OTL Log
OTL logfile created on: 5/15/2012 12:46:07 PM - Run 2
OTL by OldTimer - Version 3.2.43.0 Folder = C:\Documents and Settings\Matthew\My Documents
Windows XP Professional Edition Service Pack 3 (Version = 5.1.2600) - Type = NTWorkstation
Internet Explorer (Version = 8.0.6001.18702)
Locale: 00000409 | Country: United States | Language: ENU | Date Format: M/d/yyyy
1.97 Gb Total Physical Memory | 1.13 Gb Available Physical Memory | 57.32% Memory free
3.81 Gb Paging File | 3.08 Gb Available in Paging File | 80.82% Paging File free
Paging file location(s): C:\pagefile.sys 2046 4092 [binary data]
%SystemDrive% = C: | %SystemRoot% = C:\WINDOWS | %ProgramFiles% = C:\Program Files
Drive C: | 148.97 Gb Total Space | 75.55 Gb Free Space | 50.71% Space Free | Partition Type: NTFS
Computer Name: JAMMIN | User Name: Matthew | Logged in as Administrator.
Boot Mode: Normal | Scan Mode: Current user | Quick Scan
Company Name Whitelist: On | Skip Microsoft Files: On | No Company Name Whitelist: On | File Age = 30 Days
========== Processes (SafeList) ========== PRC - [2012/05/15 12:20:36 | 000,595,456 | ---- | M] (OldTimer Tools) -- C:\Documents and Settings\Matthew\My Documents\OTL.scr
PRC - [2012/04/23 21:45:57 | 000,982,880 | ---- | M] () -- C:\Program Files\AVG Secure Search\vprot.exe
PRC - [2012/04/19 20:56:02 | 003,905,920 | ---- | M] (SUPERAntiSpyware.com) -- C:\Program Files\SUPERAntiSpyware\SUPERAntiSpyware.exe
PRC - [2012/04/04 15:56:40 | 000,654,408 | ---- | M] (Malwarebytes Corporation) -- C:\Program Files\Malwarebytes' Anti-Malware\mbamservice.exe
PRC - [2012/04/04 15:56:38 | 000,462,408 | ---- | M] (Malwarebytes Corporation) -- C:\Program Files\Malwarebytes' Anti-Malware\mbamgui.exe
PRC - [2012/03/12 13:16:39 | 000,918,880 | ---- | M] () -- C:\Program Files\Common Files\AVG Secure Search\vToolbarUpdater\10.2.0\ToolbarUpdater.exe
PRC - [2012/01/24 18:24:26 | 002,416,480 | ---- | M] (AVG Technologies CZ, s.r.o.) -- C:\Program Files\AVG\AVG2012\avgtray.exe
PRC - [2011/11/28 02:19:04 | 001,229,664 | ---- | M] (AVG Technologies CZ, s.r.o.) -- C:\Program Files\AVG\AVG2012\avgnsx.exe
PRC - [2011/10/12 07:25:22 | 004,433,248 | ---- | M] (AVG Technologies CZ, s.r.o.) -- C:\Program Files\AVG\AVG2012\AVGIDSAgent.exe
PRC - [2011/09/08 21:53:26 | 000,743,264 | ---- | M] (AVG Technologies CZ, s.r.o.) -- C:\Program Files\AVG\AVG2012\avgrsx.exe
PRC - [2011/08/15 07:21:40 | 000,337,760 | ---- | M] (AVG Technologies CZ, s.r.o.) -- C:\Program Files\AVG\AVG2012\avgcsrvx.exe
PRC - [2011/08/02 07:09:08 | 000,192,776 | ---- | M] (AVG Technologies CZ, s.r.o.) -- C:\Program Files\AVG\AVG2012\avgwdsvc.exe
PRC - [2011/07/28 19:08:12 | 001,259,376 | ---- | M] () -- C:\Program Files\DivX\DivX Update\DivXUpdate.exe
PRC - [2009/07/26 22:10:00 | 001,983,816 | ---- | M] (CANON INC.) -- C:\Program Files\Canon\MyPrinter\BJMYPRT.EXE
PRC - [2009/02/10 12:01:49 | 000,116,104 | ---- | M] () -- C:\Program Files\Canon\IJPLM\ijplmsvc.exe
PRC - [2008/11/09 16:48:14 | 000,602,392 | ---- | M] (Yahoo! Inc.) -- C:\Program Files\Yahoo!\SoftwareUpdate\YahooAUService.exe
PRC - [2008/04/14 08:00:00 | 001,033,728 | ---- | M] (Microsoft Corporation) -- C:\WINDOWS\explorer.exe
========== Modules (No Company Name) ========== MOD - [2012/05/15 12:43:39 | 000,065,024 | ---- | M] () -- C:\Documents and Settings\All Users\Application Data\SUPERAntiSpyware.com\SUPERAntiSpyware\SDDLLS\SD10006.dll
MOD - [2012/05/15 12:43:39 | 000,052,736 | ---- | M] () -- C:\Documents and Settings\All Users\Application Data\SUPERAntiSpyware.com\SUPERAntiSpyware\SDDLLS\SD10007.dll
MOD - [2012/04/29 14:29:14 | 000,117,760 | ---- | M] () -- C:\Documents and Settings\All Users\Application Data\SUPERAntiSpyware.com\SUPERAntiSpyware\SDDLLS\UIREPAIR.DLL
MOD - [2012/04/29 14:29:13 | 000,052,224 | ---- | M] () -- C:\Documents and Settings\All Users\Application Data\SUPERAntiSpyware.com\SUPERAntiSpyware\SDDLLS\SD10005.dll
MOD - [2012/04/23 21:45:57 | 000,982,880 | ---- | M] () -- C:\Program Files\AVG Secure Search\vprot.exe
MOD - [2012/04/23 21:45:56 | 001,869,152 | ---- | M] () -- C:\Program Files\AVG Secure Search\10.2.0.3\AVG Secure Search_toolbar.dll
MOD - [2012/03/12 13:16:39 | 000,918,880 | ---- | M] () -- C:\Program Files\Common Files\AVG Secure Search\vToolbarUpdater\10.2.0\ToolbarUpdater.exe
MOD - [2011/07/28 19:09:42 | 000,096,112 | ---- | M] () -- C:\Program Files\DivX\DivX Update\DivXUpdateCheck.dll
MOD - [2011/07/28 19:08:12 | 001,259,376 | ---- | M] () -- C:\Program Files\DivX\DivX Update\DivXUpdate.exe
MOD - [2009/02/10 12:01:49 | 000,116,104 | ---- | M] () -- C:\Program Files\Canon\IJPLM\ijplmsvc.exe
========== Win32 Services (SafeList) ========== SRV - File not found [Auto | Stopped] -- C:\WINDOWS\system32\spoolsv.exe -- (Spooler)
SRV - File not found [Disabled | Stopped] -- %SystemRoot%\System32\hidserv.dll -- (HidServ)
SRV - File not found [Auto | Stopped] -- C:\Program Files\Automated Feedback Tool\v5.1.460.0\aftservice.exe -- (aftservice)
SRV - [2012/04/27 20:17:50 | 000,253,088 | ---- | M] (Adobe Systems Incorporated) [On_Demand | Stopped] -- C:\WINDOWS\system32\Macromed\Flash\FlashPlayerUpdateService.exe -- (AdobeFlashPlayerUpdateSvc)
SRV - [2012/04/04 15:56:40 | 000,654,408 | ---- | M] (Malwarebytes Corporation) [Auto | Running] -- C:\Program Files\Malwarebytes' Anti-Malware\mbamservice.exe -- (MBAMService)
SRV - [2012/03/12 13:16:39 | 000,918,880 | ---- | M] () [Auto | Running] -- C:\Program Files\Common Files\AVG Secure Search\vToolbarUpdater\10.2.0\ToolbarUpdater.exe -- (vToolbarUpdater10.2.0)
SRV - [2011/10/12 07:25:22 | 004,433,248 | ---- | M] (AVG Technologies CZ, s.r.o.) [Auto | Running] -- C:\Program Files\AVG\AVG2012\AVGIDSAgent.exe -- (AVGIDSAgent)
SRV - [2011/08/02 07:09:08 | 000,192,776 | ---- | M] (AVG Technologies CZ, s.r.o.) [Auto | Running] -- C:\Program Files\AVG\AVG2012\avgwdsvc.exe -- (avgwd)
SRV - [2009/02/10 12:01:49 | 000,116,104 | ---- | M] () [Auto | Running] -- C:\Program Files\Canon\IJPLM\ijplmsvc.exe -- (IJPLMSVC)
SRV - [2008/11/09 16:48:14 | 000,602,392 | ---- | M] (Yahoo! Inc.) [Auto | Running] -- C:\Program Files\Yahoo!\SoftwareUpdate\YahooAUService.exe -- (YahooAUService)
========== Driver Services (SafeList) ========== DRV - File not found [Kernel | Auto | Stopped] -- system32\DRIVERS\zumbus.sys -- (zumbus)
DRV - File not found [Kernel | On_Demand | Stopped] -- -- (WDICA)
DRV - File not found [Kernel | On_Demand | Stopped] -- -- (PDRFRAME)
DRV - File not found [Kernel | On_Demand | Stopped] -- -- (PDRELI)
DRV - File not found [Kernel | On_Demand | Stopped] -- -- (PDFRAME)
DRV - File not found [Kernel | On_Demand | Stopped] -- -- (PDCOMP)
DRV - File not found [Kernel | System | Stopped] -- -- (PCIDump)
DRV - File not found [Kernel | Boot | Stopped] -- system32\DRIVERS\nielprt.sys -- (nielprt)
DRV - File not found [Kernel | On_Demand | Stopped] -- system32\drivers\nielgfx.sys -- (NielGfx)
DRV - File not found [Kernel | System | Stopped] -- -- (lbrtfdc)
DRV - File not found [Kernel | System | Stopped] -- -- (i2omgmt)
DRV - File not found [Kernel | On_Demand | Stopped] -- System32\Drivers\Diag69xp.sys -- (Diag69xp)
DRV - File not found [Kernel | System | Stopped] -- -- (Changer)
DRV - File not found [Kernel | Boot | Stopped] -- -- (cerc6)
DRV - [2012/04/04 15:56:40 | 000,022,344 | ---- | M] (Malwarebytes Corporation) [File_System | On_Demand | Running] -- C:\WINDOWS\system32\drivers\mbam.sys -- (MBAMProtector)
DRV - [2011/10/07 07:23:48 | 000,230,608 | ---- | M] (AVG Technologies CZ, s.r.o.) [Kernel | System | Running] -- C:\WINDOWS\system32\drivers\avgldx86.sys -- (Avgldx86)
DRV - [2011/10/04 07:21:42 | 000,016,720 | ---- | M] (AVG Technologies CZ, s.r.o. ) [Kernel | On_Demand | Running] -- C:\WINDOWS\system32\drivers\AVGIDSShim.sys -- (AVGIDSShim)
DRV - [2011/09/13 07:30:10 | 000,032,592 | ---- | M] (AVG Technologies CZ, s.r.o.) [File_System | Boot | Running] -- C:\WINDOWS\system32\drivers\avgrkx86.sys -- (Avgrkx86)
DRV - [2011/08/08 07:08:58 | 000,040,016 | ---- | M] (AVG Technologies CZ, s.r.o.) [File_System | System | Running] -- C:\WINDOWS\system32\drivers\avgmfx86.sys -- (Avgmfx86)
DRV - [2011/07/22 12:27:02 | 000,012,880 | ---- | M] (SUPERAdBlocker.com and SUPERAntiSpyware.com) [Kernel | System | Running] -- C:\Program Files\SUPERAntiSpyware\sasdifsv.sys -- (SASDIFSV)
DRV - [2011/07/12 17:55:22 | 000,067,664 | ---- | M] (SUPERAdBlocker.com and SUPERAntiSpyware.com) [Kernel | System | Running] -- C:\Program Files\SUPERAntiSpyware\SASKUTIL.SYS -- (SASKUTIL)
DRV - [2011/07/11 02:14:38 | 000,295,248 | ---- | M] (AVG Technologies CZ, s.r.o.) [Kernel | System | Running] -- C:\WINDOWS\system32\drivers\avgtdix.sys -- (Avgtdix)
DRV - [2011/07/11 02:14:28 | 000,024,272 | ---- | M] (AVG Technologies CZ, s.r.o. ) [Kernel | On_Demand | Running] -- C:\WINDOWS\system32\drivers\AVGIDSFilter.sys -- (AVGIDSFilter)
DRV - [2011/07/11 02:14:28 | 000,023,120 | ---- | M] (AVG Technologies CZ, s.r.o. ) [Kernel | Boot | Running] -- C:\WINDOWS\system32\drivers\AVGIDSEH.sys -- (AVGIDSEH)
DRV - [2011/07/11 02:14:26 | 000,134,608 | ---- | M] (AVG Technologies CZ, s.r.o. ) [Kernel | On_Demand | Running] -- C:\WINDOWS\system32\drivers\AVGIDSDriver.sys -- (AVGIDSDriver)
DRV - [2008/08/04 18:04:12 | 004,752,896 | ---- | M] (Realtek Semiconductor Corp.) [Kernel | On_Demand | Running] -- C:\WINDOWS\system32\drivers\RtkHDAud.sys -- (IntcAzAudAddService) Service for Realtek HD Audio (WDM)
DRV - [2008/05/07 20:31:16 | 000,106,368 | ---- | M] (Realtek Semiconductor Corporation ) [Kernel | On_Demand | Running] -- C:\WINDOWS\system32\drivers\Rtenicxp.sys -- (RTLE8023xp)
DRV - [2006/11/02 07:00:08 | 000,039,368 | ---- | M] (Microsoft Corporation) [Kernel | On_Demand | Stopped] -- C:\WINDOWS\system32\drivers\winusb.sys -- (WinUSB)
========== Standard Registry (SafeList) ========== ========== Internet Explorer ========== IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Search,Default_Search_URL =
http://www.google.com/ieIE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Search,SearchAssistant =
http://www.google.com/ieIE - HKLM\..\SearchScopes,DefaultScope = {0633EE93-D776-472f-A0FF-E1416B8B2E3A}
IE - HKLM\..\SearchScopes\{0633EE93-D776-472f-A0FF-E1416B8B2E3A}: "URL" =
http://search.live.c...ferrer:source?} IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Search Bar =
http://www.google.com/ieIE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Search Page =
http://www.google.comIE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Start Page =
http://yahoo.com/IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Search,SearchAssistant =
http://www.google.com/ieIE - HKCU\..\URLSearchHook: - No CLSID value found
IE - HKCU\..\SearchScopes,DefaultScope = {6A1806CD-94D4-4689-BA73-E35EA1EA9990}
IE - HKCU\..\SearchScopes\{0633EE93-D776-472f-A0FF-E1416B8B2E3A}: "URL" =
http://www.bing.com/...Box&FORM=IE8SRCIE - HKCU\..\SearchScopes\{60E08808-5AD2-40D2-88C2-AF7B9B3BCADE}: "URL" =
http://mp3tubetoolba...f993afacb22a3c6IE - HKCU\..\SearchScopes\{6A1806CD-94D4-4689-BA73-E35EA1EA9990}: "URL" =
http://www.google.co...1I7GGLL_enUS379IE - HKCU\..\SearchScopes\{95B7759C-8C7F-4BF1-B163-73684A933233}: "URL" =
http://isearch.avg.c...fr&d=2012-04-23 11:04:18&v=10.0.0.7&sap=dsp&q={searchTerms}
IE - HKCU\..\SearchScopes\{AFBCB7E0-F91A-4951-9F31-58FEE57A25C4}: "URL" =
http://www.ask.com/w...q={SEARCHTERMS}IE - HKCU\..\SearchScopes\{afdbddaa-5d3f-42ee-b79c-185a7020515b}: "URL" =
http://search.condui...4&ctid=CT672154IE - HKCU\..\SearchScopes\{C5215FD1-CD03-46AA-AFBB-2D75F196F256}: "URL" =
http://search.yahoo....p={searchTerms}IE - HKCU\..\SearchScopes\{CF739809-1C6C-47C0-85B9-569DBB141420}: "URL" =
http://toolbar.ask.c...m=1&toolbar=VZ2IE - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyEnable" = 0
IE - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyServer" = :0
========== FireFox ========== FF - HKLM\Software\MozillaPlugins\@canon.com/EPPEX: C:\Program Files\Canon\Easy-PhotoPrint EX\NPEZFFPI.DLL (CANON INC.)
