Anyway, today, at some point, I must have visted an infected webpage and had a Rouge software program installed, I didn't know untill later on tonight when it popped up saying "Your infected blah blah" and I knew instantly what it was, I've had some experience with these programs, Imeediately I went to do a system restore, finding all the saves deleted (is there a way to make a backup of these?) I went onto use HiJackThis and Spybox S&D, Spybot told me I had SmitFraud-c so I ran Smitfraudfix even after removing the entry via Spybot just incase.
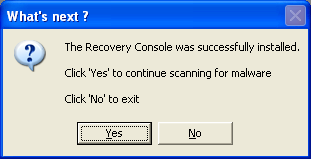
After all this I ran safe mode and proceeded to search up fixes to the name of which this particular program called itself (Virus Remover 2008) and whist doing so had various pages redirected to the random AdAware websites... I came here after remembering the URL and I did as instructed in the section above this and downloaded "Malwarebytes", used it, and so far, everything is fine, of course, the question is, is it really fine?
While posting this I have run both HiJackThis and Malwarebytes for updated logs (one at a time), here they are, hope you can help (if it isn't already gone).
Thanks for any help
Logfile of Trend Micro HijackThis v2.0.2
Scan saved at 9:06:16 PM, on 2/7/2009
Platform: Windows XP SP2 (WinNT 5.01.2600)
MSIE: Internet Explorer v7.00 (7.00.6000.16674)
Boot mode: Normal
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\system32\spoolsv.exe
C:\WINDOWS\Explorer.EXE
C:\WINDOWS\RTHDCPL.EXE
C:\PROGRA~1\Grisoft\AVG7\avgcc.exe
C:\Program Files\CyberLink\PowerDVD\PDVDServ.exe
C:\Program Files\Java\jre1.6.0_07\bin\jusched.exe
C:\Program Files\Common Files\Real\Update_OB\realsched.exe
C:\Program Files\Grisoft\AVG Anti-Spyware 7.5\avgas.exe
C:\Program Files\Adobe\Reader 8.0\Reader\Reader_sl.exe
C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\MOM.exe
C:\Program Files\iTunes\iTunesHelper.exe
C:\Program Files\ScanSoft\OmniPageSE4\OpwareSE4.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\Windows Live\Messenger\MsnMsgr.Exe
C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
C:\Program Files\DAEMON Tools\daemon.exe
C:\PROGRA~1\Grisoft\AVG7\avgamsvr.exe
C:\PROGRA~1\Grisoft\AVG7\avgupsvc.exe
C:\PROGRA~1\Grisoft\AVG7\avgemc.exe
C:\Documents and Settings\Timothy Halton\Local Settings\Application Data\Google\Update\GoogleUpdate.exe
C:\Program Files\DNA\btdna.exe
C:\Program Files\Windows Media Player\WMPNSCFG.exe
C:\Program Files\Nikon\PictureProject\NkbMonitor.exe
C:\Program Files\Bonjour\mDNSResponder.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\CyberLink\Shared Files\RichVideo.exe
C:\WINDOWS\system32\svchost.exe
C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\ccc.exe
C:\Program Files\Canon\CAL\CALMAIN.exe
C:\Program Files\iPod\bin\iPodService.exe
C:\Program Files\Windows Live\Messenger\usnsvc.exe
C:\Program Files\Opera\opera.exe
C:\Documents and Settings\Timothy Halton\Desktop\Timmy's Things\Useful Programs\hijackthis\HijackThis.exe
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL = http://go.microsoft....k/?LinkId=69157
R0 - HKLM\Software\Microsoft\Internet Explorer\Main,Start Page = http://go.microsoft....k/?LinkId=69157
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,ProxyOverride = *.local
R3 - URLSearchHook: Yahoo! Toolbar - {EF99BD32-C1FB-11D2-892F-0090271D4F88} - C:\PROGRA~1\Yahoo!\Companion\Installs\cpn\yt.dll
