Nasty Redirect Virus
#16

 Posted 27 March 2011 - 09:02 PM
Posted 27 March 2011 - 09:02 PM

#17

 Posted 27 March 2011 - 09:16 PM
Posted 27 March 2011 - 09:16 PM

Thanks,
Bill
In Training at WTT Classroom
#18

 Posted 28 March 2011 - 09:24 AM
Posted 28 March 2011 - 09:24 AM

Let's try this please:
Print out these instructions as we may need to close every window that is open later in the fix.
It is possible that the infection you are trying to remove will not allow you to download files on the infected computer. If this is the case, then you will need to download the files requested in this guide on another computer and then transfer them to the infected computer. You can transfer the files via a CD/DVD, external drive, or USB flash drive.
Do not reboot your computer after running rkill as the malware programs will start again.
Please download and run the following tool to help allow other programs to run. (courtesy of BleepingComputer.com)
There are 3 different versions. If one of them won't run then download and try to run the other one.
Vista and Win7 users need to right click and choose Run as Admin
You only need to get one of them to run, not all of them.
Do not reboot your computer after running rkill as the malware programs will start again.
Next
Run GMER as instructed.
Next
- Please download OTH.scr to your desktop.
- Now download OTL to your desktop.
- Double click the OTH file and select Kill All Processes, your desktop will go blank
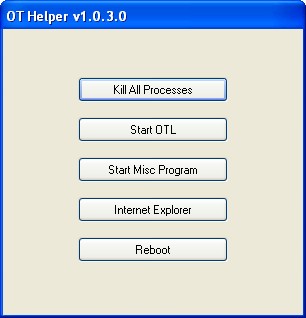
Then select Start OTL, - OTL will now run:
- When the window appears, underneath Output at the top change it to Minimal Output.
- Under the Standard Registry box change it to All.
- Under Custom scan's and fixes section paste in the below in bold
netsvcs
%SYSTEMDRIVE%\*.exe
/md5start
eventlog.dll
scecli.dll
netlogon.dll
cngaudit.dll
sceclt.dll
ntelogon.dll
logevent.dll
iaStor.sys
nvstor.sys
atapi.sys
IdeChnDr.sys
viasraid.sys
AGP440.sys
vaxscsi.sys
nvatabus.sys
viamraid.sys
nvata.sys
nvgts.sys
iastorv.sys
ViPrt.sys
eNetHook.dll
ahcix86.sys
KR10N.sys
nvstor32.sys
ahcix86s.sys
nvrd32.sys
symmpi.sys
adp3132.sys
mv61xx.sys
nvraid.sys
/md5stop
%systemroot%\*. /mp /s
CREATERESTOREPOINT
%systemroot%\system32\*.dll /lockedfiles
%systemroot%\Tasks\*.job /lockedfiles
%systemroot%\system32\drivers\*.sys /lockedfiles
%systemroot%\System32\config\*.sav
%systemroot%\system32\drivers\*.sys /90 - Check the boxes beside LOP Check and Purity Check.
- Click the Run Scan button. Do not change any settings unless otherwise told to do so. The scan wont take long.
- When the scan completes, it will open two notepad windows. OTL.Txt and Extras.Txt. These are saved in the same location as OTL.
- Please copy (Edit->Select All, Edit->Copy) the contents of these files, one at a time, and post it with your next reply.
Bill
In Training at WTT Classroom
Edited by redcar92, 28 March 2011 - 10:01 AM.
#19

 Posted 28 March 2011 - 10:06 AM
Posted 28 March 2011 - 10:06 AM

#20

 Posted 28 March 2011 - 08:19 PM
Posted 28 March 2011 - 08:19 PM

Do you want the rkill log file?
#21

 Posted 29 March 2011 - 10:17 AM
Posted 29 March 2011 - 10:17 AM

You stated that RKill runs but nothing else.
Did you download and run OTH and OTL? What were the results?
Did you try to boot in Safe mode and run RKill, DDS, GMER? What were the results
Did you try running OTH and OTL in Safe Mode? What were the results.
Here are the instructions to boot to safe mode:
To start the computer in Safe Mode, follow these steps:
As the computer is booting continuously tap the F8 Key which should bring up the Windows Advanced Options Menu.
Use the arrow keys to move to Safe Mode and press your Enter key.
Once you're done in Safe Mode and you want to get back into Normal Windows simply restart the computer like you normally would and let it boot normally.
Thanks,
Bill
In Training at WTT Classroom
#22

