Thanks so much! First is the OTL Log, followed by the ComboFix log. You're a lifesaver!
OTL Log
========== PROCESSES ==========
All processes killed
========== FILES ==========
C:\WINDOWS\System32\drivers\ikymzs.sys moved successfully.
========== COMMANDS ==========
OTL by OldTimer - Version 3.2.11.0 log created on 09042010_214708
Files\Folders moved on Reboot...
Registry entries deleted on Reboot...
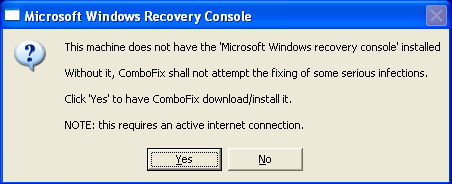
ComboFix 10-09-04.04 - Mommy 09/04/2010 22:09:26.1.2 - x86
Microsoft Windows XP Professional 5.1.2600.3.1252.1.1033.18.894.624 [GMT -4:00]
Running from: c:\documents and settings\Mommy\Desktop\ComboFix.exe
AV: Lavasoft Ad-Watch Live! Anti-Virus *On-access scanning disabled* (Updated) {A1C4F2E0-7FDE-4917-AFAE-013EFC3EDE33}
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
c:\documents and settings\Mommy\Local Settings\Application Data\Windows Server
c:\documents and settings\Mommy\Local Settings\Application Data\Windows Server\server.dat
c:\windows\msconfig32.exe
c:\windows\system32\BSTIEPrintCtl1.dll
c:\windows\system32\drivers\block.txt
c:\windows\system32\ico.ico
c:\windows\system32\vbzlib1.dll
D:\install.exe
Infected copy of c:\windows\system32\drivers\isapnp.sys was found and disinfected
Restored copy from - Kitty had a snack

.
((((((((((((((((((((((((((((((((((((((( Drivers/Services )))))))))))))))))))))))))))))))))))))))))))))))))
.
-------\Legacy_6TO4
-------\Service_6to4
((((((((((((((((((((((((( Files Created from 2010-08-05 to 2010-09-05 )))))))))))))))))))))))))))))))
.
2010-09-05 02:20 . 2010-09-05 02:20 -------- d-----w- c:\windows\LastGood
2010-09-05 01:21 . 2010-09-05 01:21 -------- dc----w- C:\_OTL
2010-09-04 15:47 . 2010-09-04 15:47 -------- d-----w- c:\documents and settings\Administrator\Local Settings\Application Data\Mozilla
2010-09-01 14:57 . 2010-09-01 15:00 -------- d-----w- c:\documents and settings\NetworkService\Local Settings\Application Data\Adobe
2010-08-29 23:46 . 2010-08-29 23:46 -------- d-----w- c:\windows\system32\msmq
2010-08-29 23:46 . 2010-08-29 23:47 -------- dc----w- C:\Inetpub
2010-08-29 22:33 . 2010-08-29 22:33 -------- d-----w- c:\documents and settings\Mommy\Local Settings\Application Data\Mozilla
2010-08-29 18:48 . 2010-08-29 18:57 -------- d-----w- c:\program files\Windows Live Safety Center
2010-08-29 17:42 . 2010-08-29 17:42 -------- d-----w- c:\documents and settings\All Users\Application Data\NOS
2010-08-29 17:42 . 2010-08-29 17:42 -------- d-----w- c:\program files\NOS
2010-08-28 22:57 . 2010-08-12 12:15 15880 ----a-w- c:\windows\system32\lsdelete.exe
2010-08-28 19:39 . 2010-08-12 12:15 64288 -c--a-w- c:\windows\system32\drivers\Lbd.sys
2010-08-28 19:39 . 2010-08-28 19:39 95024 ----a-w- c:\windows\system32\drivers\SBREDrv.sys
2010-08-28 19:16 . 2010-08-28 19:16 -------- d-----w- c:\documents and settings\Mommy\Local Settings\Application Data\Sunbelt Software
