- Download AntiZeroAccess to Desktop
- Double click on it to run it (If running Vista or Windows 7, right click on it and select "Run as an Administrator")
- Type y and press enter to run the scan
- Please post AntiZeroAccess_Log.txt contents in your next post. This file is saved in the same location as AntiZeroAccess program.
search engine redirects and virus scans won't run
Started by
dmills
, Sep 19 2011 11:05 AM
#16

 Posted 20 September 2011 - 02:56 PM
Posted 20 September 2011 - 02:56 PM

#17

 Posted 20 September 2011 - 03:05 PM
Posted 20 September 2011 - 03:05 PM

I ran AntiZeroAccess.
Webroot AntiZeroAccess 0.8 Log File
Execution time: 20/09/2011 - 16:03
Host operation System: Windows Xp X86 version 5.1.2600 Service Pack 3
16:03:18 - CheckSystem - Begin to check system...
16:03:18 - OpenRootDrive - Opening system root volume and physical drive....
16:03:18 - C Root Drive: Disk number: 0 Start sector: 0x00017886 Partition Size: 0x0ACAE347 sectors.
16:03:18 - PrevX Main driver extracted in "C:\WINDOWS\system32\drivers\ZeroAccess.sys".
16:03:19 - InstallAndStartDriver - Main driver was installed and now is running.
16:03:19 - CheckSystem - Warning! Disk class driver is INFECTED.
16:03:28 - StopAndRemoveDriver - AntiZeroAccess Driver is stopped and removed.
16:03:28 - StopAndRemoveDriver - File "ZeroAccess.sys" was deleted!
16:03:28 - Execution Ended!
Webroot AntiZeroAccess 0.8 Log File
Execution time: 20/09/2011 - 16:03
Host operation System: Windows Xp X86 version 5.1.2600 Service Pack 3
16:03:18 - CheckSystem - Begin to check system...
16:03:18 - OpenRootDrive - Opening system root volume and physical drive....
16:03:18 - C Root Drive: Disk number: 0 Start sector: 0x00017886 Partition Size: 0x0ACAE347 sectors.
16:03:18 - PrevX Main driver extracted in "C:\WINDOWS\system32\drivers\ZeroAccess.sys".
16:03:19 - InstallAndStartDriver - Main driver was installed and now is running.
16:03:19 - CheckSystem - Warning! Disk class driver is INFECTED.
16:03:28 - StopAndRemoveDriver - AntiZeroAccess Driver is stopped and removed.
16:03:28 - StopAndRemoveDriver - File "ZeroAccess.sys" was deleted!
16:03:28 - Execution Ended!
#18

 Posted 20 September 2011 - 03:15 PM
Posted 20 September 2011 - 03:15 PM

OK. Please reboot your system and then run TDSSKiller once again:
Please read carefully and follow these steps.
Please read carefully and follow these steps.
- Download TDSSKiller and save it to your Desktop.
- Extract its contents to your desktop.
- Once extracted, open the TDSSKiller folder and doubleclick on TDSSKiller.exe to run the application, then on Start Scan.
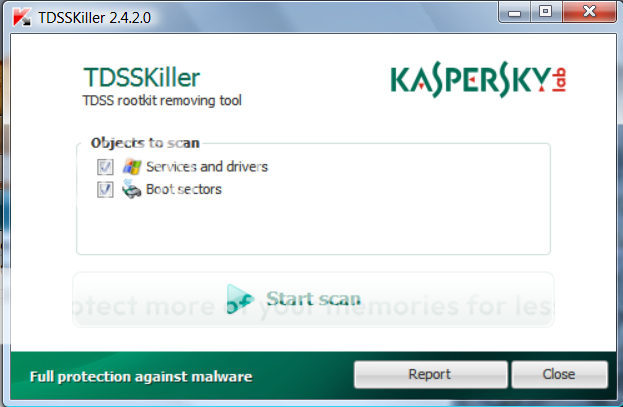
- If an infected file is detected, the default action will be Cure, click on Continue.

- If a suspicious file is detected, the default action will be Skip, click on Continue.

- It may ask you to reboot the computer to complete the process. Click on Reboot Now.

- If no reboot is require, click on Report. A log file should appear. Please copy and paste the contents of that file here.
- If a reboot is required, the report can also be found in your root directory, (usually C:\ folder) in the form of "TDSSKiller.[Version]_[Date]_[Time]_log.txt". Please copy and paste the contents of that file here.
#19