FF - HKLM\Software\MozillaPlugins\@divx.com/DivX Browser Plugin,version=1.0.0: C:\Program Files\DivX\DivX Plus Web Player\npdivx32.dll (DivX, LLC)
FF - HKLM\Software\MozillaPlugins\@divx.com/DivX Player Plugin,version=1.0.0: C:\Program Files\DivX\DivX Player\npDivxPlayerPlugin.dll File not found
FF - HKLM\Software\MozillaPlugins\@divx.com/DivX VOD Helper,version=1.0.0: C:\Program Files\DivX\DivX OVS Helper\npovshelper.dll (DivX, LLC.)
FF - HKLM\Software\MozillaPlugins\@java.com/JavaPlugin: C:\Program Files\Java\jre6\bin\new_plugin\npjp2.dll (Sun Microsystems, Inc.)
FF - HKLM\Software\MozillaPlugins\@microsoft.com/WPF,version=3.5: c:\WINDOWS\Microsoft.NET\Framework\v3.5\Windows Presentation Foundation\NPWPF.dll (Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@pandonetworks.com/PandoWebPlugin: C:\Program Files\Pando Networks\Media Booster\npPandoWebPlugin.dll File not found
FF - HKLM\Software\MozillaPlugins\Adobe Reader: C:\Program Files\Adobe\Reader 9.0\Reader\AIR\nppdf32.dll (Adobe Systems Inc.)
FF - HKEY_LOCAL_MACHINE\software\mozilla\Firefox\extensions\\
[email protected]: C:\Documents and Settings\All Users\Application Data\CodecCheck\firefox [2011/09/18 15:04:12 | 000,000,000 | -H-D | M]
FF - HKEY_LOCAL_MACHINE\software\mozilla\Firefox\extensions\\avg@toolbar: C:\Documents and Settings\All Users\Application Data\AVG Secure Search\10.2.0.3\ [2012/03/12 13:16:41 | 000,000,000 | -H-D | M]
FF - HKEY_LOCAL_MACHINE\software\mozilla\Firefox\extensions\\{1E73965B-8B48-48be-9C8D-68B920ABC1C4}: C:\Program Files\AVG\AVG2012\Firefox4\ [2012/02/02 10:54:27 | 000,000,000 | ---D | M]
FF - HKEY_LOCAL_MACHINE\software\mozilla\Firefox\extensions\\{23fcfd51-4958-4f00-80a3-ae97e717ed8b}: C:\Program Files\DivX\DivX Plus Web Player\firefox\DivXHTML5 [2012/03/27 09:34:33 | 000,000,000 | ---D | M]
[2011/07/29 13:15:41 | 000,000,000 | -H-D | M] (No name found) -- C:\Documents and Settings\Matthew\Application Data\Mozilla\Extensions
O1 HOSTS File: ([2012/04/28 17:08:52 | 000,000,882 | RH-- | M]) - C:\WINDOWS\system32\drivers\etc\hosts
O1 - Hosts: 94.63.147.16 www.google.com
O1 - Hosts: 94.63.147.17 www.bing.com
O2 - BHO: (no name) - {02478D38-C3F9-4efb-9B51-7695ECA05670} - No CLSID value found.
O2 - BHO: (Canon Easy-WebPrint EX BHO) - {3785D0AD-BFFF-47F6-BF5B-A587C162FED9} - C:\Program Files\Canon\Easy-WebPrint EX\ewpexbho.dll (CANON INC.)
O2 - BHO: (AVG Safe Search) - {3CA2F312-6F6E-4B53-A66E-4E65E497C8C0} - C:\Program Files\AVG\AVG2012\avgssie.dll (AVG Technologies CZ, s.r.o.)
O2 - BHO: (AVG Security Toolbar) - {95B7759C-8C7F-4BF1-B163-73684A933233} - C:\Program Files\AVG Secure Search\10.2.0.3\AVG Secure Search_toolbar.dll ()
O2 - BHO: (Yontoo Layers) - {FD72061E-9FDE-484D-A58A-0BAB4151CAD8} - C:\Program Files\Yontoo Layers Runtime\YontooIEClient.dll (Yontoo LLC)
O3 - HKLM\..\Toolbar: (Canon Easy-WebPrint EX) - {759D9886-0C6F-4498-BAB6-4A5F47C6C72F} - C:\Program Files\Canon\Easy-WebPrint EX\ewpexhlp.dll (CANON INC.)
O3 - HKLM\..\Toolbar: (AVG Security Toolbar) - {95B7759C-8C7F-4BF1-B163-73684A933233} - C:\Program Files\AVG Secure Search\10.2.0.3\AVG Secure Search_toolbar.dll ()
O3 - HKLM\..\Toolbar: (no name) - Locked - No CLSID value found.
O3 - HKCU\..\Toolbar\WebBrowser: (no name) - {2318C2B1-4965-11D4-9B18-009027A5CD4F} - No CLSID value found.
O3 - HKCU\..\Toolbar\WebBrowser: (Canon Easy-WebPrint EX) - {759D9886-0C6F-4498-BAB6-4A5F47C6C72F} - C:\Program Files\Canon\Easy-WebPrint EX\ewpexhlp.dll (CANON INC.)
O4 - HKLM..\Run: [Alcmtr] C:\WINDOWS\Alcmtr.exe (Realtek Semiconductor Corp.)
O4 - HKLM..\Run: [AVG_TRAY] C:\Program Files\AVG\AVG2012\avgtray.exe (AVG Technologies CZ, s.r.o.)
O4 - HKLM..\Run: [CanonMyPrinter] C:\Program Files\Canon\MyPrinter\BJMyPrt.exe (CANON INC.)
O4 - HKLM..\Run: [DivXUpdate] C:\Program Files\DivX\DivX Update\DivXUpdate.exe ()
O4 - HKLM..\Run: [Malwarebytes' Anti-Malware] C:\Program Files\Malwarebytes' Anti-Malware\mbamgui.exe (Malwarebytes Corporation)
O4 - HKLM..\Run: [ROC_roc_dec12] "C:\Program Files\AVG Secure Search\ROC_roc_dec12.exe" /PROMPT /CMPID=roc_dec12 File not found
O4 - HKLM..\Run: [vProt] C:\Program Files\AVG Secure Search\vprot.exe ()
O4 - HKCU..\Run: [SUPERAntiSpyware] C:\Program Files\SUPERAntiSpyware\SUPERAntiSpyware.exe (SUPERAntiSpyware.com)
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: HonorAutoRunSetting = 1
O7 - HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDriveTypeAutoRun = 145
O16 - DPF: {63DF43C2-469A-41F3-B119-17B1ACE8BB34}
http://elephantcam.i...SncRz30View.cab (Sony SNC-RZ30 Image Viewer)
O16 - DPF: {8AD9C840-044E-11D1-B3E9-00805F499D93}
http://java.sun.com/...indows-i586.cab (Java Plug-in 1.6.0_29)
O16 - DPF: {8F6E7FB2-E56B-4F66-A4E1-9765D2565280}
http://www.worldwinn....0/iewwload.cab (WorldWinner ActiveX Launcher Control)
O16 - DPF: {924B4927-D3BA-41EA-9F7E-8A89194AB3AC}
http://panda-plugin..../p3dactivex.cab (P3DActiveX Control)
O16 - DPF: {CAFEEFAC-0016-0000-0029-ABCDEFFEDCBA}
http://java.sun.com/...indows-i586.cab (Java Plug-in 1.6.0_29)
O16 - DPF: {CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA}
http://java.sun.com/...indows-i586.cab (Java Plug-in 1.6.0_29)
O16 - DPF: {E2883E8F-472F-4FB0-9522-AC9BF37916A7}
http://platformdl.ad...Plus/1.6/gp.cab (Reg Error: Key error.)
O16 - DPF: {E7637F18-B2C8-43E4-BCFE-BC3437DF469F}
https://s.userzoom.com/s/UserZoom.cab (Reg Error: Key error.)
O17 - HKLM\System\CCS\Services\Tcpip\Parameters: DhcpNameServer = 192.168.2.1
O17 - HKLM\System\CCS\Services\Tcpip\Parameters\Interfaces\{D6E2F278-5FCB-423B-ADE5-F33BEEC67C60}: DhcpNameServer = 192.168.2.1
O18 - Protocol\Handler\linkscanner {F274614C-63F8-47D5-A4D1-FBDDE494F8D1} - C:\Program Files\AVG\AVG2012\avgpp.dll (AVG Technologies CZ, s.r.o.)
