To answer your first question, I don't need any of them, they are related to the websites for a previous job.
Here is the Extra log:OTL Extras logfile created on: 8/15/2011 2:03:03 AM - Run 1
OTL by OldTimer - Version 3.2.26.4 Folder = C:\Documents and Settings\Vernon Burdette\My Documents\Downloads
Windows XP Home Edition Service Pack 3 (Version = 5.1.2600) - Type = NTWorkstation
Internet Explorer (Version = 8.0.6001.18702)
Locale: 00000409 | Country: United States | Language: ENU | Date Format: M/d/yyyy
1.87 Gb Total Physical Memory | 1.33 Gb Available Physical Memory | 71.24% Memory free
3.72 Gb Paging File | 3.34 Gb Available in Paging File | 89.62% Paging File free
Paging file location(s): C:\pagefile.sys 2046 4092 [binary data]
%SystemDrive% = C: | %SystemRoot% = C:\WINDOWS | %ProgramFiles% = C:\Program Files
Drive C: | 111.73 Gb Total Space | 85.60 Gb Free Space | 76.62% Space Free | Partition Type: NTFS
Computer Name: VERNON | User Name: Vernon Burdette | Logged in as Administrator.
Boot Mode: Normal | Scan Mode: Current user | Quick Scan
Company Name Whitelist: On | Skip Microsoft Files: On | No Company Name Whitelist: On | File Age = 30 Days
========== Extra Registry (SafeList) ========== ========== File Associations ========== [HKEY_LOCAL_MACHINE\SOFTWARE\Classes\<extension>]
.cpl [@ = cplfile] -- rundll32.exe shell32.dll,Control_RunDLL "%1",%*
========== Shell Spawning ========== [HKEY_LOCAL_MACHINE\SOFTWARE\Classes\<key>\shell\[command]\command]
batfile [open] -- "%1" %*
cmdfile [open] -- "%1" %*
comfile [open] -- "%1" %*
cplfile [cplopen] -- rundll32.exe shell32.dll,Control_RunDLL "%1",%*
exefile [open] -- "%1" %*
helpfile [open] -- winhlp32.exe %1 (Microsoft Corporation)
piffile [open] -- "%1" %*
regfile [merge] -- Reg Error: Key error.
scrfile [config] -- "%1"
scrfile [install] -- rundll32.exe desk.cpl,InstallScreenSaver %l
scrfile [open] -- "%1" /S
txtfile [edit] -- Reg Error: Key error.
Unknown [openas] -- %SystemRoot%\system32\rundll32.exe %SystemRoot%\system32\shell32.dll,OpenAs_RunDLL %1
========== Security Center Settings ========== [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center]
"FirstRunDisabled" = 1
"AntiVirusOverride" = 1
"FirewallOverride" = 1
"AntiVirusDisableNotify" = 0
"FirewallDisableNotify" = 0
"UpdatesDisableNotify" = 0
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\AhnlabAntiVirus]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\ComputerAssociatesAntiVirus]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\KasperskyAntiVirus]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\McAfeeAntiVirus]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\McAfeeFirewall]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\PandaAntiVirus]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\PandaFirewall]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\SophosAntiVirus]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\SymantecAntiVirus]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\SymantecFirewall]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\TinyFirewall]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\TrendAntiVirus]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\TrendFirewall]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center\Monitoring\ZoneLabsFirewall]
========== System Restore Settings ========== [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore]
"DisableSR" = 1
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Sr]
"Start" = 4
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SrService]
"Start" = 2
========== Firewall Settings ========== [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\DomainProfile]
"EnableFirewall" = 0
"DoNotAllowExceptions" = 0
"DisableNotifications" = 1
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\DomainProfile\GloballyOpenPorts\List]
"139:TCP" = 139:TCP:*:Enabled:@xpsp2res.dll,-22004
"445:TCP" = 445:TCP:*:Enabled:@xpsp2res.dll,-22005
"137:UDP" = 137:UDP:*:Enabled:@xpsp2res.dll,-22001
"138:UDP" = 138:UDP:*:Enabled:@xpsp2res.dll,-22002
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile]
"EnableFirewall" = 0
"DisableNotifications" = 1
"DoNotAllowExceptions" = 0
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\GloballyOpenPorts\List]
"10421:UDP" = 10421:UDP:*:Enabled:SingleClick Discovery Protocol
"10426:UDP" = 10426:UDP:*:Enabled:SingleClick ICC
"139:TCP" = 139:TCP:LocalSubNet:Enabled:@xpsp2res.dll,-22004
"445:TCP" = 445:TCP:LocalSubNet:Enabled:@xpsp2res.dll,-22005
"137:UDP" = 137:UDP:LocalSubNet:Enabled:@xpsp2res.dll,-22001
"138:UDP" = 138:UDP:LocalSubNet:Enabled:@xpsp2res.dll,-22002
"1900:UDP" = 1900:UDP:LocalSubNet:Enabled:@xpsp2res.dll,-22007
"2869:TCP" = 2869:TCP:LocalSubNet:Enabled:@xpsp2res.dll,-22008
========== Authorized Applications List ========== [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\DomainProfile\AuthorizedApplications\List]
"C:\Program Files\CyberLink\PowerDVD DX\PowerDVD.exe" = C:\Program Files\CyberLink\PowerDVD DX\PowerDVD.exe:*:Enabled:CyberLink PowerDVD DX -- (CyberLink Corp.)
"C:\Program Files\CyberLink\PowerDVD DX\PDVDDXSrv.exe" = C:\Program Files\CyberLink\PowerDVD DX\PDVDDXSrv.exe:*:Enabled:CyberLink PowerDVD DX Resident Program -- (CyberLink Corp.)
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\SharedAccess\Parameters\FirewallPolicy\StandardProfile\AuthorizedApplications\List]
"C:\Program Files\CyberLink\PowerDVD DX\PowerDVD.exe" = C:\Program Files\CyberLink\PowerDVD DX\PowerDVD.exe:*:Enabled:CyberLink PowerDVD DX -- (CyberLink Corp.)
"C:\Program Files\CyberLink\PowerDVD DX\PDVDDXSrv.exe" = C:\Program Files\CyberLink\PowerDVD DX\PDVDDXSrv.exe:*:Enabled:CyberLink PowerDVD DX Resident Program -- (CyberLink Corp.)
"C:\Program Files\Sybase\SQL Anywhere 9\win32\dbeng9.exe" = C:\Program Files\Sybase\SQL Anywhere 9\win32\dbeng9.exe:*:Enabled:Adaptive Server Anywhere Database Engine -- (iAnywhere Solutions, Inc.)
"C:\Program Files\Yahoo!\Messenger\YahooMessenger.exe" = C:\Program Files\Yahoo!\Messenger\YahooMessenger.exe:*:Enabled:Yahoo! Messenger -- (Yahoo! Inc.)
