Massive Sality executable file infection [Solved]
#1
![Massive Sality executable file infection [Solved]: post #1](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 September 2012 - 05:04 AM
Posted 08 September 2012 - 05:04 AM

#2
![Massive Sality executable file infection [Solved]: post #2](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 08 September 2012 - 06:04 AM
Posted 08 September 2012 - 06:04 AM

Download Sality Killer zip to your desktop and extract SalityKiller.exe
Run the utility SalityKiller.exe on the infected computer
A reboot might require after disinfection.
Download the file Sality_RegKeys.zip
unpack the file Sality_RegKeys.zip
run the file Disable_autorun.reg from the archive Sality_RegKeys.zip
Once the scan is over, from the archive Sality_RegKeys.zip run the file of the registry key:
under Windows 2000 run the registry file SafeBootWin200.reg
under Windows XP run the registry file SafeBootWinXP.reg
under Windows 2003 run the registry file SafeBootWinServer2003.reg
under Windows Vista / 2008 run the registry file SafebootVista.reg
under Windows 7 / 2008 R2 run the registry file SafebootWin7.reg
THEN
Download OTL to your Desktop
- Double click on the icon to run it. Make sure all other windows are closed and to let it run uninterrupted.

- Select All Users
- Under the Custom Scan box paste this in
netsvcs
BASESERVICES
%SYSTEMDRIVE%\*.exe
/md5start
services.*
explorer.exe
winlogon.exe
Userinit.exe
svchost.exe
qmgr.dll
/md5stop
%systemdrive%\$Recycle.Bin|@;true;true;true
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\BITS /s
CREATERESTOREPOINT - Click the Quick Scan button. Do not change any settings unless otherwise told to do so. The scan wont take long.
- When the scan completes, it will open two notepad windows. OTL.Txt and Extras.Txt. These are saved in the same location as OTL.
- Post both logs
FINALLY
Download aswMBR.exe ( 4.8mb ) to your desktop.
Double click the aswMBR.exe to run it Click the "Scan" button to start scan

On completion of the scan click save log, save it to your desktop and post in your next reply

#3
![Massive Sality executable file infection [Solved]: post #3](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2012 - 12:21 AM
Posted 09 September 2012 - 12:21 AM

OTL logfile created on: 9/9/2012 1:49:39 AM - Run 1
OTL by OldTimer - Version 3.2.61.2 Folder = C:\Users\joeniqua c\Downloads
64bit- Home Premium Edition Service Pack 1 (Version = 6.1.7601) - Type = NTWorkstation
Internet Explorer (Version = 9.0.8112.16421)
Locale: 00000409 | Country: United States | Language: ENU | Date Format: M/d/yyyy
2.75 Gb Total Physical Memory | 1.52 Gb Available Physical Memory | 55.32% Memory free
5.49 Gb Paging File | 4.07 Gb Available in Paging File | 74.05% Paging File free
Paging file location(s): ?:\pagefile.sys [binary data]
%SystemDrive% = C: | %SystemRoot% = C:\Windows | %ProgramFiles% = C:\Program Files (x86)
Drive C: | 136.95 Gb Total Space | 31.90 Gb Free Space | 23.30% Space Free | Partition Type: NTFS
Computer Name: OWNER-PC | User Name: joeniqua c | Logged in as Administrator.
Boot Mode: Normal | Scan Mode: All users | Quick Scan | Include 64bit Scans
Company Name Whitelist: On | Skip Microsoft Files: On | No Company Name Whitelist: On | File Age = 30 Days
========== Processes (SafeList) ==========
PRC - [2012/09/09 01:44:03 | 000,599,552 | ---- | M] (OldTimer Tools) -- C:\Users\joeniqua c\Downloads\OTL.exe
PRC - [2012/08/10 18:59:52 | 004,440,896 | ---- | M] (Akamai Technologies, Inc.) -- C:\Users\joeniqua c\AppData\Local\Akamai\netsession_win.exe
PRC - [2012/08/02 21:16:04 | 000,408,944 | ---- | M] (AnchorFree Inc.) -- C:\Program Files (x86)\Hotspot Shield\HssWPR\hsssrv.exe
PRC - [2012/08/02 21:12:18 | 000,387,440 | ---- | M] () -- C:\Program Files (x86)\Hotspot Shield\bin\hsswd.exe
PRC - [2012/08/02 21:10:40 | 000,476,016 | ---- | M] () -- C:\Program Files (x86)\Hotspot Shield\bin\openvpnas.exe
PRC - [2012/07/09 22:57:46 | 001,240,944 | ---- | M] () -- C:\Program Files (x86)\Hotspot Shield\bin\openvpntray.exe
PRC - [2012/03/07 15:40:34 | 000,913,144 | ---- | M] (ESET) -- C:\Program Files\ESET\ESET Smart Security\x86\ekrn.exe
PRC - [2009/09/10 09:42:46 | 000,305,448 | ---- | M] (Egis Technology Inc.) -- C:\Program Files (x86)\EgisTec\MyWinLocker 3\x86\MWLService.exe
PRC - [2009/08/28 05:38:58 | 001,150,496 | ---- | M] (Acer Incorporated) -- C:\Program Files (x86)\Acer\Registration\GregHSRW.exe
PRC - [2009/07/03 22:47:12 | 000,240,160 | ---- | M] (Acer) -- C:\Program Files\Acer\Acer Updater\UpdaterService.exe
========== Modules (No Company Name) ==========
MOD - [2012/08/02 21:19:06 | 000,009,584 | ---- | M] () -- C:\Program Files (x86)\Hotspot Shield\bin\lang\gui-eng.dll
MOD - [2012/07/09 22:57:46 | 001,240,944 | ---- | M] () -- C:\Program Files (x86)\Hotspot Shield\bin\openvpntray.exe
========== Services (SafeList) ==========
SRV:64bit: - [2012/05/21 13:20:02 | 000,059,904 | ---- | M] (Drive Headquarter) [Auto | Running] -- C:\Program Files\DriveHQ\DriveHQ FileManager\DHQFMSvc.exe -- (FileManagerFun)
SRV:64bit: - [2012/03/07 15:40:34 | 000,913,144 | ---- | M] (ESET) [Auto | Running] -- C:\Program Files\ESET\ESET Smart Security\x86\ekrn.exe -- (ekrn)
SRV:64bit: - [2011/08/24 18:52:40 | 000,130,392 | ---- | M] (Microsoft Corporation) [Auto | Stopped] -- C:\Program Files\Microsoft Visual Studio 11.0\Common7\IDE\Remote Debugger\x64\rdbgservice.exe -- (msvsmon110)
SRV:64bit: - [2011/06/17 09:30:54 | 000,094,480 | ---- | M] (SANDBOXIE L.T.D) [Auto | Running] -- C:\Program Files\Sandboxie\SbieSvc.exe -- (SbieSvc)
SRV:64bit: - [2009/10/29 15:10:02 | 000,844,320 | ---- | M] (Acer Incorporated) [Auto | Running] -- C:\Program Files\Acer\Acer ePower Management\ePowerSvc.exe -- (ePowerSvc)
SRV:64bit: - [2009/07/29 08:03:42 | 000,203,264 | ---- | M] (AMD) [Auto | Running] -- C:\Windows\SysNative\atiesrxx.exe -- (AMD External Events Utility)
SRV:64bit: - [2009/07/13 21:41:27 | 001,011,712 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Program Files\Windows Defender\MpSvc.dll -- (WinDefend)
SRV:64bit: - [2009/07/03 22:47:12 | 000,240,160 | ---- | M] (Acer) [Auto | Running] -- C:\Program Files\Acer\Acer Updater\UpdaterService.exe -- (Updater Service)
SRV - [2012/08/30 16:07:15 | 004,537,664 | ---- | M] () [Auto | Running] -- c:\program files (x86)\common files\akamai/netsession_win_5891ae0.dll -- (Akamai)
SRV - [2012/08/02 21:20:24 | 000,078,072 | ---- | M] () [On_Demand | Stopped] -- C:\Program Files (x86)\Hotspot Shield\bin\HSSTrayService.exe -- (HssTrayService)
SRV - [2012/08/02 21:16:04 | 000,408,944 | ---- | M] (AnchorFree Inc.) [Auto | Running] -- C:\Program Files (x86)\Hotspot Shield\HssWPR\hsssrv.exe -- (HssSrv)
SRV - [2012/08/02 21:12:18 | 000,387,440 | ---- | M] () [Auto | Running] -- C:\Program Files (x86)\Hotspot Shield\bin\hsswd.exe -- (HssWd)
SRV - [2012/08/02 21:10:40 | 000,476,016 | ---- | M] () [Auto | Running] -- C:\Program Files (x86)\Hotspot Shield\bin\openvpnas.exe -- (hshld)
SRV - [2012/07/11 21:58:51 | 000,529,232 | ---- | M] (Valve Corporation) [On_Demand | Stopped] -- C:\Program Files (x86)\Common Files\Steam\SteamService.exe -- (Steam Client Service)
SRV - [2012/07/08 21:14:59 | 000,729,600 | ---- | M] (Aprelium) [Auto | Stopped] -- C:\Abyss Web Server\abyssws.exe -- (AbyssWebServer)
SRV - [2012/06/07 19:12:14 | 000,160,944 | R--- | M] (Skype Technologies) [Auto | Stopped] -- C:\Program Files (x86)\Skype\Updater\Updater.exe -- (SkypeUpdate)
SRV - [2012/03/19 07:38:47 | 002,666,880 | ---- | M] (TeamViewer GmbH) [Auto | Stopped] -- C:\Program Files (x86)\TeamViewer\Version7\TeamViewer_Service.exe -- (TeamViewer7)
SRV - [2012/02/23 23:51:10 | 000,099,840 | ---- | M] (PostgreSQL Global Development Group) [Auto | Stopped] -- C:\metasploit\postgresql\bin\pg_ctl.exe -- (metasploitPostgreSQL)
SRV - [2012/02/16 12:31:01 | 000,070,239 | ---- | M] (http://www.ruby-lang.org/) [Auto | Stopped] -- C:\metasploit\ruby\bin\ruby.exe -- (metasploitThin)
SRV - [2012/02/16 12:31:01 | 000,070,239 | ---- | M] (http://www.ruby-lang.org/) [Auto | Stopped] -- C:\metasploit\ruby\bin\ruby.exe -- (metasploitProSvc)
SRV - [2010/06/25 13:07:20 | 000,117,264 | ---- | M] (CACE Technologies, Inc.) [On_Demand | Stopped] -- C:\Program Files (x86)\WinPcap\rpcapd.exe -- (rpcapd)