O18 - Protocol\Handler\viprotocol {B658800C-F66E-4EF3-AB85-6C0C227862A9} - C:\Program Files\Common Files\AVG Secure Search\ViProtocolInstaller\10.2.0\ViProtocol.dll ()
O20 - HKLM Winlogon: Shell - (Explorer.exe) - C:\WINDOWS\explorer.exe (Microsoft Corporation)
O20 - HKLM Winlogon: UserInit - (C:\WINDOWS\system32\userinit.exe) - C:\WINDOWS\system32\userinit.exe (Microsoft Corporation)
O20 - Winlogon\Notify\!SASWinLogon: DllName - (C:\Program Files\SUPERAntiSpyware\SASWINLO.DLL) - C:\Program Files\SUPERAntiSpyware\SASWINLO.DLL (SUPERAntiSpyware.com)
O24 - Desktop WallPaper: C:\Documents and Settings\Matthew\Local Settings\Application Data\Microsoft\Wallpaper1.bmp
O24 - Desktop BackupWallPaper: C:\Documents and Settings\Matthew\Local Settings\Application Data\Microsoft\Wallpaper1.bmp
O28 - HKLM ShellExecuteHooks: {5AE067D3-9AFB-48E0-853A-EBB7F4A000DA} - C:\Program Files\SUPERAntiSpyware\SASSEH.DLL (SuperAdBlocker.com)
O32 - HKLM CDRom: AutoRun - 1
O32 - AutoRun File - [2009/11/02 21:24:07 | 000,000,000 | ---- | M] () - C:\AUTOEXEC.BAT -- [ NTFS ]
O34 - HKLM BootExecute: (autocheck autochk *)
O34 - HKLM BootExecute: (C:\PROGRA~1\AVG\AVG2012\avgrsx.exe /sync /restart)
O35 - HKLM\..comfile [open] -- "%1" %*
O35 - HKLM\..exefile [open] -- "%1" %*
O37 - HKLM\...com [@ = comfile] -- "%1" %*
O37 - HKLM\...exe [@ = exefile] -- "%1" %*
O38 - SubSystems\\Windows: (ServerDll=winsrv:UserServerDllInitialization,3)
O38 - SubSystems\\Windows: (ServerDll=winsrv:ConServerDllInitialization,2)
NetSvcs: 6to4 - File not found
NetSvcs: HidServ - %SystemRoot%\System32\hidserv.dll File not found
NetSvcs: Ias - File not found
NetSvcs: Iprip - File not found
NetSvcs: Irmon - File not found
NetSvcs: NWCWorkstation - File not found
NetSvcs: Nwsapagent - File not found
NetSvcs: WmdmPmSp - File not found
CREATERESTOREPOINT
Unable to start System Restore Service. Error code 1056
========== Files/Folders - Created Within 30 Days ========== [2012/05/15 12:20:32 | 000,595,456 | ---- | C] (OldTimer Tools) -- C:\Documents and Settings\Matthew\My Documents\OTL.scr
[2012/05/14 19:03:20 | 000,000,000 | -HSD | C] -- C:\found.000
[2012/05/14 17:14:45 | 000,000,000 | ---D | C] -- C:\TDSSKiller_Quarantine
[2012/05/14 17:13:42 | 000,000,000 | ---D | C] -- C:\Documents and Settings\Matthew\Desktop\123myapp
[2012/05/07 19:25:53 | 000,000,000 | ---D | C] -- C:\Documents and Settings\NetworkService\Local Settings\Application Data\Adobe
[2012/04/29 14:43:34 | 000,000,000 | ---D | C] -- C:\Documents and Settings\All Users\Start Menu\Programs\Malwarebytes' Anti-Malware
[2012/04/29 14:43:32 | 000,022,344 | ---- | C] (Malwarebytes Corporation) -- C:\WINDOWS\System32\drivers\mbam.sys
[2012/04/29 14:28:47 | 000,000,000 | ---D | C] -- C:\Documents and Settings\Matthew\Application Data\SUPERAntiSpyware.com
[2012/04/29 14:28:01 | 000,000,000 | ---D | C] -- C:\Documents and Settings\All Users\Start Menu\Programs\SUPERAntiSpyware
[2012/04/29 14:27:57 | 000,000,000 | ---D | C] -- C:\Documents and Settings\All Users\Application Data\SUPERAntiSpyware.com
[2012/04/29 14:27:57 | 000,000,000 | ---D | C] -- C:\Program Files\SUPERAntiSpyware
[2012/04/29 14:27:17 | 016,187,696 | ---- | C] (SUPERAntiSpyware.com) -- C:\Documents and Settings\Matthew\Desktop\SUPERAntiSpywarePro.exe
[2012/04/26 10:40:26 | 000,000,000 | -HSD | C] -- C:\WINDOWS\CSC
[2012/04/25 20:13:54 | 000,000,000 | ---D | C] -- C:\Documents and Settings\Matthew\Application Data\Malwarebytes
[2012/04/25 20:13:31 | 000,000,000 | ---D | C] -- C:\Program Files\MALWAREBYTES ANTI-MALWARE
[2012/04/25 20:13:06 | 000,000,000 | ---D | C] -- C:\Documents and Settings\All Users\Application Data\Malwarebytes
[2012/04/25 20:13:04 | 000,000,000 | ---D | C] -- C:\Program Files\Malwarebytes' Anti-Malware
[2012/04/25 20:00:40 | 000,000,000 | ---D | C] -- C:\Documents and Settings\NetworkService\Application Data\Google
[2012/04/25 20:00:18 | 000,000,000 | ---D | C] -- C:\WINDOWS\System32\%APPDATA%
[2012/04/25 19:55:35 | 000,000,000 | RH-D | C] -- C:\Documents and Settings\Matthew\Recent
[2012/04/25 19:36:00 | 000,000,000 | ---D | C] -- C:\Documents and Settings\Matthew\Start Menu\Programs\Data Recovery
[2012/04/24 23:32:20 | 000,000,000 | ---D | C] -- C:\Documents and Settings\NetworkService\Application Data\Sun
[2012/04/23 11:04:16 | 000,000,000 | ---D | C] -- C:\Program Files\AVG Secure Search
[2012/02/27 18:08:35 | 000,047,360 | ---- | C] (VSO Software) -- C:\Documents and Settings\Matthew\Application Data\pcouffin.sys
[5 C:\WINDOWS\System32\*.tmp files -> C:\WINDOWS\System32\*.tmp -> ]
[3 C:\WINDOWS\*.tmp files -> C:\WINDOWS\*.tmp -> ]
[1 C:\Documents and Settings\Matthew\Local Settings\Application Data\*.tmp files -> C:\Documents and Settings\Matthew\Local Settings\Application Data\*.tmp -> ]
========== Files - Modified Within 30 Days ========== [2012/05/15 12:43:21 | 000,002,048 | --S- | M] () -- C:\WINDOWS\bootstat.dat
[2012/05/15 12:20:36 | 000,595,456 | ---- | M] (OldTimer Tools) -- C:\Documents and Settings\Matthew\My Documents\OTL.scr
[2012/05/15 12:16:00 | 000,000,830 | ---- | M] () -- C:\WINDOWS\tasks\Adobe Flash Player Updater.job
[2012/05/15 12:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At37.job
[2012/05/15 12:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At13.job
[2012/05/15 11:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At36.job
[2012/05/15 11:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At12.job
[2012/05/15 10:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At35.job
[2012/05/15 10:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At11.job
[2012/05/15 09:59:18 | 098,203,570 | ---- | M] () -- C:\WINDOWS\System32\drivers\AVG\incavi.avm
[2012/05/15 09:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At34.job
[2012/05/15 09:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At10.job
[2012/05/15 08:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At33.job
[2012/05/15 08:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At9.job
[2012/05/15 07:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At32.job
[2012/05/15 07:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At8.job
[2012/05/15 06:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At31.job
[2012/05/15 06:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At7.job
[2012/05/15 05:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At30.job
[2012/05/15 05:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At6.job
[2012/05/15 04:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At29.job
[2012/05/15 04:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At5.job
[2012/05/15 03:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At28.job
[2012/05/15 03:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At4.job
[2012/05/15 02:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At27.job
[2012/05/15 02:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At3.job
[2012/05/15 01:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At26.job
[2012/05/15 01:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At2.job
[2012/05/15 00:54:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At1.job
[2012/05/15 00:32:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At25.job
[2012/05/14 23:35:07 | 000,000,664 | ---- | M] () -- C:\WINDOWS\System32\d3d9caps.dat
[2012/05/14 23:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At48.job
[2012/05/14 23:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At24.job
[2012/05/14 22:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At47.job
[2012/05/14 22:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At23.job
[2012/05/14 21:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At46.job
[2012/05/14 21:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At22.job
[2012/05/14 20:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At45.job
[2012/05/14 20:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At21.job
[2012/05/14 17:12:07 | 002,055,783 | ---- | M] () -- C:\Documents and Settings\Matthew\Desktop\123myapp.zip
[2012/05/14 15:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At40.job
[2012/05/14 15:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At16.job
[2012/05/14 14:00:01 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At39.job
[2012/05/14 14:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At15.job
[2012/05/14 13:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At38.job
[2012/05/14 13:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At14.job
[2012/05/14 09:08:15 | 000,002,206 | ---- | M] () -- C:\WINDOWS\System32\wpa.dbl
[2012/05/12 09:36:54 | 000,484,518 | ---- | M] () -- C:\WINDOWS\System32\perfh009.dat
[2012/05/12 09:36:54 | 000,080,788 | ---- | M] () -- C:\WINDOWS\System32\perfc009.dat
[2012/05/07 18:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At43.job
[2012/05/07 18:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At19.job
[2012/05/07 17:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At42.job
[2012/05/07 17:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At18.job
[2012/05/07 16:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At41.job
[2012/05/07 16:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At17.job
[2012/05/06 19:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\tasks\At44.job
[2012/05/06 19:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\tasks\At20.job
[2012/05/04 17:11:25 | 000,060,558 | ---- | M] () -- C:\WINDOWS\System32\drivers\AVG\iavichjg.avm
[2012/04/29 14:43:35 | 000,000,784 | ---- | M] () -- C:\Documents and Settings\All Users\Desktop\Malwarebytes Anti-Malware.lnk
[2012/04/29 14:28:11 | 000,001,678 | ---- | M] () -- C:\Documents and Settings\All Users\Desktop\SUPERAntiSpyware Professional.lnk
[2012/04/29 14:27:33 | 016,187,696 | ---- | M] (SUPERAntiSpyware.com) -- C:\Documents and Settings\Matthew\Desktop\SUPERAntiSpywarePro.exe
[2012/04/25 19:58:35 | 001,008,141 | ---- | M] () -- C:\Documents and Settings\Matthew\Desktop\iExplore.exe
[2012/04/25 19:36:00 | 000,000,855 | ---- | M] () -- C:\Documents and Settings\Matthew\Application Data\Microsoft\Internet Explorer\Quick Launch\Data_Recovery.lnk
[2012/04/23 11:08:32 | 000,001,729 | -H-- | M] () -- C:\Documents and Settings\All Users\Desktop\Adobe Reader 9.lnk
[2012/04/23 11:00:09 | 000,000,154 | ---- | M] () -- C:\Documents and Settings\Matthew\Local Settings\Application Data\svcxdcl32.dat
[5 C:\WINDOWS\System32\*.tmp files -> C:\WINDOWS\System32\*.tmp -> ]
[3 C:\WINDOWS\*.tmp files -> C:\WINDOWS\*.tmp -> ]
[1 C:\Documents and Settings\Matthew\Local Settings\Application Data\*.tmp files -> C:\Documents and Settings\Matthew\Local Settings\Application Data\*.tmp -> ]
========== Files Created - No Company Name ========== [2012/05/14 17:11:56 | 002,055,783 | ---- | C] () -- C:\Documents and Settings\Matthew\Desktop\123myapp.zip
[2012/04/29 14:43:35 | 000,000,784 | ---- | C] () -- C:\Documents and Settings\All Users\Desktop\Malwarebytes Anti-Malware.lnk
[2012/04/29 14:28:11 | 000,001,678 | ---- | C] () -- C:\Documents and Settings\All Users\Desktop\SUPERAntiSpyware Professional.lnk
[2012/04/25 19:58:28 | 001,008,141 | ---- | C] () -- C:\Documents and Settings\Matthew\Desktop\iExplore.exe
