Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]
Started by
John Dont
, Jun 03 2010 11:24 PM
#16
![Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]: post #16](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 June 2010 - 08:21 PM
Posted 08 June 2010 - 08:21 PM

#17
![Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]: post #17](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 June 2010 - 09:00 AM
Posted 09 June 2010 - 09:00 AM

Here's the log from my second ESET scan:
ESETSmartInstaller@High as downloader log:
all ok
# version=7
# OnlineScannerApp.exe=1.0.0.1
# OnlineScanner.ocx=1.0.0.6211
# api_version=3.0.2
# EOSSerial=906894f00406a246a98c25e4988212a3
# end=finished
# remove_checked=true
# archives_checked=false
# unwanted_checked=true
# unsafe_checked=false
# antistealth_checked=true
# utc_time=2010-06-09 02:53:43
# local_time=2010-06-09 10:53:43 (-0500, Eastern Daylight Time)
# country="United States"
# lang=1033
# osver=5.1.2600 NT Service Pack 3
# compatibility_mode=768 16777215 100 0 64635 64635 0 0
# compatibility_mode=1024 16777215 100 0 16517903 16517903 0 0
# compatibility_mode=3584 16777191 100 0 0 0 0 0
# compatibility_mode=8192 67108863 100 0 0 0 0 0
# scanned=115922
# found=0
# cleaned=0
# scan_time=5706
ESETSmartInstaller@High as downloader log:
all ok
# version=7
# OnlineScannerApp.exe=1.0.0.1
# OnlineScanner.ocx=1.0.0.6211
# api_version=3.0.2
# EOSSerial=906894f00406a246a98c25e4988212a3
# end=finished
# remove_checked=true
# archives_checked=false
# unwanted_checked=true
# unsafe_checked=false
# antistealth_checked=true
# utc_time=2010-06-09 02:53:43
# local_time=2010-06-09 10:53:43 (-0500, Eastern Daylight Time)
# country="United States"
# lang=1033
# osver=5.1.2600 NT Service Pack 3
# compatibility_mode=768 16777215 100 0 64635 64635 0 0
# compatibility_mode=1024 16777215 100 0 16517903 16517903 0 0
# compatibility_mode=3584 16777191 100 0 0 0 0 0
# compatibility_mode=8192 67108863 100 0 0 0 0 0
# scanned=115922
# found=0
# cleaned=0
# scan_time=5706
#18
![Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]: post #18](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 June 2010 - 05:04 PM
Posted 09 June 2010 - 05:04 PM

that all looks good, just a couple of things before we wrap this up:
====STEP 1====
try and run a GMER scan as per: go to http://www.geekstogo...uide-t2852.html and run GMER Rootkit Scanner in Step Four: Rootkit Detection
====STEP 2====
lets scan that file, i am quite sure it is fine, looks like it is from Fortinet Inc.
In your next reply could i see:
1. the GMER scan if you can run it
2. the virscan log or link
3. some idea of how your machine is running now
The text from these files may exceed the maximum post length for this forum. Hence, you may need to post the information over 2 or more posts.
andrewuk
====STEP 1====
try and run a GMER scan as per: go to http://www.geekstogo...uide-t2852.html and run GMER Rootkit Scanner in Step Four: Rootkit Detection
====STEP 2====
lets scan that file, i am quite sure it is fine, looks like it is from Fortinet Inc.
- Please go to VirSCAN.org FREE on-line scan service
- Copy and paste the following file path into the "Suspicious files to scan"box on the top of the page (you may have to use the browse button):
- c:\windows\system32\drivers\pppop.sys
- Click on the Upload button
- Once the Scan is completed, click on the "Copy to Clipboard" button. This will copy the link of the report into the Clipboard. . . . . if the copy function does not work then copy the url link in your reply.
- Paste the contents of the Clipboard in your next reply (you will need to paste the link onto a notepad before you do the other scans below, else the contents of your clipboard will be written over with the new links).
