I'm still treading water but fear I may drown [RESOLVED]
Started by
mrhiccups
, May 06 2008 06:45 PM
#16
![I'm still treading water but fear I may drown [RESOLVED]: post #16](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 04:57 AM
Posted 08 May 2008 - 04:57 AM

#17
![I'm still treading water but fear I may drown [RESOLVED]: post #17](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 09:26 AM
Posted 08 May 2008 - 09:26 AM

ok, in which case you follow the instructions on this page http://www.bleepingc...to-use-combofix starting at the paragraph ........If you use Windows XP and do not have the Windows CD, ComboFix includes a method of installing the Windows Recovery console by downloading a file from Microsoft. which is about a third of the way down the page.
in summary, the file from microsoft that you download is the Windows XP Setup boot disk which will contain the Recovery Console. the file you want will be towards the bottom of the microsoft site page, most likely one of the bottom two files (the link is provided in the above instructions, but is here http://support.microsoft.com/kb/310994). once you have downloaded the file, you drag and drop it onto the combofix program, as demonstrated in the instructions.
once you have done all that, then you can run the combofix program.
in summary, the file from microsoft that you download is the Windows XP Setup boot disk which will contain the Recovery Console. the file you want will be towards the bottom of the microsoft site page, most likely one of the bottom two files (the link is provided in the above instructions, but is here http://support.microsoft.com/kb/310994). once you have downloaded the file, you drag and drop it onto the combofix program, as demonstrated in the instructions.
once you have done all that, then you can run the combofix program.
#18
![I'm still treading water but fear I may drown [RESOLVED]: post #18](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 09:52 AM
Posted 08 May 2008 - 09:52 AM

ok I'm still not clear
The options I have:
Windows xp setup boot disk
Windows xp with service pack 2 setup boot disk
Microsoft diagnostics and recovery toolset
I understand the instructions perfectly but these are the closest I can find to what is described
The options I have:
Windows xp setup boot disk
Windows xp with service pack 2 setup boot disk
Microsoft diagnostics and recovery toolset
I understand the instructions perfectly but these are the closest I can find to what is described
#19
![I'm still treading water but fear I may drown [RESOLVED]: post #19](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 10:26 AM
Posted 08 May 2008 - 10:26 AM

think I have it
#20
![I'm still treading water but fear I may drown [RESOLVED]: post #20](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 10:34 AM
Posted 08 May 2008 - 10:34 AM

sorry
just me being a twit
will post logs shortly
Thanks
just me being a twit
will post logs shortly
Thanks
#21
![I'm still treading water but fear I may drown [RESOLVED]: post #21](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 02:35 PM
Posted 08 May 2008 - 02:35 PM

1.
Explorer killed successfully
File/Folder C:\WINDOWS\system32\iifefCrR.dll not found.
File/Folder C:\WINDOWS\system32\aiwnujva.dll not found.
File/Folder C:\WINDOWS\nslbvxpgtkn.dll not found.
File/Folder C:\WINDOWS\system32\tuvVOFYo.dll not found.
File/Folder C:\WINDOWS\sgoblxtm.dll not found.
File/Folder C:\Program Files\webHancer not found.
File/Folder C:\WINDOWS\system32\ifuujxhh.dll not found.
File/Folder C:\Documents and Settings\All Users\Application Data\anwbqpep\kviponex.exe not found.
File/Folder C:\WINDOWS\dsktbwfe.dll not found.
File/Folder C:\WINDOWS\ogxtsepr.dll not found.
< purity >
Explorer started successfully
OTMoveIt2 by OldTimer - Version 1.0.4.1 log created on 01232002_150259
2.
Malwarebytes' Anti-Malware 1.12
Database version: 730
Scan type: Full Scan (C:\|)
Objects scanned: 118551
Time elapsed: 56 minute(s), 2 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 36
Registry Values Infected: 2
Registry Data Items Infected: 0
Folders Infected: 4
Files Infected: 69
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
HKEY_CLASSES_ROOT\CLSID\{9dd4258a-7138-49c4-8d34-587879a5c7a4} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{9dd4258a-7138-49c4-8d34-587879a5c7a4} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{b8c0220d-763d-49a4-95f4-61dfdec66ee6} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{c3bcc488-1ae7-11d4-ab82-0010a4ec2338} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{c3bcc488-1ae7-11d4-ab82-0010a4ec2338} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Interface\{7d4c17e6-b0d7-4de2-a128-67f2fa1d4ff6} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Typelib\{cba0a72a-c5b0-47f8-9bd7-307b7708a58d} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Interface\{0882b175-f982-41b1-91a6-3593ab992df7} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Interface\{4708135c-9d19-4b8a-a47c-7f85ec67b5ee} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Typelib\{17d4667e-4c4b-4f45-a22b-4087f9e1ff00} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{000000da-0786-4633-87c6-1aa7a4429ef1} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\dpcproxy (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify\logons (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\uninstall (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\typelib (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\HOL5_VXIEWER.FULL.1 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Classes\applications\accessdiver.exe (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\fwbd (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\HolLol (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Inet Delivery (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\mslagent (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorertoolbar (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\mwc (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Golden Palace Casino NEW (Trojan.DNSChanger) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SYSTEM\currentcontrolset\Services\iTunesMusic (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SYSTEM\currentcontrolset\Services\rdriv (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\aldd (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\affri (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\affltid (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\rdfa (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\affltid (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\affri (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\FCOVM (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RemoveRP (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\sgoblxtm.bpsb (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\sgoblxtm.toolbar.1 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
Registry Values Infected:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ShellExecuteHooks\{eec73ea5-1367-49d1-93f4-ca1d8c22e9f9} (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SharedTaskScheduler\{0656a137-b161-cadd-9777-e37a75727e78} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
C:\WINDOWS\mslagent (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\Program Files\PC-Cleaner (Rogue.PC-Cleaner) -> Quarantined and deleted successfully.
C:\WINDOWS\system32smp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
Files Infected:
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP732\A0281770.dll (Trojan.Vundo) -> Quarantined and deleted successfully.
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP732\A0281833.dll (Trojan.Vundo) -> Quarantined and deleted successfully.
C:\VundoFix Backups\amjhbosu.dll.bad (Trojan.Vundo) -> Quarantined and deleted successfully.
C:\WINDOWS\Web\def.htm (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\WINDOWS\mslagent\2_mslagent.dll (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\WINDOWS\mslagent\mslagent.exe (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\WINDOWS\mslagent\uninstall.exe (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\WINDOWS\system32smp\msrc.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.bl.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.p.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.r.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.t.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.v.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\a.bat (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\base64.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\FVProtect.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32akttzn.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32anticipator.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32awtoolb.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32bdn.com (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32bsva-egihsg52.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32dpcproxy.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32emesx.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32h@tkeysh@@k.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32hoproxy.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32hxiwlgpm.dat (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32hxiwlgpm.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32medup012.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32medup020.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32msgp.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32msnbho.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32mssecu.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32msvchost.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32mtr2.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32mwin32.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32netode.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32newsd32.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32ps1.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32psof1.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32psoft1.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32regc64.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32regm64.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32Rundl1.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32sncntr.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32ssurf022.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32ssvchost.com (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32ssvchost.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32sysreq.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32taack.dat (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32taack.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32temp#01.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32thun.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32thun32.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32VBIEWER.OCX (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32vbsys2.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32vcatchpi.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32winlogonpc.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32winsystem.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32WINWGPX.EXE (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\userconfig9x.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\winsystem.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zip1.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zip2.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zip3.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zipped.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\bdn.com (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\iTunesMusic.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\mssecu.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\rs.txt (Malware.Trace) -> Quarantined and deleted successfully.
Explorer killed successfully
File/Folder C:\WINDOWS\system32\iifefCrR.dll not found.
File/Folder C:\WINDOWS\system32\aiwnujva.dll not found.
File/Folder C:\WINDOWS\nslbvxpgtkn.dll not found.
File/Folder C:\WINDOWS\system32\tuvVOFYo.dll not found.
File/Folder C:\WINDOWS\sgoblxtm.dll not found.
File/Folder C:\Program Files\webHancer not found.
File/Folder C:\WINDOWS\system32\ifuujxhh.dll not found.
File/Folder C:\Documents and Settings\All Users\Application Data\anwbqpep\kviponex.exe not found.
File/Folder C:\WINDOWS\dsktbwfe.dll not found.
File/Folder C:\WINDOWS\ogxtsepr.dll not found.
< purity >
Explorer started successfully
OTMoveIt2 by OldTimer - Version 1.0.4.1 log created on 01232002_150259
2.
Malwarebytes' Anti-Malware 1.12
Database version: 730
Scan type: Full Scan (C:\|)
Objects scanned: 118551
Time elapsed: 56 minute(s), 2 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 36
Registry Values Infected: 2
Registry Data Items Infected: 0
Folders Infected: 4
Files Infected: 69
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
HKEY_CLASSES_ROOT\CLSID\{9dd4258a-7138-49c4-8d34-587879a5c7a4} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{9dd4258a-7138-49c4-8d34-587879a5c7a4} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{b8c0220d-763d-49a4-95f4-61dfdec66ee6} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{c3bcc488-1ae7-11d4-ab82-0010a4ec2338} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{c3bcc488-1ae7-11d4-ab82-0010a4ec2338} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Interface\{7d4c17e6-b0d7-4de2-a128-67f2fa1d4ff6} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Typelib\{cba0a72a-c5b0-47f8-9bd7-307b7708a58d} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Interface\{0882b175-f982-41b1-91a6-3593ab992df7} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Interface\{4708135c-9d19-4b8a-a47c-7f85ec67b5ee} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\Typelib\{17d4667e-4c4b-4f45-a22b-4087f9e1ff00} (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{000000da-0786-4633-87c6-1aa7a4429ef1} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\dpcproxy (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify\logons (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\uninstall (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\typelib (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\HOL5_VXIEWER.FULL.1 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Classes\applications\accessdiver.exe (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\fwbd (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\HolLol (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Inet Delivery (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\mslagent (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Internet Explorertoolbar (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\mwc (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Golden Palace Casino NEW (Trojan.DNSChanger) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SYSTEM\currentcontrolset\Services\iTunesMusic (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SYSTEM\currentcontrolset\Services\rdriv (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\aldd (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\affri (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\affltid (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\Microsoft\rdfa (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\affltid (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\affri (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\FCOVM (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RemoveRP (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\sgoblxtm.bpsb (Trojan.FakeAlert) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\sgoblxtm.toolbar.1 (Trojan.FakeAlert) -> Quarantined and deleted successfully.
Registry Values Infected:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ShellExecuteHooks\{eec73ea5-1367-49d1-93f4-ca1d8c22e9f9} (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SharedTaskScheduler\{0656a137-b161-cadd-9777-e37a75727e78} (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
C:\WINDOWS\mslagent (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\Program Files\PC-Cleaner (Rogue.PC-Cleaner) -> Quarantined and deleted successfully.
C:\WINDOWS\system32smp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
Files Infected:
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP732\A0281770.dll (Trojan.Vundo) -> Quarantined and deleted successfully.
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP732\A0281833.dll (Trojan.Vundo) -> Quarantined and deleted successfully.
C:\VundoFix Backups\amjhbosu.dll.bad (Trojan.Vundo) -> Quarantined and deleted successfully.
C:\WINDOWS\Web\def.htm (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\WINDOWS\mslagent\2_mslagent.dll (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\WINDOWS\mslagent\mslagent.exe (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\WINDOWS\mslagent\uninstall.exe (Adware.EGDAccess) -> Quarantined and deleted successfully.
C:\WINDOWS\system32smp\msrc.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.bl.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.p.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.r.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.t.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\Documents and Settings\Tobyzooka\Desktopvirii\Trojan-Downloader.Win32.Agent.v.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\a.bat (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\base64.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\FVProtect.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32akttzn.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32anticipator.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32awtoolb.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32bdn.com (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32bsva-egihsg52.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32dpcproxy.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32emesx.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32h@tkeysh@@k.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32hoproxy.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32hxiwlgpm.dat (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32hxiwlgpm.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32medup012.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32medup020.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32msgp.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32msnbho.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32mssecu.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32msvchost.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32mtr2.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32mwin32.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32netode.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32newsd32.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32ps1.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32psof1.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32psoft1.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32regc64.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32regm64.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32Rundl1.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32sncntr.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32ssurf022.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32ssvchost.com (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32ssvchost.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32sysreq.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32taack.dat (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32taack.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32temp#01.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32thun.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32thun32.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32VBIEWER.OCX (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32vbsys2.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32vcatchpi.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32winlogonpc.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32winsystem.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\System32WINWGPX.EXE (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\userconfig9x.dll (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\winsystem.exe (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zip1.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zip2.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zip3.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\zipped.tmp (Fake.Dropped.Malware) -> Quarantined and deleted successfully.
C:\WINDOWS\bdn.com (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\iTunesMusic.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\mssecu.exe (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\rs.txt (Malware.Trace) -> Quarantined and deleted successfully.
#22
![I'm still treading water but fear I may drown [RESOLVED]: post #22](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 02:40 PM
Posted 08 May 2008 - 02:40 PM