2010-08-28 19:14 . 2010-08-28 19:14 -------- d-----w- c:\program files\Google
2010-08-28 19:12 . 2010-08-28 19:39 -------- d-----w- c:\documents and settings\All Users\Application Data\Lavasoft
2010-08-28 19:12 . 2010-08-28 19:12 -------- d-----w- c:\program files\Lavasoft
2010-08-28 18:44 . 2010-08-28 18:44 -------- d-----w- c:\documents and settings\Mommy\Application Data\MSNInstaller
2010-08-28 17:54 . 2010-08-29 01:30 -------- d-----w- c:\windows\system32\MpEngineStore
2010-08-28 03:36 . 2010-08-28 03:36 -------- d-----w- c:\documents and settings\Mommy\Application Data\Malwarebytes
2010-08-28 03:35 . 2010-04-29 19:39 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2010-08-28 03:35 . 2010-08-28 03:35 -------- d-----w- c:\documents and settings\All Users\Application Data\Malwarebytes
2010-08-28 03:35 . 2010-08-28 03:35 -------- d-----w- c:\program files\Malwarebytes' Anti-Malware
2010-08-28 03:35 . 2010-04-29 19:39 20952 ----a-w- c:\windows\system32\drivers\mbam.sys
2010-08-27 23:19 . 2010-08-27 23:19 -------- d-----w- c:\documents and settings\All Users\Application Data\SUPERAntiSpyware.com
2010-08-27 23:17 . 2010-08-27 23:54 -------- d-----w- c:\program files\SUPERAntiSpyware
2010-08-27 23:17 . 2010-08-27 23:17 -------- d-----w- c:\documents and settings\Mommy\Application Data\SUPERAntiSpyware.com
2010-08-27 22:56 . 2008-04-14 09:39 6656 -c--a-w- c:\windows\system32\dllcache\fxsres.dll
2010-08-27 22:55 . 2008-04-14 09:42 142848 -c--a-w- c:\windows\system32\dllcache\fxsclnt.exe
2010-08-27 22:40 . 2010-08-27 22:40 -------- d-----w- c:\program files\WhoCrashed
2010-08-27 01:40 . 2010-08-27 01:40 -------- d-----w- c:\documents and settings\Administrator\Local Settings\Application Data\Apple
2010-08-27 01:13 . 2010-08-27 15:35 -------- d-----w- c:\documents and settings\Administrator\Application Data\.clamwin
2010-08-27 00:32 . 2010-08-27 00:32 -------- d--h--w- c:\windows\system32\GroupPolicy
2010-08-27 00:27 . 2010-08-27 00:27 -------- d-----w- c:\program files\Common Files\Wise Installation Wizard
2010-08-26 04:29 . 2010-08-28 19:14 -------- dc-h--w- c:\documents and settings\All Users\Application Data\{ECC164E0-3133-4C70-A831-F08DB2940F70}
2010-08-25 22:14 . 2010-08-25 22:15 -------- d-----w- c:\documents and settings\Administrator
2010-08-25 22:11 . 2010-08-28 15:20 -------- d-----w- c:\documents and settings\Mommy\Local Settings\Application Data\lgbvddeqj
2010-08-25 22:11 . 2010-08-28 15:20 -------- d-----w- c:\documents and settings\Mommy\Local Settings\Application Data\osgvdmqyu
2010-08-25 22:11 . 2010-08-27 15:38 -------- d-----w- c:\documents and settings\All Users\Application Data\Update
2010-08-25 22:06 . 2009-09-08 21:54 158720 ----a-w- c:\windows\system32\drivers\skybound.gecko.dll
