I have an expired trial version of ESET Smart Security. The signatures aren't up to date, but the firewall and everything else still works.
A couple of days ago, ESET alerted me that an unknown exe was trying to access the internet. I denied it access, closed all my browser tabs, and went looking for it:
C:\documents and settings\ default\application data\ylanukmgh\bkkwhygtssd.exe
It had just been created within the last few minutes. I hadn't been intentionally downloading anything at the time.
A full system scan with ESET found no threats. I updated Pest Patrol the next day, and a full scan found no threats. Trend Micro Housecall found no threats. My computer wasn't doing anything suspicious, and I didn't receive any new firewall alerts, but the unknown exe was still there.
I used ESET's online scanner to do another full system scan, and it found several trojans and two "Spyware Protect" applications. It quarantined them.
I rebooted my computer, and got back on the internet. After a few minutes, a new window popped up for no reason, advertising "Betty Crocker Recipes" in my zip code. Nothing like this had happened up until then. A while later, another new window appeared saying I was being redirected to another site. The site I was redirected to had no content other than links to other sites. I used task manager to close out my browsing session on both occasions to prevent further infection.
I ran another ESET online scan overnight, and it found two more trojans.
I went to this forum, and a new window opened up for "Registry Defender 2010".
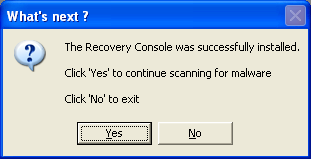
Following the steps in your malware guide, I ran TFC, ERUNT, and MBAM. MBAM found 10 infections in my registry and one other infected file. It needed a reboot to finish. I ran MBAM again, and it found no new threats. I did one more ESET online scan, and it found no new threats.
MBAM and GMER logs are pasted below.
I screwed up the order of running OTL. I ran it once before my last ESET scan and running GMER. I ran it again afterwards, but it didn't produce an "extras" log the second time. I've pasted the original two logs.
I haven't had any new pop ups since running MBAM, but I'd really like to make sure my system is clean now since I had so many infections that weren't doing anything to arouse my suspicion.
Thank you for your time!
Edit:
Edit:
I can't post the OTL logs. They are HUGE! If I try and paste everything at once, IE won't display the webpage. If I try and paste even one OTL log as an edit, I get a "loading" message from the forum forever. If I try and paste it as a reply, IE can't display the webpage after I submit the reply. I've been trying to do this for hours now.
I tried using Firefox, but it won't open because it says it's already running and not responding (this has never happened before, and still won't open after rebooting). I've gotten a notification about Windows Genuine the last few times I've tried to reboot. I've never gotten a notification about this before.
Edit:
MBAM LOG:
Malwarebytes' Anti-Malware 1.46
www.malwarebytes.org
Database version: 4052
Windows 5.1.2600 Service Pack 3
Internet Explorer 8.0.6001.18702
6/24/2010 6:25:52 PM
mbam-log-2010-06-24 (18-25-52).txt
Scan type: Quick scan
Objects scanned: 121035
Time elapsed: 16 minute(s), 7 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 10
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 1
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
HKEY_CLASSES_ROOT\dnscache.dnscacheobj (Trojan.BHO) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\dnscache.dnscacheobj.1 (Trojan.BHO) -> Quarantined and deleted successfully.
HKEY_CLASSES_ROOT\CLSID\{376892ae-1825-4e5f-9f85-23f9640051cc} (Trojan.BHO) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Stats\{376892ae-1825-4e5f-9f85-23f9640051cc} (Trojan.BHO) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Ext\Settings\{376892ae-1825-4e5f-9f85-23f9640051cc} (Trojan.BHO) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\{376892ae-1825-4e5f-9f85-23f9640051cc} (Trojan.BHO) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\avsuite (Rogue.AntivirusSuite) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\avsuite (Rogue.AntivirusSuite) -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\avsoft (Trojan.Fraudpack) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\avsoft (Trojan.Fraudpack) -> Quarantined and deleted successfully.