3.
ComboFix 08-05-07.2 - Tobyzooka 2008-05-08 18:02:35.1 - NTFSx86
Microsoft Windows XP Professional 5.1.2600.2.1252.1.1033.18.557 [GMT 1:00]
Running from: C:\Documents and Settings\Tobyzooka\Desktop\ComboFix.exe
Command switches used :: C:\Documents and Settings\Tobyzooka\Desktop\WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
* Created a new restore point
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
C:\autorun.inf
C:\Program Files\newdotnet
C:\Program Files\newdotnet\readme.txt
C:\setup.exe
C:\WINDOWS\cookies.ini
C:\WINDOWS\system32\hhxjuufi.ini
C:\WINDOWS\system32\RrCfefii.ini
C:\WINDOWS\system32\RrCfefii.ini2
.
((((((((((((((((((((((((( Files Created from 2008-04-08 to 2008-05-08 )))))))))))))))))))))))))))))))
.
2008-05-14 12:13 . 2008-05-14 18:34 <DIR> d--h----- C:\$AVG8.VAULT$
2008-05-14 12:06 . 2008-05-14 12:06 10,520 --a------ C:\WINDOWS\system32\avgrsstx.dll
2008-05-14 12:05 . 2008-05-14 12:28 <DIR> d-------- C:\WINDOWS\system32\drivers\Avg
2008-05-14 12:05 . 2008-05-14 12:05 96,520 --a------ C:\WINDOWS\system32\drivers\avgldx86.sys
2008-05-14 12:05 . 2008-05-14 12:05 75,272 --a------ C:\WINDOWS\system32\drivers\avgtdix.sys
2008-05-14 12:05 . 2008-05-14 12:05 12,424 --a------ C:\WINDOWS\system32\drivers\avgrkx86.sys
2008-05-14 12:03 . 2008-05-14 12:03 <DIR> d-------- C:\Documents and Settings\Tobyzooka\Application Data\TmpRecentIcons
2008-05-14 10:36 . 2008-05-14 15:10 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\anwbqpep
2008-05-10 12:56 . 2008-05-10 12:56 233,472 --a------ C:\WINDOWS\system32\REX Shared Library.dll
2008-05-10 12:51 . 2008-05-10 12:51 <DIR> d-------- C:\Program Files\Propellerhead
2008-05-10 12:48 . 2008-05-10 12:48 <DIR> d-------- C:\Program Files\DAEMON Tools Lite
2008-05-10 12:45 . 2008-05-10 12:45 <DIR> d-------- C:\Documents and Settings\Tobyzooka\Application Data\DAEMON Tools
2008-05-10 12:45 . 2008-05-10 12:45 717,296 --a------ C:\WINDOWS\system32\drivers\sptd.sys
2008-05-04 16:31 . 2008-05-04 16:31 <DIR> d-------- C:\Program Files\Common Files\Wise Installation Wizard
2008-05-01 13:01 . 2008-05-01 13:03 49,152 --a------ C:\WINDOWS\system32\apache.dll
2008-04-30 19:08 . 2008-04-30 19:08 <DIR> d-------- C:\Program Files\SystemRequirementsLab
2008-04-09 11:14 . 2008-04-09 11:14 <DIR> d-------- C:\SDPlugins
2008-04-09 11:14 . 2008-04-09 11:14 <DIR> d-------- C:\DirectX
2008-04-09 11:11 . 2008-04-09 11:14 <DIR> d-------- C:\data
2008-04-09 11:11 . 2008-04-09 11:11 <DIR> d-------- C:\AppData
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2008-05-14 15:41 22,328 ----a-w C:\WINDOWS\system32\drivers\PnkBstrK.sys
2008-05-14 15:38 107,832 ----a-w C:\WINDOWS\system32\PnkBstrB.exe
2008-05-14 11:02 --------- d-----w C:\Documents and Settings\All Users\Application Data\avg8
2008-05-08 17:08 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Skype
2008-05-05 20:46 27,048 ----a-w C:\WINDOWS\system32\drivers\mbamcatchme.sys
2008-05-05 20:46 15,864 ----a-w C:\WINDOWS\system32\drivers\mbam.sys
2008-05-04 23:41 --------- d-----w C:\Program Files\SlySoft
2008-05-04 15:32 --------- d-----w C:\Program Files\Lavasoft
2008-05-04 15:31 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Lavasoft
2008-05-01 22:38 --------- d--h--w C:\Program Files\InstallShield Installation Information
2008-05-01 22:38 --------- d-----w C:\Program Files\EA Games
2008-04-28 08:03 82,944 ----a-w C:\WINDOWS\system32\IEDFix.exe
2008-04-28 08:03 82,944 ----a-w C:\WINDOWS\system32\404Fix.exe
2008-04-24 08:10 86,528 ----a-w C:\WINDOWS\system32\VACFix.exe
2008-04-15 11:44 --------- d-----w C:\Program Files\Azureus
2008-03-29 18:16 --------- d-----w C:\Program Files\iTunes
2008-03-29 18:16 --------- d-----w C:\Program Files\iPod
2008-03-29 18:15 --------- d-----w C:\Program Files\QuickTime
2008-03-22 01:51 --------- d-----w C:\Program Files\BestGameEver
2008-03-21 19:50 --------- d-----w C:\Program Files\AVG
2008-03-19 19:32 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Sony Corporation
2008-03-19 19:24 --------- d-----w C:\Program Files\Sony
2008-03-19 19:08 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Publish Providers
2008-03-19 19:07 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Sony
2008-03-19 19:06 --------- d-----w C:\Program Files\Sony Setup
2008-03-19 14:46 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Cakewalk
2008-03-19 14:45 --------- d-----w C:\Documents and Settings\All Users\Application Data\Cakewalk
2008-03-19 14:44 --------- d-----w C:\Program Files\Cakewalk
2008-03-19 10:11 --------- d-----w C:\Program Files\MagicISO
2008-03-19 09:47 1,845,248 ----a-w C:\WINDOWS\system32\win32k.sys
2008-02-20 06:51 282,624 ----a-w C:\WINDOWS\system32\gdi32.dll
2008-02-20 05:32 45,568 ----a-w C:\WINDOWS\system32\dnsrslvr.dll
2005-10-09 19:21 18,704 ----a-w C:\Documents and Settings\Tobyzooka\Application Data\GDIPFONTCACHEV1.DAT
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_LOCAL_MACHINE\~\Browser Helper Objects\{4A2AACF3-ADF6-11D5-98A9-00E018981B9E}]
C:\Program Files\NewDotNet\newdotnet3_88.dll
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"CTFMON.EXE"="C:\WINDOWS\system32\ctfmon.exe" [2004-08-04 08:56 15360]
"SetDefaultMIDI"="MIDIDef.exe" []
"Skype"="C:\Program Files\Skype\Phone\Skype.exe" [2005-10-10 14:01 14881320]
"swg"="C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe" [2007-09-16 12:50 68856]
"Steam"="c:\progra~1\valve\steam\steam.exe" [2008-04-27 17:07 1271032]
"MsnMsgr"="C:\Program Files\MSN Messenger\MsnMsgr.exe" [2007-01-19 12:54 5674352]
"DAEMON Tools Lite"="C:\Program Files\DAEMON Tools Lite\daemon.exe" [2008-04-01 10:39 486856]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ATIPTA"="C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe" [2005-05-12 21:05 344064]
"zBrowser Launcher"="C:\Program Files\Logitech\iTouch\iTouch.exe" [2003-04-07 03:16 631364]
"Logitech Utility"="Logi_MwX.Exe" [2002-11-08 11:50 19968 C:\WINDOWS\LOGI_MWX.EXE]
"DAEMON Tools-1033"="C:\Program Files\D-Tools\daemon.exe" [2004-08-22 18:05 81920]
"UserFaultCheck"="C:\WINDOWS\system32\dumprep 0 -u" [ ]
"NeroFilterCheck"="C:\WINDOWS\system32\NeroCheck.exe" [2001-07-09 11:50 155648]
"SunJavaUpdateSched"="C:\Program Files\Java\jre1.5.0_04\bin\jusched.exe" [2005-06-03 03:52 36975]
"DU Meter"="C:\Program Files\DU Meter\DUMeter.exe" [2005-02-01 19:28 1469952]
"StartCCC"="C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\CLIStart.exe" [2006-11-10 12:35 90112]
"ATICCC"="C:\Program Files\ATI Technologies\ATI.ACE\cli.exe" [2006-01-02 17:41 45056]
"AVG8_TRAY"="C:\PROGRA~1\AVG\AVG8\avgtray.exe" [2008-05-14 12:30 1177368]
"QuickTime Task"="C:\Program Files\QuickTime\qttask.exe" [2008-02-01 00:13 385024]
"iTunesHelper"="C:\Program Files\iTunes\iTunesHelper.exe" [2008-02-19 14:10 267048]
"4oD"="C:\Program Files\Kontiki\KHost.exe" [ ]
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run]
"CTFMON.EXE"="C:\WINDOWS\System32\CTFMON.EXE" [2004-08-04 08:56 15360]
"Norton SystemWorks"="C:\Program Files\Norton SystemWorks\cfgwiz.exe" [ ]
C:\Documents and Settings\Tobyzooka\Start Menu\Programs\Startup\
Picture Motion Browser Media Check Tool.lnk - C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe [2008-03-19 20:24:18 344064]
C:\Documents and Settings\All Users\Start Menu\Programs\Startup\
Adobe Reader Speed Launch.lnk - C:\Program Files\Adobe\Acrobat 7.0\Reader\reader_sl.exe [2005-09-23 22:05:26 29696]
Microsoft Office.lnk - C:\Program Files\Microsoft Office\Office10\OSA.EXE [2001-02-13 02:01:04 83360]
WinZip Quick Pick.lnk - C:\Program Files\WinZip\WZQKPICK.EXE [2005-09-25 20:31:11 118784]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\windows]
"AppInit_DLLs"=avgrsstx.dll
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\drivers32]
"vidc.ffds"= ffdshow.ax
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusDisableNotify"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"C:\\Program Files\\Valve\\Steam\\SteamApps\\tobazooka\\counter-strike source\\hl2.exe"=
"C:\\Program Files\\Valve\\Steam\\Steam.exe"=
"C:\\Program Files\\Real\\RealPlayer\\realplay.exe"=
"C:\\Program Files\\Messenger\\msmsgs.exe"=
"C:\\WINDOWS\\system32\\dpvsetup.exe"=
"C:\\WINDOWS\\system32\\rundll32.exe"=
"C:\\WINDOWS\\system32\\dplaysvr.exe"=
"C:\\Program Files\\Java\\jre1.5.0_04\\bin\\javaw.exe"=
"C:\\Program Files\\Valve\\Steam\\SteamApps\\tobazooka\\source sdk base\\hl2.exe"=
"C:\\Program Files\\MSN Messenger\\msnmsgr.exe"=
"C:\\Program Files\\MSN Messenger\\livecall.exe"=
"C:\\WINDOWS\\system32\\dpnsvr.exe"=
"C:\\Program Files\\iTunes\\iTunes.exe"=
"C:\\Program Files\\Azureus\\Azureus.exe"=
"C:\\Program Files\\EA Games\\Battlefield 2\\BF2.exe"=
"C:\\Program Files\\AVG\\AVG8\\avgupd.exe"=
"C:\\Program Files\\AVG\\AVG8\\avgnsx.exe"=
"C:\\Program Files\\Skype\\Phone\\Skype.exe"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"3389:TCP"= 3389:TCP:@xpsp2res.dll,-22009
R0 AvgRkx86;avgrkx86.sys;C:\WINDOWS\system32\Drivers\avgrkx86.sys [2008-05-14 12:05]
R0 xmasbus;xmasbus;C:\WINDOWS\system32\DRIVERS\xmasbus.sys [2003-12-21 18:24]
R0 xmasscsi;xmasscsi;C:\WINDOWS\system32\Drivers\xmasscsi.sys [2003-12-23 03:15]
R1 aswSP;avast! Self Protection;C:\WINDOWS\system32\drivers\aswSP.sys [2008-03-29 19:31]
R1 AvgLdx86;AVG AVI Loader Driver x86;C:\WINDOWS\system32\Drivers\avgldx86.sys [2008-05-14 12:05]
R2 aswFsBlk;aswFsBlk;C:\WINDOWS\system32\DRIVERS\aswFsBlk.sys [2008-03-29 19:35]
R2 avg8wd;AVG8 WatchDog;C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe [2008-05-14 12:05]
R2 AvgTdiX;AVG8 Network Redirector;C:\WINDOWS\system32\Drivers\avgtdix.sys [2008-05-14 12:05]
S2 asurscsi;asurscsi;C:\Program Files\Voyetra\AudioSurgeon 5\asurscsi.exe []
S3 ldiskl;ldiskl;C:\DOCUME~1\TOBYZO~1\LOCALS~1\Temp\ldiskl.sys []
S3 SetupNTGLM7X;SetupNTGLM7X;D:\NTGLM7X.sys []
[HKEY_CURRENT_USER\software\microsoft\windows\currentversion\explorer\mountpoints2\C]
\Shell\AutoRun\command - C:\autorun.exe
.
Contents of the 'Scheduled Tasks' folder
"2008-05-06 14:13:02 C:\WINDOWS\Tasks\AppleSoftwareUpdate.job"
- C:\Program Files\Apple Software Update\SoftwareUpdate.exe
"2008-05-14 14:35:14 C:\WINDOWS\Tasks\Symantec NetDetect.job"
- C:\Program Files\Symantec\LiveUpdate\NDETECT.EXE
.
**************************************************************************
catchme 0.3.1353 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2008-05-08 18:07:34
Windows 5.1.2600 Service Pack 2 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
--------------------- DLLs Loaded Under Running Processes ---------------------
PROCESS: C:\WINDOWS\system32\lsass.exe
-> C:\WINDOWS\system32\xfire_lsp_10650.dll
.
------------------------ Other Running Processes ------------------------
.
C:\WINDOWS\system32\ati2evxx.exe
C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
C:\Program Files\Alwil Software\Avast4\aswUpdSv.exe
C:\WINDOWS\system32\ati2evxx.exe
C:\Program Files\Logitech\MouseWare\system\EM_EXEC.EXE
C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
C:\WINDOWS\system32\PnkBstrA.exe
C:\WINDOWS\system32\PnkBstrB.exe
C:\WINDOWS\system32\wdfmgr.exe
C:\WINDOWS\system32\MsPMSPSv.exe
C:\PROGRA~1\AVG\AVG8\avgam.exe
C:\PROGRA~1\AVG\AVG8\avgnsx.exe
C:\Program Files\iPod\bin\iPodService.exe
C:\Program Files\MSN Messenger\usnsvc.exe
C:\Program Files\AVG\AVG8\avgrsx.exe
C:\Program Files\AVG\AVG8\avgrsx.exe
.
**************************************************************************
.
Completion time: 2008-05-08 18:14:14 - machine was rebooted [Tobyzooka]
ComboFix-quarantined-files.txt 2008-05-08 17:14:07
Pre-Run: 24,043,114,496 bytes free
Post-Run: 23,928,598,528 bytes free
WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
[boot loader]
timeout=2
default=multi(0)disk(0)rdisk(0)partition(1)\WINDOWS
[operating systems]
multi(0)disk(0)rdisk(0)partition(1)\WINDOWS="Microsoft Windows XP Professional" /fastdetect /NoExecute=OptIn
C:\CMDCONS\BOOTSECT.DAT="Microsoft Windows Recovery Console" /cmdcons
210 --- E O F --- 2008-05-12 06:56:26
4.
Logfile of Trend Micro HijackThis v2.0.2
Scan saved at 22:10:34, on 08/05/2008
Platform: Windows XP SP2 (WinNT 5.01.2600)
MSIE: Internet Explorer v6.00 SP2 (6.00.2900.2180)
Boot mode: Normal
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
C:\Program Files\Alwil Software\Avast4\aswUpdSv.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\Program Files\Logitech\iTouch\iTouch.exe
C:\Program Files\Java\jre1.5.0_04\bin\jusched.exe
C:\Program Files\DU Meter\DUMeter.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\PROGRA~1\AVG\AVG8\avgtray.exe
C:\Program Files\iTunes\iTunesHelper.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\Logitech\MouseWare\system\em_exec.exe
C:\WINDOWS\system32\spoolsv.exe
C:\Program Files\Skype\Phone\Skype.exe
C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe
C:\Program Files\MSN Messenger\MsnMsgr.Exe
C:\Program Files\DAEMON Tools Lite\daemon.exe
C:\WINDOWS\system32\PnkBstrA.exe
C:\WINDOWS\system32\PnkBstrB.exe
C:\WINDOWS\system32\MsPMSPSv.exe
C:\Program Files\WinZip\WZQKPICK.EXE
C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe
C:\PROGRA~1\AVG\AVG8\avgam.exe
C:\PROGRA~1\AVG\AVG8\avgnsx.exe
C:\Program Files\iPod\bin\iPodService.exe
C:\WINDOWS\system32\wuauclt.exe
C:\Program Files\MSN Messenger\usnsvc.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\WINDOWS\explorer.exe
C:\Program Files\AVG\AVG8\avgrsx.exe
C:\Program Files\AVG\AVG8\avgrsx.exe
C:\Program Files\Internet Explorer\IEXPLORE.EXE
C:\Program Files\Trend Micro\HijackThis\HijackThis.exe
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL = http://go.microsoft....k/?LinkId=69157
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Search_URL = http://go.microsoft....k/?LinkId=54896
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Page = http://go.microsoft....k/?LinkId=54896
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,AutoConfigURL = 192.168.0.65
O2 - BHO: Adobe PDF Reader Link Helper - {06849E9F-C8D7-4D59-B87D-784B7D6BE0B3} - C:\Program Files\Adobe\Acrobat 7.0\ActiveX\AcroIEHelper.dll
O2 - BHO: WormRadar.com IESiteBlocker.NavFilter - {3CA2F312-6F6E-4B53-A66E-4E65E497C8C0} - C:\Program Files\AVG\AVG8\avgssie.dll
O2 - BHO: URLLink Class - {4A2AACF3-ADF6-11D5-98A9-00E018981B9E} - C:\Program Files\NewDotNet\newdotnet3_88.dll (file missing)
O2 - BHO: Google Toolbar Helper - {AA58ED58-01DD-4d91-8333-CF10577473F7} - c:\program files\google\googletoolbar1.dll
O2 - BHO: Google Toolbar Notifier BHO - {AF69DE43-7D58-4638-B6FA-CE66B5AD205D} - C:\Program Files\Google\GoogleToolbarNotifier\2.0.1121.2472\swg.dll
O3 - Toolbar: &Google - {2318C2B1-4965-11d4-9B18-009027A5CD4F} - c:\program files\google\googletoolbar1.dll
O4 - HKLM\..\Run: [ATIPTA] C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe
O4 - HKLM\..\Run: [zBrowser Launcher] C:\Program Files\Logitech\iTouch\iTouch.exe
O4 - HKLM\..\Run: [Logitech Utility] Logi_MwX.Exe
O4 - HKLM\..\Run: [DAEMON Tools-1033] "C:\Program Files\D-Tools\daemon.exe" -lang 1033
O4 - HKLM\..\Run: [UserFaultCheck] %systemroot%\system32\dumprep 0 -u
O4 - HKLM\..\Run: [NeroFilterCheck] C:\WINDOWS\system32\NeroCheck.exe
O4 - HKLM\..\Run: [SunJavaUpdateSched] C:\Program Files\Java\jre1.5.0_04\bin\jusched.exe
O4 - HKLM\..\Run: [DU Meter] C:\Program Files\DU Meter\DUMeter.exe
O4 - HKLM\..\Run: [StartCCC] "C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\CLIStart.exe"
O4 - HKLM\..\Run: [ATICCC] "C:\Program Files\ATI Technologies\ATI.ACE\cli.exe" runtime -Delay
O4 - HKLM\..\Run: [AVG8_TRAY] C:\PROGRA~1\AVG\AVG8\avgtray.exe
O4 - HKLM\..\Run: [QuickTime Task] "C:\Program Files\QuickTime\qttask.exe" -atboottime
O4 - HKLM\..\Run: [iTunesHelper] "C:\Program Files\iTunes\iTunesHelper.exe"
O4 - HKLM\..\Run: [4oD] "C:\Program Files\Kontiki\KHost.exe" -all
O4 - HKCU\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\ctfmon.exe
O4 - HKCU\..\Run: [SetDefaultMIDI] MIDIDef.exe
O4 - HKCU\..\Run: [Skype] "C:\Program Files\Skype\Phone\Skype.exe" /nosplash /minimized
O4 - HKCU\..\Run: [swg] C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
O4 - HKCU\..\Run: [Steam] "c:\progra~1\valve\steam\steam.exe" -silent
O4 - HKCU\..\Run: [MsnMsgr] "C:\Program Files\MSN Messenger\MsnMsgr.Exe" /background
O4 - HKCU\..\Run: [DAEMON Tools Lite] "C:\Program Files\DAEMON Tools Lite\daemon.exe" -autorun
O4 - HKUS\S-1-5-19\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'LOCAL SERVICE')
O4 - HKUS\S-1-5-20\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'NETWORK SERVICE')
O4 - HKUS\S-1-5-18\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'SYSTEM')
O4 - HKUS\.DEFAULT\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'Default user')
O4 - Startup: Picture Motion Browser Media Check Tool.lnk = C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe
O4 - Global Startup: Adobe Reader Speed Launch.lnk = C:\Program Files\Adobe\Acrobat 7.0\Reader\reader_sl.exe
O4 - Global Startup: Microsoft Office.lnk = C:\Program Files\Microsoft Office\Office10\OSA.EXE
O4 - Global Startup: WinZip Quick Pick.lnk = C:\Program Files\WinZip\WZQKPICK.EXE
O8 - Extra context menu item: E&xport to Microsoft Excel - res://C:\PROGRA~1\MICROS~2\Office10\EXCEL.EXE/3000
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.5.0_04\bin\npjpi150_04.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.5.0_04\bin\npjpi150_04.dll
O9 - Extra button: Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O9 - Extra 'Tools' menuitem: Windows Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O12 - Plugin for .spop: C:\Program Files\Internet Explorer\Plugins\NPDocBox.dll
O16 - DPF: {05CDEE1D-D109-4992-B72B-6D4F5E2AB731} (PhotoBox uploader) - http://static.photob...geUploader4.cab
O16 - DPF: {0EB0E74A-2A76-4AB3-A7FB-9BD8C29F7F75} (CKAVWebScan Object) - http://www.kaspersky...can_unicode.cab
O16 - DPF: {4F1E5B1A-2A80-42CA-8532-2D05CB959537} (MSN Photo Upload Tool) - http://gfx1.hotmail....es/MSNPUpld.cab
O16 - DPF: {5C6698D9-7BE4-4122-8EC5-291D84DBD4A0} (Facebook Photo Uploader 4 Control) - http://upload.facebo...toUploader3.cab
O16 - DPF: {6414512B-B978-451D-A0D8-FCFDF33E833C} (WUWebControl Class) - http://v5.windowsupd...b?1099406122515
O16 - DPF: {67A5F8DC-1A4B-4D66-9F24-A704AD929EEE} (System Requirements Lab) - http://www.systemreq.../sysreqlab2.cab
O18 - Protocol: linkscanner - {F274614C-63F8-47D5-A4D1-FBDDE494F8D1} - C:\Program Files\AVG\AVG8\avgpp.dll
O20 - AppInit_DLLs: avgrsstx.dll
O23 - Service: Ad-Aware 2007 Service (aawservice) - Lavasoft - C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
O23 - Service: Apple Mobile Device - Apple, Inc. - C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
O23 - Service: asurscsi - Unknown owner - C:\Program Files\Voyetra\AudioSurgeon 5\asurscsi.exe (file missing)
O23 - Service: avast! iAVS4 Control Service (aswUpdSv) - ALWIL Software - C:\Program Files\Alwil Software\Avast4\aswUpdSv.exe
O23 - Service: Ati HotKey Poller - ATI Technologies Inc. - C:\WINDOWS\system32\Ati2evxx.exe
O23 - Service: ATI Smart - Unknown owner - C:\WINDOWS\system32\ati2sgag.exe
O23 - Service: avast! Antivirus - ALWIL Software - C:\Program Files\Alwil Software\Avast4\ashServ.exe
O23 - Service: avast! Mail Scanner - ALWIL Software - C:\Program Files\Alwil Software\Avast4\ashMaiSv.exe
O23 - Service: avast! Web Scanner - ALWIL Software - C:\Program Files\Alwil Software\Avast4\ashWebSv.exe
O23 - Service: AVG8 WatchDog (avg8wd) - AVG Technologies CZ, s.r.o. - C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe
O23 - Service: Google Updater Service (gusvc) - Google - C:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
O23 - Service: InstallDriver Table Manager (IDriverT) - Macrovision Corporation - C:\Program Files\Common Files\InstallShield\Driver\11\Intel 32\IDriverT.exe
O23 - Service: iPod Service - Apple Inc. - C:\Program Files\iPod\bin\iPodService.exe
O23 - Service: PnkBstrA - Unknown owner - C:\WINDOWS\system32\PnkBstrA.exe
O23 - Service: PnkBstrB - Unknown owner - C:\WINDOWS\system32\PnkBstrB.exe
--
End of file - 9400 bytes
ComboFix 08-05-07.2 - Tobyzooka 2008-05-08 18:02:35.1 - NTFSx86
Microsoft Windows XP Professional 5.1.2600.2.1252.1.1033.18.557 [GMT 1:00]