[2012/04/25 19:36:00 | 000,000,855 | ---- | C] () -- C:\Documents and Settings\Matthew\Application Data\Microsoft\Internet Explorer\Quick Launch\Data_Recovery.lnk
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At48.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At47.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At46.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At45.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At44.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At43.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At42.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At41.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At40.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At39.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At38.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At37.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At36.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At35.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At34.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At33.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At32.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At31.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At30.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At29.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At28.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At27.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At26.job
[2012/04/25 19:02:24 | 000,000,418 | ---- | C] () -- C:\WINDOWS\tasks\At25.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At24.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At23.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At22.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At21.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At20.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At19.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At18.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At17.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At16.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At15.job
[2012/04/25 19:02:24 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At14.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At9.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At8.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At7.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At6.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At5.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At4.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At3.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At2.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At13.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At12.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At11.job
[2012/04/25 19:02:23 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At10.job
[2012/04/25 19:02:22 | 000,000,416 | ---- | C] () -- C:\WINDOWS\tasks\At1.job
[2012/04/24 23:28:52 | 000,000,830 | ---- | C] () -- C:\WINDOWS\tasks\Adobe Flash Player Updater.job
[2012/04/22 20:30:02 | 000,000,154 | ---- | C] () -- C:\Documents and Settings\Matthew\Local Settings\Application Data\svcxdcl32.dat
[2012/02/27 18:08:35 | 000,087,608 | ---- | C] () -- C:\Documents and Settings\Matthew\Application Data\inst.exe
[2012/02/27 18:08:35 | 000,007,887 | ---- | C] () -- C:\Documents and Settings\Matthew\Application Data\pcouffin.cat
[2012/02/27 18:08:35 | 000,001,144 | ---- | C] () -- C:\Documents and Settings\Matthew\Application Data\pcouffin.inf
[2012/02/27 17:40:23 | 000,001,057 | ---- | C] () -- C:\Documents and Settings\Matthew\Application Data\vso_ts_preview.xml
[2012/02/27 10:36:40 | 000,334,914 | -H-- | C] () -- C:\Documents and Settings\LocalService\Local Settings\Application Data\WPFFontCache_v0400-System.dat
[2012/02/27 10:36:40 | 000,334,914 | -H-- | C] () -- C:\Documents and Settings\LocalService\Local Settings\Application Data\WPFFontCache_v0400-S-1-5-21-1078081533-1708537768-1417001333-1003-0.dat
[2012/02/25 15:33:55 | 000,000,318 | ---- | C] () -- C:\Documents and Settings\Matthew\Application Data\burnaware.ini
[2012/02/15 01:48:23 | 000,003,072 | ---- | C] () -- C:\WINDOWS\System32\iacenc.dll
[2012/01/30 17:14:14 | 000,000,064 | ---- | C] () -- C:\WINDOWS\GPlrLanc.dat
[2010/05/23 19:19:32 | 000,000,376 | ---- | C] () -- C:\WINDOWS\ODBC.INI
========== LOP Check ========== [2012/01/27 15:42:46 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\AFT
[2012/03/12 13:16:41 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\AVG Secure Search
[2012/02/09 17:28:08 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\AVG2012
[2012/01/30 17:57:29 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\avg9
[2009/11/03 20:00:41 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\Azureus
[2012/01/19 23:55:00 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\Babylon
[2010/05/21 00:10:38 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\CanonBJ
[2012/04/06 11:58:32 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\CanonIJ
[2010/05/23 19:36:20 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\CanonIJEGV
[2010/05/21 00:16:50 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\CanonIJEPPEX
[2010/05/21 00:14:50 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\CanonIJMyPrinter
[2012/04/12 08:31:47 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\CanonIJPLM
[2010/05/22 14:18:43 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\CanonIJScan
[2010/05/21 00:24:50 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\CanonIJSolutionMenu
[2011/08/24 18:13:11 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\CodecCheck
[2011/03/14 10:26:20 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\Common Files
[2012/02/06 15:00:38 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\InstallMate
[2010/04/16 00:32:22 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\IsolatedStorage
[2012/05/15 09:59:24 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\MFAData
[2009/11/04 11:42:56 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\PCSettings
[2011/09/18 15:03:16 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\Premium
[2012/02/27 18:08:16 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\Temp
[2012/02/09 16:48:12 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\TuneUp Software
[2012/05/14 09:49:57 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\W3i
[2012/02/09 16:47:16 | 000,000,000 | -HSD | M] -- C:\Documents and Settings\All Users\Application Data\{32364CEA-7855-4A3C-B674-53D8E9B97936}
[2009/11/02 21:12:01 | 000,000,000 | -H-D | M] -- C:\Documents and Settings\All Users\Application Data\{3276BE95_AF08_429F_A64F_CA64CB79BCF6}
[2012/01/30 14:16:23 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\AVG Secure Search
[2012/01/30 18:02:21 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\AVG2012
[2012/04/25 09:32:23 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\Azureus
[2012/01/19 23:55:00 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\Babylon
[2010/05/19 23:15:42 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\bppenu11
[2010/05/22 14:18:43 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\Canon
[2011/05/11 20:19:04 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\Canon Easy-WebPrint EX
[2009/11/05 15:09:08 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\com.adobe.mauby.4875E02D9FB21EE389F73B8D1702B320485DF8CE.1
[2012/02/09 16:19:14 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\Curiolab
[2012/03/27 19:02:52 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\DDMSettings
[2011/07/26 19:24:49 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\FCTB000062133
[2011/06/07 20:25:45 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\FLV Blaster
[2009/12/05 11:14:03 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\FrostWire
[2010/05/20 18:23:52 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\GetRightToGo
[2011/09/01 15:07:30 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\Keynote Systems
[2010/08/11 11:41:14 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\MSNInstaller
[2010/05/21 01:08:30 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\OpenOffice.org
[2009/11/03 18:55:14 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\Recorder
[2010/10/05 11:33:55 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\SmartDraw
[2012/02/09 16:47:46 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\TuneUp Software
[2011/09/07 16:03:21 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\TweetAdder3
[2011/08/02 14:07:16 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\Unity
[2012/02/27 18:08:36 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\Vso
[2011/07/30 20:02:29 | 000,000,000 | ---D | M] -- C:\Documents and Settings\Matthew\Application Data\WhiteSmoke
[2012/05/15 00:54:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At1.job
[2012/05/15 09:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At10.job
[2012/05/15 10:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At11.job
[2012/05/15 11:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At12.job
[2012/05/15 12:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At13.job
[2012/05/14 13:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At14.job
[2012/05/14 14:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At15.job
[2012/05/14 15:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At16.job
[2012/05/07 16:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At17.job
[2012/05/07 17:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At18.job
[2012/05/07 18:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At19.job
[2012/05/15 01:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At2.job
[2012/05/06 19:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At20.job
[2012/05/14 20:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At21.job
[2012/05/14 21:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At22.job
[2012/05/14 22:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At23.job
[2012/05/14 23:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At24.job
[2012/05/15 00:32:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At25.job
[2012/05/15 01:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At26.job
[2012/05/15 02:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At27.job
[2012/05/15 03:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At28.job
[2012/05/15 04:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At29.job
[2012/05/15 02:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At3.job
[2012/05/15 05:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At30.job
[2012/05/15 06:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At31.job
[2012/05/15 07:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At32.job
[2012/05/15 08:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At33.job
[2012/05/15 09:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At34.job