SRV - [2010/03/18 14:16:28 | 000,130,384 | ---- | M] (Microsoft Corporation) [Auto | Stopped] -- C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -- (clr_optimization_v4.0.30319_32)
SRV - [2009/09/10 09:42:46 | 000,305,448 | ---- | M] () [Auto | Running] -- C:\Program Files (x86)\EgisTec\MyWinLocker 3\x86\\MWLService.exe -- (MWLService)
SRV - [2009/08/28 05:38:58 | 001,150,496 | ---- | M] (Acer Incorporated) [Auto | Running] -- C:\Program Files (x86)\Acer\Registration\GregHSRW.exe -- (Greg_Service)
SRV - [2009/06/10 17:23:09 | 000,066,384 | ---- | M] (Microsoft Corporation) [Disabled | Stopped] -- C:\Windows\Microsoft.NET\Framework\v2.0.50727\mscorsvw.exe -- (clr_optimization_v2.0.50727_32)
========== Driver Services (SafeList) ==========
DRV:64bit: - [2012/08/10 21:55:48 | 000,560,184 | ---- | M] (Duplex Secure Ltd.) [Kernel | Boot | Running] -- C:\Windows\SysNative\drivers\sptd.sys -- (sptd)
DRV:64bit: - [2012/07/09 22:48:18 | 000,041,704 | ---- | M] (AnchorFree Inc.) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\hssdrv6.sys -- (HssDRV6)
DRV:64bit: - [2012/06/05 16:03:52 | 000,147,288 | ---- | M] (Oracle Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\VBoxNetAdp.sys -- (VBoxNetAdp)
DRV:64bit: - [2012/03/26 17:45:14 | 000,037,888 | ---- | M] (AnchorFree Inc) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\taphss.sys -- (taphss)
DRV:64bit: - [2012/03/14 08:40:04 | 000,187,632 | ---- | M] (ESET) [Kernel | Auto | Running] -- C:\Windows\SysNative\drivers\epfw.sys -- (epfw)
DRV:64bit: - [2012/03/14 08:40:04 | 000,062,496 | ---- | M] (ESET) [Kernel | Boot | Running] -- C:\Windows\SysNative\drivers\epfwwfp.sys -- (epfwwfp)
DRV:64bit: - [2012/03/14 08:40:04 | 000,038,288 | ---- | M] (ESET) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\EpfwLWF.sys -- (EpfwLWF)
DRV:64bit: - [2012/03/14 08:40:02 | 000,209,768 | ---- | M] (ESET) [File_System | System | Running] -- C:\Windows\SysNative\drivers\eamonm.sys -- (eamonm)
DRV:64bit: - [2012/03/14 08:40:02 | 000,148,528 | ---- | M] (ESET) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\ehdrv.sys -- (ehdrv)
DRV:64bit: - [2012/03/01 02:46:16 | 000,023,408 | ---- | M] (Microsoft Corporation) [Recognizer | Boot | Unknown] -- C:\Windows\SysNative\drivers\fs_rec.sys -- (Fs_Rec)
DRV:64bit: - [2011/09/05 11:56:38 | 002,156,872 | ---- | M] (TamoSoft) [CommView] Atheros AR5008 Wireless Network Adapter Service 7.7 [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\ts_athwx.sys -- (TS_AR5416)
DRV:64bit: - [2011/06/17 09:30:50 | 000,154,752 | ---- | M] (SANDBOXIE L.T.D) [Kernel | On_Demand | Running] -- C:\Program Files\Sandboxie\SbieDrv.sys -- (SbieDrv)
DRV:64bit: - [2011/03/11 02:41:12 | 000,107,904 | ---- | M] (Advanced Micro Devices) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\amdsata.sys -- (amdsata)
DRV:64bit: - [2011/03/11 02:41:12 | 000,027,008 | ---- | M] (Advanced Micro Devices) [Kernel | Boot | Running] -- C:\Windows\SysNative\drivers\amdxata.sys -- (amdxata)
DRV:64bit: - [2011/02/11 17:23:34 | 000,035,344 | ---- | M] (CACE Technologies, Inc.) [Kernel | Auto | Running] -- C:\Windows\SysNative\drivers\npf.sys -- (npf)
DRV:64bit: - [2010/11/20 09:33:35 | 000,078,720 | ---- | M] (Hewlett-Packard Company) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\HpSAMD.sys -- (HpSAMD)
DRV:64bit: - [2010/11/20 07:07:05 | 000,059,392 | ---- | M] (Microsoft Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\TsUsbFlt.sys -- (TsUsbFlt)
DRV:64bit: - [2009/10/04 21:34:00 | 001,542,656 | ---- | M] (Atheros Communications, Inc.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\athrx.sys -- (athr)
DRV:64bit: - [2009/07/29 18:11:24 | 006,038,016 | ---- | M] (ATI Technologies Inc.) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\atikmdag.sys -- (atikmdag)
DRV:64bit: - [2009/07/27 03:04:36 | 000,058,880 | ---- | M] (Atheros Communications, Inc.) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\L1C62x64.sys -- (L1C)
DRV:64bit: - [2009/07/13 21:52:20 | 000,194,128 | ---- | M] (AMD Technologies Inc.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\amdsbs.sys -- (amdsbs)
DRV:64bit: - [2009/07/13 21:48:04 | 000,065,600 | ---- | M] (LSI Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\lsi_sas2.sys -- (LSI_SAS2)
DRV:64bit: - [2009/07/13 21:45:55 | 000,024,656 | ---- | M] (Promise Technology) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\stexstor.sys -- (stexstor)
DRV:64bit: - [2009/06/18 08:12:32 | 000,272,432 | ---- | M] (Synaptics Incorporated) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\SynTP.sys -- (SynTP)
DRV:64bit: - [2009/06/10 16:34:33 | 003,286,016 | ---- | M] (Broadcom Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\evbda.sys -- (ebdrv)
DRV:64bit: - [2009/06/10 16:34:28 | 000,468,480 | ---- | M] (Broadcom Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\bxvbda.sys -- (b06bdrv)
DRV:64bit: - [2009/06/10 16:34:23 | 000,270,848 | ---- | M] (Broadcom Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\b57nd60a.sys -- (b57nd60a)
DRV:64bit: - [2009/06/10 16:31:59 | 000,031,232 | ---- | M] (Hauppauge Computer Works, Inc.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\hcw85cir.sys -- (hcw85cir)
DRV:64bit: - [2009/06/02 07:15:30 | 000,060,464 | ---- | M] (Egis Technology Inc.) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\mwlPSDVDisk.sys -- (mwlPSDVDisk)
DRV:64bit: - [2009/06/02 07:15:30 | 000,022,576 | ---- | M] (Egis Technology Inc.) [File_System | System | Running] -- C:\Windows\SysNative\drivers\mwlPSDFilter.sys -- (mwlPSDFilter)
DRV:64bit: - [2009/06/02 07:15:30 | 000,020,016 | ---- | M] (Egis Technology Inc.) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\mwlPSDNserv.sys -- (mwlPSDNServ)
DRV:64bit: - [2009/05/05 04:46:08 | 000,018,432 | ---- | M] (NewTech Infosystems, Inc.) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\NTIDrvr.sys -- (NTIDrvr)
DRV:64bit: - [2009/05/05 04:46:08 | 000,016,896 | ---- | M] (NewTech Infosystems Corporation) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\UBHelper.sys -- (UBHelper)
DRV:64bit: - [2009/05/04 09:30:28 | 000,016,440 | ---- | M] (Advanced Micro Devices Inc.) [Kernel | Boot | Running] -- C:\Windows\SysNative\drivers\AtiPcie.sys -- (AtiPcie)
DRV:64bit: - [2009/04/03 10:39:58 | 000,034,872 | ---- | M] (Advanced Micro Devices) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\usbfilter.sys -- (usbfilter)
DRV - [2009/07/13 21:19:10 | 000,019,008 | ---- | M] (Microsoft Corporation) [File_System | On_Demand | Stopped] -- C:\Windows\SysWOW64\drivers\wimmount.sys -- (WIMMount)
DRV - [2009/03/25 23:16:08 | 000,025,608 | ---- | M] (Dritek System Inc.) [Kernel | On_Demand | Running] -- C:\Windows\SysWOW64\drivers\DKbFltr.sys -- (DKbFltr)
========== Standard Registry (SafeList) ==========
========== Internet Explorer ==========
IE:64bit: - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Default_Page_URL = http://homepage.acer...44z125t49n2x228
IE:64bit: - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Start Page = http://homepage.acer...44z125t49n2x228
IE:64bit: - HKLM\..\SearchScopes,DefaultScope = {6A1806CD-94D4-4689-BA73-E35EA1EA9990}
IE:64bit: - HKLM\..\SearchScopes\{0633EE93-D776-472f-A0FF-E1416B8B2E3A}: "URL" = http://www.bing.com/...ms}&FORM=IE8SRC
IE:64bit: - HKLM\..\SearchScopes\{6A1806CD-94D4-4689-BA73-E35EA1EA9990}: "URL" = http://www.google.co...g}&sourceid=ie7
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Default_Page_URL = http://homepage.acer...44z125t49n2x228
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Local Page = C:\Windows\SysWOW64\blank.htm
IE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Start Page = http://homepage.acer...44z125t49n2x228
IE - HKLM\..\URLSearchHook: {687578b9-7132-4a7a-80e4-30ee31099e03} - C:\Program Files (x86)\uTorrentControl2\prxtbuTor.dll (Conduit Ltd.)
IE - HKLM\..\URLSearchHook: {97bceb59-cfcd-4b16-a863-b3f72cf9f196} - SOFTWARE\Classes\CLSID\{97bceb59-cfcd-4b16-a863-b3f72cf9f196}\InprocServer32 File not found
IE - HKLM\..\URLSearchHook: {bf7380fa-e3b4-4db2-af3e-9d8783a45bfc} - C:\Program Files (x86)\uTorrentBar\prxtbuTor.dll (Conduit Ltd.)