"C:\Program Files\Yahoo!\Messenger\YServer.exe" = C:\Program Files\Yahoo!\Messenger\YServer.exe:*:Enabled:Yahoo! FT Server
"C:\Program Files\Google\Google Desktop Search\GoogleDesktop.exe" = C:\Program Files\Google\Google Desktop Search\GoogleDesktop.exe:*:Enabled:Google Desktop
"C:\Program Files\Ares\Ares.exe" = C:\Program Files\Ares\Ares.exe:*:Enabled:Ares p2p for windows -- (Ares Development Group)
"C:\Program Files\Dell Network Assistant\ezi_hnm2.exe" = C:\Program Files\Dell Network Assistant\ezi_hnm2.exe:*:Enabled:Dell Network Assistant -- (SingleClick Systems)
"C:\Program Files\BitTorrent\bittorrent.exe" = C:\Program Files\BitTorrent\bittorrent.exe:*:Enabled:BitTorrent
"C:\Program Files\LimeWire\LimeWire.exe" = C:\Program Files\LimeWire\LimeWire.exe:*:Enabled:LimeWire
"C:\Documents and Settings\All Users\Application Data\Kaspersky Lab Setup Files\Kaspersky Internet Security 2010 9.0.0.736\English\setup.exe" = C:\Documents and Settings\All Users\Application Data\Kaspersky Lab Setup Files\Kaspersky Internet Security 2010 9.0.0.736\English\setup.exe:*:Enabled:Kaspersky Internet Security 2010 Setup -- (Kaspersky Lab)
"C:\Program Files\Java\jre6\bin\java.exe" = C:\Program Files\Java\jre6\bin\java.exe:*:Enabled:Java™ Platform SE binary -- (Sun Microsystems, Inc.)
"C:\Program Files\Google\Google Earth\client\googleearth.exe" = C:\Program Files\Google\Google Earth\client\googleearth.exe:*:Enabled:Google Earth -- (Google)
========== HKEY_LOCAL_MACHINE Uninstall List ========== [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall]
"{0240BDFB-2995-4A3F-8C96-18D41282B716}" = Dell Network Assistant
"{0394CDC8-FABD-4ED8-B104-03393876DFDF}" = Roxio Creator Tools
"{07159635-9DFE-4105-BFC0-2817DB540C68}" = Roxio Activation Module
"{0D397393-9B50-4C52-84D5-77E344289F87}" = Roxio Creator Data
"{183B7569-90FB-4C56-9761-0EEB002CAB83}" = Adobe Camera Raw 4.0
"{1F1C2DFC-2D24-3E06-BCB8-725134ADF989}" = Microsoft Visual C++ 2008 Redistributable - x86 9.0.30729.4148
"{20B83B31-09C4-4F0E-9774-EF8A12A0A527}" = Adobe Device Central CS3
"{216AB108-2AE1-4130-B3D5-20B2C4C80F8F}" = QuickTime
"{24D7346D-D4B4-45E8-98EA-75EC14B42DD8}" = Adobe ExtendScript Toolkit 2
"{26A24AE4-039D-4CA4-87B4-2F83216010FF}" = Java™ 6 Update 10
"{28C2DED6-325B-4CC7-983A-1777C8F7FBAB}" = RealUpgrade 1.1
"{2A539CD9-0F75-4875-9A32-E06DD93C4114}" = Adobe Extension Manager CS3
"{2F4C24E6-CBD4-4AAC-B56F-C9FD44DE5668}" = Roxio Drag-to-Disc
"{30465B6C-B53F-49A1-9EBA-A3F187AD502E}" = Roxio Update Manager
"{3248F0A8-6813-11D6-A77B-00B0D0150090}" = J2SE Runtime Environment 5.0 Update 9
"{350C97B0-3D7C-4EE8-BAA9-00BCB3D54227}" = WebFldrs XP
"{35343FF7-939B-401A-87B3-FF90A5123D88}" = Microsoft XML Parser and SDK
"{3A12C952-61D5-4C3B-B68B-8CFBE47E22F1}" = Adobe Setup
"{3F92ABBB-6BBF-11D5-B229-002078017FBF}" = NetWaiting
"{41C3C974-EC5E-494C-AFE6-E31D92E2E6CB}" = Adobe Version Cue CS3 Client
"{4DF98D0B-637E-42B4-B9D6-EB7693D2FBF8}" = Adobe ExtendScript Toolkit 2
"{5576CA87-D0FE-497A-AC09-D4153311AA13}" = Field Technology Illustration System
"{619CDD8A-14B6-43A1-AB6C-0F4EE48CE048}" = Roxio Creator Copy
"{64C1FA9A-FA94-4B6E-B3E4-8573738E4AD1}" = Adobe Setup
"{6811CAA0-BF12-11D4-9EA1-0050BAE317E1}" = PowerDVD
"{68CF6DD2-8BA3-4A70-81D8-7CC5F24C9BA2}" = Adobe Bridge CS3
"{6D4AC5A4-4CF9-4F90-8111-B9B53CE257BF}" = Adobe Color Common Settings
"{733D84D6-AAFD-4368-A1D0-F2734F6B9082}" = Adobe Help Viewer CS3
"{7770E71B-2D43-4800-9CB3-5B6CAAEBEBEA}" = RealNetworks - Microsoft Visual C++ 2008 Runtime
"{7F3A2319-79CF-4701-95FB-034E99281808}" = Adobe Bridge Start Meeting
"{83FFCFC7-88C6-41C6-8752-958A45325C82}" = Roxio Creator Audio
"{86CE85E6-DBAC-3FFD-B977-E4B79F83C909}" = Microsoft Visual C++ 2008 Redistributable - KB2467174 - x86 9.0.30729.5570
"{880AF49C-34F7-4285-A8AD-8F7A3D1C33DC}" = Roxio Creator BDAV Plugin
"{8A25392D-C5D2-4E79-A2BD-C15DDC5B0959}" = Bonjour
"{8BC84ECC-EA87-49C0-93C0-2B5DF62745CD}" = Adobe Asset Services CS3
"{8D337F77-BE7F-41A2-A7CB-D5A63FD7049B}" = Sonic CinePlayer Decoder Pack
"{8E6808E2-613D-4FCD-81A2-6C8FA8E03312}" = Adobe Type Support
"{90110409-6000-11D3-8CFE-0150048383C9}" = Microsoft Office Professional Edition 2003
"{90120000-0020-0409-0000-0000000FF1CE}" = Compatibility Pack for the 2007 Office system
"{90176341-0A8B-4CCC-A78D-F862228A6B95}" = Adobe Anchor Service CS3
"{95120000-00AF-0409-0000-0000000FF1CE}" = Microsoft Office PowerPoint Viewer 2007 (English)
"{A2B242BD-FF8D-4840-9DAA-9170EABEC59C}" = Adobe CMaps
"{A2BCA9F1-566C-4805-97D1-7FDC93386723}" = Adobe AIR
"{A3051CD0-2F64-3813-A88D-B8DCCDE8F8C7}" = Microsoft .NET Framework 3.0 Service Pack 2
"{A92DAB39-4E2C-4304-9AB6-BC44E68B55E2}" = Google Update Helper
"{AC76BA86-7AD7-1033-7B44-A82000000003}" = Adobe Reader 8.2.6
"{AD88355B-A4E0-4DA1-BAC3-EA4FEA930691}" = Ipswitch WS_FTP Professional 2007
"{AF36CE1D-FD2C-4BA0-93FA-1196785DD610}" = Adobe Flash Player 10 Plugin
"{B3C02EC1-A7B0-4987-9A43-8789426AAA7D}" = Adobe Setup
"{B3FED300-806C-11E0-A0D0-B8AC6F97B88E}" = Google Earth
"{B9B35331-B7E4-4E5C-BF4C-7BC87856124D}" = Adobe Default Language CS3
"{C09FB3CD-3D0C-3F2D-899A-6A1D67F2073F}" = Microsoft .NET Framework 2.0 Service Pack 2
"{C5074CC4-0E26-4716-A307-960272A90040}" = QuickSet
"{C8B0680B-CDAE-4809-9F91-387B6DE00F7C}" = Roxio Creator DE
"{C99C0593-3B48-41D9-B42F-6E035B320449}" = Broadcom Management Programs
"{CB2F7EDD-9D1F-43C1-90FC-4F52EAE172A1}" = Microsoft .NET Framework 1.1
"{CDDCBBF1-2703-46BC-938B-BCC81A1EEAAA}" = SUPERAntiSpyware
"{CE2CDD62-0124-36CA-84D3-9F4DCF5C5BD9}" = Microsoft .NET Framework 3.5 SP1
"{D1C59F81-66FD-4E8E-B9F7-F4B2442D5222}" = Adobe Update Manager CS3
