10 Mar 2000 20,480 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\DNET3260.DLL"
Fri 10 Mar 2000 78,848 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\EDNT3260.DLL"
Fri 10 Mar 2000 446,976 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\ENCN3260.DLL"
Fri 10 Mar 2000 21,504 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\ENLV3260.DLL"
Fri 10 Mar 2000 92,672 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\ERV13260.DLL"
Fri 10 Mar 2000 272,384 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\ERV23260.DLL"
Fri 10 Mar 2000 59,392 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\ESPR3260.DLL"
Tue 16 Oct 2001 139,264 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\jpeglib.dll"
Fri 10 Mar 2000 278,528 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\PNCRT.DLL"
Fri 10 Mar 2000 379,904 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\PNGU3264.DLL"
Fri 10 Mar 2000 11,264 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\PNRS3260.DLL"
Fri 10 Mar 2000 508,928 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\RMBE3260.DLL"
Fri 10 Mar 2000 521,216 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\RMME3260.DLL"
Fri 10 Mar 2000 328,192 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\RMTO3260.DLL"
Fri 10 Mar 2000 28,160 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\RN5A3260.DLL"
Fri 10 Mar 2000 500,224 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\RNCO3260.DLL"
Fri 10 Mar 2000 30,208 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\RV103260.DLL"
Fri 10 Mar 2000 90,624 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\RV203260.DLL"
Fri 10 Mar 2000 41,472 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\SDPP3260.DLL"
Fri 10 Mar 2000 17,408 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\SIPR3260.DLL"
Tue 16 Oct 2001 569,344 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\tablib.dll"
Tue 16 Oct 2001 1,167,360 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\tassdll.dll"
Tue 16 Oct 2001 32,768 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\thereal.dll"
Tue 16 Oct 2001 20,480 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\vidfowin.dll"
Tue 16 Oct 2001 20,480 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\wavout.dll"
Tue 16 Oct 2001 98,304 A.SH. --- "C:\Program Files\Thugs at Bay\Zwei-Stein\wmfwrite.dll"
Finished!
#21
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #21](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 April 2008 - 04:22 PM
Posted 10 April 2008 - 04:22 PM