 Posted 20 September 2011 - 04:00 PM
Posted 20 September 2011 - 04:00 PM

I ran TDSSKiller. I rebooted and ran it again.
2011/09/20 16:55:56.0640 0872 TDSS rootkit removing tool 2.5.23.0 Sep 20 2011 08:53:10
2011/09/20 16:55:57.0125 0872 ================================================================================
2011/09/20 16:55:57.0125 0872 SystemInfo:
2011/09/20 16:55:57.0125 0872
2011/09/20 16:55:57.0125 0872 OS Version: 5.1.2600 ServicePack: 3.0
2011/09/20 16:55:57.0125 0872 Product type: Workstation
2011/09/20 16:55:57.0125 0872 ComputerName: D82M1C4
2011/09/20 16:55:57.0125 0872 UserName: David Mills
2011/09/20 16:55:57.0125 0872 Windows directory: C:\WINDOWS
2011/09/20 16:55:57.0125 0872 System windows directory: C:\WINDOWS
2011/09/20 16:55:57.0125 0872 Processor architecture: Intel x86
2011/09/20 16:55:57.0125 0872 Number of processors: 2
2011/09/20 16:55:57.0125 0872 Page size: 0x1000
2011/09/20 16:55:57.0125 0872 Boot type: Normal boot
2011/09/20 16:55:57.0125 0872 ================================================================================
2011/09/20 16:55:59.0312 0872 Initialize success
2011/09/20 16:56:12.0015 4072 ================================================================================
2011/09/20 16:56:12.0015 4072 Scan started
2011/09/20 16:56:12.0015 4072 Mode: Manual;
2011/09/20 16:56:12.0015 4072 ================================================================================
2011/09/20 16:56:13.0171 4072 abp480n5 (6abb91494fe6c59089b9336452ab2ea3) C:\WINDOWS\system32\DRIVERS\ABP480N5.SYS
2011/09/20 16:56:13.0281 4072 ACPI (8fd99680a539792a30e97944fdaecf17) C:\WINDOWS\system32\DRIVERS\ACPI.sys
2011/09/20 16:56:13.0312 4072 ACPIEC (9859c0f6936e723e4892d7141b1327d5) C:\WINDOWS\system32\drivers\ACPIEC.sys
2011/09/20 16:56:13.0390 4072 ADM8511 (b05f2367f62552a2de7e3c352b7b9885) C:\WINDOWS\system32\DRIVERS\ADM8511.SYS
2011/09/20 16:56:13.0515 4072 adpu160m (9a11864873da202c996558b2106b0bbc) C:\WINDOWS\system32\DRIVERS\adpu160m.sys
2011/09/20 16:56:13.0609 4072 aec (8bed39e3c35d6a489438b8141717a557) C:\WINDOWS\system32\drivers\aec.sys
2011/09/20 16:56:13.0718 4072 AFD (355556d9e580915118cd7ef736653a89) C:\WINDOWS\System32\drivers\afd.sys
2011/09/20 16:56:13.0765 4072 agp440 (08fd04aa961bdc77fb983f328334e3d7) C:\WINDOWS\system32\DRIVERS\agp440.sys
2011/09/20 16:56:13.0890 4072 agpCPQ (03a7e0922acfe1b07d5db2eeb0773063) C:\WINDOWS\system32\DRIVERS\agpCPQ.sys
2011/09/20 16:56:13.0937 4072 Aha154x (c23ea9b5f46c7f7910db3eab648ff013) C:\WINDOWS\system32\DRIVERS\aha154x.sys
2011/09/20 16:56:14.0000 4072 aic78u2 (19dd0fb48b0c18892f70e2e7d61a1529) C:\WINDOWS\system32\DRIVERS\aic78u2.sys
2011/09/20 16:56:14.0046 4072 aic78xx (b7fe594a7468aa0132deb03fb8e34326) C:\WINDOWS\system32\DRIVERS\aic78xx.sys
2011/09/20 16:56:14.0109 4072 AliIde (1140ab9938809700b46bb88e46d72a96) C:\WINDOWS\system32\DRIVERS\aliide.sys
2011/09/20 16:56:14.0171 4072 alim1541 (cb08aed0de2dd889a8a820cd8082d83c) C:\WINDOWS\system32\DRIVERS\alim1541.sys
2011/09/20 16:56:14.0296 4072 amdagp (95b4fb835e28aa1336ceeb07fd5b9398) C:\WINDOWS\system32\DRIVERS\amdagp.sys
2011/09/20 16:56:14.0359 4072 amsint (79f5add8d24bd6893f2903a3e2f3fad6) C:\WINDOWS\system32\DRIVERS\amsint.sys
2011/09/20 16:56:14.0453 4072 AngelUsb (b001ead648a3e8fa06af7c221a5c1a4e) C:\WINDOWS\system32\DRIVERS\AngelUsb.sys
2011/09/20 16:56:14.0562 4072 APPDRV (ec94e05b76d033b74394e7b2175103cf) C:\WINDOWS\SYSTEM32\DRIVERS\APPDRV.SYS
2011/09/20 16:56:14.0656 4072 Arp1394 (b5b8a80875c1dededa8b02765642c32f) C:\WINDOWS\system32\DRIVERS\arp1394.sys
2011/09/20 16:56:14.0765 4072 asc (62d318e9a0c8fc9b780008e724283707) C:\WINDOWS\system32\DRIVERS\asc.sys
2011/09/20 16:56:14.0828 4072 asc3350p (69eb0cc7714b32896ccbfd5edcbea447) C:\WINDOWS\system32\DRIVERS\asc3350p.sys
2011/09/20 16:56:14.0890 4072 asc3550 (5d8de112aa0254b907861e9e9c31d597) C:\WINDOWS\system32\DRIVERS\asc3550.sys
2011/09/20 16:56:14.0953 4072 AsyncMac (b153affac761e7f5fcfa822b9c4e97bc) C:\WINDOWS\system32\DRIVERS\asyncmac.sys
2011/09/20 16:56:15.0015 4072 atapi (9f3a2f5aa6875c72bf062c712cfa2674) C:\WINDOWS\system32\DRIVERS\atapi.sys
2011/09/20 16:56:15.0156 4072 ati2mtag (2573c08729dd52b7b4f18df1592e0b37) C:\WINDOWS\system32\DRIVERS\ati2mtag.sys
2011/09/20 16:56:15.0375 4072 Atmarpc (9916c1225104ba14794209cfa8012159) C:\WINDOWS\system32\DRIVERS\atmarpc.sys
2011/09/20 16:56:15.0453 4072 audstub (d9f724aa26c010a217c97606b160ed68) C:\WINDOWS\system32\DRIVERS\audstub.sys
2011/09/20 16:56:15.0546 4072 BCM43XX (48a376e100ba257cb9d761e38577904f) C:\WINDOWS\system32\DRIVERS\bcmwl5.sys
2011/09/20 16:56:15.0625 4072 bcm4sbxp (cd4646067cc7dcba1907fa0acf7e3966) C:\WINDOWS\system32\DRIVERS\bcm4sbxp.sys
2011/09/20 16:56:15.0718 4072 Beep (da1f27d85e0d1525f6621372e7b685e9) C:\WINDOWS\system32\drivers\Beep.sys
2011/09/20 16:56:15.0796 4072 Bridge (f934d1b230f84e1d19dd00ac5a7a83ed) C:\WINDOWS\system32\DRIVERS\bridge.sys
2011/09/20 16:56:15.0843 4072 BridgeMP (f934d1b230f84e1d19dd00ac5a7a83ed) C:\WINDOWS\system32\DRIVERS\bridge.sys
2011/09/20 16:56:15.0906 4072 btaudio (8893ae0b6b9b60e0521a60e8b2160216) C:\WINDOWS\system32\drivers\btaudio.sys
2011/09/20 16:56:16.0015 4072 BTDriver (fde318e3569f57264af74b7e431f60ae) C:\WINDOWS\system32\DRIVERS\btport.sys
2011/09/20 16:56:16.0171 4072 BTKRNL (9c3c8b9e2eda516eb44b51dab81dbd68) C:\WINDOWS\system32\DRIVERS\btkrnl.sys
2011/09/20 16:56:16.0328 4072 BTSERIAL (089f7526ff41c17b0a43896d0553d5a2) C:\WINDOWS\system32\drivers\btserial.sys
2011/09/20 16:56:16.0437 4072 BTWDNDIS (28531ab3183f498e58d93d585e6a6b70) C:\WINDOWS\system32\DRIVERS\btwdndis.sys
2011/09/20 16:56:16.0515 4072 btwhid (c5c0e21c67089f053b964e0a8b8adbac) C:\WINDOWS\system32\DRIVERS\btwhid.sys
2011/09/20 16:56:16.0593 4072 btwmodem (7d295223c172ab4d61dc256721b2f09e) C:\WINDOWS\system32\DRIVERS\btwmodem.sys
2011/09/20 16:56:16.0671 4072 BTWUSB (56c701580f2891952761362ba7594b3d) C:\WINDOWS\system32\Drivers\btwusb.sys
2011/09/20 16:56:16.0796 4072 BVRPMPR5 (51b327292408b5f3a42e295bce055859) C:\WINDOWS\system32\drivers\BVRPMPR5.SYS
2011/09/20 16:56:16.0921 4072 cbidf (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\DRIVERS\cbidf2k.sys
2011/09/20 16:56:16.0968 4072 cbidf2k (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\drivers\cbidf2k.sys
2011/09/20 16:56:17.0031 4072 CCDECODE (0be5aef125be881c4f854c554f2b025c) C:\WINDOWS\system32\DRIVERS\CCDECODE.sys
2011/09/20 16:56:17.0078 4072 cd20xrnt (f3ec03299634490e97bbce94cd2954c7) C:\WINDOWS\system32\DRIVERS\cd20xrnt.sys
2011/09/20 16:56:17.0140 4072 Cdaudio (c1b486a7658353d33a10cc15211a873b) C:\WINDOWS\system32\drivers\Cdaudio.sys
2011/09/20 16:56:17.0218 4072 Cdfs (c885b02847f5d2fd45a24e219ed93b32) C:\WINDOWS\system32\drivers\Cdfs.sys
2011/09/20 16:56:17.0312 4072 Cdrom (1f4260cc5b42272d71f79e570a27a4fe) C:\WINDOWS\system32\DRIVERS\cdrom.sys
2011/09/20 16:56:17.0390 4072 CmBatt (0f6c187d38d98f8df904589a5f94d411) C:\WINDOWS\system32\DRIVERS\CmBatt.sys
2011/09/20 16:56:17.0437 4072 CmdIde (e5dcb56c533014ecbc556a8357c929d5) C:\WINDOWS\system32\DRIVERS\cmdide.sys
2011/09/20 16:56:17.0484 4072 Compbatt (6e4c9f21f0fae8940661144f41b13203) C:\WINDOWS\system32\DRIVERS\compbatt.sys
2011/09/20 16:56:17.0578 4072 Cpqarray (3ee529119eed34cd212a215e8c40d4b6) C:\WINDOWS\system32\DRIVERS\cpqarray.sys
2011/09/20 16:56:17.0656 4072 ctsfm2k (8db84de3aab34a8b4c2f644eff41cd76) C:\WINDOWS\system32\DRIVERS\ctsfm2k.sys
2011/09/20 16:56:17.0734 4072 CTUSFSYN (4ee8822adb764edd28ce44e808097995) C:\WINDOWS\system32\drivers\ctusfsyn.sys
2011/09/20 16:56:17.0812 4072 dac2w2k (e550e7418984b65a78299d248f0a7f36) C:\WINDOWS\system32\DRIVERS\dac2w2k.sys
2011/09/20 16:56:17.0875 4072 dac960nt (683789caa3864eb46125ae86ff677d34) C:\WINDOWS\system32\DRIVERS\dac960nt.sys
2011/09/20 16:56:17.0953 4072 Disk (044452051f3e02e7963599fc8f4f3e25) C:\WINDOWS\system32\DRIVERS\disk.sys
2011/09/20 16:56:18.0031 4072 dmboot (d992fe1274bde0f84ad826acae022a41) C:\WINDOWS\system32\drivers\dmboot.sys
2011/09/20 16:56:18.0187 4072 dmio (7c824cf7bbde77d95c08005717a95f6f) C:\WINDOWS\system32\drivers\dmio.sys
2011/09/20 16:56:18.0265 4072 dmload (e9317282a63ca4d188c0df5e09c6ac5f) C:\WINDOWS\system32\drivers\dmload.sys
2011/09/20 16:56:18.0328 4072 DMusic (8a208dfcf89792a484e76c40e5f50b45) C:\WINDOWS\system32\drivers\DMusic.sys
2011/09/20 16:56:18.0390 4072 dpti2o (40f3b93b4e5b0126f2f5c0a7a5e22660) C:\WINDOWS\system32\DRIVERS\dpti2o.sys
2011/09/20 16:56:18.0437 4072 drmkaud (8f5fcff8e8848afac920905fbd9d33c8) C:\WINDOWS\system32\drivers\drmkaud.sys
2011/09/20 16:56:18.0484 4072 drvmcdb (96bc8f872f0270c10edc3931f1c03776) C:\WINDOWS\system32\drivers\drvmcdb.sys
2011/09/20 16:56:18.0546 4072 drvnddm (5afbec7a6ac61b211633dfdb1d9e0c89) C:\WINDOWS\system32\drivers\drvnddm.sys
2011/09/20 16:56:18.0718 4072 DSproct (2ac2372ffad9adc85672cc8e8ae14be9) C:\Program Files\Dell Support\GTAction\triggers\DSproct.sys
2011/09/20 16:56:18.0859 4072 E100B (3fca03cbca11269f973b70fa483c88ef) C:\WINDOWS\system32\DRIVERS\e100b325.sys
2011/09/20 16:56:18.0968 4072 EuMusDesignVirtualAudioCableWdm (0531fc85e96822d60d3e41f30f075fc2) C:\WINDOWS\system32\DRIVERS\PC2TVAudio.sys
2011/09/20 16:56:19.0046 4072 f08ea724 (8f2bb1827cac01aee6a16e30a1260199) C:\WINDOWS\614960880:259086555.exe
2011/09/20 16:56:20.0578 4072 Suspicious file (Hidden): C:\WINDOWS\614960880:259086555.exe. md5: 8f2bb1827cac01aee6a16e30a1260199
2011/09/20 16:56:20.0578 4072 f08ea724 - detected HiddenFile.Multi.Generic (1)
2011/09/20 16:56:20.0718 4072 Fastfat (38d332a6d56af32635675f132548343e) C:\WINDOWS\system32\drivers\Fastfat.sys
2011/09/20 16:56:20.0796 4072 Fdc (92cdd60b6730b9f50f6a1a0c1f8cdc81) C:\WINDOWS\system32\DRIVERS\fdc.sys
2011/09/20 16:56:20.0875 4072 FilterService (50104c5f1ee1e295781caf9521ca2e56) C:\WINDOWS\system32\DRIVERS\lvuvcflt.sys
2011/09/20 16:56:20.0937 4072 Fips (d45926117eb9fa946a6af572fbe1caa3) C:\WINDOWS\system32\drivers\Fips.sys
2011/09/20 16:56:21.0000 4072 Flpydisk (9d27e7b80bfcdf1cdd9b555862d5e7f0) C:\WINDOWS\system32\DRIVERS\flpydisk.sys
2011/09/20 16:56:21.0046 4072 FltMgr (b2cf4b0786f8212cb92ed2b50c6db6b0) C:\WINDOWS\system32\drivers\fltmgr.sys
2011/09/20 16:56:21.0203 4072 Fs_Rec (3e1e2bd4f39b0e2b7dc4f4d2bcc2779a) C:\WINDOWS\system32\drivers\Fs_Rec.sys
2011/09/20 16:56:21.0281 4072 Ftdisk (6ac26732762483366c3969c9e4d2259d) C:\WINDOWS\system32\DRIVERS\ftdisk.sys