IE - HKLM\..\SearchScopes,DefaultScope = {6A1806CD-94D4-4689-BA73-E35EA1EA9990}
IE - HKLM\..\SearchScopes\{0633EE93-D776-472f-A0FF-E1416B8B2E3A}: "URL" = http://www.bing.com/...ms}&FORM=IE8SRC
IE - HKLM\..\SearchScopes\{67A2568C-7A0A-4EED-AECC-B5405DE63B64}: "URL" = http://www.google.co...ng}&rlz=1I7ACAW
IE - HKLM\..\SearchScopes\{6A1806CD-94D4-4689-BA73-E35EA1EA9990}: "URL" = http://www.google.co...g}&sourceid=ie7
IE - HKLM\..\SearchScopes\{8A96AF9E-4074-43b7-BEA3-87217BDA7406}: "URL" = http://www.searchqu....q={searchTerms}
IE - HKLM\..\SearchScopes\{ac2e4ae7-2d16-45ea-991c-2441dfd05696}: "URL" = http://search.mywebs...r={searchTerms}
IE - HKLM\..\SearchScopes\{afdbddaa-5d3f-42ee-b79c-185a7020515b}: "URL" = http://search.condui...&ctid=CT2786678
IE - HKU\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyEnable" = 0
IE - HKU\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyOverride" = 127.0.0.1:9421;<local>
IE - HKU\S-1-5-18\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyEnable" = 0
IE - HKU\S-1-5-18\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyOverride" = 127.0.0.1:9421;<local>
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\SOFTWARE\Microsoft\Internet Explorer\Main,Default_Page_URL = http://homepage.acer...44z125t49n2x228
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\SOFTWARE\Microsoft\Internet Explorer\Main,Start Page = http://www.google.com/
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\SOFTWARE\Microsoft\Internet Explorer\Main,Start Page Restore = http://flamesofrage....mesofrage&gid=0
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\URLSearchHook: {687578b9-7132-4a7a-80e4-30ee31099e03} - C:\Program Files (x86)\uTorrentControl2\prxtbuTor.dll (Conduit Ltd.)
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\URLSearchHook: {bf7380fa-e3b4-4db2-af3e-9d8783a45bfc} - C:\Program Files (x86)\uTorrentBar\prxtbuTor.dll (Conduit Ltd.)
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes,DefaultScope = {0ECDF796-C2DC-4d79-A620-CCE0C0A66CC9}
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes\{0633EE93-D776-472f-A0FF-E1416B8B2E3A}: "URL" = http://www.bing.com/...Box&FORM=IE8SRC
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes\{0ECDF796-C2DC-4d79-A620-CCE0C0A66CC9}: "URL" = http://search.babylo...000701a04849685
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes\{67A2568C-7A0A-4EED-AECC-B5405DE63B64}: "URL" = http://www.google.co...ng}&rlz=1I7ACAW
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes\{6A1806CD-94D4-4689-BA73-E35EA1EA9990}: "URL" = http://www.google.co...&rlz=1I7ACAW_en
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes\{95B7759C-8C7F-4BF1-B163-73684A933233}: "URL" = https://isearch.avg....pr&d=2012-09-06 10:17:19&v=12.2.0.5&sap=dsp&q={searchTerms}
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes\{ac2e4ae7-2d16-45ea-991c-2441dfd05696}: "URL" = http://search.mywebs...r={searchTerms}
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes\{CE1648DA-1CFD-4108-ABD9-DBF5C0051A4A}: "URL" = http://www.youtube.c...y={searchTerms}
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyEnable" = 0
IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyOverride" = 127.0.0.1:9421;<local>
========== FireFox ==========
FF - prefs.js..browser.search.defaultenginename: "Search the web (Babylon)"
FF - prefs.js..browser.search.defaultthis.engineName: "uTorrentControl2 Customized Web Search"
FF - prefs.js..browser.search.defaulturl: "http://search.condui...={searchTerms}"
FF - prefs.js..browser.search.order.1: "Search the web (Babylon)"
FF - prefs.js..browser.search.selectedEngine: "Google"
FF - prefs.js..browser.search.useDBForOrder: true
FF - prefs.js..browser.startup.homepage: "http://www.google.com"
FF - prefs.js..extensions.enabledAddons: [email protected]:1.20.00
FF - prefs.js..extensions.enabledAddons: {EB9394A3-4AD6-4918-9537-31A1FD8E8EDF}:2.0
FF - prefs.js..extensions.enabledAddons: {bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}:3.15.1.0
FF - prefs.js..extensions.enabledAddons: {687578b9-7132-4a7a-80e4-30ee31099e03}:3.15.1.0
FF - prefs.js..extensions.enabledAddons: {8f8fe09b-0bd3-4470-bc1b-8cad42b8203a}:0.17
FF - prefs.js..extensions.enabledAddons: [email protected]:1.1
FF - prefs.js..extensions.enabledAddons: [email protected]:0.83.32
FF - prefs.js..extensions.enabledAddons: [email protected]:0.6.20120813
FF - prefs.js..extensions.enabledItems: [email protected]:1.2
FF - prefs.js..extensions.enabledItems: {bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}:3.5.0.12
FF - prefs.js..keyword.URL: "http://search.condui...rchSource=2&q="
FF:64bit: - HKLM\Software\MozillaPlugins\@microsoft.com/GENUINE: disabled File not found
FF:64bit: - HKLM\Software\MozillaPlugins\@Microsoft.com/NpCtrl,version=1.0: c:\Program Files\Microsoft Silverlight\5.1.10411.0\npctrl.dll ( Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@adobe.com/FlashPlayer: C:\Windows\SysWOW64\Macromed\Flash\NPSWF32.dll ()
FF - HKLM\Software\MozillaPlugins\@java.com/DTPlugin,version=1.6.0_33: C:\Windows\SysWOW64\npdeployJava1.dll (Sun Microsystems, Inc.)
FF - HKLM\Software\MozillaPlugins\@java.com/JavaPlugin: C:\Program Files (x86)\Java\jre6\bin\plugin2\npjp2.dll (Sun Microsystems, Inc.)
FF - HKLM\Software\MozillaPlugins\@microsoft.com/GENUINE: disabled File not found
FF - HKLM\Software\MozillaPlugins\@Microsoft.com/NpCtrl,version=1.0: c:\Program Files (x86)\Microsoft Silverlight\5.1.10411.0\npctrl.dll ( Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@microsoft.com/WLPG,version=14.0.8117.0416: C:\Program Files (x86)\Windows Live\Photo Gallery\NPWLPG.dll (Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@pandonetworks.com/PandoWebPlugin: C:\Program Files (x86)\Pando Networks\Media Booster\npPandoWebPlugin.dll File not found
FF - HKLM\Software\MozillaPlugins\@raidcall.com/RCplugin: C:\Users\joeniqua c\AppData\LocalLow\raidcall\plugins\webplugin.dll (Raidcall)
FF - HKLM\Software\MozillaPlugins\@tools.google.com/Google Update;version=3: C:\Program Files (x86)\Google\Update\1.3.21.115\npGoogleUpdate3.dll (Google Inc.)
FF - HKLM\Software\MozillaPlugins\@tools.google.com/Google Update;version=9: C:\Program Files (x86)\Google\Update\1.3.21.115\npGoogleUpdate3.dll (Google Inc.)
FF - HKCU\Software\MozillaPlugins\pandonetworks.com/PandoWebPlugin: C:\Program Files (x86)\Pando Networks\Media Booster\npPandoWebPlugin.dll File not found
64bit-FF - HKEY_LOCAL_MACHINE\software\mozilla\Thunderbird\Extensions\\[email protected]: C:\PROGRAM FILES\ESET\ESET SMART SECURITY\MOZILLA THUNDERBIRD [2012/09/07 07:39:21 | 000,000,000 | ---D | M]
FF - HKEY_LOCAL_MACHINE\software\mozilla\Firefox\Extensions\\[email protected]: C:\Users\joeniqua c\AppData\Roaming\2YourFace\ffextension [2012/06/19 22:25:45 | 000,000,000 | ---D | M]
FF - HKEY_LOCAL_MACHINE\software\mozilla\Mozilla Firefox 14.0.1\extensions\\Components: C:\Program Files (x86)\Mozilla Firefox\components [2012/07/18 17:24:15 | 000,000,000 | ---D | M]
FF - HKEY_LOCAL_MACHINE\software\mozilla\Mozilla Firefox 14.0.1\extensions\\Plugins: C:\Program Files (x86)\Mozilla Firefox\plugins
FF - HKEY_LOCAL_MACHINE\software\mozilla\Thunderbird\Extensions\\[email protected]: C:\Program Files\ESET\ESET Smart Security\Mozilla Thunderbird [2012/09/07 07:39:21 | 000,000,000 | ---D | M]
FF - HKEY_CURRENT_USER\software\mozilla\Firefox\Extensions\\[email protected]: C:\Users\joeniqua c\AppData\Roaming\2YourFace\ffextension [2012/06/19 22:25:45 | 000,000,000 | ---D | M]
[2011/07/29 22:32:48 | 000,000,000 | ---D | M] (No name found) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Extensions
[2012/09/07 04:19:55 | 000,000,000 | ---D | M] (No name found) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions
[2012/08/29 16:08:56 | 000,000,000 | ---D | M] (uTorrentControl2 Community Toolbar) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\{687578b9-7132-4a7a-80e4-30ee31099e03}
[2012/09/06 20:26:11 | 000,000,000 | ---D | M] (Live HTTP Headers) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\{8f8fe09b-0bd3-4470-bc1b-8cad42b8203a}
[2012/08/29 16:09:01 | 000,000,000 | ---D | M] (uTorrentBar Community Toolbar) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc}
[2012/08/13 06:39:37 | 000,000,000 | ---D | M] (DealPly) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\{EB9394A3-4AD6-4918-9537-31A1FD8E8EDF}
[2012/09/07 04:19:55 | 000,000,000 | ---D | M] ("Coupon Companion") -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\[email protected]
[2012/06/19 22:25:17 | 000,000,000 | ---D | M] (Babylon) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\[email protected]
[2012/07/08 22:10:58 | 000,000,000 | ---D | M] (Yontoo) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\[email protected]
[2012/08/16 23:01:42 | 002,282,511 | ---- | M] () (No name found) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\firefox\profiles\9opbbadv.default\extensions\[email protected]
[2012/07/24 23:52:09 | 000,741,958 | ---- | M] () (No name found) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\firefox\profiles\9opbbadv.default\extensions\{d10d0bf8-f5b5-c8b4-a8b2-2b9879e08c5d}.xpi
[2012/07/24 14:35:28 | 000,004,140 | ---- | M] () -- C:\Users\joeniqua c\AppData\Roaming\mozilla\firefox\profiles\9opbbadv.default\searchplugins\youtube.xml
[2012/07/20 12:56:58 | 000,000,000 | ---D | M] (No name found) -- C:\Program Files (x86)\Mozilla Firefox\extensions
[2012/07/20 12:56:59 | 000,000,000 | ---D | M] (Java Console) -- C:\Program Files (x86)\Mozilla Firefox\extensions\{CAFEEFAC-0016-0000-0033-ABCDEFFEDCBA}
[2012/06/19 22:24:25 | 000,000,000 | ---D | M] (Hotspot Shield Helper (Please allow this installation)) -- C:\Program Files (x86)\Mozilla Firefox\extensions\[email protected]
[2012/07/13 20:17:47 | 000,136,672 | ---- | M] (Mozilla Foundation) -- C:\Program Files (x86)\mozilla firefox\components\browsercomps.dll
[2012/09/06 10:17:14 | 000,003,768 | ---- | M] () -- C:\Program Files (x86)\mozilla firefox\searchplugins\avg-secure-search.xml
[2012/06/19 22:25:00 | 000,002,352 | ---- | M] () -- C:\Program Files (x86)\mozilla firefox\searchplugins\babylon.xml
[2012/07/13 20:16:36 | 000,002,252 | ---- | M] () -- C:\Program Files (x86)\mozilla firefox\searchplugins\bing.xml
[2012/07/13 20:16:36 | 000,002,040 | ---- | M] () -- C:\Program Files (x86)\mozilla firefox\searchplugins\twitter.xml
========== Chrome ==========
O1 HOSTS File: ([2009/06/10 17:00:26 | 000,000,824 | ---- | M]) - C:\Windows\SysNative\drivers\etc\hosts
O2:64bit: - BHO: (Google Toolbar Helper) - {AA58ED58-01DD-4d91-8333-CF10577473F7} - C:\Program Files (x86)\Google\Google Toolbar\GoogleToolbar_64.dll (Google Inc.)