[2012/05/15 10:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At35.job
[2012/05/15 11:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At36.job
[2012/05/15 12:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At37.job
[2012/05/14 13:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At38.job
[2012/05/14 14:00:01 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At39.job
[2012/05/15 03:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At4.job
[2012/05/14 15:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At40.job
[2012/05/07 16:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At41.job
[2012/05/07 17:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At42.job
[2012/05/07 18:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At43.job
[2012/05/06 19:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At44.job
[2012/05/14 20:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At45.job
[2012/05/14 21:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At46.job
[2012/05/14 22:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At47.job
[2012/05/14 23:00:00 | 000,000,418 | ---- | M] () -- C:\WINDOWS\Tasks\At48.job
[2012/05/15 04:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At5.job
[2012/05/15 05:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At6.job
[2012/05/15 06:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At7.job
[2012/05/15 07:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At8.job
[2012/05/15 08:00:00 | 000,000,416 | ---- | M] () -- C:\WINDOWS\Tasks\At9.job
========== Purity Check ========== ========== Custom Scans ========== < %SYSTEMDRIVE%\*.exe >[2007/11/07 09:03:18 | 000,562,688 | ---- | M] (Microsoft Corporation) -- C:\install.exe
< MD5 for: EXPLORER.EXE >[2008/04/14 08:00:00 | 001,033,728 | ---- | M] (Microsoft Corporation) MD5=12896823FB95BFB3DC9B46BCAEDC9923 -- C:\WINDOWS\explorer.exe
[2008/04/14 08:00:00 | 001,033,728 | ---- | M] (Microsoft Corporation) MD5=12896823FB95BFB3DC9B46BCAEDC9923 -- C:\WINDOWS\system32\dllcache\explorer.exe
[2011/01/16 15:55:21 | 000,255,488 | ---- | M] () MD5=3C33B26F2F7FA61D882515F2D6078691 -- C:\Documents and Settings\Administrator\Local Settings\Temp\RarSFX0\procs\explorer.exe
[2011/01/16 15:55:21 | 000,255,488 | ---- | M] () MD5=3C33B26F2F7FA61D882515F2D6078691 -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX2\procs\explorer.exe
[2011/01/16 15:55:21 | 000,255,488 | ---- | M] () MD5=3C33B26F2F7FA61D882515F2D6078691 -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX4\procs\explorer.exe
[2005/08/16 01:54:58 | 000,001,536 | ---- | M] () MD5=53E979547D8C2EA86560AC45DE08AE25 -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX3\h\explorer.exe
[2011/01/16 15:55:21 | 000,255,488 | ---- | M] () MD5=A09B6C794B2A02C1D3412FA53231138B -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX3\procs\explorer.exe
[2005/08/16 01:54:58 | 000,001,536 | ---- | M] () MD5=ABC6379205DE2618851C4FCBF72112EB -- C:\Documents and Settings\Administrator\Local Settings\Temp\RarSFX0\h\explorer.exe
[2005/08/16 01:54:58 | 000,001,536 | ---- | M] () MD5=ABC6379205DE2618851C4FCBF72112EB -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX2\h\explorer.exe
[2005/08/16 01:54:58 | 000,001,536 | ---- | M] () MD5=ABC6379205DE2618851C4FCBF72112EB -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX4\h\explorer.exe
< MD5 for: SVCHOST.EXE >[2012/04/04 15:56:38 | 000,199,240 | ---- | M] () MD5=097D0E812D7A9A3101CE46CB2BE0474D -- C:\Program Files\Malwarebytes' Anti-Malware\Chameleon\svchost.exe
[2008/04/14 08:00:00 | 000,014,336 | ---- | M] (Microsoft Corporation) MD5=27C6D03BCDB8CFEB96B716F3D8BE3E18 -- C:\WINDOWS\system32\dllcache\svchost.exe
[2008/04/14 08:00:00 | 000,014,336 | ---- | M] (Microsoft Corporation) MD5=27C6D03BCDB8CFEB96B716F3D8BE3E18 -- C:\WINDOWS\system32\svchost.exe
< MD5 for: USERINIT.EXE >[2008/04/14 08:00:00 | 000,026,112 | ---- | M] (Microsoft Corporation) MD5=A93AEE1928A9D7CE3E16D24EC7380F89 -- C:\WINDOWS\system32\dllcache\userinit.exe
[2008/04/14 08:00:00 | 000,026,112 | ---- | M] (Microsoft Corporation) MD5=A93AEE1928A9D7CE3E16D24EC7380F89 -- C:\WINDOWS\system32\userinit.exe
[2009/05/26 18:47:22 | 000,031,232 | ---- | M] (NirSoft) MD5=AC6094297CD882B8626466CDEB64F19F -- C:\Documents and Settings\Administrator\Local Settings\Temp\RarSFX0\userinit.exe
[2009/05/26 18:47:22 | 000,031,232 | ---- | M] (NirSoft) MD5=AC6094297CD882B8626466CDEB64F19F -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX2\userinit.exe
[2009/05/26 18:47:22 | 000,031,232 | ---- | M] (NirSoft) MD5=AC6094297CD882B8626466CDEB64F19F -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX4\userinit.exe
< MD5 for: WINLOGON.EXE >[2012/04/04 15:56:38 | 000,199,240 | ---- | M] () MD5=097D0E812D7A9A3101CE46CB2BE0474D -- C:\Program Files\Malwarebytes' Anti-Malware\Chameleon\winlogon.exe
[2009/05/26 18:47:22 | 000,031,232 | ---- | M] () MD5=9CC544B7333C1F741765CE8AFC8B8F27 -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX3\winlogon.exe
[2009/05/26 18:47:22 | 000,031,232 | ---- | M] (NirSoft) MD5=AC6094297CD882B8626466CDEB64F19F -- C:\Documents and Settings\Administrator\Local Settings\Temp\RarSFX0\winlogon.exe
[2009/05/26 18:47:22 | 000,031,232 | ---- | M] (NirSoft) MD5=AC6094297CD882B8626466CDEB64F19F -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX2\winlogon.exe
[2009/05/26 18:47:22 | 000,031,232 | ---- | M] (NirSoft) MD5=AC6094297CD882B8626466CDEB64F19F -- C:\Documents and Settings\Matthew\Local Settings\Temp\RarSFX4\winlogon.exe
[2008/04/14 08:00:00 | 000,507,904 | ---- | M] (Microsoft Corporation) MD5=ED0EF0A136DEC83DF69F04118870003E -- C:\WINDOWS\system32\dllcache\winlogon.exe
[2008/04/14 08:00:00 | 000,507,904 | ---- | M] (Microsoft Corporation) MD5=ED0EF0A136DEC83DF69F04118870003E -- C:\WINDOWS\system32\winlogon.exe
< %systemroot%\*. /mp /s > < hklm\software\clients\startmenuinternet|command /rs >HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\InstallInfo\\ReinstallCommand: "C:\WINDOWS\system32\ie4uinit.exe" -reinstall [2011/12/16 08:23:08 | 000,174,080 | ---- | M] (Microsoft Corporation)
HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\InstallInfo\\HideIconsCommand: "C:\WINDOWS\system32\ie4uinit.exe" -hide [2011/12/16 08:23:08 | 000,174,080 | ---- | M] (Microsoft Corporation)
HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\InstallInfo\\ShowIconsCommand: "C:\WINDOWS\system32\ie4uinit.exe" -show [2011/12/16 08:23:08 | 000,174,080 | ---- | M] (Microsoft Corporation)
HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\shell\naom\command\\: "C:\Program Files\Internet Explorer\iexplore.exe" -extoff [2009/03/08 15:09:26 | 000,638,816 | ---- | M] (Microsoft Corporation)
HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\shell\open\command\\: C:\Program Files\Internet Explorer\iexplore.exe [2009/03/08 15:09:26 | 000,638,816 | ---- | M] (Microsoft Corporation)
< hklm\software\clients\startmenuinternet|command /64 /rs >HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\InstallInfo\\ReinstallCommand: "C:\WINDOWS\system32\ie4uinit.exe" -reinstall [2011/12/16 08:23:08 | 000,174,080 | ---- | M] (Microsoft Corporation)
HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\InstallInfo\\HideIconsCommand: "C:\WINDOWS\system32\ie4uinit.exe" -hide [2011/12/16 08:23:08 | 000,174,080 | ---- | M] (Microsoft Corporation)
HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\InstallInfo\\ShowIconsCommand: "C:\WINDOWS\system32\ie4uinit.exe" -show [2011/12/16 08:23:08 | 000,174,080 | ---- | M] (Microsoft Corporation)
HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\shell\naom\command\\: "C:\Program Files\Internet Explorer\iexplore.exe" -extoff [2009/03/08 15:09:26 | 000,638,816 | ---- | M] (Microsoft Corporation)
HKEY_LOCAL_MACHINE\software\clients\startmenuinternet\IEXPLORE.EXE\shell\open\command\\: C:\Program Files\Internet Explorer\iexplore.exe [2009/03/08 15:09:26 | 000,638,816 | ---- | M] (Microsoft Corporation)
< > ========== Hard Links - Junction Points - Mount Points - Symbolic Links ==========[C:\WINDOWS\$NtUninstallKB57856$] -> Error: Cannot create file handle -> Unknown point type
========== Alternate Data Streams ========== @Alternate Data Stream - 125 bytes -> C:\Documents and Settings\All Users\Application Data\Temp:AC6124CA
< End of report >
TDSSKiller Log
17:13:51.0031 2884 TDSS rootkit removing tool 2.7.34.0 May 2 2012 09:59:18
17:13:51.0375 2884 ============================================================
17:13:51.0375 2884 Current date / time: 2012/05/14 17:13:51.0375
17:13:51.0375 2884 SystemInfo:
17:13:51.0375 2884
17:13:51.0375 2884 OS Version: 5.1.2600 ServicePack: 3.0
17:13:51.0375 2884 Product type: Workstation
17:13:51.0375 2884 ComputerName: JAMMIN
17:13:51.0375 2884 UserName: Matthew
17:13:51.0375 2884 Windows directory: C:\WINDOWS
17:13:51.0375 2884 System windows directory: C:\WINDOWS
17:13:51.0375 2884 Processor architecture: Intel x86
17:13:51.0375 2884 Number of processors: 2
17:13:51.0375 2884 Page size: 0x1000
17:13:51.0375 2884 Boot type: Normal boot
17:13:51.0375 2884 ============================================================
17:13:51.0812 2884 Drive \Device\Harddisk0\DR0 - Size: 0x2540BE4000 (149.01 Gb), SectorSize: 0x200, Cylinders: 0x4BFC, SectorsPerTrack: 0x3F, TracksPerCylinder: 0xFF, Type 'K0', Flags 0x00000050
17:13:51.0812 2884 ============================================================
17:13:51.0812 2884 \Device\Harddisk0\DR0:
17:13:51.0812 2884 MBR partitions:
17:13:51.0812 2884 \Device\Harddisk0\DR0\Partition0: MBR, Type 0x7, StartLBA 0x14000, BlocksNum 0x129F1720
17:13:51.0812 2884 ============================================================
17:13:51.0937 2884 C: <-> \Device\Harddisk0\DR0\Partition0
17:13:51.0937 2884 ============================================================
17:13:51.0937 2884 Initialize success
17:13:51.0937 2884 ============================================================
17:13:55.0156 3400 ============================================================
17:13:55.0156 3400 Scan started
17:13:55.0156 3400 Mode: Manual;
17:13:55.0156 3400 ============================================================
17:13:56.0640 3400 Abiosdsk - ok
17:13:56.0671 3400 abp480n5 - ok
17:13:56.0734 3400 ACPI (8fd99680a539792a30e97944fdaecf17) C:\WINDOWS\system32\DRIVERS\ACPI.sys
17:13:56.0750 3400 ACPI - ok
17:13:56.0968 3400 ACPIEC (9859c0f6936e723e4892d7141b1327d5) C:\WINDOWS\system32\drivers\ACPIEC.sys
17:13:56.0968 3400 ACPIEC - ok
17:13:57.0078 3400 AdobeFlashPlayerUpdateSvc (459ac130c6ab892b1cd5d7544626efc5) C:\WINDOWS\system32\Macromed\Flash\FlashPlayerUpdateService.exe
17:13:57.0125 3400 AdobeFlashPlayerUpdateSvc - ok
17:13:57.0140 3400 adpu160m - ok
17:13:57.0218 3400 aec (8bed39e3c35d6a489438b8141717a557) C:\WINDOWS\system32\drivers\aec.sys
17:13:57.0218 3400 aec - ok
17:13:57.0250 3400 AFD (1e44bc1e83d8fd2305f8d452db109cf9) C:\WINDOWS\System32\drivers\afd.sys
17:13:57.0250 3400 AFD - ok
17:13:57.0281 3400 aftservice - ok
17:13:57.0312 3400 Aha154x - ok
17:13:57.0343 3400 aic78u2 - ok
17:13:57.0375 3400 aic78xx - ok
17:13:57.0468 3400 Alerter (a9a3daa780ca6c9671a19d52456705b4) C:\WINDOWS\system32\alrsvc.dll
17:13:57.0468 3400 Alerter - ok