O2 - BHO: &Yahoo! Toolbar Helper - {02478D38-C3F9-4efb-9B51-7695ECA05670} - C:\PROGRA~1\Yahoo!\Companion\Installs\cpn\yt.dll
O2 - BHO: Adobe PDF Reader Link Helper - {06849E9F-C8D7-4D59-B87D-784B7D6BE0B3} - C:\Program Files\Common Files\Adobe\Acrobat\ActiveX\AcroIEHelper.dll
O2 - BHO: RealPlayer Download and Record Plugin for Internet Explorer - {3049C3E9-B461-4BC5-8870-4C09146192CA} - C:\Program Files\Real\RealPlayer\rpbrowserrecordplugin.dll
O2 - BHO: (no name) - {53707962-6F74-2D53-2644-206D7942484F} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O2 - BHO: SSVHelper Class - {761497BB-D6F0-462C-B6EB-D4DAF1D92D43} - C:\Program Files\Java\jre1.6.0_07\bin\ssv.dll
O2 - BHO: Windows Live Sign-in Helper - {9030D464-4C02-4ABF-8ECC-5164760863C6} - C:\Program Files\Common Files\Microsoft Shared\Windows Live\WindowsLiveLogin.dll
O3 - Toolbar: Yahoo! Toolbar - {EF99BD32-C1FB-11D2-892F-0090271D4F88} - C:\PROGRA~1\Yahoo!\Companion\Installs\cpn\yt.dll
O4 - HKLM\..\Run: [RTHDCPL] RTHDCPL.EXE
O4 - HKLM\..\Run: [AVG7_CC] C:\PROGRA~1\Grisoft\AVG7\avgcc.exe /STARTUP
O4 - HKLM\..\Run: [NeroFilterCheck] C:\Program Files\Common Files\Ahead\Lib\NeroCheck.exe
O4 - HKLM\..\Run: [RemoteControl] "C:\Program Files\CyberLink\PowerDVD\PDVDServ.exe"
O4 - HKLM\..\Run: [LanguageShortcut] "C:\Program Files\CyberLink\PowerDVD\Language\Language.exe"
O4 - HKLM\..\Run: [SunJavaUpdateSched] "C:\Program Files\Java\jre1.6.0_07\bin\jusched.exe"
O4 - HKLM\..\Run: [TkBellExe] "C:\Program Files\Common Files\Real\Update_OB\realsched.exe" -osboot
O4 - HKLM\..\Run: [!AVG Anti-Spyware] "C:\Program Files\Grisoft\AVG Anti-Spyware 7.5\avgas.exe" /minimized
O4 - HKLM\..\Run: [ISUSPM Startup] "C:\Program Files\Common Files\InstallShield\UpdateService\isuspm.exe" -startup
O4 - HKLM\..\Run: [ISUSScheduler] "C:\Program Files\Common Files\InstallShield\UpdateService\issch.exe" -start
O4 - HKLM\..\Run: [Adobe Reader Speed Launcher] "C:\Program Files\Adobe\Reader 8.0\Reader\Reader_sl.exe"
O4 - HKLM\..\Run: [StartCCC] "C:\Program Files\ATI Technologies\ATI.ACE\Core-Static\CLIStart.exe"
O4 - HKLM\..\Run: [QuickTime Task] "C:\Program Files\QuickTime\qttask.exe" -atboottime
O4 - HKLM\..\Run: [iTunesHelper] "C:\Program Files\iTunes\iTunesHelper.exe"
O4 - HKLM\..\Run: [SSBkgdUpdate] "C:\Program Files\Common Files\Scansoft Shared\SSBkgdUpdate\SSBkgdupdate.exe" -Embedding -boot
O4 - HKLM\..\Run: [OpwareSE4] "C:\Program Files\ScanSoft\OmniPageSE4\OpwareSE4.exe"
O4 - HKCU\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\ctfmon.exe
O4 - HKCU\..\Run: [MsnMsgr] "C:\Program Files\Windows Live\Messenger\MsnMsgr.Exe" /background
O4 - HKCU\..\Run: [DAEMON Tools Lite] "C:\Program Files\DAEMON Tools\daemon.exe" -autorun
O4 - HKCU\..\Run: [Yahoo! Pager] "C:\Program Files\Yahoo!\Messenger\YahooMessenger.exe" -quiet
O4 - HKCU\..\Run: [Google Update] "C:\Documents and Settings\Timothy Halton\Local Settings\Application Data\Google\Update\GoogleUpdate.exe" /c
O4 - HKCU\..\Run: [BitTorrent DNA] "C:\Program Files\DNA\btdna.exe"
O4 - HKCU\..\Run: [WMPNSCFG] C:\Program Files\Windows Media Player\WMPNSCFG.exe
O4 - HKUS\S-1-5-19\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\CTFMON.EXE (User 'LOCAL SERVICE')
O4 - HKUS\S-1-5-19\..\Run: [AVG7_Run] C:\PROGRA~1\Grisoft\AVG7\avgw.exe /RUNONCE (User 'LOCAL SERVICE')
O4 - HKUS\S-1-5-20\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\CTFMON.EXE (User 'NETWORK SERVICE')