 Posted 29 March 2011 - 04:48 PM
Posted 29 March 2011 - 04:48 PM

#23

 Posted 29 March 2011 - 04:50 PM
Posted 29 March 2011 - 04:50 PM

Did you try to boot in Safe mode and run RKill, DDS, GMER? I will try it tonight What were the results
Did you try running OTH and OTL in Safe Mode? I will try it tonight What were the results.
Thanks
#24

 Posted 29 March 2011 - 06:31 PM
Posted 29 March 2011 - 06:31 PM

The gmer shows an hour glass for 2 seconds and then nothing. Everything else just hangs and freezes.
This is while in safe mode. Have we have exhausted all options?
Thanks
#25

 Posted 29 March 2011 - 07:09 PM
Posted 29 March 2011 - 07:09 PM

Rerun RKILL then'
Do not reboot your computer after running rkill as the malware programs will start again.
Next:
Please run Malwaraebytes, be sure to click on the Update tab and update, start at step 4. if you have removed Malwarebys do the next step.
Please download Malwarebytes' Anti-Malware to your desktop.
- Double-click mbam-setup.exe and follow the prompts to install the program.
- At the end, be sure a checkmark is placed next to Update Malwarebytes' Anti-Malware and Launch Malwarebytes' Anti-Malware, then click Finish.
- If an update is found, it will download and install the latest version.
- Once the program has loaded, select Perform quick scan, then click Scan.
- When the scan is complete, click OK, then Show Results to view the results.
- Then click Remove Selected .
- When completed, a log will open in Notepad. Please save it to a convenient location and post the results.
- Note: If you receive a notice that some of the items couldn't be removed, that they have been added to the delete on reboot list, please reboot.
Also please describe how your computer behaves at the moment.
Please don't attach the scans / logs, use "copy/paste". .
If that fails, try running MalwareBytes in Safe Mode.
Thanks
Bill
In Training at WTT Classroom
#26

 Posted 29 March 2011 - 07:38 PM
Posted 29 March 2011 - 07:38 PM

I can now run all the programs you suggested.
Here's the log
Malwarebytes' Anti-Malware 1.50.1.1100
www.malwarebytes.org
Database version: 6210
Windows 5.1.2600 Service Pack 3
Internet Explorer 8.0.6001.18702
3/29/2011 6:26:07 PM
mbam-log-2011-03-29 (18-26-07).txt
Scan type: Quick scan
Objects scanned: 153329
Time elapsed: 4 minute(s), 8 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 1
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 1
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
c:\WINDOWS\system32\lnksedir.dll (Trojan.Agent) -> Delete on reboot.
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
c:\WINDOWS\system32\lnksedir.dll (Trojan.Agent) -> Delete on reboot.
#27