2010-08-25 22:06 . 2010-08-26 21:41 -------- d-----w- c:\windows\system32\drivers\f
2010-08-25 22:06 . 2010-08-25 22:06 69992 ----a-w- c:\documents and settings\LocalService\Local Settings\Application Data\GDIPFONTCACHEV1.DAT
2010-08-25 22:05 . 2010-08-25 22:05 -------- d-----w- c:\windows\system32\system333
2010-08-25 22:05 . 2010-08-25 22:05 -------- d-----w- c:\windows\system32\weber
2010-08-23 00:29 . 2010-08-23 00:29 -------- d-----w- c:\documents and settings\Mommy\Application Data\Vast Studios
2010-08-23 00:18 . 2010-08-23 00:18 -------- d-----w- c:\windows\Nightfall Mysteries - The Asylum Conspiracy
2010-08-15 03:31 . 2010-08-15 03:31 -------- d-----w- c:\documents and settings\Mommy\Application Data\Silverback Productions
2010-08-15 01:23 . 2010-08-15 01:23 -------- d-----w- c:\documents and settings\All Users\Application Data\Exorcist DS 7
2010-08-10 22:28 . 2010-08-10 22:28 -------- d-----w- c:\documents and settings\Mommy\Application Data\ERS Game Studios
2010-08-10 22:25 . 2010-08-10 22:25 -------- d--h--w- c:\windows\PIF
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2010-09-02 22:36 . 2010-02-19 18:22 1324 ----a-w- c:\windows\system32\d3d9caps.dat
2010-09-02 21:34 . 2010-08-29 02:16 63488 ----a-w- c:\documents and settings\Mommy\Application Data\SUPERAntiSpyware.com\SUPERAntiSpyware\SDDLLS\SD10006.dll
2010-09-02 21:34 . 2010-08-27 23:19 117760 ----a-w- c:\documents and settings\Mommy\Application Data\SUPERAntiSpyware.com\SUPERAntiSpyware\SDDLLS\UIREPAIR.DLL
2010-09-02 20:58 . 2010-02-11 18:11 -------- d-----w- c:\program files\Coupons
2010-09-02 13:21 . 2010-02-09 01:33 70768 ----a-w- c:\documents and settings\Mommy\Local Settings\Application Data\GDIPFONTCACHEV1.DAT
2010-09-01 14:02 . 2010-02-09 02:07 -------- d--h--w- c:\program files\InstallShield Installation Information
2010-08-30 08:49 . 2010-02-22 22:24 -------- d---a-w- c:\documents and settings\All Users\Application Data\TEMP
2010-08-29 17:42 . 2010-08-29 17:42 77184 ----a-w- c:\documents and settings\All Users\Application Data\NOS\Adobe_Downloads\arh.exe
2010-08-28 19:08 . 2010-02-13 04:27 -------- d-----w- c:\documents and settings\Mommy\Application Data\BitComet
2010-08-28 18:44 . 2010-08-28 18:44 1244648 ----a-w- c:\documents and settings\Mommy\Application Data\MSNInstaller\msnauins.exe
2010-08-27 23:19 . 2010-08-27 23:19 52224 ----a-w- c:\documents and settings\Mommy\Application Data\SUPERAntiSpyware.com\SUPERAntiSpyware\SDDLLS\SD10005.dll
2010-08-27 23:11 . 2010-02-09 01:34 -------- d-----w- c:\program files\ClamWin
2010-08-27 17:23 . 2010-03-19 03:57 -------- d-----w- c:\program files\Microsoft Reader
2010-08-27 17:16 . 2010-05-23 20:12 -------- d-----w- c:\program files\FLAC
2010-08-27 16:50 . 2010-02-13 04:27 -------- d-----w- c:\program files\BitComet
2010-08-27 16:50 . 2010-03-03 02:37 -------- d-----w- c:\program files\Audio Workstation