2011/09/20 16:56:21.0359 4072 GEARAspiWDM (8182ff89c65e4d38b2de4bb0fb18564e) C:\WINDOWS\system32\DRIVERS\GEARAspiWDM.sys
2011/09/20 16:56:21.0437 4072 Gpc (0a02c63c8b144bd8c86b103dee7c86a2) C:\WINDOWS\system32\DRIVERS\msgpc.sys
2011/09/20 16:56:21.0531 4072 HDAudBus (573c7d0a32852b48f3058cfd8026f511) C:\WINDOWS\system32\DRIVERS\HDAudBus.sys
2011/09/20 16:56:21.0656 4072 HidUsb (ccf82c5ec8a7326c3066de870c06daf1) C:\WINDOWS\system32\DRIVERS\hidusb.sys
2011/09/20 16:56:21.0750 4072 hpn (b028377dea0546a5fcfba928a8aefae0) C:\WINDOWS\system32\DRIVERS\hpn.sys
2011/09/20 16:56:21.0859 4072 HPZid412 (d03d10f7ded688fecf50f8fbf1ea9b8a) C:\WINDOWS\system32\DRIVERS\HPZid412.sys
2011/09/20 16:56:21.0953 4072 HPZipr12 (89f41658929393487b6b7d13c8528ce3) C:\WINDOWS\system32\DRIVERS\HPZipr12.sys
2011/09/20 16:56:22.0031 4072 HPZius12 (abcb05ccdbf03000354b9553820e39f8) C:\WINDOWS\system32\DRIVERS\HPZius12.sys
2011/09/20 16:56:22.0218 4072 HSFHWAZL (1c8caa80e91fb71864e9426f9eed048d) C:\WINDOWS\system32\DRIVERS\HSFHWAZL.sys
2011/09/20 16:56:22.0328 4072 HSF_DPV (698204d9c2832e53633e53a30a53fc3d) C:\WINDOWS\system32\DRIVERS\HSF_DPV.sys
2011/09/20 16:56:22.0578 4072 HTTP (f80a415ef82cd06ffaf0d971528ead38) C:\WINDOWS\system32\Drivers\HTTP.sys
2011/09/20 16:56:22.0609 4072 i2omgmt (9368670bd426ebea5e8b18a62416ec28) C:\WINDOWS\system32\drivers\i2omgmt.sys
2011/09/20 16:56:22.0671 4072 i2omp (f10863bf1ccc290babd1a09188ae49e0) C:\WINDOWS\system32\DRIVERS\i2omp.sys
2011/09/20 16:56:22.0718 4072 i8042prt (4a0b06aa8943c1e332520f7440c0aa30) C:\WINDOWS\system32\DRIVERS\i8042prt.sys
2011/09/20 16:56:22.0796 4072 Imapi (083a052659f5310dd8b6a6cb05edcf8e) C:\WINDOWS\system32\DRIVERS\imapi.sys
2011/09/20 16:56:22.0875 4072 ini910u (4a40e045faee58631fd8d91afc620719) C:\WINDOWS\system32\DRIVERS\ini910u.sys
2011/09/20 16:56:23.0046 4072 IntelIde (b5466a9250342a7aa0cd1fba13420678) C:\WINDOWS\system32\DRIVERS\intelide.sys
2011/09/20 16:56:23.0109 4072 intelppm (8c953733d8f36eb2133f5bb58808b66b) C:\WINDOWS\system32\DRIVERS\intelppm.sys
2011/09/20 16:56:23.0140 4072 Ip6Fw (3bb22519a194418d5fec05d800a19ad0) C:\WINDOWS\system32\drivers\ip6fw.sys
2011/09/20 16:56:23.0203 4072 IpFilterDriver (731f22ba402ee4b62748adaf6363c182) C:\WINDOWS\system32\DRIVERS\ipfltdrv.sys
2011/09/20 16:56:23.0250 4072 IpInIp (b87ab476dcf76e72010632b5550955f5) C:\WINDOWS\system32\DRIVERS\ipinip.sys
2011/09/20 16:56:23.0312 4072 IpNat (cc748ea12c6effde940ee98098bf96bb) C:\WINDOWS\system32\DRIVERS\ipnat.sys
2011/09/20 16:56:23.0453 4072 IPSec (c3b55c9f04b8b9214b26659c56ec3e04) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2011/09/20 16:56:23.0484 4072 Suspicious file (Forged): C:\WINDOWS\system32\DRIVERS\ipsec.sys. Real md5: c3b55c9f04b8b9214b26659c56ec3e04, Fake md5: 23c74d75e36e7158768dd63d92789a91
2011/09/20 16:56:23.0484 4072 IPSec - detected Rootkit.Win32.ZAccess.e (0)
2011/09/20 16:56:23.0515 4072 IRENUM (c93c9ff7b04d772627a3646d89f7bf89) C:\WINDOWS\system32\DRIVERS\irenum.sys
2011/09/20 16:56:23.0578 4072 isapnp (05a299ec56e52649b1cf2fc52d20f2d7) C:\WINDOWS\system32\DRIVERS\isapnp.sys
2011/09/20 16:56:23.0718 4072 Kbdclass (463c1ec80cd17420a542b7f36a36f128) C:\WINDOWS\system32\DRIVERS\kbdclass.sys
2011/09/20 16:56:23.0765 4072 kbdhid (9ef487a186dea361aa06913a75b3fa99) C:\WINDOWS\system32\DRIVERS\kbdhid.sys
2011/09/20 16:56:23.0812 4072 kmixer (692bcf44383d056aed41b045a323d378) C:\WINDOWS\system32\drivers\kmixer.sys
2011/09/20 16:56:23.0843 4072 KSecDD (b467646c54cc746128904e1654c750c1) C:\WINDOWS\system32\drivers\KSecDD.sys
2011/09/20 16:56:23.0906 4072 LVPr2Mon (a6919138f29ae45e90e99fa94737e04c) C:\WINDOWS\system32\DRIVERS\LVPr2Mon.sys
2011/09/20 16:56:24.0078 4072 LVRS (b895839b8743e400d7c7dae156f74e7e) C:\WINDOWS\system32\DRIVERS\lvrs.sys
2011/09/20 16:56:24.0140 4072 LVUSBSta (23f8ef78bb9553e465a476f3cee5ca18) C:\WINDOWS\system32\drivers\LVUSBSta.sys
2011/09/20 16:56:24.0328 4072 LVUVC (8bc0d5f6e3898f465a94c6d03afb5a20) C:\WINDOWS\system32\DRIVERS\lvuvc.sys
2011/09/20 16:56:24.0812 4072 mdmxsdk (3c318b9cd391371bed62126581ee9961) C:\WINDOWS\system32\DRIVERS\mdmxsdk.sys
2011/09/20 16:56:24.0906 4072 MHNDRV (7f2f1d2815a6449d346fcccbc569fbd6) C:\WINDOWS\system32\DRIVERS\mhndrv.sys
2011/09/20 16:56:24.0953 4072 mnmdd (4ae068242760a1fb6e1a44bf4e16afa6) C:\WINDOWS\system32\drivers\mnmdd.sys
2011/09/20 16:56:25.0031 4072 Modem (dfcbad3cec1c5f964962ae10e0bcc8e1) C:\WINDOWS\system32\drivers\Modem.sys
2011/09/20 16:56:25.0125 4072 monfilt (9fa7207d1b1adead88ae8eed9cdbbaa5) C:\WINDOWS\system32\drivers\monfilt.sys
2011/09/20 16:56:25.0375 4072 Mouclass (35c9e97194c8cfb8430125f8dbc34d04) C:\WINDOWS\system32\DRIVERS\mouclass.sys
2011/09/20 16:56:25.0453 4072 mouhid (b1c303e17fb9d46e87a98e4ba6769685) C:\WINDOWS\system32\DRIVERS\mouhid.sys
2011/09/20 16:56:25.0515 4072 MountMgr (a80b9a0bad1b73637dbcbba7df72d3fd) C:\WINDOWS\system32\drivers\MountMgr.sys
2011/09/20 16:56:25.0578 4072 mraid35x (3f4bb95e5a44f3be34824e8e7caf0737) C:\WINDOWS\system32\DRIVERS\mraid35x.sys
2011/09/20 16:56:25.0640 4072 MRxDAV (11d42bb6206f33fbb3ba0288d3ef81bd) C:\WINDOWS\system32\DRIVERS\mrxdav.sys
2011/09/20 16:56:25.0734 4072 MRxSmb (7d304a5eb4344ebeeab53a2fe3ffb9f0) C:\WINDOWS\system32\DRIVERS\mrxsmb.sys
2011/09/20 16:56:25.0875 4072 Msfs (c941ea2454ba8350021d774daf0f1027) C:\WINDOWS\system32\drivers\Msfs.sys
2011/09/20 16:56:25.0937 4072 MSKSSRV (d1575e71568f4d9e14ca56b7b0453bf1) C:\WINDOWS\system32\drivers\MSKSSRV.sys
2011/09/20 16:56:25.0984 4072 MSPCLOCK (325bb26842fc7ccc1fcce2c457317f3e) C:\WINDOWS\system32\drivers\MSPCLOCK.sys
2011/09/20 16:56:26.0015 4072 MSPQM (bad59648ba099da4a17680b39730cb3d) C:\WINDOWS\system32\drivers\MSPQM.sys
2011/09/20 16:56:26.0078 4072 mssmbios (af5f4f3f14a8ea2c26de30f7a1e17136) C:\WINDOWS\system32\DRIVERS\mssmbios.sys
2011/09/20 16:56:26.0125 4072 MSTEE (e53736a9e30c45fa9e7b5eac55056d1d) C:\WINDOWS\system32\drivers\MSTEE.sys
2011/09/20 16:56:26.0203 4072 Mup (de6a75f5c270e756c5508d94b6cf68f5) C:\WINDOWS\system32\drivers\Mup.sys
2011/09/20 16:56:26.0328 4072 NABTSFEC (5b50f1b2a2ed47d560577b221da734db) C:\WINDOWS\system32\DRIVERS\NABTSFEC.sys
2011/09/20 16:56:26.0437 4072 NDIS (1df7f42665c94b825322fae71721130d) C:\WINDOWS\system32\drivers\NDIS.sys
2011/09/20 16:56:26.0515 4072 NdisIP (7ff1f1fd8609c149aa432f95a8163d97) C:\WINDOWS\system32\DRIVERS\NdisIP.sys
2011/09/20 16:56:26.0593 4072 NdisTapi (0109c4f3850dfbab279542515386ae22) C:\WINDOWS\system32\DRIVERS\ndistapi.sys
2011/09/20 16:56:26.0625 4072 Ndisuio (f927a4434c5028758a842943ef1a3849) C:\WINDOWS\system32\DRIVERS\ndisuio.sys
2011/09/20 16:56:26.0656 4072 NdisWan (edc1531a49c80614b2cfda43ca8659ab) C:\WINDOWS\system32\DRIVERS\ndiswan.sys
2011/09/20 16:56:26.0750 4072 NDProxy (9282bd12dfb069d3889eb3fcc1000a9b) C:\WINDOWS\system32\drivers\NDProxy.sys
2011/09/20 16:56:26.0890 4072 NetBIOS (5d81cf9a2f1a3a756b66cf684911cdf0) C:\WINDOWS\system32\DRIVERS\netbios.sys
2011/09/20 16:56:26.0953 4072 NetBT (74b2b2f5bea5e9a3dc021d685551bd3d) C:\WINDOWS\system32\DRIVERS\netbt.sys
2011/09/20 16:56:27.0031 4072 NIC1394 (e9e47cfb2d461fa0fc75b7a74c6383ea) C:\WINDOWS\system32\DRIVERS\nic1394.sys
2011/09/20 16:56:27.0046 4072 Npfs (3182d64ae053d6fb034f44b6def8034a) C:\WINDOWS\system32\drivers\Npfs.sys
2011/09/20 16:56:27.0093 4072 Ntfs (78a08dd6a8d65e697c18e1db01c5cdca) C:\WINDOWS\system32\drivers\Ntfs.sys
2011/09/20 16:56:27.0250 4072 Null (73c1e1f395918bc2c6dd67af7591a3ad) C:\WINDOWS\system32\drivers\Null.sys
2011/09/20 16:56:27.0359 4072 nv (2b298519edbfcf451d43e0f1e8f1006d) C:\WINDOWS\system32\DRIVERS\nv4_mini.sys
2011/09/20 16:56:27.0562 4072 NwlnkFlt (b305f3fad35083837ef46a0bbce2fc57) C:\WINDOWS\system32\DRIVERS\nwlnkflt.sys
2011/09/20 16:56:27.0625 4072 NwlnkFwd (c99b3415198d1aab7227f2c88fd664b9) C:\WINDOWS\system32\DRIVERS\nwlnkfwd.sys
2011/09/20 16:56:27.0703 4072 ohci1394 (ca33832df41afb202ee7aeb05145922f) C:\WINDOWS\system32\DRIVERS\ohci1394.sys
2011/09/20 16:56:27.0765 4072 omci (b17228142cec9b3c222239fd935a37ca) C:\WINDOWS\system32\DRIVERS\omci.sys
2011/09/20 16:56:27.0843 4072 ossrv (103a9b117a7d9903111955cdafe65ac6) C:\WINDOWS\system32\DRIVERS\ctoss2k.sys
2011/09/20 16:56:27.0968 4072 Parport (5575faf8f97ce5e713d108c2a58d7c7c) C:\WINDOWS\system32\DRIVERS\parport.sys
2011/09/20 16:56:28.0156 4072 PartMgr (beb3ba25197665d82ec7065b724171c6) C:\WINDOWS\system32\drivers\PartMgr.sys
2011/09/20 16:56:28.0218 4072 ParVdm (70e98b3fd8e963a6a46a2e6247e0bea1) C:\WINDOWS\system32\drivers\ParVdm.sys
2011/09/20 16:56:28.0296 4072 PCI (a219903ccf74233761d92bef471a07b1) C:\WINDOWS\system32\DRIVERS\pci.sys
2011/09/20 16:56:28.0375 4072 PCIIde (ccf5f451bb1a5a2a522a76e670000ff0) C:\WINDOWS\system32\DRIVERS\pciide.sys
2011/09/20 16:56:28.0421 4072 Pcmcia (9e89ef60e9ee05e3f2eef2da7397f1c1) C:\WINDOWS\system32\drivers\Pcmcia.sys
2011/09/20 16:56:28.0562 4072 perc2 (6c14b9c19ba84f73d3a86dba11133101) C:\WINDOWS\system32\DRIVERS\perc2.sys
2011/09/20 16:56:28.0703 4072 perc2hib (f50f7c27f131afe7beba13e14a3b9416) C:\WINDOWS\system32\DRIVERS\perc2hib.sys
2011/09/20 16:56:28.0781 4072 PfModNT (ede8241b75dadef090aadb6c81c8e1d7) C:\WINDOWS\system32\drivers\PfModNT.sys
2011/09/20 16:56:28.0906 4072 PptpMiniport (efeec01b1d3cf84f16ddd24d9d9d8f99) C:\WINDOWS\system32\DRIVERS\raspptp.sys
2011/09/20 16:56:28.0953 4072 PSched (09298ec810b07e5d582cb3a3f9255424) C:\WINDOWS\system32\DRIVERS\psched.sys
2011/09/20 16:56:29.0000 4072 Ptilink (80d317bd1c3dbc5d4fe7b1678c60cadd) C:\WINDOWS\system32\DRIVERS\ptilink.sys
2011/09/20 16:56:29.0046 4072 PxHelp20 (81088114178112618b1c414a65e50f7c) C:\WINDOWS\system32\Drivers\PxHelp20.sys
2011/09/20 16:56:29.0125 4072 ql1080 (0a63fb54039eb5662433caba3b26dba7) C:\WINDOWS\system32\DRIVERS\ql1080.sys
2011/09/20 16:56:29.0187 4072 Ql10wnt (6503449e1d43a0ff0201ad5cb1b8c706) C:\WINDOWS\system32\DRIVERS\ql10wnt.sys
2011/09/20 16:56:29.0359 4072 ql12160 (156ed0ef20c15114ca097a34a30d8a01) C:\WINDOWS\system32\DRIVERS\ql12160.sys
2011/09/20 16:56:29.0421 4072 ql1240 (70f016bebde6d29e864c1230a07cc5e6) C:\WINDOWS\system32\DRIVERS\ql1240.sys
2011/09/20 16:56:29.0484 4072 ql1280 (907f0aeea6bc451011611e732bd31fcf) C:\WINDOWS\system32\DRIVERS\ql1280.sys
2011/09/20 16:56:29.0562 4072 RasAcd (fe0d99d6f31e4fad8159f690d68ded9c) C:\WINDOWS\system32\DRIVERS\rasacd.sys
2011/09/20 16:56:29.0640 4072 Rasl2tp (11b4a627bc9614b885c4969bfa5ff8a6) C:\WINDOWS\system32\DRIVERS\rasl2tp.sys
2011/09/20 16:56:29.0687 4072 RasPppoe (5bc962f2654137c9909c3d4603587dee) C:\WINDOWS\system32\DRIVERS\raspppoe.sys