"{D2559B88-CC9D-4B48-81BB-F492BAA9C48C}" = Adobe PDF Library Files
"{D7F58B2A-8157-4456-8A9A-26982DFFC0A5}" = Field Technology Illustration System
"{E2883E8F-472F-4fb0-9522-AC9BF37916A7}" = Adobe Download Manager
"{E3BFEE55-39E2-4BE0-B966-89FE583822C1}" = Dell Support Center (Support Software)
"{E646DCF0-5A68-11D5-B229-002078017FBF}" = Digital Line Detect
"{E7D68102-199C-4EC0-8AD9-8295EEA6EFAB}" = Field Technology Illustration System
"{EF40BAC3-372B-46F4-A32D-B37CF4217CE7}" = ATI Catalyst Control Center
"{F01D5ED5-D53A-4468-B428-149DC2CB3110}" = Adobe Dreamweaver CS3
"{F63A3748-B93D-4360-9AD4-B064481A5C7B}" = Modem Diagnostic Tool
"{FA298A96-4E7D-469B-B12A-F16B001CE8DC}" = MS Scripting ActiveX Fix
"Adobe AIR" = Adobe AIR
"Adobe Flash Player ActiveX" = Adobe Flash Player 10 ActiveX
"Adobe_3e054d2218e7aa282c2369d939e58ff" = Adobe ExtendScript Toolkit 2
"Adobe_435a6af7459cb02a9c1138113a26e93" = Adobe Dreamweaver CS3
"Adobe_6c8e2cb4fd241c55406016127a6ab2e" = Adobe Color Common Settings
"Ares" = Ares 2.0.9
"ATI Display Driver" = ATI Display Driver
"avast" = avast! Free Antivirus
"Broadcom 802.11b Network Adapter" = Dell Wireless WLAN Card
"CCleaner" = CCleaner
"CNXT_MODEM_HDAUDIO_VEN_14F1&DEV_2C06&SUBSYS_14F1000F" = Conexant HDA D330 MDC V.92 Modem
"Coupon Printer for Windows5.0.0.0" = Coupon Printer for Windows
"Crystal Button 2008 InMotion! Pack_is1" = Crystal Button 2008 InMotion! (v.3.2)
"CutePDF Writer Installation" = CutePDF Writer 2.7
"G-Force" = G-Force
"Glary Utilities_is1" = Glary Utilities 2.35.0.1216
"Google Chrome" = Google Chrome
"IDNMitigationAPIs" = Microsoft Internationalized Domain Names Mitigation APIs
"ie7" = Windows Internet Explorer 7
"ie8" = Windows Internet Explorer 8
"Malwarebytes' Anti-Malware_is1" = Malwarebytes' Anti-Malware version 1.51.1.1800
"Microsoft .NET Framework 1.1 (1033)" = Microsoft .NET Framework 1.1
"Microsoft .NET Framework 3.5 SP1" = Microsoft .NET Framework 3.5 SP1
"Mozilla Firefox (3.0.19)" = Mozilla Firefox (3.0.19)
"MSCompPackV1" = Microsoft Compression Client Pack 1.0 for Windows XP
"NLSDownlevelMapping" = Microsoft National Language Support Downlevel APIs
"RealPlayer 12.0" = RealPlayer
"SynTPDeinstKey" = Dell Touchpad
"Time Stamp_is1" = Time Stamp
"Windows Media Format Runtime" = Windows Media Format 11 runtime
"Windows Media Player" = Windows Media Player 11
"Windows XP Service Pack" = Windows XP Service Pack 3
"WinZip" = WinZip
"WMCSetup" = Windows Media Connect
"WMFDist11" = Windows Media Format 11 runtime
"wmp11" = Windows Media Player 11
"Wudf01000" = Microsoft User-Mode Driver Framework Feature Pack 1.0
"Yahoo! Mail" = Yahoo! Internet Mail
"Yahoo! Messenger" = Yahoo! Messenger
========== HKEY_CURRENT_USER Uninstall List ========== [HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall]
"Move Media Player" = Move Media Player
========== Last 10 Event Log Errors ========== [ Application Events ]
Error - 5/14/2011 2:59:11 PM | Computer Name = VERNON | Source = Application Hang | ID = 1002
Description = Hanging application YahooMessenger.exe, version 9.0.0.2162, hang module
hungapp, version 0.0.0.0, hang address 0x00000000.
Error - 5/30/2011 11:35:41 AM | Computer Name = VERNON | Source = PerfNet | ID = 2004
Description = Unable to open the Server service. Server performance data will not
be returned. Error code returned is in data DWORD 0.
Error - 5/30/2011 4:40:39 PM | Computer Name = VERNON | Source = crypt32 | ID = 131080
Description = Failed auto update retrieval of third-party root list sequence number
from: <
http://www.download....uthrootseq.txt> with error: This operation returned because the timeout period expired.
Error - 5/30/2011 4:40:39 PM | Computer Name = VERNON | Source = crypt32 | ID = 131080
Description = Failed auto update retrieval of third-party root list sequence number
from: <
http://www.download....uthrootseq.txt> with error: The specified server cannot perform the requested operation.
Error - 5/30/2011 4:40:39 PM | Computer Name = VERNON | Source = crypt32 | ID = 131080
Description = Failed auto update retrieval of third-party root list sequence number
from: <
http://www.download....uthrootseq.txt> with error: The specified server cannot perform the requested operation.
Error - 6/6/2011 6:01:15 PM | Computer Name = VERNON | Source = PerfNet | ID = 2004
Description = Unable to open the Server service. Server performance data will not
be returned. Error code returned is in data DWORD 0.
Error - 6/7/2011 12:45:10 PM | Computer Name = VERNON | Source = PerfNet | ID = 2004
Description = Unable to open the Server service. Server performance data will not
be returned. Error code returned is in data DWORD 0.
Error - 6/8/2011 5:59:35 PM | Computer Name = VERNON | Source = Application Error | ID = 1000
Description = Faulting application iexplore.exe, version 8.0.6001.18702, faulting
module flash10q.ocx, version 10.3.181.14, fault address 0x0015e792.
Error - 7/5/2011 1:39:21 PM | Computer Name = VERNON | Source = Application Hang | ID = 1002
Description = Hanging application iexplore.exe, version 8.0.6001.18702, hang module
hungapp, version 0.0.0.0, hang address 0x00000000.
Error - 7/11/2011 1:51:34 PM | Computer Name = VERNON | Source = PerfNet | ID = 2004
Description = Unable to open the Server service. Server performance data will not
be returned. Error code returned is in data DWORD 0.
[ System Events ]
Error - 8/15/2011 1:38:35 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the SENS service.
Error - 8/15/2011 1:47:26 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the SENS service.
Error - 8/15/2011 1:48:31 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the Schedule service.
