Been Google Hijacked HELP!
Started by
Madara
, May 06 2011 10:10 PM
#16

 Posted 07 May 2011 - 03:20 PM
Posted 07 May 2011 - 03:20 PM

#17

 Posted 07 May 2011 - 03:22 PM
Posted 07 May 2011 - 03:22 PM

Ahh you do not get off that easily  I have to give you a wash and brush up
I have to give you a wash and brush up
Subject to no further problems
I will remove my tools now and give some recommendations, but, I would like you to run for 24 hours or so and come back if you have any problems
Now the best part of the day ----- Your log now appears clean
A good workman always cleans up after himself so..The following will implement some cleanup procedures as well as reset System Restore points:
Run OTL
Run OTL and hit the cleanup button. It will remove all the programmes we have used plus itself.
We will now confirm that your hidden files are set to that, as some of the tools I use will change that
SPRING CLEAN
Download and run Puran Disc Defragmenter
For the first run I would recommend a boot defrag and disk check
Now that you are clean, to help protect your computer in the future I recommend that you get the following free programmes:
 Malwarebytes. Update and run weekly to keep your system clean
Malwarebytes. Update and run weekly to keep your system clean
Download and install FileHippo update checker and run it monthly it will show you which programmes on your system need updating and give a download link
It is critical to have both a firewall and anti virus to protect your system and to keep them updated.
To keep your operating system up to date visit
To learn more about how to protect yourself while on the internet read our little guide How did I get infected in the first place ?
Keep safe
Subject to no further problems
I will remove my tools now and give some recommendations, but, I would like you to run for 24 hours or so and come back if you have any problems
Now the best part of the day ----- Your log now appears clean
A good workman always cleans up after himself so..The following will implement some cleanup procedures as well as reset System Restore points:
Run OTL
- Under the Custom Scans/Fixes box at the bottom, paste in the following
:Commands
[resethosts]
[purity]
[emptytemp]
[EMPTYFLASH]
[CLEARALLRESTOREPOINTS]
[Reboot]
- Then click the Run Fix button at the top
- Let the program run unhindered, reboot the PC when it is done
Run OTL and hit the cleanup button. It will remove all the programmes we have used plus itself.
We will now confirm that your hidden files are set to that, as some of the tools I use will change that
- Click Start.
- Open My Computer.
- Select the Tools menu and click Folder Options.
- Select the View Tab.
- Under the Hidden files and folders heading select Do not show hidden files and folders.
- Click Yes to confirm.
- Click OK.
SPRING CLEAN
Download and run Puran Disc Defragmenter
For the first run I would recommend a boot defrag and disk check
Now that you are clean, to help protect your computer in the future I recommend that you get the following free programmes:
Download and install FileHippo update checker and run it monthly it will show you which programmes on your system need updating and give a download link
It is critical to have both a firewall and anti virus to protect your system and to keep them updated.
To keep your operating system up to date visit
To learn more about how to protect yourself while on the internet read our little guide How did I get infected in the first place ?
Keep safe
#18

 Posted 07 May 2011 - 08:59 PM
Posted 07 May 2011 - 08:59 PM

Still getting random tab pop ups :/ i use Firefox the most I hardly and i mean hardly use IE
#19

 Posted 08 May 2011 - 04:42 AM
Posted 08 May 2011 - 04:42 AM

OK lets get the big boy on the job
When you run this Avast may offer to sandbox it - allow it to run normally plus all associated files
Right click the AVast blob and select shield control
Select disable shields for 1 hour
Download ComboFix from one of these locations:
Link 1
Link 2
* IMPORTANT !!! Save ComboFix.exe to your Desktop
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
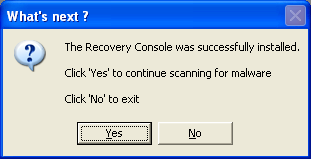
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt in your next reply.
When you run this Avast may offer to sandbox it - allow it to run normally plus all associated files
Right click the AVast blob and select shield control
Select disable shields for 1 hour
Download ComboFix from one of these locations:
Link 1
Link 2
* IMPORTANT !!! Save ComboFix.exe to your Desktop
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools
- Double click on ComboFix.exe & follow the prompts.
- As part of it's process, ComboFix will check to see if the Microsoft Windows Recovery Console is installed. With malware infections being as they are today, it's strongly recommended to have this pre-installed on your machine before doing any malware removal. It will allow you to boot up into a special recovery/repair mode that will allow us to more easily help you should your computer have a problem after an attempted removal of malware.
- Follow the prompts to allow ComboFix to download and install the Microsoft Windows Recovery Console, and when prompted, agree to the End-User License Agreement to install the Microsoft Windows Recovery Console.
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
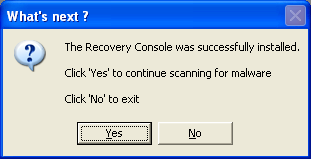
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt in your next reply.
#20

 Posted 08 May 2011 - 04:00 PM
Posted 08 May 2011 - 04:00 PM

Should i be fine saying my Norton 360 Anti Virus Desktop and Symantec antivirus scans are still on even tho i dont even use them anymore?
#21

 Posted 09 May 2011 - 11:02 AM
Posted 09 May 2011 - 11:02 AM

Yes I will give the removal tool for Norton http://us.norton.com...3834EN&ln=en_US run this
#22