O2:64bit: - BHO: (Hotspot Shield Class) - {F9E4A054-E9B1-4BC3-83A3-76A1AE736170} - C:\Program Files (x86)\Hotspot Shield\HssIE\HssIE_64.dll (AnchorFree Inc.)
O2 - BHO: (Coupon Companion) - {11111111-1111-1111-1111-110011441193} - Reg Error: Value error. File not found
O2 - BHO: (2YourFace Addon) - {1185823F-F22F-4027-80E5-4F68ACD5DE5E} - C:\Users\joeniqua c\AppData\Roaming\2YourFace\bho.dll ()
O2 - BHO: (Conduit Engine ) - {30F9B915-B755-4826-820B-08FBA6BD249D} - C:\Program Files (x86)\ConduitEngine\prxConduitEngine.dll (Conduit Ltd.)
O2 - BHO: (uTorrentControl2 Toolbar) - {687578b9-7132-4a7a-80e4-30ee31099e03} - C:\Program Files (x86)\uTorrentControl2\prxtbuTor.dll (Conduit Ltd.)
O2 - BHO: (Java™ Plug-In SSV Helper) - {761497BB-D6F0-462C-B6EB-D4DAF1D92D43} - C:\Program Files (x86)\Java\jre6\bin\ssv.dll (Sun Microsystems, Inc.)
O2 - BHO: (BitZipperSearch Toolbar) - {97bceb59-cfcd-4b16-a863-b3f72cf9f196} - C:\Program Files (x86)\BitZipperSearch\prxtbBit0.dll File not found
O2 - BHO: (Searchqu Toolbar) - {99079a25-328f-4bd4-be04-00955acaa0a7} - C:\PROGRA~2\WI3C8A~1\ToolBar\searchqudtx.dll File not found
O2 - BHO: (DealPly) - {A6174F27-1FFF-E1D6-A93F-BA48AD5DD448} - C:\Program Files (x86)\DealPly\DealPlyIE.dll (DealPly Technologies Ltd)
O2 - BHO: (Skype Browser Helper) - {AE805869-2E5C-4ED4-8F7B-F1F7851A4497} - C:\Program Files (x86)\Skype\Toolbars\Internet Explorer\skypeieplugin.dll (Skype Technologies S.A.)
O2 - BHO: (uTorrentBar Toolbar) - {bf7380fa-e3b4-4db2-af3e-9d8783a45bfc} - C:\Program Files (x86)\uTorrentBar\prxtbuTor.dll (Conduit Ltd.)
O2 - BHO: (Hotspot Shield Class) - {F9E4A054-E9B1-4BC3-83A3-76A1AE736170} - C:\Program Files (x86)\Hotspot Shield\HssIE\HssIE.dll (AnchorFree Inc.)
O2 - BHO: (Yontoo) - {FD72061E-9FDE-484D-A58A-0BAB4151CAD8} - Reg Error: Value error. File not found
O3:64bit: - HKLM\..\Toolbar: (no name) - !{2318C2B1-4965-11d4-9B18-009027A5CD4F} - No CLSID value found.
O3:64bit: - HKLM\..\Toolbar: (no name) - !{687578b9-7132-4a7a-80e4-30ee31099e03} - No CLSID value found.
O3:64bit: - HKLM\..\Toolbar: (no name) - !{95B7759C-8C7F-4BF1-B163-73684A933233} - No CLSID value found.
O3:64bit: - HKLM\..\Toolbar: (no name) - !{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc} - No CLSID value found.
O3:64bit: - HKLM\..\Toolbar: (Google Toolbar) - {2318C2B1-4965-11d4-9B18-009027A5CD4F} - C:\Program Files (x86)\Google\Google Toolbar\GoogleToolbar_64.dll (Google Inc.)
O3:64bit: - HKLM\..\Toolbar: (no name) - 10 - No CLSID value found.
O3:64bit: - HKLM\..\Toolbar: (no name) - Locked - No CLSID value found.
O3 - HKLM\..\Toolbar: (BitZipperSearch Toolbar) - {97bceb59-cfcd-4b16-a863-b3f72cf9f196} - C:\Program Files (x86)\BitZipperSearch\prxtbBit0.dll File not found
O3 - HKLM\..\Toolbar: (Searchqu Toolbar) - {99079a25-328f-4bd4-be04-00955acaa0a7} - C:\PROGRA~2\WI3C8A~1\ToolBar\searchqudtx.dll File not found
O3 - HKLM\..\Toolbar: (no name) - 10 - No CLSID value found.
O3 - HKLM\..\Toolbar: (no name) - Locked - No CLSID value found.
O3:64bit: - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\Toolbar\WebBrowser: (Google Toolbar) - {2318C2B1-4965-11D4-9B18-009027A5CD4F} - C:\Program Files (x86)\Google\Google Toolbar\GoogleToolbar_64.dll (Google Inc.)
O3 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\Toolbar\WebBrowser: (BitZipperSearch Toolbar) - {97BCEB59-CFCD-4B16-A863-B3F72CF9F196} - C:\Program Files (x86)\BitZipperSearch\prxtbBit0.dll File not found
O4:64bit: - HKLM..\Run: [egui] C:\Program Files\ESET\ESET Smart Security\egui.exe (ESET)
O4 - HKLM..\Run: [HF_G_Jul] "C:\Program Files (x86)\AVG Secure Search\HF_G_Jul.exe" /DoAction File not found
O4 - HKLM..\Run: [PC Cleaners] C:\Program Files (x86)\PC Cleaners\PCCleaners.exe (PC Cleaners Inc.)
O4 - HKLM..\Run: [ROC_ROC_JULY_P1] "C:\Program Files (x86)\AVG Secure Search\ROC_ROC_JULY_P1.exe" / /PROMPT /CMPID=ROC_JULY_P1 File not found
O4 - HKLM..\Run: [ROC_roc_ssl_v12] "C:\Program Files (x86)\AVG Secure Search\ROC_roc_ssl_v12.exe" / /PROMPT /CMPID=roc_ssl_v12 File not found
O4 - HKU\S-1-5-19..\Run: [Sidebar] C:\Program Files (x86)\Windows Sidebar\Sidebar.exe (Microsoft Corporation)
O4 - HKU\S-1-5-20..\Run: [Sidebar] C:\Program Files (x86)\Windows Sidebar\Sidebar.exe (Microsoft Corporation)
O4 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001..\Run: [Akamai NetSession Interface] C:\Users\joeniqua c\AppData\Local\Akamai\netsession_win.exe (Akamai Technologies, Inc.)
O4 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001..\Run: [bqyfq] C:\Users\JOENIQ~1\AppData\Local\Temp\Bash2.exe File not found
O4 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001..\Run: [FileManager] C:\Program Files\DriveHQ\DriveHQ FileManager\FileManager.exe (DriveHQ)
O4 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001..\Run: [SandboxieControl] C:\Program Files\Sandboxie\SbieCtrl.exe (SANDBOXIE L.T.D)
O4 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001..\Run: [uTorrent] C:\Program Files (x86)\uTorrent\uTorrent.exe (BitTorrent, Inc.)
O4 - HKU\S-1-5-19..\RunOnce: [mctadmin] C:\Windows\System32\mctadmin.exe File not found
O4 - HKU\S-1-5-20..\RunOnce: [mctadmin] C:\Windows\System32\mctadmin.exe File not found
O4 - Startup: C:\Users\joeniqua c\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Full glass.exe ()
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoActiveDesktop = 1
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoActiveDesktopChanges = 1
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDriveTypeAutoRun = 255
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer\NoDriveTypeAutoRun: NoDriveTypeAutoRun = 177
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: ConsentPromptBehaviorAdmin = 5
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: ConsentPromptBehaviorUser = 3
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: DisableStartupSound = 1
O7 - HKU\.DEFAULT\Software\Policies\Microsoft\Internet Explorer\Restrictions present
O7 - HKU\S-1-5-18\Software\Policies\Microsoft\Internet Explorer\Restrictions present
O7 - HKU\S-1-5-19\Software\Policies\Microsoft\Internet Explorer\Restrictions present
O7 - HKU\S-1-5-20\Software\Policies\Microsoft\Internet Explorer\Restrictions present
O7 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\Software\Policies\Microsoft\Internet Explorer\Restrictions present
O7 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDesktopCleanupWizard = 1
O7 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoDriveTypeAutoRun = 177
O7 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: LogonHoursAction = 2
O7 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: DontDisplayLogonHoursWarnings = 1
O9 - Extra Button: Skype Plug-In - {898EA8C8-E7FF-479B-8935-AEC46303B9E5} - C:\Program Files (x86)\Skype\Toolbars\Internet Explorer\skypeieplugin.dll (Skype Technologies S.A.)