2011/09/20 16:56:29.0734 4072 Raspti (fdbb1d60066fcfbb7452fd8f9829b242) C:\WINDOWS\system32\DRIVERS\raspti.sys
2011/09/20 16:56:29.0781 4072 Rdbss (7ad224ad1a1437fe28d89cf22b17780a) C:\WINDOWS\system32\DRIVERS\rdbss.sys
2011/09/20 16:56:29.0843 4072 RDPCDD (4912d5b403614ce99c28420f75353332) C:\WINDOWS\system32\DRIVERS\RDPCDD.sys
2011/09/20 16:56:29.0890 4072 rdpdr (15cabd0f7c00c47c70124907916af3f1) C:\WINDOWS\system32\DRIVERS\rdpdr.sys
2011/09/20 16:56:30.0062 4072 RDPWD (fc105dd312ed64eb66bff111e8ec6eac) C:\WINDOWS\system32\drivers\RDPWD.sys
2011/09/20 16:56:30.0093 4072 redbook (f828dd7e1419b6653894a8f97a0094c5) C:\WINDOWS\system32\DRIVERS\redbook.sys
2011/09/20 16:56:30.0171 4072 rimmptsk (24ed7af20651f9fa1f249482e7c1f165) C:\WINDOWS\system32\DRIVERS\rimmptsk.sys
2011/09/20 16:56:30.0203 4072 rimsptsk (1bdba2d2d402415a78a4ba766dfe0f7b) C:\WINDOWS\system32\DRIVERS\rimsptsk.sys
2011/09/20 16:56:30.0234 4072 rismxdp (f774ecd11a064f0debb2d4395418153c) C:\WINDOWS\system32\DRIVERS\rixdptsk.sys
2011/09/20 16:56:30.0328 4072 sdbus (8d04819a3ce51b9eb47e5689b44d43c4) C:\WINDOWS\system32\DRIVERS\sdbus.sys
2011/09/20 16:56:30.0390 4072 Secdrv (90a3935d05b494a5a39d37e71f09a677) C:\WINDOWS\system32\DRIVERS\secdrv.sys
2011/09/20 16:56:30.0468 4072 serenum (0f29512ccd6bead730039fb4bd2c85ce) C:\WINDOWS\system32\DRIVERS\serenum.sys
2011/09/20 16:56:30.0593 4072 Serial (cca207a8896d4c6a0c9ce29a4ae411a7) C:\WINDOWS\system32\DRIVERS\serial.sys
2011/09/20 16:56:30.0671 4072 sffdisk (0fa803c64df0914b41f807ea276bf2a6) C:\WINDOWS\system32\DRIVERS\sffdisk.sys
2011/09/20 16:56:30.0718 4072 sffp_sd (c17c331e435ed8737525c86a7557b3ac) C:\WINDOWS\system32\DRIVERS\sffp_sd.sys
2011/09/20 16:56:30.0781 4072 Sfloppy (8e6b8c671615d126fdc553d1e2de5562) C:\WINDOWS\system32\drivers\Sfloppy.sys
2011/09/20 16:56:30.0875 4072 sisagp (6b33d0ebd30db32e27d1d78fe946a754) C:\WINDOWS\system32\DRIVERS\sisagp.sys
2011/09/20 16:56:30.0968 4072 SLIP (866d538ebe33709a5c9f5c62b73b7d14) C:\WINDOWS\system32\DRIVERS\SLIP.sys
2011/09/20 16:56:31.0093 4072 Sockblkd (02ab5ac03a1e66c8e8ed764ff8effc68) C:\Program Files\Extegrity\Exam4\Sockblkd.sys
2011/09/20 16:56:31.0218 4072 Sparrow (83c0f71f86d3bdaf915685f3d568b20e) C:\WINDOWS\system32\DRIVERS\sparrow.sys
2011/09/20 16:56:31.0328 4072 splitter (ab8b92451ecb048a4d1de7c3ffcb4a9f) C:\WINDOWS\system32\drivers\splitter.sys
2011/09/20 16:56:31.0375 4072 sr (76bb022c2fb6902fd5bdd4f78fc13a5d) C:\WINDOWS\system32\DRIVERS\sr.sys
2011/09/20 16:56:31.0453 4072 Srv (47ddfc2f003f7f9f0592c6874962a2e7) C:\WINDOWS\system32\DRIVERS\srv.sys
2011/09/20 16:56:31.0484 4072 sscdbhk5 (98625722ad52b40305e74aaa83c93086) C:\WINDOWS\system32\drivers\sscdbhk5.sys
2011/09/20 16:56:31.0531 4072 ssrtln (d79412e3942c8a257253487536d5a994) C:\WINDOWS\system32\drivers\ssrtln.sys
2011/09/20 16:56:31.0656 4072 STHDA (3ad78e22210d3fbd9f76de84a8df19b5) C:\WINDOWS\system32\drivers\sthda.sys
2011/09/20 16:56:31.0890 4072 StillCam (a9573045baa16eab9b1085205b82f1ed) C:\WINDOWS\system32\DRIVERS\serscan.sys
2011/09/20 16:56:31.0968 4072 streamip (77813007ba6265c4b6098187e6ed79d2) C:\WINDOWS\system32\DRIVERS\StreamIP.sys
2011/09/20 16:56:32.0046 4072 swenum (3941d127aef12e93addf6fe6ee027e0f) C:\WINDOWS\system32\DRIVERS\swenum.sys
2011/09/20 16:56:32.0078 4072 swmidi (8ce882bcc6cf8a62f2b2323d95cb3d01) C:\WINDOWS\system32\drivers\swmidi.sys
2011/09/20 16:56:32.0171 4072 symc810 (1ff3217614018630d0a6758630fc698c) C:\WINDOWS\system32\DRIVERS\symc810.sys
2011/09/20 16:56:32.0218 4072 symc8xx (070e001d95cf725186ef8b20335f933c) C:\WINDOWS\system32\DRIVERS\symc8xx.sys
2011/09/20 16:56:32.0343 4072 sym_hi (80ac1c4abbe2df3b738bf15517a51f2c) C:\WINDOWS\system32\DRIVERS\sym_hi.sys
2011/09/20 16:56:32.0406 4072 sym_u3 (bf4fab949a382a8e105f46ebb4937058) C:\WINDOWS\system32\DRIVERS\sym_u3.sys
2011/09/20 16:56:32.0500 4072 SynTP (fa2daa32bed908023272a0f77d625dae) C:\WINDOWS\system32\DRIVERS\SynTP.sys
2011/09/20 16:56:32.0593 4072 sysaudio (8b83f3ed0f1688b4958f77cd6d2bf290) C:\WINDOWS\system32\drivers\sysaudio.sys
2011/09/20 16:56:32.0687 4072 Tcpip (9aefa14bd6b182d61e3119fa5f436d3d) C:\WINDOWS\system32\DRIVERS\tcpip.sys
2011/09/20 16:56:32.0812 4072 TDPIPE (6471a66807f5e104e4885f5b67349397) C:\WINDOWS\system32\drivers\TDPIPE.sys
2011/09/20 16:56:32.0859 4072 TDTCP (c56b6d0402371cf3700eb322ef3aaf61) C:\WINDOWS\system32\drivers\TDTCP.sys
2011/09/20 16:56:32.0921 4072 TermDD (88155247177638048422893737429d9e) C:\WINDOWS\system32\DRIVERS\termdd.sys
2011/09/20 16:56:33.0000 4072 tfsnboio (d0177776e11b0b3f272eebd262a69661) C:\WINDOWS\system32\dla\tfsnboio.sys
2011/09/20 16:56:33.0078 4072 tfsncofs (599804bc938b8305a5422319774da871) C:\WINDOWS\system32\dla\tfsncofs.sys
2011/09/20 16:56:33.0125 4072 tfsndrct (a1902c00adc11c4d83f8e3ed947a6a32) C:\WINDOWS\system32\dla\tfsndrct.sys
2011/09/20 16:56:33.0187 4072 tfsndres (d8ddb3f2b1bef15cff6728d89c042c61) C:\WINDOWS\system32\dla\tfsndres.sys
2011/09/20 16:56:33.0250 4072 tfsnifs (c4f2dea75300971cdaee311007de138d) C:\WINDOWS\system32\dla\tfsnifs.sys
2011/09/20 16:56:33.0453 4072 tfsnopio (272925be0ea919f08286d2ee6f102b0f) C:\WINDOWS\system32\dla\tfsnopio.sys
2011/09/20 16:56:33.0500 4072 tfsnpool (7b7d955e5cebc2fb88b03ef875d52a2f) C:\WINDOWS\system32\dla\tfsnpool.sys
2011/09/20 16:56:33.0531 4072 tfsnudf (e3d01263109d800c1967c12c10a0b018) C:\WINDOWS\system32\dla\tfsnudf.sys
2011/09/20 16:56:33.0593 4072 tfsnudfa (b9e9c377906e3a65bc74598fff7f7458) C:\WINDOWS\system32\dla\tfsnudfa.sys
2011/09/20 16:56:33.0687 4072 tmcfw (3929c6784db38788d76a88d9c4043dee) C:\WINDOWS\system32\DRIVERS\TM_CFW.sys
2011/09/20 16:56:34.0046 4072 tmpreflt (0c89809f1df614bd42093a446b222a32) C:\WINDOWS\system32\DRIVERS\tmpreflt.sys
2011/09/20 16:56:34.0140 4072 tmtdi (264ea39fdebd0b5e9d49d79923ed91ad) C:\WINDOWS\system32\DRIVERS\tmtdi.sys
2011/09/20 16:56:34.0218 4072 tmxpflt (3d473e97ff805dab903aa66f08286c90) C:\WINDOWS\system32\drivers\TmXPFlt.sys
2011/09/20 16:56:34.0546 4072 TosIde (f2790f6af01321b172aa62f8e1e187d9) C:\WINDOWS\system32\DRIVERS\toside.sys
2011/09/20 16:56:34.0703 4072 Udfs (5787b80c2e3c5e2f56c2a233d91fa2c9) C:\WINDOWS\system32\drivers\Udfs.sys
2011/09/20 16:56:34.0984 4072 ultra (1b698a51cd528d8da4ffaed66dfc51b9) C:\WINDOWS\system32\DRIVERS\ultra.sys
2011/09/20 16:56:35.0140 4072 Update (402ddc88356b1bac0ee3dd1580c76a31) C:\WINDOWS\system32\DRIVERS\update.sys
2011/09/20 16:56:35.0296 4072 USBAAPL (5c2bdc152bbab34f36473deaf7713f22) C:\WINDOWS\system32\Drivers\usbaapl.sys
2011/09/20 16:56:35.0359 4072 usbaudio (e919708db44ed8543a7c017953148330) C:\WINDOWS\system32\drivers\usbaudio.sys
2011/09/20 16:56:35.0437 4072 usbccgp (173f317ce0db8e21322e71b7e60a27e8) C:\WINDOWS\system32\DRIVERS\usbccgp.sys
2011/09/20 16:56:35.0625 4072 usbehci (65dcf09d0e37d4c6b11b5b0b76d470a7) C:\WINDOWS\system32\DRIVERS\usbehci.sys
2011/09/20 16:56:35.0687 4072 usbhub (1ab3cdde553b6e064d2e754efe20285c) C:\WINDOWS\system32\DRIVERS\usbhub.sys
2011/09/20 16:56:35.0765 4072 usbprint (a717c8721046828520c9edf31288fc00) C:\WINDOWS\system32\DRIVERS\usbprint.sys
2011/09/20 16:56:35.0875 4072 usbscan (a0b8cf9deb1184fbdd20784a58fa75d4) C:\WINDOWS\system32\DRIVERS\usbscan.sys
2011/09/20 16:56:36.0187 4072 USBSTOR (a32426d9b14a089eaa1d922e0c5801a9) C:\WINDOWS\system32\DRIVERS\USBSTOR.SYS
2011/09/20 16:56:36.0328 4072 usbuhci (26496f9dee2d787fc3e61ad54821ffe6) C:\WINDOWS\system32\DRIVERS\usbuhci.sys
2011/09/20 16:56:36.0406 4072 usbvideo (63bbfca7f390f4c49ed4b96bfb1633e0) C:\WINDOWS\system32\Drivers\usbvideo.sys
2011/09/20 16:56:36.0593 4072 usb_rndisx (b6cc50279d6cd28e090a5d33244adc9a) C:\WINDOWS\system32\DRIVERS\usb8023x.sys
2011/09/20 16:56:36.0656 4072 VgaSave (0d3a8fafceacd8b7625cd549757a7df1) C:\WINDOWS\System32\drivers\vga.sys
2011/09/20 16:56:36.0718 4072 viaagp (754292ce5848b3738281b4f3607eaef4) C:\WINDOWS\system32\DRIVERS\viaagp.sys
2011/09/20 16:56:36.0781 4072 ViaIde (3b3efcda263b8ac14fdf9cbdd0791b2e) C:\WINDOWS\system32\DRIVERS\viaide.sys
2011/09/20 16:56:36.0828 4072 VolSnap (4c8fcb5cc53aab716d810740fe59d025) C:\WINDOWS\system32\drivers\VolSnap.sys
2011/09/20 16:56:36.0968 4072 vsapint (50e1ea1dd3ea74919d7a1c5d6c9c0b56) C:\WINDOWS\system32\DRIVERS\vsapint.sys
2011/09/20 16:56:37.0125 4072 Wanarp (e20b95baedb550f32dd489265c1da1f6) C:\WINDOWS\system32\DRIVERS\wanarp.sys
2011/09/20 16:56:37.0250 4072 WDC_SAM (d6efaf429fd30c5df613d220e344cce7) C:\WINDOWS\system32\DRIVERS\wdcsam.sys
2011/09/20 16:56:37.0312 4072 wdmaud (6768acf64b18196494413695f0c3a00f) C:\WINDOWS\system32\drivers\wdmaud.sys
2011/09/20 16:56:37.0437 4072 winachsf (74cf3f2e4e40c4a2e18d39d6300a5c24) C:\WINDOWS\system32\DRIVERS\HSF_CNXT.sys
2011/09/20 16:56:37.0734 4072 WmiAcpi (c42584fd66ce9e17403aebca199f7bdb) C:\WINDOWS\system32\DRIVERS\wmiacpi.sys
2011/09/20 16:56:37.0781 4072 WpdUsb (bbaeaca1ffa3c86361cf0998474f6c3a) C:\WINDOWS\system32\Drivers\wpdusb.sys
2011/09/20 16:56:37.0843 4072 WSTCODEC (c98b39829c2bbd34e454150633c62c78) C:\WINDOWS\system32\DRIVERS\WSTCODEC.SYS
2011/09/20 16:56:37.0890 4072 MBR (0x1B8) (5cb90281d1a59b251f6603134774eec3) \Device\Harddisk0\DR0
2011/09/20 16:56:37.0906 4072 MBR (0x1B8) (8f558eb6672622401da993e1e865c861) \Device\Harddisk1\DR5
2011/09/20 16:56:37.0921 4072 Boot (0x1200) (01b2009c09ccf404384a3b6b2db466a9) \Device\Harddisk0\DR0\Partition0
2011/09/20 16:56:37.0921 4072 Boot (0x1200) (4a40ea518c7320400832be752e44629b) \Device\Harddisk1\DR5\Partition0
2011/09/20 16:56:37.0937 4072 ================================================================================
2011/09/20 16:56:37.0937 4072 Scan finished
2011/09/20 16:56:37.0937 4072 ================================================================================
2011/09/20 16:56:37.0937 5788 Detected object count: 2
2011/09/20 16:56:37.0937 5788 Actual detected object count: 2
2011/09/20 16:56:45.0546 5788 HiddenFile.Multi.Generic(f08ea724) - User select action: Skip
2011/09/20 16:56:45.0718 5788 IPSec (c3b55c9f04b8b9214b26659c56ec3e04) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2011/09/20 16:56:45.0718 5788 Suspicious file (Forged): C:\WINDOWS\system32\DRIVERS\ipsec.sys. Real md5: c3b55c9f04b8b9214b26659c56ec3e04, Fake md5: 23c74d75e36e7158768dd63d92789a91
2011/09/20 16:56:46.0078 5788 Backup copy found, using it..
2011/09/20 16:56:46.0109 5788 C:\WINDOWS\system32\DRIVERS\ipsec.sys - will be cured after reboot