In your next reply could i see:
1. the GMER scan if you can run it
2. the virscan log or link
3. some idea of how your machine is running now
The text from these files may exceed the maximum post length for this forum. Hence, you may need to post the information over 2 or more posts.
andrewuk
#19
![Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]: post #19](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 June 2010 - 09:57 AM
Posted 10 June 2010 - 09:57 AM

Hello,
1. GMER locked up again. However, I ran Rootkit Revealer about ten days ago and it only displayed about 5 files, all of which seemed safe to me. My gut tells me there are no rootkit problems; I'm sure that helps a lot haha.
2. pppop.sys is safe (as is pppop64.sys) http://virscan.org/r...5b3f9dc728.html
3. My system is running great! I haven't seen an intrusion attempt or popup since running ComboFix. Also, my LocalService and NetworkService folders have reappeared!
I want to thank you for all you've done so far andrewuk, you've been a great help. It seems to me like the only thing left to do is clear out the quarantined files?
1. GMER locked up again. However, I ran Rootkit Revealer about ten days ago and it only displayed about 5 files, all of which seemed safe to me. My gut tells me there are no rootkit problems; I'm sure that helps a lot haha.
2. pppop.sys is safe (as is pppop64.sys) http://virscan.org/r...5b3f9dc728.html
3. My system is running great! I haven't seen an intrusion attempt or popup since running ComboFix. Also, my LocalService and NetworkService folders have reappeared!
I want to thank you for all you've done so far andrewuk, you've been a great help. It seems to me like the only thing left to do is clear out the quarantined files?
#20
![Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]: post #20](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 June 2010 - 10:07 AM
Posted 10 June 2010 - 10:07 AM

we should do at least one complete rootkit scan here given there was rootkit activity on your machine:
Download RootRepeal from one of the following locations and save it to your desktop:Link 1
Link 2
Link 3
To attach a file, do the following:
Download RootRepeal from one of the following locations and save it to your desktop:Link 1
Link 2
Link 3
- Double click
 to start the program
to start the program - Click on the Report tab at the bottom of the program window
- Click the
 button
button - In the Select Scan dialog, check:
- Drivers
- Files
- Processes
- SSDT
- Stealth Objects
- Hidden Services
- Shadow SSDT
- Click the OK button
- In the next dialog, select all drives showing
- Click OK to start the scan
Note: The scan can take some time. DO NOT run any other programs while the scan is running
- When the scan is complete, click the
 button and save the report to your Desktop as RootRepeal.txt
button and save the report to your Desktop as RootRepeal.txt - Go to File, then Exit to close the program
To attach a file, do the following:
- Click Add Reply
- Under the reply panel is the Attachments Panel
- Browse for the attachment file you want to upload, then click the green Upload button
- Once it has uploaded, click the Manage Current Attachments drop down box
- Click on
 to insert the attachment into your post
to insert the attachment into your post
#21
![Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]: post #21](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 June 2010 - 11:00 AM
Posted 10 June 2010 - 11:00 AM

ROOTREPEAL © AD, 2007-2009
==================================================
Scan Start Time: 2010/06/10 12:47
Program Version: Version 1.3.5.0
Windows Version: Windows XP SP3
==================================================
Drivers
-------------------
Name: dump_atapi.sys
Image Path: C:\WINDOWS\System32\Drivers\dump_atapi.sys
Address: 0xA9A3D000 Size: 98304 File Visible: No Signed: -
Status: -
Name: dump_WMILIB.SYS
Image Path: C:\WINDOWS\System32\Drivers\dump_WMILIB.SYS
Address: 0xF7AC0000 Size: 8192 File Visible: No Signed: -
Status: -
Name: rootrepeal.sys
Image Path: C:\WINDOWS\system32\drivers\rootrepeal.sys
Address: 0xA8465000 Size: 49152 File Visible: No Signed: -
Status: -
Hidden/Locked Files
-------------------
Path: C:\hiberfil.sys
Status: Locked to the Windows API!