 Posted 29 March 2011 - 07:46 PM
Posted 29 March 2011 - 07:46 PM

#28

 Posted 29 March 2011 - 07:48 PM
Posted 29 March 2011 - 07:48 PM

#29

 Posted 30 March 2011 - 06:57 AM
Posted 30 March 2011 - 06:57 AM

Also please see dds-Attached.txt and gmer.log attached.
.
DDS (Ver_11-03-05.01) - NTFSx86 NETWORK
Run by terra at 18:49:33.73 on Tue 03/29/2011
Internet Explorer: 8.0.6001.18702 BrowserJavaVersion: 1.6.0_23
Microsoft Windows XP Professional 5.1.2600.3.1252.1.1033.18.1022.712 [GMT -7:00]
.
AV: Microsoft Security Essentials *Disabled/Updated* {EDB4FA23-53B8-4AFA-8C5D-99752CCA7095}
AV: Microsoft Security Essentials *Disabled/Updated* {BCF43643-A118-4432-AEDE-D861FCBCFCDF}
.
============== Running Processes ===============
.
C:\WINDOWS\system32\svchost -k DcomLaunch
svchost.exe
c:\Program Files\Microsoft Security Client\Antimalware\MsMpEng.exe
C:\WINDOWS\system32\svchost.exe -k netsvcs
svchost.exe
svchost.exe
C:\WINDOWS\Explorer.EXE
C:\Documents and Settings\terra\Desktop\dds.scr
.
============== Pseudo HJT Report ===============
.
uStart Page = hxxp://www.charter.net/
uSearch Page = hxxp://www.charter.net/google/index.php?q=
uSearch Bar =
uDefault_Page_URL = hxxp://www.google.com/ig/dell?hl=en&client=dell-inc&channel=us
uWindow Title = Powered by Charter Communications
BHO: AcroIEHlprObj Class: {06849e9f-c8d7-4d59-b87d-784b7d6be0b3} - c:\program files\adobe\acrobat 6.0\reader\activex\AcroIEHelper.dll
BHO: DriveLetterAccess: {5ca3d70e-1895-11cf-8e15-001234567890} - c:\windows\system32\dla\DLASHX_W.DLL
BHO: Java™ Plug-In 2 SSV Helper: {dbc80044-a445-435b-bc74-9c25c1c588a9} - c:\program files\java\jre6\bin\jp2ssv.dll
BHO: JQSIEStartDetectorImpl Class: {e7e6f031-17ce-4c07-bc86-eabfe594f69c} - c:\program files\java\jre6\lib\deploy\jqs\ie\jqs_plugin.dll
TB: {2318C2B1-4965-11D4-9B18-009027A5CD4F} - No File
uRun: [SetDefaultMIDI] MIDIDef.exe
uRun: [ctfmon.exe] c:\windows\system32\ctfmon.exe
mRun: [ehTray] c:\windows\ehome\ehtray.exe
mRun: [SunJavaUpdateSched] "c:\program files\common files\java\java update\jusched.exe"
mRun: [SigmatelSysTrayApp] stsystra.exe
mRun: [ATIPTA] "c:\program files\ati technologies\ati control panel\atiptaxx.exe"
mRun: [CTSysVol] c:\program files\creative\sbaudigy\surround mixer\CTSysVol.exe /r
mRun: [MBMon] Rundll32 CTMBHA.DLL,MBMon
mRun: [UpdReg] c:\windows\UpdReg.EXE
mRun: [DLA] c:\windows\system32\dla\DLACTRLW.EXE
mRun: [MSC] "c:\program files\microsoft security client\msseces.exe" -hide -runkey
mRun: [Microsoft Default Manager] "c:\program files\microsoft\search enhancement pack\default manager\DefMgr.exe" -resume
mRun: [ISUSScheduler] "c:\program files\common files\installshield\updateservice\issch.exe" -start
mRun: [ISUSPM Startup] "c:\program files\common files\installshield\updateservice\isuspm.exe" -startup
StartupFolder: c:\docume~1\alluse~1\startm~1\programs\startup\adobeg~1.lnk - c:\program files\common files\adobe\calibration\Adobe Gamma Loader.exe
StartupFolder: c:\docume~1\alluse~1\startm~1\programs\startup\digita~1.lnk - c:\program files\digital line detect\DLG.exe
IE: {CD67F990-D8E9-11d2-98FE-00C0F0318AFE}
IE: {e2e2dd38-d088-4134-82b7-f2ba38496583} - %windir%\Network Diagnostic\xpnetdiag.exe
IE: {FB5F1910-F110-11d2-BB9E-00C04F795683} - c:\program files\messenger\msmsgs.exe
DPF: {6414512B-B978-451D-A0D8-FCFDF33E833C} - hxxp://update.microsoft.com/windowsupdate/v6/V5Controls/en/x86/client/wuweb_site.cab?1286416658140
DPF: {8AD9C840-044E-11D1-B3E9-00805F499D93} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_23-windows-i586.cab
DPF: {CAFEEFAC-0014-0002-0003-ABCDEFFEDCBA} - hxxp://java.sun.com/products/plugin/autodl/jinstall-142-windows-i586.cab
DPF: {CAFEEFAC-0016-0000-0023-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_23-windows-i586.cab
DPF: {CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA} - hxxp://java.sun.com/update/1.6.0/jinstall-1_6_0_23-windows-i586.cab
.
================= FIREFOX ===================
.
FF - ProfilePath - c:\docume~1\terra\applic~1\mozilla\firefox\profiles\ffuujbci.default\
FF - prefs.js: browser.startup.homepage - hxxp://www.google.com
FF - component: c:\documents and settings\terra\application data\mozilla\firefox\profiles\ffuujbci.default\extensions\{7b13ec3e-999a-4b70-b9cb-2617b8323822}\components\FFExternalAlert.dll
FF - component: c:\documents and settings\terra\application data\mozilla\firefox\profiles\ffuujbci.default\extensions\{7b13ec3e-999a-4b70-b9cb-2617b8323822}\components\RadioWMPCore.dll