Running from: C:\Documents and Settings\Tobyzooka\Desktop\ComboFix.exe
Command switches used :: C:\Documents and Settings\Tobyzooka\Desktop\WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
* Created a new restore point
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
C:\autorun.inf
C:\Program Files\newdotnet
C:\Program Files\newdotnet\readme.txt
C:\setup.exe
C:\WINDOWS\cookies.ini
C:\WINDOWS\system32\hhxjuufi.ini
C:\WINDOWS\system32\RrCfefii.ini
C:\WINDOWS\system32\RrCfefii.ini2
.
((((((((((((((((((((((((( Files Created from 2008-04-08 to 2008-05-08 )))))))))))))))))))))))))))))))
.
2008-05-14 12:13 . 2008-05-14 18:34 <DIR> d--h----- C:\$AVG8.VAULT$
2008-05-14 12:06 . 2008-05-14 12:06 10,520 --a------ C:\WINDOWS\system32\avgrsstx.dll
2008-05-14 12:05 . 2008-05-14 12:28 <DIR> d-------- C:\WINDOWS\system32\drivers\Avg
2008-05-14 12:05 . 2008-05-14 12:05 96,520 --a------ C:\WINDOWS\system32\drivers\avgldx86.sys
2008-05-14 12:05 . 2008-05-14 12:05 75,272 --a------ C:\WINDOWS\system32\drivers\avgtdix.sys
2008-05-14 12:05 . 2008-05-14 12:05 12,424 --a------ C:\WINDOWS\system32\drivers\avgrkx86.sys
2008-05-14 12:03 . 2008-05-14 12:03 <DIR> d-------- C:\Documents and Settings\Tobyzooka\Application Data\TmpRecentIcons
2008-05-14 10:36 . 2008-05-14 15:10 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\anwbqpep
2008-05-10 12:56 . 2008-05-10 12:56 233,472 --a------ C:\WINDOWS\system32\REX Shared Library.dll
2008-05-10 12:51 . 2008-05-10 12:51 <DIR> d-------- C:\Program Files\Propellerhead
2008-05-10 12:48 . 2008-05-10 12:48 <DIR> d-------- C:\Program Files\DAEMON Tools Lite
2008-05-10 12:45 . 2008-05-10 12:45 <DIR> d-------- C:\Documents and Settings\Tobyzooka\Application Data\DAEMON Tools
2008-05-10 12:45 . 2008-05-10 12:45 717,296 --a------ C:\WINDOWS\system32\drivers\sptd.sys
2008-05-04 16:31 . 2008-05-04 16:31 <DIR> d-------- C:\Program Files\Common Files\Wise Installation Wizard
2008-05-01 13:01 . 2008-05-01 13:03 49,152 --a------ C:\WINDOWS\system32\apache.dll
2008-04-30 19:08 . 2008-04-30 19:08 <DIR> d-------- C:\Program Files\SystemRequirementsLab
2008-04-09 11:14 . 2008-04-09 11:14 <DIR> d-------- C:\SDPlugins
2008-04-09 11:14 . 2008-04-09 11:14 <DIR> d-------- C:\DirectX
2008-04-09 11:11 . 2008-04-09 11:14 <DIR> d-------- C:\data
2008-04-09 11:11 . 2008-04-09 11:11 <DIR> d-------- C:\AppData
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2008-05-14 15:41 22,328 ----a-w C:\WINDOWS\system32\drivers\PnkBstrK.sys
2008-05-14 15:38 107,832 ----a-w C:\WINDOWS\system32\PnkBstrB.exe
2008-05-14 11:02 --------- d-----w C:\Documents and Settings\All Users\Application Data\avg8
2008-05-08 17:08 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Skype
2008-05-05 20:46 27,048 ----a-w C:\WINDOWS\system32\drivers\mbamcatchme.sys
2008-05-05 20:46 15,864 ----a-w C:\WINDOWS\system32\drivers\mbam.sys
2008-05-04 23:41 --------- d-----w C:\Program Files\SlySoft
2008-05-04 15:32 --------- d-----w C:\Program Files\Lavasoft
2008-05-04 15:31 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Lavasoft
2008-05-01 22:38 --------- d--h--w C:\Program Files\InstallShield Installation Information
2008-05-01 22:38 --------- d-----w C:\Program Files\EA Games
2008-04-28 08:03 82,944 ----a-w C:\WINDOWS\system32\IEDFix.exe
2008-04-28 08:03 82,944 ----a-w C:\WINDOWS\system32\404Fix.exe
2008-04-24 08:10 86,528 ----a-w C:\WINDOWS\system32\VACFix.exe
2008-04-15 11:44 --------- d-----w C:\Program Files\Azureus
2008-03-29 18:16 --------- d-----w C:\Program Files\iTunes
2008-03-29 18:16 --------- d-----w C:\Program Files\iPod
2008-03-29 18:15 --------- d-----w C:\Program Files\QuickTime
2008-03-22 01:51 --------- d-----w C:\Program Files\BestGameEver
2008-03-21 19:50 --------- d-----w C:\Program Files\AVG
2008-03-19 19:32 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Sony Corporation
2008-03-19 19:24 --------- d-----w C:\Program Files\Sony
2008-03-19 19:08 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Publish Providers
2008-03-19 19:07 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Sony
2008-03-19 19:06 --------- d-----w C:\Program Files\Sony Setup
2008-03-19 14:46 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Cakewalk
2008-03-19 14:45 --------- d-----w C:\Documents and Settings\All Users\Application Data\Cakewalk
2008-03-19 14:44 --------- d-----w C:\Program Files\Cakewalk
2008-03-19 10:11 --------- d-----w C:\Program Files\MagicISO
2008-03-19 09:47 1,845,248 ----a-w C:\WINDOWS\system32\win32k.sys
2008-02-20 06:51 282,624 ----a-w C:\WINDOWS\system32\gdi32.dll
2008-02-20 05:32 45,568 ----a-w C:\WINDOWS\system32\dnsrslvr.dll
2005-10-09 19:21 18,704 ----a-w C:\Documents and Settings\Tobyzooka\Application Data\GDIPFONTCACHEV1.DAT
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_LOCAL_MACHINE\~\Browser Helper Objects\{4A2AACF3-ADF6-11D5-98A9-00E018981B9E}]
C:\Program Files\NewDotNet\newdotnet3_88.dll
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"CTFMON.EXE"="C:\WINDOWS\system32\ctfmon.exe" [2004-08-04 08:56 15360]
"SetDefaultMIDI"="MIDIDef.exe" []
"Skype"="C:\Program Files\Skype\Phone\Skype.exe" [2005-10-10 14:01 14881320]
"swg"="C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe" [2007-09-16 12:50 68856]
"Steam"="c:\progra~1\valve\steam\steam.exe" [2008-04-27 17:07 1271032]
"MsnMsgr"="C:\Program Files\MSN Messenger\MsnMsgr.exe" [2007-01-19 12:54 5674352]
"DAEMON Tools Lite"="C:\Program Files\DAEMON Tools Lite\daemon.exe" [2008-04-01 10:39 486856]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ATIPTA"="C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe" [2005-05-12 21:05 344064]
"zBrowser Launcher"="C:\Program Files\Logitech\iTouch\iTouch.exe" [2003-04-07 03:16 631364]
"Logitech Utility"="Logi_MwX.Exe" [2002-11-08 11:50 19968 C:\WINDOWS\LOGI_MWX.EXE]
"DAEMON Tools-1033"="C:\Program Files\D-Tools\daemon.exe" [2004-08-22 18:05 81920]
"UserFaultCheck"="C:\WINDOWS\system32\dumprep 0 -u" [ ]
"NeroFilterCheck"="C:\WINDOWS\system32\NeroCheck.exe" [2001-07-09 11:50 155648]
"SunJavaUpdateSched"="C:\Program Files\Java\jre1.5.0_04\bin\jusched.exe" [2005-06-03 03:52 36975]
"DU Meter"="C:\Program Files\DU Meter\DUMeter.exe" [2005-02-01 19:28 1469952]
"StartCCC"="C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\CLIStart.exe" [2006-11-10 12:35 90112]
"ATICCC"="C:\Program Files\ATI Technologies\ATI.ACE\cli.exe" [2006-01-02 17:41 45056]
"AVG8_TRAY"="C:\PROGRA~1\AVG\AVG8\avgtray.exe" [2008-05-14 12:30 1177368]
"QuickTime Task"="C:\Program Files\QuickTime\qttask.exe" [2008-02-01 00:13 385024]
"iTunesHelper"="C:\Program Files\iTunes\iTunesHelper.exe" [2008-02-19 14:10 267048]
"4oD"="C:\Program Files\Kontiki\KHost.exe" [ ]
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run]
"CTFMON.EXE"="C:\WINDOWS\System32\CTFMON.EXE" [2004-08-04 08:56 15360]
"Norton SystemWorks"="C:\Program Files\Norton SystemWorks\cfgwiz.exe" [ ]
C:\Documents and Settings\Tobyzooka\Start Menu\Programs\Startup\
Picture Motion Browser Media Check Tool.lnk - C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe [2008-03-19 20:24:18 344064]
C:\Documents and Settings\All Users\Start Menu\Programs\Startup\
Adobe Reader Speed Launch.lnk - C:\Program Files\Adobe\Acrobat 7.0\Reader\reader_sl.exe [2005-09-23 22:05:26 29696]
Microsoft Office.lnk - C:\Program Files\Microsoft Office\Office10\OSA.EXE [2001-02-13 02:01:04 83360]
WinZip Quick Pick.lnk - C:\Program Files\WinZip\WZQKPICK.EXE [2005-09-25 20:31:11 118784]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\windows]
"AppInit_DLLs"=avgrsstx.dll
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\drivers32]
"vidc.ffds"= ffdshow.ax
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusDisableNotify"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"C:\\Program Files\\Valve\\Steam\\SteamApps\\tobazooka\\counter-strike source\\hl2.exe"=
"C:\\Program Files\\Valve\\Steam\\Steam.exe"=
"C:\\Program Files\\Real\\RealPlayer\\realplay.exe"=
"C:\\Program Files\\Messenger\\msmsgs.exe"=
"C:\\WINDOWS\\system32\\dpvsetup.exe"=
"C:\\WINDOWS\\system32\\rundll32.exe"=
"C:\\WINDOWS\\system32\\dplaysvr.exe"=
"C:\\Program Files\\Java\\jre1.5.0_04\\bin\\javaw.exe"=
"C:\\Program Files\\Valve\\Steam\\SteamApps\\tobazooka\\source sdk base\\hl2.exe"=
"C:\\Program Files\\MSN Messenger\\msnmsgr.exe"=
"C:\\Program Files\\MSN Messenger\\livecall.exe"=
"C:\\WINDOWS\\system32\\dpnsvr.exe"=
"C:\\Program Files\\iTunes\\iTunes.exe"=
"C:\\Program Files\\Azureus\\Azureus.exe"=
"C:\\Program Files\\EA Games\\Battlefield 2\\BF2.exe"=
"C:\\Program Files\\AVG\\AVG8\\avgupd.exe"=
"C:\\Program Files\\AVG\\AVG8\\avgnsx.exe"=
"C:\\Program Files\\Skype\\Phone\\Skype.exe"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"3389:TCP"= 3389:TCP:@xpsp2res.dll,-22009
R0 AvgRkx86;avgrkx86.sys;C:\WINDOWS\system32\Drivers\avgrkx86.sys [2008-05-14 12:05]
R0 xmasbus;xmasbus;C:\WINDOWS\system32\DRIVERS\xmasbus.sys [2003-12-21 18:24]
R0 xmasscsi;xmasscsi;C:\WINDOWS\system32\Drivers\xmasscsi.sys [2003-12-23 03:15]
R1 aswSP;avast! Self Protection;C:\WINDOWS\system32\drivers\aswSP.sys [2008-03-29 19:31]
R1 AvgLdx86;AVG AVI Loader Driver x86;C:\WINDOWS\system32\Drivers\avgldx86.sys [2008-05-14 12:05]
R2 aswFsBlk;aswFsBlk;C:\WINDOWS\system32\DRIVERS\aswFsBlk.sys [2008-03-29 19:35]
R2 avg8wd;AVG8 WatchDog;C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe [2008-05-14 12:05]
R2 AvgTdiX;AVG8 Network Redirector;C:\WINDOWS\system32\Drivers\avgtdix.sys [2008-05-14 12:05]
S2 asurscsi;asurscsi;C:\Program Files\Voyetra\AudioSurgeon 5\asurscsi.exe []
S3 ldiskl;ldiskl;C:\DOCUME~1\TOBYZO~1\LOCALS~1\Temp\ldiskl.sys []
S3 SetupNTGLM7X;SetupNTGLM7X;D:\NTGLM7X.sys []
[HKEY_CURRENT_USER\software\microsoft\windows\currentversion\explorer\mountpoints2\C]
\Shell\AutoRun\command - C:\autorun.exe
.
Contents of the 'Scheduled Tasks' folder
"2008-05-06 14:13:02 C:\WINDOWS\Tasks\AppleSoftwareUpdate.job"
- C:\Program Files\Apple Software Update\SoftwareUpdate.exe
"2008-05-14 14:35:14 C:\WINDOWS\Tasks\Symantec NetDetect.job"
- C:\Program Files\Symantec\LiveUpdate\NDETECT.EXE
.
**************************************************************************
catchme 0.3.1353 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2008-05-08 18:07:34
Windows 5.1.2600 Service Pack 2 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
--------------------- DLLs Loaded Under Running Processes ---------------------
PROCESS: C:\WINDOWS\system32\lsass.exe
-> C:\WINDOWS\system32\xfire_lsp_10650.dll
.
------------------------ Other Running Processes ------------------------
.
C:\WINDOWS\system32\ati2evxx.exe
C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
C:\Program Files\Alwil Software\Avast4\aswUpdSv.exe
C:\WINDOWS\system32\ati2evxx.exe
C:\Program Files\Logitech\MouseWare\system\EM_EXEC.EXE
C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
C:\WINDOWS\system32\PnkBstrA.exe
C:\WINDOWS\system32\PnkBstrB.exe
C:\WINDOWS\system32\wdfmgr.exe
C:\WINDOWS\system32\MsPMSPSv.exe
C:\PROGRA~1\AVG\AVG8\avgam.exe
C:\PROGRA~1\AVG\AVG8\avgnsx.exe
C:\Program Files\iPod\bin\iPodService.exe
C:\Program Files\MSN Messenger\usnsvc.exe
C:\Program Files\AVG\AVG8\avgrsx.exe
C:\Program Files\AVG\AVG8\avgrsx.exe
.
**************************************************************************
.
Completion time: 2008-05-08 18:14:14 - machine was rebooted [Tobyzooka]
ComboFix-quarantined-files.txt 2008-05-08 17:14:07
Pre-Run: 24,043,114,496 bytes free
Post-Run: 23,928,598,528 bytes free
WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
[boot loader]
timeout=2
default=multi(0)disk(0)rdisk(0)partition(1)\WINDOWS
[operating systems]
multi(0)disk(0)rdisk(0)partition(1)\WINDOWS="Microsoft Windows XP Professional" /fastdetect /NoExecute=OptIn
C:\CMDCONS\BOOTSECT.DAT="Microsoft Windows Recovery Console" /cmdcons
210 --- E O F --- 2008-05-12 06:56:26
4.
Logfile of Trend Micro HijackThis v2.0.2
Scan saved at 22:10:34, on 08/05/2008
Platform: Windows XP SP2 (WinNT 5.01.2600)
MSIE: Internet Explorer v6.00 SP2 (6.00.2900.2180)
Boot mode: Normal
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
C:\Program Files\Alwil Software\Avast4\aswUpdSv.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\Program Files\Logitech\iTouch\iTouch.exe
C:\Program Files\Java\jre1.5.0_04\bin\jusched.exe
C:\Program Files\DU Meter\DUMeter.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\PROGRA~1\AVG\AVG8\avgtray.exe
C:\Program Files\iTunes\iTunesHelper.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\Logitech\MouseWare\system\em_exec.exe
C:\WINDOWS\system32\spoolsv.exe
C:\Program Files\Skype\Phone\Skype.exe
C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe
C:\Program Files\MSN Messenger\MsnMsgr.Exe
C:\Program Files\DAEMON Tools Lite\daemon.exe
C:\WINDOWS\system32\PnkBstrA.exe
C:\WINDOWS\system32\PnkBstrB.exe
C:\WINDOWS\system32\MsPMSPSv.exe
C:\Program Files\WinZip\WZQKPICK.EXE
C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe
C:\PROGRA~1\AVG\AVG8\avgam.exe
C:\PROGRA~1\AVG\AVG8\avgnsx.exe
C:\Program Files\iPod\bin\iPodService.exe
C:\WINDOWS\system32\wuauclt.exe
C:\Program Files\MSN Messenger\usnsvc.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\WINDOWS\explorer.exe
C:\Program Files\AVG\AVG8\avgrsx.exe
C:\Program Files\AVG\AVG8\avgrsx.exe
C:\Program Files\Internet Explorer\IEXPLORE.EXE
C:\Program Files\Trend Micro\HijackThis\HijackThis.exe
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL = http://go.microsoft....k/?LinkId=69157
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Search_URL = http://go.microsoft....k/?LinkId=54896
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Page = http://go.microsoft....k/?LinkId=54896
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,AutoConfigURL = 192.168.0.65
O2 - BHO: Adobe PDF Reader Link Helper - {06849E9F-C8D7-4D59-B87D-784B7D6BE0B3} - C:\Program Files\Adobe\Acrobat 7.0\ActiveX\AcroIEHelper.dll
O2 - BHO: WormRadar.com IESiteBlocker.NavFilter - {3CA2F312-6F6E-4B53-A66E-4E65E497C8C0} - C:\Program Files\AVG\AVG8\avgssie.dll
O2 - BHO: URLLink Class - {4A2AACF3-ADF6-11D5-98A9-00E018981B9E} - C:\Program Files\NewDotNet\newdotnet3_88.dll (file missing)
O2 - BHO: Google Toolbar Helper - {AA58ED58-01DD-4d91-8333-CF10577473F7} - c:\program files\google\googletoolbar1.dll
O2 - BHO: Google Toolbar Notifier BHO - {AF69DE43-7D58-4638-B6FA-CE66B5AD205D} - C:\Program Files\Google\GoogleToolbarNotifier\2.0.1121.2472\swg.dll
O3 - Toolbar: &Google - {2318C2B1-4965-11d4-9B18-009027A5CD4F} - c:\program files\google\googletoolbar1.dll
O4 - HKLM\..\Run: [ATIPTA] C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe
O4 - HKLM\..\Run: [zBrowser Launcher] C:\Program Files\Logitech\iTouch\iTouch.exe
O4 - HKLM\..\Run: [Logitech Utility] Logi_MwX.Exe
O4 - HKLM\..\Run: [DAEMON Tools-1033] "C:\Program Files\D-Tools\daemon.exe" -lang 1033
O4 - HKLM\..\Run: [UserFaultCheck] %systemroot%\system32\dumprep 0 -u
O4 - HKLM\..\Run: [NeroFilterCheck] C:\WINDOWS\system32\NeroCheck.exe
O4 - HKLM\..\Run: [SunJavaUpdateSched] C:\Program Files\Java\jre1.5.0_04\bin\jusched.exe
O4 - HKLM\..\Run: [DU Meter] C:\Program Files\DU Meter\DUMeter.exe
O4 - HKLM\..\Run: [StartCCC] "C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\CLIStart.exe"
O4 - HKLM\..\Run: [ATICCC] "C:\Program Files\ATI Technologies\ATI.ACE\cli.exe" runtime -Delay
O4 - HKLM\..\Run: [AVG8_TRAY] C:\PROGRA~1\AVG\AVG8\avgtray.exe
O4 - HKLM\..\Run: [QuickTime Task] "C:\Program Files\QuickTime\qttask.exe" -atboottime
O4 - HKLM\..\Run: [iTunesHelper] "C:\Program Files\iTunes\iTunesHelper.exe"
O4 - HKLM\..\Run: [4oD] "C:\Program Files\Kontiki\KHost.exe" -all
O4 - HKCU\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\ctfmon.exe
O4 - HKCU\..\Run: [SetDefaultMIDI] MIDIDef.exe
O4 - HKCU\..\Run: [Skype] "C:\Program Files\Skype\Phone\Skype.exe" /nosplash /minimized
O4 - HKCU\..\Run: [swg] C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
O4 - HKCU\..\Run: [Steam] "c:\progra~1\valve\steam\steam.exe" -silent
O4 - HKCU\..\Run: [MsnMsgr] "C:\Program Files\MSN Messenger\MsnMsgr.Exe" /background
O4 - HKCU\..\Run: [DAEMON Tools Lite] "C:\Program Files\DAEMON Tools Lite\daemon.exe" -autorun
O4 - HKUS\S-1-5-19\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'LOCAL SERVICE')
O4 - HKUS\S-1-5-20\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'NETWORK SERVICE')
O4 - HKUS\S-1-5-18\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'SYSTEM')
O4 - HKUS\.DEFAULT\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'Default user')
O4 - Startup: Picture Motion Browser Media Check Tool.lnk = C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe
O4 - Global Startup: Adobe Reader Speed Launch.lnk = C:\Program Files\Adobe\Acrobat 7.0\Reader\reader_sl.exe
O4 - Global Startup: Microsoft Office.lnk = C:\Program Files\Microsoft Office\Office10\OSA.EXE
O4 - Global Startup: WinZip Quick Pick.lnk = C:\Program Files\WinZip\WZQKPICK.EXE
O8 - Extra context menu item: E&xport to Microsoft Excel - res://C:\PROGRA~1\MICROS~2\Office10\EXCEL.EXE/3000
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.5.0_04\bin\npjpi150_04.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.5.0_04\bin\npjpi150_04.dll
O9 - Extra button: Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O9 - Extra 'Tools' menuitem: Windows Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O10 - Unknown file in Winsock LSP: xfire_lsp_10650.dll
O12 - Plugin for .spop: C:\Program Files\Internet Explorer\Plugins\NPDocBox.dll
O16 - DPF: {05CDEE1D-D109-4992-B72B-6D4F5E2AB731} (PhotoBox uploader) - http://static.photob...geUploader4.cab
O16 - DPF: {0EB0E74A-2A76-4AB3-A7FB-9BD8C29F7F75} (CKAVWebScan Object) - http://www.kaspersky...can_unicode.cab
O16 - DPF: {4F1E5B1A-2A80-42CA-8532-2D05CB959537} (MSN Photo Upload Tool) - http://gfx1.hotmail....es/MSNPUpld.cab
O16 - DPF: {5C6698D9-7BE4-4122-8EC5-291D84DBD4A0} (Facebook Photo Uploader 4 Control) - http://upload.facebo...toUploader3.cab
O16 - DPF: {6414512B-B978-451D-A0D8-FCFDF33E833C} (WUWebControl Class) - http://v5.windowsupd...b?1099406122515
O16 - DPF: {67A5F8DC-1A4B-4D66-9F24-A704AD929EEE} (System Requirements Lab) - http://www.systemreq.../sysreqlab2.cab
O18 - Protocol: linkscanner - {F274614C-63F8-47D5-A4D1-FBDDE494F8D1} - C:\Program Files\AVG\AVG8\avgpp.dll
O20 - AppInit_DLLs: avgrsstx.dll
O23 - Service: Ad-Aware 2007 Service (aawservice) - Lavasoft - C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
O23 - Service: Apple Mobile Device - Apple, Inc. - C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
O23 - Service: asurscsi - Unknown owner - C:\Program Files\Voyetra\AudioSurgeon 5\asurscsi.exe (file missing)
O23 - Service: avast! iAVS4 Control Service (aswUpdSv) - ALWIL Software - C:\Program Files\Alwil Software\Avast4\aswUpdSv.exe
O23 - Service: Ati HotKey Poller - ATI Technologies Inc. - C:\WINDOWS\system32\Ati2evxx.exe
O23 - Service: ATI Smart - Unknown owner - C:\WINDOWS\system32\ati2sgag.exe
O23 - Service: avast! Antivirus - ALWIL Software - C:\Program Files\Alwil Software\Avast4\ashServ.exe
O23 - Service: avast! Mail Scanner - ALWIL Software - C:\Program Files\Alwil Software\Avast4\ashMaiSv.exe
O23 - Service: avast! Web Scanner - ALWIL Software - C:\Program Files\Alwil Software\Avast4\ashWebSv.exe
O23 - Service: AVG8 WatchDog (avg8wd) - AVG Technologies CZ, s.r.o. - C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe
O23 - Service: Google Updater Service (gusvc) - Google - C:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
O23 - Service: InstallDriver Table Manager (IDriverT) - Macrovision Corporation - C:\Program Files\Common Files\InstallShield\Driver\11\Intel 32\IDriverT.exe
O23 - Service: iPod Service - Apple Inc. - C:\Program Files\iPod\bin\iPodService.exe
O23 - Service: PnkBstrA - Unknown owner - C:\WINDOWS\system32\PnkBstrA.exe
O23 - Service: PnkBstrB - Unknown owner - C:\WINDOWS\system32\PnkBstrB.exe
--
End of file - 9400 bytes
#23
![I'm still treading water but fear I may drown [RESOLVED]: post #23](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 02:42 PM
Posted 08 May 2008 - 02:42 PM

