directdr.com redirect problem using IE 8
Started by
hsartin
, May 13 2010 08:19 PM
#1

 Posted 13 May 2010 - 08:19 PM
Posted 13 May 2010 - 08:19 PM

#2

 Posted 14 May 2010 - 02:31 AM
Posted 14 May 2010 - 02:31 AM

Hello there  Welcome to the GeeksToGo forums.
Welcome to the GeeksToGo forums.
My name is NeonFx. I'll be glad to help you with your computer problems. Logs can take some time to research, so please be patient with me.
Please note the following:
Step 1
Download OTS to your Desktop
Please attach the log in your next post. To do so click on the blue "Add Reply" button and click on the "Browse.." button under "Manage Current Attachments"
To ensure that I get all the information this log will need to be attached. If it is too large to attach then upload it to Dropio and post the sharing link/url (The Drop's URL will be similar to : http:://drop.io/daerk)
Step 2
 GMER Rootkit Scanner
GMER Rootkit Scanner
Please download GMER from one of the following locations and save it to your desktop:
If you have trouble running GMER, please try running it in Safe Mode. To get to Safe Mode you'll need to repeatedly tap the F8 key on your keyboard as you turn your computer on until a black and white menu appears with the option.
If you continue to have trouble with it, try running it without the "Files" scan checked.
Again, if the results are really long, please attach them using the instructions I gave you at the end of step 1. This is to avoid having to scroll down the page too much and make the space cleaner.
My name is NeonFx. I'll be glad to help you with your computer problems. Logs can take some time to research, so please be patient with me.
Please note the following:
- The fixes are specific to your problem and should only be used on this machine.
- Please continue to review my answers until I tell you your machine appears to be clean. Absence of symptoms does not necessarily mean that the system is completely clean.
- It's often worth reading through these instructions and printing them for ease of reference. I may ask you to boot into Safe Mode where you will be unable to follow my instructions online.
- If you don't know or understand something, please don't hesitate to say or ask!! It's better to be sure and safe than sorry.
- Please reply to this thread. Do not start a new topic.
Step 1
Download OTS to your Desktop
- Close ALL OTHER PROGRAMS.
- Double-click on OTS.exe to start the program.
- Check the box that says Scan All Users
- Under Basic Scans please change the radio button under Registry from Safe List to All.
- Under Additional Scans check the following:
- Reg - Desktop Components
- Reg - Disabled MS Config Items
- Reg - NetSvcs
- Reg - Shell Spawning
- Reg - Uninstall List
- File - Lop Check
- File - Purity Scan
- Evnt - EvtViewer (last 10)
- Please paste the contents of the following codebox into the Custom Scans box at the bottom
%SYSTEMDRIVE%\*.exe /md5start eventlog.dll scecli.dll netlogon.dll cngaudit.dll sceclt.dll ntelogon.dll logevent.dll iaStor.sys nvstor.sys atapi.sys IdeChnDr.sys viasraid.sys AGP440.sys vaxscsi.sys nvatabus.sys viamraid.sys nvata.sys nvgts.sys iastorv.sys nvatabus.sys si3112.sys viadsk.sys ViPrt.sys eNetHook.dll ahcix86.sys KR10N.sys /md5stop %systemroot%\*. /mp /s CREATERESTOREPOINT
- Now click the Run Scan button on the toolbar.
- Let it run unhindered until it finishes.
- When the scan is complete Notepad will open with the report file loaded in it.
- Click the Format menu and make sure that Wordwrap is not checked. If it is then click on it to uncheck it.
Please attach the log in your next post. To do so click on the blue "Add Reply" button and click on the "Browse.." button under "Manage Current Attachments"
To ensure that I get all the information this log will need to be attached. If it is too large to attach then upload it to Dropio and post the sharing link/url (The Drop's URL will be similar to : http:://drop.io/daerk)
Step 2
Please download GMER from one of the following locations and save it to your desktop:
- Main Mirror
This version will download a randomly named file (Recommended) - Zipped Mirror
This version will download a zip file you will need to extract first. If you use this mirror, please extract the zip file to your desktop.
- Disconnect from the Internet and close all running programs. Make sure you disable your security programs as well, as they may interfere with the program.
- Double-click on the randomly named GMER file (i.e. n7gmo46c.exe) and allow the gmer.sys driver to load if asked.
- Note: If you downloaded the zipped version, extract the file to its own folder such as C:\gmer and then double-click on gmer.exe.