Error - 8/15/2011 1:49:37 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the SENS service.
Error - 8/15/2011 1:50:22 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the SENS service.
Error - 8/15/2011 1:57:06 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the SENS service.
Error - 8/15/2011 2:00:06 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the SENS service.
Error - 8/15/2011 2:06:34 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the SENS service.
Error - 8/15/2011 2:09:30 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the SENS service.
Error - 8/15/2011 2:13:52 AM | Computer Name = VERNON | Source = Service Control Manager | ID = 7011
Description = Timeout (30000 milliseconds) waiting for a transaction response from
the Schedule service.
< End of report >
Here is new OTL log:========== SERVICES/DRIVERS ==========
========== PROCESSES ==========
All processes killed
========== OTL ==========
C:\DOCUMENTS AND SETTINGS\VERNON BURDETTE\LOCAL SETTINGS\APPLICATION DATA\{7D16DCC9-78D2-4A42-9413-6075F7E646CE}\chrome\content folder moved successfully.
C:\DOCUMENTS AND SETTINGS\VERNON BURDETTE\LOCAL SETTINGS\APPLICATION DATA\{7D16DCC9-78D2-4A42-9413-6075F7E646CE}\chrome folder moved successfully.
C:\DOCUMENTS AND SETTINGS\VERNON BURDETTE\LOCAL SETTINGS\APPLICATION DATA\{7D16DCC9-78D2-4A42-9413-6075F7E646CE} folder moved successfully.
Registry value HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar\WebBrowser\\{604BC32A-9680-40D1-9AC6-E06B23A1BA4C} deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{604BC32A-9680-40D1-9AC6-E06B23A1BA4C}\ not found.
Registry value HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar\WebBrowser\\{EF99BD32-C1FB-11D2-892F-0090271D4F88} deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{EF99BD32-C1FB-11D2-892F-0090271D4F88}\ not found.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Extensions\{F4430FE8-2638-42e5-B849-800749B94EED}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F4430FE8-2638-42e5-B849-800749B94EED}\ not found.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Extensions\{F4430FE8-2638-42e5-B849-800749B94EED}\ not found.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{F4430FE8-2638-42e5-B849-800749B94EED}\ not found.
Starting removal of ActiveX control {8AD9C840-044E-11D1-B3E9-00805F499D93}
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Code Store Database\Distribution Units\{8AD9C840-044E-11D1-B3E9-00805F499D93}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{8AD9C840-044E-11D1-B3E9-00805F499D93}\ deleted successfully.
Registry key HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{8AD9C840-044E-11D1-B3E9-00805F499D93}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{8AD9C840-044E-11D1-B3E9-00805F499D93}\ not found.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{8AD9C840-044E-11D1-B3E9-00805F499D93}\ not found.
Starting removal of ActiveX control {CAFEEFAC-0015-0000-0009-ABCDEFFEDCBA}
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Code Store Database\Distribution Units\{CAFEEFAC-0015-0000-0009-ABCDEFFEDCBA}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{CAFEEFAC-0015-0000-0009-ABCDEFFEDCBA}\ deleted successfully.
Registry key HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{CAFEEFAC-0015-0000-0009-ABCDEFFEDCBA}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{CAFEEFAC-0015-0000-0009-ABCDEFFEDCBA}\ not found.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{CAFEEFAC-0015-0000-0009-ABCDEFFEDCBA}\ not found.
Starting removal of ActiveX control {CAFEEFAC-0016-0000-0010-ABCDEFFEDCBA}
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Code Store Database\Distribution Units\{CAFEEFAC-0016-0000-0010-ABCDEFFEDCBA}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{CAFEEFAC-0016-0000-0010-ABCDEFFEDCBA}\ deleted successfully.
Registry key HKEY_CURRENT_USER\SOFTWARE\Classes\CLSID\{CAFEEFAC-0016-0000-0010-ABCDEFFEDCBA}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{CAFEEFAC-0016-0000-0010-ABCDEFFEDCBA}\ not found.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{CAFEEFAC-0016-0000-0010-ABCDEFFEDCBA}\ not found.
Starting removal of ActiveX control {CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA}
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Code Store Database\Distribution Units\{CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\{CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA}\ not found.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA}\ not found.
File oft XML Parser for Java file:///C:/WINDOWS/Java/classes/xmldso.cab not found.
Starting removal of ActiveX control Microsoft XML Parser for Java
Registry error reading value HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Code Store Database\Distribution Units\Microsoft XML Parser for Java\DownloadInformation\\INF .
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Code Store Database\Distribution Units\Microsoft XML Parser for Java\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\Microsoft XML Parser for Java\ not found.
Registry key HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\{b01dab40-20a2-11de-a083-001644c97dd2}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{b01dab40-20a2-11de-a083-001644c97dd2}\ not found.
File E:\SetupAssistant.exe not found.
Registry key HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\{e447807d-b5d8-11dd-a065-001644c97dd2}\ deleted successfully.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{e447807d-b5d8-11dd-a065-001644c97dd2}\ not found.
Registry key HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\{e447807d-b5d8-11dd-a065-001644c97dd2}\ not found.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{e447807d-b5d8-11dd-a065-001644c97dd2}\ not found.
Registry key HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\MountPoints2\{e447807d-b5d8-11dd-a065-001644c97dd2}\ not found.
Registry key HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{e447807d-b5d8-11dd-a065-001644c97dd2}\ not found.
File E:\LaunchU3.exe -a not found.
C:\Documents and Settings\Vernon Burdette\Local Settings\Application Data\ubu1g06qna22xo0d6g4fsrfg2do moved successfully.
C:\Documents and Settings\All Users\Application Data\ubu1g06qna22xo0d6g4fsrfg2do moved successfully.
C:\WINDOWS\Xlahipidu.dat moved successfully.
C:\WINDOWS\Tsecimijigokima.bin moved successfully.
C:\WINDOWS\system32\drivers\mcelfmgx.sys moved successfully.
ADS C:\Documents and Settings\All Users\Application Data\TEMP:54F7A151 deleted successfully.
ADS C:\Documents and Settings\All Users\Application Data\TEMP:62E2D794 deleted successfully.
========== REGISTRY ==========
========== FILES ==========
< echo,Y|cacls "%WinDir%\system32\drivers\etc\hosts" /G everyone:f /c >C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\cmd.bat deleted successfully.
C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\cmd.txt deleted successfully.
< ipconfig /flushdns /c >C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\cmd.bat deleted successfully.
C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\cmd.txt deleted successfully.
========== COMMANDS ==========
C:\WINDOWS\System32\drivers\etc\Hosts moved successfully.
HOSTS file reset successfully
Unable to start service SrService!
[EMPTYFLASH]
User: All Users
User: Default User
->Flash cache emptied: 41620 bytes
User: LocalService
User: NetworkService
User: Vernon Burdette
->Flash cache emptied: 323154 bytes
Total Flash Files Cleaned = 0.00 mb
OTL by OldTimer - Version 3.2.26.4 log created on 08152011_162526
Files\Folders moved on Reboot...
Registry entries deleted on Reboot...