 Posted 09 May 2011 - 09:38 PM
Posted 09 May 2011 - 09:38 PM

ComboFix 11-05-09.02 - Samuel 05/09/2011 21:58:17.1.1 - x86
Microsoft Windows XP Professional 5.1.2600.3.1252.1.1033.18.958.683 [GMT -5:00]
Running from: c:\documents and settings\Samuel\Desktop\ComboFix.exe
AV: AntiVir Desktop *Enabled/Outdated* {AD166499-45F9-482A-A743-FDD3350758C7}
AV: avast! Antivirus *Disabled/Updated* {7591DB91-41F0-48A3-B128-1A293FD8233D}
AV: Symantec AntiVirus Corporate Edition *Enabled/Outdated* {FB06448E-52B8-493A-90F3-E43226D3305C}
.
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
.
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}\chrome.manifest
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}\chrome\content\_cfg.js
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}\chrome\content\overlay.xul
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}\install.rdf
c:\documents and settings\Samuel\WINDOWS
C:\install.exe
c:\program files\Common Files\rwri
c:\program files\Common Files\rwri\rwria.lck
c:\program files\Common Files\rwri\rwrid\class-barrel
c:\program files\Common Files\rwri\rwril.lck
c:\program files\Common Files\rwri\rwrim.lck
c:\program files\Mozilla Firefox\searchplugins\google_search.xml
c:\windows\system32\Ijl11.dll
.
.
((((((((((((((((((((((((((((((((((((((( Drivers/Services )))))))))))))))))))))))))))))))))))))))))))))))))
.
.
-------\Legacy_6TO4
-------\Legacy_MYWEBSEARCHSERVICE
-------\Legacy_TDSSSERV.SYS
-------\Service_6to4
.
.
((((((((((((((((((((((((( Files Created from 2011-04-10 to 2011-05-10 )))))))))))))))))))))))))))))))
.
.
2011-05-10 03:12 . 2011-05-10 03:12 -------- d-sh--w- c:\documents and settings\LocalService\IETldCache
2011-05-08 01:28 . 2011-04-08 21:06 233472 ----a-w- c:\windows\system32\PuranDefragS.exe
2011-05-08 01:28 . 2011-04-08 21:06 229376 ----a-w- c:\windows\system32\PuranDC.exe
2011-05-08 01:28 . 2011-04-08 21:06 1114112 ----a-w- c:\windows\system32\PuranFD.exe
2011-05-08 01:28 . 2011-04-08 21:06 109056 ----a-w- c:\windows\system32\PuranDefragBT.exe
2011-05-08 01:28 . 2009-12-31 19:02 212992 ----a-w- c:\windows\system32\PuranDefrag.dll
2011-05-08 01:28 . 2011-05-08 01:28 -------- d-----w- c:\program files\Puran Defrag
2011-05-07 01:43 . 2011-05-07 01:43 781272 ----a-w- c:\program files\Mozilla Firefox\mozsqlite3.dll
2011-05-07 01:43 . 2011-05-07 01:43 1874904 ----a-w- c:\program files\Mozilla Firefox\mozjs.dll
2011-05-07 01:43 . 2011-05-07 01:43 89048 ----a-w- c:\program files\Mozilla Firefox\libEGL.dll
2011-05-07 01:43 . 2011-05-07 01:43 465880 ----a-w- c:\program files\Mozilla Firefox\libGLESv2.dll
2011-05-07 01:43 . 2011-05-07 01:43 15832 ----a-w- c:\program files\Mozilla Firefox\mozalloc.dll
2011-05-07 01:43 . 2011-05-07 01:43 1892184 ----a-w- c:\program files\Mozilla Firefox\d3dx9_42.dll
2011-05-07 01:43 . 2011-05-07 01:43 1974616 ----a-w- c:\program files\Mozilla Firefox\D3DCompiler_42.dll
2011-05-07 01:43 . 2011-05-07 01:43 142296 ----a-w- c:\program files\Mozilla Firefox\components\browsercomps.dll
2011-05-04 23:05 . 2011-05-04 23:05 388096 ----a-r- c:\documents and settings\Samuel\Application Data\Microsoft\Installer\{45A66726-69BC-466B-A7A4-12FCBA4883D7}\HiJackThis.exe
2011-05-04 22:43 . 2011-05-04 22:43 -------- d-----w- c:\documents and settings\Samuel\temp
2011-05-01 23:03 . 2011-05-06 19:43 -------- d-----w- c:\program files\Silkroad
2011-05-01 22:29 . 2011-05-01 22:33 125976576 ----a-w- C:\SilkroadOnline_GlobalOfficial_v1_298.exe
2011-05-01 22:24 . 2011-05-01 23:00 40630489 ----a-w- C:\SilkroadOnline_GlobalOfficial_v1_298(for_v1_295_297).exe
2011-04-18 07:06 . 2009-07-13 20:24 378408 ----a-w- c:\windows\glbNMDownloaderUpdater.exe
2011-04-18 07:06 . 2009-07-31 00:32 804368 ----a-w- c:\windows\GlbNMUpdater.exe
2011-04-18 07:05 . 2010-11-22 19:20 475136 ----a-w- c:\windows\npGlbNMFFUpdaterModule.dll
2011-04-18 07:05 . 2010-11-22 19:13 90112 ----a-w- c:\windows\GlbNMVistaUpdater.exe
2011-04-18 07:04 . 2001-09-05 09:18 77824 ----a-w- c:\program files\Common Files\InstallShield\Engine\6\Intel 32\ctor.dll
2011-04-18 07:04 . 2001-09-05 09:18 225280 ------w- c:\program files\Common Files\InstallShield\IScript\iscript.dll
2011-04-18 07:04 . 2001-09-05 09:14 176128 ------w- c:\program files\Common Files\InstallShield\Engine\6\Intel 32\iuser.dll
2011-04-18 07:04 . 2001-09-05 09:13 32768 ------w- c:\program files\Common Files\InstallShield\Engine\6\Intel 32\objectps.dll
2011-04-18 07:04 . 2002-07-25 21:07 614532 ----a-w- c:\program files\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe
2011-04-17 09:51 . 2011-02-23 13:56 371544 ----a-w- c:\windows\system32\drivers\aswSnx.sys
2011-04-14 03:58 . 2011-04-29 04:26 -------- d-----w- c:\program files\Tales of Pirates II
2011-04-10 21:28 . 2011-05-05 18:54 -------- d-----w- c:\documents and settings\All Users\Application Data\Skype Extras
2011-04-10 21:27 . 2011-04-10 21:27 -------- d-----w- c:\program files\Common Files\Skype
.
.
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2011-04-08 11:28 . 2011-04-08 11:28 41872 ----a-w- c:\windows\system32\xfcodec.dll
2011-03-01 19:29 . 2009-08-29 03:59 3912008 ----a-w- c:\windows\system32\GameMon.des
2011-02-23 14:04 . 2010-08-17 05:12 40648 ----a-w- c:\windows\avastSS.scr
2011-02-23 14:04 . 2010-08-17 05:12 190016 ----a-w- c:\windows\system32\aswBoot.exe
2011-02-23 13:56 . 2010-08-17 05:12 301528 ----a-w- c:\windows\system32\drivers\aswSP.sys
2011-02-23 13:55 . 2010-08-17 05:12 49240 ----a-w- c:\windows\system32\drivers\aswTdi.sys
2011-02-23 13:55 . 2010-08-17 05:12 102232 ----a-w- c:\windows\system32\drivers\aswmon2.sys
2011-02-23 13:55 . 2010-08-17 05:12 96344 ----a-w- c:\windows\system32\drivers\aswmon.sys
2011-02-23 13:55 . 2010-08-17 05:12 25432 ----a-w- c:\windows\system32\drivers\aswRdr.sys
2011-02-23 13:54 . 2010-08-17 05:12 30680 ----a-w- c:\windows\system32\drivers\aavmker4.sys
2011-02-23 13:54 . 2010-08-17 05:12 19544 ----a-w- c:\windows\system32\drivers\aswFsBlk.sys
2009-02-24 19:34 . 2009-02-24 19:34 1044480 ----a-w- c:\program files\mozilla firefox\plugins\libdivx.dll
2009-02-24 19:34 . 2009-02-24 19:34 200704 ----a-w- c:\program files\mozilla firefox\plugins\ssldivx.dll
2011-05-07 01:43 . 2011-05-07 01:43 142296 ----a-w- c:\program files\mozilla firefox\components\browsercomps.dll
.
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
.
[HKEY_LOCAL_MACHINE\~\Browser Helper Objects\{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}]
2010-12-09 18:51 3911776 ----a-w- c:\program files\uTorrentBar\tbuTor.dll
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Toolbar]
"{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}"= "c:\program files\uTorrentBar\tbuTor.dll" [2010-12-09 3911776]
.
[HKEY_CLASSES_ROOT\clsid\{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}]
.
[HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar\Webbrowser]
"{BF7380FA-E3B4-4DB2-AF3E-9D8783A45BFC}"= "c:\program files\uTorrentBar\tbuTor.dll" [2010-12-09 3911776]
.
[HKEY_CLASSES_ROOT\clsid\{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}]
.
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\explorer\shelliconoverlayidentifiers\00avast]
@="{472083B0-C522-11CF-8763-00608CC02F24}"
[HKEY_CLASSES_ROOT\CLSID\{472083B0-C522-11CF-8763-00608CC02F24}]
2011-02-23 14:04 122512 ----a-w- c:\program files\Alwil Software\Avast5\ashShell.dll
.
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"igndlm.exe"="c:\program files\Download Manager\DLM.exe" [2009-05-15 1103216]
"BitTorrent DNA"="c:\program files\DNA\btdna.exe" [2009-11-13 323392]
"DAEMON Tools Lite"="c:\program files\DAEMON Tools Lite\DTLite.exe" [2010-04-01 357696]
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"QuickTime Task"="c:\program files\QuickTime\qttask.exe" [2009-01-05 413696]
"SunJavaUpdateSched"="c:\program files\Common Files\Java\Java Update\jusched.exe" [2010-02-18 248040]
"RTHDCPL"="RTHDCPL.EXE" [2007-05-28 16132608]
"GrooveMonitor"="c:\program files\Microsoft Office\Office12\GrooveMonitor.exe" [2008-10-25 31072]
"avast5"="c:\progra~1\ALWILS~1\Avast5\avastUI.exe" [2011-02-23 3451496]
"nwiz"="c:\program files\NVIDIA Corporation\nView\nwiz.exe" [2010-07-08 1753192]
"NvCplDaemon"="c:\windows\system32\NvCpl.dll" [2010-07-09 13923432]
"NvMediaCenter"="c:\windows\system32\NvMcTray.dll" [2010-07-09 110696]
.
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\RunOnce]
"tscuninstall"="c:\windows\system32\tscupgrd.exe" [2007-12-16 40448]
.
c:\documents and settings\Samuel\Start Menu\Programs\Startup\
CurseClientStartup.ccip [2010-2-1 0]
.
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\winlogon\notify\LMIinit]
2008-10-17 02:35 87352 ----a-w- c:\windows\system32\LMIinit.dll
.
[HKEY_LOCAL_MACHINE\system\currentcontrolset\control\securityproviders]
SecurityProviders msapsspc.dll, schannel.dll, digest.dll, credssp.dll, msnsspc.dll
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\Adobe Reader Speed Launcher]
2007-10-11 01:51 39792 -c--a-w- c:\program files\Adobe\Reader 8.0\Reader\reader_sl.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\MSMSGS]
2007-10-31 06:32 1695232 ------w- c:\program files\Messenger\msmsgs.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\NvCplDaemon]
2010-07-09 21:24 13923432 ----a-w- c:\windows\system32\nvcpl.dll
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\NvMediaCenter]
2010-07-09 21:24 110696 ----a-w- c:\windows\system32\nvmctray.dll
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\QuickTime Task]
2009-01-05 22:18 413696 ----a-w- c:\program files\QuickTime\QTTask.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\Skype]
2011-04-01 23:17 15145352 ----a-r- c:\program files\Skype\Phone\Skype.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\SunJavaUpdateSched]
2007-09-25 07:11 132496 -c--a-w- c:\program files\Java\jre1.6.0_03\bin\jusched.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusOverride"=dword:00000001
"FirewallOverride"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring]
"DisableMonitoring"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecAntiVirus]
"DisableMonitoring"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecFirewall]
"DisableMonitoring"=dword:00000001
.
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile]
"DisableNotifications"= 1 (0x1)
.
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\Network Diagnostic\\xpnetdiag.exe"=
"%windir%\\system32\\sessmgr.exe"=
"c:\\WINDOWS\\system32\\dplaysvr.exe"=
"c:\\Program Files\\DNA\\btdna.exe"=
"c:\\Program Files\\Xfire\\xfire.exe"=
"c:\\Program Files\\Bonjour\\mDNSResponder.exe"=
"c:\\Program Files\\uTorrent\\uTorrent.exe"=
"c:\\Documents and Settings\\Samuel\\Local Settings\\Application Data\\Dyyno Receiver\\DPPM.exe"=
"c:\\Program Files\\Mozilla Firefox\\firefox.exe"=
"c:\\Program Files\\Kaiba Corp VDS\\KCVDS.exe"=
"c:\\Program Files\\Java\\jre6\\bin\\java.exe"=
"c:\\Program Files\\Warcraft III\\war3.exe"=
"c:\\WINDOWS\\Downloaded Program Files\\PurpleBean.exe"=
"c:\\Program Files\\Skype\\Plugin Manager\\skypePM.exe"=
"c:\\Documents and Settings\\Samuel\\My Documents\\Downloads\\GhostOne\\GHostOne\\ghost.exe"=
"c:\\Documents and Settings\\Samuel\\My Documents\\Downloads\\GhostOne\\GHostOne\\GHostOne.exe"=
"c:\\Program Files\\Microsoft Office\\Office12\\OUTLOOK.EXE"=
"c:\\Program Files\\Microsoft Office\\Office12\\GROOVE.EXE"=
"c:\\Program Files\\Microsoft Office\\Office12\\ONENOTE.EXE"=
"c:\\Program Files\\Pando Networks\\Media Booster\\PMB.exe"=
"c:\\Program Files\\Skype\\Phone\\Skype.exe"=
"c:\\Program Files\\TeamViewer\\Version5\\TeamViewer.exe"=
.
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"22297:TCP"= 22297:TCP:BitComet 22297 TCP
"22297:UDP"= 22297:UDP:BitComet 22297 UDP
"26485:TCP"= 26485:TCP:BitComet 26485 TCP
"26485:UDP"= 26485:UDP:BitComet 26485 UDP
"3389:TCP"= 3389:TCP:*:Disabled:@xpsp2res.dll,-22009
"6112:TCP"= 6112:TCP:Warcraft
"58513:TCP"= 58513:TCP:Pando Media Booster
"58513:UDP"= 58513:UDP:Pando Media Booster
"3724:TCP"= 3724:TCP:Blizzard Downloader: 3724
"8376:TCP"= 8376:TCP:League of Legends Launcher
"8376:UDP"= 8376:UDP:League of Legends Launcher
"56234:TCP"= 56234:TCP:Pando Media Booster
"56234:UDP"= 56234:UDP:Pando Media Booster
"5985:TCP"= 5985:TCP:*:Disabled:Windows Remote Management
"57235:TCP"= 57235:TCP:Pando Media Booster
"57235:UDP"= 57235:UDP:Pando Media Booster
"8378:TCP"= 8378:TCP:League of Legends Launcher
"8378:UDP"= 8378:UDP:League of Legends Launcher
"8379:TCP"= 8379:TCP:League of Legends Launcher
"8379:UDP"= 8379:UDP:League of Legends Launcher
"58057:TCP"= 58057:TCP:Pando Media Booster
"58057:UDP"= 58057:UDP:Pando Media Booster
"57452:TCP"= 57452:TCP:Pando Media Booster
"57452:UDP"= 57452:UDP:Pando Media Booster
"1034:TCP"= 1034:TCP:Akamai NetSession Interface
"5000:UDP"= 5000:UDP:Akamai NetSession Interface
.
R0 sptd;sptd;c:\windows\system32\drivers\sptd.sys [2/19/2009 10:58 AM 691696]
R1 aswSnx;aswSnx;c:\windows\system32\drivers\aswSnx.sys [4/17/2011 4:51 AM 371544]
R1 aswSP;aswSP;c:\windows\system32\drivers\aswSP.sys [8/17/2010 12:12 AM 301528]
R2 Akamai;Akamai NetSession Interface;c:\windows\System32\svchost.exe -k Akamai [4/14/2008 5:42 AM 14336]
R2 aswFsBlk;aswFsBlk;c:\windows\system32\drivers\aswFsBlk.sys [8/17/2010 12:12 AM 19544]
R2 NPF;NetGroup Packet Filter Driver;c:\windows\system32\drivers\npf.sys [10/20/2009 1:19 PM 50704]
R3 radpms;Driver for RADPMS Device;c:\windows\system32\drivers\radpms.sys [7/24/2008 7:45 PM 12192]
S2 clr_optimization_v4.0.30319_32;Microsoft .NET Framework NGEN v4.0.30319_X86;c:\windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe [3/18/2010 1:16 PM 130384]
S2 LMIInfo;LogMeIn Kernel Information Provider;\??\c:\program files\LogMeIn\x86\RaInfo.sys --> c:\program files\LogMeIn\x86\RaInfo.sys [?]
S3 cpuz130;cpuz130;\??\c:\docume~1\Samuel\LOCALS~1\Temp\cpuz130\cpuz_x32.sys --> c:\docume~1\Samuel\LOCALS~1\Temp\cpuz130\cpuz_x32.sys [?]
S3 EagleXNt;EagleXNt;\??\c:\windows\system32\drivers\EagleXNt.sys --> c:\windows\system32\drivers\EagleXNt.sys [?]
S3 npggsvc;nProtect GameGuard Service;c:\windows\system32\GameMon.des -service --> c:\windows\system32\GameMon.des -service [?]
S3 WinRM;Windows Remote Management (WS-Management);c:\windows\system32\svchost.exe -k WINRM [4/14/2008 5:42 AM 14336]
S3 WPFFontCache_v0400;Windows Presentation Foundation Font Cache 4.0.0.0;c:\windows\Microsoft.NET\Framework\v4.0.30319\WPF\WPFFontCache_v0400.exe [3/18/2010 1:16 PM 753504]
S3 XDva037;XDva037;\??\c:\windows\system32\XDva037.sys --> c:\windows\system32\XDva037.sys [?]
S3 XDva190;XDva190;\??\c:\windows\system32\XDva190.sys --> c:\windows\system32\XDva190.sys [?]
S3 XDva346;XDva346;\??\c:\windows\system32\XDva346.sys --> c:\windows\system32\XDva346.sys [?]
S3 XDva347;XDva347;\??\c:\windows\system32\XDva347.sys --> c:\windows\system32\XDva347.sys [?]
S4 PuranDefrag;PuranDefrag;c:\windows\system32\PuranDefragS.exe [5/7/2011 8:28 PM 233472]
.
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\svchost]
WINRM REG_MULTI_SZ WINRM
Akamai REG_MULTI_SZ Akamai
.
Contents of the 'Scheduled Tasks' folder
.
.
------- Supplementary Scan -------
.
uStart Page = hxxp://global.netmarble.com/
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~2\Office12\EXCEL.EXE/3000
Trusted Zone: clonewarsadventures.com
Trusted Zone: freerealms.com
Trusted Zone: soe.com
Trusted Zone: sony.com
DPF: {AA07EBD2-EBDD-4BD6-9F8F-114BD513492C} - hxxp://disteng.nefficient.com/disteng/neffy/NeffyLauncher.cab
FF - ProfilePath - c:\documents and settings\Samuel\Application Data\Mozilla\Firefox\Profiles\nuyvtaef.default\
FF - prefs.js: browser.search.defaulturl - hxxp://www.bing.com/search?FORM=BSRTDF&PC=BBSR&q=
FF - prefs.js: browser.search.selectedEngine - Google
FF - prefs.js: browser.startup.homepage - www.google.com
FF - prefs.js: network.proxy.type - 4
.
- - - - ORPHANS REMOVED - - - -
.
WebBrowser-{CCC7A320-B3CA-4199-B1A6-9F516DD69829} - (no file)
WebBrowser-{D4027C7F-154A-4066-A1AD-4243D8127440} - (no file)
HKCU-Run-DAEMON Tools - c:\program files\DAEMON Tools\daemon.exe
HKCU-Run-DW6 - c:\program files\The Weather Channel FW\Desktop\DesktopWeather.exe
HKLM-Run-iTunesHelper - c:\program files\iTunes\iTunesHelper.exe
HKLM-Run-LogMeIn GUI - c:\program files\LogMeIn\x86\LogMeInSystray.exe
ShellExecuteHooks-{CB0A0BE8-AF3C-B1D2-C901-A0C141D91972} - (no file)
MSConfigStartUp-FreeCall - c:\program files\FreeCall.com\FreeCall\FreeCall.exe
MSConfigStartUp-iTunesHelper - c:\program files\iTunes\iTunesHelper.exe
MSConfigStartUp-nwiz - nwiz.exe
MSConfigStartUp-SeekmoSA - c:\program files\Seekmo\bin\10.0.406.0\SeekmoSA.exe
AddRemove-KLiteCodecPack_is1 - c:\program files\K-Lite Codec Pack\unins000.exe
AddRemove-NVIDIA Display Control Panel - c:\program files\NVIDIA Corporation\Uninstall\nvuninst.exe
AddRemove-{EA2DB6E0-72C5-4ef9-A3A0-E6705F4A6A9E} - c:\documents and settings\All Users\Application Data\NexonUS\NGM\NGM.exe
.
.
.
**************************************************************************
.
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2011-05-09 22:14
Windows 5.1.2600 Service Pack 3 NTFS
.
scanning hidden processes ...
.
scanning hidden autostart entries ...
.
scanning hidden files ...
.
.
c:\docume~1\Samuel\LOCALS~1\Temp\RGI1.tmp
.
scan completed successfully
hidden files: 1
.
**************************************************************************
.
Stealth MBR rootkit/Mebroot/Sinowal/TDL4 detector 0.4.2 by Gmer, http://www.gmer.net
Windows 5.1.2600 Disk: WDC_WD1600AAJS-75PSA0 rev.05.06H05 -> Harddisk0\DR0 -> \Device\00000032
.
device: opened successfully
user: MBR read successfully
.
Disk trace:
called modules: ntkrnlpa.exe CLASSPNP.SYS disk.sys ACPI.sys hal.dll >>UNKNOWN [0x85D3D4F0]<<
_asm { PUSH EBP; MOV EBP, ESP; PUSH ECX; MOV EAX, [EBP+0x8]; CMP EAX, [0x85d437d0]; MOV EAX, [0x85d4384c]; PUSH EBX; PUSH ESI; MOV ESI, [EBP+0xc]; MOV EBX, [ESI+0x60]; PUSH EDI; JNZ 0x20; MOV [EBP+0x8], EAX; }
1 ntkrnlpa!IofCallDriver[0x804EE130] -> \Device\Harddisk0\DR0[0x85E40AB8]
3 CLASSPNP[0xF74C7FD7] -> ntkrnlpa!IofCallDriver[0x804EE130] -> \Device\00000075[0x85CA2BA0]
5 ACPI[0xF7253620] -> ntkrnlpa!IofCallDriver[0x804EE130] -> [0x85D88030]
\Driver\nvata[0x85D4EDF0] -> IRP_MJ_CREATE -> 0x85D3D4F0
error: Read The system cannot find the file specified.
kernel: MBR read successfully
_asm { XOR AX, AX; MOV SS, AX; MOV SP, 0x7c00; STI ; PUSH AX; POP ES; PUSH AX; POP DS; CLD ; MOV SI, 0x7c1b; MOV DI, 0x61b; PUSH AX; PUSH DI; MOV CX, 0x1e5; REP MOVSB ; RETF ; MOV BP, 0x7be; MOV CL, 0x4; CMP [BP+0x0], CH; JL 0x2e; JNZ 0x3a; }
detected disk devices:
\Device\00000073 -> \??\IDE#DiskWDC_WD1600AAJS-75PSA0___________________05.06H05#2020202057202D444D5750413839313637343834#{53f56307-b6bf-11d0-94f2-00a0c91efb8b} device not found
detected hooks:
user & kernel MBR OK
Warning: possible TDL3 rootkit infection !
.
**************************************************************************
.
[HKEY_LOCAL_MACHINE\System\ControlSet001\Services\npggsvc]
"ImagePath"="c:\windows\system32\GameMon.des -service"
.
--------------------- LOCKED REGISTRY KEYS ---------------------
.
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}]
@Denied: (A 2) (Everyone)
@="FlashBroker"
"LocalizedString"="@c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10l_ActiveX.exe,-101"
.
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\Elevation]
"Enabled"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\LocalServer32]
@="c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10l_ActiveX.exe"
.
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
.
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}]
@Denied: (A 2) (Everyone)
@="IFlashBroker4"
.
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\ProxyStubClsid32]
@="{00020424-0000-0000-C000-000000000046}"
.
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
"Version"="1.0"
.
--------------------- DLLs Loaded Under Running Processes ---------------------
.
- - - - - - - > 'winlogon.exe'(736)
c:\windows\system32\WININET.dll
c:\windows\system32\LMIinit.dll
c:\windows\system32\LMIRfsClientNP.dll
.
- - - - - - - > 'lsass.exe'(804)
c:\windows\system32\WININET.dll
.
- - - - - - - > 'explorer.exe'(2720)
c:\windows\system32\WININET.dll
c:\windows\WinSxS\x86_Microsoft.VC80.CRT_1fc8b3b9a1e18e3b_8.0.50727.4053_x-ww_e6967989\MSVCR80.dll
.
------------------------ Other Running Processes ------------------------
.
c:\windows\system32\nvsvc32.exe
c:\program files\Alwil Software\Avast5\AvastSvc.exe
c:\windows\RTHDCPL.EXE
c:\windows\system32\RUNDLL32.EXE
c:\windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe
c:\program files\Bonjour\mDNSResponder.exe
c:\program files\Java\jre6\bin\jqs.exe
c:\program files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE
c:\windows\system32\PnkBstrA.exe
c:\windows\system32\PnkBstrB.exe
.
**************************************************************************
.
Completion time: 2011-05-09 22:31:36 - machine was rebooted
ComboFix-quarantined-files.txt 2011-05-10 03:31
.
Pre-Run: 112,539,287,552 bytes free
Post-Run: 112,397,852,672 bytes free
.
WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
[boot loader]
timeout=2
default=multi(0)disk(0)rdisk(0)partition(3)\WINDOWS
[operating systems]
c:\cmdcons\BOOTSECT.DAT="Microsoft Windows Recovery Console" /cmdcons
UnsupportedDebug="do not select this" /debug
multi(0)disk(0)rdisk(0)partition(3)\WINDOWS="Microsoft Windows XP Professional" /noexecute=optin /fastdetect
.
