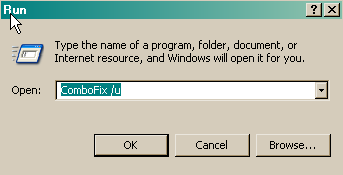
here's the combofix log, sorry for the delay but I had to download the Java from another laptop on a Memory stick for Kaspersky as I kept getting a 'Page cannot be displayed' message:
ComboFix 08-08-28.04 - Julie 2008-08-29 18:10:10.5 - NTFSx86
Microsoft Windows XP Professional 5.1.2600.2.1252.1.1033.18.237 [GMT 1:00]
Running from: C:\Documents and Settings\Julie\Desktop\ComboFix.exe
Command switches used :: C:\Documents and Settings\Julie\Desktop\CFScript.txt
* Created a new restore point
FILE ::
4C:\WINDOWS\system32\ujolidedyl.ban
.
((((((((((((((((((((((((( Files Created from 2008-07-28 to 2008-08-29 )))))))))))))))))))))))))))))))
.
2008-08-29 07:51 . 2008-08-29 07:51 <DIR> d-------- C:\Program Files\Malwarebytes' Anti-Malware
2008-08-29 07:51 . 2008-08-29 07:51 <DIR> d-------- C:\Documents and Settings\Julie\Application Data\Malwarebytes
2008-08-29 07:51 . 2008-08-29 07:51 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\Malwarebytes
2008-08-29 07:51 . 2008-08-17 15:01 38,472 --a------ C:\WINDOWS\system32\drivers\mbamswissarmy.sys
2008-08-29 07:51 . 2008-08-17 15:01 17,144 --a------ C:\WINDOWS\system32\drivers\mbam.sys
2008-08-28 22:21 . 2008-08-28 22:21 <DIR> d-------- C:\WINDOWS\LastGood
2008-08-24 18:11 . 2008-08-29 18:03 11,289 --a------ C:\WINDOWS\system32\nvModes.001
2008-08-24 18:10 . 2008-08-29 18:03 11,289 --a------ C:\WINDOWS\system32\nvModes.dat
2008-08-24 09:59 . 2008-08-24 18:10 <DIR> d-------- C:\WINDOWS\nview
2008-08-24 09:59 . 2004-10-26 12:01 176,128 --a------ C:\WINDOWS\system32\nvudisp.exe
2008-08-24 09:59 . 2004-10-26 12:01 13,866 --a------ C:\WINDOWS\system32\nvdisp.nvu
2008-08-23 20:54 . 2008-04-11 19:50 683,520 -----c--- C:\WINDOWS\system32\dllcache\inetcomm.dll
2008-08-23 20:54 . 2008-05-01 15:30 331,776 -----c--- C:\WINDOWS\system32\dllcache\msadce.dll
2008-08-23 20:54 . 2008-06-13 14:10 272,128 -----c--- C:\WINDOWS\system32\dllcache\bthport.sys
2008-08-23 08:39 . 2008-08-23 08:39 <DIR> d-------- C:\Program Files\Trend Micro
2008-08-23 00:58 . 2008-08-23 00:58 <DIR> d-------- C:\Program Files\Windows Defender
2008-08-23 00:42 . 2008-08-23 00:55 316,640 --a------ C:\WINDOWS\WMSysPr9.prx
2008-08-23 00:35 . 2008-08-23 00:35 <DIR> d-------- C:\WINDOWS\ServicePackFiles
2008-08-23 00:26 . 2004-07-17 11:40 19,528 --a------ C:\WINDOWS\002470_.tmp
2008-08-23 00:14 . 2008-08-23 00:14 <DIR> d-------- C:\WINDOWS\EHome
2008-08-22 23:47 . 2008-08-22 23:49 <DIR> d-------- C:\Program Files\SpywareBlaster
2008-08-22 23:47 . 2008-08-23 00:55 <DIR> d-a------ C:\Documents and Settings\All Users\Application Data\TEMP
2008-08-22 23:47 . 2005-08-25 19:18 118,784 --a------ C:\WINDOWS\system32\MSSTDFMT.DLL
2008-08-22 23:46 . 2008-08-29 07:50 <DIR> d-------- C:\Documents and Settings\LocalService\Application Data\SACore
2008-08-22 23:45 . 2008-08-22 23:45 <DIR> d-------- C:\Program Files\Common Files\McAfee
2008-08-22 23:45 . 2008-08-22 23:45 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\SiteAdvisor
2008-08-22 23:43 . 2008-08-28 22:21 <DIR> d-------- C:\Program Files\McAfee
2008-08-22 23:43 . 2008-08-22 23:43 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\McAfee