2011/09/20 16:56:46.0109 5788 Rootkit.Win32.ZAccess.e(IPSec) - User select action: Cure
2011/09/20 16:55:56.0640 0872 TDSS rootkit removing tool 2.5.23.0 Sep 20 2011 08:53:10
2011/09/20 16:55:57.0125 0872 ================================================================================
2011/09/20 16:55:57.0125 0872 SystemInfo:
2011/09/20 16:55:57.0125 0872
2011/09/20 16:55:57.0125 0872 OS Version: 5.1.2600 ServicePack: 3.0
2011/09/20 16:55:57.0125 0872 Product type: Workstation
2011/09/20 16:55:57.0125 0872 ComputerName: D82M1C4
2011/09/20 16:55:57.0125 0872 UserName: David Mills
2011/09/20 16:55:57.0125 0872 Windows directory: C:\WINDOWS
2011/09/20 16:55:57.0125 0872 System windows directory: C:\WINDOWS
2011/09/20 16:55:57.0125 0872 Processor architecture: Intel x86
2011/09/20 16:55:57.0125 0872 Number of processors: 2
2011/09/20 16:55:57.0125 0872 Page size: 0x1000
2011/09/20 16:55:57.0125 0872 Boot type: Normal boot
2011/09/20 16:55:57.0125 0872 ================================================================================
2011/09/20 16:55:59.0312 0872 Initialize success
2011/09/20 16:56:12.0015 4072 ================================================================================
2011/09/20 16:56:12.0015 4072 Scan started
2011/09/20 16:56:12.0015 4072 Mode: Manual;
2011/09/20 16:56:12.0015 4072 ================================================================================
2011/09/20 16:56:13.0171 4072 abp480n5 (6abb91494fe6c59089b9336452ab2ea3) C:\WINDOWS\system32\DRIVERS\ABP480N5.SYS
2011/09/20 16:56:13.0281 4072 ACPI (8fd99680a539792a30e97944fdaecf17) C:\WINDOWS\system32\DRIVERS\ACPI.sys
2011/09/20 16:56:13.0312 4072 ACPIEC (9859c0f6936e723e4892d7141b1327d5) C:\WINDOWS\system32\drivers\ACPIEC.sys
2011/09/20 16:56:13.0390 4072 ADM8511 (b05f2367f62552a2de7e3c352b7b9885) C:\WINDOWS\system32\DRIVERS\ADM8511.SYS
2011/09/20 16:56:13.0515 4072 adpu160m (9a11864873da202c996558b2106b0bbc) C:\WINDOWS\system32\DRIVERS\adpu160m.sys
2011/09/20 16:56:13.0609 4072 aec (8bed39e3c35d6a489438b8141717a557) C:\WINDOWS\system32\drivers\aec.sys
2011/09/20 16:56:13.0718 4072 AFD (355556d9e580915118cd7ef736653a89) C:\WINDOWS\System32\drivers\afd.sys
2011/09/20 16:56:13.0765 4072 agp440 (08fd04aa961bdc77fb983f328334e3d7) C:\WINDOWS\system32\DRIVERS\agp440.sys
2011/09/20 16:56:13.0890 4072 agpCPQ (03a7e0922acfe1b07d5db2eeb0773063) C:\WINDOWS\system32\DRIVERS\agpCPQ.sys
2011/09/20 16:56:13.0937 4072 Aha154x (c23ea9b5f46c7f7910db3eab648ff013) C:\WINDOWS\system32\DRIVERS\aha154x.sys
2011/09/20 16:56:14.0000 4072 aic78u2 (19dd0fb48b0c18892f70e2e7d61a1529) C:\WINDOWS\system32\DRIVERS\aic78u2.sys
2011/09/20 16:56:14.0046 4072 aic78xx (b7fe594a7468aa0132deb03fb8e34326) C:\WINDOWS\system32\DRIVERS\aic78xx.sys
2011/09/20 16:56:14.0109 4072 AliIde (1140ab9938809700b46bb88e46d72a96) C:\WINDOWS\system32\DRIVERS\aliide.sys
2011/09/20 16:56:14.0171 4072 alim1541 (cb08aed0de2dd889a8a820cd8082d83c) C:\WINDOWS\system32\DRIVERS\alim1541.sys
2011/09/20 16:56:14.0296 4072 amdagp (95b4fb835e28aa1336ceeb07fd5b9398) C:\WINDOWS\system32\DRIVERS\amdagp.sys
2011/09/20 16:56:14.0359 4072 amsint (79f5add8d24bd6893f2903a3e2f3fad6) C:\WINDOWS\system32\DRIVERS\amsint.sys
2011/09/20 16:56:14.0453 4072 AngelUsb (b001ead648a3e8fa06af7c221a5c1a4e) C:\WINDOWS\system32\DRIVERS\AngelUsb.sys
2011/09/20 16:56:14.0562 4072 APPDRV (ec94e05b76d033b74394e7b2175103cf) C:\WINDOWS\SYSTEM32\DRIVERS\APPDRV.SYS
2011/09/20 16:56:14.0656 4072 Arp1394 (b5b8a80875c1dededa8b02765642c32f) C:\WINDOWS\system32\DRIVERS\arp1394.sys
2011/09/20 16:56:14.0765 4072 asc (62d318e9a0c8fc9b780008e724283707) C:\WINDOWS\system32\DRIVERS\asc.sys
2011/09/20 16:56:14.0828 4072 asc3350p (69eb0cc7714b32896ccbfd5edcbea447) C:\WINDOWS\system32\DRIVERS\asc3350p.sys
2011/09/20 16:56:14.0890 4072 asc3550 (5d8de112aa0254b907861e9e9c31d597) C:\WINDOWS\system32\DRIVERS\asc3550.sys
2011/09/20 16:56:14.0953 4072 AsyncMac (b153affac761e7f5fcfa822b9c4e97bc) C:\WINDOWS\system32\DRIVERS\asyncmac.sys
2011/09/20 16:56:15.0015 4072 atapi (9f3a2f5aa6875c72bf062c712cfa2674) C:\WINDOWS\system32\DRIVERS\atapi.sys
2011/09/20 16:56:15.0156 4072 ati2mtag (2573c08729dd52b7b4f18df1592e0b37) C:\WINDOWS\system32\DRIVERS\ati2mtag.sys
2011/09/20 16:56:15.0375 4072 Atmarpc (9916c1225104ba14794209cfa8012159) C:\WINDOWS\system32\DRIVERS\atmarpc.sys
2011/09/20 16:56:15.0453 4072 audstub (d9f724aa26c010a217c97606b160ed68) C:\WINDOWS\system32\DRIVERS\audstub.sys
2011/09/20 16:56:15.0546 4072 BCM43XX (48a376e100ba257cb9d761e38577904f) C:\WINDOWS\system32\DRIVERS\bcmwl5.sys
2011/09/20 16:56:15.0625 4072 bcm4sbxp (cd4646067cc7dcba1907fa0acf7e3966) C:\WINDOWS\system32\DRIVERS\bcm4sbxp.sys
2011/09/20 16:56:15.0718 4072 Beep (da1f27d85e0d1525f6621372e7b685e9) C:\WINDOWS\system32\drivers\Beep.sys
2011/09/20 16:56:15.0796 4072 Bridge (f934d1b230f84e1d19dd00ac5a7a83ed) C:\WINDOWS\system32\DRIVERS\bridge.sys
2011/09/20 16:56:15.0843 4072 BridgeMP (f934d1b230f84e1d19dd00ac5a7a83ed) C:\WINDOWS\system32\DRIVERS\bridge.sys
2011/09/20 16:56:15.0906 4072 btaudio (8893ae0b6b9b60e0521a60e8b2160216) C:\WINDOWS\system32\drivers\btaudio.sys
2011/09/20 16:56:16.0015 4072 BTDriver (fde318e3569f57264af74b7e431f60ae) C:\WINDOWS\system32\DRIVERS\btport.sys
2011/09/20 16:56:16.0171 4072 BTKRNL (9c3c8b9e2eda516eb44b51dab81dbd68) C:\WINDOWS\system32\DRIVERS\btkrnl.sys
2011/09/20 16:56:16.0328 4072 BTSERIAL (089f7526ff41c17b0a43896d0553d5a2) C:\WINDOWS\system32\drivers\btserial.sys
2011/09/20 16:56:16.0437 4072 BTWDNDIS (28531ab3183f498e58d93d585e6a6b70) C:\WINDOWS\system32\DRIVERS\btwdndis.sys
2011/09/20 16:56:16.0515 4072 btwhid (c5c0e21c67089f053b964e0a8b8adbac) C:\WINDOWS\system32\DRIVERS\btwhid.sys
2011/09/20 16:56:16.0593 4072 btwmodem (7d295223c172ab4d61dc256721b2f09e) C:\WINDOWS\system32\DRIVERS\btwmodem.sys
2011/09/20 16:56:16.0671 4072 BTWUSB (56c701580f2891952761362ba7594b3d) C:\WINDOWS\system32\Drivers\btwusb.sys
2011/09/20 16:56:16.0796 4072 BVRPMPR5 (51b327292408b5f3a42e295bce055859) C:\WINDOWS\system32\drivers\BVRPMPR5.SYS
2011/09/20 16:56:16.0921 4072 cbidf (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\DRIVERS\cbidf2k.sys
2011/09/20 16:56:16.0968 4072 cbidf2k (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\drivers\cbidf2k.sys
2011/09/20 16:56:17.0031 4072 CCDECODE (0be5aef125be881c4f854c554f2b025c) C:\WINDOWS\system32\DRIVERS\CCDECODE.sys
2011/09/20 16:56:17.0078 4072 cd20xrnt (f3ec03299634490e97bbce94cd2954c7) C:\WINDOWS\system32\DRIVERS\cd20xrnt.sys
2011/09/20 16:56:17.0140 4072 Cdaudio (c1b486a7658353d33a10cc15211a873b) C:\WINDOWS\system32\drivers\Cdaudio.sys
2011/09/20 16:56:17.0218 4072 Cdfs (c885b02847f5d2fd45a24e219ed93b32) C:\WINDOWS\system32\drivers\Cdfs.sys
2011/09/20 16:56:17.0312 4072 Cdrom (1f4260cc5b42272d71f79e570a27a4fe) C:\WINDOWS\system32\DRIVERS\cdrom.sys
2011/09/20 16:56:17.0390 4072 CmBatt (0f6c187d38d98f8df904589a5f94d411) C:\WINDOWS\system32\DRIVERS\CmBatt.sys
2011/09/20 16:56:17.0437 4072 CmdIde (e5dcb56c533014ecbc556a8357c929d5) C:\WINDOWS\system32\DRIVERS\cmdide.sys
2011/09/20 16:56:17.0484 4072 Compbatt (6e4c9f21f0fae8940661144f41b13203) C:\WINDOWS\system32\DRIVERS\compbatt.sys
2011/09/20 16:56:17.0578 4072 Cpqarray (3ee529119eed34cd212a215e8c40d4b6) C:\WINDOWS\system32\DRIVERS\cpqarray.sys
2011/09/20 16:56:17.0656 4072 ctsfm2k (8db84de3aab34a8b4c2f644eff41cd76) C:\WINDOWS\system32\DRIVERS\ctsfm2k.sys
2011/09/20 16:56:17.0734 4072 CTUSFSYN (4ee8822adb764edd28ce44e808097995) C:\WINDOWS\system32\drivers\ctusfsyn.sys
2011/09/20 16:56:17.0812 4072 dac2w2k (e550e7418984b65a78299d248f0a7f36) C:\WINDOWS\system32\DRIVERS\dac2w2k.sys
2011/09/20 16:56:17.0875 4072 dac960nt (683789caa3864eb46125ae86ff677d34) C:\WINDOWS\system32\DRIVERS\dac960nt.sys
2011/09/20 16:56:17.0953 4072 Disk (044452051f3e02e7963599fc8f4f3e25) C:\WINDOWS\system32\DRIVERS\disk.sys
2011/09/20 16:56:18.0031 4072 dmboot (d992fe1274bde0f84ad826acae022a41) C:\WINDOWS\system32\drivers\dmboot.sys
2011/09/20 16:56:18.0187 4072 dmio (7c824cf7bbde77d95c08005717a95f6f) C:\WINDOWS\system32\drivers\dmio.sys
2011/09/20 16:56:18.0265 4072 dmload (e9317282a63ca4d188c0df5e09c6ac5f) C:\WINDOWS\system32\drivers\dmload.sys
2011/09/20 16:56:18.0328 4072 DMusic (8a208dfcf89792a484e76c40e5f50b45) C:\WINDOWS\system32\drivers\DMusic.sys
2011/09/20 16:56:18.0390 4072 dpti2o (40f3b93b4e5b0126f2f5c0a7a5e22660) C:\WINDOWS\system32\DRIVERS\dpti2o.sys
2011/09/20 16:56:18.0437 4072 drmkaud (8f5fcff8e8848afac920905fbd9d33c8) C:\WINDOWS\system32\drivers\drmkaud.sys
2011/09/20 16:56:18.0484 4072 drvmcdb (96bc8f872f0270c10edc3931f1c03776) C:\WINDOWS\system32\drivers\drvmcdb.sys
2011/09/20 16:56:18.0546 4072 drvnddm (5afbec7a6ac61b211633dfdb1d9e0c89) C:\WINDOWS\system32\drivers\drvnddm.sys
2011/09/20 16:56:18.0718 4072 DSproct (2ac2372ffad9adc85672cc8e8ae14be9) C:\Program Files\Dell Support\GTAction\triggers\DSproct.sys
2011/09/20 16:56:18.0859 4072 E100B (3fca03cbca11269f973b70fa483c88ef) C:\WINDOWS\system32\DRIVERS\e100b325.sys
2011/09/20 16:56:18.0968 4072 EuMusDesignVirtualAudioCableWdm (0531fc85e96822d60d3e41f30f075fc2) C:\WINDOWS\system32\DRIVERS\PC2TVAudio.sys
2011/09/20 16:56:19.0046 4072 f08ea724 (8f2bb1827cac01aee6a16e30a1260199) C:\WINDOWS\614960880:259086555.exe
2011/09/20 16:56:20.0578 4072 Suspicious file (Hidden): C:\WINDOWS\614960880:259086555.exe. md5: 8f2bb1827cac01aee6a16e30a1260199
2011/09/20 16:56:20.0578 4072 f08ea724 - detected HiddenFile.Multi.Generic (1)
2011/09/20 16:56:20.0718 4072 Fastfat (38d332a6d56af32635675f132548343e) C:\WINDOWS\system32\drivers\Fastfat.sys
2011/09/20 16:56:20.0796 4072 Fdc (92cdd60b6730b9f50f6a1a0c1f8cdc81) C:\WINDOWS\system32\DRIVERS\fdc.sys
2011/09/20 16:56:20.0875 4072 FilterService (50104c5f1ee1e295781caf9521ca2e56) C:\WINDOWS\system32\DRIVERS\lvuvcflt.sys
2011/09/20 16:56:20.0937 4072 Fips (d45926117eb9fa946a6af572fbe1caa3) C:\WINDOWS\system32\drivers\Fips.sys
2011/09/20 16:56:21.0000 4072 Flpydisk (9d27e7b80bfcdf1cdd9b555862d5e7f0) C:\WINDOWS\system32\DRIVERS\flpydisk.sys
2011/09/20 16:56:21.0046 4072 FltMgr (b2cf4b0786f8212cb92ed2b50c6db6b0) C:\WINDOWS\system32\drivers\fltmgr.sys
2011/09/20 16:56:21.0203 4072 Fs_Rec (3e1e2bd4f39b0e2b7dc4f4d2bcc2779a) C:\WINDOWS\system32\drivers\Fs_Rec.sys
2011/09/20 16:56:21.0281 4072 Ftdisk (6ac26732762483366c3969c9e4d2259d) C:\WINDOWS\system32\DRIVERS\ftdisk.sys
2011/09/20 16:56:21.0359 4072 GEARAspiWDM (8182ff89c65e4d38b2de4bb0fb18564e) C:\WINDOWS\system32\DRIVERS\GEARAspiWDM.sys