2010-08-26 03:31 . 2010-08-25 22:06 35 ----a-w- c:\windows\system32\drivers\auth.txt
2010-08-25 22:06 . 2010-08-25 22:06 16896 ----a-w- c:\windows\system32\drivers\up.exe.old
2010-08-25 00:58 . 2010-07-31 20:24 22 ----a-w- c:\windows\popcinfot.dat
2010-08-24 02:11 . 2010-08-25 22:06 19456 ----a-w- c:\windows\system32\drivers\surfguard.exe.old
2010-08-24 02:11 . 2010-06-25 22:15 210944 ----a-w- c:\windows\system32\drivers\safesurf.old
2010-08-12 12:16 . 2010-08-28 19:14 2979848 -c--a-w- c:\documents and settings\All Users\Application Data\{ECC164E0-3133-4C70-A831-F08DB2940F70}\Ad-AwareInstall.exe
2010-08-05 03:15 . 2010-08-05 03:15 -------- d-----w- c:\documents and settings\Mommy\Application Data\runic games
2010-08-05 03:08 . 2010-08-05 03:08 -------- d-----w- c:\program files\Runic Games
2010-07-31 20:24 . 2010-07-31 20:24 0 ----a-w- c:\windows\popcreg.dat
2010-07-22 20:37 . 2010-07-22 20:37 -------- d-----w- c:\program files\Microsoft Silverlight
2010-07-20 08:04 . 2010-03-08 00:43 256 -c--a-w- c:\windows\system32\pool.bin
2010-07-20 07:49 . 2010-05-08 00:45 -------- d-----w- c:\documents and settings\Mommy\Application Data\calibre
2010-07-20 07:45 . 2010-02-13 04:37 -------- d-----w- c:\program files\ABC Amber LIT Converter
2010-06-30 12:31 . 2008-04-14 12:00 149504 ----a-w- c:\windows\system32\schannel.dll
2010-06-24 12:15 . 2008-04-14 12:00 832512 ----a-w- c:\windows\system32\wininet.dll
2010-06-24 12:15 . 2008-04-14 12:00 78336 ----a-w- c:\windows\system32\ieencode.dll
2010-06-24 12:15 . 2008-04-14 12:00 17408 ----a-w- c:\windows\system32\corpol.dll
2010-06-23 13:44 . 2008-04-14 12:00 1851904 ----a-w- c:\windows\system32\win32k.sys
2010-06-21 15:27 . 2008-04-14 12:00 354304 ----a-w- c:\windows\system32\drivers\srv.sys
2010-06-20 06:09 . 2010-06-20 06:09 10134 ----a-r- c:\documents and settings\Mommy\Application Data\Microsoft\Installer\{E3E71D07-CD27-46CB-8448-16D4FB29AA13}\ARPPRODUCTICON.exe
2010-06-17 14:03 . 2008-04-14 12:00 80384 ----a-w- c:\windows\system32\iccvid.dll
2010-06-14 14:31 . 2010-02-09 00:53 744448 ----a-w- c:\windows\pchealth\helpctr\binaries\helpsvc.exe
2010-06-14 07:41 . 2008-04-14 12:00 1172480 ----a-w- c:\windows\system32\msxml3.dll
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"SUPERAntiSpyware"="c:\program files\SUPERAntiSpyware\SUPERAntiSpyware.exe" [2010-08-27 2424560]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ClamWin"="c:\program files\ClamWin\bin\ClamTray.exe" [2010-08-20 86016]
"NvCplDaemon"="c:\windows\system32\NvCpl.dll" [2007-02-02 7933952]
"nwiz"="nwiz.exe" [2007-02-02 1622016]
"NvMediaCenter"="c:\windows\system32\NvMcTray.dll" [2007-02-02 81920]
"EKIJ5000StatusMonitor"="c:\windows\System32\spool\DRIVERS\W32X86\3\EKIJ5000MUI.exe" [2010-02-08 1634304]
[hkey_local_machine\software\microsoft\windows\currentversion\explorer\ShellExecuteHooks]