2008-08-22 23:36 . 2008-08-24 10:02 <DIR> d--h----- C:\WINDOWS\$hf_mig$
2008-08-22 23:36 . 2005-02-25 04:35 22,752 --a------ C:\WINDOWS\system32\spupdsvc.exe
2008-08-22 23:35 . 2008-08-22 23:35 <DIR> d-------- C:\WINDOWS\system32\bits
2008-08-22 23:35 . 2008-08-24 10:01 1,374 --a------ C:\WINDOWS\imsins.BAK
2008-08-22 23:34 . 2004-08-04 00:56 438,784 --------- C:\WINDOWS\system32\xpob2res.dll
2008-08-22 23:34 . 2004-08-04 00:56 351,232 --a------ C:\WINDOWS\system32\winhttp.dll
2008-08-22 23:34 . 2004-08-04 00:56 18,944 --a------ C:\WINDOWS\system32\qmgrprxy.dll
2008-08-22 23:34 . 2004-08-04 00:56 8,192 --------- C:\WINDOWS\system32\bitsprx2.dll
2008-08-22 23:34 . 2004-08-04 00:56 7,168 --------- C:\WINDOWS\system32\bitsprx3.dll
2008-08-22 23:04 . 2008-08-22 23:04 <DIR> d-------- C:\Program Files\CCleaner
2008-08-22 22:58 . 2008-08-22 22:58 <DIR> d-------- C:\!KillBox
2008-08-22 22:18 . 2007-09-06 00:22 289,144 --a------ C:\WINDOWS\system32\VCCLSID.exe
2008-08-22 22:18 . 2006-04-27 17:49 288,417 --a------ C:\WINDOWS\system32\SrchSTS.exe
2008-08-22 22:18 . 2008-08-21 23:41 87,552 --a------ C:\WINDOWS\system32\AntiXPVSTFix.exe
2008-08-22 22:18 . 2008-05-29 09:35 86,528 --a------ C:\WINDOWS\system32\VACFix.exe
2008-08-22 22:18 . 2008-05-18 21:40 82,944 --a------ C:\WINDOWS\system32\IEDFix.exe
2008-08-22 22:18 . 2008-08-14 21:52 82,432 --a------ C:\WINDOWS\system32\IEDFix.C.exe
2008-08-22 22:18 . 2008-08-18 12:19 82,432 --a------ C:\WINDOWS\system32\404Fix.exe
2008-08-22 22:18 . 2003-06-05 21:13 53,248 --a------ C:\WINDOWS\system32\Process.exe
2008-08-22 22:18 . 2004-07-31 18:50 51,200 --a------ C:\WINDOWS\system32\dumphive.exe
2008-08-22 22:18 . 2007-10-04 00:36 25,600 --a------ C:\WINDOWS\system32\WS2Fix.exe
2008-08-22 22:06 . 2008-08-22 22:16 <DIR> d-------- C:\Program Files\ewido anti-spyware 4.0
2008-08-22 18:05 . 2008-08-22 18:05 19,409 --a------ C:\WINDOWS\system32\ujolidedyl.ban
2008-08-22 18:05 . 2008-08-22 18:05 18,522 --a------ C:\WINDOWS\system32\ugohinol.db
2008-08-22 18:05 . 2008-08-22 18:05 17,640 --a------ C:\WINDOWS\ufimyjybez.inf
2008-08-22 18:05 . 2008-08-22 18:05 17,482 --a------ C:\WINDOWS\mopafan.dat
2008-08-22 18:05 . 2008-08-22 18:05 16,475 --a------ C:\WINDOWS\enydefov.lib
2008-08-22 18:05 . 2008-08-22 18:05 15,906 --a------ C:\WINDOWS\ylegapytil.ban
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2008-07-20 21:01 50,176 ----a-w C:\WINDOWS\system32\dcrick.dll
2008-07-20 20:42 50,176 ----a-w C:\WINDOWS\system32\ritz8.dll
2008-07-18 21:10 94,920 ----a-w C:\WINDOWS\system32\cdm.dll
2008-07-18 21:10 53,448 ----a-w C:\WINDOWS\system32\wuauclt.exe
2008-07-18 21:10 45,768 ----a-w C:\WINDOWS\system32\wups2.dll
2008-07-18 21:10 36,552 ----a-w C:\WINDOWS\system32\wups.dll
2008-07-18 21:09 563,912 ----a-w C:\WINDOWS\system32\wuapi.dll
2008-07-18 21:09 325,832 ----a-w C:\WINDOWS\system32\wucltui.dll
2008-07-18 21:09 205,000 ----a-w C:\WINDOWS\system32\wuweb.dll
2008-07-18 21:09 1,811,656 ----a-w C:\WINDOWS\system32\wuaueng.dll
2008-07-07 20:32 253,952 ----a-w C:\WINDOWS\system32\es.dll
2008-06-24 16:23 74,240 ----a-w C:\WINDOWS\system32\mscms.dll
2008-06-23 15:38 659,456 ----a-w C:\WINDOWS\system32\wininet.dll
2008-06-20 17:41 245,248 ----a-w C:\WINDOWS\system32\mswsock.dll
.