SSDT
-------------------
#: 012 Function Name: NtAlertResumeThread
Status: Hooked by "<unknown>" at address 0x86ad45b8
#: 013 Function Name: NtAlertThread
Status: Hooked by "<unknown>" at address 0x86aa66f8
#: 017 Function Name: NtAllocateVirtualMemory
Status: Hooked by "<unknown>" at address 0x867addf0
#: 019 Function Name: NtAssignProcessToJobObject
Status: Hooked by "<unknown>" at address 0x866b9a78
#: 031 Function Name: NtConnectPort
Status: Hooked by "<unknown>" at address 0x866b6148
#: 041 Function Name: NtCreateKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec5210
#: 043 Function Name: NtCreateMutant
Status: Hooked by "<unknown>" at address 0x8672fd00
#: 052 Function Name: NtCreateSymbolicLinkObject
Status: Hooked by "<unknown>" at address 0x86a2e5a0
#: 053 Function Name: NtCreateThread
Status: Hooked by "<unknown>" at address 0x86721cb0
#: 057 Function Name: NtDebugActiveProcess
Status: Hooked by "<unknown>" at address 0x86a3e818
#: 063 Function Name: NtDeleteKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec5490
#: 065 Function Name: NtDeleteValueKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec59f0
#: 068 Function Name: NtDuplicateObject
Status: Hooked by "<unknown>" at address 0x867907d0
#: 083 Function Name: NtFreeVirtualMemory
Status: Hooked by "<unknown>" at address 0x86a37740
#: 089 Function Name: NtImpersonateAnonymousToken
Status: Hooked by "<unknown>" at address 0x867c5e50
#: 091 Function Name: NtImpersonateThread
Status: Hooked by "<unknown>" at address 0x86788e50
#: 097 Function Name: NtLoadDriver
Status: Hooked by "<unknown>" at address 0x86b4e0e0
#: 108 Function Name: NtMapViewOfSection
Status: Hooked by "<unknown>" at address 0x86a375a0
#: 114 Function Name: NtOpenEvent
Status: Hooked by "<unknown>" at address 0x867a8e50
#: 119 Function Name: NtOpenKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec57a0
#: 122 Function Name: NtOpenProcess
Status: Hooked by "<unknown>" at address 0x86790a70
#: 123 Function Name: NtOpenProcessToken
Status: Hooked by "<unknown>" at address 0x86480128
#: 125 Function Name: NtOpenSection
Status: Hooked by "<unknown>" at address 0x86b39d58
#: 128 Function Name: NtOpenThread
Status: Hooked by "<unknown>" at address 0x86790920
#: 137 Function Name: NtProtectVirtualMemory
Status: Hooked by "<unknown>" at address 0x86737870
#: 206 Function Name: NtResumeThread
Status: Hooked by "<unknown>" at address 0x866aa3f8
#: 213 Function Name: NtSetContextThread
Status: Hooked by "<unknown>" at address 0x86ac2840
#: 228 Function Name: NtSetInformationProcess
Status: Hooked by "<unknown>" at address 0x86a37308
#: 240 Function Name: NtSetSystemInformation
Status: Hooked by "<unknown>" at address 0x86a62e50
#: 247 Function Name: NtSetValueKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec5c40
#: 253 Function Name: NtSuspendProcess
Status: Hooked by "<unknown>" at address 0x867d1e50
#: 254 Function Name: NtSuspendThread
Status: Hooked by "<unknown>" at address 0x86727388
#: 257 Function Name: NtTerminateProcess
Status: Hooked by "<unknown>" at address 0x864af128
#: 258 Function Name: NtTerminateThread
Status: Hooked by "<unknown>" at address 0x867d12c8
#: 267 Function Name: NtUnmapViewOfSection
Status: Hooked by "<unknown>" at address 0x86462128
#: 277 Function Name: NtWriteVirtualMemory
Status: Hooked by "<unknown>" at address 0x867ada60
Shadow SSDT
-------------------
#: 307 Function Name: NtUserAttachThreadInput
Status: Hooked by "<unknown>" at address 0x866b6b28
#: 383 Function Name: NtUserGetAsyncKeyState
Status: Hooked by "<unknown>" at address 0x869ecbd8