- - End Of File - - 909094A20BFEE53EE875E2C9E5228403
Microsoft Windows XP Professional 5.1.2600.3.1252.1.1033.18.958.683 [GMT -5:00]
Running from: c:\documents and settings\Samuel\Desktop\ComboFix.exe
AV: AntiVir Desktop *Enabled/Outdated* {AD166499-45F9-482A-A743-FDD3350758C7}
AV: avast! Antivirus *Disabled/Updated* {7591DB91-41F0-48A3-B128-1A293FD8233D}
AV: Symantec AntiVirus Corporate Edition *Enabled/Outdated* {FB06448E-52B8-493A-90F3-E43226D3305C}
.
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
.
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}\chrome.manifest
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}\chrome\content\_cfg.js
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}\chrome\content\overlay.xul
c:\documents and settings\Samuel\Local Settings\Application Data\{1C40CF7A-C356-4144-B10B-67C1F1B5E71C}\install.rdf
c:\documents and settings\Samuel\WINDOWS
C:\install.exe
c:\program files\Common Files\rwri
c:\program files\Common Files\rwri\rwria.lck
c:\program files\Common Files\rwri\rwrid\class-barrel
c:\program files\Common Files\rwri\rwril.lck
c:\program files\Common Files\rwri\rwrim.lck
c:\program files\Mozilla Firefox\searchplugins\google_search.xml
c:\windows\system32\Ijl11.dll
.
.
((((((((((((((((((((((((((((((((((((((( Drivers/Services )))))))))))))))))))))))))))))))))))))))))))))))))
.
.
-------\Legacy_6TO4
-------\Legacy_MYWEBSEARCHSERVICE
-------\Legacy_TDSSSERV.SYS
-------\Service_6to4
.
.
((((((((((((((((((((((((( Files Created from 2011-04-10 to 2011-05-10 )))))))))))))))))))))))))))))))
.
.
2011-05-10 03:12 . 2011-05-10 03:12 -------- d-sh--w- c:\documents and settings\LocalService\IETldCache
2011-05-08 01:28 . 2011-04-08 21:06 233472 ----a-w- c:\windows\system32\PuranDefragS.exe
2011-05-08 01:28 . 2011-04-08 21:06 229376 ----a-w- c:\windows\system32\PuranDC.exe
2011-05-08 01:28 . 2011-04-08 21:06 1114112 ----a-w- c:\windows\system32\PuranFD.exe
2011-05-08 01:28 . 2011-04-08 21:06 109056 ----a-w- c:\windows\system32\PuranDefragBT.exe
2011-05-08 01:28 . 2009-12-31 19:02 212992 ----a-w- c:\windows\system32\PuranDefrag.dll
2011-05-08 01:28 . 2011-05-08 01:28 -------- d-----w- c:\program files\Puran Defrag
2011-05-07 01:43 . 2011-05-07 01:43 781272 ----a-w- c:\program files\Mozilla Firefox\mozsqlite3.dll
2011-05-07 01:43 . 2011-05-07 01:43 1874904 ----a-w- c:\program files\Mozilla Firefox\mozjs.dll
2011-05-07 01:43 . 2011-05-07 01:43 89048 ----a-w- c:\program files\Mozilla Firefox\libEGL.dll
2011-05-07 01:43 . 2011-05-07 01:43 465880 ----a-w- c:\program files\Mozilla Firefox\libGLESv2.dll
2011-05-07 01:43 . 2011-05-07 01:43 15832 ----a-w- c:\program files\Mozilla Firefox\mozalloc.dll
2011-05-07 01:43 . 2011-05-07 01:43 1892184 ----a-w- c:\program files\Mozilla Firefox\d3dx9_42.dll
2011-05-07 01:43 . 2011-05-07 01:43 1974616 ----a-w- c:\program files\Mozilla Firefox\D3DCompiler_42.dll
2011-05-07 01:43 . 2011-05-07 01:43 142296 ----a-w- c:\program files\Mozilla Firefox\components\browsercomps.dll
2011-05-04 23:05 . 2011-05-04 23:05 388096 ----a-r- c:\documents and settings\Samuel\Application Data\Microsoft\Installer\{45A66726-69BC-466B-A7A4-12FCBA4883D7}\HiJackThis.exe
2011-05-04 22:43 . 2011-05-04 22:43 -------- d-----w- c:\documents and settings\Samuel\temp
2011-05-01 23:03 . 2011-05-06 19:43 -------- d-----w- c:\program files\Silkroad
2011-05-01 22:29 . 2011-05-01 22:33 125976576 ----a-w- C:\SilkroadOnline_GlobalOfficial_v1_298.exe
2011-05-01 22:24 . 2011-05-01 23:00 40630489 ----a-w- C:\SilkroadOnline_GlobalOfficial_v1_298(for_v1_295_297).exe
2011-04-18 07:06 . 2009-07-13 20:24 378408 ----a-w- c:\windows\glbNMDownloaderUpdater.exe
2011-04-18 07:06 . 2009-07-31 00:32 804368 ----a-w- c:\windows\GlbNMUpdater.exe
2011-04-18 07:05 . 2010-11-22 19:20 475136 ----a-w- c:\windows\npGlbNMFFUpdaterModule.dll
2011-04-18 07:05 . 2010-11-22 19:13 90112 ----a-w- c:\windows\GlbNMVistaUpdater.exe
2011-04-18 07:04 . 2001-09-05 09:18 77824 ----a-w- c:\program files\Common Files\InstallShield\Engine\6\Intel 32\ctor.dll
2011-04-18 07:04 . 2001-09-05 09:18 225280 ------w- c:\program files\Common Files\InstallShield\IScript\iscript.dll
2011-04-18 07:04 . 2001-09-05 09:14 176128 ------w- c:\program files\Common Files\InstallShield\Engine\6\Intel 32\iuser.dll
2011-04-18 07:04 . 2001-09-05 09:13 32768 ------w- c:\program files\Common Files\InstallShield\Engine\6\Intel 32\objectps.dll
2011-04-18 07:04 . 2002-07-25 21:07 614532 ----a-w- c:\program files\Common Files\InstallShield\Engine\6\Intel 32\IKernel.exe
2011-04-17 09:51 . 2011-02-23 13:56 371544 ----a-w- c:\windows\system32\drivers\aswSnx.sys
2011-04-14 03:58 . 2011-04-29 04:26 -------- d-----w- c:\program files\Tales of Pirates II
2011-04-10 21:28 . 2011-05-05 18:54 -------- d-----w- c:\documents and settings\All Users\Application Data\Skype Extras
2011-04-10 21:27 . 2011-04-10 21:27 -------- d-----w- c:\program files\Common Files\Skype
.
.
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2011-04-08 11:28 . 2011-04-08 11:28 41872 ----a-w- c:\windows\system32\xfcodec.dll
2011-03-01 19:29 . 2009-08-29 03:59 3912008 ----a-w- c:\windows\system32\GameMon.des
2011-02-23 14:04 . 2010-08-17 05:12 40648 ----a-w- c:\windows\avastSS.scr
2011-02-23 14:04 . 2010-08-17 05:12 190016 ----a-w- c:\windows\system32\aswBoot.exe
2011-02-23 13:56 . 2010-08-17 05:12 301528 ----a-w- c:\windows\system32\drivers\aswSP.sys
2011-02-23 13:55 . 2010-08-17 05:12 49240 ----a-w- c:\windows\system32\drivers\aswTdi.sys
2011-02-23 13:55 . 2010-08-17 05:12 102232 ----a-w- c:\windows\system32\drivers\aswmon2.sys
2011-02-23 13:55 . 2010-08-17 05:12 96344 ----a-w- c:\windows\system32\drivers\aswmon.sys
2011-02-23 13:55 . 2010-08-17 05:12 25432 ----a-w- c:\windows\system32\drivers\aswRdr.sys
2011-02-23 13:54 . 2010-08-17 05:12 30680 ----a-w- c:\windows\system32\drivers\aavmker4.sys
2011-02-23 13:54 . 2010-08-17 05:12 19544 ----a-w- c:\windows\system32\drivers\aswFsBlk.sys
2009-02-24 19:34 . 2009-02-24 19:34 1044480 ----a-w- c:\program files\mozilla firefox\plugins\libdivx.dll
2009-02-24 19:34 . 2009-02-24 19:34 200704 ----a-w- c:\program files\mozilla firefox\plugins\ssldivx.dll
2011-05-07 01:43 . 2011-05-07 01:43 142296 ----a-w- c:\program files\mozilla firefox\components\browsercomps.dll
.
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
.
[HKEY_LOCAL_MACHINE\~\Browser Helper Objects\{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}]
2010-12-09 18:51 3911776 ----a-w- c:\program files\uTorrentBar\tbuTor.dll
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Toolbar]
"{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}"= "c:\program files\uTorrentBar\tbuTor.dll" [2010-12-09 3911776]
.
[HKEY_CLASSES_ROOT\clsid\{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}]
.
[HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar\Webbrowser]
"{BF7380FA-E3B4-4DB2-AF3E-9D8783A45BFC}"= "c:\program files\uTorrentBar\tbuTor.dll" [2010-12-09 3911776]
.
[HKEY_CLASSES_ROOT\clsid\{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}]
.
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\explorer\shelliconoverlayidentifiers\00avast]
@="{472083B0-C522-11CF-8763-00608CC02F24}"
[HKEY_CLASSES_ROOT\CLSID\{472083B0-C522-11CF-8763-00608CC02F24}]
2011-02-23 14:04 122512 ----a-w- c:\program files\Alwil Software\Avast5\ashShell.dll
.
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"igndlm.exe"="c:\program files\Download Manager\DLM.exe" [2009-05-15 1103216]
"BitTorrent DNA"="c:\program files\DNA\btdna.exe" [2009-11-13 323392]
"DAEMON Tools Lite"="c:\program files\DAEMON Tools Lite\DTLite.exe" [2010-04-01 357696]
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"QuickTime Task"="c:\program files\QuickTime\qttask.exe" [2009-01-05 413696]
"SunJavaUpdateSched"="c:\program files\Common Files\Java\Java Update\jusched.exe" [2010-02-18 248040]
"RTHDCPL"="RTHDCPL.EXE" [2007-05-28 16132608]
"GrooveMonitor"="c:\program files\Microsoft Office\Office12\GrooveMonitor.exe" [2008-10-25 31072]
"avast5"="c:\progra~1\ALWILS~1\Avast5\avastUI.exe" [2011-02-23 3451496]
"nwiz"="c:\program files\NVIDIA Corporation\nView\nwiz.exe" [2010-07-08 1753192]
"NvCplDaemon"="c:\windows\system32\NvCpl.dll" [2010-07-09 13923432]
"NvMediaCenter"="c:\windows\system32\NvMcTray.dll" [2010-07-09 110696]
.
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\RunOnce]
"tscuninstall"="c:\windows\system32\tscupgrd.exe" [2007-12-16 40448]
.
c:\documents and settings\Samuel\Start Menu\Programs\Startup\
CurseClientStartup.ccip [2010-2-1 0]
.
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\winlogon\notify\LMIinit]
2008-10-17 02:35 87352 ----a-w- c:\windows\system32\LMIinit.dll
.
[HKEY_LOCAL_MACHINE\system\currentcontrolset\control\securityproviders]
SecurityProviders msapsspc.dll, schannel.dll, digest.dll, credssp.dll, msnsspc.dll
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\Adobe Reader Speed Launcher]
2007-10-11 01:51 39792 -c--a-w- c:\program files\Adobe\Reader 8.0\Reader\reader_sl.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\MSMSGS]
2007-10-31 06:32 1695232 ------w- c:\program files\Messenger\msmsgs.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\NvCplDaemon]
2010-07-09 21:24 13923432 ----a-w- c:\windows\system32\nvcpl.dll
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\NvMediaCenter]
2010-07-09 21:24 110696 ----a-w- c:\windows\system32\nvmctray.dll
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\QuickTime Task]
2009-01-05 22:18 413696 ----a-w- c:\program files\QuickTime\QTTask.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\Skype]
2011-04-01 23:17 15145352 ----a-r- c:\program files\Skype\Phone\Skype.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\SunJavaUpdateSched]
2007-09-25 07:11 132496 -c--a-w- c:\program files\Java\jre1.6.0_03\bin\jusched.exe
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusOverride"=dword:00000001
"FirewallOverride"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring]
"DisableMonitoring"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecAntiVirus]
"DisableMonitoring"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecFirewall]
"DisableMonitoring"=dword:00000001
.
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile]
"DisableNotifications"= 1 (0x1)
.
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\Network Diagnostic\\xpnetdiag.exe"=
"%windir%\\system32\\sessmgr.exe"=
"c:\\WINDOWS\\system32\\dplaysvr.exe"=
"c:\\Program Files\\DNA\\btdna.exe"=
"c:\\Program Files\\Xfire\\xfire.exe"=
"c:\\Program Files\\Bonjour\\mDNSResponder.exe"=
"c:\\Program Files\\uTorrent\\uTorrent.exe"=
"c:\\Documents and Settings\\Samuel\\Local Settings\\Application Data\\Dyyno Receiver\\DPPM.exe"=
"c:\\Program Files\\Mozilla Firefox\\firefox.exe"=
"c:\\Program Files\\Kaiba Corp VDS\\KCVDS.exe"=
"c:\\Program Files\\Java\\jre6\\bin\\java.exe"=
"c:\\Program Files\\Warcraft III\\war3.exe"=
"c:\\WINDOWS\\Downloaded Program Files\\PurpleBean.exe"=
"c:\\Program Files\\Skype\\Plugin Manager\\skypePM.exe"=
"c:\\Documents and Settings\\Samuel\\My Documents\\Downloads\\GhostOne\\GHostOne\\ghost.exe"=
"c:\\Documents and Settings\\Samuel\\My Documents\\Downloads\\GhostOne\\GHostOne\\GHostOne.exe"=
"c:\\Program Files\\Microsoft Office\\Office12\\OUTLOOK.EXE"=
"c:\\Program Files\\Microsoft Office\\Office12\\GROOVE.EXE"=
"c:\\Program Files\\Microsoft Office\\Office12\\ONENOTE.EXE"=
"c:\\Program Files\\Pando Networks\\Media Booster\\PMB.exe"=
"c:\\Program Files\\Skype\\Phone\\Skype.exe"=
"c:\\Program Files\\TeamViewer\\Version5\\TeamViewer.exe"=
.
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"22297:TCP"= 22297:TCP:BitComet 22297 TCP
"22297:UDP"= 22297:UDP:BitComet 22297 UDP
"26485:TCP"= 26485:TCP:BitComet 26485 TCP
"26485:UDP"= 26485:UDP:BitComet 26485 UDP
"3389:TCP"= 3389:TCP:*:Disabled:@xpsp2res.dll,-22009
"6112:TCP"= 6112:TCP:Warcraft
"58513:TCP"= 58513:TCP:Pando Media Booster
"58513:UDP"= 58513:UDP:Pando Media Booster
"3724:TCP"= 3724:TCP:Blizzard Downloader: 3724
"8376:TCP"= 8376:TCP:League of Legends Launcher
"8376:UDP"= 8376:UDP:League of Legends Launcher
"56234:TCP"= 56234:TCP:Pando Media Booster
"56234:UDP"= 56234:UDP:Pando Media Booster
"5985:TCP"= 5985:TCP:*:Disabled:Windows Remote Management
"57235:TCP"= 57235:TCP:Pando Media Booster
"57235:UDP"= 57235:UDP:Pando Media Booster
"8378:TCP"= 8378:TCP:League of Legends Launcher
"8378:UDP"= 8378:UDP:League of Legends Launcher
"8379:TCP"= 8379:TCP:League of Legends Launcher
"8379:UDP"= 8379:UDP:League of Legends Launcher
"58057:TCP"= 58057:TCP:Pando Media Booster
"58057:UDP"= 58057:UDP:Pando Media Booster
"57452:TCP"= 57452:TCP:Pando Media Booster
"57452:UDP"= 57452:UDP:Pando Media Booster
"1034:TCP"= 1034:TCP:Akamai NetSession Interface
"5000:UDP"= 5000:UDP:Akamai NetSession Interface
.
R0 sptd;sptd;c:\windows\system32\drivers\sptd.sys [2/19/2009 10:58 AM 691696]
R1 aswSnx;aswSnx;c:\windows\system32\drivers\aswSnx.sys [4/17/2011 4:51 AM 371544]
R1 aswSP;aswSP;c:\windows\system32\drivers\aswSP.sys [8/17/2010 12:12 AM 301528]
R2 Akamai;Akamai NetSession Interface;c:\windows\System32\svchost.exe -k Akamai [4/14/2008 5:42 AM 14336]
R2 aswFsBlk;aswFsBlk;c:\windows\system32\drivers\aswFsBlk.sys [8/17/2010 12:12 AM 19544]
R2 NPF;NetGroup Packet Filter Driver;c:\windows\system32\drivers\npf.sys [10/20/2009 1:19 PM 50704]
R3 radpms;Driver for RADPMS Device;c:\windows\system32\drivers\radpms.sys [7/24/2008 7:45 PM 12192]
S2 clr_optimization_v4.0.30319_32;Microsoft .NET Framework NGEN v4.0.30319_X86;c:\windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe [3/18/2010 1:16 PM 130384]
S2 LMIInfo;LogMeIn Kernel Information Provider;\??\c:\program files\LogMeIn\x86\RaInfo.sys --> c:\program files\LogMeIn\x86\RaInfo.sys [?]
S3 cpuz130;cpuz130;\??\c:\docume~1\Samuel\LOCALS~1\Temp\cpuz130\cpuz_x32.sys --> c:\docume~1\Samuel\LOCALS~1\Temp\cpuz130\cpuz_x32.sys [?]
S3 EagleXNt;EagleXNt;\??\c:\windows\system32\drivers\EagleXNt.sys --> c:\windows\system32\drivers\EagleXNt.sys [?]
S3 npggsvc;nProtect GameGuard Service;c:\windows\system32\GameMon.des -service --> c:\windows\system32\GameMon.des -service [?]
S3 WinRM;Windows Remote Management (WS-Management);c:\windows\system32\svchost.exe -k WINRM [4/14/2008 5:42 AM 14336]
S3 WPFFontCache_v0400;Windows Presentation Foundation Font Cache 4.0.0.0;c:\windows\Microsoft.NET\Framework\v4.0.30319\WPF\WPFFontCache_v0400.exe [3/18/2010 1:16 PM 753504]
S3 XDva037;XDva037;\??\c:\windows\system32\XDva037.sys --> c:\windows\system32\XDva037.sys [?]
S3 XDva190;XDva190;\??\c:\windows\system32\XDva190.sys --> c:\windows\system32\XDva190.sys [?]
S3 XDva346;XDva346;\??\c:\windows\system32\XDva346.sys --> c:\windows\system32\XDva346.sys [?]
S3 XDva347;XDva347;\??\c:\windows\system32\XDva347.sys --> c:\windows\system32\XDva347.sys [?]
S4 PuranDefrag;PuranDefrag;c:\windows\system32\PuranDefragS.exe [5/7/2011 8:28 PM 233472]
.
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\svchost]
WINRM REG_MULTI_SZ WINRM
Akamai REG_MULTI_SZ Akamai
.
Contents of the 'Scheduled Tasks' folder
.
.
------- Supplementary Scan -------
.
uStart Page = hxxp://global.netmarble.com/
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~2\Office12\EXCEL.EXE/3000
Trusted Zone: clonewarsadventures.com
Trusted Zone: freerealms.com
Trusted Zone: soe.com
Trusted Zone: sony.com
DPF: {AA07EBD2-EBDD-4BD6-9F8F-114BD513492C} - hxxp://disteng.nefficient.com/disteng/neffy/NeffyLauncher.cab
FF - ProfilePath - c:\documents and settings\Samuel\Application Data\Mozilla\Firefox\Profiles\nuyvtaef.default\
FF - prefs.js: browser.search.defaulturl - hxxp://www.bing.com/search?FORM=BSRTDF&PC=BBSR&q=
FF - prefs.js: browser.search.selectedEngine - Google
FF - prefs.js: browser.startup.homepage - www.google.com
FF - prefs.js: network.proxy.type - 4
.
- - - - ORPHANS REMOVED - - - -
.
WebBrowser-{CCC7A320-B3CA-4199-B1A6-9F516DD69829} - (no file)
WebBrowser-{D4027C7F-154A-4066-A1AD-4243D8127440} - (no file)
HKCU-Run-DAEMON Tools - c:\program files\DAEMON Tools\daemon.exe
HKCU-Run-DW6 - c:\program files\The Weather Channel FW\Desktop\DesktopWeather.exe
HKLM-Run-iTunesHelper - c:\program files\iTunes\iTunesHelper.exe
HKLM-Run-LogMeIn GUI - c:\program files\LogMeIn\x86\LogMeInSystray.exe
ShellExecuteHooks-{CB0A0BE8-AF3C-B1D2-C901-A0C141D91972} - (no file)
MSConfigStartUp-FreeCall - c:\program files\FreeCall.com\FreeCall\FreeCall.exe
MSConfigStartUp-iTunesHelper - c:\program files\iTunes\iTunesHelper.exe
MSConfigStartUp-nwiz - nwiz.exe
MSConfigStartUp-SeekmoSA - c:\program files\Seekmo\bin\10.0.406.0\SeekmoSA.exe
AddRemove-KLiteCodecPack_is1 - c:\program files\K-Lite Codec Pack\unins000.exe
AddRemove-NVIDIA Display Control Panel - c:\program files\NVIDIA Corporation\Uninstall\nvuninst.exe
AddRemove-{EA2DB6E0-72C5-4ef9-A3A0-E6705F4A6A9E} - c:\documents and settings\All Users\Application Data\NexonUS\NGM\NGM.exe
.
.
.
**************************************************************************
.
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2011-05-09 22:14
Windows 5.1.2600 Service Pack 3 NTFS
.
scanning hidden processes ...
.
scanning hidden autostart entries ...
.
scanning hidden files ...
.
.
c:\docume~1\Samuel\LOCALS~1\Temp\RGI1.tmp
.
scan completed successfully
hidden files: 1
.
**************************************************************************
.
Stealth MBR rootkit/Mebroot/Sinowal/TDL4 detector 0.4.2 by Gmer, http://www.gmer.net
Windows 5.1.2600 Disk: WDC_WD1600AAJS-75PSA0 rev.05.06H05 -> Harddisk0\DR0 -> \Device\00000032
.
device: opened successfully
user: MBR read successfully
.
Disk trace:
called modules: ntkrnlpa.exe CLASSPNP.SYS disk.sys ACPI.sys hal.dll >>UNKNOWN [0x85D3D4F0]<<
_asm { PUSH EBP; MOV EBP, ESP; PUSH ECX; MOV EAX, [EBP+0x8]; CMP EAX, [0x85d437d0]; MOV EAX, [0x85d4384c]; PUSH EBX; PUSH ESI; MOV ESI, [EBP+0xc]; MOV EBX, [ESI+0x60]; PUSH EDI; JNZ 0x20; MOV [EBP+0x8], EAX; }
1 ntkrnlpa!IofCallDriver[0x804EE130] -> \Device\Harddisk0\DR0[0x85E40AB8]
3 CLASSPNP[0xF74C7FD7] -> ntkrnlpa!IofCallDriver[0x804EE130] -> \Device\00000075[0x85CA2BA0]
5 ACPI[0xF7253620] -> ntkrnlpa!IofCallDriver[0x804EE130] -> [0x85D88030]
\Driver\nvata[0x85D4EDF0] -> IRP_MJ_CREATE -> 0x85D3D4F0
error: Read The system cannot find the file specified.
kernel: MBR read successfully
_asm { XOR AX, AX; MOV SS, AX; MOV SP, 0x7c00; STI ; PUSH AX; POP ES; PUSH AX; POP DS; CLD ; MOV SI, 0x7c1b; MOV DI, 0x61b; PUSH AX; PUSH DI; MOV CX, 0x1e5; REP MOVSB ; RETF ; MOV BP, 0x7be; MOV CL, 0x4; CMP [BP+0x0], CH; JL 0x2e; JNZ 0x3a; }
detected disk devices:
\Device\00000073 -> \??\IDE#DiskWDC_WD1600AAJS-75PSA0___________________05.06H05#2020202057202D444D5750413839313637343834#{53f56307-b6bf-11d0-94f2-00a0c91efb8b} device not found
detected hooks:
user & kernel MBR OK
Warning: possible TDL3 rootkit infection !
.
**************************************************************************
.
[HKEY_LOCAL_MACHINE\System\ControlSet001\Services\npggsvc]
"ImagePath"="c:\windows\system32\GameMon.des -service"
.
--------------------- LOCKED REGISTRY KEYS ---------------------
.
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}]
@Denied: (A 2) (Everyone)
@="FlashBroker"
"LocalizedString"="@c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10l_ActiveX.exe,-101"
.
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\Elevation]
"Enabled"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\LocalServer32]
@="c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10l_ActiveX.exe"
.
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
.
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}]
@Denied: (A 2) (Everyone)
@="IFlashBroker4"
.
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\ProxyStubClsid32]
@="{00020424-0000-0000-C000-000000000046}"
.
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
"Version"="1.0"
.
--------------------- DLLs Loaded Under Running Processes ---------------------
.
- - - - - - - > 'winlogon.exe'(736)
c:\windows\system32\WININET.dll
c:\windows\system32\LMIinit.dll
c:\windows\system32\LMIRfsClientNP.dll
.
- - - - - - - > 'lsass.exe'(804)
c:\windows\system32\WININET.dll
.
- - - - - - - > 'explorer.exe'(2720)
c:\windows\system32\WININET.dll
c:\windows\WinSxS\x86_Microsoft.VC80.CRT_1fc8b3b9a1e18e3b_8.0.50727.4053_x-ww_e6967989\MSVCR80.dll
.
------------------------ Other Running Processes ------------------------
.
c:\windows\system32\nvsvc32.exe
c:\program files\Alwil Software\Avast5\AvastSvc.exe
c:\windows\RTHDCPL.EXE
c:\windows\system32\RUNDLL32.EXE
c:\windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe
c:\program files\Bonjour\mDNSResponder.exe
c:\program files\Java\jre6\bin\jqs.exe
c:\program files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE
c:\windows\system32\PnkBstrA.exe
c:\windows\system32\PnkBstrB.exe
.
**************************************************************************
.
Completion time: 2011-05-09 22:31:36 - machine was rebooted
ComboFix-quarantined-files.txt 2011-05-10 03:31
.
Pre-Run: 112,539,287,552 bytes free
Post-Run: 112,397,852,672 bytes free
.
WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
[boot loader]
timeout=2
default=multi(0)disk(0)rdisk(0)partition(3)\WINDOWS
[operating systems]
c:\cmdcons\BOOTSECT.DAT="Microsoft Windows Recovery Console" /cmdcons
UnsupportedDebug="do not select this" /debug
multi(0)disk(0)rdisk(0)partition(3)\WINDOWS="Microsoft Windows XP Professional" /noexecute=optin /fastdetect
.
- - End Of File - - 909094A20BFEE53EE875E2C9E5228403
#23