And finally here is GMER log:
GMER 1.0.15.15641 -
http://www.gmer.netRootkit scan 2011-08-15 20:29:28
Windows 5.1.2600 Service Pack 3 Harddisk0\DR0 -> \Device\Ide\IdeDeviceP2T0L0-3 Hitachi_HTS542512K9SA00 rev.BB2OC39P
Running: gmer.exe; Driver: C:\DOCUME~1\VERNON~1\LOCALS~1\Temp\uxtdypog.sys
---- System - GMER 1.0.15 ----
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwAddBootEntry [0xB116A202]
SSDT \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software) ZwAllocateVirtualMemory [0xB11D0D8C]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwClose [0xB118E6C1]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwCreateEvent [0xB116C7F0]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwCreateEventPair [0xB116C848]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwCreateIoCompletion [0xB116C95E]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwCreateKey [0xB118E075]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwCreateMutant [0xB116C746]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwCreateSection [0xB116C898]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwCreateSemaphore [0xB116C79A]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwCreateTimer [0xB116C90C]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwDeleteBootEntry [0xB116A226]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwDeleteKey [0xB118ED87]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwDeleteValueKey [0xB118F03D]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwDuplicateObject [0xB116CBE2]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwEnumerateKey [0xB118EBF2]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwEnumerateValueKey [0xB118EA5D]
SSDT \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software) ZwFreeVirtualMemory [0xB11D0E3C]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwLoadDriver [0xB1169FF0]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwModifyBootEntry [0xB116A24A]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwNotifyChangeKey [0xB116CD56]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwNotifyChangeMultipleKeys [0xB116ACDA]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenEvent [0xB116C820]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenEventPair [0xB116C870]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenIoCompletion [0xB116C988]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenKey [0xB118E3D1]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenMutant [0xB116C772]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenProcess [0xB116CA1A]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenSection [0xB116C8D8]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenSemaphore [0xB116C7C8]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenThread [0xB116CAFE]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwOpenTimer [0xB116C936]
SSDT \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software) ZwProtectVirtualMemory [0xB11D0ED4]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwQueryKey [0xB118E8D8]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwQueryObject [0xB116ABA0]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwQueryValueKey [0xB118E72A]
SSDT \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software) ZwRenameKey [0xB11D910E]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwRestoreKey [0xB118D6E8]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwSetBootEntryOrder [0xB116A26E]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwSetBootOptions [0xB116A292]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwSetSystemInformation [0xB116A04A]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwSetSystemPowerState [0xB116A186]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwSetValueKey [0xB118EE8E]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwShutdownSystem [0xB116A162]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwSystemDebugControl [0xB116A1AA]
SSDT \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software) ZwVdmControl [0xB116A2B6]
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software) ZwCreateProcessEx [0xB11E6398]
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software) ObInsertObject
Code \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software) ObMakeTemporaryObject
---- Kernel code sections - GMER 1.0.15 ----
.text ntkrnlpa.exe!ZwCallbackReturn + 24A8 80501CE0 4 Bytes JMP 926EB118
.text ntkrnlpa.exe!ZwCallbackReturn + 2604 80501E3C 4 Bytes [D8, E8, 18, B1]
.text ntkrnlpa.exe!ZwCallbackReturn + 26B4 80501EEC 4 Bytes [E8, D6, 18, B1]
PAGE ntkrnlpa.exe!ZwReplyWaitReceivePortEx + 5EC 8059B8EC 4 Bytes CALL B116B335 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
PAGE ntkrnlpa.exe!ObMakeTemporaryObject 805B1DB4 5 Bytes JMP B11E1D4C \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software)
PAGE ntkrnlpa.exe!ObInsertObject 805B8C2C 5 Bytes JMP B11E37F2 \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software)
PAGE ntkrnlpa.exe!ZwCreateProcessEx 805C74CC 7 Bytes JMP B11E639C \SystemRoot\System32\Drivers\aswSP.SYS (avast! self protection module/AVAST Software)
.text win32k.sys!EngFreeUserMem + 674 BF809922 5 Bytes JMP B116DCA2 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngDeleteSurface + 45 BF813911 5 Bytes JMP B116DBAE \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngSetLastError + 783B BF824157 5 Bytes JMP B116CF34 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngCreateBitmap + F9C BF828CE9 5 Bytes JMP B116DE0C \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngUnmapFontFileFD + 2C50 BF8316DA 5 Bytes JMP B116E014 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngUnmapFontFileFD + B8F2 BF83A37C 5 Bytes JMP B116DB1E \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngCopyBits + 5F35 BF857E69 5 Bytes JMP B116CFA4 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!XLATEOBJ_iXlate + 348C BF866FF4 5 Bytes JMP B116D180 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!XLATEOBJ_iXlate + 3517 BF86707F 5 Bytes JMP B116D326 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!XLATEOBJ_iXlate + 3F47 BF867AAF 5 Bytes JMP B116CE58 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!XLATEOBJ_iXlate + AAFC BF86E664 5 Bytes JMP B116DBD8 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngUnicodeToMultiByteN + 2ED7 BF871F85 5 Bytes JMP B116DF72 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngGetCurrentCodePage + 411E BF88C9D8 5 Bytes JMP B116D2FE \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngTextOut + 4149 BF8B0CBE 5 Bytes JMP B116CE70 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngCreatePalette + 2DBF BF8C26A3 5 Bytes JMP B116DD54 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngStretchBltROP + 450 BF8C3048 5 Bytes JMP B116D03E \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngFillPath + 1517 BF8CB4AA 1 Byte [E9]
.text win32k.sys!EngFillPath + 1517 BF8CB4AA 5 Bytes JMP B116D0AE \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngFillPath + 1797 BF8CB72A 5 Bytes JMP B116D0E8 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngDeleteSemaphore + 3B3E BF8ED1B7 5 Bytes JMP B116CD8C \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngCreateClip + 19B2 BF913F1F 5 Bytes JMP B116CEF0 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngCreateClip + 2586 BF914AF3 5 Bytes JMP B116D008 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngCreateClip + 4EE5 BF917452 5 Bytes JMP B116D440 \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
.text win32k.sys!EngPlgBlt + 1924 BF945FB0 5 Bytes JMP B116DECA \SystemRoot\System32\Drivers\aswSnx.SYS (avast! Virtualization Driver/AVAST Software)
---- User code sections - GMER 1.0.15 ----
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 00390804
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 00390A08
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 00390600
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003901F8
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003903FC
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 003A1014
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 003A0804
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 003A0A08
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 003A0C0C
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 003A0E10
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003A01F8
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003A03FC
.text C:\Program Files\SUPERAntiSpyware\SASCORE.EXE[124] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 003A0600
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 00391014
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 00390804
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 00390A08
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 00390C0C
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 00390E10
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003901F8
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003903FC
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 00390600
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 003A0804
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 003A0A08
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 003A0600
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003A01F8
.text C:\Program Files\Bonjour\mDNSResponder.exe[156] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003A03FC
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 004A1014
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 004A0804
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 004A0A08
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 004A0C0C
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 004A0E10
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 004A01F8
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 004A03FC
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 004A0600
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 004B0804
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 004B0A08
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 004B0600
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 004B01F8
.text C:\Program Files\Dell Network Assistant\hnm_svc.exe[220] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 004B03FC
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 00391014
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 00390804
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 00390A08
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 00390C0C
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 00390E10
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003901F8
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003903FC