O4 - HKUS\S-1-5-18\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\CTFMON.EXE (User 'SYSTEM')
O4 - HKUS\.DEFAULT\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\CTFMON.EXE (User 'Default user')
O4 - Startup: Adobe Gamma.lnk = C:\Program Files\Common Files\Adobe\Calibration\Adobe Gamma Loader.exe
O4 - Startup: Xfire.lnk = C:\Program Files\Xfire\xfire.exe
O4 - Global Startup: NkbMonitor.exe.lnk = C:\Program Files\Nikon\PictureProject\NkbMonitor.exe
O8 - Extra context menu item: E&xport to Microsoft Excel - res://C:\PROGRA~1\MICROS~2\OFFICE11\EXCEL.EXE/3000
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_07\bin\ssv.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre1.6.0_07\bin\ssv.dll
O9 - Extra button: Research - {92780B25-18CC-41C8-B9BE-3C9C571A8263} - C:\PROGRA~1\MICROS~2\OFFICE11\REFIEBAR.DLL
O9 - Extra button: (no name) - {e2e2dd38-d088-4134-82b7-f2ba38496583} - C:\WINDOWS\Network Diagnostic\xpnetdiag.exe
O9 - Extra 'Tools' menuitem: @xpsp3res.dll,-20001 - {e2e2dd38-d088-4134-82b7-f2ba38496583} - C:\WINDOWS\Network Diagnostic\xpnetdiag.exe
O9 - Extra button: Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O9 - Extra 'Tools' menuitem: Windows Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O16 - DPF: {20A60F0D-9AFA-4515-A0FD-83BD84642501} (Checkers Class) - http://messenger.zon...kr.cab56986.cab
O16 - DPF: {5D6F45B3-9043-443D-A792-115447494D24} (UnoCtrl Class) - http://messenger.zon...1/GAME_UNO1.cab
O16 - DPF: {6414512B-B978-451D-A0D8-FCFDF33E833C} (WUWebControl Class) - http://www.update.mi...b?1202356700750
O16 - DPF: {BD393C14-72AD-4790-A095-76522973D6B8} (CBreakshotControl Class) - http://messenger.zon...ot.cab57213.cab
O16 - DPF: {C3F79A2B-B9B4-4A66-B012-3EE46475B072} (MessengerStatsClient Class) - http://messenger.zon...nt.cab56907.cab
O16 - DPF: {D27CDB6E-AE6D-11CF-96B8-444553540000} (Shockwave Flash Object) - http://fpdownload2.m...ash/swflash.cab
O16 - DPF: {F5A7706B-B9C0-4C89-A715-7A0C6B05DD48} (Minesweeper Flags Class) - http://messenger.zon...er.cab56986.cab
O23 - Service: Ad-Aware 2007 Service (aawservice) - Lavasoft - C:\Program Files\Lavasoft\Ad-Aware 2007\aawservice.exe
O23 - Service: Adobe LM Service - Adobe Systems - C:\Program Files\Common Files\Adobe Systems Shared\Service\Adobelmsvc.exe
O23 - Service: Apple Mobile Device - Apple Inc. - C:\Program Files\Common Files\Apple\Mobile Device Support\bin\AppleMobileDeviceService.exe
O23 - Service: Ati HotKey Poller - ATI Technologies Inc. - C:\WINDOWS\system32\Ati2evxx.exe
O23 - Service: ATI Smart - Unknown owner - C:\WINDOWS\system32\ati2sgag.exe
O23 - Service: AVG Anti-Spyware Guard - GRISOFT s.r.o. - C:\Program Files\Grisoft\AVG Anti-Spyware 7.5\guard.exe
O23 - Service: AVG7 Alert Manager Server (Avg7Alrt) - GRISOFT, s.r.o. - C:\PROGRA~1\Grisoft\AVG7\avgamsvr.exe
O23 - Service: AVG7 Update Service (Avg7UpdSvc) - GRISOFT, s.r.o. - C:\PROGRA~1\Grisoft\AVG7\avgupsvc.exe
O23 - Service: AVG E-mail Scanner (AVGEMS) - GRISOFT, s.r.o. - C:\PROGRA~1\Grisoft\AVG7\avgemc.exe
O23 - Service: Bonjour Service - Apple Inc. - C:\Program Files\Bonjour\mDNSResponder.exe
O23 - Service: Canon Camera Access Library 8 (CCALib8) - Canon Inc. - C:\Program Files\Canon\CAL\CALMAIN.exe
O23 - Service: iPod Service - Apple Inc. - C:\Program Files\iPod\bin\iPodService.exe
O23 - Service: NBService - Nero AG - C:\Program Files\Nero\Nero 7\Nero BackItUp\NBService.exe