"{5AE067D3-9AFB-48E0-853A-EBB7F4A000DA}"= "c:\program files\SUPERAntiSpyware\SASSEH.DLL" [2008-05-13 77824]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\winlogon\notify\!SASWinLogon]
2009-09-03 18:21 548352 ----a-w- c:\program files\SUPERAntiSpyware\SASWINLO.dll
[HKEY_LOCAL_MACHINE\system\currentcontrolset\control\session manager]
BootExecute REG_MULTI_SZ \0lsdelete
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\Lavasoft Ad-Aware Service]
@="Service"
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusOverride"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\Network Diagnostic\\xpnetdiag.exe"=
"%windir%\\system32\\sessmgr.exe"=
"c:\\Program Files\\Yahoo!\\Messenger\\YahooMessenger.exe"=
"c:\\Program Files\\BitComet\\BitComet.exe"=
"c:\\Program Files\\AIM\\aim.exe"=
"c:\\Program Files\\Kodak\\AiO\\Center\\AiOHomeCenter.exe"=
"c:\\Program Files\\Kodak\\AiO\\Center\\Kodak.Statistics.exe"=
"c:\\Program Files\\Kodak\\AiO\\Center\\NetworkPrinterDiscovery.exe"=
"c:\\Program Files\\Kodak\\AiO\\Firmware\\KodakAiOUpdater.exe"=
"c:\\Documents and Settings\\All Users\\Application Data\\Kodak\\Installer\\Setup.exe"=
"c:\\Program Files\\Microsoft Office\\Office12\\OUTLOOK.EXE"=
"c:\\Program Files\\Mozilla Firefox\\firefox.exe"=
"c:\\Program Files\\Mozilla Firefox\\plugin-container.exe"=
"Updater Service"= c:\windows\system32\drivers\safesurf.exe
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"8831:TCP"= 8831:TCP:BitComet 8831 TCP
"8831:UDP"= 8831:UDP:BitComet 8831 UDP
"9322:TCP"= 9322:TCP:EKDiscovery
"4000:TCP"= 4000:TCP:192.168.0.10/255.255.255.255,192.168.0.13/255.255.255.255:Enabled:diablo
"4000:UDP"= 4000:UDP:diablo
R0 Lbd;Lbd;c:\windows\system32\drivers\Lbd.sys [8/28/2010 3:39 PM 64288]
R1 SASDIFSV;SASDIFSV;c:\program files\SUPERAntiSpyware\SASDIFSV.SYS [12/16/2009 4:26 PM 12872]
R1 SASKUTIL;SASKUTIL;c:\program files\SUPERAntiSpyware\SASKUTIL.SYS [12/16/2009 4:26 PM 67656]
S2 Kodak AiO Network Discovery Service;Kodak AiO Network Discovery Service;c:\program files\Kodak\AiO\Center\ekdiscovery.exe [2/11/2010 3:36 PM 300400]
S2 Lavasoft Ad-Aware Service;Lavasoft Ad-Aware Service;c:\program files\Lavasoft\Ad-Aware\AAWService.exe [8/12/2010 8:15 AM 1355928]
S3 Ambfilt;Ambfilt;c:\windows\system32\drivers\Ambfilt.sys [2/10/2010 10:46 PM 1691480]
S3 Lavasoft Kernexplorer;Lavasoft helper driver;c:\program files\Lavasoft\Ad-Aware\kernexplorer.sys [8/12/2010 8:15 AM 15008]
S3 nosGetPlusHelper;getPlus® Helper 3004;c:\windows\System32\svchost.exe -k nosGetPlusHelper [4/14/2008 8:00 AM 14336]
S3 SASENUM;SASENUM;c:\program files\SUPERAntiSpyware\SASENUM.SYS [12/16/2009 4:27 PM 12872]
S4 sptd;sptd;c:\windows\system32\drivers\sptd.sys [5/1/2010 12:07 AM 691696]
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\svchost]
nosGetPlusHelper REG_MULTI_SZ nosGetPlusHelper
.