No this is the right place to ask all those questions
First off I will remove all the programmes I had you download
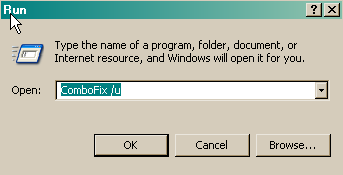
Follow these steps to uninstall Combofix and tools used in the removal of malware
- Click START then RUN
- Now type Combofix /u in the runbox and click OK. Note the space between the X and the U, it needs to be there.
Double click OTScanit once again and you should see a CleanUp! button, press that button, you may get prompted by your firewall that OTScanit wants to contact the internet, allow this, a cleanup.txt will be downloaded, a message dialog will ask you if you want to proceed with the cleanup process, click Yes. This will delete all the tools you have downloaded plus itself
I will now give the clean spiel and follow up with some answers
Now to get you off to a good start we will re-set your restore points so that all the bad stuff is gone for good. Then if you need to restore at some stage you will be clean. There are several ways to reset your your restore point but this is my method:
1. Select Start > All Programs > Accessories > System tools > System Restore.
2. On the dialogue box that appears select Create a Restore Point
3. Click NEXT
4. Enter a name e.g. Clean
5. Click CREATE
You now have a clean restore point, to get rid of the bad ones:
1. Select Start > All Programs > Accessories > System tools > Disk Cleanup.
2. In the Drop down box that appears select your main drive e.g. C
3. Click OK
4. The System will do some calculation and the display a dialogue box with TABS
5. Select the More Options Tab.
6. At the bottom will be a system restore box with a CLEANUP button click this
7. Accept the Warning and select OK again, the program will close and you are done
Now that you are clean, to help protect your computer in the future I recommend that you get the following free program:
- SpywareBlaster to help prevent spyware from installing in the first place.
- SuperAntispyware Run weekly to keep your system clean
To keep your operating system up to date visit
To learn more about how to protect yourself while on the internet read this article by Tony Klien: So how did I get infected in the first place?
Keep safe
Answer time
Keep it enabled as a bad restore point is better than noneShould I keep system restore disabled?
Difficult question, I tend to steer clear of the suites that do it all as the phrase "Jack of all trades and master of none" springs to mind. I use a layered approach.And is there just ONE program that will do it all? After running so many antis so many times, it seems that one finds this, the other finds that and misses this, how can I know which one is "best?"
Firewall - Zone Alarm Pro behind a router firewall
AV - Avast Pro purely because I like and trust it and it scans downloads on the fly
Antispy - Superantispyware Pro
Blocker - SpywareBlaster, fills my registry with killbits for the most common BHO's
That is the total of my protection (Plus I am on Vista so most of my online time is in protected mode )
That is part of the Syinternals suite and like all powerfull tools can be used for good or bad. If you have no requirement it can be deleted.Can I just delete PSEXESVC.EXE? Nothing I have read indicates that it is something I would ever use, but it seems that the same cannot be said of the Bad Things.
Unfortunately I have no knowledge of anti-keylogger programmes. There are several on the market and through Google I found one here http://www.anti-keyl....com/index.htmlI am especially terrified of keyloggers.
I will pass that on to the experts who create the tools that I, a mere mortal, use.Thank you. There! I knew I could not do it. Words will only do so much, may all applicable deities, djinns and spirits rain blessings and munificence upon your house and head unto all generations, and likewise to your comrades-at-mouse, and all the program authors who so generously share their gifts with all earth residents
If you have any more questions feel free to ask
#22
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #22](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 April 2008 - 05:53 PM
Posted 10 April 2008 - 05:53 PM

I am attaching images of spywareterminator, I can't figure out how to get it to make a text one, and I have attached some other scans, superantispyware, kapersky, avg in a zip file, and probably there will be more. The kapersky one made no sense, but here it is anyway.
I continue to google matrix dialer and 123 mania, terrified that something is using my phone line to call somewhere or other, also generally terrified.
IT COMES BACK!!!!
And 00dDialer. I am not making sense.
I will get more scans, to give you as much information as I can, there is a page with information about Matrix Dialer and trusted publishers, I only have population in my root publishers, should I go in and delete anything that could be from Spain? That information may be old and now they have new names.
The % signs on this page confuse me, but it all confuses me now, here is a url I found
MatrixDialer
And here is a page about 123 mania
123 Mania
I had such a wonderful message here before, I am sorry I had to change it to this, you probably have much better information on these things than me, but you will be able to understand all of it better, I think and explain to me what I have to do, I will try to calm down.
Thank you.



Attached Files
Edited by MoonBloo, 11 April 2008 - 06:32 AM.
#23
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #23](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 11 April 2008 - 09:23 AM
Posted 11 April 2008 - 09:23 AM

HKLM\Software\Microsoft\Windows\CurrentVersion This references the registry area - but without a file associated with it, it is just writing on the disc.only some less harmfull parts of the infection were detected (i.e. orphan registry entries
)
C:\WINDOWS\msa64chk.dll this is the dialler and we deleted the file with OTMoveit along with 180/2020 and zango et. al. So the final analysis indicates that there are no malicious files on your system just the remnant orphan registry entries
Superantispyware again just showed orphan registry entries - unfortunately with the tools I use we will not be able to clear them all, some will evade. But as I say they are not a problem.
However to put your mind at rest lets run one more scan which usually picks up the registry bits I fail to see
Please download Malwarebytes' Anti-Malware from Here or Here
Double Click mbam-setup.exe to install the application.
- Make sure a checkmark is placed next to Update Malwarebytes' Anti-Malware and Launch Malwarebytes' Anti-Malware, then click Finish.
- If an update is found, it will download and install the latest version.
- Once the program has loaded, select "Perform Quick Scan", then click Scan.
- The scan may take some time to finish,so please be patient.
- When the scan is complete, click OK, then Show Results to view the results.
- Make sure that everything is checked, and click Remove Selected.
- When disinfection is completed, a log will open in Notepad and you may be prompted to Restart.(See Extra Note)
- The log is automatically saved by MBAM and can be viewed by clicking the Logs tab in MBAM.
- Copy&Paste the entire report in your next reply.
If MBAM encounters a file that is difficult to remove,you will be presented with 1 of 2 prompts,click OK to either and let MBAM proceed with the disinfection process,if asked to restart the computer,please do so immediatly.
I won't let you go until you are totally happy
#24
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #24](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 11 April 2008 - 12:12 PM
Posted 11 April 2008 - 12:12 PM

