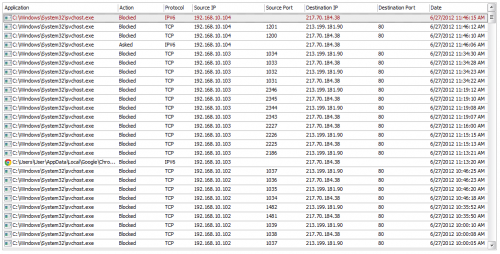
Some of it seems to be IPV6 traffic? Strange, some sort of IPV4 tunneling possibly? Also, ignore 213.199.181.90, I'm just blocking Microsoft.
Anyway, I did multiple malware scans (malwarebytes, spybot, super-antispyware, Dr. Web, Gmer) and never found a thing. I also re-imaged my entire system HDD to 3 weeks ago, but the exact same behavior occurs (And it never did so previously). So time to dig deeper...
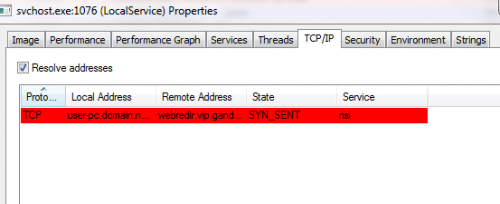
Using TCP View I found the Svchost process attempting the connection. I then moved on to Process Monitor to track the PID and found that the service NIS (Network Store Interface Service) is initiating the connection.
So that doesn't help much.
So I fired up Wireshark. Following the TCP traffic I originally got nothing, but then I gave up and decided to let the connection through. Managed to follow those packets and I got:
GET /wpad.dat HTTP/1.1Connection: Keep-AliveAccept: */*Host: 217.70.184.38HTTP/1.1 404 Not FoundServer: BaseHTTP/0.3 Python/2.6.6Content-type: text/htmlVary: HostContent-Length: 384Accept-Ranges: bytesDate: Wed, 27 Jun 2012 11:21:03 GMTAge: 0Via: 1.1 varnishConnection: close<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.1//EN"
"http://www.w3.org/TR...D/xhtml11.dtd">
<html xmlns="http://www.w3.org/1999/xhtml" xml:lang="en">
<head>
<meta http-equiv="Content-Type" content="text/HTML; charset=iso-8859-15" />
<title>404 Not Found</title>
</head>
<body>
<h1>Not Found</h1>
<p>Nothing matches the given URI</p>
</body>
</html>
This is supposed to be hosted at 217.70.184.38/wpad.dat. Going to this page results in a 404 error just as seen in the HTML from wireshark.
Attached are screenshots from Process Monitor and my Comodo firewall log. Any ideas?















 Sign In
Sign In Create Account
Create Account