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 00390600
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 003A0804
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 003A0A08
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 003A0600
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003A01F8
.text C:\Program Files\Google\Update\GoogleUpdate.exe[248] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003A03FC
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001401F8
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001403FC
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 00381014
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 00380804
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 00380A08
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 00380C0C
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 00380E10
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003801F8
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003803FC
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 00380600
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 00390804
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 00390A08
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 00390600
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003901F8
.text C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE[304] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003903FC
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 00390804
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 00390A08
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 00390600
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003901F8
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003903FC
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 003A1014
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 003A0804
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 003A0A08
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 003A0C0C
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 003A0E10
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003A01F8
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003A03FC
.text C:\Program Files\Dell Support Center\bin\sprtsvc.exe[568] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 003A0600
.text C:\WINDOWS\System32\smss.exe[584] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[624] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\svchost.exe[624] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[624] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\svchost.exe[624] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[624] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\svchost.exe[624] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\svchost.exe[624] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\svchost.exe[624] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\svchost.exe[624] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\svchost.exe[624] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\svchost.exe[624] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\svchost.exe[624] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\svchost.exe[624] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\svchost.exe[624] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\svchost.exe[624] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\svchost.exe[624] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\svchost.exe[624] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\csrss.exe[632] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\csrss.exe[632] KERNEL32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\winlogon.exe[660] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000701F8
.text C:\WINDOWS\system32\winlogon.exe[660] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\winlogon.exe[660] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000703FC
.text C:\WINDOWS\system32\winlogon.exe[660] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\winlogon.exe[660] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\winlogon.exe[660] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\winlogon.exe[660] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\winlogon.exe[660] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\winlogon.exe[660] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\winlogon.exe[660] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\winlogon.exe[660] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\winlogon.exe[660] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\winlogon.exe[660] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\winlogon.exe[660] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\winlogon.exe[660] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\winlogon.exe[660] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\winlogon.exe[660] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\services.exe[704] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\services.exe[704] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\services.exe[704] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\services.exe[704] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\services.exe[704] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\services.exe[704] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\services.exe[704] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\services.exe[704] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\services.exe[704] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\services.exe[704] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\services.exe[704] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\services.exe[704] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\services.exe[704] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\services.exe[704] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\services.exe[704] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\services.exe[704] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\services.exe[704] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\lsass.exe[716] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\lsass.exe[716] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\lsass.exe[716] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\lsass.exe[716] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\lsass.exe[716] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\lsass.exe[716] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\lsass.exe[716] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\lsass.exe[716] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\lsass.exe[716] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\lsass.exe[716] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\lsass.exe[716] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\lsass.exe[716] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\lsass.exe[716] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\lsass.exe[716] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\lsass.exe[716] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\lsass.exe[716] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\lsass.exe[716] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\svchost.exe[900] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\svchost.exe[900] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[900] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\svchost.exe[900] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[900] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\svchost.exe[900] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\svchost.exe[900] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\svchost.exe[900] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\svchost.exe[900] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\svchost.exe[900] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\svchost.exe[900] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\svchost.exe[900] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\svchost.exe[900] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\svchost.exe[900] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\svchost.exe[900] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\svchost.exe[900] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\svchost.exe[900] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\svchost.exe[968] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\svchost.exe[968] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[968] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\svchost.exe[968] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[968] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\svchost.exe[968] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\svchost.exe[968] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\svchost.exe[968] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\svchost.exe[968] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\svchost.exe[968] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\svchost.exe[968] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\svchost.exe[968] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\svchost.exe[968] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\svchost.exe[968] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\svchost.exe[968] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\svchost.exe[968] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\svchost.exe[968] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\System32\svchost.exe[1008] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\System32\svchost.exe[1008] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\System32\svchost.exe[1008] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\System32\svchost.exe[1008] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\System32\svchost.exe[1008] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\System32\svchost.exe[1008] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\System32\svchost.exe[1008] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\System32\svchost.exe[1008] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\System32\svchost.exe[1008] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\System32\svchost.exe[1008] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\System32\svchost.exe[1008] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\System32\svchost.exe[1008] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\System32\svchost.exe[1008] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\System32\svchost.exe[1008] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\System32\svchost.exe[1008] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\System32\svchost.exe[1008] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\System32\svchost.exe[1008] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\svchost.exe[1096] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\svchost.exe[1096] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[1096] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\svchost.exe[1096] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[1096] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\svchost.exe[1096] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\svchost.exe[1096] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\svchost.exe[1096] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\svchost.exe[1096] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\svchost.exe[1096] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\svchost.exe[1096] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\svchost.exe[1096] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\svchost.exe[1096] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\svchost.exe[1096] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\svchost.exe[1096] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\svchost.exe[1096] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\svchost.exe[1096] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\svchost.exe[1172] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\svchost.exe[1172] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[1172] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\svchost.exe[1172] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[1172] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\svchost.exe[1172] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\svchost.exe[1172] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\svchost.exe[1172] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\svchost.exe[1172] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\svchost.exe[1172] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\svchost.exe[1172] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\svchost.exe[1172] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\svchost.exe[1172] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\svchost.exe[1172] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\svchost.exe[1172] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\svchost.exe[1172] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\svchost.exe[1172] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 00390804
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 00390A08
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 00390600
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003901F8
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003903FC
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 003A1014
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 003A0804
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 003A0A08
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 003A0C0C
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 003A0E10
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003A01F8
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003A03FC
.text C:\WINDOWS\System32\WLTRYSVC.EXE[1416] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 003A0600
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\WINDOWS\System32\bcmwltry.exe[1436] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 003D1014
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 003D0804
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 003D0A08
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 003D0C0C
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 003D0E10
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003D01F8
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003D03FC
.text C:\WINDOWS\System32\bcmwltry.exe[1436] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 003D0600
.text C:\WINDOWS\System32\bcmwltry.exe[1436] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 003E0804
.text C:\WINDOWS\System32\bcmwltry.exe[1436] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 003E0A08
.text C:\WINDOWS\System32\bcmwltry.exe[1436] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 003E0600
.text C:\WINDOWS\System32\bcmwltry.exe[1436] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003E01F8
.text C:\WINDOWS\System32\bcmwltry.exe[1436] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003E03FC
.text C:\Program Files\Alwil Software\Avast5\AvastSvc.exe[1540] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\Alwil Software\Avast5\AvastSvc.exe[1540] kernel32.dll!SetUnhandledExceptionFilter 7C84495D 4 Bytes [C2, 04, 00, 90] {RET 0x4; NOP }
.text C:\Program Files\Alwil Software\Avast5\AvastSvc.exe[1540] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\Explorer.EXE[1564] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\Explorer.EXE[1564] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\Explorer.EXE[1564] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\Explorer.EXE[1564] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\Explorer.EXE[1564] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002C1014
.text C:\WINDOWS\Explorer.EXE[1564] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002C0804
.text C:\WINDOWS\Explorer.EXE[1564] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002C0A08
.text C:\WINDOWS\Explorer.EXE[1564] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002C0C0C
.text C:\WINDOWS\Explorer.EXE[1564] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002C0E10
.text C:\WINDOWS\Explorer.EXE[1564] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002C01F8
.text C:\WINDOWS\Explorer.EXE[1564] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002C03FC
.text C:\WINDOWS\Explorer.EXE[1564] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002C0600
.text C:\WINDOWS\Explorer.EXE[1564] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002D0804
.text C:\WINDOWS\Explorer.EXE[1564] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002D0A08
.text C:\WINDOWS\Explorer.EXE[1564] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002D0600
.text C:\WINDOWS\Explorer.EXE[1564] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002D01F8
.text C:\WINDOWS\Explorer.EXE[1564] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002D03FC
.text C:\WINDOWS\system32\spoolsv.exe[1944] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\spoolsv.exe[1944] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\spoolsv.exe[1944] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\spoolsv.exe[1944] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\spoolsv.exe[1944] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\spoolsv.exe[1944] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\spoolsv.exe[1944] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\spoolsv.exe[1944] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\spoolsv.exe[1944] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\spoolsv.exe[1944] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\spoolsv.exe[1944] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\spoolsv.exe[1944] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\spoolsv.exe[1944] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\spoolsv.exe[1944] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\spoolsv.exe[1944] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\spoolsv.exe[1944] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\spoolsv.exe[1944] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\svchost.exe[2016] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\svchost.exe[2016] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[2016] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\svchost.exe[2016] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\svchost.exe[2016] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\system32\svchost.exe[2016] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\system32\svchost.exe[2016] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\system32\svchost.exe[2016] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\system32\svchost.exe[2016] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\system32\svchost.exe[2016] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\system32\svchost.exe[2016] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\system32\svchost.exe[2016] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\system32\svchost.exe[2016] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\svchost.exe[2016] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\svchost.exe[2016] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\svchost.exe[2016] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\svchost.exe[2016] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\wscntfy.exe[2360] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\system32\wscntfy.exe[2360] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\wscntfy.exe[2360] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\system32\wscntfy.exe[2360] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\wscntfy.exe[2360] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002D0804
.text C:\WINDOWS\system32\wscntfy.exe[2360] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002D0A08
.text C:\WINDOWS\system32\wscntfy.exe[2360] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002D0600
.text C:\WINDOWS\system32\wscntfy.exe[2360] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002D01F8
.text C:\WINDOWS\system32\wscntfy.exe[2360] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002D03FC
.text C:\WINDOWS\system32\wscntfy.exe[2360] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002E1014
.text C:\WINDOWS\system32\wscntfy.exe[2360] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002E0804
.text C:\WINDOWS\system32\wscntfy.exe[2360] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002E0A08
.text C:\WINDOWS\system32\wscntfy.exe[2360] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002E0C0C
.text C:\WINDOWS\system32\wscntfy.exe[2360] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002E0E10
.text C:\WINDOWS\system32\wscntfy.exe[2360] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002E01F8
.text C:\WINDOWS\system32\wscntfy.exe[2360] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002E03FC
.text C:\WINDOWS\system32\wscntfy.exe[2360] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002E0600
.text C:\Program Files\ATI Technologies\ATI.ACE\cli.exe[3024] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\ATI Technologies\ATI.ACE\cli.exe[3024] KERNEL32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001401F8
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001403FC