#: 414 Function Name: NtUserGetKeyboardState
Status: Hooked by "<unknown>" at address 0x8678a470
#: 416 Function Name: NtUserGetKeyState
Status: Hooked by "<unknown>" at address 0x867c7b28
#: 428 Function Name: NtUserGetRawInputData
Status: Hooked by "<unknown>" at address 0x86d50d40
#: 460 Function Name: NtUserMessageCall
Status: Hooked by "<unknown>" at address 0x86a051f0
#: 475 Function Name: NtUserPostMessage
Status: Hooked by "<unknown>" at address 0x86d4b3a0
#: 476 Function Name: NtUserPostThreadMessage
Status: Hooked by "<unknown>" at address 0x86ce4f00
#: 549 Function Name: NtUserSetWindowsHookEx
Status: Hooked by "<unknown>" at address 0x86d47138
#: 552 Function Name: NtUserSetWinEventHook
Status: Hooked by "<unknown>" at address 0x86ce68a8
==EOF==
==================================================
Scan Start Time: 2010/06/10 12:47
Program Version: Version 1.3.5.0
Windows Version: Windows XP SP3
==================================================
Drivers
-------------------
Name: dump_atapi.sys
Image Path: C:\WINDOWS\System32\Drivers\dump_atapi.sys
Address: 0xA9A3D000 Size: 98304 File Visible: No Signed: -
Status: -
Name: dump_WMILIB.SYS
Image Path: C:\WINDOWS\System32\Drivers\dump_WMILIB.SYS
Address: 0xF7AC0000 Size: 8192 File Visible: No Signed: -
Status: -
Name: rootrepeal.sys
Image Path: C:\WINDOWS\system32\drivers\rootrepeal.sys
Address: 0xA8465000 Size: 49152 File Visible: No Signed: -
Status: -
Hidden/Locked Files
-------------------
Path: C:\hiberfil.sys
Status: Locked to the Windows API!
SSDT
-------------------
#: 012 Function Name: NtAlertResumeThread
Status: Hooked by "<unknown>" at address 0x86ad45b8
#: 013 Function Name: NtAlertThread
Status: Hooked by "<unknown>" at address 0x86aa66f8
#: 017 Function Name: NtAllocateVirtualMemory
Status: Hooked by "<unknown>" at address 0x867addf0
#: 019 Function Name: NtAssignProcessToJobObject
Status: Hooked by "<unknown>" at address 0x866b9a78
#: 031 Function Name: NtConnectPort
Status: Hooked by "<unknown>" at address 0x866b6148
#: 041 Function Name: NtCreateKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec5210
#: 043 Function Name: NtCreateMutant
Status: Hooked by "<unknown>" at address 0x8672fd00
#: 052 Function Name: NtCreateSymbolicLinkObject
Status: Hooked by "<unknown>" at address 0x86a2e5a0
#: 053 Function Name: NtCreateThread
Status: Hooked by "<unknown>" at address 0x86721cb0
#: 057 Function Name: NtDebugActiveProcess
Status: Hooked by "<unknown>" at address 0x86a3e818
#: 063 Function Name: NtDeleteKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec5490
#: 065 Function Name: NtDeleteValueKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec59f0
#: 068 Function Name: NtDuplicateObject
Status: Hooked by "<unknown>" at address 0x867907d0
#: 083 Function Name: NtFreeVirtualMemory
Status: Hooked by "<unknown>" at address 0x86a37740
#: 089 Function Name: NtImpersonateAnonymousToken
Status: Hooked by "<unknown>" at address 0x867c5e50
#: 091 Function Name: NtImpersonateThread
Status: Hooked by "<unknown>" at address 0x86788e50
#: 097 Function Name: NtLoadDriver
Status: Hooked by "<unknown>" at address 0x86b4e0e0
#: 108 Function Name: NtMapViewOfSection
Status: Hooked by "<unknown>" at address 0x86a375a0
#: 114 Function Name: NtOpenEvent
Status: Hooked by "<unknown>" at address 0x867a8e50
#: 119 Function Name: NtOpenKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec57a0
#: 122 Function Name: NtOpenProcess
Status: Hooked by "<unknown>" at address 0x86790a70
#: 123 Function Name: NtOpenProcessToken
Status: Hooked by "<unknown>" at address 0x86480128
#: 125 Function Name: NtOpenSection