((((((((((((((((((((((((((((( snapshot_2008-08-28_ 7.50.14.54 )))))))))))))))))))))))))))))))))))))))))
.
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ctfmon.exe"="C:\WINDOWS\system32\ctfmon.exe" [2004-08-04 00:56 15360]
"MSMSGS"="C:\Program Files\Messenger\msmsgs.exe" [2004-08-04 00:56 1667584]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"AdaptecDirectCD"="C:\Program Files\Roxio\Easy CD Creator 5\DirectCD\DirectCD.exe" [2002-12-17 12:28 684032]
"Adobe Reader Speed Launcher"="C:\Program Files\Adobe\Reader 8.0\Reader\Reader_sl.exe" [2008-01-11 22:16 39792]
"!ewido"="C:\Program Files\ewido anti-spyware 4.0\ewido.exe" [2008-08-22 22:15 6283264]
"NvCplDaemon"="C:\WINDOWS\system32\NvCpl.dll" [2004-10-26 12:01 4632576]
"nwiz"="nwiz.exe" [2004-10-26 12:01 921600 C:\WINDOWS\system32\nwiz.exe]
[HKEY_LOCAL_MACHINE\system\currentcontrolset\control\securityproviders]
SecurityProviders msapsspc.dllschannel.dlldigest.dllmsnsspc.dll
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\services]
"Pml Driver HPZ12"=2 (0x2)
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
R2 McAfee SiteAdvisor Service;McAfee SiteAdvisor Service;C:\Program Files\McAfee\SiteAdvisor\McSACore.exe [2008-07-23 18:52]
S2 0035301219958581mcinstcleanup;McAfee Application Installer Cleanup (0035301219958581);C:\WINDOWS\TEMP\003530~1.EXE C:\PROGRA~1\COMMON~1\McAfee\INSTAL~1\cleanup.ini []
.
Contents of the 'Scheduled Tasks' folder
2008-08-29 C:\WINDOWS\Tasks\MP Scheduled Scan.job
- C:\Program Files\Windows Defender\MpCmdRun.exe [2006-11-03 19:20]
.
**************************************************************************
catchme 0.3.1361 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2008-08-29 18:11:33
Windows 5.1.2600 Service Pack 2 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
--------------------- DLLs Loaded Under Running Processes ---------------------
PROCESS: C:\WINDOWS\explorer.exe
-> C:\Program Files\McAfee\SiteAdvisor\saHook.dll
.
Completion time: 2008-08-29 18:12:28
ComboFix-quarantined-files.txt 2008-08-29 17:12:24
ComboFix2.txt 2008-08-29 06:48:35
ComboFix3.txt 2008-08-28 21:30:42
ComboFix4.txt 2008-08-28 06:50:37
ComboFix5.txt 2008-08-29 17:09:34
Pre-Run: 25,242,542,080 bytes free
Post-Run: 25,238,323,200 bytes free
137 --- E O F --- 2008-08-26 21:45:18
......and here's the Kaspersky log:
--------------------------------------------------------------------------------
KASPERSKY ONLINE SCANNER 7 REPORT
Friday, August 29, 2008
Operating System: Microsoft Windows XP Professional Service Pack 2 (build 2600)
Kaspersky Online Scanner 7 version: 7.0.25.0
Program database last update: Friday, August 29, 2008 17:15:08
Records in database: 1163294
--------------------------------------------------------------------------------
Scan settings:
Scan using the following database: extended
Scan archives: yes
Scan mail databases: yes
Scan area - My Computer:
C:\
D:\
Scan statistics:
Files scanned: 25248
Threat name: 5
Infected objects: 6
Suspicious objects: 0
Duration of the scan: 00:35:25
File name / Threat name / Threats count
C:\Documents and Settings\Julie\Desktop\SmitfraudFix\Reboot.exe Infected: not-a-virus:RiskTool.Win32.Reboot.f 1
C:\QooBox\Quarantine\C\Documents and Settings\All Users\Application Data\olwjmfyd\gnufypgh.exe.vir Infected: Trojan-Downloader.Win32.Agent.acnm 1
C:\QooBox\Quarantine\C\WINDOWS\system32\dllcache\beep.sys.vir Infected: not-a-virus:FraudTool.Win32.UltimateDefender.cm 1
C:\QooBox\Quarantine\C\WINDOWS\system32\lbbd32.dll.vir Infected: Trojan-Downloader.Win32.BHO.me 1
C:\WINDOWS\system32\dcrick.dll Infected: Trojan-Spy.Win32.Banker.pcl 1
C:\WINDOWS\system32\ritz8.dll Infected: Trojan-Spy.Win32.Banker.pcl 1
The selected area was scanned.

 This topic is locked
This topic is locked













 Sign In
Sign In Create Account
Create Account