5.
-------------------------------------------------------------------------------
KASPERSKY ONLINE SCANNER REPORT
Thursday, May 08, 2008 9:59:50 PM
Operating System: Microsoft Windows XP Professional, Service Pack 2 (Build 2600)
Kaspersky Online Scanner version: 5.0.98.0
Kaspersky Anti-Virus database last update: 8/05/2008
Kaspersky Anti-Virus database records: 747047
-------------------------------------------------------------------------------
Scan Settings:
Scan using the following antivirus database: extended
Scan Archives: true
Scan Mail Bases: true
Scan Target - My Computer:
A:\
C:\
D:\
E:\
G:\
H:\
I:\
Scan Statistics:
Total number of scanned objects: 83073
Number of viruses found: 5
Number of infected objects: 6
Number of suspicious objects: 0
Duration of the scan process: 02:07:19
Infected Object Name / Virus Name / Last Action
C:\Documents and Settings\All Users\Application Data\avg8\AvgAm\avgam.lck Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgam.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgcfg.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgcore.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avglng.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgns.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgrs.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgsched.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgui.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgwd.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\Microsoft\Network\Downloader\qmgr0.dat Object is locked skipped
C:\Documents and Settings\All Users\Application Data\Microsoft\Network\Downloader\qmgr1.dat Object is locked skipped
C:\Documents and Settings\LocalService\Cookies\index.dat Object is locked skipped
C:\Documents and Settings\LocalService\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat Object is locked skipped
C:\Documents and Settings\LocalService\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.LOG Object is locked skipped
C:\Documents and Settings\LocalService\Local Settings\History\History.IE5\index.dat Object is locked skipped
C:\Documents and Settings\LocalService\Local Settings\Temporary Internet Files\Content.IE5\index.dat Object is locked skipped
C:\Documents and Settings\LocalService\NTUSER.DAT Object is locked skipped
C:\Documents and Settings\LocalService\ntuser.dat.LOG Object is locked skipped
C:\Documents and Settings\NetworkService\Cookies\index.dat Object is locked skipped
C:\Documents and Settings\NetworkService\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat Object is locked skipped
C:\Documents and Settings\NetworkService\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.LOG Object is locked skipped
C:\Documents and Settings\NetworkService\Local Settings\History\History.IE5\index.dat Object is locked skipped
C:\Documents and Settings\NetworkService\Local Settings\Temporary Internet Files\Content.IE5\index.dat Object is locked skipped
C:\Documents and Settings\NetworkService\NTUSER.DAT Object is locked skipped
C:\Documents and Settings\NetworkService\ntuser.dat.LOG Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\call256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chat256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chat4096.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chat512.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chatmsg1024.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chatmsg2048.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chatmsg256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chatmsg512.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\contactgroup256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\index2.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\message256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\profile4096.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\transfer256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\transfer512.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\user1024.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Cookies\index.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\ApplicationHistory\cli.exe.c88dbd71.ini.inuse Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Logs\Dfsr00005.log Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\pending.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Working\database_380C_327C_C32_34EA\dfsr.db Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Working\database_380C_327C_C32_34EA\fsr.log Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Working\database_380C_327C_C32_34EA\fsrtmp.log Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Working\database_380C_327C_C32_34EA\tmp.edb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.LOG Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Windows Live Contacts\[email protected]\real\members.stg Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Windows Live Contacts\[email protected]\shadow\members.stg Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\History\History.IE5\index.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\History\History.IE5\MSHist012008050820080509\index.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\Perflib_Perfdata_494.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\Perflib_Perfdata_52c.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\Perflib_Perfdata_c40.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\~DF5DC3.tmp Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\~DF6130.tmp Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\~DFF2CA.tmp Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\~DFF722.tmp Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temporary Internet Files\Content.IE5\index.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\ntuser.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\ntuser.dat.LOG Object is locked skipped
C:\Documents and Settings\Tobyzooka\UserData\index.dat Object is locked skipped
C:\found.000\dir0000.chk\get_video[1] Object is locked skipped
C:\found.000\dir0000.chk\GET_VI~2 Object is locked skipped
C:\found.000\dir0001.chk\default;sz=300x250;kr=F;kw=mel%20b;tile=1;dcopt=ist;ord=2296506701064828[2] Object is locked skipped
C:\found.000\dir0001.chk\default[3].jpg Object is locked skipped
C:\found.000\dir0001.chk\main_6;sz=480x70;!c=6;kvid=N6WhI9JNVrs;kpu=universalmusicgroup;ko=p;kpid=6;kr=F;k1=hip%20hop;u=N6WhI9JNVrs_6_37A5A123D24D56BB;tile=1;dcopt=ist;ord=41039[1].asx Object is locked skipped
C:\found.000\file0000.chk Object is locked skipped
C:\Program Files\Norton SystemWorks\Norton AntiVirus\Quarantine\1E4176C1.exe Infected: not-a-virus:Porn-Dialer.Win32.Intexdial skipped
C:\Program Files\Norton SystemWorks\Norton AntiVirus\Quarantine\3CF82F36.htm Infected: Exploit.HTML.Mht skipped
C:\Program Files\Norton SystemWorks\Norton AntiVirus\Quarantine\4C0924B5.htm Infected: Exploit.HTML.Mht skipped
C:\Program Files\Norton SystemWorks\Norton AntiVirus\Quarantine\63BB3BE0.htm Infected: Trojan-Downloader.JS.Small.d skipped
C:\System Volume Information\MountPointManagerRemoteDatabase Object is locked skipped
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP728\A0263458.dll Infected: not-a-virus:AdWare.Win32.HotBar.ck skipped
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP733\A0281846.exe Infected: not-a-virus:AdWare.Win32.NewDotNet.e skipped
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP734\change.log Object is locked skipped
C:\WINDOWS\Debug\PASSWD.LOG Object is locked skipped
C:\WINDOWS\SchedLgU.Txt Object is locked skipped
C:\WINDOWS\SoftwareDistribution\DataStore\DataStore.edb Object is locked skipped
C:\WINDOWS\SoftwareDistribution\DataStore\Logs\edb.log Object is locked skipped
C:\WINDOWS\SoftwareDistribution\DataStore\Logs\tmp.edb Object is locked skipped
C:\WINDOWS\SoftwareDistribution\ReportingEvents.log Object is locked skipped
C:\WINDOWS\system32\CatRoot2\edb.log Object is locked skipped
C:\WINDOWS\system32\CatRoot2\tmp.edb Object is locked skipped
C:\WINDOWS\system32\config\ACEEvent.evt Object is locked skipped
C:\WINDOWS\system32\config\Antivirus.Evt Object is locked skipped
C:\WINDOWS\system32\config\AppEvent.Evt Object is locked skipped
C:\WINDOWS\system32\config\default Object is locked skipped
C:\WINDOWS\system32\config\default.LOG Object is locked skipped
C:\WINDOWS\system32\config\Internet.evt Object is locked skipped
C:\WINDOWS\system32\config\SAM Object is locked skipped
C:\WINDOWS\system32\config\SAM.LOG Object is locked skipped
C:\WINDOWS\system32\config\SecEvent.Evt Object is locked skipped
C:\WINDOWS\system32\config\SECURITY Object is locked skipped
C:\WINDOWS\system32\config\SECURITY.LOG Object is locked skipped
C:\WINDOWS\system32\config\software Object is locked skipped
C:\WINDOWS\system32\config\software.LOG Object is locked skipped
C:\WINDOWS\system32\config\SysEvent.Evt Object is locked skipped
C:\WINDOWS\system32\config\system Object is locked skipped
C:\WINDOWS\system32\config\system.LOG Object is locked skipped
C:\WINDOWS\system32\drivers\sptd.sys Object is locked skipped
C:\WINDOWS\system32\h323log.txt Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\INDEX.BTR Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\INDEX.MAP Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\MAPPING.VER Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\MAPPING1.MAP Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\MAPPING2.MAP Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\OBJECTS.DATA Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\OBJECTS.MAP Object is locked skipped
C:\WINDOWS\WindowsUpdate.log Object is locked skipped
Scan process completed.
-------------------------------------------------------------------------------
KASPERSKY ONLINE SCANNER REPORT
Thursday, May 08, 2008 9:59:50 PM
Operating System: Microsoft Windows XP Professional, Service Pack 2 (Build 2600)
Kaspersky Online Scanner version: 5.0.98.0
Kaspersky Anti-Virus database last update: 8/05/2008
Kaspersky Anti-Virus database records: 747047
-------------------------------------------------------------------------------
Scan Settings:
Scan using the following antivirus database: extended
Scan Archives: true
Scan Mail Bases: true
Scan Target - My Computer:
A:\
C:\
D:\
E:\
G:\
H:\
I:\
Scan Statistics:
Total number of scanned objects: 83073
Number of viruses found: 5
Number of infected objects: 6
Number of suspicious objects: 0
Duration of the scan process: 02:07:19
Infected Object Name / Virus Name / Last Action
C:\Documents and Settings\All Users\Application Data\avg8\AvgAm\avgam.lck Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgam.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgcfg.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgcore.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avglng.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgns.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgrs.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgsched.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgui.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\avg8\Log\avgwd.log Object is locked skipped
C:\Documents and Settings\All Users\Application Data\Microsoft\Network\Downloader\qmgr0.dat Object is locked skipped
C:\Documents and Settings\All Users\Application Data\Microsoft\Network\Downloader\qmgr1.dat Object is locked skipped
C:\Documents and Settings\LocalService\Cookies\index.dat Object is locked skipped
C:\Documents and Settings\LocalService\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat Object is locked skipped
C:\Documents and Settings\LocalService\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.LOG Object is locked skipped
C:\Documents and Settings\LocalService\Local Settings\History\History.IE5\index.dat Object is locked skipped
C:\Documents and Settings\LocalService\Local Settings\Temporary Internet Files\Content.IE5\index.dat Object is locked skipped
C:\Documents and Settings\LocalService\NTUSER.DAT Object is locked skipped
C:\Documents and Settings\LocalService\ntuser.dat.LOG Object is locked skipped
C:\Documents and Settings\NetworkService\Cookies\index.dat Object is locked skipped
C:\Documents and Settings\NetworkService\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat Object is locked skipped
C:\Documents and Settings\NetworkService\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.LOG Object is locked skipped
C:\Documents and Settings\NetworkService\Local Settings\History\History.IE5\index.dat Object is locked skipped
C:\Documents and Settings\NetworkService\Local Settings\Temporary Internet Files\Content.IE5\index.dat Object is locked skipped
C:\Documents and Settings\NetworkService\NTUSER.DAT Object is locked skipped
C:\Documents and Settings\NetworkService\ntuser.dat.LOG Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\call256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chat256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chat4096.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chat512.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chatmsg1024.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chatmsg2048.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chatmsg256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\chatmsg512.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\contactgroup256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\index2.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\message256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\profile4096.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\transfer256.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\transfer512.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Application Data\Skype\to[bleep]\user1024.dbb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Cookies\index.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\ApplicationHistory\cli.exe.c88dbd71.ini.inuse Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Logs\Dfsr00005.log Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\pending.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Working\database_380C_327C_C32_34EA\dfsr.db Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Working\database_380C_327C_C32_34EA\fsr.log Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Working\database_380C_327C_C32_34EA\fsrtmp.log Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Messenger\[email protected]\SharingMetadata\Working\database_380C_327C_C32_34EA\tmp.edb Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Windows\UsrClass.dat.LOG Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Windows Live Contacts\[email protected]\real\members.stg Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Application Data\Microsoft\Windows Live Contacts\[email protected]\shadow\members.stg Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\History\History.IE5\index.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\History\History.IE5\MSHist012008050820080509\index.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\Perflib_Perfdata_494.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\Perflib_Perfdata_52c.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\Perflib_Perfdata_c40.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\~DF5DC3.tmp Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\~DF6130.tmp Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\~DFF2CA.tmp Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temp\~DFF722.tmp Object is locked skipped
C:\Documents and Settings\Tobyzooka\Local Settings\Temporary Internet Files\Content.IE5\index.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\ntuser.dat Object is locked skipped
C:\Documents and Settings\Tobyzooka\ntuser.dat.LOG Object is locked skipped
C:\Documents and Settings\Tobyzooka\UserData\index.dat Object is locked skipped
C:\found.000\dir0000.chk\get_video[1] Object is locked skipped
C:\found.000\dir0000.chk\GET_VI~2 Object is locked skipped
C:\found.000\dir0001.chk\default;sz=300x250;kr=F;kw=mel%20b;tile=1;dcopt=ist;ord=2296506701064828[2] Object is locked skipped
C:\found.000\dir0001.chk\default[3].jpg Object is locked skipped
C:\found.000\dir0001.chk\main_6;sz=480x70;!c=6;kvid=N6WhI9JNVrs;kpu=universalmusicgroup;ko=p;kpid=6;kr=F;k1=hip%20hop;u=N6WhI9JNVrs_6_37A5A123D24D56BB;tile=1;dcopt=ist;ord=41039[1].asx Object is locked skipped
C:\found.000\file0000.chk Object is locked skipped
C:\Program Files\Norton SystemWorks\Norton AntiVirus\Quarantine\1E4176C1.exe Infected: not-a-virus:Porn-Dialer.Win32.Intexdial skipped
C:\Program Files\Norton SystemWorks\Norton AntiVirus\Quarantine\3CF82F36.htm Infected: Exploit.HTML.Mht skipped
C:\Program Files\Norton SystemWorks\Norton AntiVirus\Quarantine\4C0924B5.htm Infected: Exploit.HTML.Mht skipped
C:\Program Files\Norton SystemWorks\Norton AntiVirus\Quarantine\63BB3BE0.htm Infected: Trojan-Downloader.JS.Small.d skipped
C:\System Volume Information\MountPointManagerRemoteDatabase Object is locked skipped
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP728\A0263458.dll Infected: not-a-virus:AdWare.Win32.HotBar.ck skipped
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP733\A0281846.exe Infected: not-a-virus:AdWare.Win32.NewDotNet.e skipped
C:\System Volume Information\_restore{CA71844E-75EB-4E5C-B38D-EDB5AC338045}\RP734\change.log Object is locked skipped
C:\WINDOWS\Debug\PASSWD.LOG Object is locked skipped
C:\WINDOWS\SchedLgU.Txt Object is locked skipped
C:\WINDOWS\SoftwareDistribution\DataStore\DataStore.edb Object is locked skipped
C:\WINDOWS\SoftwareDistribution\DataStore\Logs\edb.log Object is locked skipped
C:\WINDOWS\SoftwareDistribution\DataStore\Logs\tmp.edb Object is locked skipped
C:\WINDOWS\SoftwareDistribution\ReportingEvents.log Object is locked skipped
C:\WINDOWS\system32\CatRoot2\edb.log Object is locked skipped
C:\WINDOWS\system32\CatRoot2\tmp.edb Object is locked skipped
C:\WINDOWS\system32\config\ACEEvent.evt Object is locked skipped
C:\WINDOWS\system32\config\Antivirus.Evt Object is locked skipped
C:\WINDOWS\system32\config\AppEvent.Evt Object is locked skipped
C:\WINDOWS\system32\config\default Object is locked skipped
C:\WINDOWS\system32\config\default.LOG Object is locked skipped
C:\WINDOWS\system32\config\Internet.evt Object is locked skipped
C:\WINDOWS\system32\config\SAM Object is locked skipped
C:\WINDOWS\system32\config\SAM.LOG Object is locked skipped
C:\WINDOWS\system32\config\SecEvent.Evt Object is locked skipped
C:\WINDOWS\system32\config\SECURITY Object is locked skipped
C:\WINDOWS\system32\config\SECURITY.LOG Object is locked skipped
C:\WINDOWS\system32\config\software Object is locked skipped
C:\WINDOWS\system32\config\software.LOG Object is locked skipped
C:\WINDOWS\system32\config\SysEvent.Evt Object is locked skipped
C:\WINDOWS\system32\config\system Object is locked skipped
C:\WINDOWS\system32\config\system.LOG Object is locked skipped
C:\WINDOWS\system32\drivers\sptd.sys Object is locked skipped
C:\WINDOWS\system32\h323log.txt Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\INDEX.BTR Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\INDEX.MAP Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\MAPPING.VER Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\MAPPING1.MAP Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\MAPPING2.MAP Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\OBJECTS.DATA Object is locked skipped
C:\WINDOWS\system32\wbem\Repository\FS\OBJECTS.MAP Object is locked skipped
C:\WINDOWS\WindowsUpdate.log Object is locked skipped
Scan process completed.
#24
![I'm still treading water but fear I may drown [RESOLVED]: post #24](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 03:33 PM
Posted 08 May 2008 - 03:33 PM