But what horrifies not only my heart, but my mind, is that yesterday, on 4-10, the same program gave a clean report!
Something is still in there that is making the stuff come back, and I read all kinds of things about some of these beasts binding themselves to the socks of Windows and repropagating, and botnets that can turn me into a zombie computer that calls Antwerp and infects the computers of innocent Belgians.
I am as much of a mess as the computer, and prone to babble on even more than usual, but you can see that you have calmed me down considerably, and I was able to uninstall the Malwarebytes from the other day, and get a dewy-fresh one.
When I rebooted, one of the antis asked if I would allow a change to an extension handler, and I said yes, hope that was the right answer, and that it had to do with the actions of Mbam and not the dialer trying to repropagate itself.
Thank you for helping me to breathe, and allowing me to rant, I am trying so hard to be Brief, I fear I am nothing short of rudely terse.
I am sorry, I did a full scan instead of quick, hope that is OK and I did not get an extra, here is the log:
========================
Malwarebytes' Anti-Malware 1.11
Database version: 614
Scan type: Full Scan (C:\|)
Objects scanned: 99999
Time elapsed: 16 minute(s), 28 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 1
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 3
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{8674aea0-9d3d-11d9-99dc-00600f9a01f1} (Fake.Dropped.Malware.Renos) -> Quarantined and deleted successfully.
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
C:\WINDOWS\licencia.txt (Malware.Trace) -> Quarantined and deleted successfully.
C:\WINDOWS\telefonos.txt (Malware.Trace) -> Quarantined and deleted successfully.
C:\WINDOWS\textos.txt (Malware.Trace) -> Quarantined and deleted successfully.
Edited by MoonBloo, 11 April 2008 - 12:13 PM.
#25
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #25](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 11 April 2008 - 12:32 PM
Posted 11 April 2008 - 12:32 PM

Had it updated in between ?But what horrifies not only my heart, but my mind, is that yesterday, on 4-10, the same program gave a clean report!
Now that looked good - again one orphan registry entry and some cookies
Thats all it found and MBAM is quite good for the unusual ones... That I missHKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{8674aea0-9d3d-11d9-99dc-00600f9a01f1}
Are you any happier now ?
Is your system performing OK ?
#26
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #26](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 11 April 2008 - 12:47 PM
Posted 11 April 2008 - 12:47 PM

I think at least one of them had updated, I tried to remember to update them before scanning, it seems that one would have to be in a constant state of updating to keep up, and if it seems that way to me, I do not imagine it is any better for the good people manning the battle stations of the various antis.
Just glancing at some of the other threads here, it seems that every infection is unique, as if it were configuring itself to each individual machine upon which it pounces, and this is bound to make your days oh! so interesting!
Here is what I would like to try. Because it appears that after a day or so, some things came back, will you please leave the thread open for the US weekend?
I will just let it all sit and brew and stew, and on Monday see what spyware terminator, superantispyware et.al. have to say then.
#27
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #27](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 11 April 2008 - 02:24 PM
Posted 11 April 2008 - 02:24 PM

#28
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #28](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 14 April 2008 - 01:32 AM
Posted 14 April 2008 - 01:32 AM