 Posted 10 May 2011 - 11:06 AM
Posted 10 May 2011 - 11:06 AM

Please read carefully and follow these steps.
- Download TDSSKiller and save it to your Desktop.
- Extract its contents to your desktop.
- Once extracted, open the TDSSKiller folder and doubleclick on TDSSKiller.exe to run the application, then on Start Scan.
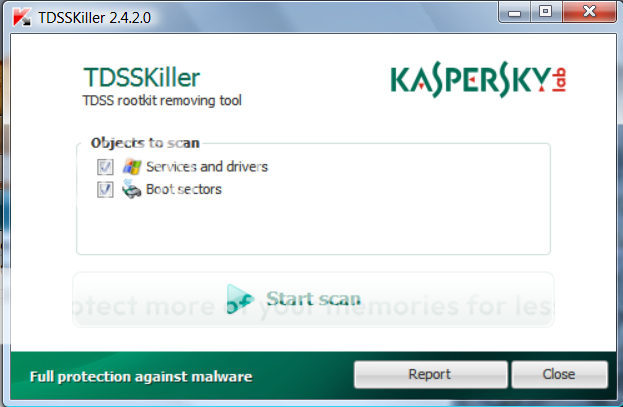
- If an infected file is detected, the default action will be Cure, click on Continue.

- If a suspicious file is detected, the default action will be Skip, click on Continue.
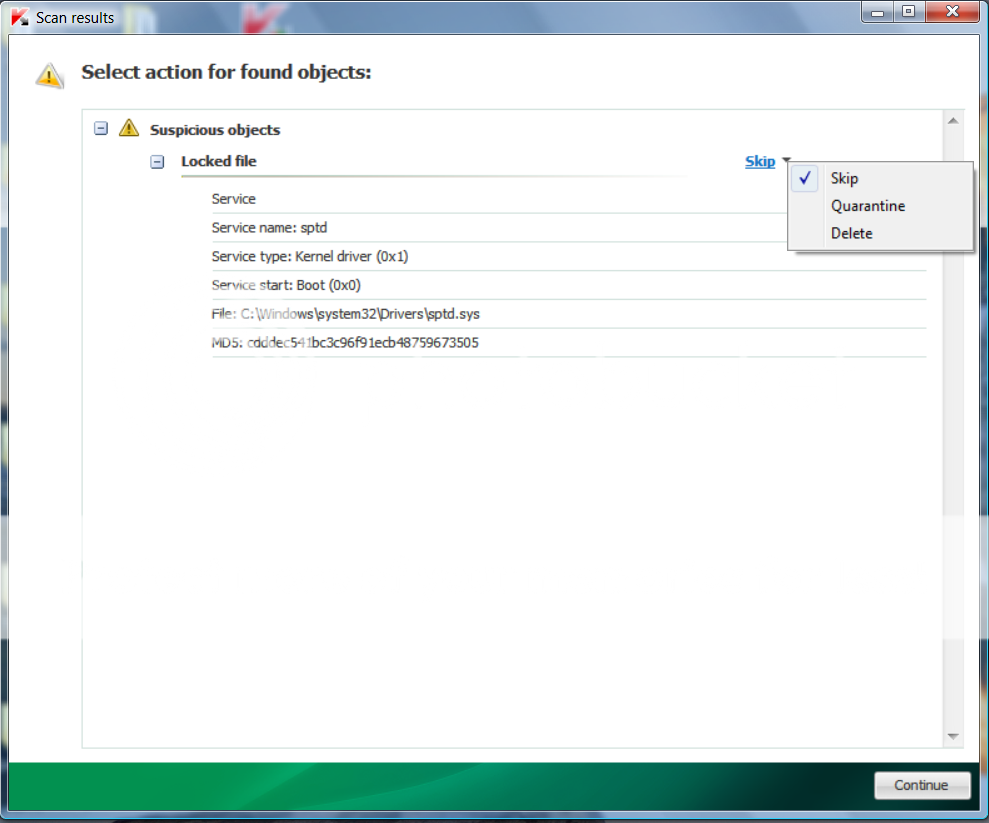
- It may ask you to reboot the computer to complete the process. Click on Reboot Now.