that is looking much better 
the infections the kaspersky scan found were all either safely quarantined or in your system restore points (which we will clean out at the end).
in this post we will remove the last of the malware and update your java.
we will also remove !Avast - you need only one antivirus, having 2 can use up system resources, slow down your PC and provide less instead of more protection.
====STEP 1====
A malicious .DLL file is disrupting the LSP chain on your computer. We need to get rid of it.
====STEP 2====
i am assuming your main antivirus is AVG? if not, then skip this step and let me know.
Please go to Start > Control Panel > Add/Remove Programs and remove the following (if present):
avast! Antivirus
Please note any other programs that you dont recognize in that list in your next response
====STEP 3====
Clearing the Java cache:
there is a nice set of instructions http://www.java.com/.../5000020300.xml
Please go to Start > Control Panel > Add/Remove Programs and remove the following (if present):
J2SE Runtime Environment 5.0 Update 4
Upgrading Java:
====STEP 4====
1. Please open Notepad
2. Now copy/paste the entire content of the codebox below into the Notepad window:
3. Save the above as CFScript.txt
4. Then drag the CFScript.txt into ComboFix.exe as depicted in the animation below. This will start ComboFix again.

5. After reboot, (in case it asks to reboot), please post the following reports/logs into your next reply:
In your next reply could i see:
1. the combofix log
2. a new hijackthis log
3. some idea of how your machine is running now
The text from these files may exceed the maximum post length for this forum. Hence, you may need to post the information over 2 or more posts.
andrewuk
the infections the kaspersky scan found were all either safely quarantined or in your system restore points (which we will clean out at the end).
in this post we will remove the last of the malware and update your java.
we will also remove !Avast - you need only one antivirus, having 2 can use up system resources, slow down your PC and provide less instead of more protection.
====STEP 1====
A malicious .DLL file is disrupting the LSP chain on your computer. We need to get rid of it.
- If you dont have it from before then please download LSPFix from here.
- Run the LSPFix.exe that you have just finished downloading.
- Check the I know what I'm doing box.
- In the Keep box you should see one or more instances of xfire_lsp_10650.dll.
- Select every instance of xfire_lsp_10650.dll and move each one to the Remove box by clicking the >> button.
- When you are done click Finish>>.
====STEP 2====
i am assuming your main antivirus is AVG? if not, then skip this step and let me know.
Please go to Start > Control Panel > Add/Remove Programs and remove the following (if present):
avast! Antivirus
Please note any other programs that you dont recognize in that list in your next response
====STEP 3====
Clearing the Java cache:
there is a nice set of instructions http://www.java.com/.../5000020300.xml
- Click Start > Control Panel.
- Double-click the Java icon in the control panel and then the Java Control Panel will appear.
- Click Settings under Temporary Internet Files and the Temporary Files Settings dialog box appears.
- Click Delete Files and the Delete Temporary Files dialog box appears.
- Make sure all three boxes are ticked: Downloaded Applets, Downloaded Applications and Other Files and then Click OK on Delete Temporary Files window. Note: This deletes all the Downloaded Applications and Applets from the cache.
- Click OK on Temporary Files Settings window.
Please go to Start > Control Panel > Add/Remove Programs and remove the following (if present):
J2SE Runtime Environment 5.0 Update 4
Upgrading Java:
- Download the latest version of Java Runtime Environment (JRE) 6 Update 6.
- Scroll down to where it says "The J2SE Runtime Environment (JRE) allows end-users to run Java applications".
- Click the "Download" button to the right.
- Select your Platform and check the box that says: "I agree to the Java SE Runtime Environment 6 License Agreement.".
- Click on Continue.
- Click on the link to download Windows Offline Installation (jre-6u6-windows-i586-p.exe) and save it to your desktop. Do NOT use the Sun Download Manager..
- Close any programs you may have running - especially your web browser.
- Go to Start > Control Panel, double-click on Add/Remove programs and remove all older versions of Java.
- Check any item with Java Runtime Environment (JRE or J2SE) in the name.
- Click the Remove or Change/Remove button.
- Repeat as many times as necessary to remove each Java version.
- Reboot your computer once all Java components are removed.
- Then from your desktop double-click on the download to install the newest version.
====STEP 4====
1. Please open Notepad
- Click Start , then Run
- Type notepad .exe in the Run Box.
2. Now copy/paste the entire content of the codebox below into the Notepad window:
Registry::
[-HKEY_CURRENT_USER\software\microsoft\windows\currentversion\explorer\mountpoints2\C]
[-HKEY_LOCAL_MACHINE\~\Browser Helper Objects\{4A2AACF3-ADF6-11D5-98A9-00E018981B9E}]3. Save the above as CFScript.txt
4. Then drag the CFScript.txt into ComboFix.exe as depicted in the animation below. This will start ComboFix again.

5. After reboot, (in case it asks to reboot), please post the following reports/logs into your next reply:
- Combofix.txt
- A new HijackThis log.
In your next reply could i see:
1. the combofix log
2. a new hijackthis log
3. some idea of how your machine is running now
The text from these files may exceed the maximum post length for this forum. Hence, you may need to post the information over 2 or more posts.
andrewuk
#25
![I'm still treading water but fear I may drown [RESOLVED]: post #25](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 05:03 PM
Posted 08 May 2008 - 05:03 PM