O9 - Extra 'Tools' menuitem : Skype Plug-In - {898EA8C8-E7FF-479B-8935-AEC46303B9E5} - C:\Program Files (x86)\Skype\Toolbars\Internet Explorer\skypeieplugin.dll (Skype Technologies S.A.)
O1364bit: - gopher Prefix: missing
O13 - gopher Prefix: missing
O15 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..Trusted Ranges: Range1979 ([http] in Trusted sites)
O16 - DPF: {8AD9C840-044E-11D1-B3E9-00805F499D93} http://java.sun.com/...indows-i586.cab (Java Plug-in 1.6.0_33)
O16 - DPF: {CAFEEFAC-0016-0000-0033-ABCDEFFEDCBA} http://java.sun.com/...indows-i586.cab (Java Plug-in 1.6.0_33)
O16 - DPF: {CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA} http://java.sun.com/...indows-i586.cab (Java Plug-in 1.6.0_33)
O17 - HKLM\System\CCS\Services\Tcpip\Parameters: DhcpNameServer = 10.128.128.128
O17 - HKLM\System\CCS\Services\Tcpip\Parameters\Interfaces\{1043280D-E5B7-4C7B-B14C-F9ABF63A90EE}: DhcpNameServer = 10.128.128.128
O17 - HKLM\System\CCS\Services\Tcpip\Parameters\Interfaces\{8AEB272B-A6AF-4E6C-90E2-3813A347459D}: NameServer = 10.3.16.1
O18:64bit: - Protocol\Handler\ms-help - No CLSID value found
O18:64bit: - Protocol\Handler\ms-itss - No CLSID value found
O18:64bit: - Protocol\Handler\skype4com - No CLSID value found
O18:64bit: - Protocol\Handler\skype-ie-addon-data - No CLSID value found
O18:64bit: - Protocol\Handler\wlmailhtml - No CLSID value found
O18 - Protocol\Handler\skype4com {FFC8B962-9B40-4DFF-9458-1830C7DD7F5D} - C:\Program Files (x86)\Common Files\Skype\Skype4COM.dll (Skype Technologies)
O18 - Protocol\Handler\skype-ie-addon-data {91774881-D725-4E58-B298-07617B9B86A8} - C:\Program Files (x86)\Skype\Toolbars\Internet Explorer\skypeieplugin.dll (Skype Technologies S.A.)
O20:64bit: - AppInit_DLLs: (C:\PROGRA~2\WI3C8A~1\Datamngr\x64\datamngr.dll) - File not found
O20:64bit: - AppInit_DLLs: (C:\PROGRA~2\WI3C8A~1\Datamngr\x64\IEBHO.dll) - File not found
O20:64bit: - HKLM Winlogon: Shell - (explorer.exe) - C:\Windows\explorer.exe (Microsoft Corporation)
O20:64bit: - HKLM Winlogon: UserInit - (C:\Windows\system32\userinit.exe) - C:\Windows\SysNative\userinit.exe (Microsoft Corporation)
O20:64bit: - HKLM Winlogon: VMApplet - (/pagefile) - File not found
O20 - HKLM Winlogon: Shell - (explorer.exe) - C:\Windows\SysWow64\explorer.exe (Microsoft Corporation)
O20 - HKLM Winlogon: UserInit - (userinit.exe) - C:\Windows\SysWow64\userinit.exe (Microsoft Corporation)
O20 - HKLM Winlogon: VMApplet - (/pagefile) - File not found
O21:64bit: - SSODL: WebCheck - {E6FB5E20-DE35-11CF-9C87-00AA005127ED} - No CLSID value found.
O21 - SSODL: WebCheck - {E6FB5E20-DE35-11CF-9C87-00AA005127ED} - No CLSID value found.
O32 - HKLM CDRom: AutoRun - 0
O33 - MountPoints2\{90a595d8-5a15-11df-9d73-00235a729e73}\Shell - "" = AutoRun
O33 - MountPoints2\{90a595d8-5a15-11df-9d73-00235a729e73}\Shell\AutoRun\command - "" = E:\LaunchU3.exe -a
O34 - HKLM BootExecute: (autocheck autochk *)
O35:64bit: - HKLM\..comfile [open] -- "%1" %*
O35:64bit: - HKLM\..exefile [open] -- "%1" %*
O35 - HKLM\..comfile [open] -- "%1" %*
O35 - HKLM\..exefile [open] -- "%1" %*
O37:64bit: - HKLM\...com [@ = comfile] -- "%1" %*
O37:64bit: - HKLM\...exe [@ = exefile] -- "%1" %*
O37 - HKLM\...com [@ = comfile] -- "%1" %*
O37 - HKLM\...exe [@ = exefile] -- "%1" %*
O38 - SubSystems\\Windows: (ServerDll=winsrv:UserServerDllInitialization,3)
O38 - SubSystems\\Windows: (ServerDll=winsrv:ConServerDllInitialization,2)
O38 - SubSystems\\Windows: (ServerDll=sxssrv,4)
CREATERESTOREPOINT
Restore point Set: OTL Restore Point
========== Files/Folders - Created Within 30 Days ==========
[2012/09/08 07:07:11 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\PC Cleaners
[2012/09/08 07:07:06 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\PC Cleaners
[2012/09/08 07:07:05 | 004,571,960 | ---- | C] (PC Cleaners) -- C:\Windows\uninst.exe
[2012/09/08 07:07:03 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\PCPro
[2012/09/08 07:07:03 | 000,000,000 | ---D | C] -- C:\ProgramData\PC1Data
[2012/09/08 07:07:03 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\PC Cleaners
[2012/09/08 02:50:46 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DarkComet RAT Remover
[2012/09/08 02:50:45 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\PhrozenSoft
[2012/09/08 02:21:14 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Simple Port Forwarding
[2012/09/08 02:21:10 | 000,000,000 | ---D | C] -- C:\Windows\Simple Port Forwarding
[2012/09/08 02:21:10 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\Simple Port Forwarding
[2012/09/07 10:27:36 | 000,000,000 | ---D | C] -- C:\Windows\SysWow64\bg-BG
[2012/09/07 07:43:39 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\ESET
[2012/09/07 07:43:39 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Local\ESET
[2012/09/07 07:39:03 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\ESET
[2012/09/07 07:39:03 | 000,000,000 | ---D | C] -- C:\ProgramData\ESET
[2012/09/07 07:39:03 | 000,000,000 | ---D | C] -- C:\Program Files\ESET
[2012/09/07 02:42:45 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\DriveHQHOOK
[2012/09/07 02:38:38 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\Documents\DriveHQ SyncFolder
[2012/09/07 02:38:01 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\DriveHQ
[2012/09/07 02:36:20 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DriveHQ
[2012/09/07 02:35:27 | 000,000,000 | ---D | C] -- C:\Program Files\DriveHQ
[2012/09/06 23:53:00 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Local\Xenocode
[2012/09/06 20:33:51 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Xeus Technologies
[2012/09/06 20:33:50 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\Xeus Technologies
[2012/09/06 20:33:18 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Local\Coupon Companion
[2012/09/06 20:33:11 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\Coupon Companion
[2012/09/06 20:25:58 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Local\Welltek_Software
[2012/09/06 20:20:22 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\001 File Joiner and Splitter
[2012/09/06 20:20:21 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\001 File Joiner and Splitter 4.0
[2012/09/06 10:20:04 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\AVG2012
[2012/09/06 10:15:04 | 000,000,000 | -H-D | C] -- C:\$AVG
[2012/09/06 10:15:04 | 000,000,000 | ---D | C] -- C:\ProgramData\AVG2012
[2012/09/06 07:29:17 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Ardamax Keylogger 3.9
[2012/08/15 17:04:35 | 000,000,000 | ---D | C] -- C:\ProgramData\hssff
[2012/08/13 06:33:32 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DealPly
[2012/08/13 06:33:24 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\DealPly
[2012/08/10 21:55:48 | 000,560,184 | ---- | C] (Duplex Secure Ltd.) -- C:\Windows\SysNative\drivers\sptd.sys
[1 C:\Windows\SysWow64\*.tmp files -> C:\Windows\SysWow64\*.tmp -> ]
[1 C:\Windows\*.tmp files -> C:\Windows\*.tmp -> ]
========== Files - Modified Within 30 Days ==========
[2012/09/09 01:35:47 | 000,107,326 | ---- | M] () -- C:\Users\joeniqua c\Desktop\Untitled.jpg
[2012/09/09 01:28:02 | 000,000,898 | ---- | M] () -- C:\Windows\tasks\GoogleUpdateTaskMachineUA.job
[2012/09/08 23:04:25 | 000,055,335 | ---- | M] () -- C:\Users\joeniqua c\Desktop\mico2.jpg
[2012/09/08 18:32:01 | 000,067,584 | --S- | M] () -- C:\Windows\bootstat.dat
[2012/09/08 18:11:22 | 000,002,522 | ---- | M] () -- C:\Windows\Sandboxie.ini
[2012/09/08 07:06:21 | 004,571,960 | ---- | M] (PC Cleaners) -- C:\Windows\uninst.exe
[2012/09/08 05:18:14 | 000,009,920 | -H-- | M] () -- C:\Windows\SysNative\7B296FB0-376B-497e-B012-9C450E1B7327-5P-1.C7483456-A289-439d-8115-601632D005A0
[2012/09/08 05:18:14 | 000,009,920 | -H-- | M] () -- C:\Windows\SysNative\7B296FB0-376B-497e-B012-9C450E1B7327-5P-0.C7483456-A289-439d-8115-601632D005A0
[2012/09/08 03:28:06 | 000,000,894 | ---- | M] () -- C:\Windows\tasks\GoogleUpdateTaskMachineCore.job
[2012/09/08 02:21:14 | 000,001,978 | ---- | M] () -- C:\Users\joeniqua c\Desktop\Simple Port Forwarding.lnk
[2012/09/07 20:32:53 | 000,103,175 | ---- | M] () -- C:\Users\joeniqua c\Desktop\MICO.jpg
[2012/09/07 07:14:48 | 2211,483,648 | -HS- | M] () -- C:\hiberfil.sys
[2012/09/03 17:39:14 | 000,281,104 | ---- | M] (CACE Technologies, Inc.) -- C:\Windows\SysWow64\wpcap.dll
[2012/09/03 17:39:14 | 000,096,784 | ---- | M] (CACE Technologies, Inc.) -- C:\Windows\SysWow64\Packet.dll
[2012/08/25 00:52:08 | 003,793,566 | ---- | M] () -- C:\Windows\SysNative\perfh009.dat