- GMER will open to the Rootkit/Malware tab and perform an automatic quick scan when first run. (do not use the computer while the scan is in progress)
- If you receive a WARNING!!! about rootkit activity and are asked to fully scan your system...click NO.
- Now click the Scan button. If you see a rootkit warning window, click OK.
- When the scan is finished, click the Save... button to save the scan results to your Desktop. Save the file as gmer.log.
- Click the Copy button and paste the results into your next reply.
- Exit GMER and re-enable your security programs when done.
If you have trouble running GMER, please try running it in Safe Mode. To get to Safe Mode you'll need to repeatedly tap the F8 key on your keyboard as you turn your computer on until a black and white menu appears with the option.
If you continue to have trouble with it, try running it without the "Files" scan checked.
Again, if the results are really long, please attach them using the instructions I gave you at the end of step 1. This is to avoid having to scroll down the page too much and make the space cleaner.
#3

 Posted 14 May 2010 - 09:36 PM
Posted 14 May 2010 - 09:36 PM

Hi NeonFx,
Thanks for helping me with this issue.
hsartin
Thanks for helping me with this issue.
hsartin
Attached Files
#4

 Posted 14 May 2010 - 09:49 PM
Posted 14 May 2010 - 09:49 PM

Hi NeonFx,
Here is the log file produced by GMER:
GMER 1.0.15.15281 - http://www.gmer.net
Rootkit quick scan 2010-05-14 20:42:59
Windows 5.1.2600 Service Pack 3
Running: jz2fqp7h.exe; Driver: C:\DOCUME~1\Owner\LOCALS~1\Temp\uxldipob.sys
---- System - GMER 1.0.15 ----
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ZwCreateProcessEx [0xB8107AC6]
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ZwCreateSection [0xB81078EA]
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ZwLoadDriver [0xB8107A24]
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) NtCreateSection
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ObInsertObject
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ObMakeTemporaryObject
---- Devices - GMER 1.0.15 ----
Device \FileSystem\Ntfs \Ntfs aswSP.SYS (avast! self protection module/ALWIL Software)
AttachedDevice \FileSystem\Ntfs \Ntfs aswMon2.SYS (avast! File System Filter Driver for Windows XP/ALWIL Software)
Device \FileSystem\Fastfat \Fat aswSP.SYS (avast! self protection module/ALWIL Software)
AttachedDevice \FileSystem\Fastfat \Fat fltmgr.sys (Microsoft Filesystem Filter Manager/Microsoft Corporation)
AttachedDevice \FileSystem\Fastfat \Fat aswMon2.SYS (avast! File System Filter Driver for Windows XP/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Ip SYMTDI.SYS (Network Dispatch Driver/Symantec Corporation)
AttachedDevice \Driver\Tcpip \Device\Ip aswRdr.SYS (avast! TDI RDR Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Ip aswTdi.SYS (avast! TDI Filter Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Tcp aswTdi.SYS (avast! TDI Filter Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Tcp SYMTDI.SYS (Network Dispatch Driver/Symantec Corporation)
AttachedDevice \Driver\Tcpip \Device\Tcp aswRdr.SYS (avast! TDI RDR Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Udp aswTdi.SYS (avast! TDI Filter Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Udp SYMTDI.SYS (Network Dispatch Driver/Symantec Corporation)
AttachedDevice \Driver\Tcpip \Device\Udp aswRdr.SYS (avast! TDI RDR Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\RawIp aswTdi.SYS (avast! TDI Filter Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\RawIp SYMTDI.SYS (Network Dispatch Driver/Symantec Corporation)
Device -> \Driver\atapi \Device\Harddisk0\DR0 8A412EE4
---- Files - GMER 1.0.15 ----
File C:\WINDOWS\system32\drivers\atapi.sys suspicious modification
---- EOF - GMER 1.0.15 ----
Here is the log file produced by GMER:
GMER 1.0.15.15281 - http://www.gmer.net
Rootkit quick scan 2010-05-14 20:42:59
Windows 5.1.2600 Service Pack 3
Running: jz2fqp7h.exe; Driver: C:\DOCUME~1\Owner\LOCALS~1\Temp\uxldipob.sys
---- System - GMER 1.0.15 ----
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ZwCreateProcessEx [0xB8107AC6]
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ZwCreateSection [0xB81078EA]
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ZwLoadDriver [0xB8107A24]
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) NtCreateSection
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ObInsertObject
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/ALWIL Software) ObMakeTemporaryObject
---- Devices - GMER 1.0.15 ----
Device \FileSystem\Ntfs \Ntfs aswSP.SYS (avast! self protection module/ALWIL Software)
AttachedDevice \FileSystem\Ntfs \Ntfs aswMon2.SYS (avast! File System Filter Driver for Windows XP/ALWIL Software)
Device \FileSystem\Fastfat \Fat aswSP.SYS (avast! self protection module/ALWIL Software)
AttachedDevice \FileSystem\Fastfat \Fat fltmgr.sys (Microsoft Filesystem Filter Manager/Microsoft Corporation)
AttachedDevice \FileSystem\Fastfat \Fat aswMon2.SYS (avast! File System Filter Driver for Windows XP/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Ip SYMTDI.SYS (Network Dispatch Driver/Symantec Corporation)
AttachedDevice \Driver\Tcpip \Device\Ip aswRdr.SYS (avast! TDI RDR Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Ip aswTdi.SYS (avast! TDI Filter Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Tcp aswTdi.SYS (avast! TDI Filter Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Tcp SYMTDI.SYS (Network Dispatch Driver/Symantec Corporation)
AttachedDevice \Driver\Tcpip \Device\Tcp aswRdr.SYS (avast! TDI RDR Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Udp aswTdi.SYS (avast! TDI Filter Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\Udp SYMTDI.SYS (Network Dispatch Driver/Symantec Corporation)
AttachedDevice \Driver\Tcpip \Device\Udp aswRdr.SYS (avast! TDI RDR Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\RawIp aswTdi.SYS (avast! TDI Filter Driver/ALWIL Software)
AttachedDevice \Driver\Tcpip \Device\RawIp SYMTDI.SYS (Network Dispatch Driver/Symantec Corporation)
Device -> \Driver\atapi \Device\Harddisk0\DR0 8A412EE4
---- Files - GMER 1.0.15 ----
File C:\WINDOWS\system32\drivers\atapi.sys suspicious modification
---- EOF - GMER 1.0.15 ----
#5