Here is the url:
http://psmantikeylog....net/prod01.htm
Apparently, I failed to deactivate or turn off or whatever one (or more) of the antis before installing the thing, it asked a few times if the install program could do this or that, I said yes, and I was just going to go turn it off when all went blue, and a heart-stopping glob of text about crucial and critical, saying horrible things to me:
0x000000F4 (0x00000003 0x8690DDA0 0x8690DF14 0x805D13B6)
(Only the first two in combination have any google results, still looking for one that tells me how to fix it)
I did safe mode, and tried to use Tune Up Utilities, and also system restore by itself, no luck.
And I can't even uninstall the part of the PSM anti-keylogger because it didn't make an install log before the computer stopped and I don't know - I just don't know.
My scans of things were looking good, I had just about decided I could stop clinging to your shirt like a traumatized howler monkey, I got an anti-dialer from A squared and it made me feel better, and I wanted to be extra safe and get an anti-keylogger because the Jotti online scan said that Clamwin said my mchinijdrv.sys or something like that had a small trojan in it, and I read about that file, a mad hook injector, used by Good things like antis sometimes, but Bad things also latch onto it.
I have NEVER had such terrible problems before this computer and Windows XP!
Sorry. Few Words. Can you help me? I even tried putting my Windows CD in, but it was no help.
Will I have to reinstall Windows? The very thought is just about as scary as that blue screen of zeros and recriminations, and if I survive this, one day I will tell you the backstory, a short scrap of my story, and you will have a little better idea of just what a hero you really are, but for now, just help.
I can't be online as much on this rustic old squirrel-powered computer because the new fancy connection only gives me a few hours of dial-up "for backup purposes" on my computer.
I should have put system restore back, it talks like it came back, but I guess it didn't really, since it is not restoring the system.
Oh and in safe mode I ran msconfig and disabled all the startup things and that didn't work either and I am scared to do anything else.
#29
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #29](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 14 April 2008 - 01:06 PM
Posted 14 April 2008 - 01:06 PM

What is the version of XP disc that you have - is it a recovery disc from the computer manufacturer or is it a full windows XP disc
#30
![wmsdkns, locked taskbar, awful stuff please help me! [RESOLVED]: post #30](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 14 April 2008 - 10:31 PM
Posted 14 April 2008 - 10:31 PM

I spoke today with the evil corporation that made the computer, and it appears that the client from whom I obtained it in that bit of "creative invoicing" I mentioned has some sort of support agreement with them, so a young man in the Philipines will be walking me through the process by telephone.
Although his geek factor is nowhere near your own (if harsh truth be told, I suspect it may hover even below MY own, which you will be painfully aware is solidly in the "laughable" category) there is a possibility that he will be better than nothing, and if he is not, I always have the option of requesting someone who knows that Roxio drag to disk does not work in safe mode, nor does "safe mode with networking" mean that internet access is a certainty.
I also emailed the author of the program, who was kind enough to favor me with a reply to the effect that the program is no longer supported, and even suggested that I "disable the service," which would be a terrific idea had Windows not stopped before the thing was installed.
In my heart, I know that there is some file, probably a driver of some kind, deep in the most unlovely entrails of the core of this alleged operating system, that could probably be deleted in DOS, but finding it, and you know those things are like cockroaches, if there is one, there are more, so finding them, would take more time and effort, on my part and your own, than reinstalling windows, putting back all my programs, reslurping client sites AND re-obtaining my little secret directory of movies I had just learned to put onto DVDs and thus amaze and delight loved ones with my geekhood.
So you may mercifully close this behemoth of a thread, as your sad little howler monkey at last lets go of your now hopelessly wrinkled shirt collar, bats its paw at a grateful eye, and slowly hops away, only to suddenly turn and scamper back to chitter a promise to return and tell you, no doubt at great length, how it all turns out!
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked






 Sign In
Sign In Create Account
Create Account