- If no reboot is require, click on Report. A log file should appear. Please copy and paste the contents of that file here.
- If a reboot is required, the report can also be found in your root directory, (usually C:\ folder) in the form of "TDSSKiller.[Version]_[Date]_[Time]_log.txt". Please copy and paste the contents of that file here.
#24

 Posted 10 May 2011 - 02:59 PM
Posted 10 May 2011 - 02:59 PM

2011/05/10 15:53:09.0515 1540 TDSS rootkit removing tool 2.5.0.0 May 1 2011 14:20:16
2011/05/10 15:53:10.0031 1540 ================================================================================
2011/05/10 15:53:10.0031 1540 SystemInfo:
2011/05/10 15:53:10.0031 1540
2011/05/10 15:53:10.0031 1540 OS Version: 5.1.2600 ServicePack: 3.0
2011/05/10 15:53:10.0031 1540 Product type: Workstation
2011/05/10 15:53:10.0031 1540 ComputerName: SAMUEL-D27BC6AB
2011/05/10 15:53:10.0031 1540 UserName: Samuel
2011/05/10 15:53:10.0031 1540 Windows directory: C:\WINDOWS
2011/05/10 15:53:10.0031 1540 System windows directory: C:\WINDOWS
2011/05/10 15:53:10.0031 1540 Processor architecture: Intel x86
2011/05/10 15:53:10.0031 1540 Number of processors: 1
2011/05/10 15:53:10.0031 1540 Page size: 0x1000
2011/05/10 15:53:10.0031 1540 Boot type: Safe boot with network
2011/05/10 15:53:10.0031 1540 ================================================================================
2011/05/10 15:53:10.0406 1540 Initialize success
2011/05/10 15:54:02.0234 1752 ================================================================================
2011/05/10 15:54:02.0234 1752 Scan started
2011/05/10 15:54:02.0234 1752 Mode: Manual;
2011/05/10 15:54:02.0234 1752 ================================================================================
2011/05/10 15:54:03.0406 1752 Aavmker4 (83631291adf2887cffc786d034d3fa15) C:\WINDOWS\system32\drivers\Aavmker4.sys
2011/05/10 15:54:03.0546 1752 ACPI (8fd99680a539792a30e97944fdaecf17) C:\WINDOWS\system32\DRIVERS\ACPI.sys
2011/05/10 15:54:03.0609 1752 ACPIEC (9859c0f6936e723e4892d7141b1327d5) C:\WINDOWS\system32\drivers\ACPIEC.sys
2011/05/10 15:54:03.0703 1752 aec (8bed39e3c35d6a489438b8141717a557) C:\WINDOWS\system32\drivers\aec.sys
2011/05/10 15:54:03.0781 1752 AFD (7e775010ef291da96ad17ca4b17137d7) C:\WINDOWS\System32\drivers\afd.sys
2011/05/10 15:54:04.0046 1752 AmdPPM (033448d435e65c4bd72e70521fd05c76) C:\WINDOWS\system32\DRIVERS\AmdPPM.sys
2011/05/10 15:54:04.0265 1752 aswFsBlk (1c2e6bb4fe8621b1b863855b02bc33eb) C:\WINDOWS\system32\drivers\aswFsBlk.sys
2011/05/10 15:54:04.0328 1752 aswMon2 (452d0ecd14fa02f9b061f42c8a30dd49) C:\WINDOWS\system32\drivers\aswMon2.sys
2011/05/10 15:54:04.0375 1752 aswRdr (b6a9373619d851be80fb5f1b5eed0d4e) C:\WINDOWS\system32\drivers\aswRdr.sys
2011/05/10 15:54:04.0484 1752 aswSnx (9be41c1ae8bc481eb662d85c98d979c2) C:\WINDOWS\system32\drivers\aswSnx.sys
2011/05/10 15:54:04.0609 1752 aswSP (4b1a54ba2bc5873a774df6b70ab8b0b3) C:\WINDOWS\system32\drivers\aswSP.sys
2011/05/10 15:54:04.0671 1752 aswTdi (c7f1cea32766184911293f4e1ee653f5) C:\WINDOWS\system32\drivers\aswTdi.sys
2011/05/10 15:54:04.0734 1752 AsyncMac (b153affac761e7f5fcfa822b9c4e97bc) C:\WINDOWS\system32\DRIVERS\asyncmac.sys
2011/05/10 15:54:04.0781 1752 atapi (9f3a2f5aa6875c72bf062c712cfa2674) C:\WINDOWS\system32\DRIVERS\atapi.sys
2011/05/10 15:54:04.0890 1752 Atmarpc (9916c1225104ba14794209cfa8012159) C:\WINDOWS\system32\DRIVERS\atmarpc.sys
2011/05/10 15:54:04.0953 1752 audstub (d9f724aa26c010a217c97606b160ed68) C:\WINDOWS\system32\DRIVERS\audstub.sys
2011/05/10 15:54:05.0015 1752 Beep (da1f27d85e0d1525f6621372e7b685e9) C:\WINDOWS\system32\drivers\Beep.sys
2011/05/10 15:54:05.0109 1752 cbidf2k (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\drivers\cbidf2k.sys
2011/05/10 15:54:05.0171 1752 Cdaudio (c1b486a7658353d33a10cc15211a873b) C:\WINDOWS\system32\drivers\Cdaudio.sys
2011/05/10 15:54:05.0203 1752 Cdfs (c885b02847f5d2fd45a24e219ed93b32) C:\WINDOWS\system32\drivers\Cdfs.sys
2011/05/10 15:54:05.0265 1752 Cdrom (1f4260cc5b42272d71f79e570a27a4fe) C:\WINDOWS\system32\DRIVERS\cdrom.sys
2011/05/10 15:54:05.0781 1752 Disk (044452051f3e02e7963599fc8f4f3e25) C:\WINDOWS\system32\DRIVERS\disk.sys
2011/05/10 15:54:05.0890 1752 dmboot (d992fe1274bde0f84ad826acae022a41) C:\WINDOWS\system32\drivers\dmboot.sys
2011/05/10 15:54:05.0937 1752 dmio (7c824cf7bbde77d95c08005717a95f6f) C:\WINDOWS\system32\DRIVERS\dmio.sys
2011/05/10 15:54:05.0984 1752 dmload (e9317282a63ca4d188c0df5e09c6ac5f) C:\WINDOWS\system32\drivers\dmload.sys
2011/05/10 15:54:06.0046 1752 DMusic (8a208dfcf89792a484e76c40e5f50b45) C:\WINDOWS\system32\drivers\DMusic.sys
2011/05/10 15:54:06.0140 1752 drmkaud (8f5fcff8e8848afac920905fbd9d33c8) C:\WINDOWS\system32\drivers\drmkaud.sys
2011/05/10 15:54:06.0265 1752 ENTECH (16ebd8bf1d5090923694cc972c7ce1b4) C:\WINDOWS\system32\DRIVERS\ENTECH.sys
2011/05/10 15:54:06.0359 1752 Fastfat (38d332a6d56af32635675f132548343e) C:\WINDOWS\system32\drivers\Fastfat.sys
2011/05/10 15:54:06.0421 1752 Fdc (92cdd60b6730b9f50f6a1a0c1f8cdc81) C:\WINDOWS\system32\drivers\Fdc.sys
2011/05/10 15:54:06.0500 1752 Fips (d45926117eb9fa946a6af572fbe1caa3) C:\WINDOWS\system32\drivers\Fips.sys
2011/05/10 15:54:06.0531 1752 Flpydisk (9d27e7b80bfcdf1cdd9b555862d5e7f0) C:\WINDOWS\system32\drivers\Flpydisk.sys
2011/05/10 15:54:06.0593 1752 FltMgr (b2cf4b0786f8212cb92ed2b50c6db6b0) C:\WINDOWS\system32\DRIVERS\fltMgr.sys
2011/05/10 15:54:06.0656 1752 Fs_Rec (3e1e2bd4f39b0e2b7dc4f4d2bcc2779a) C:\WINDOWS\system32\drivers\Fs_Rec.sys
2011/05/10 15:54:06.0734 1752 Ftdisk (6ac26732762483366c3969c9e4d2259d) C:\WINDOWS\system32\DRIVERS\ftdisk.sys
2011/05/10 15:54:06.0812 1752 GEARAspiWDM (ab8a6a87d9d7255c3884d5b9541a6e80) C:\WINDOWS\system32\Drivers\GEARAspiWDM.sys
2011/05/10 15:54:06.0890 1752 Gpc (0a02c63c8b144bd8c86b103dee7c86a2) C:\WINDOWS\system32\DRIVERS\msgpc.sys
2011/05/10 15:54:06.0953 1752 hamachi (7929a161f9951d173ca9900fe7067391) C:\WINDOWS\system32\DRIVERS\hamachi.sys
2011/05/10 15:54:07.0015 1752 HDAudBus (573c7d0a32852b48f3058cfd8026f511) C:\WINDOWS\system32\DRIVERS\HDAudBus.sys
2011/05/10 15:54:07.0093 1752 hidusb (ccf82c5ec8a7326c3066de870c06daf1) C:\WINDOWS\system32\DRIVERS\hidusb.sys
2011/05/10 15:54:07.0187 1752 HSFHWBS2 (77e4ff0b73bc0aeaaf39bf0c8104231f) C:\WINDOWS\system32\DRIVERS\HSFHWBS2.sys
2011/05/10 15:54:07.0250 1752 HSF_DP (60e1604729a15ef4a3b05f298427b3b1) C:\WINDOWS\system32\DRIVERS\HSF_DP.sys
2011/05/10 15:54:07.0328 1752 HTTP (f80a415ef82cd06ffaf0d971528ead38) C:\WINDOWS\system32\Drivers\HTTP.sys
2011/05/10 15:54:07.0453 1752 i8042prt (4a0b06aa8943c1e332520f7440c0aa30) C:\WINDOWS\system32\drivers\i8042prt.sys
2011/05/10 15:54:07.0546 1752 Imapi (083a052659f5310dd8b6a6cb05edcf8e) C:\WINDOWS\system32\DRIVERS\imapi.sys
2011/05/10 15:54:07.0750 1752 IntcAzAudAddService (39a817320087ef1c851d7a8f1701b3e0) C:\WINDOWS\system32\drivers\RtkHDAud.sys
2011/05/10 15:54:07.0937 1752 Ip6Fw (3bb22519a194418d5fec05d800a19ad0) C:\WINDOWS\system32\DRIVERS\Ip6Fw.sys
2011/05/10 15:54:07.0984 1752 IpFilterDriver (731f22ba402ee4b62748adaf6363c182) C:\WINDOWS\system32\DRIVERS\ipfltdrv.sys
2011/05/10 15:54:08.0015 1752 IpInIp (b87ab476dcf76e72010632b5550955f5) C:\WINDOWS\system32\DRIVERS\ipinip.sys
2011/05/10 15:54:08.0078 1752 IpNat (cc748ea12c6effde940ee98098bf96bb) C:\WINDOWS\system32\DRIVERS\ipnat.sys
2011/05/10 15:54:08.0156 1752 IPSec (23c74d75e36e7158768dd63d92789a91) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2011/05/10 15:54:08.0234 1752 IRENUM (c93c9ff7b04d772627a3646d89f7bf89) C:\WINDOWS\system32\DRIVERS\irenum.sys
2011/05/10 15:54:08.0296 1752 isapnp (05a299ec56e52649b1cf2fc52d20f2d7) C:\WINDOWS\system32\DRIVERS\isapnp.sys
2011/05/10 15:54:08.0328 1752 Kbdclass (463c1ec80cd17420a542b7f36a36f128) C:\WINDOWS\system32\DRIVERS\kbdclass.sys
2011/05/10 15:54:08.0343 1752 kbdhid (9ef487a186dea361aa06913a75b3fa99) C:\WINDOWS\system32\DRIVERS\kbdhid.sys
2011/05/10 15:54:08.0437 1752 kmixer (692bcf44383d056aed41b045a323d378) C:\WINDOWS\system32\drivers\kmixer.sys
2011/05/10 15:54:08.0484 1752 KSecDD (b467646c54cc746128904e1654c750c1) C:\WINDOWS\system32\drivers\KSecDD.sys
2011/05/10 15:54:08.0656 1752 lmimirr (4477689e2d8ae6b78ba34c9af4cc1ed1) C:\WINDOWS\system32\DRIVERS\lmimirr.sys
2011/05/10 15:54:08.0718 1752 LMIRfsDriver (3faa563ddf853320f90259d455a01d79) C:\WINDOWS\system32\drivers\LMIRfsDriver.sys
2011/05/10 15:54:08.0796 1752 mdmxsdk (eeaea6514ba7c9d273b5e87c4e1aab30) C:\WINDOWS\system32\DRIVERS\mdmxsdk.sys
2011/05/10 15:54:08.0890 1752 mnmdd (4ae068242760a1fb6e1a44bf4e16afa6) C:\WINDOWS\system32\drivers\mnmdd.sys
2011/05/10 15:54:08.0968 1752 Modem (dfcbad3cec1c5f964962ae10e0bcc8e1) C:\WINDOWS\system32\drivers\Modem.sys
2011/05/10 15:54:09.0000 1752 MODEMCSA (1992e0d143b09653ab0f9c5e04b0fd65) C:\WINDOWS\system32\drivers\MODEMCSA.sys
2011/05/10 15:54:09.0046 1752 Mouclass (35c9e97194c8cfb8430125f8dbc34d04) C:\WINDOWS\system32\DRIVERS\mouclass.sys
2011/05/10 15:54:09.0093 1752 mouhid (b1c303e17fb9d46e87a98e4ba6769685) C:\WINDOWS\system32\DRIVERS\mouhid.sys
2011/05/10 15:54:09.0171 1752 MountMgr (a80b9a0bad1b73637dbcbba7df72d3fd) C:\WINDOWS\system32\drivers\MountMgr.sys
2011/05/10 15:54:09.0234 1752 MRxDAV (11d42bb6206f33fbb3ba0288d3ef81bd) C:\WINDOWS\system32\DRIVERS\mrxdav.sys
2011/05/10 15:54:09.0312 1752 MRxSmb (f3aefb11abc521122b67095044169e98) C:\WINDOWS\system32\DRIVERS\mrxsmb.sys
2011/05/10 15:54:09.0390 1752 Msfs (c941ea2454ba8350021d774daf0f1027) C:\WINDOWS\system32\drivers\Msfs.sys
2011/05/10 15:54:09.0437 1752 MSKSSRV (d1575e71568f4d9e14ca56b7b0453bf1) C:\WINDOWS\system32\drivers\MSKSSRV.sys
2011/05/10 15:54:09.0468 1752 MSPCLOCK (325bb26842fc7ccc1fcce2c457317f3e) C:\WINDOWS\system32\drivers\MSPCLOCK.sys
2011/05/10 15:54:09.0500 1752 MSPQM (bad59648ba099da4a17680b39730cb3d) C:\WINDOWS\system32\drivers\MSPQM.sys
2011/05/10 15:54:09.0546 1752 mssmbios (af5f4f3f14a8ea2c26de30f7a1e17136) C:\WINDOWS\system32\DRIVERS\mssmbios.sys
2011/05/10 15:54:09.0578 1752 Mup (2f625d11385b1a94360bfc70aaefdee1) C:\WINDOWS\system32\drivers\Mup.sys
2011/05/10 15:54:09.0656 1752 NDIS (1df7f42665c94b825322fae71721130d) C:\WINDOWS\system32\drivers\NDIS.sys
2011/05/10 15:54:09.0718 1752 NdisTapi (1ab3d00c991ab086e69db84b6c0ed78f) C:\WINDOWS\system32\DRIVERS\ndistapi.sys
2011/05/10 15:54:09.0750 1752 Ndisuio (f927a4434c5028758a842943ef1a3849) C:\WINDOWS\system32\DRIVERS\ndisuio.sys
2011/05/10 15:54:09.0781 1752 NdisWan (edc1531a49c80614b2cfda43ca8659ab) C:\WINDOWS\system32\DRIVERS\ndiswan.sys
2011/05/10 15:54:09.0843 1752 NDProxy (6215023940cfd3702b46abc304e1d45a) C:\WINDOWS\system32\drivers\NDProxy.sys
2011/05/10 15:54:09.0875 1752 NetBIOS (5d81cf9a2f1a3a756b66cf684911cdf0) C:\WINDOWS\system32\DRIVERS\netbios.sys
2011/05/10 15:54:09.0937 1752 NetBT (74b2b2f5bea5e9a3dc021d685551bd3d) C:\WINDOWS\system32\DRIVERS\netbt.sys
2011/05/10 15:54:10.0093 1752 NPF (b9730495e0cf674680121e34bd95a73b) C:\WINDOWS\system32\drivers\npf.sys
2011/05/10 15:54:10.0109 1752 Npfs (3182d64ae053d6fb034f44b6def8034a) C:\WINDOWS\system32\drivers\Npfs.sys
2011/05/10 15:54:10.0218 1752 Ntfs (78a08dd6a8d65e697c18e1db01c5cdca) C:\WINDOWS\system32\drivers\Ntfs.sys
2011/05/10 15:54:10.0312 1752 Null (73c1e1f395918bc2c6dd67af7591a3ad) C:\WINDOWS\system32\drivers\Null.sys
2011/05/10 15:54:10.0640 1752 nv (ed9816dbaf6689542ea7d022631906a1) C:\WINDOWS\system32\DRIVERS\nv4_mini.sys
2011/05/10 15:54:10.0968 1752 nvata (947c4a0e7b25bcecc3b40f0f1070378b) C:\WINDOWS\system32\DRIVERS\nvata.sys
2011/05/10 15:54:11.0031 1752 nvatabus (947c4a0e7b25bcecc3b40f0f1070378b) C:\WINDOWS\system32\DRIVERS\nvatabus.sys
2011/05/10 15:54:11.0078 1752 NVENETFD (7d275ecda4628318912f6c945d5cf963) C:\WINDOWS\system32\DRIVERS\NVENETFD.sys
2011/05/10 15:54:11.0109 1752 nvnetbus (b64aacefad2be5bff5353fe681253c67) C:\WINDOWS\system32\DRIVERS\nvnetbus.sys
2011/05/10 15:54:11.0171 1752 NwlnkFlt (b305f3fad35083837ef46a0bbce2fc57) C:\WINDOWS\system32\DRIVERS\nwlnkflt.sys
2011/05/10 15:54:11.0203 1752 NwlnkFwd (c99b3415198d1aab7227f2c88fd664b9) C:\WINDOWS\system32\DRIVERS\nwlnkfwd.sys
2011/05/10 15:54:11.0312 1752 Parport (5575faf8f97ce5e713d108c2a58d7c7c) C:\WINDOWS\system32\drivers\Parport.sys
2011/05/10 15:54:11.0390 1752 PartMgr (beb3ba25197665d82ec7065b724171c6) C:\WINDOWS\system32\drivers\PartMgr.sys
2011/05/10 15:54:11.0437 1752 ParVdm (70e98b3fd8e963a6a46a2e6247e0bea1) C:\WINDOWS\system32\drivers\ParVdm.sys