2011/09/20 16:56:21.0437 4072 Gpc (0a02c63c8b144bd8c86b103dee7c86a2) C:\WINDOWS\system32\DRIVERS\msgpc.sys
2011/09/20 16:56:21.0531 4072 HDAudBus (573c7d0a32852b48f3058cfd8026f511) C:\WINDOWS\system32\DRIVERS\HDAudBus.sys
2011/09/20 16:56:21.0656 4072 HidUsb (ccf82c5ec8a7326c3066de870c06daf1) C:\WINDOWS\system32\DRIVERS\hidusb.sys
2011/09/20 16:56:21.0750 4072 hpn (b028377dea0546a5fcfba928a8aefae0) C:\WINDOWS\system32\DRIVERS\hpn.sys
2011/09/20 16:56:21.0859 4072 HPZid412 (d03d10f7ded688fecf50f8fbf1ea9b8a) C:\WINDOWS\system32\DRIVERS\HPZid412.sys
2011/09/20 16:56:21.0953 4072 HPZipr12 (89f41658929393487b6b7d13c8528ce3) C:\WINDOWS\system32\DRIVERS\HPZipr12.sys
2011/09/20 16:56:22.0031 4072 HPZius12 (abcb05ccdbf03000354b9553820e39f8) C:\WINDOWS\system32\DRIVERS\HPZius12.sys
2011/09/20 16:56:22.0218 4072 HSFHWAZL (1c8caa80e91fb71864e9426f9eed048d) C:\WINDOWS\system32\DRIVERS\HSFHWAZL.sys
2011/09/20 16:56:22.0328 4072 HSF_DPV (698204d9c2832e53633e53a30a53fc3d) C:\WINDOWS\system32\DRIVERS\HSF_DPV.sys
2011/09/20 16:56:22.0578 4072 HTTP (f80a415ef82cd06ffaf0d971528ead38) C:\WINDOWS\system32\Drivers\HTTP.sys
2011/09/20 16:56:22.0609 4072 i2omgmt (9368670bd426ebea5e8b18a62416ec28) C:\WINDOWS\system32\drivers\i2omgmt.sys
2011/09/20 16:56:22.0671 4072 i2omp (f10863bf1ccc290babd1a09188ae49e0) C:\WINDOWS\system32\DRIVERS\i2omp.sys
2011/09/20 16:56:22.0718 4072 i8042prt (4a0b06aa8943c1e332520f7440c0aa30) C:\WINDOWS\system32\DRIVERS\i8042prt.sys
2011/09/20 16:56:22.0796 4072 Imapi (083a052659f5310dd8b6a6cb05edcf8e) C:\WINDOWS\system32\DRIVERS\imapi.sys
2011/09/20 16:56:22.0875 4072 ini910u (4a40e045faee58631fd8d91afc620719) C:\WINDOWS\system32\DRIVERS\ini910u.sys
2011/09/20 16:56:23.0046 4072 IntelIde (b5466a9250342a7aa0cd1fba13420678) C:\WINDOWS\system32\DRIVERS\intelide.sys
2011/09/20 16:56:23.0109 4072 intelppm (8c953733d8f36eb2133f5bb58808b66b) C:\WINDOWS\system32\DRIVERS\intelppm.sys
2011/09/20 16:56:23.0140 4072 Ip6Fw (3bb22519a194418d5fec05d800a19ad0) C:\WINDOWS\system32\drivers\ip6fw.sys
2011/09/20 16:56:23.0203 4072 IpFilterDriver (731f22ba402ee4b62748adaf6363c182) C:\WINDOWS\system32\DRIVERS\ipfltdrv.sys
2011/09/20 16:56:23.0250 4072 IpInIp (b87ab476dcf76e72010632b5550955f5) C:\WINDOWS\system32\DRIVERS\ipinip.sys
2011/09/20 16:56:23.0312 4072 IpNat (cc748ea12c6effde940ee98098bf96bb) C:\WINDOWS\system32\DRIVERS\ipnat.sys
2011/09/20 16:56:23.0453 4072 IPSec (c3b55c9f04b8b9214b26659c56ec3e04) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2011/09/20 16:56:23.0484 4072 Suspicious file (Forged): C:\WINDOWS\system32\DRIVERS\ipsec.sys. Real md5: c3b55c9f04b8b9214b26659c56ec3e04, Fake md5: 23c74d75e36e7158768dd63d92789a91
2011/09/20 16:56:23.0484 4072 IPSec - detected Rootkit.Win32.ZAccess.e (0)
2011/09/20 16:56:23.0515 4072 IRENUM (c93c9ff7b04d772627a3646d89f7bf89) C:\WINDOWS\system32\DRIVERS\irenum.sys
2011/09/20 16:56:23.0578 4072 isapnp (05a299ec56e52649b1cf2fc52d20f2d7) C:\WINDOWS\system32\DRIVERS\isapnp.sys
2011/09/20 16:56:23.0718 4072 Kbdclass (463c1ec80cd17420a542b7f36a36f128) C:\WINDOWS\system32\DRIVERS\kbdclass.sys
2011/09/20 16:56:23.0765 4072 kbdhid (9ef487a186dea361aa06913a75b3fa99) C:\WINDOWS\system32\DRIVERS\kbdhid.sys
2011/09/20 16:56:23.0812 4072 kmixer (692bcf44383d056aed41b045a323d378) C:\WINDOWS\system32\drivers\kmixer.sys
2011/09/20 16:56:23.0843 4072 KSecDD (b467646c54cc746128904e1654c750c1) C:\WINDOWS\system32\drivers\KSecDD.sys
2011/09/20 16:56:23.0906 4072 LVPr2Mon (a6919138f29ae45e90e99fa94737e04c) C:\WINDOWS\system32\DRIVERS\LVPr2Mon.sys
2011/09/20 16:56:24.0078 4072 LVRS (b895839b8743e400d7c7dae156f74e7e) C:\WINDOWS\system32\DRIVERS\lvrs.sys
2011/09/20 16:56:24.0140 4072 LVUSBSta (23f8ef78bb9553e465a476f3cee5ca18) C:\WINDOWS\system32\drivers\LVUSBSta.sys
2011/09/20 16:56:24.0328 4072 LVUVC (8bc0d5f6e3898f465a94c6d03afb5a20) C:\WINDOWS\system32\DRIVERS\lvuvc.sys
2011/09/20 16:56:24.0812 4072 mdmxsdk (3c318b9cd391371bed62126581ee9961) C:\WINDOWS\system32\DRIVERS\mdmxsdk.sys
2011/09/20 16:56:24.0906 4072 MHNDRV (7f2f1d2815a6449d346fcccbc569fbd6) C:\WINDOWS\system32\DRIVERS\mhndrv.sys
2011/09/20 16:56:24.0953 4072 mnmdd (4ae068242760a1fb6e1a44bf4e16afa6) C:\WINDOWS\system32\drivers\mnmdd.sys
2011/09/20 16:56:25.0031 4072 Modem (dfcbad3cec1c5f964962ae10e0bcc8e1) C:\WINDOWS\system32\drivers\Modem.sys
2011/09/20 16:56:25.0125 4072 monfilt (9fa7207d1b1adead88ae8eed9cdbbaa5) C:\WINDOWS\system32\drivers\monfilt.sys
2011/09/20 16:56:25.0375 4072 Mouclass (35c9e97194c8cfb8430125f8dbc34d04) C:\WINDOWS\system32\DRIVERS\mouclass.sys
2011/09/20 16:56:25.0453 4072 mouhid (b1c303e17fb9d46e87a98e4ba6769685) C:\WINDOWS\system32\DRIVERS\mouhid.sys
2011/09/20 16:56:25.0515 4072 MountMgr (a80b9a0bad1b73637dbcbba7df72d3fd) C:\WINDOWS\system32\drivers\MountMgr.sys
2011/09/20 16:56:25.0578 4072 mraid35x (3f4bb95e5a44f3be34824e8e7caf0737) C:\WINDOWS\system32\DRIVERS\mraid35x.sys
2011/09/20 16:56:25.0640 4072 MRxDAV (11d42bb6206f33fbb3ba0288d3ef81bd) C:\WINDOWS\system32\DRIVERS\mrxdav.sys
2011/09/20 16:56:25.0734 4072 MRxSmb (7d304a5eb4344ebeeab53a2fe3ffb9f0) C:\WINDOWS\system32\DRIVERS\mrxsmb.sys
2011/09/20 16:56:25.0875 4072 Msfs (c941ea2454ba8350021d774daf0f1027) C:\WINDOWS\system32\drivers\Msfs.sys
2011/09/20 16:56:25.0937 4072 MSKSSRV (d1575e71568f4d9e14ca56b7b0453bf1) C:\WINDOWS\system32\drivers\MSKSSRV.sys
2011/09/20 16:56:25.0984 4072 MSPCLOCK (325bb26842fc7ccc1fcce2c457317f3e) C:\WINDOWS\system32\drivers\MSPCLOCK.sys
2011/09/20 16:56:26.0015 4072 MSPQM (bad59648ba099da4a17680b39730cb3d) C:\WINDOWS\system32\drivers\MSPQM.sys
2011/09/20 16:56:26.0078 4072 mssmbios (af5f4f3f14a8ea2c26de30f7a1e17136) C:\WINDOWS\system32\DRIVERS\mssmbios.sys
2011/09/20 16:56:26.0125 4072 MSTEE (e53736a9e30c45fa9e7b5eac55056d1d) C:\WINDOWS\system32\drivers\MSTEE.sys
2011/09/20 16:56:26.0203 4072 Mup (de6a75f5c270e756c5508d94b6cf68f5) C:\WINDOWS\system32\drivers\Mup.sys
2011/09/20 16:56:26.0328 4072 NABTSFEC (5b50f1b2a2ed47d560577b221da734db) C:\WINDOWS\system32\DRIVERS\NABTSFEC.sys
2011/09/20 16:56:26.0437 4072 NDIS (1df7f42665c94b825322fae71721130d) C:\WINDOWS\system32\drivers\NDIS.sys
2011/09/20 16:56:26.0515 4072 NdisIP (7ff1f1fd8609c149aa432f95a8163d97) C:\WINDOWS\system32\DRIVERS\NdisIP.sys
2011/09/20 16:56:26.0593 4072 NdisTapi (0109c4f3850dfbab279542515386ae22) C:\WINDOWS\system32\DRIVERS\ndistapi.sys
2011/09/20 16:56:26.0625 4072 Ndisuio (f927a4434c5028758a842943ef1a3849) C:\WINDOWS\system32\DRIVERS\ndisuio.sys
2011/09/20 16:56:26.0656 4072 NdisWan (edc1531a49c80614b2cfda43ca8659ab) C:\WINDOWS\system32\DRIVERS\ndiswan.sys
2011/09/20 16:56:26.0750 4072 NDProxy (9282bd12dfb069d3889eb3fcc1000a9b) C:\WINDOWS\system32\drivers\NDProxy.sys
2011/09/20 16:56:26.0890 4072 NetBIOS (5d81cf9a2f1a3a756b66cf684911cdf0) C:\WINDOWS\system32\DRIVERS\netbios.sys
2011/09/20 16:56:26.0953 4072 NetBT (74b2b2f5bea5e9a3dc021d685551bd3d) C:\WINDOWS\system32\DRIVERS\netbt.sys
2011/09/20 16:56:27.0031 4072 NIC1394 (e9e47cfb2d461fa0fc75b7a74c6383ea) C:\WINDOWS\system32\DRIVERS\nic1394.sys
2011/09/20 16:56:27.0046 4072 Npfs (3182d64ae053d6fb034f44b6def8034a) C:\WINDOWS\system32\drivers\Npfs.sys
2011/09/20 16:56:27.0093 4072 Ntfs (78a08dd6a8d65e697c18e1db01c5cdca) C:\WINDOWS\system32\drivers\Ntfs.sys
2011/09/20 16:56:27.0250 4072 Null (73c1e1f395918bc2c6dd67af7591a3ad) C:\WINDOWS\system32\drivers\Null.sys
2011/09/20 16:56:27.0359 4072 nv (2b298519edbfcf451d43e0f1e8f1006d) C:\WINDOWS\system32\DRIVERS\nv4_mini.sys
2011/09/20 16:56:27.0562 4072 NwlnkFlt (b305f3fad35083837ef46a0bbce2fc57) C:\WINDOWS\system32\DRIVERS\nwlnkflt.sys
2011/09/20 16:56:27.0625 4072 NwlnkFwd (c99b3415198d1aab7227f2c88fd664b9) C:\WINDOWS\system32\DRIVERS\nwlnkfwd.sys
2011/09/20 16:56:27.0703 4072 ohci1394 (ca33832df41afb202ee7aeb05145922f) C:\WINDOWS\system32\DRIVERS\ohci1394.sys
2011/09/20 16:56:27.0765 4072 omci (b17228142cec9b3c222239fd935a37ca) C:\WINDOWS\system32\DRIVERS\omci.sys
2011/09/20 16:56:27.0843 4072 ossrv (103a9b117a7d9903111955cdafe65ac6) C:\WINDOWS\system32\DRIVERS\ctoss2k.sys
2011/09/20 16:56:27.0968 4072 Parport (5575faf8f97ce5e713d108c2a58d7c7c) C:\WINDOWS\system32\DRIVERS\parport.sys
2011/09/20 16:56:28.0156 4072 PartMgr (beb3ba25197665d82ec7065b724171c6) C:\WINDOWS\system32\drivers\PartMgr.sys
2011/09/20 16:56:28.0218 4072 ParVdm (70e98b3fd8e963a6a46a2e6247e0bea1) C:\WINDOWS\system32\drivers\ParVdm.sys
2011/09/20 16:56:28.0296 4072 PCI (a219903ccf74233761d92bef471a07b1) C:\WINDOWS\system32\DRIVERS\pci.sys
2011/09/20 16:56:28.0375 4072 PCIIde (ccf5f451bb1a5a2a522a76e670000ff0) C:\WINDOWS\system32\DRIVERS\pciide.sys
2011/09/20 16:56:28.0421 4072 Pcmcia (9e89ef60e9ee05e3f2eef2da7397f1c1) C:\WINDOWS\system32\drivers\Pcmcia.sys
2011/09/20 16:56:28.0562 4072 perc2 (6c14b9c19ba84f73d3a86dba11133101) C:\WINDOWS\system32\DRIVERS\perc2.sys
2011/09/20 16:56:28.0703 4072 perc2hib (f50f7c27f131afe7beba13e14a3b9416) C:\WINDOWS\system32\DRIVERS\perc2hib.sys
2011/09/20 16:56:28.0781 4072 PfModNT (ede8241b75dadef090aadb6c81c8e1d7) C:\WINDOWS\system32\drivers\PfModNT.sys
2011/09/20 16:56:28.0906 4072 PptpMiniport (efeec01b1d3cf84f16ddd24d9d9d8f99) C:\WINDOWS\system32\DRIVERS\raspptp.sys
2011/09/20 16:56:28.0953 4072 PSched (09298ec810b07e5d582cb3a3f9255424) C:\WINDOWS\system32\DRIVERS\psched.sys
2011/09/20 16:56:29.0000 4072 Ptilink (80d317bd1c3dbc5d4fe7b1678c60cadd) C:\WINDOWS\system32\DRIVERS\ptilink.sys
2011/09/20 16:56:29.0046 4072 PxHelp20 (81088114178112618b1c414a65e50f7c) C:\WINDOWS\system32\Drivers\PxHelp20.sys
2011/09/20 16:56:29.0125 4072 ql1080 (0a63fb54039eb5662433caba3b26dba7) C:\WINDOWS\system32\DRIVERS\ql1080.sys
2011/09/20 16:56:29.0187 4072 Ql10wnt (6503449e1d43a0ff0201ad5cb1b8c706) C:\WINDOWS\system32\DRIVERS\ql10wnt.sys
2011/09/20 16:56:29.0359 4072 ql12160 (156ed0ef20c15114ca097a34a30d8a01) C:\WINDOWS\system32\DRIVERS\ql12160.sys
2011/09/20 16:56:29.0421 4072 ql1240 (70f016bebde6d29e864c1230a07cc5e6) C:\WINDOWS\system32\DRIVERS\ql1240.sys
2011/09/20 16:56:29.0484 4072 ql1280 (907f0aeea6bc451011611e732bd31fcf) C:\WINDOWS\system32\DRIVERS\ql1280.sys
2011/09/20 16:56:29.0562 4072 RasAcd (fe0d99d6f31e4fad8159f690d68ded9c) C:\WINDOWS\system32\DRIVERS\rasacd.sys
2011/09/20 16:56:29.0640 4072 Rasl2tp (11b4a627bc9614b885c4969bfa5ff8a6) C:\WINDOWS\system32\DRIVERS\rasl2tp.sys
2011/09/20 16:56:29.0687 4072 RasPppoe (5bc962f2654137c9909c3d4603587dee) C:\WINDOWS\system32\DRIVERS\raspppoe.sys