[2012/08/25 00:52:07 | 001,211,992 | ---- | M] () -- C:\Windows\SysNative\perfc009.dat
[2012/08/25 00:52:07 | 000,006,230 | ---- | M] () -- C:\Windows\SysNative\PerfStringBackup.INI
[2012/08/16 08:19:13 | 000,343,552 | ---- | M] () -- C:\Windows\SysNative\FNTCACHE.DAT
[2012/08/10 21:55:48 | 000,560,184 | ---- | M] (Duplex Secure Ltd.) -- C:\Windows\SysNative\drivers\sptd.sys
[1 C:\Windows\SysWow64\*.tmp files -> C:\Windows\SysWow64\*.tmp -> ]
[1 C:\Windows\*.tmp files -> C:\Windows\*.tmp -> ]
========== Files Created - No Company Name ==========
[2012/09/09 01:33:38 | 000,107,326 | ---- | C] () -- C:\Users\joeniqua c\Desktop\Untitled.jpg
[2012/09/08 23:04:21 | 000,055,335 | ---- | C] () -- C:\Users\joeniqua c\Desktop\mico2.jpg
[2012/09/08 02:21:14 | 000,001,978 | ---- | C] () -- C:\Users\joeniqua c\Desktop\Simple Port Forwarding.lnk
[2012/09/07 20:32:49 | 000,103,175 | ---- | C] () -- C:\Users\joeniqua c\Desktop\MICO.jpg
[2012/08/08 21:34:38 | 000,000,000 | ---- | C] () -- C:\Windows\SysWow64\cd.dat
[2012/07/23 15:34:39 | 000,006,212 | ---- | C] () -- C:\Windows\SysWow64\PerfStringBackup.INI
[2012/07/18 22:53:34 | 424,029,708 | ---- | C] () -- C:\Users\joeniqua c\Desktop0001.avi
[2012/07/01 10:52:14 | 000,001,284 | ---- | C] () -- C:\Users\joeniqua c\AppData\Local\recently-used.xbel
[2012/05/22 21:12:54 | 000,290,816 | ---- | C] () -- C:\Windows\SysWow64\nmapserv.exe
[2012/05/22 21:12:53 | 000,452,096 | ---- | C] () -- C:\Windows\SysWow64\nmap.exe
[2011/08/23 03:23:25 | 000,002,522 | ---- | C] () -- C:\Windows\Sandboxie.ini
[2011/07/29 22:28:56 | 000,000,000 | ---- | C] () -- C:\Windows\nsreg.dat
[2011/07/22 15:47:41 | 000,003,306 | ---- | C] () -- C:\Windows\SysWow64\CONFIG.INI
[2011/06/24 11:45:45 | 000,000,000 | ---- | C] () -- C:\Users\joeniqua c\AppData\Local\{72BE25B1-B843-4641-8046-5C7B47A3E39F}
[2011/05/07 02:52:38 | 000,007,600 | ---- | C] () -- C:\Users\joeniqua c\AppData\Local\Resmon.ResmonCfg
[2011/05/06 22:49:06 | 000,230,752 | ---- | C] () -- C:\Windows\patchw32.dll
[2011/05/06 22:48:55 | 000,118,176 | ---- | C] () -- C:\Windows\patchw.dll
[2011/02/11 17:23:34 | 000,053,299 | ---- | C] () -- C:\Windows\SysWow64\pthreadVC.dll
[2011/01/31 19:23:48 | 000,000,268 | ---- | C] () -- C:\Windows\{789289CA-F73A-4A16-A331-54D498CE069F}_WiseFW.ini
[2010/04/25 15:51:34 | 000,002,018 | ---- | C] () -- C:\Users\joeniqua c\AppData\Roaming\wklnhst.dat
[2010/02/08 17:14:01 | 000,004,594 | RHS- | C] () -- C:\Users\joeniqua c\ntuser.pol
========== LOP Check ==========
[2012/06/19 22:25:49 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\2YourFace
[2012/06/25 14:01:37 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\AVG
[2012/09/06 10:20:04 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\AVG2012
[2012/06/19 22:24:39 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Babylon
[2012/07/06 10:22:01 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\BitTorrent
[2010/06/10 17:21:11 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\BitZipper
[2012/08/13 02:28:39 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Dev-Cpp
[2012/09/07 02:42:45 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\DriveHQ
[2012/09/07 02:42:45 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\DriveHQHOOK
[2012/07/23 03:48:42 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\e-academy Inc
[2012/09/07 07:43:39 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\ESET
[2011/07/03 00:04:43 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\go
[2012/07/20 10:50:36 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Hod_Uninstall
[2012/08/10 19:32:03 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\HulkOnDesk
[2012/04/21 02:41:12 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\LolClient
[2012/07/07 11:23:39 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Mael
[2012/07/09 06:06:05 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Mavituna Security Ltd
[2012/06/23 22:30:54 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Notepad++
[2012/09/08 07:07:11 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\PC Cleaners
[2012/09/08 07:07:14 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\PCPro
[2012/06/24 01:02:36 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\PowerCinema
[2012/06/24 01:03:06 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\SoftDMA
[2012/07/17 21:13:27 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Subversion
[2012/06/23 21:36:47 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Systweak
[2012/07/08 22:14:19 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\TeamViewer
[2010/07/10 23:11:36 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Template
[2012/06/17 16:30:49 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\TS3Client
[2012/09/08 00:08:01 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\uTorrent
[2010/04/24 10:38:00 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\WildTangent
[2012/06/19 07:49:24 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Wireshark
[2012/06/26 18:07:21 | 000,032,564 | ---- | M] () -- C:\Windows\Tasks\SCHEDLGU.TXT
========== Purity Check ==========
========== Custom Scans ==========
========== Base Services ==========
SRV:64bit: - [2009/07/13 21:40:01 | 000,072,192 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\aelupsvc.dll -- (AeLookupSvc)
SRV:64bit: - [2010/11/20 09:25:40 | 000,070,656 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysNative\appinfo.dll -- (Appinfo)
SRV:64bit: - [2009/07/13 21:38:55 | 000,079,360 | ---- | M] (Microsoft Corporation) [Disabled | Stopped] -- C:\Windows\SysNative\alg.exe -- (ALG)
SRV:64bit: - [2010/11/20 09:27:23 | 000,849,920 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\qmgr.dll -- (BITS)
SRV:64bit: - [2010/11/20 09:25:45 | 000,705,024 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\BFE.DLL -- (BFE)
SRV:64bit: - [2011/11/17 02:33:55 | 000,031,232 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysNative\lsass.exe -- (KeyIso)
SRV:64bit: - [2009/07/13 21:40:50 | 000,402,944 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\es.dll -- (EventSystem)
SRV - [2009/07/13 21:15:19 | 000,271,360 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysWOW64\es.dll -- (EventSystem)
SRV:64bit: - [2012/07/04 18:13:27 | 000,136,704 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysNative\browser.dll -- (Browser)
SRV:64bit: - [2012/04/24 01:37:37 | 000,184,320 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\cryptsvc.dll -- (CryptSvc)
SRV - [2012/04/24 00:36:42 | 000,140,288 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysWOW64\cryptsvc.dll -- (CryptSvc)
SRV:64bit: - [2010/11/20 09:27:24 | 000,512,000 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\rpcss.dll -- (DcomLaunch)
SRV:64bit: - [2010/11/20 09:26:04 | 000,317,952 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\dhcpcore.dll -- (Dhcp)
SRV - [2010/11/20 08:18:30 | 000,254,464 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysWOW64\dhcpcore.dll -- (Dhcp)
SRV:64bit: - [2011/03/03 02:24:16 | 000,183,296 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\dnsrslvr.dll -- (Dnscache)
SRV:64bit: - [2009/07/13 21:40:35 | 000,111,104 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysNative\eapsvc.dll -- (EapHost)
SRV:64bit: - [2009/07/13 21:41:00 | 000,038,912 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysNative\hidserv.dll -- (hidserv)
SRV - [2009/07/13 21:15:24 | 000,049,152 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysWOW64\hidserv.dll -- (hidserv)
SRV:64bit: - [2009/07/13 21:41:10 | 000,359,424 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\ipnathlp.dll -- (SharedAccess)
SRV:64bit: - [2010/11/20 09:26:39 | 000,501,248 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysNative\IPSECSVC.DLL -- (PolicyAgent)
No service found with a name of MsMpSvc
No service found with a name of NisSrv
SRV:64bit: - [2009/07/13 21:41:54 | 000,524,288 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\swprv.dll -- (swprv)
SRV:64bit: - [2009/07/13 21:41:26 | 000,067,584 | ---- | M] (Microsoft Corporation) [Auto | Stopped] -- C:\Windows\SysNative\mmcss.dll -- (MMCSS)
SRV:64bit: - [2009/07/13 21:41:52 | 000,360,448 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysNative\netman.dll -- (Netman)
SRV:64bit: - [2009/07/13 21:41:52 | 000,459,776 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysNative\netprofm.dll -- (netprofm)