ComboFix 08-05-07.2 - Tobyzooka 2008-05-09 0:21:41.2 - NTFSx86
Microsoft Windows XP Professional 5.1.2600.2.1252.1.1033.18.570 [GMT 1:00]
Running from: C:\Documents and Settings\Tobyzooka\Desktop\ComboFix.exe
Command switches used :: C:\Documents and Settings\Tobyzooka\Desktop\CFScript.txt
* Created a new restore point
.
((((((((((((((((((((((((( Files Created from 2008-04-08 to 2008-05-08 )))))))))))))))))))))))))))))))
.
2008-05-14 12:13 . 2008-05-14 18:34 <DIR> d--h----- C:\$AVG8.VAULT$
2008-05-14 12:06 . 2008-05-14 12:06 10,520 --a------ C:\WINDOWS\system32\avgrsstx.dll
2008-05-14 12:05 . 2008-05-14 12:28 <DIR> d-------- C:\WINDOWS\system32\drivers\Avg
2008-05-14 12:05 . 2008-05-14 12:05 96,520 --a------ C:\WINDOWS\system32\drivers\avgldx86.sys
2008-05-14 12:05 . 2008-05-14 12:05 75,272 --a------ C:\WINDOWS\system32\drivers\avgtdix.sys
2008-05-14 12:05 . 2008-05-14 12:05 12,424 --a------ C:\WINDOWS\system32\drivers\avgrkx86.sys
2008-05-14 12:03 . 2008-05-14 12:03 <DIR> d-------- C:\Documents and Settings\Tobyzooka\Application Data\TmpRecentIcons
2008-05-14 10:36 . 2008-05-14 15:10 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\anwbqpep
2008-05-10 12:56 . 2008-05-10 12:56 233,472 --a------ C:\WINDOWS\system32\REX Shared Library.dll
2008-05-10 12:51 . 2008-05-10 12:51 <DIR> d-------- C:\Program Files\Propellerhead
2008-05-10 12:48 . 2008-05-10 12:48 <DIR> d-------- C:\Program Files\DAEMON Tools Lite
2008-05-10 12:45 . 2008-05-10 12:45 <DIR> d-------- C:\Documents and Settings\Tobyzooka\Application Data\DAEMON Tools
2008-05-10 12:45 . 2008-05-10 12:45 717,296 --a------ C:\WINDOWS\system32\drivers\sptd.sys
2008-05-09 00:17 . 2008-05-09 00:17 <DIR> d-------- C:\Program Files\Common Files\Java
2008-05-09 00:17 . 2008-03-25 02:37 69,632 --a------ C:\WINDOWS\system32\javacpl.cpl
2008-05-08 23:29 . 2008-05-08 23:29 0 --a------ C:\WINDOWS\system32\REN7.tmp
2008-05-08 23:29 . 2008-05-08 23:29 0 --a------ C:\WINDOWS\system32\REN6.tmp
2008-05-08 18:57 . 2008-05-08 18:57 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\Kaspersky Lab
2008-05-04 16:31 . 2008-05-04 16:31 <DIR> d-------- C:\Program Files\Common Files\Wise Installation Wizard
2008-05-01 13:01 . 2008-05-01 13:03 49,152 --a------ C:\WINDOWS\system32\apache.dll
2008-04-30 19:08 . 2008-04-30 19:08 <DIR> d-------- C:\Program Files\SystemRequirementsLab
2008-04-09 11:14 . 2008-04-09 11:14 <DIR> d-------- C:\SDPlugins
2008-04-09 11:14 . 2008-04-09 11:14 <DIR> d-------- C:\DirectX
2008-04-09 11:11 . 2008-04-09 11:14 <DIR> d-------- C:\data
2008-04-09 11:11 . 2008-04-09 11:11 <DIR> d-------- C:\AppData
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2008-05-14 15:41 22,328 ----a-w C:\WINDOWS\system32\drivers\PnkBstrK.sys
2008-05-14 15:38 107,832 ----a-w C:\WINDOWS\system32\PnkBstrB.exe
2008-05-14 11:02 --------- d-----w C:\Documents and Settings\All Users\Application Data\avg8
2008-05-08 23:25 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Skype
2008-05-08 23:17 --------- d-----w C:\Program Files\Java
2008-05-05 20:46 27,048 ----a-w C:\WINDOWS\system32\drivers\mbamcatchme.sys
2008-05-05 20:46 15,864 ----a-w C:\WINDOWS\system32\drivers\mbam.sys
2008-05-04 23:41 --------- d-----w C:\Program Files\SlySoft
2008-05-04 15:32 --------- d-----w C:\Program Files\Lavasoft
2008-05-04 15:31 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Lavasoft
2008-05-01 22:38 --------- d--h--w C:\Program Files\InstallShield Installation Information
2008-05-01 22:38 --------- d-----w C:\Program Files\EA Games
2008-04-28 08:03 82,944 ----a-w C:\WINDOWS\system32\IEDFix.exe
2008-04-28 08:03 82,944 ----a-w C:\WINDOWS\system32\404Fix.exe
2008-04-24 08:10 86,528 ----a-w C:\WINDOWS\system32\VACFix.exe
2008-04-15 11:44 --------- d-----w C:\Program Files\Azureus
2008-03-29 18:16 --------- d-----w C:\Program Files\iTunes
2008-03-29 18:16 --------- d-----w C:\Program Files\iPod
2008-03-29 18:15 --------- d-----w C:\Program Files\QuickTime
2008-03-22 01:51 --------- d-----w C:\Program Files\BestGameEver
2008-03-21 19:50 --------- d-----w C:\Program Files\AVG
2008-03-19 19:32 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Sony Corporation
2008-03-19 19:24 --------- d-----w C:\Program Files\Sony
2008-03-19 19:08 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Publish Providers
2008-03-19 19:07 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Sony
2008-03-19 19:06 --------- d-----w C:\Program Files\Sony Setup
2008-03-19 14:46 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Cakewalk
2008-03-19 14:45 --------- d-----w C:\Documents and Settings\All Users\Application Data\Cakewalk
2008-03-19 14:44 --------- d-----w C:\Program Files\Cakewalk
2008-03-19 10:11 --------- d-----w C:\Program Files\MagicISO
2008-03-19 09:47 1,845,248 ----a-w C:\WINDOWS\system32\win32k.sys
2008-02-20 06:51 282,624 ----a-w C:\WINDOWS\system32\gdi32.dll
2008-02-20 05:32 45,568 ----a-w C:\WINDOWS\system32\dnsrslvr.dll
2005-10-09 19:21 18,704 ----a-w C:\Documents and Settings\Tobyzooka\Application Data\GDIPFONTCACHEV1.DAT
.
((((((((((((((((((((((((((((( snapshot@2008-05-08_18.13.45.39 )))))))))))))))))))))))))))))))))))))))))
.
- 2008-05-08 17:06:05 2,048 --s-a-w C:\WINDOWS\bootstat.dat
+ 2008-05-08 22:20:35 2,048 --s-a-w C:\WINDOWS\bootstat.dat
- 2005-06-03 01:24:06 49,248 ----a-w C:\WINDOWS\system32\java.exe
+ 2008-03-25 00:28:39 135,168 ----a-w C:\WINDOWS\system32\java.exe
- 2005-06-03 01:24:14 49,250 ----a-w C:\WINDOWS\system32\javaw.exe
+ 2008-03-25 00:28:43 135,168 ----a-w C:\WINDOWS\system32\javaw.exe
- 2005-06-03 02:52:56 127,078 ----a-w C:\WINDOWS\system32\javaws.exe
+ 2008-03-25 01:37:01 139,264 ----a-w C:\WINDOWS\system32\javaws.exe
- 2005-05-24 12:27:16 213,048 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavss.dll
+ 2005-05-24 11:27:16 213,048 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavss.dll
- 2007-08-29 15:47:20 94,208 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavuninstall.exe
+ 2007-08-29 14:47:20 94,208 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavuninstall.exe
- 2007-08-29 15:49:54 950,272 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavwebscan.dll
+ 2007-08-29 14:49:54 950,272 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavwebscan.dll
- 2002-01-22 12:26:55 63,760 ----a-w C:\WINDOWS\system32\perfc009.dat
+ 2008-05-08 17:10:19 63,760 ----a-w C:\WINDOWS\system32\perfc009.dat
- 2002-01-22 12:26:55 406,944 ----a-w C:\WINDOWS\system32\perfh009.dat
+ 2008-05-08 17:10:20 406,944 ----a-w C:\WINDOWS\system32\perfh009.dat
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"CTFMON.EXE"="C:\WINDOWS\system32\ctfmon.exe" [2004-08-04 08:56 15360]
"SetDefaultMIDI"="MIDIDef.exe" []
"Skype"="C:\Program Files\Skype\Phone\Skype.exe" [2005-10-10 14:01 14881320]
"swg"="C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe" [2007-09-16 12:50 68856]
"Steam"="c:\progra~1\valve\steam\steam.exe" [2008-04-27 17:07 1271032]
"MsnMsgr"="C:\Program Files\MSN Messenger\MsnMsgr.exe" [2007-01-19 12:54 5674352]
"DAEMON Tools Lite"="C:\Program Files\DAEMON Tools Lite\daemon.exe" [2008-04-01 10:39 486856]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ATIPTA"="C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe" [2005-05-12 21:05 344064]
"zBrowser Launcher"="C:\Program Files\Logitech\iTouch\iTouch.exe" [2003-04-07 03:16 631364]
"Logitech Utility"="Logi_MwX.Exe" [2002-11-08 11:50 19968 C:\WINDOWS\LOGI_MWX.EXE]
"DAEMON Tools-1033"="C:\Program Files\D-Tools\daemon.exe" [2004-08-22 18:05 81920]
"UserFaultCheck"="C:\WINDOWS\system32\dumprep 0 -u" [ ]
"NeroFilterCheck"="C:\WINDOWS\system32\NeroCheck.exe" [2001-07-09 11:50 155648]
"DU Meter"="C:\Program Files\DU Meter\DUMeter.exe" [2005-02-01 19:28 1469952]
"StartCCC"="C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\CLIStart.exe" [2006-11-10 12:35 90112]
"ATICCC"="C:\Program Files\ATI Technologies\ATI.ACE\cli.exe" [2006-01-02 17:41 45056]
"AVG8_TRAY"="C:\PROGRA~1\AVG\AVG8\avgtray.exe" [2008-05-14 12:30 1177368]
"QuickTime Task"="C:\Program Files\QuickTime\qttask.exe" [2008-02-01 00:13 385024]
"iTunesHelper"="C:\Program Files\iTunes\iTunesHelper.exe" [2008-02-19 14:10 267048]
"4oD"="C:\Program Files\Kontiki\KHost.exe" [ ]
"SunJavaUpdateSched"="C:\Program Files\Java\jre1.6.0_06\bin\jusched.exe" [2008-03-25 04:28 144784]
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run]
"CTFMON.EXE"="C:\WINDOWS\System32\CTFMON.EXE" [2004-08-04 08:56 15360]
"Norton SystemWorks"="C:\Program Files\Norton SystemWorks\cfgwiz.exe" [ ]
C:\Documents and Settings\Tobyzooka\Start Menu\Programs\Startup\
Picture Motion Browser Media Check Tool.lnk - C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe [2008-03-19 20:24:18 344064]
C:\Documents and Settings\All Users\Start Menu\Programs\Startup\
Adobe Reader Speed Launch.lnk - C:\Program Files\Adobe\Acrobat 7.0\Reader\reader_sl.exe [2005-09-23 22:05:26 29696]
Microsoft Office.lnk - C:\Program Files\Microsoft Office\Office10\OSA.EXE [2001-02-13 02:01:04 83360]
WinZip Quick Pick.lnk - C:\Program Files\WinZip\WZQKPICK.EXE [2005-09-25 20:31:11 118784]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\windows]
"AppInit_DLLs"=avgrsstx.dll
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\drivers32]
"vidc.ffds"= ffdshow.ax
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusDisableNotify"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"C:\\Program Files\\Valve\\Steam\\SteamApps\\tobazooka\\counter-strike source\\hl2.exe"=
"C:\\Program Files\\Valve\\Steam\\Steam.exe"=
"C:\\Program Files\\Real\\RealPlayer\\realplay.exe"=
"C:\\Program Files\\Messenger\\msmsgs.exe"=
"C:\\WINDOWS\\system32\\dpvsetup.exe"=
"C:\\WINDOWS\\system32\\rundll32.exe"=
"C:\\WINDOWS\\system32\\dplaysvr.exe"=
"C:\\Program Files\\Valve\\Steam\\SteamApps\\tobazooka\\source sdk base\\hl2.exe"=
"C:\\Program Files\\MSN Messenger\\msnmsgr.exe"=
"C:\\Program Files\\MSN Messenger\\livecall.exe"=
"C:\\WINDOWS\\system32\\dpnsvr.exe"=
"C:\\Program Files\\iTunes\\iTunes.exe"=
"C:\\Program Files\\Azureus\\Azureus.exe"=
"C:\\Program Files\\EA Games\\Battlefield 2\\BF2.exe"=
"C:\\Program Files\\AVG\\AVG8\\avgupd.exe"=
"C:\\Program Files\\AVG\\AVG8\\avgnsx.exe"=
"C:\\Program Files\\Skype\\Phone\\Skype.exe"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"3389:TCP"= 3389:TCP:@xpsp2res.dll,-22009
R0 AvgRkx86;avgrkx86.sys;C:\WINDOWS\system32\Drivers\avgrkx86.sys [2008-05-14 12:05]
R0 xmasbus;xmasbus;C:\WINDOWS\system32\DRIVERS\xmasbus.sys [2003-12-21 18:24]
R0 xmasscsi;xmasscsi;C:\WINDOWS\system32\Drivers\xmasscsi.sys [2003-12-23 03:15]
R1 AvgLdx86;AVG AVI Loader Driver x86;C:\WINDOWS\system32\Drivers\avgldx86.sys [2008-05-14 12:05]
R2 avg8wd;AVG8 WatchDog;C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe [2008-05-14 12:05]
R2 AvgTdiX;AVG8 Network Redirector;C:\WINDOWS\system32\Drivers\avgtdix.sys [2008-05-14 12:05]
S2 asurscsi;asurscsi;C:\Program Files\Voyetra\AudioSurgeon 5\asurscsi.exe []
S3 ldiskl;ldiskl;C:\DOCUME~1\TOBYZO~1\LOCALS~1\Temp\ldiskl.sys []
S3 SetupNTGLM7X;SetupNTGLM7X;D:\NTGLM7X.sys []
.
Contents of the 'Scheduled Tasks' folder
"2008-05-06 14:13:02 C:\WINDOWS\Tasks\AppleSoftwareUpdate.job"
- C:\Program Files\Apple Software Update\SoftwareUpdate.exe
"2008-05-14 14:35:14 C:\WINDOWS\Tasks\Symantec NetDetect.job"
- C:\Program Files\Symantec\LiveUpdate\NDETECT.EXE
.
**************************************************************************
catchme 0.3.1353 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2008-05-09 00:25:03
Windows 5.1.2600 Service Pack 2 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
Completion time: 2008-05-09 0:26:09
ComboFix-quarantined-files.txt 2008-05-08 23:25:56
ComboFix2.txt 2008-05-08 17:14:15
Pre-Run: 24,431,722,496 bytes free
Post-Run: 24,443,355,136 bytes free
188 --- E O F --- 2008-05-12 06:56:26
Logfile of Trend Micro HijackThis v2.0.2
Scan saved at 00:27:51, on 09/05/2008
Platform: Windows XP SP2 (WinNT 5.01.2600)
MSIE: Internet Explorer v6.00 SP2 (6.00.2900.2180)
Boot mode: Normal
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
C:\WINDOWS\system32\spoolsv.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\Program Files\Logitech\MouseWare\system\em_exec.exe
C:\Program Files\DU Meter\DUMeter.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\PROGRA~1\AVG\AVG8\avgtray.exe
C:\Program Files\iTunes\iTunesHelper.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
C:\Program Files\Skype\Phone\Skype.exe
C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
C:\Program Files\MSN Messenger\MsnMsgr.Exe
C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe
C:\Program Files\WinZip\WZQKPICK.EXE
C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe
C:\WINDOWS\system32\PnkBstrA.exe
C:\WINDOWS\system32\PnkBstrB.exe
C:\PROGRA~1\AVG\AVG8\avgam.exe
C:\WINDOWS\system32\MsPMSPSv.exe
C:\PROGRA~1\AVG\AVG8\avgrsx.exe
C:\PROGRA~1\AVG\AVG8\avgnsx.exe
C:\Program Files\iPod\bin\iPodService.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\WINDOWS\system32\wuauclt.exe
C:\WINDOWS\system32\msiexec.exe
C:\WINDOWS\system32\wuauclt.exe
C:\WINDOWS\explorer.exe
C:\Program Files\Trend Micro\HijackThis\HijackThis.exe
C:\Program Files\Internet Explorer\IEXPLORE.EXE
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL = http://go.microsoft....k/?LinkId=69157
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Search_URL = http://go.microsoft....k/?LinkId=54896
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Page = http://go.microsoft....k/?LinkId=54896
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,AutoConfigURL = 192.168.0.65
O2 - BHO: Adobe PDF Reader Link Helper - {06849E9F-C8D7-4D59-B87D-784B7D6BE0B3} - C:\Program Files\Adobe\Acrobat 7.0\ActiveX\AcroIEHelper.dll
O2 - BHO: WormRadar.com IESiteBlocker.NavFilter - {3CA2F312-6F6E-4B53-A66E-4E65E497C8C0} - C:\Program Files\AVG\AVG8\avgssie.dll
O2 - BHO: SSVHelper Class - {761497BB-D6F0-462C-B6EB-D4DAF1D92D43} - C:\Program Files\Java\jre1.6.0_06\bin\ssv.dll
O2 - BHO: Google Toolbar Helper - {AA58ED58-01DD-4d91-8333-CF10577473F7} - c:\program files\google\googletoolbar1.dll
O2 - BHO: Google Toolbar Notifier BHO - {AF69DE43-7D58-4638-B6FA-CE66B5AD205D} - C:\Program Files\Google\GoogleToolbarNotifier\2.0.1121.2472\swg.dll
O3 - Toolbar: &Google - {2318C2B1-4965-11d4-9B18-009027A5CD4F} - c:\program files\google\googletoolbar1.dll
O4 - HKLM\..\Run: [ATIPTA] C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe
O4 - HKLM\..\Run: [zBrowser Launcher] C:\Program Files\Logitech\iTouch\iTouch.exe
O4 - HKLM\..\Run: [Logitech Utility] Logi_MwX.Exe
O4 - HKLM\..\Run: [DAEMON Tools-1033] "C:\Program Files\D-Tools\daemon.exe" -lang 1033
O4 - HKLM\..\Run: [UserFaultCheck] %systemroot%\system32\dumprep 0 -u
O4 - HKLM\..\Run: [NeroFilterCheck] C:\WINDOWS\system32\NeroCheck.exe
O4 - HKLM\..\Run: [DU Meter] C:\Program Files\DU Meter\DUMeter.exe
O4 - HKLM\..\Run: [StartCCC] "C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\CLIStart.exe"
O4 - HKLM\..\Run: [ATICCC] "C:\Program Files\ATI Technologies\ATI.ACE\cli.exe" runtime -Delay
O4 - HKLM\..\Run: [AVG8_TRAY] C:\PROGRA~1\AVG\AVG8\avgtray.exe
O4 - HKLM\..\Run: [QuickTime Task] "C:\Program Files\QuickTime\qttask.exe" -atboottime
O4 - HKLM\..\Run: [iTunesHelper] "C:\Program Files\iTunes\iTunesHelper.exe"
O4 - HKLM\..\Run: [4oD] "C:\Program Files\Kontiki\KHost.exe" -all
O4 - HKLM\..\Run: [SunJavaUpdateSched] "C:\Program Files\Java\jre1.6.0_06\bin\jusched.exe"
O4 - HKCU\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\ctfmon.exe
O4 - HKCU\..\Run: [SetDefaultMIDI] MIDIDef.exe
O4 - HKCU\..\Run: [Skype] "C:\Program Files\Skype\Phone\Skype.exe" /nosplash /minimized
O4 - HKCU\..\Run: [swg] C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
O4 - HKCU\..\Run: [Steam] "c:\progra~1\valve\steam\steam.exe" -silent
O4 - HKCU\..\Run: [MsnMsgr] "C:\Program Files\MSN Messenger\MsnMsgr.Exe" /background
O4 - HKCU\..\Run: [DAEMON Tools Lite] "C:\Program Files\DAEMON Tools Lite\daemon.exe" -autorun
O4 - HKUS\S-1-5-19\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'LOCAL SERVICE')
O4 - HKUS\S-1-5-20\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'NETWORK SERVICE')
O4 - HKUS\S-1-5-18\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'SYSTEM')
O4 - HKUS\.DEFAULT\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'Default user')
O4 - Startup: Picture Motion Browser Media Check Tool.lnk = C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe
O4 - Global Startup: Adobe Reader Speed Launch.lnk = C:\Program Files\Adobe\Acrobat 7.0\Reader\reader_sl.exe
O4 - Global Startup: Microsoft Office.lnk = C:\Program Files\Microsoft Office\Office10\OSA.EXE
O4 - Global Startup: WinZip Quick Pick.lnk = C:\Program Files\WinZip\WZQKPICK.EXE
O8 - Extra context menu item: E&xport to Microsoft Excel - res://C:\PROGRA~1\MICROS~2\Office10\EXCEL.EXE/3000
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_06\bin\ssv.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_06\bin\ssv.dll
O9 - Extra button: Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O9 - Extra 'Tools' menuitem: Windows Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O12 - Plugin for .spop: C:\Program Files\Internet Explorer\Plugins\NPDocBox.dll
O16 - DPF: {05CDEE1D-D109-4992-B72B-6D4F5E2AB731} (PhotoBox uploader) - http://static.photob...geUploader4.cab
O16 - DPF: {0EB0E74A-2A76-4AB3-A7FB-9BD8C29F7F75} (CKAVWebScan Object) - http://www.kaspersky...can_unicode.cab
O16 - DPF: {4F1E5B1A-2A80-42CA-8532-2D05CB959537} (MSN Photo Upload Tool) - http://gfx1.hotmail....es/MSNPUpld.cab
O16 - DPF: {5C6698D9-7BE4-4122-8EC5-291D84DBD4A0} (Facebook Photo Uploader 4 Control) - http://upload.facebo...toUploader3.cab
O16 - DPF: {6414512B-B978-451D-A0D8-FCFDF33E833C} (WUWebControl Class) - http://v5.windowsupd...b?1099406122515
O16 - DPF: {67A5F8DC-1A4B-4D66-9F24-A704AD929EEE} (System Requirements Lab) - http://www.systemreq.../sysreqlab2.cab
O18 - Protocol: linkscanner - {F274614C-63F8-47D5-A4D1-FBDDE494F8D1} - C:\Program Files\AVG\AVG8\avgpp.dll
O20 - AppInit_DLLs: avgrsstx.dll
O23 - Service: Ad-Aware 2007 Service (aawservice) - Lavasoft - C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
O23 - Service: Apple Mobile Device - Apple, Inc. - C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
O23 - Service: asurscsi - Unknown owner - C:\Program Files\Voyetra\AudioSurgeon 5\asurscsi.exe (file missing)
O23 - Service: Ati HotKey Poller - ATI Technologies Inc. - C:\WINDOWS\system32\Ati2evxx.exe
O23 - Service: ATI Smart - Unknown owner - C:\WINDOWS\system32\ati2sgag.exe
O23 - Service: AVG8 WatchDog (avg8wd) - AVG Technologies CZ, s.r.o. - C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe
O23 - Service: Google Updater Service (gusvc) - Google - C:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
O23 - Service: InstallDriver Table Manager (IDriverT) - Macrovision Corporation - C:\Program Files\Common Files\InstallShield\Driver\11\Intel 32\IDriverT.exe
O23 - Service: iPod Service - Apple Inc. - C:\Program Files\iPod\bin\iPodService.exe
O23 - Service: PnkBstrA - Unknown owner - C:\WINDOWS\system32\PnkBstrA.exe
O23 - Service: PnkBstrB - Unknown owner - C:\WINDOWS\system32\PnkBstrB.exe
--
End of file - 8379 bytes
3. I'll have to have a bit of a ply around but it does seem better than before. Although the java install only seemed to be downloading at 9kb.
Microsoft Windows XP Professional 5.1.2600.2.1252.1.1033.18.570 [GMT 1:00]