2011/09/20 16:56:29.0734 4072 Raspti (fdbb1d60066fcfbb7452fd8f9829b242) C:\WINDOWS\system32\DRIVERS\raspti.sys
2011/09/20 16:56:29.0781 4072 Rdbss (7ad224ad1a1437fe28d89cf22b17780a) C:\WINDOWS\system32\DRIVERS\rdbss.sys
2011/09/20 16:56:29.0843 4072 RDPCDD (4912d5b403614ce99c28420f75353332) C:\WINDOWS\system32\DRIVERS\RDPCDD.sys
2011/09/20 16:56:29.0890 4072 rdpdr (15cabd0f7c00c47c70124907916af3f1) C:\WINDOWS\system32\DRIVERS\rdpdr.sys
2011/09/20 16:56:30.0062 4072 RDPWD (fc105dd312ed64eb66bff111e8ec6eac) C:\WINDOWS\system32\drivers\RDPWD.sys
2011/09/20 16:56:30.0093 4072 redbook (f828dd7e1419b6653894a8f97a0094c5) C:\WINDOWS\system32\DRIVERS\redbook.sys
2011/09/20 16:56:30.0171 4072 rimmptsk (24ed7af20651f9fa1f249482e7c1f165) C:\WINDOWS\system32\DRIVERS\rimmptsk.sys
2011/09/20 16:56:30.0203 4072 rimsptsk (1bdba2d2d402415a78a4ba766dfe0f7b) C:\WINDOWS\system32\DRIVERS\rimsptsk.sys
2011/09/20 16:56:30.0234 4072 rismxdp (f774ecd11a064f0debb2d4395418153c) C:\WINDOWS\system32\DRIVERS\rixdptsk.sys
2011/09/20 16:56:30.0328 4072 sdbus (8d04819a3ce51b9eb47e5689b44d43c4) C:\WINDOWS\system32\DRIVERS\sdbus.sys
2011/09/20 16:56:30.0390 4072 Secdrv (90a3935d05b494a5a39d37e71f09a677) C:\WINDOWS\system32\DRIVERS\secdrv.sys
2011/09/20 16:56:30.0468 4072 serenum (0f29512ccd6bead730039fb4bd2c85ce) C:\WINDOWS\system32\DRIVERS\serenum.sys
2011/09/20 16:56:30.0593 4072 Serial (cca207a8896d4c6a0c9ce29a4ae411a7) C:\WINDOWS\system32\DRIVERS\serial.sys
2011/09/20 16:56:30.0671 4072 sffdisk (0fa803c64df0914b41f807ea276bf2a6) C:\WINDOWS\system32\DRIVERS\sffdisk.sys
2011/09/20 16:56:30.0718 4072 sffp_sd (c17c331e435ed8737525c86a7557b3ac) C:\WINDOWS\system32\DRIVERS\sffp_sd.sys
2011/09/20 16:56:30.0781 4072 Sfloppy (8e6b8c671615d126fdc553d1e2de5562) C:\WINDOWS\system32\drivers\Sfloppy.sys
2011/09/20 16:56:30.0875 4072 sisagp (6b33d0ebd30db32e27d1d78fe946a754) C:\WINDOWS\system32\DRIVERS\sisagp.sys
2011/09/20 16:56:30.0968 4072 SLIP (866d538ebe33709a5c9f5c62b73b7d14) C:\WINDOWS\system32\DRIVERS\SLIP.sys
2011/09/20 16:56:31.0093 4072 Sockblkd (02ab5ac03a1e66c8e8ed764ff8effc68) C:\Program Files\Extegrity\Exam4\Sockblkd.sys
2011/09/20 16:56:31.0218 4072 Sparrow (83c0f71f86d3bdaf915685f3d568b20e) C:\WINDOWS\system32\DRIVERS\sparrow.sys
2011/09/20 16:56:31.0328 4072 splitter (ab8b92451ecb048a4d1de7c3ffcb4a9f) C:\WINDOWS\system32\drivers\splitter.sys
2011/09/20 16:56:31.0375 4072 sr (76bb022c2fb6902fd5bdd4f78fc13a5d) C:\WINDOWS\system32\DRIVERS\sr.sys
2011/09/20 16:56:31.0453 4072 Srv (47ddfc2f003f7f9f0592c6874962a2e7) C:\WINDOWS\system32\DRIVERS\srv.sys
2011/09/20 16:56:31.0484 4072 sscdbhk5 (98625722ad52b40305e74aaa83c93086) C:\WINDOWS\system32\drivers\sscdbhk5.sys
2011/09/20 16:56:31.0531 4072 ssrtln (d79412e3942c8a257253487536d5a994) C:\WINDOWS\system32\drivers\ssrtln.sys
2011/09/20 16:56:31.0656 4072 STHDA (3ad78e22210d3fbd9f76de84a8df19b5) C:\WINDOWS\system32\drivers\sthda.sys
2011/09/20 16:56:31.0890 4072 StillCam (a9573045baa16eab9b1085205b82f1ed) C:\WINDOWS\system32\DRIVERS\serscan.sys
2011/09/20 16:56:31.0968 4072 streamip (77813007ba6265c4b6098187e6ed79d2) C:\WINDOWS\system32\DRIVERS\StreamIP.sys
2011/09/20 16:56:32.0046 4072 swenum (3941d127aef12e93addf6fe6ee027e0f) C:\WINDOWS\system32\DRIVERS\swenum.sys
2011/09/20 16:56:32.0078 4072 swmidi (8ce882bcc6cf8a62f2b2323d95cb3d01) C:\WINDOWS\system32\drivers\swmidi.sys
2011/09/20 16:56:32.0171 4072 symc810 (1ff3217614018630d0a6758630fc698c) C:\WINDOWS\system32\DRIVERS\symc810.sys
2011/09/20 16:56:32.0218 4072 symc8xx (070e001d95cf725186ef8b20335f933c) C:\WINDOWS\system32\DRIVERS\symc8xx.sys
2011/09/20 16:56:32.0343 4072 sym_hi (80ac1c4abbe2df3b738bf15517a51f2c) C:\WINDOWS\system32\DRIVERS\sym_hi.sys
2011/09/20 16:56:32.0406 4072 sym_u3 (bf4fab949a382a8e105f46ebb4937058) C:\WINDOWS\system32\DRIVERS\sym_u3.sys
2011/09/20 16:56:32.0500 4072 SynTP (fa2daa32bed908023272a0f77d625dae) C:\WINDOWS\system32\DRIVERS\SynTP.sys
2011/09/20 16:56:32.0593 4072 sysaudio (8b83f3ed0f1688b4958f77cd6d2bf290) C:\WINDOWS\system32\drivers\sysaudio.sys
2011/09/20 16:56:32.0687 4072 Tcpip (9aefa14bd6b182d61e3119fa5f436d3d) C:\WINDOWS\system32\DRIVERS\tcpip.sys
2011/09/20 16:56:32.0812 4072 TDPIPE (6471a66807f5e104e4885f5b67349397) C:\WINDOWS\system32\drivers\TDPIPE.sys
2011/09/20 16:56:32.0859 4072 TDTCP (c56b6d0402371cf3700eb322ef3aaf61) C:\WINDOWS\system32\drivers\TDTCP.sys
2011/09/20 16:56:32.0921 4072 TermDD (88155247177638048422893737429d9e) C:\WINDOWS\system32\DRIVERS\termdd.sys
2011/09/20 16:56:33.0000 4072 tfsnboio (d0177776e11b0b3f272eebd262a69661) C:\WINDOWS\system32\dla\tfsnboio.sys
2011/09/20 16:56:33.0078 4072 tfsncofs (599804bc938b8305a5422319774da871) C:\WINDOWS\system32\dla\tfsncofs.sys
2011/09/20 16:56:33.0125 4072 tfsndrct (a1902c00adc11c4d83f8e3ed947a6a32) C:\WINDOWS\system32\dla\tfsndrct.sys
2011/09/20 16:56:33.0187 4072 tfsndres (d8ddb3f2b1bef15cff6728d89c042c61) C:\WINDOWS\system32\dla\tfsndres.sys
2011/09/20 16:56:33.0250 4072 tfsnifs (c4f2dea75300971cdaee311007de138d) C:\WINDOWS\system32\dla\tfsnifs.sys
2011/09/20 16:56:33.0453 4072 tfsnopio (272925be0ea919f08286d2ee6f102b0f) C:\WINDOWS\system32\dla\tfsnopio.sys
2011/09/20 16:56:33.0500 4072 tfsnpool (7b7d955e5cebc2fb88b03ef875d52a2f) C:\WINDOWS\system32\dla\tfsnpool.sys
2011/09/20 16:56:33.0531 4072 tfsnudf (e3d01263109d800c1967c12c10a0b018) C:\WINDOWS\system32\dla\tfsnudf.sys
2011/09/20 16:56:33.0593 4072 tfsnudfa (b9e9c377906e3a65bc74598fff7f7458) C:\WINDOWS\system32\dla\tfsnudfa.sys
2011/09/20 16:56:33.0687 4072 tmcfw (3929c6784db38788d76a88d9c4043dee) C:\WINDOWS\system32\DRIVERS\TM_CFW.sys
2011/09/20 16:56:34.0046 4072 tmpreflt (0c89809f1df614bd42093a446b222a32) C:\WINDOWS\system32\DRIVERS\tmpreflt.sys
2011/09/20 16:56:34.0140 4072 tmtdi (264ea39fdebd0b5e9d49d79923ed91ad) C:\WINDOWS\system32\DRIVERS\tmtdi.sys
2011/09/20 16:56:34.0218 4072 tmxpflt (3d473e97ff805dab903aa66f08286c90) C:\WINDOWS\system32\drivers\TmXPFlt.sys
2011/09/20 16:56:34.0546 4072 TosIde (f2790f6af01321b172aa62f8e1e187d9) C:\WINDOWS\system32\DRIVERS\toside.sys
2011/09/20 16:56:34.0703 4072 Udfs (5787b80c2e3c5e2f56c2a233d91fa2c9) C:\WINDOWS\system32\drivers\Udfs.sys
2011/09/20 16:56:34.0984 4072 ultra (1b698a51cd528d8da4ffaed66dfc51b9) C:\WINDOWS\system32\DRIVERS\ultra.sys
2011/09/20 16:56:35.0140 4072 Update (402ddc88356b1bac0ee3dd1580c76a31) C:\WINDOWS\system32\DRIVERS\update.sys
2011/09/20 16:56:35.0296 4072 USBAAPL (5c2bdc152bbab34f36473deaf7713f22) C:\WINDOWS\system32\Drivers\usbaapl.sys
2011/09/20 16:56:35.0359 4072 usbaudio (e919708db44ed8543a7c017953148330) C:\WINDOWS\system32\drivers\usbaudio.sys
2011/09/20 16:56:35.0437 4072 usbccgp (173f317ce0db8e21322e71b7e60a27e8) C:\WINDOWS\system32\DRIVERS\usbccgp.sys
2011/09/20 16:56:35.0625 4072 usbehci (65dcf09d0e37d4c6b11b5b0b76d470a7) C:\WINDOWS\system32\DRIVERS\usbehci.sys
2011/09/20 16:56:35.0687 4072 usbhub (1ab3cdde553b6e064d2e754efe20285c) C:\WINDOWS\system32\DRIVERS\usbhub.sys
2011/09/20 16:56:35.0765 4072 usbprint (a717c8721046828520c9edf31288fc00) C:\WINDOWS\system32\DRIVERS\usbprint.sys
2011/09/20 16:56:35.0875 4072 usbscan (a0b8cf9deb1184fbdd20784a58fa75d4) C:\WINDOWS\system32\DRIVERS\usbscan.sys
2011/09/20 16:56:36.0187 4072 USBSTOR (a32426d9b14a089eaa1d922e0c5801a9) C:\WINDOWS\system32\DRIVERS\USBSTOR.SYS
2011/09/20 16:56:36.0328 4072 usbuhci (26496f9dee2d787fc3e61ad54821ffe6) C:\WINDOWS\system32\DRIVERS\usbuhci.sys
2011/09/20 16:56:36.0406 4072 usbvideo (63bbfca7f390f4c49ed4b96bfb1633e0) C:\WINDOWS\system32\Drivers\usbvideo.sys
2011/09/20 16:56:36.0593 4072 usb_rndisx (b6cc50279d6cd28e090a5d33244adc9a) C:\WINDOWS\system32\DRIVERS\usb8023x.sys
2011/09/20 16:56:36.0656 4072 VgaSave (0d3a8fafceacd8b7625cd549757a7df1) C:\WINDOWS\System32\drivers\vga.sys
2011/09/20 16:56:36.0718 4072 viaagp (754292ce5848b3738281b4f3607eaef4) C:\WINDOWS\system32\DRIVERS\viaagp.sys
2011/09/20 16:56:36.0781 4072 ViaIde (3b3efcda263b8ac14fdf9cbdd0791b2e) C:\WINDOWS\system32\DRIVERS\viaide.sys
2011/09/20 16:56:36.0828 4072 VolSnap (4c8fcb5cc53aab716d810740fe59d025) C:\WINDOWS\system32\drivers\VolSnap.sys
2011/09/20 16:56:36.0968 4072 vsapint (50e1ea1dd3ea74919d7a1c5d6c9c0b56) C:\WINDOWS\system32\DRIVERS\vsapint.sys
2011/09/20 16:56:37.0125 4072 Wanarp (e20b95baedb550f32dd489265c1da1f6) C:\WINDOWS\system32\DRIVERS\wanarp.sys
2011/09/20 16:56:37.0250 4072 WDC_SAM (d6efaf429fd30c5df613d220e344cce7) C:\WINDOWS\system32\DRIVERS\wdcsam.sys
2011/09/20 16:56:37.0312 4072 wdmaud (6768acf64b18196494413695f0c3a00f) C:\WINDOWS\system32\drivers\wdmaud.sys
2011/09/20 16:56:37.0437 4072 winachsf (74cf3f2e4e40c4a2e18d39d6300a5c24) C:\WINDOWS\system32\DRIVERS\HSF_CNXT.sys
2011/09/20 16:56:37.0734 4072 WmiAcpi (c42584fd66ce9e17403aebca199f7bdb) C:\WINDOWS\system32\DRIVERS\wmiacpi.sys
2011/09/20 16:56:37.0781 4072 WpdUsb (bbaeaca1ffa3c86361cf0998474f6c3a) C:\WINDOWS\system32\Drivers\wpdusb.sys
2011/09/20 16:56:37.0843 4072 WSTCODEC (c98b39829c2bbd34e454150633c62c78) C:\WINDOWS\system32\DRIVERS\WSTCODEC.SYS
2011/09/20 16:56:37.0890 4072 MBR (0x1B8) (5cb90281d1a59b251f6603134774eec3) \Device\Harddisk0\DR0
2011/09/20 16:56:37.0906 4072 MBR (0x1B8) (8f558eb6672622401da993e1e865c861) \Device\Harddisk1\DR5
2011/09/20 16:56:37.0921 4072 Boot (0x1200) (01b2009c09ccf404384a3b6b2db466a9) \Device\Harddisk0\DR0\Partition0
2011/09/20 16:56:37.0921 4072 Boot (0x1200) (4a40ea518c7320400832be752e44629b) \Device\Harddisk1\DR5\Partition0
2011/09/20 16:56:37.0937 4072 ================================================================================
2011/09/20 16:56:37.0937 4072 Scan finished
2011/09/20 16:56:37.0937 4072 ================================================================================
2011/09/20 16:56:37.0937 5788 Detected object count: 2
2011/09/20 16:56:37.0937 5788 Actual detected object count: 2
2011/09/20 16:56:45.0546 5788 HiddenFile.Multi.Generic(f08ea724) - User select action: Skip
2011/09/20 16:56:45.0718 5788 IPSec (c3b55c9f04b8b9214b26659c56ec3e04) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2011/09/20 16:56:45.0718 5788 Suspicious file (Forged): C:\WINDOWS\system32\DRIVERS\ipsec.sys. Real md5: c3b55c9f04b8b9214b26659c56ec3e04, Fake md5: 23c74d75e36e7158768dd63d92789a91
2011/09/20 16:56:46.0078 5788 Backup copy found, using it..
2011/09/20 16:56:46.0109 5788 C:\WINDOWS\system32\DRIVERS\ipsec.sys - will be cured after reboot
2011/09/20 16:56:46.0109 5788 Rootkit.Win32.ZAccess.e(IPSec) - User select action: Cure
#20