17:13:57.0500 3400 ALG (8c515081584a38aa007909cd02020b3d) C:\WINDOWS\System32\alg.exe
17:13:57.0515 3400 ALG - ok
17:13:57.0531 3400 AliIde - ok
17:13:57.0546 3400 amsint - ok
17:13:57.0578 3400 AppMgmt (d8849f77c0b66226335a59d26cb4edc6) C:\WINDOWS\System32\appmgmts.dll
17:13:57.0593 3400 AppMgmt - ok
17:13:57.0593 3400 asc - ok
17:13:57.0593 3400 asc3350p - ok
17:13:57.0609 3400 asc3550 - ok
17:13:57.0718 3400 aspnet_state (0e5e4957549056e2bf2c49f4f6b601ad) C:\WINDOWS\Microsoft.NET\Framework\v2.0.50727\aspnet_state.exe
17:13:57.0765 3400 aspnet_state - ok
17:13:57.0812 3400 AsyncMac (b153affac761e7f5fcfa822b9c4e97bc) C:\WINDOWS\system32\DRIVERS\asyncmac.sys
17:13:57.0812 3400 AsyncMac - ok
17:13:57.0859 3400 atapi (9f3a2f5aa6875c72bf062c712cfa2674) C:\WINDOWS\system32\drivers\atapi.sys
17:13:57.0859 3400 atapi - ok
17:13:57.0859 3400 Atdisk - ok
17:13:57.0875 3400 Atmarpc (9916c1225104ba14794209cfa8012159) C:\WINDOWS\system32\DRIVERS\atmarpc.sys
17:13:57.0875 3400 Atmarpc - ok
17:13:57.0906 3400 AudioSrv (def7a7882bec100fe0b2ce2549188f9d) C:\WINDOWS\System32\audiosrv.dll
17:13:57.0906 3400 AudioSrv - ok
17:13:57.0968 3400 audstub (d9f724aa26c010a217c97606b160ed68) C:\WINDOWS\system32\DRIVERS\audstub.sys
17:13:57.0968 3400 audstub - ok
17:13:58.0593 3400 AVGIDSAgent (6d440ff3f44ca72edfd6176c6d6a89c0) C:\Program Files\AVG\AVG2012\AVGIDSAgent.exe
17:13:58.0843 3400 AVGIDSAgent - ok
17:13:59.0000 3400 AVGIDSDriver (4fa401b33c1b50c816486f6951244a14) C:\WINDOWS\system32\DRIVERS\AVGIDSDriver.Sys
17:13:59.0000 3400 AVGIDSDriver - ok
17:13:59.0078 3400 AVGIDSEH (69578bc9d43d614c6b3455db4af19762) C:\WINDOWS\system32\DRIVERS\AVGIDSEH.Sys
17:13:59.0078 3400 AVGIDSEH - ok
17:13:59.0078 3400 AVGIDSFilter (6df528406aa22201f392b9b19121cd6f) C:\WINDOWS\system32\DRIVERS\AVGIDSFilter.Sys
17:13:59.0078 3400 AVGIDSFilter - ok
17:13:59.0109 3400 AVGIDSShim (1e01c2166b5599802bcd61b9691f7476) C:\WINDOWS\system32\DRIVERS\AVGIDSShim.Sys
17:13:59.0109 3400 AVGIDSShim - ok
17:13:59.0125 3400 Avgldx86 (bf8118cd5e2255387b715b534d64acd1) C:\WINDOWS\system32\DRIVERS\avgldx86.sys
17:13:59.0125 3400 Avgldx86 - ok
17:13:59.0140 3400 Avgmfx86 (1c77ef67f196466adc9924cb288afe87) C:\WINDOWS\system32\DRIVERS\avgmfx86.sys
17:13:59.0140 3400 Avgmfx86 - ok
17:13:59.0140 3400 Avgrkx86 (f2038ed7284b79dcef581468121192a9) C:\WINDOWS\system32\DRIVERS\avgrkx86.sys
17:13:59.0140 3400 Avgrkx86 - ok
17:13:59.0187 3400 Avgtdix (a6d562b612216d8d02a35ebeb92366bd) C:\WINDOWS\system32\DRIVERS\avgtdix.sys
17:13:59.0203 3400 Avgtdix - ok
17:13:59.0359 3400 avgwd (6699ece24fe4b3f752a66c66a602ee86) C:\Program Files\AVG\AVG2012\avgwdsvc.exe
17:13:59.0359 3400 avgwd - ok
17:13:59.0390 3400 Beep (da1f27d85e0d1525f6621372e7b685e9) C:\WINDOWS\system32\drivers\Beep.sys
17:13:59.0406 3400 Beep - ok
17:13:59.0453 3400 BITS (574738f61fca2935f5265dc4e5691314) C:\WINDOWS\system32\qmgr.dll
17:13:59.0484 3400 BITS - ok
17:13:59.0531 3400 Browser (a06ce3399d16db864f55faeb1f1927a9) C:\WINDOWS\System32\browser.dll
17:13:59.0656 3400 Browser - ok
17:13:59.0718 3400 cbidf2k (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\drivers\cbidf2k.sys
17:13:59.0718 3400 cbidf2k - ok
17:13:59.0718 3400 cd20xrnt - ok
17:13:59.0750 3400 Cdaudio (c1b486a7658353d33a10cc15211a873b) C:\WINDOWS\system32\drivers\Cdaudio.sys
17:13:59.0750 3400 Cdaudio - ok
17:13:59.0796 3400 Cdfs (c885b02847f5d2fd45a24e219ed93b32) C:\WINDOWS\system32\drivers\Cdfs.sys
17:13:59.0796 3400 Cdfs - ok
17:13:59.0828 3400 Cdrom (4b0a100eaf5c49ef3cca8c641431eacc) C:\WINDOWS\system32\DRIVERS\cdrom.sys
17:13:59.0828 3400 Cdrom - ok
17:13:59.0828 3400 cerc6 - ok
17:13:59.0843 3400 Changer - ok
17:13:59.0875 3400 CiSvc (1cfe720eb8d93a7158a4ebc3ab178bde) C:\WINDOWS\system32\cisvc.exe
17:13:59.0875 3400 CiSvc - ok
17:13:59.0890 3400 ClipSrv (34cbe729f38138217f9c80212a2a0c82) C:\WINDOWS\system32\clipsrv.exe
17:13:59.0890 3400 ClipSrv - ok
17:14:00.0000 3400 clr_optimization_v2.0.50727_32 (d87acaed61e417bba546ced5e7e36d9c) C:\WINDOWS\Microsoft.NET\Framework\v2.0.50727\mscorsvw.exe
17:14:00.0156 3400 clr_optimization_v2.0.50727_32 - ok
17:14:00.0281 3400 clr_optimization_v4.0.30319_32 (c5a75eb48e2344abdc162bda79e16841) C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe
17:14:00.0281 3400 clr_optimization_v4.0.30319_32 - ok
17:14:00.0281 3400 CmdIde - ok
17:14:00.0296 3400 COMSysApp - ok
17:14:00.0296 3400 Cpqarray - ok
17:14:00.0359 3400 CryptSvc (3d4e199942e29207970e04315d02ad3b) C:\WINDOWS\System32\cryptsvc.dll
17:14:00.0375 3400 CryptSvc - ok
17:14:00.0375 3400 dac2w2k - ok
17:14:00.0375 3400 dac960nt - ok
17:14:00.0437 3400 DcomLaunch (6b27a5c03dfb94b4245739065431322c) C:\WINDOWS\system32\rpcss.dll
17:14:00.0437 3400 DcomLaunch - ok
17:14:00.0515 3400 Dhcp (5e38d7684a49cacfb752b046357e0589) C:\WINDOWS\System32\dhcpcsvc.dll
17:14:00.0515 3400 Dhcp - ok
17:14:00.0515 3400 Diag69xp - ok
17:14:00.0562 3400 Disk (044452051f3e02e7963599fc8f4f3e25) C:\WINDOWS\system32\DRIVERS\disk.sys
17:14:00.0562 3400 Disk - ok
17:14:00.0562 3400 dmadmin - ok
17:14:00.0703 3400 dmboot (d992fe1274bde0f84ad826acae022a41) C:\WINDOWS\system32\drivers\dmboot.sys
17:14:01.0078 3400 dmboot - ok
17:14:01.0281 3400 dmio (7c824cf7bbde77d95c08005717a95f6f) C:\WINDOWS\system32\drivers\dmio.sys
17:14:01.0296 3400 dmio - ok
17:14:01.0328 3400 dmload (e9317282a63ca4d188c0df5e09c6ac5f) C:\WINDOWS\system32\drivers\dmload.sys
17:14:01.0343 3400 dmload - ok
17:14:01.0375 3400 dmserver (57edec2e5f59f0335e92f35184bc8631) C:\WINDOWS\System32\dmserver.dll
17:14:01.0375 3400 dmserver - ok
17:14:01.0437 3400 DMusic (8a208dfcf89792a484e76c40e5f50b45) C:\WINDOWS\system32\drivers\DMusic.sys
17:14:01.0437 3400 DMusic - ok
17:14:01.0500 3400 Dnscache (5f7e24fa9eab896051ffb87f840730d2) C:\WINDOWS\System32\dnsrslvr.dll
17:14:01.0500 3400 Dnscache - ok
17:14:01.0625 3400 Dot3svc (0f0f6e687e5e15579ef4da8dd6945814) C:\WINDOWS\System32\dot3svc.dll
17:14:01.0625 3400 Dot3svc - ok
17:14:01.0640 3400 dpti2o - ok
17:14:01.0687 3400 drmkaud (8f5fcff8e8848afac920905fbd9d33c8) C:\WINDOWS\system32\drivers\drmkaud.sys
17:14:01.0687 3400 drmkaud - ok
17:14:01.0703 3400 EapHost (2187855a7703adef0cef9ee4285182cc) C:\WINDOWS\System32\eapsvc.dll
17:14:01.0703 3400 EapHost - ok
17:14:01.0718 3400 ERSvc (bc93b4a066477954555966d77fec9ecb) C:\WINDOWS\System32\ersvc.dll
17:14:01.0718 3400 ERSvc - ok
17:14:01.0765 3400 Eventlog (65df52f5b8b6e9bbd183505225c37315) C:\WINDOWS\system32\services.exe
17:14:01.0812 3400 Eventlog - ok
17:14:01.0859 3400 EventSystem (d4991d98f2db73c60d042f1aef79efae) C:\WINDOWS\system32\es.dll
17:14:01.0875 3400 EventSystem - ok
17:14:01.0937 3400 Fastfat (38d332a6d56af32635675f132548343e) C:\WINDOWS\system32\drivers\Fastfat.sys
17:14:01.0937 3400 Fastfat - ok
17:14:02.0015 3400 FastUserSwitchingCompatibility (99bc0b50f511924348be19c7c7313bbf) C:\WINDOWS\System32\shsvcs.dll
17:14:02.0015 3400 FastUserSwitchingCompatibility - ok
17:14:02.0046 3400 Fdc (92cdd60b6730b9f50f6a1a0c1f8cdc81) C:\WINDOWS\system32\drivers\Fdc.sys
17:14:02.0046 3400 Fdc - ok
17:14:02.0046 3400 Fips (d45926117eb9fa946a6af572fbe1caa3) C:\WINDOWS\system32\drivers\Fips.sys
17:14:02.0046 3400 Fips - ok
17:14:02.0046 3400 Flpydisk (9d27e7b80bfcdf1cdd9b555862d5e7f0) C:\WINDOWS\system32\drivers\Flpydisk.sys
17:14:02.0046 3400 Flpydisk - ok
17:14:02.0078 3400 FltMgr (b2cf4b0786f8212cb92ed2b50c6db6b0) C:\WINDOWS\system32\DRIVERS\fltMgr.sys
17:14:02.0093 3400 FltMgr - ok
17:14:02.0203 3400 FontCache3.0.0.0 (8ba7c024070f2b7fdd98ed8a4ba41789) c:\WINDOWS\Microsoft.NET\Framework\v3.0\WPF\PresentationFontCache.exe
17:14:02.0218 3400 FontCache3.0.0.0 - ok
17:14:02.0281 3400 Fs_Rec (3e1e2bd4f39b0e2b7dc4f4d2bcc2779a) C:\WINDOWS\system32\drivers\Fs_Rec.sys
17:14:02.0281 3400 Fs_Rec - ok
17:14:02.0406 3400 Ftdisk (6ac26732762483366c3969c9e4d2259d) C:\WINDOWS\system32\DRIVERS\ftdisk.sys
17:14:02.0406 3400 Ftdisk - ok
17:14:02.0437 3400 GEARAspiWDM (ab8a6a87d9d7255c3884d5b9541a6e80) C:\WINDOWS\system32\Drivers\GEARAspiWDM.sys
17:14:02.0437 3400 GEARAspiWDM - ok
17:14:02.0468 3400 Gpc (0a02c63c8b144bd8c86b103dee7c86a2) C:\WINDOWS\system32\DRIVERS\msgpc.sys
17:14:02.0468 3400 Gpc - ok
17:14:02.0531 3400 HDAudBus (573c7d0a32852b48f3058cfd8026f511) C:\WINDOWS\system32\DRIVERS\HDAudBus.sys
17:14:02.0531 3400 HDAudBus - ok
17:14:02.0640 3400 helpsvc (4fcca060dfe0c51a09dd5c3843888bcd) C:\WINDOWS\PCHealth\HelpCtr\Binaries\pchsvc.dll
17:14:02.0640 3400 helpsvc - ok
17:14:02.0640 3400 HidServ - ok
17:14:02.0703 3400 hidusb (ccf82c5ec8a7326c3066de870c06daf1) C:\WINDOWS\system32\DRIVERS\hidusb.sys
17:14:02.0703 3400 hidusb - ok
17:14:02.0859 3400 hkmsvc (8878bd685e490239777bfe51320b88e9) C:\WINDOWS\System32\kmsvc.dll
17:14:02.0859 3400 hkmsvc - ok
17:14:02.0859 3400 hpn - ok
17:14:02.0921 3400 HTTP (f80a415ef82cd06ffaf0d971528ead38) C:\WINDOWS\system32\Drivers\HTTP.sys
17:14:02.0921 3400 HTTP - ok
17:14:02.0984 3400 HTTPFilter (6100a808600f44d999cebdef8841c7a3) C:\WINDOWS\System32\w3ssl.dll
17:14:02.0984 3400 HTTPFilter - ok
17:14:02.0984 3400 i2omgmt - ok
17:14:02.0984 3400 i2omp - ok
17:14:03.0000 3400 i8042prt (4a0b06aa8943c1e332520f7440c0aa30) C:\WINDOWS\system32\drivers\i8042prt.sys
17:14:03.0000 3400 i8042prt - ok
17:14:03.0062 3400 iastor (707c1692214b1c290271067197f075f6) C:\WINDOWS\system32\drivers\iastor.sys
17:14:03.0078 3400 iastor - ok
17:14:03.0203 3400 idsvc (c01ac32dc5c03076cfb852cb5da5229c) c:\WINDOWS\Microsoft.NET\Framework\v3.0\Windows Communication Foundation\infocard.exe
17:14:03.0406 3400 idsvc - ok
17:14:03.0734 3400 IJPLMSVC (a06efd4965f8a3f97a8c9a291d032678) C:\Program Files\Canon\IJPLM\IJPLMSVC.EXE
17:14:03.0734 3400 IJPLMSVC - ok
17:14:03.0796 3400 Imapi (083a052659f5310dd8b6a6cb05edcf8e) C:\WINDOWS\system32\DRIVERS\imapi.sys
17:14:03.0796 3400 Imapi - ok
17:14:03.0859 3400 ImapiService (30deaf54a9755bb8546168cfe8a6b5e1) C:\WINDOWS\system32\imapi.exe
17:14:03.0859 3400 ImapiService - ok
17:14:03.0859 3400 ini910u - ok
17:14:04.0343 3400 IntcAzAudAddService (5c8f36cdcb489111b24003af4dfe1fdc) C:\WINDOWS\system32\drivers\RtkHDAud.sys
17:14:04.0609 3400 IntcAzAudAddService - ok
17:14:04.0734 3400 IntelIde - ok
17:14:04.0843 3400 intelppm (8c953733d8f36eb2133f5bb58808b66b) C:\WINDOWS\system32\DRIVERS\intelppm.sys
17:14:04.0843 3400 intelppm - ok
17:14:04.0859 3400 Ip6Fw (3bb22519a194418d5fec05d800a19ad0) C:\WINDOWS\system32\DRIVERS\Ip6Fw.sys
17:14:04.0859 3400 Ip6Fw - ok
17:14:04.0906 3400 IpFilterDriver (731f22ba402ee4b62748adaf6363c182) C:\WINDOWS\system32\DRIVERS\ipfltdrv.sys
17:14:04.0906 3400 IpFilterDriver - ok
17:14:04.0906 3400 IpInIp (b87ab476dcf76e72010632b5550955f5) C:\WINDOWS\system32\DRIVERS\ipinip.sys
17:14:04.0906 3400 IpInIp - ok
17:14:04.0921 3400 IpNat (cc748ea12c6effde940ee98098bf96bb) C:\WINDOWS\system32\DRIVERS\ipnat.sys
17:14:04.0921 3400 IpNat - ok
17:14:04.0953 3400 IPSec (23c74d75e36e7158768dd63d92789a91) C:\WINDOWS\system32\DRIVERS\ipsec.sys
17:14:04.0953 3400 IPSec - ok
17:14:04.0953 3400 IRENUM (c93c9ff7b04d772627a3646d89f7bf89) C:\WINDOWS\system32\DRIVERS\irenum.sys
17:14:04.0968 3400 IRENUM - ok
17:14:04.0984 3400 isapnp (05a299ec56e52649b1cf2fc52d20f2d7) C:\WINDOWS\system32\DRIVERS\isapnp.sys
17:14:05.0000 3400 isapnp - ok