SRV - [2009/07/13 21:16:03 | 000,360,448 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysWOW64\netprofm.dll -- (netprofm)
SRV:64bit: - [2010/11/20 09:27:22 | 000,303,616 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\nlasvc.dll -- (NlaSvc)
SRV:64bit: - [2009/07/13 21:41:53 | 000,025,600 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\nsisvc.dll -- (nsi)
SRV:64bit: - [2011/05/24 07:42:55 | 000,404,480 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\umpnpmgr.dll -- (PlugPlay)
SRV:64bit: - [2012/02/11 02:36:02 | 000,559,104 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\spoolsv.exe -- (Spooler)
SRV:64bit: - [2011/11/17 02:33:55 | 000,031,232 | ---- | M] (Microsoft Corporation) [On_Demand | Running] -- C:\Windows\SysNative\lsass.exe -- (ProtectedStorage)
No service found with a name of EMDMgmt
SRV:64bit: - [2009/07/13 21:41:53 | 000,099,328 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\rasauto.dll -- (RasAuto)
SRV:64bit: - [2010/11/20 09:27:24 | 000,344,064 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\rasmans.dll -- (RasMan)
SRV:64bit: - [2010/11/20 09:27:24 | 000,512,000 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\rpcss.dll -- (RpcSs)
SRV:64bit: - [2010/11/20 09:27:25 | 000,030,720 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\seclogon.dll -- (seclogon)
SRV:64bit: - [2011/11/17 02:33:55 | 000,031,232 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\lsass.exe -- (SamSs)
SRV:64bit: - [2009/07/13 21:41:58 | 000,097,280 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\wscsvc.dll -- (wscsvc)
SRV:64bit: - [2010/11/20 09:27:26 | 000,236,032 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\srvsvc.dll -- (LanmanServer)
SRV:64bit: - [2010/11/20 09:27:25 | 000,370,688 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\shsvcs.dll -- (ShellHWDetection)
SRV - [2010/11/20 08:21:19 | 000,328,192 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysWOW64\shsvcs.dll -- (ShellHWDetection)
No service found with a name of slsvc
SRV:64bit: - [2010/11/20 09:27:25 | 001,110,016 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\schedsvc.dll -- (Schedule)
SRV:64bit: - [2010/11/20 09:27:26 | 000,316,928 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\tapisrv.dll -- (TapiSrv)
SRV - [2010/11/20 08:21:28 | 000,242,176 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysWOW64\tapisrv.dll -- (TapiSrv)
SRV:64bit: - [2009/07/13 21:41:55 | 000,044,544 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\themeservice.dll -- (Themes)
SRV:64bit: - [2012/05/01 01:40:20 | 000,209,920 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\profsvc.dll -- (ProfSvc)
SRV:64bit: - [2010/11/20 09:25:27 | 001,600,512 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\VSSVC.exe -- (VSS)
SRV:64bit: - [2010/11/20 09:25:42 | 000,679,424 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\audiosrv.dll -- (AudioSrv)
SRV:64bit: - [2010/11/20 09:25:42 | 000,679,424 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\audiosrv.dll -- (AudioEndpointBuilder)
SRV:64bit: - [2010/11/20 09:27:25 | 000,170,496 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\sdrsvc.dll -- (SDRSVC)
SRV:64bit: - [2009/07/13 21:41:27 | 001,011,712 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Program Files\Windows Defender\MpSvc.dll -- (WinDefend)
SRV:64bit: - [2010/11/20 09:27:28 | 001,646,080 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\wevtsvc.dll -- (eventlog)
SRV:64bit: - [2010/11/20 09:26:59 | 000,828,416 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\MPSSVC.dll -- (MpsSvc)
SRV:64bit: - [2010/11/20 09:27:28 | 000,580,096 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\wiaservc.dll -- (stisvc)
SRV:64bit: - [2010/11/20 09:24:58 | 000,128,000 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\msiexec.exe -- (msiserver)
SRV - [2010/11/20 08:17:22 | 000,073,216 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysWow64\msiexec.exe -- (msiserver)
SRV:64bit: - [2009/07/13 21:41:56 | 000,242,688 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\wbem\WMIsvc.dll -- (Winmgmt)
SRV:64bit: - [2012/06/02 18:19:43 | 002,428,952 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\wuaueng.dll -- (wuauserv)
SRV:64bit: - [2010/11/20 09:26:07 | 000,252,416 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Windows\SysNative\dot3svc.dll -- (dot3svc)
SRV:64bit: - [2009/07/13 21:41:56 | 000,886,784 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\wlansvc.dll -- (Wlansvc)
SRV:64bit: - [2010/11/20 09:27:28 | 000,118,784 | ---- | M] (Microsoft Corporation) [Auto | Running] -- C:\Windows\SysNative\wkssvc.dll -- (LanmanWorkstation)
< %SYSTEMDRIVE%\*.exe >
< MD5 for: EXPLORER.EXE >
[2011/02/26 02:23:14 | 002,870,272 | ---- | M] (Microsoft Corporation) MD5=0862495E0C825893DB75EF44FAEA8E93 -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.16768_none_adc24107935a7e25\explorer.exe
[2011/02/26 01:19:21 | 002,616,320 | ---- | M] (Microsoft Corporation) MD5=0FB9C74046656D1579A64660AD67B746 -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7601.21669_none_ba87e574ddfe652d\explorer.exe
[2009/07/13 21:14:20 | 002,613,248 | ---- | M] (Microsoft Corporation) MD5=15BC38A7492BEFE831966ADB477CF76F -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.16385_none_b7fe430bc7ce3761\explorer.exe
[2011/02/26 01:51:13 | 002,614,784 | ---- | M] (Microsoft Corporation) MD5=255CF508D7CFB10E0794D6AC93280BD8 -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.20910_none_b8ce9756e0b786a4\explorer.exe
[2009/10/31 01:45:39 | 002,614,272 | ---- | M] (Microsoft Corporation) MD5=2626FC9755BE22F805D3CFA0CE3EE727 -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.16450_none_b819b343c7ba6202\explorer.exe
[2011/02/26 01:33:07 | 002,614,784 | ---- | M] (Microsoft Corporation) MD5=2AF58D15EDC06EC6FDACCE1F19482BBF -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.16768_none_b816eb59c7bb4020\explorer.exe
[2011/02/25 02:19:30 | 002,871,808 | ---- | M] (Microsoft Corporation) MD5=332FEAB1435662FC6C672E25BEB37BE3 -- C:\Windows\explorer.exe
[2011/02/25 02:19:30 | 002,871,808 | ---- | M] (Microsoft Corporation) MD5=332FEAB1435662FC6C672E25BEB37BE3 -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7601.17567_none_afa79dc39081d0ba\explorer.exe
[2011/02/26 02:14:34 | 002,871,808 | ---- | M] (Microsoft Corporation) MD5=3B69712041F3D63605529BD66DC00C48 -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7601.21669_none_b0333b22a99da332\explorer.exe
[2010/11/20 08:17:09 | 002,616,320 | ---- | M] (Microsoft Corporation) MD5=40D777B7A95E00593EB1568C68514493 -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7601.17514_none_ba2f56d3c4bcbafb\explorer.exe
[2009/08/03 02:19:07 | 002,868,224 | ---- | M] (Microsoft Corporation) MD5=700073016DAC1C3D2E7E2CE4223334B6 -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.20500_none_ae84b558ac4eb41c\explorer.exe
[2009/07/13 20:14:22 | 002,613,248 | ---- | M] (Microsoft Corporation) MD5=8A78FD54AD5113ECD2A48914ACF67D69 -- C:\Windows\Resources\Themes\Kuro_2010_for_Windows_7_by_Aaron_A_Arts\Kuro2010\Replacements\explorer.exe
[2011/02/25 01:30:54 | 002,616,320 | ---- | M] (Microsoft Corporation) MD5=8B88EBBB05A0E56B7DCC708498C02B3E -- C:\Windows\SysWOW64\explorer.exe
[2011/02/25 01:30:54 | 002,616,320 | ---- | M] (Microsoft Corporation) MD5=8B88EBBB05A0E56B7DCC708498C02B3E -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7601.17567_none_b9fc4815c4e292b5\explorer.exe
[2009/10/31 02:34:59 | 002,870,272 | ---- | M] (Microsoft Corporation) MD5=9AAAEC8DAC27AA17B053E6352AD233AE -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.16450_none_adc508f19359a007\explorer.exe
[2009/08/03 01:49:47 | 002,613,248 | ---- | M] (Microsoft Corporation) MD5=9FF6C4C91A3711C0A3B18F87B08B518D -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.20500_none_b8d95faae0af7617\explorer.exe
[2010/11/20 09:24:45 | 002,872,320 | ---- | M] (Microsoft Corporation) MD5=AC4C51EB24AA95B77F705AB159189E24 -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7601.17514_none_afdaac81905bf900\explorer.exe
[2009/10/31 02:38:38 | 002,870,272 | ---- | M] (Microsoft Corporation) MD5=B8EC4BD49CE8F6FC457721BFC210B67F -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.20563_none_ae46d6aeac7ca7c7\explorer.exe
[2009/08/03 01:35:50 | 002,613,248 | ---- | M] (Microsoft Corporation) MD5=B95EEB0F4E5EFBF1038A35B3351CF047 -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.16404_none_b853c407c78e3ba9\explorer.exe