 Posted 20 September 2011 - 04:10 PM
Posted 20 September 2011 - 04:10 PM

It is ZeroAccess rootkit. If you are in hurry I would recommend reformat and fresh OS install. If not we can play a little around with it.
Please run now AntiZeroAccess one more time and post the log:
Run aswMBR scan one more time and post its log:
Please run now AntiZeroAccess one more time and post the log:
- Double click on it to run it (If running Vista or Windows 7, right click on it and select "Run as an Administrator")
- Type y and press enter to run the scan
- Please post AntiZeroAccess_Log.txt contents in your next post. This file is saved in the same location as AntiZeroAccess program.
Run aswMBR scan one more time and post its log:
- Double click the aswMBR.exe to run it.

- When asked if you want to download Avast's virus definitions please select No.
- Click the Scan button to start scan.

- On completion of the scan click Save log, save it to your desktop and post in your next reply.
#21

 Posted 20 September 2011 - 05:22 PM
Posted 20 September 2011 - 05:22 PM

I ran AntiZeroAccess and AswMBR.
Webroot AntiZeroAccess 0.8 Log File
Execution time: 20/09/2011 - 16:03
Host operation System: Windows Xp X86 version 5.1.2600 Service Pack 3
16:03:18 - CheckSystem - Begin to check system...
16:03:18 - OpenRootDrive - Opening system root volume and physical drive....
16:03:18 - C Root Drive: Disk number: 0 Start sector: 0x00017886 Partition Size: 0x0ACAE347 sectors.
16:03:18 - PrevX Main driver extracted in "C:\WINDOWS\system32\drivers\ZeroAccess.sys".
16:03:19 - InstallAndStartDriver - Main driver was installed and now is running.
16:03:19 - CheckSystem - Warning! Disk class driver is INFECTED.
16:03:28 - StopAndRemoveDriver - AntiZeroAccess Driver is stopped and removed.
16:03:28 - StopAndRemoveDriver - File "ZeroAccess.sys" was deleted!
16:03:28 - Execution Ended!
Webroot AntiZeroAccess 0.8 Log File
Execution time: 20/09/2011 - 17:43
Host operation System: Windows Xp X86 version 5.1.2600 Service Pack 3
17:43:10 - CheckSystem - Begin to check system...
17:43:10 - OpenRootDrive - Opening system root volume and physical drive....
17:43:10 - C Root Drive: Disk number: 0 Start sector: 0x00017886 Partition Size: 0x0ACAE347 sectors.
17:43:10 - PrevX Main driver extracted in "C:\WINDOWS\system32\drivers\ZeroAccess.sys".
17:43:11 - InstallAndStartDriver - Main driver was installed and now is running.
17:43:11 - CheckSystem - Warning! Disk class driver is INFECTED.
17:43:19 - CheckFile - Warning! File "mrxsmb.sys" is Infected by ZeroAccess Rootkit.
17:43:34 - DoRepair - Begin to perform system repair....
17:43:34 - DoRepair - System Disk class driver was repaired.
17:43:34 - DoRepair - Infected "mrxsmb.sys" file was renamed.
17:43:34 - DoRepair - Infected "mrxsmb.sys" file was successfully cleaned!
17:43:34 - StopAndRemoveDriver - AntiZeroAccess Driver is stopped and removed.
17:43:34 - StopAndRemoveDriver - File "ZeroAccess.sys" was deleted!
17:43:34 - Execution Ended!
aswMBR version 0.9.8.986 Copyright© 2011 AVAST Software
Run date: 2011-09-20 18:03:15
-----------------------------
18:03:15.718 OS Version: Windows 5.1.2600 Service Pack 3
18:03:15.718 Number of processors: 2 586 0xF06
18:03:15.718 ComputerName: D82M1C4 UserName:
18:03:16.359 Initialize success
18:03:23.859 AVAST engine defs: 11091900
18:03:26.203 Disk 0 (boot) \Device\Harddisk0\DR0 -> \Device\Ide\IdeDeviceP0T0L0-3
18:03:26.203 Disk 0 Vendor: Hitachi_HTS721010G9SA00 MCZOC10H Size: 95396MB BusType: 3
18:03:28.234 Disk 0 MBR read successfully
18:03:28.234 Disk 0 MBR scan
18:03:28.296 Disk 0 unknown MBR code
18:03:28.296 Disk 0 scanning sectors +195366465
18:03:28.406 Disk 0 scanning C:\WINDOWS\system32\drivers
18:04:03.718 Service scanning
18:04:04.875 Service f08ea724 C:\WINDOWS\614960880:259086555.exe **LOCKED** 5
18:04:05.671 Modules scanning
18:04:22.078 Disk 0 trace - called modules:
18:04:22.093 ntkrnlpa.exe CLASSPNP.SYS disk.sys ACPI.sys hal.dll atapi.sys >>UNKNOWN [0x89172980]<<
18:04:22.109 1 nt!IofCallDriver -> \Device\Harddisk0\DR0[0x8a840ab8]
18:04:22.109 3 CLASSPNP.SYS[ba0e8fd7] -> nt!IofCallDriver -> \Device\0000007a[0x8a822f18]
18:04:22.109 5 ACPI.sys[b9f69620] -> nt!IofCallDriver -> \Device\Ide\IdeDeviceP0T0L0-3[0x8a7cdd98]
18:04:22.640 AVAST engine scan C:\WINDOWS
18:04:46.921 AVAST engine scan C:\WINDOWS\system32
18:09:00.640 AVAST engine scan C:\WINDOWS\system32\drivers
18:09:45.859 AVAST engine scan C:\Documents and Settings\David Mills
18:17:53.000 AVAST engine scan C:\Documents and Settings\All Users
18:21:27.937 Scan finished successfully
18:21:40.062 Disk 0 MBR has been saved successfully to "C:\Documents and Settings\David Mills\Desktop\MBR.dat"
18:21:40.078 The log file has been saved successfully to "C:\Documents and Settings\David Mills\Desktop\aswMBR.txt"
Webroot AntiZeroAccess 0.8 Log File
Execution time: 20/09/2011 - 16:03
Host operation System: Windows Xp X86 version 5.1.2600 Service Pack 3
16:03:18 - CheckSystem - Begin to check system...
16:03:18 - OpenRootDrive - Opening system root volume and physical drive....
16:03:18 - C Root Drive: Disk number: 0 Start sector: 0x00017886 Partition Size: 0x0ACAE347 sectors.
16:03:18 - PrevX Main driver extracted in "C:\WINDOWS\system32\drivers\ZeroAccess.sys".
16:03:19 - InstallAndStartDriver - Main driver was installed and now is running.
16:03:19 - CheckSystem - Warning! Disk class driver is INFECTED.
16:03:28 - StopAndRemoveDriver - AntiZeroAccess Driver is stopped and removed.
16:03:28 - StopAndRemoveDriver - File "ZeroAccess.sys" was deleted!
16:03:28 - Execution Ended!
Webroot AntiZeroAccess 0.8 Log File
Execution time: 20/09/2011 - 17:43
Host operation System: Windows Xp X86 version 5.1.2600 Service Pack 3
17:43:10 - CheckSystem - Begin to check system...
17:43:10 - OpenRootDrive - Opening system root volume and physical drive....
17:43:10 - C Root Drive: Disk number: 0 Start sector: 0x00017886 Partition Size: 0x0ACAE347 sectors.
17:43:10 - PrevX Main driver extracted in "C:\WINDOWS\system32\drivers\ZeroAccess.sys".
17:43:11 - InstallAndStartDriver - Main driver was installed and now is running.
17:43:11 - CheckSystem - Warning! Disk class driver is INFECTED.
17:43:19 - CheckFile - Warning! File "mrxsmb.sys" is Infected by ZeroAccess Rootkit.
17:43:34 - DoRepair - Begin to perform system repair....
17:43:34 - DoRepair - System Disk class driver was repaired.
17:43:34 - DoRepair - Infected "mrxsmb.sys" file was renamed.
17:43:34 - DoRepair - Infected "mrxsmb.sys" file was successfully cleaned!
17:43:34 - StopAndRemoveDriver - AntiZeroAccess Driver is stopped and removed.
17:43:34 - StopAndRemoveDriver - File "ZeroAccess.sys" was deleted!
17:43:34 - Execution Ended!
aswMBR version 0.9.8.986 Copyright© 2011 AVAST Software
Run date: 2011-09-20 18:03:15
-----------------------------
18:03:15.718 OS Version: Windows 5.1.2600 Service Pack 3
18:03:15.718 Number of processors: 2 586 0xF06
18:03:15.718 ComputerName: D82M1C4 UserName:
18:03:16.359 Initialize success
18:03:23.859 AVAST engine defs: 11091900
18:03:26.203 Disk 0 (boot) \Device\Harddisk0\DR0 -> \Device\Ide\IdeDeviceP0T0L0-3
18:03:26.203 Disk 0 Vendor: Hitachi_HTS721010G9SA00 MCZOC10H Size: 95396MB BusType: 3
18:03:28.234 Disk 0 MBR read successfully
18:03:28.234 Disk 0 MBR scan
18:03:28.296 Disk 0 unknown MBR code
18:03:28.296 Disk 0 scanning sectors +195366465
18:03:28.406 Disk 0 scanning C:\WINDOWS\system32\drivers
18:04:03.718 Service scanning
18:04:04.875 Service f08ea724 C:\WINDOWS\614960880:259086555.exe **LOCKED** 5
18:04:05.671 Modules scanning
18:04:22.078 Disk 0 trace - called modules:
18:04:22.093 ntkrnlpa.exe CLASSPNP.SYS disk.sys ACPI.sys hal.dll atapi.sys >>UNKNOWN [0x89172980]<<
18:04:22.109 1 nt!IofCallDriver -> \Device\Harddisk0\DR0[0x8a840ab8]
18:04:22.109 3 CLASSPNP.SYS[ba0e8fd7] -> nt!IofCallDriver -> \Device\0000007a[0x8a822f18]
18:04:22.109 5 ACPI.sys[b9f69620] -> nt!IofCallDriver -> \Device\Ide\IdeDeviceP0T0L0-3[0x8a7cdd98]
18:04:22.640 AVAST engine scan C:\WINDOWS
18:04:46.921 AVAST engine scan C:\WINDOWS\system32
18:09:00.640 AVAST engine scan C:\WINDOWS\system32\drivers
18:09:45.859 AVAST engine scan C:\Documents and Settings\David Mills
18:17:53.000 AVAST engine scan C:\Documents and Settings\All Users
18:21:27.937 Scan finished successfully
18:21:40.062 Disk 0 MBR has been saved successfully to "C:\Documents and Settings\David Mills\Desktop\MBR.dat"
18:21:40.078 The log file has been saved successfully to "C:\Documents and Settings\David Mills\Desktop\aswMBR.txt"
#22

 Posted 20 September 2011 - 05:53 PM
Posted 20 September 2011 - 05:53 PM

Please open Windows Explorer and go here: C:\WINDOWS\614960880:259086555.exe. Can you see this file 614960880:259086555.exe?
#23

 Posted 20 September 2011 - 06:00 PM
Posted 20 September 2011 - 06:00 PM

The file in C:\WINDOWS is 614960880. The colon and rest of those numbers aren't in the file name and there is no extension attached to the file at all. The file type is "File" and its size is 0 Kb.
#24

 Posted 20 September 2011 - 06:11 PM
Posted 20 September 2011 - 06:11 PM

OK. Try to run Combofix now, but please before you save it to your desktop rename it render.exe.
 Please download ComboFix from one of these locations:
Please download ComboFix from one of these locations:
Bleepingcomputer
ForoSpyware
Notes:
Please note: If the Microsoft Windows Recovery Console is already installed, or if you are running Vista, ComboFix will continue it's malware removal procedures.


Give it at least 20-30 minutes to finish if needed.
Please do not attach the scan results from Combofix. Use copy/paste.
Also please describe how your computer behaves at the moment.
Bleepingcomputer
ForoSpyware
Notes:
- Do not mouse-click Combofix's window while it is running. That may cause it to stall.
- ComboFix may reset a number of Internet Explorer's settings, including making Internet Explorer the default browser.
- Combofix prevents autorun of ALL CD, floppy and USB devices to assist with malware removal & increase security. If this is an issue or makes it difficult for you -- please tell your helper.
- CF disconnects your machine from the internet. The connection is automatically restored before CF completes its run. If CF runs into difficulty and terminates prematurely, the connection can be manually restored by restarting your machine.
- If you are using personal certificates I recommend you to export them before running ComboFix and save them to external media.
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools. (Click on this link to see a list of programs that should be disabled. The list is not all inclusive.)
- Double click on Combofix.exe and follow the prompts.
Notes: Combofix will run without the Recovery Console installed. Skip the Recovery Console part if you're running Vista or Windows 7. - As part of it's process, ComboFix will check to see if the Microsoft Windows Recovery Console is installed. With malware infections being as they are today, it's strongly recommended to have this pre-installed on your machine before doing any malware removal. It will allow you to boot up into a special recovery/repair mode that will allow us to more easily help you should your computer have a problem after an attempted removal of malware.
- Follow the prompts to allow ComboFix to download and install the Microsoft Windows Recovery Console, and when prompted, agree to the End-User License Agreement to install the Microsoft Windows Recovery Console.
Please note: If the Microsoft Windows Recovery Console is already installed, or if you are running Vista, ComboFix will continue it's malware removal procedures.

- Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:

- Click on Yes. ComboFix will now start scanning your computer for known infections. This procedure can take some time, so please be patient.
- When finished, it shall produce a log for you. Please include the C:\ComboFix.txt in your next reply.
Give it at least 20-30 minutes to finish if needed.
Please do not attach the scan results from Combofix. Use copy/paste.
Also please describe how your computer behaves at the moment.
#25

 Posted 20 September 2011 - 07:16 PM
Posted 20 September 2011 - 07:16 PM

Once again, ComboFix (which I saved as render.exe) it will not install. The files start to extract and the progress bar seems to be going like normal then without warning, it just stops.
#26

 Posted 20 September 2011 - 07:49 PM
Posted 20 September 2011 - 07:49 PM

Try to run Combofix in Safe mode.
To restart the computer in safe mode
Reboot then continually press F8 as the system starts booting
Once a menu appears select safe mode
To restart the computer in safe mode
Reboot then continually press F8 as the system starts booting
Once a menu appears select safe mode
#27

 Posted 20 September 2011 - 08:52 PM
Posted 20 September 2011 - 08:52 PM

Safe mode behaved the same way; it started to extract the files then suddenly stopped.
#28

 Posted 20 September 2011 - 09:02 PM
Posted 20 September 2011 - 09:02 PM

Must look into this issue deeper and it could take a wile.
#29

 Posted 21 September 2011 - 05:05 AM
Posted 21 September 2011 - 05:05 AM

Hi,
Please download ComboFix from Here or Here directly to the C:\ drive.
Note: In the event you already have Combofix, this is a new version that I need you to download. It is important that it is saved and renamed following this process directly to the root of C: drive.
<li>Please do not rename Combofix to other names, but only to the one indicated.
<li>Close any open browsers.
<li>Close/disable all anti virus and anti malware programs so they do not interfere with the running of ComboFix.
<li>Double click on svchost.exe & follow the prompts.
<li>When finished, it will produce a report for you.
<li>Please post it here for further review
Note: Do not mouseclick combo-fix's window while it's running. That may cause it to stall.
Please download ComboFix from Here or Here directly to the C:\ drive.
Note: In the event you already have Combofix, this is a new version that I need you to download. It is important that it is saved and renamed following this process directly to the root of C: drive.
- If you are using Firefox, make sure that your download settings are as follows:
- Tools->Options->Main tab
- Set to "Always ask me where to Save the files".
<li>Please do not rename Combofix to other names, but only to the one indicated.
<li>Close any open browsers.
<li>Close/disable all anti virus and anti malware programs so they do not interfere with the running of ComboFix.
- Very Important! Temporarily disable your anti-virus, script blocking and any anti-malware real-time protection before performing a scan. They can interfere with ComboFix or remove some of its embedded files which may cause "unpredictable results".
- Click on this link to see a list of programs that should be disabled. The list is not all inclusive. If yours is not listed and you don't know how to disable it, please ask.
- Close any open browsers.
- WARNING: Combofix will disconnect your machine from the Internet as soon as it starts
- Please do not attempt to re-connect your machine back to the Internet until Combofix has completely finished.
- If there is no internet connection after running Combofix, then restart your computer to restore back your connection
<li>Double click on svchost.exe & follow the prompts.
<li>When finished, it will produce a report for you.
<li>Please post it here for further review
Note: Do not mouseclick combo-fix's window while it's running. That may cause it to stall.
#30

 Posted 21 September 2011 - 08:46 AM
Posted 21 September 2011 - 08:46 AM

I downloaded and saved ComboFix directly to my C: drive and it did almost exactly the same thing as before. The installer begins to extract the files and I see it extracting, then without warning it stops. The only difference is, whereas usually the icon is the default blank window box, this time the icon is the red circle ComboFix logo. Everything else is the same. I only tried to run it once.
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked





 Sign In
Sign In Create Account
Create Account