17:14:05.0109 3400 JavaQuickStarterService (381b25dc8e958d905b33130d500bbf29) C:\Program Files\Java\jre6\bin\jqs.exe
17:14:05.0125 3400 JavaQuickStarterService - ok
17:14:05.0140 3400 Kbdclass (463c1ec80cd17420a542b7f36a36f128) C:\WINDOWS\system32\DRIVERS\kbdclass.sys
17:14:05.0156 3400 Kbdclass - ok
17:14:05.0156 3400 kbdhid (9ef487a186dea361aa06913a75b3fa99) C:\WINDOWS\system32\DRIVERS\kbdhid.sys
17:14:05.0156 3400 kbdhid - ok
17:14:05.0218 3400 kmixer (692bcf44383d056aed41b045a323d378) C:\WINDOWS\system32\drivers\kmixer.sys
17:14:05.0218 3400 kmixer - ok
17:14:05.0265 3400 KSecDD (b467646c54cc746128904e1654c750c1) C:\WINDOWS\system32\drivers\KSecDD.sys
17:14:05.0265 3400 KSecDD - ok
17:14:05.0328 3400 LanmanServer (3a7c3cbe5d96b8ae96ce81f0b22fb527) C:\WINDOWS\System32\srvsvc.dll
17:14:05.0328 3400 LanmanServer - ok
17:14:05.0453 3400 lanmanworkstation (a8888a5327621856c0cec4e385f69309) C:\WINDOWS\System32\wkssvc.dll
17:14:05.0453 3400 lanmanworkstation - ok
17:14:05.0453 3400 lbrtfdc - ok
17:14:05.0515 3400 LmHosts (a7db739ae99a796d91580147e919cc59) C:\WINDOWS\System32\lmhsvc.dll
17:14:05.0515 3400 LmHosts - ok
17:14:05.0562 3400 MBAMProtector (fb097bbc1a18f044bd17bd2fccf97865) C:\WINDOWS\system32\drivers\mbam.sys
17:14:05.0562 3400 MBAMProtector - ok
17:14:05.0656 3400 MBAMService (ba400ed640bca1eae5c727ae17c10207) C:\Program Files\Malwarebytes' Anti-Malware\mbamservice.exe
17:14:05.0656 3400 MBAMService - ok
17:14:05.0718 3400 Messenger (986b1ff5814366d71e0ac5755c88f2d3) C:\WINDOWS\System32\msgsvc.dll
17:14:05.0718 3400 Messenger - ok
17:14:05.0750 3400 mnmdd (4ae068242760a1fb6e1a44bf4e16afa6) C:\WINDOWS\system32\drivers\mnmdd.sys
17:14:05.0750 3400 mnmdd - ok
17:14:05.0796 3400 mnmsrvc (d18f1f0c101d06a1c1adf26eed16fcdd) C:\WINDOWS\system32\mnmsrvc.exe
17:14:05.0796 3400 mnmsrvc - ok
17:14:05.0843 3400 Modem (dfcbad3cec1c5f964962ae10e0bcc8e1) C:\WINDOWS\system32\drivers\Modem.sys
17:14:05.0843 3400 Modem - ok
17:14:05.0875 3400 Mouclass (35c9e97194c8cfb8430125f8dbc34d04) C:\WINDOWS\system32\DRIVERS\mouclass.sys
17:14:05.0875 3400 Mouclass - ok
17:14:05.0906 3400 mouhid (b1c303e17fb9d46e87a98e4ba6769685) C:\WINDOWS\system32\DRIVERS\mouhid.sys
17:14:05.0906 3400 mouhid - ok
17:14:05.0937 3400 MountMgr (a80b9a0bad1b73637dbcbba7df72d3fd) C:\WINDOWS\system32\drivers\MountMgr.sys
17:14:05.0953 3400 MountMgr - ok
17:14:05.0968 3400 mraid35x - ok
17:14:06.0093 3400 MRxDAV (11d42bb6206f33fbb3ba0288d3ef81bd) C:\WINDOWS\system32\DRIVERS\mrxdav.sys
17:14:06.0125 3400 MRxDAV - ok
17:14:06.0171 3400 MSDTC (a137f1470499a205abbb9aafb3b6f2b1) C:\WINDOWS\system32\msdtc.exe
17:14:06.0187 3400 MSDTC - ok
17:14:06.0187 3400 Msfs (c941ea2454ba8350021d774daf0f1027) C:\WINDOWS\system32\drivers\Msfs.sys
17:14:06.0187 3400 Msfs - ok
17:14:06.0187 3400 MSIServer - ok
17:14:06.0218 3400 MSKSSRV (d1575e71568f4d9e14ca56b7b0453bf1) C:\WINDOWS\system32\drivers\MSKSSRV.sys
17:14:06.0234 3400 MSKSSRV - ok
17:14:06.0234 3400 MSPCLOCK (325bb26842fc7ccc1fcce2c457317f3e) C:\WINDOWS\system32\drivers\MSPCLOCK.sys
17:14:06.0234 3400 MSPCLOCK - ok
17:14:06.0234 3400 MSPQM (bad59648ba099da4a17680b39730cb3d) C:\WINDOWS\system32\drivers\MSPQM.sys
17:14:06.0234 3400 MSPQM - ok
17:14:06.0265 3400 mssmbios (af5f4f3f14a8ea2c26de30f7a1e17136) C:\WINDOWS\system32\DRIVERS\mssmbios.sys
17:14:06.0265 3400 mssmbios - ok
17:14:06.0281 3400 Mup (de6a75f5c270e756c5508d94b6cf68f5) C:\WINDOWS\system32\drivers\Mup.sys
17:14:06.0281 3400 Mup - ok
17:14:06.0328 3400 napagent (0102140028fad045756796e1c685d695) C:\WINDOWS\System32\qagentrt.dll
17:14:06.0343 3400 napagent - ok
17:14:06.0359 3400 NDIS (1df7f42665c94b825322fae71721130d) C:\WINDOWS\system32\drivers\NDIS.sys
17:14:06.0359 3400 NDIS - ok
17:14:06.0375 3400 NdisTapi (0109c4f3850dfbab279542515386ae22) C:\WINDOWS\system32\DRIVERS\ndistapi.sys
17:14:06.0375 3400 NdisTapi - ok
17:14:06.0390 3400 Ndisuio (f927a4434c5028758a842943ef1a3849) C:\WINDOWS\system32\DRIVERS\ndisuio.sys
17:14:06.0390 3400 Ndisuio - ok
17:14:06.0406 3400 NdisWan (edc1531a49c80614b2cfda43ca8659ab) C:\WINDOWS\system32\DRIVERS\ndiswan.sys
17:14:06.0406 3400 NdisWan - ok
17:14:06.0406 3400 NDProxy (9282bd12dfb069d3889eb3fcc1000a9b) C:\WINDOWS\system32\drivers\NDProxy.sys
17:14:06.0421 3400 NDProxy - ok
17:14:06.0421 3400 NetBIOS (5d81cf9a2f1a3a756b66cf684911cdf0) C:\WINDOWS\system32\DRIVERS\netbios.sys
17:14:06.0421 3400 NetBIOS - ok
17:14:06.0437 3400 NetBT (74b2b2f5bea5e9a3dc021d685551bd3d) C:\WINDOWS\system32\DRIVERS\netbt.sys
17:14:06.0437 3400 NetBT - ok
17:14:06.0453 3400 NetDDE (b857ba82860d7ff85ae29b095645563b) C:\WINDOWS\system32\netdde.exe
17:14:06.0453 3400 NetDDE - ok
17:14:06.0453 3400 NetDDEdsdm (b857ba82860d7ff85ae29b095645563b) C:\WINDOWS\system32\netdde.exe
17:14:06.0468 3400 NetDDEdsdm - ok
17:14:06.0484 3400 Netlogon (bf2466b3e18e970d8a976fb95fc1ca85) C:\WINDOWS\system32\lsass.exe
17:14:06.0500 3400 Netlogon - ok
17:14:06.0562 3400 Netman (13e67b55b3abd7bf3fe7aae5a0f9a9de) C:\WINDOWS\System32\netman.dll
17:14:06.0562 3400 Netman - ok
17:14:06.0718 3400 NetTcpPortSharing (d34612c5d02d026535b3095d620626ae) c:\WINDOWS\Microsoft.NET\Framework\v3.0\Windows Communication Foundation\SMSvcHost.exe
17:14:06.0734 3400 NetTcpPortSharing - ok
17:14:06.0734 3400 NielGfx - ok
17:14:06.0734 3400 nielprt - ok
17:14:06.0796 3400 Nla (943337d786a56729263071623bbb9de5) C:\WINDOWS\System32\mswsock.dll
17:14:06.0796 3400 Nla - ok
17:14:06.0828 3400 Npfs (3182d64ae053d6fb034f44b6def8034a) C:\WINDOWS\system32\drivers\Npfs.sys
17:14:06.0843 3400 Npfs - ok
17:14:06.0890 3400 Ntfs (78a08dd6a8d65e697c18e1db01c5cdca) C:\WINDOWS\system32\drivers\Ntfs.sys
17:14:06.0890 3400 Ntfs - ok
17:14:06.0937 3400 NtLmSsp (bf2466b3e18e970d8a976fb95fc1ca85) C:\WINDOWS\system32\lsass.exe
17:14:06.0937 3400 NtLmSsp - ok
17:14:07.0078 3400 NtmsSvc (156f64a3345bd23c600655fb4d10bc08) C:\WINDOWS\system32\ntmssvc.dll
17:14:07.0093 3400 NtmsSvc - ok
17:14:07.0125 3400 Null (73c1e1f395918bc2c6dd67af7591a3ad) C:\WINDOWS\system32\drivers\Null.sys
17:14:07.0140 3400 Null - ok
17:14:07.0171 3400 NwlnkFlt (b305f3fad35083837ef46a0bbce2fc57) C:\WINDOWS\system32\DRIVERS\nwlnkflt.sys
17:14:07.0171 3400 NwlnkFlt - ok
17:14:07.0171 3400 NwlnkFwd (c99b3415198d1aab7227f2c88fd664b9) C:\WINDOWS\system32\DRIVERS\nwlnkfwd.sys
17:14:07.0171 3400 NwlnkFwd - ok
17:14:07.0296 3400 Parport (5575faf8f97ce5e713d108c2a58d7c7c) C:\WINDOWS\system32\drivers\Parport.sys
17:14:07.0296 3400 Parport - ok
17:14:07.0296 3400 PartMgr (beb3ba25197665d82ec7065b724171c6) C:\WINDOWS\system32\drivers\PartMgr.sys
17:14:07.0296 3400 PartMgr - ok
17:14:07.0328 3400 ParVdm (70e98b3fd8e963a6a46a2e6247e0bea1) C:\WINDOWS\system32\drivers\ParVdm.sys
17:14:07.0328 3400 ParVdm - ok
17:14:07.0359 3400 PCI (a219903ccf74233761d92bef471a07b1) C:\WINDOWS\system32\DRIVERS\pci.sys
17:14:07.0390 3400 PCI - ok
17:14:07.0390 3400 PCIDump - ok
17:14:07.0390 3400 PCIIde - ok
17:14:07.0484 3400 Pcmcia (9e89ef60e9ee05e3f2eef2da7397f1c1) C:\WINDOWS\system32\drivers\Pcmcia.sys
17:14:07.0500 3400 Pcmcia - ok
17:14:07.0500 3400 PDCOMP - ok
17:14:07.0531 3400 PDFRAME - ok
17:14:07.0531 3400 PDRELI - ok
17:14:07.0531 3400 PDRFRAME - ok
17:14:07.0546 3400 perc2 - ok
17:14:07.0546 3400 perc2hib - ok
17:14:07.0625 3400 PlugPlay (65df52f5b8b6e9bbd183505225c37315) C:\WINDOWS\system32\services.exe
17:14:07.0625 3400 PlugPlay - ok
17:14:07.0625 3400 PolicyAgent (bf2466b3e18e970d8a976fb95fc1ca85) C:\WINDOWS\system32\lsass.exe
17:14:07.0625 3400 PolicyAgent - ok
17:14:07.0703 3400 PptpMiniport (efeec01b1d3cf84f16ddd24d9d9d8f99) C:\WINDOWS\system32\DRIVERS\raspptp.sys
17:14:07.0718 3400 PptpMiniport - ok
17:14:07.0718 3400 ProtectedStorage (bf2466b3e18e970d8a976fb95fc1ca85) C:\WINDOWS\system32\lsass.exe
17:14:07.0718 3400 ProtectedStorage - ok
17:14:07.0734 3400 PSched (09298ec810b07e5d582cb3a3f9255424) C:\WINDOWS\system32\DRIVERS\psched.sys
17:14:07.0734 3400 PSched - ok
17:14:07.0765 3400 Ptilink (80d317bd1c3dbc5d4fe7b1678c60cadd) C:\WINDOWS\system32\DRIVERS\ptilink.sys
17:14:07.0765 3400 Ptilink - ok
17:14:07.0781 3400 PxHelp20 (e42e3433dbb4cffe8fdd91eab29aea8e) C:\WINDOWS\system32\Drivers\PxHelp20.sys
17:14:07.0796 3400 PxHelp20 - ok
17:14:07.0796 3400 ql1080 - ok
17:14:07.0796 3400 Ql10wnt - ok
17:14:07.0796 3400 ql12160 - ok
17:14:07.0812 3400 ql1240 - ok
17:14:07.0812 3400 ql1280 - ok
17:14:07.0843 3400 RasAcd (fe0d99d6f31e4fad8159f690d68ded9c) C:\WINDOWS\system32\DRIVERS\rasacd.sys
17:14:07.0843 3400 RasAcd - ok
17:14:07.0875 3400 RasAuto (ad188be7bdf94e8df4ca0a55c00a5073) C:\WINDOWS\System32\rasauto.dll
17:14:07.0875 3400 RasAuto - ok
17:14:07.0906 3400 Rasl2tp (11b4a627bc9614b885c4969bfa5ff8a6) C:\WINDOWS\system32\DRIVERS\rasl2tp.sys
17:14:07.0906 3400 Rasl2tp - ok
17:14:07.0937 3400 RasMan (76a9a3cbeadd68cc57cda5e1d7448235) C:\WINDOWS\System32\rasmans.dll
17:14:07.0937 3400 RasMan - ok
17:14:07.0953 3400 RasPppoe (5bc962f2654137c9909c3d4603587dee) C:\WINDOWS\system32\DRIVERS\raspppoe.sys
17:14:07.0953 3400 RasPppoe - ok
17:14:07.0953 3400 Raspti (fdbb1d60066fcfbb7452fd8f9829b242) C:\WINDOWS\system32\DRIVERS\raspti.sys
17:14:07.0953 3400 Raspti - ok
17:14:07.0984 3400 Rdbss (7ad224ad1a1437fe28d89cf22b17780a) C:\WINDOWS\system32\DRIVERS\rdbss.sys
17:14:07.0984 3400 Rdbss - ok
17:14:08.0031 3400 RDPCDD (4912d5b403614ce99c28420f75353332) C:\WINDOWS\system32\DRIVERS\RDPCDD.sys
17:14:08.0031 3400 RDPCDD - ok
17:14:08.0062 3400 rdpdr (15cabd0f7c00c47c70124907916af3f1) C:\WINDOWS\system32\DRIVERS\rdpdr.sys
17:14:08.0062 3400 rdpdr - ok
17:14:08.0109 3400 RDPWD (5b3055daa788bd688594d2f5981f2a83) C:\WINDOWS\system32\drivers\RDPWD.sys
17:14:08.0125 3400 RDPWD - ok
17:14:08.0140 3400 RDSessMgr (3c37bf86641bda977c3bf8a840f3b7fa) C:\WINDOWS\system32\sessmgr.exe
17:14:08.0156 3400 RDSessMgr - ok
17:14:08.0203 3400 redbook (f828dd7e1419b6653894a8f97a0094c5) C:\WINDOWS\system32\DRIVERS\redbook.sys
17:14:08.0203 3400 redbook - ok
17:14:08.0250 3400 RemoteAccess (7e699ff5f59b5d9de5390e3c34c67cf5) C:\WINDOWS\System32\mprdim.dll
17:14:08.0250 3400 RemoteAccess - ok
17:14:08.0296 3400 RemoteRegistry (5b19b557b0c188210a56a6b699d90b8f) C:\WINDOWS\system32\regsvc.dll
17:14:08.0296 3400 RemoteRegistry - ok
17:14:08.0359 3400 RpcLocator (aaed593f84afa419bbae8572af87cf6a) C:\WINDOWS\system32\locator.exe
17:14:08.0359 3400 RpcLocator - ok
17:14:08.0515 3400 RpcSs (6b27a5c03dfb94b4245739065431322c) C:\WINDOWS\system32\rpcss.dll
17:14:08.0515 3400 RpcSs - ok
17:14:08.0578 3400 RSVP (471b3f9741d762abe75e9deea4787e47) C:\WINDOWS\system32\rsvp.exe
17:14:08.0593 3400 RSVP - ok
17:14:08.0671 3400 RTLE8023xp (7174f20ad9b7b7878a51ecca03c499c2) C:\WINDOWS\system32\DRIVERS\Rtenicxp.sys
17:14:08.0703 3400 RTLE8023xp - ok
17:14:08.0765 3400 SamSs (bf2466b3e18e970d8a976fb95fc1ca85) C:\WINDOWS\system32\lsass.exe
17:14:08.0765 3400 SamSs - ok
17:14:08.0875 3400 SASDIFSV (39763504067962108505bff25f024345) C:\Program Files\SUPERAntiSpyware\SASDIFSV.SYS
17:14:08.0875 3400 SASDIFSV - ok
17:14:08.0906 3400 SASKUTIL (77b9fc20084b48408ad3e87570eb4a85) C:\Program Files\SUPERAntiSpyware\SASKUTIL.SYS
17:14:08.0906 3400 SASKUTIL - ok
17:14:08.0953 3400 SCardSvr (86d007e7a654b9a71d1d7d856b104353) C:\WINDOWS\System32\SCardSvr.exe
17:14:08.0953 3400 SCardSvr - ok