Status: Hooked by "<unknown>" at address 0x86b39d58
#: 128 Function Name: NtOpenThread
Status: Hooked by "<unknown>" at address 0x86790920
#: 137 Function Name: NtProtectVirtualMemory
Status: Hooked by "<unknown>" at address 0x86737870
#: 206 Function Name: NtResumeThread
Status: Hooked by "<unknown>" at address 0x866aa3f8
#: 213 Function Name: NtSetContextThread
Status: Hooked by "<unknown>" at address 0x86ac2840
#: 228 Function Name: NtSetInformationProcess
Status: Hooked by "<unknown>" at address 0x86a37308
#: 240 Function Name: NtSetSystemInformation
Status: Hooked by "<unknown>" at address 0x86a62e50
#: 247 Function Name: NtSetValueKey
Status: Hooked by "C:\WINDOWS\system32\Drivers\SYMEVENT.SYS" at address 0xa9ec5c40
#: 253 Function Name: NtSuspendProcess
Status: Hooked by "<unknown>" at address 0x867d1e50
#: 254 Function Name: NtSuspendThread
Status: Hooked by "<unknown>" at address 0x86727388
#: 257 Function Name: NtTerminateProcess
Status: Hooked by "<unknown>" at address 0x864af128
#: 258 Function Name: NtTerminateThread
Status: Hooked by "<unknown>" at address 0x867d12c8
#: 267 Function Name: NtUnmapViewOfSection
Status: Hooked by "<unknown>" at address 0x86462128
#: 277 Function Name: NtWriteVirtualMemory
Status: Hooked by "<unknown>" at address 0x867ada60
Shadow SSDT
-------------------
#: 307 Function Name: NtUserAttachThreadInput
Status: Hooked by "<unknown>" at address 0x866b6b28
#: 383 Function Name: NtUserGetAsyncKeyState
Status: Hooked by "<unknown>" at address 0x869ecbd8
#: 414 Function Name: NtUserGetKeyboardState
Status: Hooked by "<unknown>" at address 0x8678a470
#: 416 Function Name: NtUserGetKeyState
Status: Hooked by "<unknown>" at address 0x867c7b28
#: 428 Function Name: NtUserGetRawInputData
Status: Hooked by "<unknown>" at address 0x86d50d40
#: 460 Function Name: NtUserMessageCall
Status: Hooked by "<unknown>" at address 0x86a051f0
#: 475 Function Name: NtUserPostMessage
Status: Hooked by "<unknown>" at address 0x86d4b3a0
#: 476 Function Name: NtUserPostThreadMessage
Status: Hooked by "<unknown>" at address 0x86ce4f00
#: 549 Function Name: NtUserSetWindowsHookEx
Status: Hooked by "<unknown>" at address 0x86d47138
#: 552 Function Name: NtUserSetWinEventHook
Status: Hooked by "<unknown>" at address 0x86ce68a8
==EOF==
#22
![Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]: post #22](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 June 2010 - 11:23 AM
Posted 10 June 2010 - 11:23 AM

Hello John Dont
congratulations, your logs are clean and another fix is in the can
the rootkit scan was clean, the malwarebytes scan and superantispyware scan was clean, as was ESET scan. those two bad files are quarantined / in the system restore which we will clear now.
in this post we will clear away the fix tools (this is so that should you ever be re-infected, you will download updated versions and it will also remove the quarantined Malware from your computer), reset your restore points (there will be infections lurking in there) and i will leave you with some ideas on how to enhance the protection of your machine against future infection.
====STEP 1====
Follow these steps to uninstall Combofix, some of the tools used in the removal of malware and to flush your system restore points
====STEP 2====
Double-click OTL to run it. (Vista users, please right click on OTListIt.exe and select "Run as an Administrator")
====IDEAS TO SPEED UP YOUR MACHINE====
this page http://users.telenet...owcomputer.html gives some good ideas on how to improve the efficiency of your machine and has one or two useful links to help you further.