2011/05/10 15:54:11.0468 1752 PCI (a219903ccf74233761d92bef471a07b1) C:\WINDOWS\system32\DRIVERS\pci.sys
2011/05/10 15:54:11.0531 1752 PCIIde (ccf5f451bb1a5a2a522a76e670000ff0) C:\WINDOWS\system32\DRIVERS\pciide.sys
2011/05/10 15:54:11.0578 1752 Pcmcia (9e89ef60e9ee05e3f2eef2da7397f1c1) C:\WINDOWS\system32\drivers\Pcmcia.sys
2011/05/10 15:54:11.0828 1752 PnkBstrK (8292465b89d95eb4f78c46709b7a9888) C:\WINDOWS\system32\drivers\PnkBstrK.sys
2011/05/10 15:54:11.0875 1752 PptpMiniport (efeec01b1d3cf84f16ddd24d9d9d8f99) C:\WINDOWS\system32\DRIVERS\raspptp.sys
2011/05/10 15:54:11.0921 1752 Processor (a32bebaf723557681bfc6bd93e98bd26) C:\WINDOWS\system32\DRIVERS\processr.sys
2011/05/10 15:54:11.0968 1752 PSched (09298ec810b07e5d582cb3a3f9255424) C:\WINDOWS\system32\DRIVERS\psched.sys
2011/05/10 15:54:12.0015 1752 Ptilink (80d317bd1c3dbc5d4fe7b1678c60cadd) C:\WINDOWS\system32\DRIVERS\ptilink.sys
2011/05/10 15:54:12.0218 1752 radpms (6394b4274de7749d05e4385dcdd1ef2b) C:\WINDOWS\system32\DRIVERS\radpms.sys
2011/05/10 15:54:12.0265 1752 RasAcd (fe0d99d6f31e4fad8159f690d68ded9c) C:\WINDOWS\system32\DRIVERS\rasacd.sys
2011/05/10 15:54:12.0312 1752 Rasl2tp (11b4a627bc9614b885c4969bfa5ff8a6) C:\WINDOWS\system32\DRIVERS\rasl2tp.sys
2011/05/10 15:54:12.0375 1752 RasPppoe (5bc962f2654137c9909c3d4603587dee) C:\WINDOWS\system32\DRIVERS\raspppoe.sys
2011/05/10 15:54:12.0421 1752 Raspti (fdbb1d60066fcfbb7452fd8f9829b242) C:\WINDOWS\system32\DRIVERS\raspti.sys
2011/05/10 15:54:12.0484 1752 Rdbss (7ad224ad1a1437fe28d89cf22b17780a) C:\WINDOWS\system32\DRIVERS\rdbss.sys
2011/05/10 15:54:12.0531 1752 RDPCDD (4912d5b403614ce99c28420f75353332) C:\WINDOWS\system32\DRIVERS\RDPCDD.sys
2011/05/10 15:54:12.0593 1752 rdpdr (15cabd0f7c00c47c70124907916af3f1) C:\WINDOWS\system32\DRIVERS\rdpdr.sys
2011/05/10 15:54:12.0656 1752 RDPWD (6728e45b66f93c08f11de2e316fc70dd) C:\WINDOWS\system32\drivers\RDPWD.sys
2011/05/10 15:54:12.0703 1752 redbook (f828dd7e1419b6653894a8f97a0094c5) C:\WINDOWS\system32\DRIVERS\redbook.sys
2011/05/10 15:54:12.0875 1752 Secdrv (90a3935d05b494a5a39d37e71f09a677) C:\WINDOWS\system32\DRIVERS\secdrv.sys
2011/05/10 15:54:12.0953 1752 Serial (cca207a8896d4c6a0c9ce29a4ae411a7) C:\WINDOWS\system32\drivers\Serial.sys
2011/05/10 15:54:13.0046 1752 Sfloppy (8e6b8c671615d126fdc553d1e2de5562) C:\WINDOWS\system32\drivers\Sfloppy.sys
2011/05/10 15:54:13.0187 1752 splitter (ab8b92451ecb048a4d1de7c3ffcb4a9f) C:\WINDOWS\system32\drivers\splitter.sys
2011/05/10 15:54:13.0265 1752 sptd (cdddec541bc3c96f91ecb48759673505) C:\WINDOWS\system32\Drivers\sptd.sys
2011/05/10 15:54:13.0265 1752 Suspicious file (NoAccess): C:\WINDOWS\system32\Drivers\sptd.sys. md5: cdddec541bc3c96f91ecb48759673505
2011/05/10 15:54:13.0281 1752 sptd - detected LockedFile.Multi.Generic (1)
2011/05/10 15:54:13.0343 1752 sr (76bb022c2fb6902fd5bdd4f78fc13a5d) C:\WINDOWS\system32\DRIVERS\sr.sys
2011/05/10 15:54:13.0406 1752 Srv (da852e3e0bf1cea75d756f9866241e57) C:\WINDOWS\system32\DRIVERS\srv.sys
2011/05/10 15:54:13.0468 1752 swenum (3941d127aef12e93addf6fe6ee027e0f) C:\WINDOWS\system32\DRIVERS\swenum.sys
2011/05/10 15:54:13.0515 1752 swmidi (8ce882bcc6cf8a62f2b2323d95cb3d01) C:\WINDOWS\system32\drivers\swmidi.sys
2011/05/10 15:54:13.0718 1752 sysaudio (8b83f3ed0f1688b4958f77cd6d2bf290) C:\WINDOWS\system32\drivers\sysaudio.sys
2011/05/10 15:54:13.0796 1752 Tcpip (9aefa14bd6b182d61e3119fa5f436d3d) C:\WINDOWS\system32\DRIVERS\tcpip.sys
2011/05/10 15:54:13.0859 1752 TDPIPE (6471a66807f5e104e4885f5b67349397) C:\WINDOWS\system32\drivers\TDPIPE.sys
2011/05/10 15:54:13.0890 1752 TDTCP (c56b6d0402371cf3700eb322ef3aaf61) C:\WINDOWS\system32\drivers\TDTCP.sys
2011/05/10 15:54:13.0937 1752 TermDD (88155247177638048422893737429d9e) C:\WINDOWS\system32\DRIVERS\termdd.sys
2011/05/10 15:54:14.0046 1752 Udfs (5787b80c2e3c5e2f56c2a233d91fa2c9) C:\WINDOWS\system32\drivers\Udfs.sys
2011/05/10 15:54:14.0125 1752 Update (402ddc88356b1bac0ee3dd1580c76a31) C:\WINDOWS\system32\DRIVERS\update.sys
2011/05/10 15:54:14.0203 1752 usbaudio (e919708db44ed8543a7c017953148330) C:\WINDOWS\system32\drivers\usbaudio.sys
2011/05/10 15:54:14.0234 1752 usbccgp (173f317ce0db8e21322e71b7e60a27e8) C:\WINDOWS\system32\DRIVERS\usbccgp.sys
2011/05/10 15:54:14.0265 1752 usbehci (65dcf09d0e37d4c6b11b5b0b76d470a7) C:\WINDOWS\system32\DRIVERS\usbehci.sys
2011/05/10 15:54:14.0312 1752 usbhub (1ab3cdde553b6e064d2e754efe20285c) C:\WINDOWS\system32\DRIVERS\usbhub.sys
2011/05/10 15:54:14.0359 1752 usbohci (0daecce65366ea32b162f85f07c6753b) C:\WINDOWS\system32\DRIVERS\usbohci.sys
2011/05/10 15:54:14.0390 1752 usbscan (a0b8cf9deb1184fbdd20784a58fa75d4) C:\WINDOWS\system32\DRIVERS\usbscan.sys
2011/05/10 15:54:14.0453 1752 usbstor (a32426d9b14a089eaa1d922e0c5801a9) C:\WINDOWS\system32\DRIVERS\USBSTOR.SYS
2011/05/10 15:54:14.0500 1752 VgaSave (0d3a8fafceacd8b7625cd549757a7df1) C:\WINDOWS\System32\drivers\vga.sys
2011/05/10 15:54:14.0578 1752 vncmirror (3b8f222b23917c041e4da29ccc57e7d0) C:\WINDOWS\system32\DRIVERS\vncmirror.sys
2011/05/10 15:54:14.0625 1752 VolSnap (4c8fcb5cc53aab716d810740fe59d025) C:\WINDOWS\system32\drivers\VolSnap.sys
2011/05/10 15:54:14.0718 1752 Wanarp (e20b95baedb550f32dd489265c1da1f6) C:\WINDOWS\system32\DRIVERS\wanarp.sys
2011/05/10 15:54:14.0796 1752 wdmaud (6768acf64b18196494413695f0c3a00f) C:\WINDOWS\system32\drivers\wdmaud.sys
2011/05/10 15:54:14.0890 1752 winachsf (f59ed5a43b988a18ef582bb07b2327a7) C:\WINDOWS\system32\DRIVERS\HSF_CNXT.sys
2011/05/10 15:54:15.0109 1752 WudfPf (f15feafffbb3644ccc80c5da584e6311) C:\WINDOWS\system32\DRIVERS\WudfPf.sys
2011/05/10 15:54:15.0281 1752 \HardDisk0 - detected Rootkit.Win32.TDSS.tdl4 (0)
2011/05/10 15:54:15.0296 1752 ================================================================================
2011/05/10 15:54:15.0296 1752 Scan finished
2011/05/10 15:54:15.0296 1752 ================================================================================
2011/05/10 15:54:15.0328 1744 Detected object count: 2
2011/05/10 15:54:48.0187 1744 LockedFile.Multi.Generic(sptd) - User select action: Skip
2011/05/10 15:54:48.0218 1744 \HardDisk0 (Rootkit.Win32.TDSS.tdl4) - will be cured after reboot
2011/05/10 15:54:48.0218 1744 \HardDisk0 - ok
2011/05/10 15:54:48.0218 1744 Rootkit.Win32.TDSS.tdl4(\HardDisk0) - User select action: Cure
2011/05/10 15:54:52.0890 1668 Deinitialize success
2011/05/10 15:53:10.0031 1540 ================================================================================
2011/05/10 15:53:10.0031 1540 SystemInfo:
2011/05/10 15:53:10.0031 1540
2011/05/10 15:53:10.0031 1540 OS Version: 5.1.2600 ServicePack: 3.0
2011/05/10 15:53:10.0031 1540 Product type: Workstation
2011/05/10 15:53:10.0031 1540 ComputerName: SAMUEL-D27BC6AB
2011/05/10 15:53:10.0031 1540 UserName: Samuel
2011/05/10 15:53:10.0031 1540 Windows directory: C:\WINDOWS
2011/05/10 15:53:10.0031 1540 System windows directory: C:\WINDOWS
2011/05/10 15:53:10.0031 1540 Processor architecture: Intel x86
2011/05/10 15:53:10.0031 1540 Number of processors: 1
2011/05/10 15:53:10.0031 1540 Page size: 0x1000
2011/05/10 15:53:10.0031 1540 Boot type: Safe boot with network
2011/05/10 15:53:10.0031 1540 ================================================================================
2011/05/10 15:53:10.0406 1540 Initialize success
2011/05/10 15:54:02.0234 1752 ================================================================================
2011/05/10 15:54:02.0234 1752 Scan started
2011/05/10 15:54:02.0234 1752 Mode: Manual;
2011/05/10 15:54:02.0234 1752 ================================================================================
2011/05/10 15:54:03.0406 1752 Aavmker4 (83631291adf2887cffc786d034d3fa15) C:\WINDOWS\system32\drivers\Aavmker4.sys
2011/05/10 15:54:03.0546 1752 ACPI (8fd99680a539792a30e97944fdaecf17) C:\WINDOWS\system32\DRIVERS\ACPI.sys
2011/05/10 15:54:03.0609 1752 ACPIEC (9859c0f6936e723e4892d7141b1327d5) C:\WINDOWS\system32\drivers\ACPIEC.sys
2011/05/10 15:54:03.0703 1752 aec (8bed39e3c35d6a489438b8141717a557) C:\WINDOWS\system32\drivers\aec.sys
2011/05/10 15:54:03.0781 1752 AFD (7e775010ef291da96ad17ca4b17137d7) C:\WINDOWS\System32\drivers\afd.sys
2011/05/10 15:54:04.0046 1752 AmdPPM (033448d435e65c4bd72e70521fd05c76) C:\WINDOWS\system32\DRIVERS\AmdPPM.sys
2011/05/10 15:54:04.0265 1752 aswFsBlk (1c2e6bb4fe8621b1b863855b02bc33eb) C:\WINDOWS\system32\drivers\aswFsBlk.sys
2011/05/10 15:54:04.0328 1752 aswMon2 (452d0ecd14fa02f9b061f42c8a30dd49) C:\WINDOWS\system32\drivers\aswMon2.sys
2011/05/10 15:54:04.0375 1752 aswRdr (b6a9373619d851be80fb5f1b5eed0d4e) C:\WINDOWS\system32\drivers\aswRdr.sys
2011/05/10 15:54:04.0484 1752 aswSnx (9be41c1ae8bc481eb662d85c98d979c2) C:\WINDOWS\system32\drivers\aswSnx.sys
2011/05/10 15:54:04.0609 1752 aswSP (4b1a54ba2bc5873a774df6b70ab8b0b3) C:\WINDOWS\system32\drivers\aswSP.sys
2011/05/10 15:54:04.0671 1752 aswTdi (c7f1cea32766184911293f4e1ee653f5) C:\WINDOWS\system32\drivers\aswTdi.sys
2011/05/10 15:54:04.0734 1752 AsyncMac (b153affac761e7f5fcfa822b9c4e97bc) C:\WINDOWS\system32\DRIVERS\asyncmac.sys
2011/05/10 15:54:04.0781 1752 atapi (9f3a2f5aa6875c72bf062c712cfa2674) C:\WINDOWS\system32\DRIVERS\atapi.sys
2011/05/10 15:54:04.0890 1752 Atmarpc (9916c1225104ba14794209cfa8012159) C:\WINDOWS\system32\DRIVERS\atmarpc.sys
2011/05/10 15:54:04.0953 1752 audstub (d9f724aa26c010a217c97606b160ed68) C:\WINDOWS\system32\DRIVERS\audstub.sys
2011/05/10 15:54:05.0015 1752 Beep (da1f27d85e0d1525f6621372e7b685e9) C:\WINDOWS\system32\drivers\Beep.sys
2011/05/10 15:54:05.0109 1752 cbidf2k (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\drivers\cbidf2k.sys
2011/05/10 15:54:05.0171 1752 Cdaudio (c1b486a7658353d33a10cc15211a873b) C:\WINDOWS\system32\drivers\Cdaudio.sys
2011/05/10 15:54:05.0203 1752 Cdfs (c885b02847f5d2fd45a24e219ed93b32) C:\WINDOWS\system32\drivers\Cdfs.sys
2011/05/10 15:54:05.0265 1752 Cdrom (1f4260cc5b42272d71f79e570a27a4fe) C:\WINDOWS\system32\DRIVERS\cdrom.sys
2011/05/10 15:54:05.0781 1752 Disk (044452051f3e02e7963599fc8f4f3e25) C:\WINDOWS\system32\DRIVERS\disk.sys
2011/05/10 15:54:05.0890 1752 dmboot (d992fe1274bde0f84ad826acae022a41) C:\WINDOWS\system32\drivers\dmboot.sys
2011/05/10 15:54:05.0937 1752 dmio (7c824cf7bbde77d95c08005717a95f6f) C:\WINDOWS\system32\DRIVERS\dmio.sys
2011/05/10 15:54:05.0984 1752 dmload (e9317282a63ca4d188c0df5e09c6ac5f) C:\WINDOWS\system32\drivers\dmload.sys
2011/05/10 15:54:06.0046 1752 DMusic (8a208dfcf89792a484e76c40e5f50b45) C:\WINDOWS\system32\drivers\DMusic.sys
2011/05/10 15:54:06.0140 1752 drmkaud (8f5fcff8e8848afac920905fbd9d33c8) C:\WINDOWS\system32\drivers\drmkaud.sys
2011/05/10 15:54:06.0265 1752 ENTECH (16ebd8bf1d5090923694cc972c7ce1b4) C:\WINDOWS\system32\DRIVERS\ENTECH.sys
2011/05/10 15:54:06.0359 1752 Fastfat (38d332a6d56af32635675f132548343e) C:\WINDOWS\system32\drivers\Fastfat.sys
2011/05/10 15:54:06.0421 1752 Fdc (92cdd60b6730b9f50f6a1a0c1f8cdc81) C:\WINDOWS\system32\drivers\Fdc.sys
2011/05/10 15:54:06.0500 1752 Fips (d45926117eb9fa946a6af572fbe1caa3) C:\WINDOWS\system32\drivers\Fips.sys
2011/05/10 15:54:06.0531 1752 Flpydisk (9d27e7b80bfcdf1cdd9b555862d5e7f0) C:\WINDOWS\system32\drivers\Flpydisk.sys
2011/05/10 15:54:06.0593 1752 FltMgr (b2cf4b0786f8212cb92ed2b50c6db6b0) C:\WINDOWS\system32\DRIVERS\fltMgr.sys
2011/05/10 15:54:06.0656 1752 Fs_Rec (3e1e2bd4f39b0e2b7dc4f4d2bcc2779a) C:\WINDOWS\system32\drivers\Fs_Rec.sys
2011/05/10 15:54:06.0734 1752 Ftdisk (6ac26732762483366c3969c9e4d2259d) C:\WINDOWS\system32\DRIVERS\ftdisk.sys
2011/05/10 15:54:06.0812 1752 GEARAspiWDM (ab8a6a87d9d7255c3884d5b9541a6e80) C:\WINDOWS\system32\Drivers\GEARAspiWDM.sys
2011/05/10 15:54:06.0890 1752 Gpc (0a02c63c8b144bd8c86b103dee7c86a2) C:\WINDOWS\system32\DRIVERS\msgpc.sys
2011/05/10 15:54:06.0953 1752 hamachi (7929a161f9951d173ca9900fe7067391) C:\WINDOWS\system32\DRIVERS\hamachi.sys
2011/05/10 15:54:07.0015 1752 HDAudBus (573c7d0a32852b48f3058cfd8026f511) C:\WINDOWS\system32\DRIVERS\HDAudBus.sys
2011/05/10 15:54:07.0093 1752 hidusb (ccf82c5ec8a7326c3066de870c06daf1) C:\WINDOWS\system32\DRIVERS\hidusb.sys
2011/05/10 15:54:07.0187 1752 HSFHWBS2 (77e4ff0b73bc0aeaaf39bf0c8104231f) C:\WINDOWS\system32\DRIVERS\HSFHWBS2.sys
2011/05/10 15:54:07.0250 1752 HSF_DP (60e1604729a15ef4a3b05f298427b3b1) C:\WINDOWS\system32\DRIVERS\HSF_DP.sys