17:14:09.0015 3400 Schedule (0a9a7365a1ca4319aa7c1d6cd8e4eafa) C:\WINDOWS\system32\schedsvc.dll
17:14:09.0015 3400 Schedule - ok
17:14:09.0046 3400 Secdrv (90a3935d05b494a5a39d37e71f09a677) C:\WINDOWS\system32\DRIVERS\secdrv.sys
17:14:09.0046 3400 Secdrv - ok
17:14:09.0109 3400 seclogon (cbe612e2bb6a10e3563336191eda1250) C:\WINDOWS\System32\seclogon.dll
17:14:09.0109 3400 seclogon - ok
17:14:09.0125 3400 SENS (7fdd5d0684eca8c1f68b4d99d124dcd0) C:\WINDOWS\system32\sens.dll
17:14:09.0125 3400 SENS - ok
17:14:09.0218 3400 serenum (0f29512ccd6bead730039fb4bd2c85ce) C:\WINDOWS\system32\DRIVERS\serenum.sys
17:14:09.0218 3400 serenum - ok
17:14:09.0281 3400 Serial (cca207a8896d4c6a0c9ce29a4ae411a7) C:\WINDOWS\system32\DRIVERS\serial.sys
17:14:09.0281 3400 Serial - ok
17:14:09.0390 3400 Sfloppy (8e6b8c671615d126fdc553d1e2de5562) C:\WINDOWS\system32\drivers\Sfloppy.sys
17:14:09.0390 3400 Sfloppy - ok
17:14:09.0484 3400 SharedAccess (83f41d0d89645d7235c051ab1d9523ac) C:\WINDOWS\System32\ipnathlp.dll
17:14:09.0484 3400 SharedAccess - ok
17:14:09.0640 3400 ShellHWDetection (99bc0b50f511924348be19c7c7313bbf) C:\WINDOWS\System32\shsvcs.dll
17:14:09.0640 3400 ShellHWDetection - ok
17:14:09.0656 3400 Simbad - ok
17:14:09.0718 3400 Sparrow - ok
17:14:09.0796 3400 splitter (ab8b92451ecb048a4d1de7c3ffcb4a9f) C:\WINDOWS\system32\drivers\splitter.sys
17:14:09.0796 3400 splitter - ok
17:14:09.0812 3400 Spooler - ok
17:14:09.0890 3400 sr (76bb022c2fb6902fd5bdd4f78fc13a5d) C:\WINDOWS\system32\DRIVERS\sr.sys
17:14:09.0890 3400 sr - ok
17:14:09.0937 3400 srservice (3805df0ac4296a34ba4bf93b346cc378) C:\WINDOWS\system32\srsvc.dll
17:14:09.0937 3400 srservice - ok
17:14:10.0000 3400 Srv (47ddfc2f003f7f9f0592c6874962a2e7) C:\WINDOWS\system32\DRIVERS\srv.sys
17:14:10.0015 3400 Srv - ok
17:14:10.0078 3400 SSDPSRV (0a5679b3714edab99e357057ee88fca6) C:\WINDOWS\System32\ssdpsrv.dll
17:14:10.0093 3400 SSDPSRV - ok
17:14:10.0140 3400 stisvc (8bad69cbac032d4bbacfce0306174c30) C:\WINDOWS\system32\wiaservc.dll
17:14:10.0156 3400 stisvc - ok
17:14:10.0203 3400 swenum (3941d127aef12e93addf6fe6ee027e0f) C:\WINDOWS\system32\DRIVERS\swenum.sys
17:14:10.0203 3400 swenum - ok
17:14:10.0281 3400 swmidi (8ce882bcc6cf8a62f2b2323d95cb3d01) C:\WINDOWS\system32\drivers\swmidi.sys
17:14:10.0281 3400 swmidi - ok
17:14:10.0296 3400 SwPrv - ok
17:14:10.0312 3400 symc810 - ok
17:14:10.0343 3400 symc8xx - ok
17:14:10.0375 3400 sym_hi - ok
17:14:10.0406 3400 sym_u3 - ok
17:14:10.0468 3400 sysaudio (8b83f3ed0f1688b4958f77cd6d2bf290) C:\WINDOWS\system32\drivers\sysaudio.sys
17:14:10.0468 3400 sysaudio - ok
17:14:10.0546 3400 SysmonLog (c7abbc59b43274b1109df6b24d617051) C:\WINDOWS\system32\smlogsvc.exe
17:14:10.0546 3400 SysmonLog - ok
17:14:10.0625 3400 TapiSrv (3cb78c17bb664637787c9a1c98f79c38) C:\WINDOWS\System32\tapisrv.dll
17:14:10.0625 3400 TapiSrv - ok
17:14:10.0796 3400 Tcpip (9aefa14bd6b182d61e3119fa5f436d3d) C:\WINDOWS\system32\DRIVERS\tcpip.sys
17:14:10.0812 3400 Tcpip - ok
17:14:10.0875 3400 TDPIPE (6471a66807f5e104e4885f5b67349397) C:\WINDOWS\system32\drivers\TDPIPE.sys
17:14:10.0875 3400 TDPIPE - ok
17:14:10.0890 3400 TDTCP (c56b6d0402371cf3700eb322ef3aaf61) C:\WINDOWS\system32\drivers\TDTCP.sys
17:14:10.0890 3400 TDTCP - ok
17:14:10.0968 3400 TermDD (88155247177638048422893737429d9e) C:\WINDOWS\system32\DRIVERS\termdd.sys
17:14:10.0968 3400 TermDD - ok
17:14:11.0015 3400 TermService (ff3477c03be7201c294c35f684b3479f) C:\WINDOWS\System32\termsrv.dll
17:14:11.0015 3400 TermService - ok
17:14:11.0093 3400 Themes (99bc0b50f511924348be19c7c7313bbf) C:\WINDOWS\System32\shsvcs.dll
17:14:11.0093 3400 Themes - ok
17:14:11.0140 3400 TlntSvr (db7205804759ff62c34e3efd8a4cc76a) C:\WINDOWS\system32\tlntsvr.exe
17:14:11.0156 3400 TlntSvr - ok
17:14:11.0171 3400 TosIde - ok
17:14:11.0218 3400 TrkWks (55bca12f7f523d35ca3cb833c725f54e) C:\WINDOWS\system32\trkwks.dll
17:14:11.0234 3400 TrkWks - ok
17:14:11.0265 3400 Udfs (5787b80c2e3c5e2f56c2a233d91fa2c9) C:\WINDOWS\system32\drivers\Udfs.sys
17:14:11.0281 3400 Udfs - ok
17:14:11.0281 3400 ultra - ok
17:14:11.0375 3400 Update (402ddc88356b1bac0ee3dd1580c76a31) C:\WINDOWS\system32\DRIVERS\update.sys
17:14:11.0390 3400 Update - ok
17:14:11.0468 3400 upnphost (1ebafeb9a3fbdc41b8d9c7f0f687ad91) C:\WINDOWS\System32\upnphost.dll
17:14:11.0515 3400 upnphost - ok
17:14:11.0578 3400 UPS (05365fb38fca1e98f7a566aaaf5d1815) C:\WINDOWS\System32\ups.exe
17:14:11.0578 3400 UPS - ok
17:14:11.0640 3400 usbccgp (173f317ce0db8e21322e71b7e60a27e8) C:\WINDOWS\system32\DRIVERS\usbccgp.sys
17:14:11.0640 3400 usbccgp - ok
17:14:11.0703 3400 usbehci (65dcf09d0e37d4c6b11b5b0b76d470a7) C:\WINDOWS\system32\DRIVERS\usbehci.sys
17:14:11.0703 3400 usbehci - ok
17:14:11.0718 3400 usbhub (1ab3cdde553b6e064d2e754efe20285c) C:\WINDOWS\system32\DRIVERS\usbhub.sys
17:14:11.0718 3400 usbhub - ok
17:14:11.0781 3400 usbprint (a717c8721046828520c9edf31288fc00) C:\WINDOWS\system32\DRIVERS\usbprint.sys
17:14:11.0781 3400 usbprint - ok
17:14:11.0812 3400 usbscan (a0b8cf9deb1184fbdd20784a58fa75d4) C:\WINDOWS\system32\DRIVERS\usbscan.sys
17:14:11.0812 3400 usbscan - ok
17:14:11.0921 3400 USBSTOR (a32426d9b14a089eaa1d922e0c5801a9) C:\WINDOWS\system32\DRIVERS\USBSTOR.SYS
17:14:11.0937 3400 USBSTOR - ok
17:14:11.0968 3400 usbuhci (26496f9dee2d787fc3e61ad54821ffe6) C:\WINDOWS\system32\DRIVERS\usbuhci.sys
17:14:11.0968 3400 usbuhci - ok
17:14:12.0015 3400 VgaSave (0d3a8fafceacd8b7625cd549757a7df1) C:\WINDOWS\System32\drivers\vga.sys
17:14:12.0015 3400 VgaSave - ok
17:14:12.0031 3400 ViaIde - ok
17:14:12.0093 3400 VolSnap (4c8fcb5cc53aab716d810740fe59d025) C:\WINDOWS\system32\drivers\VolSnap.sys
17:14:12.0093 3400 VolSnap - ok
17:14:12.0156 3400 VSS (7a9db3a67c333bf0bd42e42b8596854b) C:\WINDOWS\System32\vssvc.exe
17:14:12.0171 3400 VSS - ok
17:14:12.0390 3400 vToolbarUpdater10.2.0 (3080f1f093869a19fb3d1f0226c73809) C:\Program Files\Common Files\AVG Secure Search\vToolbarUpdater\10.2.0\ToolbarUpdater.exe
17:14:12.0390 3400 vToolbarUpdater10.2.0 - ok
17:14:12.0453 3400 W32Time (54af4b1d5459500ef0937f6d33b1914f) C:\WINDOWS\system32\w32time.dll
17:14:12.0453 3400 W32Time - ok
17:14:12.0546 3400 Wanarp (e20b95baedb550f32dd489265c1da1f6) C:\WINDOWS\system32\DRIVERS\wanarp.sys
17:14:12.0546 3400 Wanarp - ok
17:14:12.0640 3400 Wdf01000 (d918617b46457b9ac28027722e30f647) C:\WINDOWS\system32\Drivers\wdf01000.sys
17:14:12.0671 3400 Wdf01000 - ok
17:14:12.0671 3400 WDICA - ok
17:14:12.0750 3400 wdmaud (6768acf64b18196494413695f0c3a00f) C:\WINDOWS\system32\drivers\wdmaud.sys
17:14:12.0750 3400 wdmaud - ok
17:14:12.0812 3400 WebClient (77a354e28153ad2d5e120a5a8687bc06) C:\WINDOWS\System32\webclnt.dll
17:14:12.0812 3400 WebClient - ok
17:14:12.0937 3400 winmgmt (2d0e4ed081963804ccc196a0929275b5) C:\WINDOWS\system32\wbem\WMIsvc.dll
17:14:12.0937 3400 winmgmt - ok
17:14:13.0046 3400 WinUSB (fd600b032e741eb6aab509fc630f7c42) C:\WINDOWS\system32\DRIVERS\WinUSB.sys
17:14:13.0046 3400 WinUSB - ok
17:14:13.0140 3400 WmdmPmSN (c51b4a5c05a5475708e3c81c7765b71d) C:\WINDOWS\system32\MsPMSNSv.dll
17:14:13.0156 3400 WmdmPmSN - ok
17:14:13.0250 3400 Wmi (e76f8807070ed04e7408a86d6d3a6137) C:\WINDOWS\System32\advapi32.dll
17:14:13.0250 3400 Wmi - ok
17:14:13.0328 3400 WmiApSrv (e0673f1106e62a68d2257e376079f821) C:\WINDOWS\system32\wbem\wmiapsrv.exe
17:14:13.0328 3400 WmiApSrv - ok
17:14:13.0859 3400 WMPNetworkSvc (f74e3d9a7fa9556c3bbb14d4e5e63d3b) C:\Program Files\Windows Media Player\WMPNetwk.exe
17:14:13.0921 3400 WMPNetworkSvc - ok
17:14:13.0968 3400 WpdUsb (cf4def1bf66f06964dc0d91844239104) C:\WINDOWS\system32\DRIVERS\wpdusb.sys
17:14:13.0968 3400 WpdUsb - ok
17:14:14.0187 3400 WPFFontCache_v0400 (dcf3e3edf5109ee8bc02fe6e1f045795) C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\WPF\WPFFontCache_v0400.exe
17:14:14.0390 3400 WPFFontCache_v0400 - ok
17:14:14.0468 3400 wscsvc (7c278e6408d1dce642230c0585a854d5) C:\WINDOWS\system32\wscsvc.dll
17:14:14.0484 3400 wscsvc - ok
17:14:14.0578 3400 wuauserv (35321fb577cdc98ce3eb3a3eb9e4610a) C:\WINDOWS\system32\wuauserv.dll
17:14:14.0578 3400 wuauserv - ok
17:14:14.0640 3400 WudfPf (eaa6324f51214d2f6718977ec9ce0def) C:\WINDOWS\system32\DRIVERS\WudfPf.sys
17:14:14.0640 3400 WudfPf - ok
17:14:14.0687 3400 WudfRd (f91ff1e51fca30b3c3981db7d5924252) C:\WINDOWS\system32\DRIVERS\wudfrd.sys
17:14:14.0703 3400 WudfRd - ok
17:14:14.0765 3400 WudfSvc (ddee3682fe97037c45f4d7ab467cb8b6) C:\WINDOWS\System32\WUDFSvc.dll
17:14:14.0765 3400 WudfSvc - ok
17:14:14.0843 3400 WZCSVC (81dc3f549f44b1c1fff022dec9ecf30b) C:\WINDOWS\System32\wzcsvc.dll
17:14:14.0843 3400 WZCSVC - ok
17:14:14.0890 3400 xmlprov (295d21f14c335b53cb8154e5b1f892b9) C:\WINDOWS\System32\xmlprov.dll
17:14:14.0906 3400 xmlprov - ok
17:14:15.0109 3400 YahooAUService (dd0042f0c3b606a6a8b92d49afb18ad6) C:\Program Files\Yahoo!\SoftwareUpdate\YahooAUService.exe
17:14:15.0109 3400 YahooAUService - ok
17:14:15.0171 3400 zumbus - ok
17:14:15.0218 3400 MBR (0x1B8) (faee7e40dfb0440ad2cfc39befa1f4c2) \Device\Harddisk0\DR0
17:14:15.0250 3400 \Device\Harddisk0\DR0 ( Rootkit.Boot.Pihar.b ) - infected
17:14:15.0250 3400 \Device\Harddisk0\DR0 - detected Rootkit.Boot.Pihar.b (0)
17:14:15.0296 3400 Boot (0x1200) (5d06483c9859f3fe074fb62bcbbbc890) \Device\Harddisk0\DR0\Partition0
17:14:15.0296 3400 \Device\Harddisk0\DR0\Partition0 - ok
17:14:15.0296 3400 ============================================================
17:14:15.0296 3400 Scan finished
17:14:15.0296 3400 ============================================================
17:14:15.0343 3076 Detected object count: 1
17:14:15.0343 3076 Actual detected object count: 1
17:14:45.0671 3076 \Device\Harddisk0\DR0\# - copied to quarantine
17:14:45.0671 3076 \Device\Harddisk0\DR0 - copied to quarantine
17:14:45.0703 3076 \Device\Harddisk0\DR0\TDLFS\phm - copied to quarantine
17:14:45.0718 3076 \Device\Harddisk0\DR0\TDLFS\ph.dll - copied to quarantine
17:14:45.0718 3076 \Device\Harddisk0\DR0\TDLFS\phx.dll - copied to quarantine
17:14:45.0718 3076 \Device\Harddisk0\DR0\TDLFS\sub.dll - copied to quarantine
17:14:45.0734 3076 \Device\Harddisk0\DR0\TDLFS\subx.dll - copied to quarantine
17:14:45.0750 3076 \Device\Harddisk0\DR0\TDLFS\phd - copied to quarantine
17:14:45.0765 3076 \Device\Harddisk0\DR0\TDLFS\phdx - copied to quarantine
17:14:45.0765 3076 \Device\Harddisk0\DR0\TDLFS\phs - copied to quarantine
17:14:45.0765 3076 \Device\Harddisk0\DR0\TDLFS\phdata - copied to quarantine
17:14:45.0765 3076 \Device\Harddisk0\DR0\TDLFS\phld - copied to quarantine
17:14:45.0781 3076 \Device\Harddisk0\DR0\TDLFS\phln - copied to quarantine
17:14:45.0781 3076 \Device\Harddisk0\DR0\TDLFS\phlx - copied to quarantine
17:14:45.0828 3076 \Device\Harddisk0\DR0 ( Rootkit.Boot.Pihar.b ) - will be cured on reboot
17:14:45.0828 3076 \Device\Harddisk0\DR0 - ok
17:14:45.0828 3076 \Device\Harddisk0\DR0 ( Rootkit.Boot.Pihar.b ) - User select action: Cure
17:14:49.0703 0712 Deinitialize success
I am getting ready to do the GMER log.
Edited by pmatthew876, 15 May 2012 - 11:01 AM.

 This topic is locked
This topic is locked



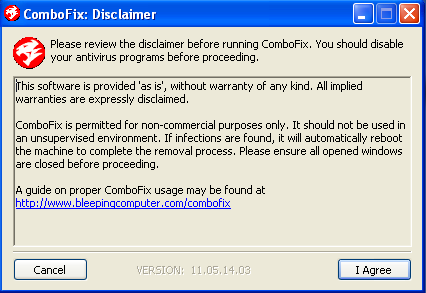
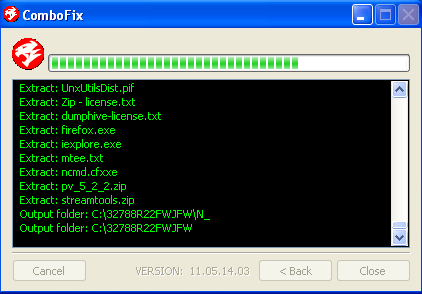











 Sign In
Sign In Create Account
Create Account