 Posted 14 May 2010 - 09:50 PM
Posted 14 May 2010 - 09:50 PM

Good job. I can see it now 
Let's do this:
NOTE: ComboFix should NOT be used without supervision by someone trained in its use. It does a whole lot more to a system than just remove infected files.
Download ComboFix from one of these locations:
Link 1
Link 2
* IMPORTANT !!! Save ComboFix.exe to your Desktop
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
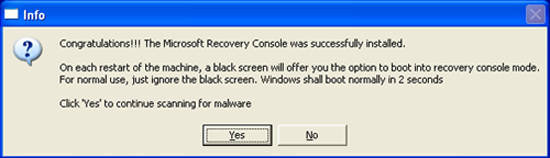
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt in your next reply.
Notes:
1. Do not mouse-click Combofix's window while it is running. That may cause it to stall.
2. ComboFix may reset a number of Internet Explorer's settings, including making I-E the default browser.
3. Combofix prevents autorun of ALL CD, floppy and USB devices to assist with malware removal & increase security. If this is an issue or makes it difficult for you please let me know. A increasing number of infections are spreading using Autoplay and leaving it disabled is a good idea.
4. CF disconnects your machine from the internet. The connection is automatically restored before CF completes its run. If CF runs into difficulty and terminates prematurely, the connection can be manually restored by restarting your machine.
Let's do this:
NOTE: ComboFix should NOT be used without supervision by someone trained in its use. It does a whole lot more to a system than just remove infected files.
Download ComboFix from one of these locations:
Link 1
Link 2
* IMPORTANT !!! Save ComboFix.exe to your Desktop
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools. Note: If you are having difficulty properly disabling your protective programs, or are unsure as to what programs need to be disabled, please refer to the information available through this link : Disabling Security Programs
- Double click on ComboFix.exe & follow the prompts.
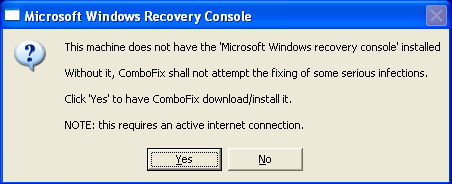
Note: Combofix will run without the Recovery Console installed. - As part of it's process, ComboFix will check to see if the Microsoft Windows Recovery Console is installed. With malware infections being as they are today, it's strongly recommended to have this pre-installed on your machine before doing any malware removal. It will allow you to boot up into a special recovery/repair mode that will allow us to more easily help you should your computer have a problem after an attempted removal of malware.
- Follow the prompts to allow ComboFix to download and install the Microsoft Windows Recovery Console, and when prompted, agree to the End-User License Agreement to install the Microsoft Windows Recovery Console.
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
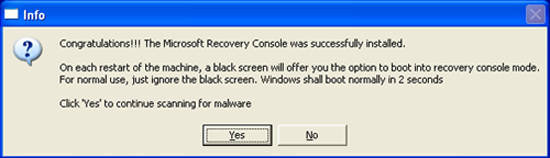
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt in your next reply.
Notes:
1. Do not mouse-click Combofix's window while it is running. That may cause it to stall.
2. ComboFix may reset a number of Internet Explorer's settings, including making I-E the default browser.
3. Combofix prevents autorun of ALL CD, floppy and USB devices to assist with malware removal & increase security. If this is an issue or makes it difficult for you please let me know. A increasing number of infections are spreading using Autoplay and leaving it disabled is a good idea.
4. CF disconnects your machine from the internet. The connection is automatically restored before CF completes its run. If CF runs into difficulty and terminates prematurely, the connection can be manually restored by restarting your machine.
#6

 Posted 14 May 2010 - 11:21 PM
Posted 14 May 2010 - 11:21 PM

The ComboFix log file is attached.
Attached Files
#7

 Posted 18 May 2010 - 04:54 PM
Posted 18 May 2010 - 04:54 PM

I'm sorry. I didn't realize you had responded.
The problem should be fixed after running that. Are you still experiencing problems?
Please run OTS again following the same instructions I gave you earlier so that I can see what has changed.
The problem should be fixed after running that. Are you still experiencing problems?
Please run OTS again following the same instructions I gave you earlier so that I can see what has changed.
#8

 Posted 19 May 2010 - 07:44 AM
Posted 19 May 2010 - 07:44 AM

I haven't experienced any redirects lately--so I think it worked. The OTS log file is attached.
Attached Files
Edited by hsartin, 19 May 2010 - 07:46 AM.
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:














 Sign In
Sign In Create Account
Create Account