FF - plugin: c:\documents and settings\terra\local settings\application data\unity\webplayer\loader\npUnity3D32.dll
FF - plugin: c:\program files\google\update\1.2.183.39\npGoogleOneClick8.dll
FF - plugin: c:\program files\java\jre6\bin\new_plugin\npdeployJava1.dll
FF - plugin: c:\program files\microsoft silverlight\4.0.60129.0\npctrlui.dll
FF - plugin: c:\program files\mozilla firefox\plugins\npdeployJava1.dll
FF - plugin: c:\program files\mozilla firefox\plugins\npFoxitReaderPlugin.dll
FF - plugin: c:\program files\viewpoint\viewpoint experience technology\npViewpoint.dll
.
============= SERVICES / DRIVERS ===============
.
S1 MpFilter;Microsoft Malware Protection Driver;c:\windows\system32\drivers\MpFilter.sys [2010-3-25 165264]
S1 MpKslc7262cdd;MpKslc7262cdd;\??\c:\documents and settings\all users\application data\microsoft\microsoft antimalware\definition updates\{6e1baeef-4127-4665-b377-11183af18007}\mpkslc7262cdd.sys --> c:\documents and settings\all users\application data\microsoft\microsoft antimalware\definition updates\{6e1baeef-4127-4665-b377-11183af18007}\MpKslc7262cdd.sys [?]
S1 ssoftnt4;ssoftnt4;c:\windows\system32\drivers\ssoftnt4.sys [2011-1-9 97784]
S2 gupdate;Google Update Service (gupdate);c:\program files\google\update\GoogleUpdate.exe [2010-12-5 136176]
S2 McrdSvc;Media Center Extender Service;c:\windows\ehome\mcrdsvc.exe [2005-8-5 99328]
.
=============== Created Last 30 ================
.
2011-03-30 00:58:24 -------- d-----w- c:\docume~1\alluse~1\applic~1\Western Digital
2011-03-30 00:53:40 -------- d-----w- c:\docume~1\terra\locals~1\applic~1\Western Digital
2011-03-29 03:19:06 6792528 ----a-w- c:\docume~1\alluse~1\applic~1\microsoft\microsoft antimalware\definition updates\{802b4456-9604-4888-95b3-c534c4d5cd36}\mpengine.dll
2011-03-27 16:01:29 -------- d-----w- c:\program files\Emsisoft Anti-Malware
2011-03-27 13:25:07 -------- d-----w- c:\docume~1\alluse~1\applic~1\Pure Networks
2011-03-26 17:34:55 16968 ----a-w- c:\windows\system32\drivers\hitmanpro35.sys
2011-03-26 17:33:54 -------- d-----w- c:\docume~1\alluse~1\applic~1\Hitman Pro
2011-03-26 16:50:11 -------- d-----w- c:\program files\Spybot - Search & Destroy
2011-03-26 16:50:11 -------- d-----w- c:\docume~1\alluse~1\applic~1\Spybot - Search & Destroy
2011-03-26 13:23:43 -------- d-----w- c:\docume~1\terra\applic~1\Malwarebytes
2011-03-26 13:23:41 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2011-03-26 13:23:40 -------- d-----w- c:\docume~1\alluse~1\applic~1\Malwarebytes
2011-03-26 13:23:33 20952 ----a-w- c:\windows\system32\drivers\mbam.sys
2011-03-26 13:23:33 -------- d-----w- c:\program files\Malwarebytes' Anti-Malware
2011-03-26 13:10:02 -------- d-----w- c:\docume~1\alluse~1\applic~1\nEmPcOjPcGc28600
2011-03-24 00:42:11 781272 ----a-w- c:\program files\mozilla firefox\mozsqlite3.dll
2011-03-24 00:42:11 728024 ----a-w- c:\program files\mozilla firefox\libGLESv2.dll
2011-03-24 00:42:11 1874904 ----a-w- c:\program files\mozilla firefox\mozjs.dll
2011-03-24 00:42:11 15832 ----a-w- c:\program files\mozilla firefox\mozalloc.dll
2011-03-24 00:42:10 1893336 ----a-w- c:\program files\mozilla firefox\d3dx9_42.dll
2011-03-24 00:42:10 142296 ----a-w- c:\program files\mozilla firefox\libEGL.dll
2011-03-24 00:42:09 1975768 ----a-w- c:\program files\mozilla firefox\D3DCompiler_42.dll
2011-03-24 00:42:09 142296 ----a-w- c:\program files\mozilla firefox\components\browsercomps.dll
2011-03-11 03:42:46 -------- d-----w- c:\program files\WinISO
2011-03-08 03:46:36 -------- d-----w- c:\docume~1\alluse~1\applic~1\SmartSound Software Inc
2011-03-08 03:46:29 -------- d-----w- c:\program files\SmartSound Software
2011-03-08 03:45:50 443752 ----a-w- c:\windows\system32\d3dx10_33.dll
2011-03-08 03:45:50 1123696 ----a-w- c:\windows\system32\D3DCompiler_33.dll
2011-03-08 03:45:48 3495784 ----a-w- c:\windows\system32\d3dx9_33.dll
.
==================== Find3M ====================
.
2011-02-05 01:48:32 456192 ----a-w- c:\windows\system32\encdec.dll
2011-02-05 01:48:30 291840 ----a-w- c:\windows\system32\sbe.dll
2011-02-02 07:58:35 2067456 ----a-w- c:\windows\system32\mstscax.dll
2011-01-27 11:57:06 677888 ----a-w- c:\windows\system32\mstsc.exe
2011-01-21 14:44:37 439296 ----a-w- c:\windows\system32\shimgvw.dll
2011-01-07 14:09:02 290048 ----a-w- c:\windows\system32\atmfd.dll
2010-12-31 13:10:33 1854976 ----a-w- c:\windows\system32\win32k.sys
.
============= FINISH: 18:50:14.04 ===============
Attached Files
#30