====AND FINALLY====
The following is a list of free tools and utilities that I like to suggest to people. This list is full of great tools and utilities to help you understand how you got infected and how to keep from getting infected again.
best wishes
andrewuk
congratulations, your logs are clean and another fix is in the can
the rootkit scan was clean, the malwarebytes scan and superantispyware scan was clean, as was ESET scan. those two bad files are quarantined / in the system restore which we will clear now.
in this post we will clear away the fix tools (this is so that should you ever be re-infected, you will download updated versions and it will also remove the quarantined Malware from your computer), reset your restore points (there will be infections lurking in there) and i will leave you with some ideas on how to enhance the protection of your machine against future infection.
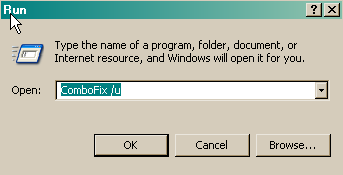
====STEP 1====
Follow these steps to uninstall Combofix, some of the tools used in the removal of malware and to flush your system restore points
- Click START then RUN
- Now type ComboFix /Uninstall in the runbox and click OK. Note the space between ComboFix and the /Uninstall, it needs to be there.
- You will be notified if combofix has been successfully removed
====STEP 2====
Double-click OTL to run it. (Vista users, please right click on OTListIt.exe and select "Run as an Administrator")
- Click the Clean up button and let the program run
- when prompted, click Yes to the reboot.
====IDEAS TO SPEED UP YOUR MACHINE====
this page http://users.telenet...owcomputer.html gives some good ideas on how to improve the efficiency of your machine and has one or two useful links to help you further.
====AND FINALLY====
The following is a list of free tools and utilities that I like to suggest to people. This list is full of great tools and utilities to help you understand how you got infected and how to keep from getting infected again.
- MBAM - Malware Bytes Anti Malware is an excellent tool for anyone's antimalware arsenal. This program should be updated and run often.
- SpywareBlaster - Great prevention tool to keep nasties from installing on your system.
- SpywareGuard - Works as a Spyware "Shield" to protect your computer from getting malware in the first place.
- IE-SpyAd - puts over 5000 sites in your restricted zone so you'll be protected when you visit innocent-looking sites that aren't actually innocent at all.
- ATF Cleaner - Cleans temporary files from IE and Windows, empties the recycle bin and more. Great tool to help speed up your computer and knock out those nasties that like to reside in the temp folders.
- Windows Updates - It is very important to make sure that both Internet Explorer and Windows are kept current with the latest critical security patches from Microsoft. To do this just start Internet Explorer and select Tools > Windows Update, and follow the online instructions from there.
- Digsby or Miranda-IM - These are Malware free Instant Messenger programs which allow you to connect to multiple IM services in one program! (AOL, Yahoo, ICQ, IRC, MSN)
- Keep a backup of your important files - Now, more than ever, it's especially important to protect your digital files and memories. This article is full of good information on alternatives for home backup solutions.
- FireFox - Alternate web browser. Open source and quick, Firefox is usually the first thing I install on a new system.
- NoScript - Addon for Firefox that stops all scripts from running on websites. Stops malicious software from invading via flash, java, javascript, and many other entry points.
best wishes
andrewuk
#23
![Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]: post #23](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 June 2010 - 12:38 PM
Posted 10 June 2010 - 12:38 PM

Thank you so much andrewuk!!! I couldn't have asked for better help from a pay service, plus I ended up learning a lot from this whole process as well. I'd definitely recommend geekstogo, it's a terrific site.
I can't thank you enough for sticking with me through the past few days, my computer is clean now!
--John Dont
I can't thank you enough for sticking with me through the past few days, my computer is clean now!
--John Dont
#24
![Winsecure2009.com, Popups, Intrusion Attempts, pppop64 [Solved]: post #24](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 13 June 2010 - 08:25 AM
Posted 13 June 2010 - 08:25 AM

Since this issue appears to be resolved ... this Topic has been closed. Glad we could help. 
If you're the topic starter, and need this topic reopened, please contact a staff member with the address of the thread.
Everyone else please begin a New Topic.
If you're the topic starter, and need this topic reopened, please contact a staff member with the address of the thread.
Everyone else please begin a New Topic.
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked




 Sign In
Sign In Create Account
Create Account