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 00381014
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 00380804
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 00380A08
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 00380C0C
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 00380E10
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003801F8
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003803FC
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 00380600
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 00390804
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 00390A08
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 00390600
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003901F8
.text C:\Program Files\Synaptics\SynTP\SynTPEnh.exe[3388] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003903FC
.text C:\Program Files\ATI Technologies\ATI.ACE\CLI.EXE[3620] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\ATI Technologies\ATI.ACE\CLI.EXE[3620] KERNEL32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\WINDOWS\system32\WLTRAY.exe[3652] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 003B1014
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 003B0804
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 003B0A08
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 003B0C0C
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 003B0E10
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003B01F8
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003B03FC
.text C:\WINDOWS\system32\WLTRAY.exe[3652] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 003B0600
.text C:\WINDOWS\system32\WLTRAY.exe[3652] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 003C0804
.text C:\WINDOWS\system32\WLTRAY.exe[3652] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 003C0A08
.text C:\WINDOWS\system32\WLTRAY.exe[3652] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 003C0600
.text C:\WINDOWS\system32\WLTRAY.exe[3652] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003C01F8
.text C:\WINDOWS\system32\WLTRAY.exe[3652] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003C03FC
.text C:\WINDOWS\System32\svchost.exe[3692] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000901F8
.text C:\WINDOWS\System32\svchost.exe[3692] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\System32\svchost.exe[3692] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000903FC
.text C:\WINDOWS\System32\svchost.exe[3692] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\System32\svchost.exe[3692] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002B1014
.text C:\WINDOWS\System32\svchost.exe[3692] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002B0804
.text C:\WINDOWS\System32\svchost.exe[3692] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002B0A08
.text C:\WINDOWS\System32\svchost.exe[3692] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002B0C0C
.text C:\WINDOWS\System32\svchost.exe[3692] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002B0E10
.text C:\WINDOWS\System32\svchost.exe[3692] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002B01F8
.text C:\WINDOWS\System32\svchost.exe[3692] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002B03FC
.text C:\WINDOWS\System32\svchost.exe[3692] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002B0600
.text C:\WINDOWS\System32\svchost.exe[3692] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002C0804
.text C:\WINDOWS\System32\svchost.exe[3692] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002C0A08
.text C:\WINDOWS\System32\svchost.exe[3692] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002C0600
.text C:\WINDOWS\System32\svchost.exe[3692] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002C01F8
.text C:\WINDOWS\System32\svchost.exe[3692] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002C03FC
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001401F8
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001403FC
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 00380804
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 00380A08
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 00380600
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003801F8
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003803FC
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 00391014
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 00390804
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 00390A08
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 00390C0C
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 00390E10
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003901F8
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003903FC
.text C:\Program Files\SigmaTel\C-Major Audio\WDM\stsystra.exe[3708] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 00390600
.text C:\Program Files\Alwil Software\Avast5\avastUI.exe[3716] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\Alwil Software\Avast5\avastUI.exe[3716] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 00390804
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 00390A08
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 00390600
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 003901F8
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 003903FC
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 003A1014
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 003A0804
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 003A0A08
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 003A0C0C
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 003A0E10
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003A01F8
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003A03FC
.text C:\Program Files\Dell Support Center\bin\sprtcmd.exe[3804] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 003A0600
.text C:\WINDOWS\system32\ctfmon.exe[3812] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 000A01F8
.text C:\WINDOWS\system32\ctfmon.exe[3812] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\WINDOWS\system32\ctfmon.exe[3812] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 000A03FC
.text C:\WINDOWS\system32\ctfmon.exe[3812] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\WINDOWS\system32\ctfmon.exe[3812] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 002C1014
.text C:\WINDOWS\system32\ctfmon.exe[3812] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 002C0804
.text C:\WINDOWS\system32\ctfmon.exe[3812] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 002C0A08
.text C:\WINDOWS\system32\ctfmon.exe[3812] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 002C0C0C
.text C:\WINDOWS\system32\ctfmon.exe[3812] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 002C0E10
.text C:\WINDOWS\system32\ctfmon.exe[3812] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 002C01F8
.text C:\WINDOWS\system32\ctfmon.exe[3812] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 002C03FC
.text C:\WINDOWS\system32\ctfmon.exe[3812] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 002C0600
.text C:\WINDOWS\system32\ctfmon.exe[3812] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 002D0804
.text C:\WINDOWS\system32\ctfmon.exe[3812] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 002D0A08
.text C:\WINDOWS\system32\ctfmon.exe[3812] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 002D0600
.text C:\WINDOWS\system32\ctfmon.exe[3812] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 002D01F8
.text C:\WINDOWS\system32\ctfmon.exe[3812] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 002D03FC
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ntdll.dll!LdrLoadDll 7C91632D 5 Bytes JMP 001501F8
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ntdll.dll!RtlDosSearchPath_U + 186 7C916865 1 Byte [62]
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ntdll.dll!LdrUnloadDll 7C9171CD 5 Bytes JMP 001503FC
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] kernel32.dll!GetBinaryTypeW + 80 7C868D8C 1 Byte [62]
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ADVAPI32.dll!SetServiceObjectSecurity 77E36D81 5 Bytes JMP 003F1014
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ADVAPI32.dll!ChangeServiceConfigA 77E36E69 5 Bytes JMP 003F0804
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ADVAPI32.dll!ChangeServiceConfigW 77E37001 5 Bytes JMP 003F0A08
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ADVAPI32.dll!ChangeServiceConfig2A 77E37101 5 Bytes JMP 003F0C0C
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ADVAPI32.dll!ChangeServiceConfig2W 77E37189 5 Bytes JMP 003F0E10
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ADVAPI32.dll!CreateServiceA 77E37211 5 Bytes JMP 003F01F8
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ADVAPI32.dll!CreateServiceW 77E373A9 5 Bytes JMP 003F03FC
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] ADVAPI32.dll!DeleteService 77E374B1 5 Bytes JMP 003F0600
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] USER32.dll!SetWindowsHookExW 7E42820F 5 Bytes JMP 00AA0804
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] USER32.dll!UnhookWindowsHookEx 7E42D5F3 5 Bytes JMP 00AA0A08
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] USER32.dll!SetWindowsHookExA 7E431211 5 Bytes JMP 00AA0600
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] USER32.dll!SetWinEventHook 7E4317F7 5 Bytes JMP 00AA01F8
.text C:\Documents and Settings\Vernon Burdette\My Documents\Downloads\gmer.exe[4088] USER32.dll!UnhookWinEvent 7E4318AC 5 Bytes JMP 00AA03FC
---- Registry - GMER 1.0.15 ----
Reg HKLM\SOFTWARE\Classes\CLSID\{91EC4B89-4AF2-1685-8B077627C8A43419}\{2EE609D8-52A7-5ABD-6D921F70AFC106D5}\{F0CB3253-4F19-C88D-A2C81B3BBC751916}
Reg HKLM\SOFTWARE\Classes\CLSID\{91EC4B89-4AF2-1685-8B077627C8A43419}\{2EE609D8-52A7-5ABD-6D921F70AFC106D5}\{F0CB3253-4F19-C88D-A2C81B3BBC751916}@1D1OWFM6WKF6TLM3S2BGKKUUDG1 0x01 0x00 0x01 0x00 ...
Reg HKLM\SOFTWARE\Classes\CLSID\{DAB5C844-BE4A-29F4-AD8FABA4C17947A0}\{6913C59A-116F-5212-1A8157F10917C9CC}\{8C3FE3F0-4F1D-5A94-937677A4B6D15CAE}
Reg HKLM\SOFTWARE\Classes\CLSID\{DAB5C844-BE4A-29F4-AD8FABA4C17947A0}\{6913C59A-116F-5212-1A8157F10917C9CC}\{8C3FE3F0-4F1D-5A94-937677A4B6D15CAE}@{3EE4C831-B7E0-4ed1-B9FC-EDC523C9612F}1 0x01 0x00 0x01 0x00 ...
---- EOF - GMER 1.0.15 ----
Edited by lady_jodie, 15 August 2011 - 06:38 PM.


 This topic is locked
This topic is locked


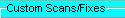


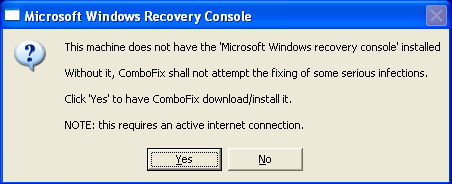
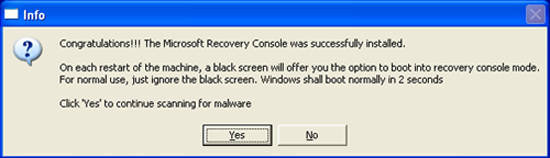












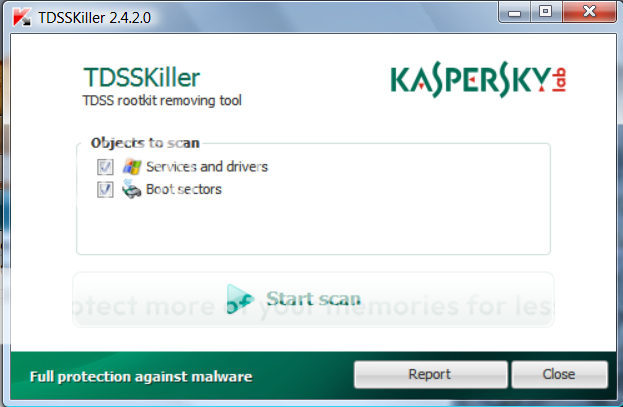

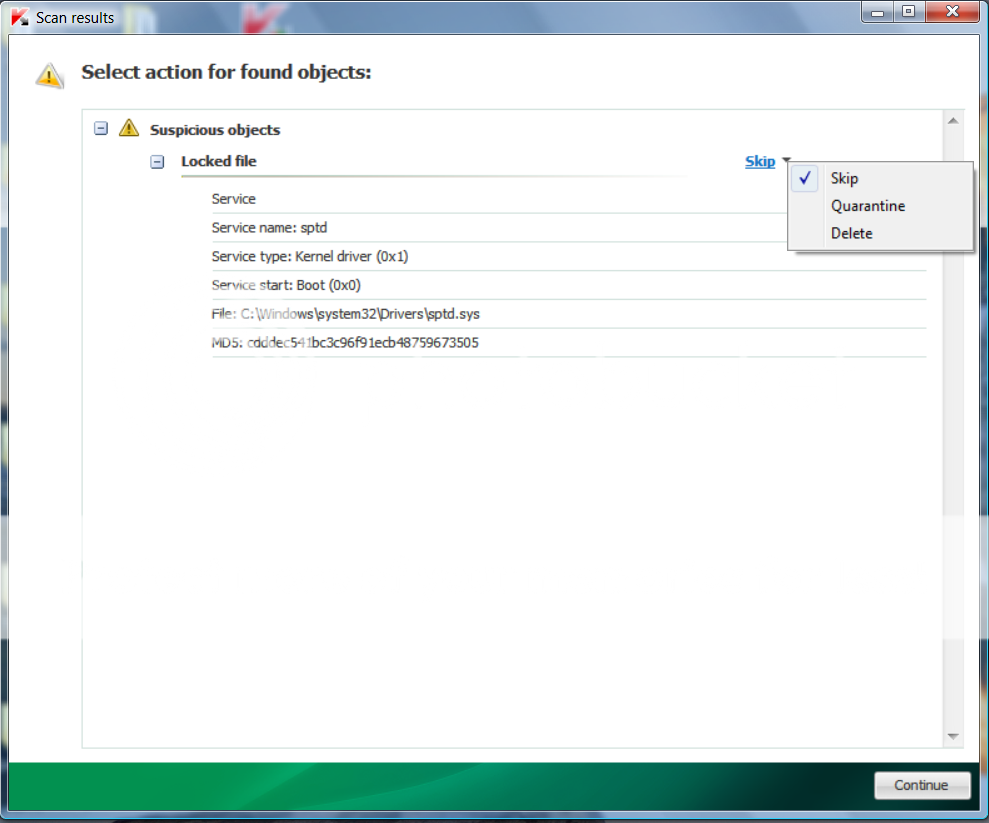












 Sign In
Sign In Create Account
Create Account