 Posted 30 March 2011 - 12:49 PM
Posted 30 March 2011 - 12:49 PM

Things are looking much better, but:
Your logs indicate that you have Peer-to-Peer software installed on your PC called uTorrent. Peer-to-Peer sites like LimeWire, and uTorrent are a major source of malware problems. It is in your best interest to avoid the sites. I strongly recommend that you remove this (these) program(s) by:
- Click Start
- Click Control Panel
- Click Add/Remove Programs
- Select uTorrent
- Click Remove
Should you decide to not remove Peer to Peer software, do not use it until we are done. Continued use of this software will eventually infect you again.
Next
***Read through this entire procedure and if you have any questions, please ask them before you begin. Then either print out, or copy this page to Notepad and save to your desktop for reference as you will not have any browsers open while you are carrying out portions of these instructions.***
Download Combofix from any of the links below and save it to your desktop.
Link 1
Link 2
* IMPORTANT !!! Save ComboFix.exe to your Desktop
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools
- See this Link for programs that need to be disabled and instruction on how to disable them.
- Remember to re-enable them when we're done.
- Double click on ComboFix.exe & follow the prompts.
- As part of it's process, ComboFix will check to see if the Microsoft Windows Recovery Console is installed. With malware infections being as they are today, it's strongly recommended to have this pre-installed on your machine before doing any malware removal. It will allow you to boot up into a special recovery/repair mode that will allow us to more easily help you should your computer have a problem after an attempted removal of malware.
- Follow the prompts to allow ComboFix to download and install the Microsoft Windows Recovery Console, and when prompted, agree to the End-User License Agreement to install the Microsoft Windows Recovery Console.
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt in your next reply.
*If there is no internet connection when Combofix has completely finished then restart your computer to restore back the connections.
Logs to post:
- Combofix.txt
- Let me know how your PC is behaving now.
Bill
In Training at WTT Classroom
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked






 Sign In
Sign In Create Account
Create Account