O23 - Service: NMIndexingService - Nero AG - C:\Program Files\Common Files\Ahead\Lib\NMIndexingService.exe
O23 - Service: Cyberlink RichVideo Service(CRVS) (RichVideo) - Unknown owner - C:\Program Files\CyberLink\Shared Files\RichVideo.exe
--
End of file - 10180 bytes
Malwarebytes' Scan 1:
Malwarebytes' Anti-Malware 1.33
Database version: 1736
Windows 5.1.2600 Service Pack 2
2/7/2009 8:55:36 PM
mbam-log-2009-02-07 (20-55-36).txt
Scan type: Quick Scan
Objects scanned: 51584
Time elapsed: 2 minute(s), 54 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 2
Registry Keys Infected: 28
Registry Values Infected: 4
Registry Data Items Infected: 2
Folders Infected: 3
Files Infected: 12
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
C:\WINDOWS\system32\nnnoNfFU.dll (Trojan.Vundo.H) -> Delete on reboot.
C:\WINDOWS\system32\ddcYoLET.dll (Trojan.Vundo) -> Delete on reboot.
Registry Keys Infected:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{f88c3356-9e1f-4599-8643-c9979f83fdf1} (Trojan.Vundo.H) -> Delete on reboot.
HKEY_CLASSES_ROOT\CLSID\{f88c3356-9e1f-4599-8643-c9979f83fdf1} (Trojan.Vundo.H) -> Delete on reboot.
HKEY_CLASSES_ROOT\Interface\{cf54be1c-9359-4395-8533-1657cf209cfe} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{6d794cb4-c7cd-4c6f-bfdc-9b77afbdc02c} (Trojan.Vundo) -> Delete on reboot.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{6d794cb4-c7cd-4c6f-bfdc-9b77afbdc02c} (Trojan.Vundo) -> Delete on reboot.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify\ddcyolet (Trojan.Vundo) -> Delete on reboot.
HKEY_CLASSES_ROOT\Typelib\{d518921a-4a03-425e-9873-b9a71756821e} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{07b18ea9-a523-4961-b6bb-170de4475cca} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{07b18eab-a523-4961-b6bb-170de4475cca} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{25560540-9571-4d7b-9389-0f166788785a} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{3dc201fb-e9c9-499c-a11f-23c360d7c3f8} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{9ff05104-b030-46fc-94b8-81276e4e27df} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{00a6faf1-072e-44cf-8957-5838f569a31d} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{59c7fc09-1c83-4648-b3e6-003d2bbc7481} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{68af847f-6e91-45dd-9b68-d6a12c30e5d7} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{9170b96c-28d4-4626-8358-27e6caeef907} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{d1a71fa0-ff48-48dd-9b6d-7a13a3e42127} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{ddb1968e-ead6-40fd-8dae-ff14757f60c7} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\ElevationPolicy\{f138d901-86f0-4383-99b6-9cdd406036da} (Adware.MyWebSearch) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\prunnet (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\xpreapp (Malware.Trace) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Low Rights\RunDll32Policy\f3ScrCtr.dll (Adware.MyWay) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\contim (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\instkey (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\rdfa (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\FCOVM (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RemoveRP (Trojan.Vundo) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Multimedia\WMPlayer\Schemes\f3pss (Adware.MyWebSearch) -> Quarantined and deleted successfully.