Contents of the 'Scheduled Tasks' folder
2010-09-05 c:\windows\Tasks\Ad-Aware Update (Weekly).job
- c:\program files\Lavasoft\Ad-Aware\Ad-AwareAdmin.exe [2010-08-12 20:15]
.
.
------- Supplementary Scan -------
.
FF - ProfilePath - c:\documents and settings\Mommy\Application Data\Mozilla\Firefox\Profiles\r258s0lq.default\
FF - plugin: c:\program files\Common Files\Research In Motion\BBWebSLLauncher\NPWebSLLauncher.dll
FF - plugin: c:\program files\Mozilla Firefox\plugins\npCouponPrinter.dll
FF - plugin: c:\program files\Mozilla Firefox\plugins\npMozCouponPrinter.dll
FF - plugin: c:\program files\NOS\bin\np_gp.dll
FF - HiddenExtension: Microsoft .NET Framework Assistant: {20a82645-c095-46ed-80e3-08825760534b} - c:\windows\Microsoft.NET\Framework\v3.5\Windows Presentation Foundation\DotNetAssistantExtension\
---- FIREFOX POLICIES ----
c:\program files\Mozilla Firefox\greprefs\all.js - pref("network.IDN.whitelist.xn--mgbaam7a8h", true);
c:\program files\Mozilla Firefox\greprefs\all.js - pref("network.IDN.whitelist.xn--mgberp4a5d4ar", true);
c:\program files\Mozilla Firefox\defaults\pref\firefox.js - pref("dom.ipc.plugins.enabled", false);
.
- - - - ORPHANS REMOVED - - - -
AddRemove-Zeus - c:\impressions games\Zeus\Uninst.isu
**************************************************************************
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer,
http://www.gmer.net
Rootkit scan 2010-09-05 00:04
Windows 5.1.2600 Service Pack 3 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
--------------------- DLLs Loaded Under Running Processes ---------------------
- - - - - - - > 'winlogon.exe'(712)
c:\program files\SUPERAntiSpyware\SASWINLO.dll
c:\windows\system32\WININET.dll
- - - - - - - > 'explorer.exe'(2324)
c:\windows\system32\WININET.dll
c:\windows\system32\msi.dll
c:\windows\system32\ieframe.dll
c:\windows\system32\WPDShServiceObj.dll
c:\windows\system32\PortableDeviceTypes.dll
c:\windows\system32\PortableDeviceApi.dll
.
------------------------ Other Running Processes ------------------------
.
c:\program files\Java\jre6\bin\jqs.exe
c:\windows\system32\nvsvc32.exe
.
**************************************************************************
.
Completion time: 2010-09-05 00:12:32 - machine was rebooted
ComboFix-quarantined-files.txt 2010-09-05 04:12
Pre-Run: 12,438,188,032 bytes free
Post-Run: 12,319,436,800 bytes free
WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
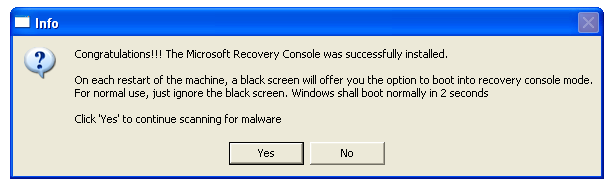
[boot loader]
timeout=2
default=multi(0)disk(0)rdisk(0)partition(1)\WINDOWS
[operating systems]
c:\cmdcons\BOOTSECT.DAT="Microsoft Windows Recovery Console" /cmdcons
UnsupportedDebug="do not select this" /debug
multi(0)disk(0)rdisk(0)partition(1)\WINDOWS="Microsoft Windows XP Professional" /noexecute=optin /fastdetect
- - End Of File - - 76973E2A4040AD09AACD338364CCD645


















 Sign In
Sign In Create Account
Create Account