Running from: C:\Documents and Settings\Tobyzooka\Desktop\ComboFix.exe
Command switches used :: C:\Documents and Settings\Tobyzooka\Desktop\CFScript.txt
* Created a new restore point
.
((((((((((((((((((((((((( Files Created from 2008-04-08 to 2008-05-08 )))))))))))))))))))))))))))))))
.
2008-05-14 12:13 . 2008-05-14 18:34 <DIR> d--h----- C:\$AVG8.VAULT$
2008-05-14 12:06 . 2008-05-14 12:06 10,520 --a------ C:\WINDOWS\system32\avgrsstx.dll
2008-05-14 12:05 . 2008-05-14 12:28 <DIR> d-------- C:\WINDOWS\system32\drivers\Avg
2008-05-14 12:05 . 2008-05-14 12:05 96,520 --a------ C:\WINDOWS\system32\drivers\avgldx86.sys
2008-05-14 12:05 . 2008-05-14 12:05 75,272 --a------ C:\WINDOWS\system32\drivers\avgtdix.sys
2008-05-14 12:05 . 2008-05-14 12:05 12,424 --a------ C:\WINDOWS\system32\drivers\avgrkx86.sys
2008-05-14 12:03 . 2008-05-14 12:03 <DIR> d-------- C:\Documents and Settings\Tobyzooka\Application Data\TmpRecentIcons
2008-05-14 10:36 . 2008-05-14 15:10 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\anwbqpep
2008-05-10 12:56 . 2008-05-10 12:56 233,472 --a------ C:\WINDOWS\system32\REX Shared Library.dll
2008-05-10 12:51 . 2008-05-10 12:51 <DIR> d-------- C:\Program Files\Propellerhead
2008-05-10 12:48 . 2008-05-10 12:48 <DIR> d-------- C:\Program Files\DAEMON Tools Lite
2008-05-10 12:45 . 2008-05-10 12:45 <DIR> d-------- C:\Documents and Settings\Tobyzooka\Application Data\DAEMON Tools
2008-05-10 12:45 . 2008-05-10 12:45 717,296 --a------ C:\WINDOWS\system32\drivers\sptd.sys
2008-05-09 00:17 . 2008-05-09 00:17 <DIR> d-------- C:\Program Files\Common Files\Java
2008-05-09 00:17 . 2008-03-25 02:37 69,632 --a------ C:\WINDOWS\system32\javacpl.cpl
2008-05-08 23:29 . 2008-05-08 23:29 0 --a------ C:\WINDOWS\system32\REN7.tmp
2008-05-08 23:29 . 2008-05-08 23:29 0 --a------ C:\WINDOWS\system32\REN6.tmp
2008-05-08 18:57 . 2008-05-08 18:57 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\Kaspersky Lab
2008-05-04 16:31 . 2008-05-04 16:31 <DIR> d-------- C:\Program Files\Common Files\Wise Installation Wizard
2008-05-01 13:01 . 2008-05-01 13:03 49,152 --a------ C:\WINDOWS\system32\apache.dll
2008-04-30 19:08 . 2008-04-30 19:08 <DIR> d-------- C:\Program Files\SystemRequirementsLab
2008-04-09 11:14 . 2008-04-09 11:14 <DIR> d-------- C:\SDPlugins
2008-04-09 11:14 . 2008-04-09 11:14 <DIR> d-------- C:\DirectX
2008-04-09 11:11 . 2008-04-09 11:14 <DIR> d-------- C:\data
2008-04-09 11:11 . 2008-04-09 11:11 <DIR> d-------- C:\AppData
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2008-05-14 15:41 22,328 ----a-w C:\WINDOWS\system32\drivers\PnkBstrK.sys
2008-05-14 15:38 107,832 ----a-w C:\WINDOWS\system32\PnkBstrB.exe
2008-05-14 11:02 --------- d-----w C:\Documents and Settings\All Users\Application Data\avg8
2008-05-08 23:25 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Skype
2008-05-08 23:17 --------- d-----w C:\Program Files\Java
2008-05-05 20:46 27,048 ----a-w C:\WINDOWS\system32\drivers\mbamcatchme.sys
2008-05-05 20:46 15,864 ----a-w C:\WINDOWS\system32\drivers\mbam.sys
2008-05-04 23:41 --------- d-----w C:\Program Files\SlySoft
2008-05-04 15:32 --------- d-----w C:\Program Files\Lavasoft
2008-05-04 15:31 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Lavasoft
2008-05-01 22:38 --------- d--h--w C:\Program Files\InstallShield Installation Information
2008-05-01 22:38 --------- d-----w C:\Program Files\EA Games
2008-04-28 08:03 82,944 ----a-w C:\WINDOWS\system32\IEDFix.exe
2008-04-28 08:03 82,944 ----a-w C:\WINDOWS\system32\404Fix.exe
2008-04-24 08:10 86,528 ----a-w C:\WINDOWS\system32\VACFix.exe
2008-04-15 11:44 --------- d-----w C:\Program Files\Azureus
2008-03-29 18:16 --------- d-----w C:\Program Files\iTunes
2008-03-29 18:16 --------- d-----w C:\Program Files\iPod
2008-03-29 18:15 --------- d-----w C:\Program Files\QuickTime
2008-03-22 01:51 --------- d-----w C:\Program Files\BestGameEver
2008-03-21 19:50 --------- d-----w C:\Program Files\AVG
2008-03-19 19:32 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Sony Corporation
2008-03-19 19:24 --------- d-----w C:\Program Files\Sony
2008-03-19 19:08 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Publish Providers
2008-03-19 19:07 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Sony
2008-03-19 19:06 --------- d-----w C:\Program Files\Sony Setup
2008-03-19 14:46 --------- d-----w C:\Documents and Settings\Tobyzooka\Application Data\Cakewalk
2008-03-19 14:45 --------- d-----w C:\Documents and Settings\All Users\Application Data\Cakewalk
2008-03-19 14:44 --------- d-----w C:\Program Files\Cakewalk
2008-03-19 10:11 --------- d-----w C:\Program Files\MagicISO
2008-03-19 09:47 1,845,248 ----a-w C:\WINDOWS\system32\win32k.sys
2008-02-20 06:51 282,624 ----a-w C:\WINDOWS\system32\gdi32.dll
2008-02-20 05:32 45,568 ----a-w C:\WINDOWS\system32\dnsrslvr.dll
2005-10-09 19:21 18,704 ----a-w C:\Documents and Settings\Tobyzooka\Application Data\GDIPFONTCACHEV1.DAT
.
((((((((((((((((((((((((((((( snapshot@2008-05-08_18.13.45.39 )))))))))))))))))))))))))))))))))))))))))
.
- 2008-05-08 17:06:05 2,048 --s-a-w C:\WINDOWS\bootstat.dat
+ 2008-05-08 22:20:35 2,048 --s-a-w C:\WINDOWS\bootstat.dat
- 2005-06-03 01:24:06 49,248 ----a-w C:\WINDOWS\system32\java.exe
+ 2008-03-25 00:28:39 135,168 ----a-w C:\WINDOWS\system32\java.exe
- 2005-06-03 01:24:14 49,250 ----a-w C:\WINDOWS\system32\javaw.exe
+ 2008-03-25 00:28:43 135,168 ----a-w C:\WINDOWS\system32\javaw.exe
- 2005-06-03 02:52:56 127,078 ----a-w C:\WINDOWS\system32\javaws.exe
+ 2008-03-25 01:37:01 139,264 ----a-w C:\WINDOWS\system32\javaws.exe
- 2005-05-24 12:27:16 213,048 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavss.dll
+ 2005-05-24 11:27:16 213,048 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavss.dll
- 2007-08-29 15:47:20 94,208 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavuninstall.exe
+ 2007-08-29 14:47:20 94,208 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavuninstall.exe
- 2007-08-29 15:49:54 950,272 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavwebscan.dll
+ 2007-08-29 14:49:54 950,272 ----a-w C:\WINDOWS\system32\Kaspersky Lab\Kaspersky Online Scanner\kavwebscan.dll
- 2002-01-22 12:26:55 63,760 ----a-w C:\WINDOWS\system32\perfc009.dat
+ 2008-05-08 17:10:19 63,760 ----a-w C:\WINDOWS\system32\perfc009.dat
- 2002-01-22 12:26:55 406,944 ----a-w C:\WINDOWS\system32\perfh009.dat
+ 2008-05-08 17:10:20 406,944 ----a-w C:\WINDOWS\system32\perfh009.dat
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"CTFMON.EXE"="C:\WINDOWS\system32\ctfmon.exe" [2004-08-04 08:56 15360]
"SetDefaultMIDI"="MIDIDef.exe" []
"Skype"="C:\Program Files\Skype\Phone\Skype.exe" [2005-10-10 14:01 14881320]
"swg"="C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe" [2007-09-16 12:50 68856]
"Steam"="c:\progra~1\valve\steam\steam.exe" [2008-04-27 17:07 1271032]
"MsnMsgr"="C:\Program Files\MSN Messenger\MsnMsgr.exe" [2007-01-19 12:54 5674352]
"DAEMON Tools Lite"="C:\Program Files\DAEMON Tools Lite\daemon.exe" [2008-04-01 10:39 486856]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ATIPTA"="C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe" [2005-05-12 21:05 344064]
"zBrowser Launcher"="C:\Program Files\Logitech\iTouch\iTouch.exe" [2003-04-07 03:16 631364]
"Logitech Utility"="Logi_MwX.Exe" [2002-11-08 11:50 19968 C:\WINDOWS\LOGI_MWX.EXE]
"DAEMON Tools-1033"="C:\Program Files\D-Tools\daemon.exe" [2004-08-22 18:05 81920]
"UserFaultCheck"="C:\WINDOWS\system32\dumprep 0 -u" [ ]
"NeroFilterCheck"="C:\WINDOWS\system32\NeroCheck.exe" [2001-07-09 11:50 155648]
"DU Meter"="C:\Program Files\DU Meter\DUMeter.exe" [2005-02-01 19:28 1469952]
"StartCCC"="C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\CLIStart.exe" [2006-11-10 12:35 90112]
"ATICCC"="C:\Program Files\ATI Technologies\ATI.ACE\cli.exe" [2006-01-02 17:41 45056]
"AVG8_TRAY"="C:\PROGRA~1\AVG\AVG8\avgtray.exe" [2008-05-14 12:30 1177368]
"QuickTime Task"="C:\Program Files\QuickTime\qttask.exe" [2008-02-01 00:13 385024]
"iTunesHelper"="C:\Program Files\iTunes\iTunesHelper.exe" [2008-02-19 14:10 267048]
"4oD"="C:\Program Files\Kontiki\KHost.exe" [ ]
"SunJavaUpdateSched"="C:\Program Files\Java\jre1.6.0_06\bin\jusched.exe" [2008-03-25 04:28 144784]
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run]
"CTFMON.EXE"="C:\WINDOWS\System32\CTFMON.EXE" [2004-08-04 08:56 15360]
"Norton SystemWorks"="C:\Program Files\Norton SystemWorks\cfgwiz.exe" [ ]
C:\Documents and Settings\Tobyzooka\Start Menu\Programs\Startup\
Picture Motion Browser Media Check Tool.lnk - C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe [2008-03-19 20:24:18 344064]
C:\Documents and Settings\All Users\Start Menu\Programs\Startup\
Adobe Reader Speed Launch.lnk - C:\Program Files\Adobe\Acrobat 7.0\Reader\reader_sl.exe [2005-09-23 22:05:26 29696]
Microsoft Office.lnk - C:\Program Files\Microsoft Office\Office10\OSA.EXE [2001-02-13 02:01:04 83360]
WinZip Quick Pick.lnk - C:\Program Files\WinZip\WZQKPICK.EXE [2005-09-25 20:31:11 118784]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\windows]
"AppInit_DLLs"=avgrsstx.dll
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\drivers32]
"vidc.ffds"= ffdshow.ax
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusDisableNotify"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"C:\\Program Files\\Valve\\Steam\\SteamApps\\tobazooka\\counter-strike source\\hl2.exe"=
"C:\\Program Files\\Valve\\Steam\\Steam.exe"=
"C:\\Program Files\\Real\\RealPlayer\\realplay.exe"=
"C:\\Program Files\\Messenger\\msmsgs.exe"=
"C:\\WINDOWS\\system32\\dpvsetup.exe"=
"C:\\WINDOWS\\system32\\rundll32.exe"=
"C:\\WINDOWS\\system32\\dplaysvr.exe"=
"C:\\Program Files\\Valve\\Steam\\SteamApps\\tobazooka\\source sdk base\\hl2.exe"=
"C:\\Program Files\\MSN Messenger\\msnmsgr.exe"=
"C:\\Program Files\\MSN Messenger\\livecall.exe"=
"C:\\WINDOWS\\system32\\dpnsvr.exe"=
"C:\\Program Files\\iTunes\\iTunes.exe"=
"C:\\Program Files\\Azureus\\Azureus.exe"=
"C:\\Program Files\\EA Games\\Battlefield 2\\BF2.exe"=
"C:\\Program Files\\AVG\\AVG8\\avgupd.exe"=
"C:\\Program Files\\AVG\\AVG8\\avgnsx.exe"=
"C:\\Program Files\\Skype\\Phone\\Skype.exe"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"3389:TCP"= 3389:TCP:@xpsp2res.dll,-22009
R0 AvgRkx86;avgrkx86.sys;C:\WINDOWS\system32\Drivers\avgrkx86.sys [2008-05-14 12:05]
R0 xmasbus;xmasbus;C:\WINDOWS\system32\DRIVERS\xmasbus.sys [2003-12-21 18:24]
R0 xmasscsi;xmasscsi;C:\WINDOWS\system32\Drivers\xmasscsi.sys [2003-12-23 03:15]
R1 AvgLdx86;AVG AVI Loader Driver x86;C:\WINDOWS\system32\Drivers\avgldx86.sys [2008-05-14 12:05]
R2 avg8wd;AVG8 WatchDog;C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe [2008-05-14 12:05]
R2 AvgTdiX;AVG8 Network Redirector;C:\WINDOWS\system32\Drivers\avgtdix.sys [2008-05-14 12:05]
S2 asurscsi;asurscsi;C:\Program Files\Voyetra\AudioSurgeon 5\asurscsi.exe []
S3 ldiskl;ldiskl;C:\DOCUME~1\TOBYZO~1\LOCALS~1\Temp\ldiskl.sys []
S3 SetupNTGLM7X;SetupNTGLM7X;D:\NTGLM7X.sys []
.
Contents of the 'Scheduled Tasks' folder
"2008-05-06 14:13:02 C:\WINDOWS\Tasks\AppleSoftwareUpdate.job"
- C:\Program Files\Apple Software Update\SoftwareUpdate.exe
"2008-05-14 14:35:14 C:\WINDOWS\Tasks\Symantec NetDetect.job"
- C:\Program Files\Symantec\LiveUpdate\NDETECT.EXE
.
**************************************************************************
catchme 0.3.1353 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2008-05-09 00:25:03
Windows 5.1.2600 Service Pack 2 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
Completion time: 2008-05-09 0:26:09
ComboFix-quarantined-files.txt 2008-05-08 23:25:56
ComboFix2.txt 2008-05-08 17:14:15
Pre-Run: 24,431,722,496 bytes free
Post-Run: 24,443,355,136 bytes free
188 --- E O F --- 2008-05-12 06:56:26
Logfile of Trend Micro HijackThis v2.0.2
Scan saved at 00:27:51, on 09/05/2008
Platform: Windows XP SP2 (WinNT 5.01.2600)
MSIE: Internet Explorer v6.00 SP2 (6.00.2900.2180)
Boot mode: Normal
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
C:\WINDOWS\system32\spoolsv.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\Program Files\Logitech\MouseWare\system\em_exec.exe
C:\Program Files\DU Meter\DUMeter.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\PROGRA~1\AVG\AVG8\avgtray.exe
C:\Program Files\iTunes\iTunesHelper.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
C:\Program Files\Skype\Phone\Skype.exe
C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
C:\Program Files\MSN Messenger\MsnMsgr.Exe
C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe
C:\Program Files\WinZip\WZQKPICK.EXE
C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe
C:\WINDOWS\system32\PnkBstrA.exe
C:\WINDOWS\system32\PnkBstrB.exe
C:\PROGRA~1\AVG\AVG8\avgam.exe
C:\WINDOWS\system32\MsPMSPSv.exe
C:\PROGRA~1\AVG\AVG8\avgrsx.exe
C:\PROGRA~1\AVG\AVG8\avgnsx.exe
C:\Program Files\iPod\bin\iPodService.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\Program Files\ATI Technologies\ATI.ACE\cli.exe
C:\WINDOWS\system32\wuauclt.exe
C:\WINDOWS\system32\msiexec.exe
C:\WINDOWS\system32\wuauclt.exe
C:\WINDOWS\explorer.exe
C:\Program Files\Trend Micro\HijackThis\HijackThis.exe
C:\Program Files\Internet Explorer\IEXPLORE.EXE
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL = http://go.microsoft....k/?LinkId=69157
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Search_URL = http://go.microsoft....k/?LinkId=54896
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Page = http://go.microsoft....k/?LinkId=54896
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,AutoConfigURL = 192.168.0.65
O2 - BHO: Adobe PDF Reader Link Helper - {06849E9F-C8D7-4D59-B87D-784B7D6BE0B3} - C:\Program Files\Adobe\Acrobat 7.0\ActiveX\AcroIEHelper.dll
O2 - BHO: WormRadar.com IESiteBlocker.NavFilter - {3CA2F312-6F6E-4B53-A66E-4E65E497C8C0} - C:\Program Files\AVG\AVG8\avgssie.dll
O2 - BHO: SSVHelper Class - {761497BB-D6F0-462C-B6EB-D4DAF1D92D43} - C:\Program Files\Java\jre1.6.0_06\bin\ssv.dll
O2 - BHO: Google Toolbar Helper - {AA58ED58-01DD-4d91-8333-CF10577473F7} - c:\program files\google\googletoolbar1.dll
O2 - BHO: Google Toolbar Notifier BHO - {AF69DE43-7D58-4638-B6FA-CE66B5AD205D} - C:\Program Files\Google\GoogleToolbarNotifier\2.0.1121.2472\swg.dll
O3 - Toolbar: &Google - {2318C2B1-4965-11d4-9B18-009027A5CD4F} - c:\program files\google\googletoolbar1.dll
O4 - HKLM\..\Run: [ATIPTA] C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe
O4 - HKLM\..\Run: [zBrowser Launcher] C:\Program Files\Logitech\iTouch\iTouch.exe
O4 - HKLM\..\Run: [Logitech Utility] Logi_MwX.Exe
O4 - HKLM\..\Run: [DAEMON Tools-1033] "C:\Program Files\D-Tools\daemon.exe" -lang 1033
O4 - HKLM\..\Run: [UserFaultCheck] %systemroot%\system32\dumprep 0 -u
O4 - HKLM\..\Run: [NeroFilterCheck] C:\WINDOWS\system32\NeroCheck.exe
O4 - HKLM\..\Run: [DU Meter] C:\Program Files\DU Meter\DUMeter.exe
O4 - HKLM\..\Run: [StartCCC] "C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\CLIStart.exe"
O4 - HKLM\..\Run: [ATICCC] "C:\Program Files\ATI Technologies\ATI.ACE\cli.exe" runtime -Delay
O4 - HKLM\..\Run: [AVG8_TRAY] C:\PROGRA~1\AVG\AVG8\avgtray.exe
O4 - HKLM\..\Run: [QuickTime Task] "C:\Program Files\QuickTime\qttask.exe" -atboottime
O4 - HKLM\..\Run: [iTunesHelper] "C:\Program Files\iTunes\iTunesHelper.exe"
O4 - HKLM\..\Run: [4oD] "C:\Program Files\Kontiki\KHost.exe" -all
O4 - HKLM\..\Run: [SunJavaUpdateSched] "C:\Program Files\Java\jre1.6.0_06\bin\jusched.exe"
O4 - HKCU\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\ctfmon.exe
O4 - HKCU\..\Run: [SetDefaultMIDI] MIDIDef.exe
O4 - HKCU\..\Run: [Skype] "C:\Program Files\Skype\Phone\Skype.exe" /nosplash /minimized
O4 - HKCU\..\Run: [swg] C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
O4 - HKCU\..\Run: [Steam] "c:\progra~1\valve\steam\steam.exe" -silent
O4 - HKCU\..\Run: [MsnMsgr] "C:\Program Files\MSN Messenger\MsnMsgr.Exe" /background
O4 - HKCU\..\Run: [DAEMON Tools Lite] "C:\Program Files\DAEMON Tools Lite\daemon.exe" -autorun
O4 - HKUS\S-1-5-19\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'LOCAL SERVICE')
O4 - HKUS\S-1-5-20\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'NETWORK SERVICE')
O4 - HKUS\S-1-5-18\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'SYSTEM')
O4 - HKUS\.DEFAULT\..\Run: [CTFMON.EXE] C:\WINDOWS\System32\CTFMON.EXE (User 'Default user')
O4 - Startup: Picture Motion Browser Media Check Tool.lnk = C:\Program Files\Sony\Sony Picture Utility\VolumeWatcher\SPUVolumeWatcher.exe
O4 - Global Startup: Adobe Reader Speed Launch.lnk = C:\Program Files\Adobe\Acrobat 7.0\Reader\reader_sl.exe
O4 - Global Startup: Microsoft Office.lnk = C:\Program Files\Microsoft Office\Office10\OSA.EXE
O4 - Global Startup: WinZip Quick Pick.lnk = C:\Program Files\WinZip\WZQKPICK.EXE
O8 - Extra context menu item: E&xport to Microsoft Excel - res://C:\PROGRA~1\MICROS~2\Office10\EXCEL.EXE/3000
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_06\bin\ssv.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_06\bin\ssv.dll
O9 - Extra button: Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O9 - Extra 'Tools' menuitem: Windows Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O12 - Plugin for .spop: C:\Program Files\Internet Explorer\Plugins\NPDocBox.dll
O16 - DPF: {05CDEE1D-D109-4992-B72B-6D4F5E2AB731} (PhotoBox uploader) - http://static.photob...geUploader4.cab
O16 - DPF: {0EB0E74A-2A76-4AB3-A7FB-9BD8C29F7F75} (CKAVWebScan Object) - http://www.kaspersky...can_unicode.cab
O16 - DPF: {4F1E5B1A-2A80-42CA-8532-2D05CB959537} (MSN Photo Upload Tool) - http://gfx1.hotmail....es/MSNPUpld.cab
O16 - DPF: {5C6698D9-7BE4-4122-8EC5-291D84DBD4A0} (Facebook Photo Uploader 4 Control) - http://upload.facebo...toUploader3.cab
O16 - DPF: {6414512B-B978-451D-A0D8-FCFDF33E833C} (WUWebControl Class) - http://v5.windowsupd...b?1099406122515
O16 - DPF: {67A5F8DC-1A4B-4D66-9F24-A704AD929EEE} (System Requirements Lab) - http://www.systemreq.../sysreqlab2.cab
O18 - Protocol: linkscanner - {F274614C-63F8-47D5-A4D1-FBDDE494F8D1} - C:\Program Files\AVG\AVG8\avgpp.dll
O20 - AppInit_DLLs: avgrsstx.dll
O23 - Service: Ad-Aware 2007 Service (aawservice) - Lavasoft - C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
O23 - Service: Apple Mobile Device - Apple, Inc. - C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
O23 - Service: asurscsi - Unknown owner - C:\Program Files\Voyetra\AudioSurgeon 5\asurscsi.exe (file missing)
O23 - Service: Ati HotKey Poller - ATI Technologies Inc. - C:\WINDOWS\system32\Ati2evxx.exe
O23 - Service: ATI Smart - Unknown owner - C:\WINDOWS\system32\ati2sgag.exe
O23 - Service: AVG8 WatchDog (avg8wd) - AVG Technologies CZ, s.r.o. - C:\PROGRA~1\AVG\AVG8\avgwdsvc.exe
O23 - Service: Google Updater Service (gusvc) - Google - C:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
O23 - Service: InstallDriver Table Manager (IDriverT) - Macrovision Corporation - C:\Program Files\Common Files\InstallShield\Driver\11\Intel 32\IDriverT.exe
O23 - Service: iPod Service - Apple Inc. - C:\Program Files\iPod\bin\iPodService.exe
O23 - Service: PnkBstrA - Unknown owner - C:\WINDOWS\system32\PnkBstrA.exe
O23 - Service: PnkBstrB - Unknown owner - C:\WINDOWS\system32\PnkBstrB.exe
--
End of file - 8379 bytes
3. I'll have to have a bit of a ply around but it does seem better than before. Although the java install only seemed to be downloading at 9kb.
#26
![I'm still treading water but fear I may drown [RESOLVED]: post #26](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 05:17 PM
Posted 08 May 2008 - 05:17 PM