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
C:\Documents and Settings\default\oashdihasidhasuidhiasdhiashdiuasdhasd (Malware.Trace) -> Quarantined and deleted successfully.
Edit:
GMER LOG:
GMER 1.0.15.15281 - http://www.gmer.net
Rootkit scan 2010-06-25 01:50:15
Windows 5.1.2600 Service Pack 3
Running: gmer.exe; Driver: C:\DOCUME~1\default\LOCALS~1\Temp\kxdcrkow.sys
---- System - GMER 1.0.15 ----
SSDT 8281B8A0 ZwAssignProcessToJobObject
SSDT 8281ACB0 ZwOpenProcess
SSDT 8281B0D0 ZwOpenThread
SSDT 8281B6D0 ZwSuspendProcess
SSDT 8281B4F0 ZwSuspendThread
SSDT 8281AEE0 ZwTerminateProcess
SSDT 8281B310 ZwTerminateThread
---- User code sections - GMER 1.0.15 ----
.text C:\WINDOWS\Explorer.EXE[344] ntdll.dll!NtProtectVirtualMemory 7C90D6EE 5 Bytes JMP 00B7000A
.text C:\WINDOWS\Explorer.EXE[344] ntdll.dll!NtWriteVirtualMemory 7C90DFAE 5 Bytes JMP 00BD000A
.text C:\WINDOWS\Explorer.EXE[344] ntdll.dll!KiUserExceptionDispatcher 7C90E47C 5 Bytes JMP 00B6000C
.text C:\Program Files\ESET\ESET Smart Security\ekrn.exe[620] kernel32.dll!SetUnhandledExceptionFilter 7C84495D 4 Bytes [C2, 04, 00, 00]
.text C:\WINDOWS\System32\svchost.exe[1200] ntdll.dll!NtProtectVirtualMemory 7C90D6EE 5 Bytes JMP 0092000A
.text C:\WINDOWS\System32\svchost.exe[1200] ntdll.dll!NtWriteVirtualMemory 7C90DFAE 5 Bytes JMP 0093000A
.text C:\WINDOWS\System32\svchost.exe[1200] ntdll.dll!KiUserExceptionDispatcher 7C90E47C 5 Bytes JMP 0091000C
.text C:\WINDOWS\System32\svchost.exe[1200] USER32.dll!GetCursorPos 7E42974E 5 Bytes JMP 00EB000A
.text C:\WINDOWS\System32\svchost.exe[1200] ole32.dll!CoCreateInstance 7750057E 5 Bytes JMP 00EE000A
---- Devices - GMER 1.0.15 ----
AttachedDevice \FileSystem\Ntfs \Ntfs eamon.sys (Amon monitor/ESET)
Device \Driver\Tcpip \Device\Ip vsdatant.sys (TrueVector Device Driver/Zone Labs, LLC)
Device \Driver\Tcpip \Device\Tcp vsdatant.sys (TrueVector Device Driver/Zone Labs, LLC)
Device \Driver\Tcpip \Device\Udp vsdatant.sys (TrueVector Device Driver/Zone Labs, LLC)
Device \Driver\Tcpip \Device\RawIp vsdatant.sys (TrueVector Device Driver/Zone Labs, LLC)
Device \Driver\Tcpip \Device\IPMULTICAST vsdatant.sys (TrueVector Device Driver/Zone Labs, LLC)
AttachedDevice \FileSystem\Fastfat \Fat eamon.sys (Amon monitor/ESET)
Device -> \Driver\atapi \Device\Harddisk0\DR0 82EF1EC5
---- Threads - GMER 1.0.15 ----
Thread System [4:396] 82819930
---- Files - GMER 1.0.15 ----
File C:\WINDOWS\system32\drivers\atapi.sys suspicious modification
---- EOF - GMER 1.0.15 ----
Edited by Levan, 25 June 2010 - 03:27 AM.

 This topic is locked
This topic is locked














 Sign In
Sign In Create Account
Create Account