2011/05/10 15:54:07.0328 1752 HTTP (f80a415ef82cd06ffaf0d971528ead38) C:\WINDOWS\system32\Drivers\HTTP.sys
2011/05/10 15:54:07.0453 1752 i8042prt (4a0b06aa8943c1e332520f7440c0aa30) C:\WINDOWS\system32\drivers\i8042prt.sys
2011/05/10 15:54:07.0546 1752 Imapi (083a052659f5310dd8b6a6cb05edcf8e) C:\WINDOWS\system32\DRIVERS\imapi.sys
2011/05/10 15:54:07.0750 1752 IntcAzAudAddService (39a817320087ef1c851d7a8f1701b3e0) C:\WINDOWS\system32\drivers\RtkHDAud.sys
2011/05/10 15:54:07.0937 1752 Ip6Fw (3bb22519a194418d5fec05d800a19ad0) C:\WINDOWS\system32\DRIVERS\Ip6Fw.sys
2011/05/10 15:54:07.0984 1752 IpFilterDriver (731f22ba402ee4b62748adaf6363c182) C:\WINDOWS\system32\DRIVERS\ipfltdrv.sys
2011/05/10 15:54:08.0015 1752 IpInIp (b87ab476dcf76e72010632b5550955f5) C:\WINDOWS\system32\DRIVERS\ipinip.sys
2011/05/10 15:54:08.0078 1752 IpNat (cc748ea12c6effde940ee98098bf96bb) C:\WINDOWS\system32\DRIVERS\ipnat.sys
2011/05/10 15:54:08.0156 1752 IPSec (23c74d75e36e7158768dd63d92789a91) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2011/05/10 15:54:08.0234 1752 IRENUM (c93c9ff7b04d772627a3646d89f7bf89) C:\WINDOWS\system32\DRIVERS\irenum.sys
2011/05/10 15:54:08.0296 1752 isapnp (05a299ec56e52649b1cf2fc52d20f2d7) C:\WINDOWS\system32\DRIVERS\isapnp.sys
2011/05/10 15:54:08.0328 1752 Kbdclass (463c1ec80cd17420a542b7f36a36f128) C:\WINDOWS\system32\DRIVERS\kbdclass.sys
2011/05/10 15:54:08.0343 1752 kbdhid (9ef487a186dea361aa06913a75b3fa99) C:\WINDOWS\system32\DRIVERS\kbdhid.sys
2011/05/10 15:54:08.0437 1752 kmixer (692bcf44383d056aed41b045a323d378) C:\WINDOWS\system32\drivers\kmixer.sys
2011/05/10 15:54:08.0484 1752 KSecDD (b467646c54cc746128904e1654c750c1) C:\WINDOWS\system32\drivers\KSecDD.sys
2011/05/10 15:54:08.0656 1752 lmimirr (4477689e2d8ae6b78ba34c9af4cc1ed1) C:\WINDOWS\system32\DRIVERS\lmimirr.sys
2011/05/10 15:54:08.0718 1752 LMIRfsDriver (3faa563ddf853320f90259d455a01d79) C:\WINDOWS\system32\drivers\LMIRfsDriver.sys
2011/05/10 15:54:08.0796 1752 mdmxsdk (eeaea6514ba7c9d273b5e87c4e1aab30) C:\WINDOWS\system32\DRIVERS\mdmxsdk.sys
2011/05/10 15:54:08.0890 1752 mnmdd (4ae068242760a1fb6e1a44bf4e16afa6) C:\WINDOWS\system32\drivers\mnmdd.sys
2011/05/10 15:54:08.0968 1752 Modem (dfcbad3cec1c5f964962ae10e0bcc8e1) C:\WINDOWS\system32\drivers\Modem.sys
2011/05/10 15:54:09.0000 1752 MODEMCSA (1992e0d143b09653ab0f9c5e04b0fd65) C:\WINDOWS\system32\drivers\MODEMCSA.sys
2011/05/10 15:54:09.0046 1752 Mouclass (35c9e97194c8cfb8430125f8dbc34d04) C:\WINDOWS\system32\DRIVERS\mouclass.sys
2011/05/10 15:54:09.0093 1752 mouhid (b1c303e17fb9d46e87a98e4ba6769685) C:\WINDOWS\system32\DRIVERS\mouhid.sys
2011/05/10 15:54:09.0171 1752 MountMgr (a80b9a0bad1b73637dbcbba7df72d3fd) C:\WINDOWS\system32\drivers\MountMgr.sys
2011/05/10 15:54:09.0234 1752 MRxDAV (11d42bb6206f33fbb3ba0288d3ef81bd) C:\WINDOWS\system32\DRIVERS\mrxdav.sys
2011/05/10 15:54:09.0312 1752 MRxSmb (f3aefb11abc521122b67095044169e98) C:\WINDOWS\system32\DRIVERS\mrxsmb.sys
2011/05/10 15:54:09.0390 1752 Msfs (c941ea2454ba8350021d774daf0f1027) C:\WINDOWS\system32\drivers\Msfs.sys
2011/05/10 15:54:09.0437 1752 MSKSSRV (d1575e71568f4d9e14ca56b7b0453bf1) C:\WINDOWS\system32\drivers\MSKSSRV.sys
2011/05/10 15:54:09.0468 1752 MSPCLOCK (325bb26842fc7ccc1fcce2c457317f3e) C:\WINDOWS\system32\drivers\MSPCLOCK.sys
2011/05/10 15:54:09.0500 1752 MSPQM (bad59648ba099da4a17680b39730cb3d) C:\WINDOWS\system32\drivers\MSPQM.sys
2011/05/10 15:54:09.0546 1752 mssmbios (af5f4f3f14a8ea2c26de30f7a1e17136) C:\WINDOWS\system32\DRIVERS\mssmbios.sys
2011/05/10 15:54:09.0578 1752 Mup (2f625d11385b1a94360bfc70aaefdee1) C:\WINDOWS\system32\drivers\Mup.sys
2011/05/10 15:54:09.0656 1752 NDIS (1df7f42665c94b825322fae71721130d) C:\WINDOWS\system32\drivers\NDIS.sys
2011/05/10 15:54:09.0718 1752 NdisTapi (1ab3d00c991ab086e69db84b6c0ed78f) C:\WINDOWS\system32\DRIVERS\ndistapi.sys
2011/05/10 15:54:09.0750 1752 Ndisuio (f927a4434c5028758a842943ef1a3849) C:\WINDOWS\system32\DRIVERS\ndisuio.sys
2011/05/10 15:54:09.0781 1752 NdisWan (edc1531a49c80614b2cfda43ca8659ab) C:\WINDOWS\system32\DRIVERS\ndiswan.sys
2011/05/10 15:54:09.0843 1752 NDProxy (6215023940cfd3702b46abc304e1d45a) C:\WINDOWS\system32\drivers\NDProxy.sys
2011/05/10 15:54:09.0875 1752 NetBIOS (5d81cf9a2f1a3a756b66cf684911cdf0) C:\WINDOWS\system32\DRIVERS\netbios.sys
2011/05/10 15:54:09.0937 1752 NetBT (74b2b2f5bea5e9a3dc021d685551bd3d) C:\WINDOWS\system32\DRIVERS\netbt.sys
2011/05/10 15:54:10.0093 1752 NPF (b9730495e0cf674680121e34bd95a73b) C:\WINDOWS\system32\drivers\npf.sys
2011/05/10 15:54:10.0109 1752 Npfs (3182d64ae053d6fb034f44b6def8034a) C:\WINDOWS\system32\drivers\Npfs.sys
2011/05/10 15:54:10.0218 1752 Ntfs (78a08dd6a8d65e697c18e1db01c5cdca) C:\WINDOWS\system32\drivers\Ntfs.sys
2011/05/10 15:54:10.0312 1752 Null (73c1e1f395918bc2c6dd67af7591a3ad) C:\WINDOWS\system32\drivers\Null.sys
2011/05/10 15:54:10.0640 1752 nv (ed9816dbaf6689542ea7d022631906a1) C:\WINDOWS\system32\DRIVERS\nv4_mini.sys
2011/05/10 15:54:10.0968 1752 nvata (947c4a0e7b25bcecc3b40f0f1070378b) C:\WINDOWS\system32\DRIVERS\nvata.sys
2011/05/10 15:54:11.0031 1752 nvatabus (947c4a0e7b25bcecc3b40f0f1070378b) C:\WINDOWS\system32\DRIVERS\nvatabus.sys
2011/05/10 15:54:11.0078 1752 NVENETFD (7d275ecda4628318912f6c945d5cf963) C:\WINDOWS\system32\DRIVERS\NVENETFD.sys
2011/05/10 15:54:11.0109 1752 nvnetbus (b64aacefad2be5bff5353fe681253c67) C:\WINDOWS\system32\DRIVERS\nvnetbus.sys
2011/05/10 15:54:11.0171 1752 NwlnkFlt (b305f3fad35083837ef46a0bbce2fc57) C:\WINDOWS\system32\DRIVERS\nwlnkflt.sys
2011/05/10 15:54:11.0203 1752 NwlnkFwd (c99b3415198d1aab7227f2c88fd664b9) C:\WINDOWS\system32\DRIVERS\nwlnkfwd.sys
2011/05/10 15:54:11.0312 1752 Parport (5575faf8f97ce5e713d108c2a58d7c7c) C:\WINDOWS\system32\drivers\Parport.sys
2011/05/10 15:54:11.0390 1752 PartMgr (beb3ba25197665d82ec7065b724171c6) C:\WINDOWS\system32\drivers\PartMgr.sys
2011/05/10 15:54:11.0437 1752 ParVdm (70e98b3fd8e963a6a46a2e6247e0bea1) C:\WINDOWS\system32\drivers\ParVdm.sys
2011/05/10 15:54:11.0468 1752 PCI (a219903ccf74233761d92bef471a07b1) C:\WINDOWS\system32\DRIVERS\pci.sys
2011/05/10 15:54:11.0531 1752 PCIIde (ccf5f451bb1a5a2a522a76e670000ff0) C:\WINDOWS\system32\DRIVERS\pciide.sys
2011/05/10 15:54:11.0578 1752 Pcmcia (9e89ef60e9ee05e3f2eef2da7397f1c1) C:\WINDOWS\system32\drivers\Pcmcia.sys
2011/05/10 15:54:11.0828 1752 PnkBstrK (8292465b89d95eb4f78c46709b7a9888) C:\WINDOWS\system32\drivers\PnkBstrK.sys
2011/05/10 15:54:11.0875 1752 PptpMiniport (efeec01b1d3cf84f16ddd24d9d9d8f99) C:\WINDOWS\system32\DRIVERS\raspptp.sys
2011/05/10 15:54:11.0921 1752 Processor (a32bebaf723557681bfc6bd93e98bd26) C:\WINDOWS\system32\DRIVERS\processr.sys
2011/05/10 15:54:11.0968 1752 PSched (09298ec810b07e5d582cb3a3f9255424) C:\WINDOWS\system32\DRIVERS\psched.sys
2011/05/10 15:54:12.0015 1752 Ptilink (80d317bd1c3dbc5d4fe7b1678c60cadd) C:\WINDOWS\system32\DRIVERS\ptilink.sys
2011/05/10 15:54:12.0218 1752 radpms (6394b4274de7749d05e4385dcdd1ef2b) C:\WINDOWS\system32\DRIVERS\radpms.sys
2011/05/10 15:54:12.0265 1752 RasAcd (fe0d99d6f31e4fad8159f690d68ded9c) C:\WINDOWS\system32\DRIVERS\rasacd.sys
2011/05/10 15:54:12.0312 1752 Rasl2tp (11b4a627bc9614b885c4969bfa5ff8a6) C:\WINDOWS\system32\DRIVERS\rasl2tp.sys
2011/05/10 15:54:12.0375 1752 RasPppoe (5bc962f2654137c9909c3d4603587dee) C:\WINDOWS\system32\DRIVERS\raspppoe.sys
2011/05/10 15:54:12.0421 1752 Raspti (fdbb1d60066fcfbb7452fd8f9829b242) C:\WINDOWS\system32\DRIVERS\raspti.sys
2011/05/10 15:54:12.0484 1752 Rdbss (7ad224ad1a1437fe28d89cf22b17780a) C:\WINDOWS\system32\DRIVERS\rdbss.sys
2011/05/10 15:54:12.0531 1752 RDPCDD (4912d5b403614ce99c28420f75353332) C:\WINDOWS\system32\DRIVERS\RDPCDD.sys
2011/05/10 15:54:12.0593 1752 rdpdr (15cabd0f7c00c47c70124907916af3f1) C:\WINDOWS\system32\DRIVERS\rdpdr.sys
2011/05/10 15:54:12.0656 1752 RDPWD (6728e45b66f93c08f11de2e316fc70dd) C:\WINDOWS\system32\drivers\RDPWD.sys
2011/05/10 15:54:12.0703 1752 redbook (f828dd7e1419b6653894a8f97a0094c5) C:\WINDOWS\system32\DRIVERS\redbook.sys
2011/05/10 15:54:12.0875 1752 Secdrv (90a3935d05b494a5a39d37e71f09a677) C:\WINDOWS\system32\DRIVERS\secdrv.sys
2011/05/10 15:54:12.0953 1752 Serial (cca207a8896d4c6a0c9ce29a4ae411a7) C:\WINDOWS\system32\drivers\Serial.sys
2011/05/10 15:54:13.0046 1752 Sfloppy (8e6b8c671615d126fdc553d1e2de5562) C:\WINDOWS\system32\drivers\Sfloppy.sys
2011/05/10 15:54:13.0187 1752 splitter (ab8b92451ecb048a4d1de7c3ffcb4a9f) C:\WINDOWS\system32\drivers\splitter.sys
2011/05/10 15:54:13.0265 1752 sptd (cdddec541bc3c96f91ecb48759673505) C:\WINDOWS\system32\Drivers\sptd.sys
2011/05/10 15:54:13.0265 1752 Suspicious file (NoAccess): C:\WINDOWS\system32\Drivers\sptd.sys. md5: cdddec541bc3c96f91ecb48759673505
2011/05/10 15:54:13.0281 1752 sptd - detected LockedFile.Multi.Generic (1)
2011/05/10 15:54:13.0343 1752 sr (76bb022c2fb6902fd5bdd4f78fc13a5d) C:\WINDOWS\system32\DRIVERS\sr.sys
2011/05/10 15:54:13.0406 1752 Srv (da852e3e0bf1cea75d756f9866241e57) C:\WINDOWS\system32\DRIVERS\srv.sys
2011/05/10 15:54:13.0468 1752 swenum (3941d127aef12e93addf6fe6ee027e0f) C:\WINDOWS\system32\DRIVERS\swenum.sys
2011/05/10 15:54:13.0515 1752 swmidi (8ce882bcc6cf8a62f2b2323d95cb3d01) C:\WINDOWS\system32\drivers\swmidi.sys
2011/05/10 15:54:13.0718 1752 sysaudio (8b83f3ed0f1688b4958f77cd6d2bf290) C:\WINDOWS\system32\drivers\sysaudio.sys
2011/05/10 15:54:13.0796 1752 Tcpip (9aefa14bd6b182d61e3119fa5f436d3d) C:\WINDOWS\system32\DRIVERS\tcpip.sys
2011/05/10 15:54:13.0859 1752 TDPIPE (6471a66807f5e104e4885f5b67349397) C:\WINDOWS\system32\drivers\TDPIPE.sys
2011/05/10 15:54:13.0890 1752 TDTCP (c56b6d0402371cf3700eb322ef3aaf61) C:\WINDOWS\system32\drivers\TDTCP.sys
2011/05/10 15:54:13.0937 1752 TermDD (88155247177638048422893737429d9e) C:\WINDOWS\system32\DRIVERS\termdd.sys
2011/05/10 15:54:14.0046 1752 Udfs (5787b80c2e3c5e2f56c2a233d91fa2c9) C:\WINDOWS\system32\drivers\Udfs.sys
2011/05/10 15:54:14.0125 1752 Update (402ddc88356b1bac0ee3dd1580c76a31) C:\WINDOWS\system32\DRIVERS\update.sys
2011/05/10 15:54:14.0203 1752 usbaudio (e919708db44ed8543a7c017953148330) C:\WINDOWS\system32\drivers\usbaudio.sys
2011/05/10 15:54:14.0234 1752 usbccgp (173f317ce0db8e21322e71b7e60a27e8) C:\WINDOWS\system32\DRIVERS\usbccgp.sys
2011/05/10 15:54:14.0265 1752 usbehci (65dcf09d0e37d4c6b11b5b0b76d470a7) C:\WINDOWS\system32\DRIVERS\usbehci.sys
2011/05/10 15:54:14.0312 1752 usbhub (1ab3cdde553b6e064d2e754efe20285c) C:\WINDOWS\system32\DRIVERS\usbhub.sys
2011/05/10 15:54:14.0359 1752 usbohci (0daecce65366ea32b162f85f07c6753b) C:\WINDOWS\system32\DRIVERS\usbohci.sys
2011/05/10 15:54:14.0390 1752 usbscan (a0b8cf9deb1184fbdd20784a58fa75d4) C:\WINDOWS\system32\DRIVERS\usbscan.sys
2011/05/10 15:54:14.0453 1752 usbstor (a32426d9b14a089eaa1d922e0c5801a9) C:\WINDOWS\system32\DRIVERS\USBSTOR.SYS
2011/05/10 15:54:14.0500 1752 VgaSave (0d3a8fafceacd8b7625cd549757a7df1) C:\WINDOWS\System32\drivers\vga.sys
2011/05/10 15:54:14.0578 1752 vncmirror (3b8f222b23917c041e4da29ccc57e7d0) C:\WINDOWS\system32\DRIVERS\vncmirror.sys
2011/05/10 15:54:14.0625 1752 VolSnap (4c8fcb5cc53aab716d810740fe59d025) C:\WINDOWS\system32\drivers\VolSnap.sys
2011/05/10 15:54:14.0718 1752 Wanarp (e20b95baedb550f32dd489265c1da1f6) C:\WINDOWS\system32\DRIVERS\wanarp.sys
2011/05/10 15:54:14.0796 1752 wdmaud (6768acf64b18196494413695f0c3a00f) C:\WINDOWS\system32\drivers\wdmaud.sys
2011/05/10 15:54:14.0890 1752 winachsf (f59ed5a43b988a18ef582bb07b2327a7) C:\WINDOWS\system32\DRIVERS\HSF_CNXT.sys
2011/05/10 15:54:15.0109 1752 WudfPf (f15feafffbb3644ccc80c5da584e6311) C:\WINDOWS\system32\DRIVERS\WudfPf.sys
2011/05/10 15:54:15.0281 1752 \HardDisk0 - detected Rootkit.Win32.TDSS.tdl4 (0)
2011/05/10 15:54:15.0296 1752 ================================================================================
2011/05/10 15:54:15.0296 1752 Scan finished
2011/05/10 15:54:15.0296 1752 ================================================================================
2011/05/10 15:54:15.0328 1744 Detected object count: 2
2011/05/10 15:54:48.0187 1744 LockedFile.Multi.Generic(sptd) - User select action: Skip
2011/05/10 15:54:48.0218 1744 \HardDisk0 (Rootkit.Win32.TDSS.tdl4) - will be cured after reboot
2011/05/10 15:54:48.0218 1744 \HardDisk0 - ok
2011/05/10 15:54:48.0218 1744 Rootkit.Win32.TDSS.tdl4(\HardDisk0) - User select action: Cure
2011/05/10 15:54:52.0890 1668 Deinitialize success
#25