Registry Values Infected:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\684e63dc (Trojan.Vundo.H) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\prunnet (Trojan.Downloader) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ShellExecuteHooks\{6d794cb4-c7cd-4c6f-bfdc-9b77afbdc02c} (Trojan.Vundo) -> Delete on reboot.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\MenuExt\&Search\ (Adware.Hotbar) -> Quarantined and deleted successfully.
Registry Data Items Infected:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\LSA\Notification Packages (Trojan.Vundo.H) -> Data: c:\windows\system32\nnnonffu -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\LSA\Authentication Packages (Trojan.Vundo.H) -> Data: c:\windows\system32\nnnonffu -> Delete on reboot.
Folders Infected:
C:\Documents and Settings\Timothy Halton\Application Data\FunWebProducts (Adware.MyWay) -> Quarantined and deleted successfully.
C:\Documents and Settings\Timothy Halton\Application Data\FunWebProducts\Data (Adware.MyWay) -> Quarantined and deleted successfully.
C:\Documents and Settings\Timothy Halton\Application Data\FunWebProducts\Data\Timothy Halton (Adware.MyWay) -> Quarantined and deleted successfully.
Files Infected:
C:\WINDOWS\system32\nnnoNfFU.dll (Trojan.Vundo.H) -> Delete on reboot.
C:\WINDOWS\system32\UFfNonnn.ini (Trojan.Vundo.H) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\UFfNonnn.ini2 (Trojan.Vundo.H) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\lnhjvbao.dll (Trojan.Vundo.H) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\oabvjhnl.ini (Trojan.Vundo.H) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\prunnet.exe (Trojan.Downloader) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\ddcYoLET.dll (Trojan.Vundo) -> Delete on reboot.
C:\WINDOWS\system32\hgGywWOg.dll (Trojan.Vundo) -> Quarantined and deleted successfully.
C:\Documents and Settings\Timothy Halton\Application Data\FunWebProducts\Data\Timothy Halton\avatar.dat (Adware.MyWay) -> Quarantined and deleted successfully.
C:\Documents and Settings\Timothy Halton\Application Data\FunWebProducts\Data\Timothy Halton\outfit.dat (Adware.MyWay) -> Quarantined and deleted successfully.
C:\Documents and Settings\Timothy Halton\Application Data\FunWebProducts\Data\Timothy Halton\zbucks.dat (Adware.MyWay) -> Quarantined and deleted successfully.
C:\Documents and Settings\Timothy Halton\list.txt (Malware.Trace) -> Quarantined and deleted successfully.
Malwarebytes' Scan 2:
Malwarebytes' Anti-Malware 1.33
Database version: 1736
Windows 5.1.2600 Service Pack 2
2/7/2009 9:02:44 PM
mbam-log-2009-02-07 (21-02-44).txt
Scan type: Quick Scan
Objects scanned: 53090
Time elapsed: 2 minute(s), 12 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 1
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 7
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
C:\Program Files\Windows Live\Messenger\msimg32.dll (Adware.MyWebSearch) -> Delete on reboot.
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
C:\Program Files\Windows Live\Messenger\msimg32.dll (Adware.MyWebSearch) -> Delete on reboot.
C:\WINDOWS\system32\senekafaomyvtr.dll (Trojan.Agent) -> Delete on reboot.
C:\WINDOWS\system32\senekalfobwrtq.dll (Trojan.Agent) -> Delete on reboot.
C:\WINDOWS\system32\senekaovcxtjol.dll (Trojan.Agent) -> Delete on reboot.
C:\WINDOWS\system32\senekarkldjboh.dat (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\senekarqllhypv.dat (Trojan.Agent) -> Quarantined and deleted successfully.
C:\WINDOWS\system32\drivers\senekankndpuxb.sys (Trojan.Agent) -> Quarantined and deleted successfully.
Malwarebytes' Scan 3:
Malwarebytes' Anti-Malware 1.33
Database version: 1736
Windows 5.1.2600 Service Pack 2
2/7/2009 9:24:30 PM
mbam-log-2009-02-07 (21-24-30).txt
Scan type: Quick Scan
Objects scanned: 53218
Time elapsed: 2 minute(s), 20 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 1
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
C:\WINDOWS\system32\drivers\seneka.sys (Trojan.Agent) -> Quarantined and deleted successfully.

 This topic is locked
This topic is locked













 Sign In
Sign In Create Account
Create Account