congratulations, your logs are clean and another fix is in the can 
in this post we will clear away the fix tools (this is so that should you ever be re-infected, you will download updated versions and it will also remove the quarantined Malware from your computer), reset your restore points (there will be infections lurking in there) and i will leave you with some ideas on how to enhance the protection of your machine against future infection.
====STEP 1====
Follow these steps to uninstall Combofix and tools used in the removal of malware
====STEP 2====
clear your restore points:
To reset your restore points, please note that you will need to log into your computer with an account which has full administrator access. You will know if the account has administrator access because you will be able to see the System Restore tab. If the tab is missing, you are logged in under a limited account.
Instructions with screenshots to help is http://www.f-secure..../sfc_dis1.shtml
(Windows XP)
1. Turn off System Restore.
On the Desktop, right-click My Computer.
Click Properties.
Click the System Restore tab.
Check Turn off System Restore.
Click Apply, and then click OK.
2. Reboot.
3. Turn ON System Restore.
On the Desktop, right-click My Computer.
Click Properties.
Click the System Restore tab.
UN-Check *Turn off System Restore*.
Click Apply, and then click OK.
How to Turn On and Turn Off System Restore in Windows XP
http://support.microsoft.com/kb/310405
====IDEAS TO SPEED UP YOUR MACHINE====
this page http://users.telenet...owcomputer.html gives some good ideas on how to improve the efficiency of your machine and has one or two useful links to help your further.
====AND FINALLY====
The following is a list of tools and utilities that I like to suggest to people. This list is full of great tools and utilities to help you understand how you got infected and how to keep from getting infected again.
andrewuk
in this post we will clear away the fix tools (this is so that should you ever be re-infected, you will download updated versions and it will also remove the quarantined Malware from your computer), reset your restore points (there will be infections lurking in there) and i will leave you with some ideas on how to enhance the protection of your machine against future infection.
go through the steps in this post, and if your internet connection is still slow or other issues arise, then let me know and we will do another deep scan to see if it is malware related before i point you in the direction to another part of the forum. but, as far as i can tell, we removed all the malware. and there was plenty of it.Although the java install only seemed to be downloading at 9kb.
====STEP 1====
Follow these steps to uninstall Combofix and tools used in the removal of malware
- Click START then RUN
- Now type Combofix /u in the runbox and click OK. Note the space between the X and the U, it needs to be there.
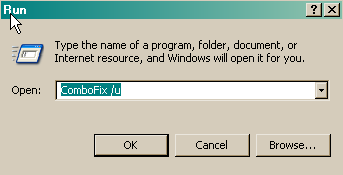
====STEP 2====
clear your restore points:
To reset your restore points, please note that you will need to log into your computer with an account which has full administrator access. You will know if the account has administrator access because you will be able to see the System Restore tab. If the tab is missing, you are logged in under a limited account.
Instructions with screenshots to help is http://www.f-secure..../sfc_dis1.shtml
(Windows XP)
1. Turn off System Restore.
On the Desktop, right-click My Computer.
Click Properties.
Click the System Restore tab.
Check Turn off System Restore.
Click Apply, and then click OK.
2. Reboot.
3. Turn ON System Restore.
On the Desktop, right-click My Computer.
Click Properties.
Click the System Restore tab.
UN-Check *Turn off System Restore*.
Click Apply, and then click OK.
How to Turn On and Turn Off System Restore in Windows XP
http://support.microsoft.com/kb/310405
====IDEAS TO SPEED UP YOUR MACHINE====
this page http://users.telenet...owcomputer.html gives some good ideas on how to improve the efficiency of your machine and has one or two useful links to help your further.
====AND FINALLY====
The following is a list of tools and utilities that I like to suggest to people. This list is full of great tools and utilities to help you understand how you got infected and how to keep from getting infected again.
- Spybot Search & Destroy - Uber powerful tool which can search and annhilate nasties that make it onto your system. Now with an Immunize section that will help prevent future infections.
- AdAware - Another very powerful tool which searches and kills nasties that infect your system. AdAware and Spybot Search & Destroy compliment each other very well.
- SpywareBlaster - Great prevention tool to keep nasties from installing on your system.
- SpywareGuard - Works as a Spyware "Shield" to protect your computer from getting malware in the first place.
- IE-SpyAd - puts over 5000 sites in your restricted zone so you'll be protected when you visit innocent-looking sites that aren't actually innocent at all.
- ATF Cleaner - Cleans temporary files from IE and Windows, empties the recycle bin and more. Great tool to help speed up your computer and knock out those nasties that like to reside in the temp folders.
- Windows Updates - It is very important to make sure that both Internet Explorer and Windows are kept current with the latest critical security patches from Microsoft. To do this just start Internet Explorer and select Tools > Windows Update, and follow the online instructions from there.
- Google Toolbar - Free google toolbar that allows you to use the powerful Google search engine from the bar, but also blocks pop up windows.
- Trillian or Miranda-IM - These are Malware free Instant Messenger programs which allow you to connect to multiple IM services in one program! (AOL, Yahoo, ICQ, IRC, MSN)
andrewuk
#27
![I'm still treading water but fear I may drown [RESOLVED]: post #27](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 05:32 PM
Posted 08 May 2008 - 05:32 PM

Everything is running perfectly. I can't thank you enough for your help and patience
#28
![I'm still treading water but fear I may drown [RESOLVED]: post #28](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 May 2008 - 08:53 PM
Posted 08 May 2008 - 08:53 PM

Since this issue appears to be resolved ... this Topic has been closed. Glad we could help. 
If you're the topic starter, and need this topic reopened, please contact a staff member with the address of the thread.
Everyone else please begin a New Topic.
If you're the topic starter, and need this topic reopened, please contact a staff member with the address of the thread.
Everyone else please begin a New Topic.
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked




 Sign In
Sign In Create Account
Create Account