 Posted 10 May 2011 - 03:46 PM
Posted 10 May 2011 - 03:46 PM

That looks good - could you do some searches now and check the redirects have gone, also visit windows update to ensure that works please
#26

 Posted 10 May 2011 - 07:51 PM
Posted 10 May 2011 - 07:51 PM

Everything seems fine Google not redirecting Windows Updates looks fine too no tab pop ups yet 
#27

 Posted 11 May 2011 - 11:18 AM
Posted 11 May 2011 - 11:18 AM

OK a final sweep for orphans before I let you go 
 Please download Malwarebytes' Anti-Malware from Here.
Please download Malwarebytes' Anti-Malware from Here.
Double Click mbam-setup.exe to install the application.
If MBAM encounters a file that is difficult to remove,you will be presented with 1 of 2 prompts,click OK to either and let MBAM proceed with the disinfection process. If asked to restart the computer, please do so immediately.
Double Click mbam-setup.exe to install the application.
- Make sure a checkmark is placed next to Update Malwarebytes' Anti-Malware and Launch Malwarebytes' Anti-Malware, then click Finish.
- If an update is found, it will download and install the latest version.
- Once the program has loaded, select "Perform Quick Scan", then click Scan.
- The scan may take some time to finish,so please be patient.
- When the scan is complete, click OK, then Show Results to view the results.
- Make sure that everything is checked, and click Remove Selected.
- When disinfection is completed, a log will open in Notepad and you may be prompted to Restart.(See Extra Note)
- The log is automatically saved by MBAM and can be viewed by clicking the Logs tab in MBAM.
- Copy&Paste the entire report in your next reply.
If MBAM encounters a file that is difficult to remove,you will be presented with 1 of 2 prompts,click OK to either and let MBAM proceed with the disinfection process. If asked to restart the computer, please do so immediately.
#28

 Posted 11 May 2011 - 02:59 PM
Posted 11 May 2011 - 02:59 PM

Malwarebytes' Anti-Malware 1.50.1.1100
www.malwarebytes.org
Database version: 6557
Windows 5.1.2600 Service Pack 3
Internet Explorer 8.0.6001.18702
5/11/2011 3:58:24 PM
mbam-log-2011-05-11 (15-58-24).txt
Scan type: Quick scan
Objects scanned: 168003
Time elapsed: 8 minute(s), 53 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 0
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
(No malicious items detected)
www.malwarebytes.org
Database version: 6557
Windows 5.1.2600 Service Pack 3
Internet Explorer 8.0.6001.18702
5/11/2011 3:58:24 PM
mbam-log-2011-05-11 (15-58-24).txt
Scan type: Quick scan
Objects scanned: 168003
Time elapsed: 8 minute(s), 53 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 0
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
(No malicious items detected)
#29

 Posted 11 May 2011 - 03:02 PM
Posted 11 May 2011 - 03:02 PM

Subject to no further problems 
I will remove my tools now and give some recommendations, but, I would like you to run for 24 hours or so and come back if you have any problems
Now the best part of the day ----- Your log now appears clean
A good workman always cleans up after himself so..The following will implement some cleanup procedures as well as reset System Restore points:
Run OTL
Click Start > Run and copy/paste the following bolded text into the Run box and click OK:
ComboFix /Uninstall
Run OTL and hit the cleanup button. It will remove all the programmes we have used plus itself.
We will now confirm that your hidden files are set to that, as some of the tools I use will change that
SPRING CLEAN
Download and run Puran Disc Defragmenter
For the first run I would recommend a boot defrag and disk check
Now that you are clean, to help protect your computer in the future I recommend that you get the following free programmes:
 Malwarebytes. Update and run weekly to keep your system clean
Malwarebytes. Update and run weekly to keep your system clean
Download and install FileHippo update checker and run it monthly it will show you which programmes on your system need updating and give a download link
It is critical to have both a firewall and anti virus to protect your system and to keep them updated.
To keep your operating system up to date visit
To learn more about how to protect yourself while on the internet read our little guide How did I get infected in the first place ?
Keep safe
I will remove my tools now and give some recommendations, but, I would like you to run for 24 hours or so and come back if you have any problems
Now the best part of the day ----- Your log now appears clean
A good workman always cleans up after himself so..The following will implement some cleanup procedures as well as reset System Restore points:
Run OTL
- Under the Custom Scans/Fixes box at the bottom, paste in the following
:Commands
[resethosts]
[purity]
[emptytemp]
[EMPTYFLASH]
[CLEARALLRESTOREPOINTS]
[Reboot]
- Then click the Run Fix button at the top
- Let the program run unhindered, reboot the PC when it is done
Click Start > Run and copy/paste the following bolded text into the Run box and click OK:
ComboFix /Uninstall
Run OTL and hit the cleanup button. It will remove all the programmes we have used plus itself.
We will now confirm that your hidden files are set to that, as some of the tools I use will change that
- Click Start.
- Open My Computer.
- Select the Tools menu and click Folder Options.
- Select the View Tab.
- Under the Hidden files and folders heading select Do not show hidden files and folders.
- Click Yes to confirm.
- Click OK.
SPRING CLEAN
Download and run Puran Disc Defragmenter
For the first run I would recommend a boot defrag and disk check
Now that you are clean, to help protect your computer in the future I recommend that you get the following free programmes:
Download and install FileHippo update checker and run it monthly it will show you which programmes on your system need updating and give a download link
It is critical to have both a firewall and anti virus to protect your system and to keep them updated.
To keep your operating system up to date visit
To learn more about how to protect yourself while on the internet read our little guide How did I get infected in the first place ?
Keep safe
#30

 Posted 11 May 2011 - 10:35 PM
Posted 11 May 2011 - 10:35 PM

Um no Idea what happen the computer is stuck now on Windows Xp Start up Screen wont go past that done safe mode as well dont work last thing i did was that Puran Disc Fragmenter. It said Disc clean up finished for a really long time so did a force reboot now it keeps getting stuck on Windows Xp Start up Screen. Using a Diffrent Computer right now till i can get this problem fixed
Edited by Madara, 12 May 2011 - 08:23 AM.
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked





 Sign In
Sign In Create Account
Create Account