[2009/07/13 21:39:10 | 002,868,224 | ---- | M] (Microsoft Corporation) MD5=C235A51CB740E45FFA0EBFB9BAFCDA64 -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.16385_none_ada998b9936d7566\explorer.exe
[2009/10/31 02:00:51 | 002,614,272 | ---- | M] (Microsoft Corporation) MD5=C76153C7ECA00FA852BB0C193378F917 -- C:\Windows\winsxs\wow64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.20563_none_b89b8100e0dd69c2\explorer.exe
[2011/02/26 02:26:45 | 002,870,784 | ---- | M] (Microsoft Corporation) MD5=E38899074D4951D31B4040E994DD7C8D -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.20910_none_ae79ed04ac56c4a9\explorer.exe
[2009/08/03 02:17:37 | 002,868,224 | ---- | M] (Microsoft Corporation) MD5=F170B4A061C9E026437B193B4D571799 -- C:\Windows\winsxs\amd64_microsoft-windows-explorer_31bf3856ad364e35_6.1.7600.16404_none_adff19b5932d79ae\explorer.exe
< MD5 for: QMGR.DLL >
[2010/11/20 09:27:23 | 000,849,920 | ---- | M] (Microsoft Corporation) MD5=1EA7969E3271CBC59E1730697DC74682 -- C:\Windows\SysNative\qmgr.dll
[2010/11/20 09:27:23 | 000,849,920 | ---- | M] (Microsoft Corporation) MD5=1EA7969E3271CBC59E1730697DC74682 -- C:\Windows\winsxs\amd64_microsoft-windows-bits-client_31bf3856ad364e35_6.1.7601.17514_none_81b6ca5c101195cd\qmgr.dll
[2009/07/13 21:41:53 | 000,848,384 | ---- | M] (Microsoft Corporation) MD5=7F0C323FE3DA28AA4AA1BDA3F575707F -- C:\Windows\winsxs\amd64_microsoft-windows-bits-client_31bf3856ad364e35_6.1.7600.16385_none_7f85b69413231233\qmgr.dll
< MD5 for: SERVICES >
[2012/07/04 17:02:16 | 000,000,094 | --S- | M] () MD5=713F38DC6C1E73D06F1516873E1E8919 -- C:\cygwin\etc\services
[2012/05/22 10:32:56 | 002,492,858 | ---- | M] () MD5=99FF822BF8665F96DC62E79C30F75F28 -- C:\Program Files (x86)\Wireshark\services
[2009/06/10 17:00:26 | 000,017,463 | ---- | M] () MD5=D9E1A01B480D961B7CF0509D597A92D6 -- C:\Windows\winsxs\amd64_microsoft-windows-w..nfrastructure-other_31bf3856ad364e35_6.1.7600.16385_none_6079f415110c0210\services
< MD5 for: SERVICES.EXE >
[2009/07/13 21:39:37 | 000,328,704 | ---- | M] (Microsoft Corporation) MD5=24ACB7E5BE595468E3B9AA488B9B4FCB -- C:\Windows\SysNative\services.exe
[2009/07/13 21:39:37 | 000,328,704 | ---- | M] (Microsoft Corporation) MD5=24ACB7E5BE595468E3B9AA488B9B4FCB -- C:\Windows\winsxs\amd64_microsoft-windows-s..s-servicecontroller_31bf3856ad364e35_6.1.7600.16385_none_2b54b20ee6fa07b1\services.exe
< MD5 for: SERVICES.EXE.MUI >
[2009/07/13 22:25:40 | 000,017,408 | ---- | M] (Microsoft Corporation) Unable to obtain MD5 -- C:\Windows\SysNative\en-US\services.exe.mui
[2009/07/13 22:25:40 | 000,017,408 | ---- | M] (Microsoft Corporation) Unable to obtain MD5 -- C:\Windows\winsxs\amd64_microsoft-windows-s..ontroller.resources_31bf3856ad364e35_6.1.7600.16385_en-us_c5f238be3fa63468\services.exe.mui
< MD5 for: SERVICES.H >
[2012/05/02 00:16:24 | 000,010,870 | ---- | M] () MD5=591003E7C26019872A3E0F2726214990 -- C:\metasploit\msf3\external\source\meterpreter\source\bionic\libc\netbsd\net\services.h
< MD5 for: SERVICES.JAVA >
[2012/08/03 10:40:39 | 000,002,703 | ---- | M] () MD5=8BDF12D469231FD8841DF8B2DA1B4CEB -- C:\metasploit\msf3\external\source\armitage\src\cortana\data\Services.java
< MD5 for: SERVICES.LNK >
[2009/07/14 00:54:05 | 000,001,288 | ---- | M] () MD5=CA0D9F4743DFF86EBAF09D763139E958 -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Administrative Tools\services.lnk
[2009/07/14 00:54:05 | 000,001,288 | ---- | M] () MD5=CA0D9F4743DFF86EBAF09D763139E958 -- C:\Users\All Users\Microsoft\Windows\Start Menu\Programs\Administrative Tools\services.lnk
< MD5 for: SERVICES.MOF >
[2009/06/10 16:44:06 | 000,002,866 | ---- | M] () MD5=26A11C895A7F0B6D32105EBE127D8500 -- C:\Windows\SysNative\wbem\services.mof
[2009/06/10 16:44:06 | 000,002,866 | ---- | M] () MD5=26A11C895A7F0B6D32105EBE127D8500 -- C:\Windows\winsxs\amd64_microsoft-windows-s..s-servicecontroller_31bf3856ad364e35_6.1.7600.16385_none_2b54b20ee6fa07b1\services.mof
< MD5 for: SERVICES.MSC >
[2009/07/13 22:23:30 | 000,092,745 | ---- | M] () MD5=7A1D35F59468B8118AF5B8E21DF78AE2 -- C:\Windows\SysNative\en-US\services.msc
[2009/06/10 16:38:36 | 000,092,745 | ---- | M] () MD5=7A1D35F59468B8118AF5B8E21DF78AE2 -- C:\Windows\SysNative\services.msc
[2009/07/13 22:08:50 | 000,092,745 | ---- | M] () MD5=7A1D35F59468B8118AF5B8E21DF78AE2 -- C:\Windows\SysWOW64\en-US\services.msc
[2009/06/10 17:21:09 | 000,092,745 | ---- | M] () MD5=7A1D35F59468B8118AF5B8E21DF78AE2 -- C:\Windows\SysWOW64\services.msc
[2009/07/13 22:23:30 | 000,092,745 | ---- | M] () MD5=7A1D35F59468B8118AF5B8E21DF78AE2 -- C:\Windows\winsxs\amd64_microsoft-windows-s..cessnapin.resources_31bf3856ad364e35_6.1.7600.16385_en-us_003408aa160fce5b\services.msc
[2009/06/10 16:38:36 | 000,092,745 | ---- | M] () MD5=7A1D35F59468B8118AF5B8E21DF78AE2 -- C:\Windows\winsxs\amd64_microsoft-windows-servicessnapin_31bf3856ad364e35_6.1.7600.16385_none_2b58d44b5f6beb8a\services.msc
[2009/07/13 22:08:50 | 000,092,745 | ---- | M] () MD5=7A1D35F59468B8118AF5B8E21DF78AE2 -- C:\Windows\winsxs\x86_microsoft-windows-s..cessnapin.resources_31bf3856ad364e35_6.1.7600.16385_en-us_a4156d265db25d25\services.msc
[2009/06/10 17:21:09 | 000,092,745 | ---- | M] () MD5=7A1D35F59468B8118AF5B8E21DF78AE2 -- C:\Windows\winsxs\x86_microsoft-windows-servicessnapin_31bf3856ad364e35_6.1.7600.16385_none_cf3a38c7a70e7a54\services.msc
< MD5 for: SERVICES.PTXML >
[2009/07/13 16:16:17 | 000,001,061 | ---- | M] () MD5=640D7DD61B1CFA6C96F80F68F78CDFA7 -- C:\Windows\SysNative\wdi\perftrack\Services.ptxml
[2009/07/13 16:16:17 | 000,001,061 | ---- | M] () MD5=640D7DD61B1CFA6C96F80F68F78CDFA7 -- C:\Windows\winsxs\amd64_microsoft-windows-s..s-servicecontroller_31bf3856ad364e35_6.1.7600.16385_none_2b54b20ee6fa07b1\Services.ptxml
< MD5 for: SERVICES.RB >
[2012/07/10 11:01:34 | 000,000,191 | ---- | M] () MD5=7906B9B454D8E46C9955C66368E68167 -- C:\metasploit\msf3\lib\msf\scripts\meterpreter\services.rb
[2012/05/03 17:41:56 | 000,006,184 | ---- | M] () MD5=9AE11B1DB53E75253533C24220D3C85C -- C:\metasploit\apps\pro\msf3\lib\msf\core\post\windows\services.rb
[2012/08/02 10:40:23 | 000,006,768 | ---- | M] () MD5=A7773FE28D911AC5B7F29676A14D1A5D -- C:\metasploit\msf3\lib\msf\core\post\windows\services.rb
[2012/05/03 17:41:56 | 000,005,054 | ---- | M] () MD5=B81CFE21196D261497DDAE8929EA266A -- C:\metasploit\apps\pro\msf3\test\modules\post\test\services.rb
[2012/05/02 00:16:18 | 000,005,054 | ---- | M] () MD5=B81CFE21196D261497DDAE8929EA266A -- C:\metasploit\msf3\test\modules\post\test\services.rb
[2012/05/03 17:41:56 | 000,000,166 | ---- | M] () MD5=F7E7D9F0E22105D65E3D0B67E7DFAADC -- C:\metasploit\apps\pro\msf3\lib\msf\scripts\meterpreter\services.rb
< MD5 for: SERVICES.SL >
[2012/08/03 10:40:35 | 000,002,366 | ---- | M] () MD5=260F5FDE8F2ECBBEC0A85C6BF1F5F7F2 -- C:\metasploit\msf3\external\source\armitage\scripts\services.sl
< MD5 for: SERVICES.TICO >
[2009/09/25 08:00:00 | 000,002,038 | ---- | M] () MD5=D669B1B2EBE288A61680C3C863828D28 -- C:\Windows\TacoFilez\Prams\TUU2012\TuneUpPortable\App\TuneUp\data\services.tico
< MD5 for: SVCHOST.EXE >
[2009/07/13 21:14:41 | 000,020,992 | ---- | M] (Microsoft Corporation) MD5=54A47F6B5E09A77E61649109C6A08866 -- C:\Windows\SysWOW64\svchost.exe
[2009/07/13 21:14:41 | 000,020,992 | ---- | M] (Microsoft Corporation) MD5=54A47F6B5E09A77E61649109C6A08866 -- C:\Windows\winsxs\x86_microsoft-windows-services-svchost_31bf3856ad364e35_6.1.7600.16385_none_b591afc466a15356\svchost.exe
[2009/07/13 21:39:46 | 000,027,136 | ---- | M] (Microsoft Corporation) MD5=C78655BC80301D76ED4FEF1C1EA40A7D -- C:\Windows\SysNative\svchost.exe
[2009/07/13 21:39:46 | 000,027,136 | ---- | M] (Microsoft Corporation) MD5=C78655BC80301D76ED4FEF1C1EA40A7D -- C:\Windows\winsxs\amd64_microsoft-windows-services-svchost_31bf3856ad364e35_6.1.7600.16385_none_11b04b481efec48c\svchost.exe
< MD5 for: USERINIT.EXE >
[2010/11/20 08:17:48 | 000,026,624 | ---- | M] (Microsoft Corporation) MD5=61AC3EFDFACFDD3F0F11DD4FD4044223 -- C:\Windows\SysWOW64\userinit.exe
[2010/11/20 08:17:48 | 000,026,624 | ---- | M] (Microsoft Corporation) MD5=61AC3EFDFACFDD3F0F11DD4FD4044223 -- C:\Windows\winsxs\x86_microsoft-windows-userinit_31bf3856ad364e35_6.1.7601.17514_none_de3024012ff21116\userinit.exe
[2009/07/13 21:14:43 | 000,026,112 | ---- | M] (Microsoft Corporation) MD5=6DE80F60D7DE9CE6B8C2DDFDF79EF175 -- C:\Windows\winsxs\x86_microsoft-windows-userinit_31bf3856ad364e35_6.1.7600.16385_none_dbff103933038d7c\userinit.exe
[2009/07/13 21:39:48 | 000,030,208 | ---- | M] (Microsoft Corporation) MD5=6F8F1376A13114CC10C0E69274F5A4DE -- C:\Windows\winsxs\amd64_microsoft-windows-userinit_31bf3856ad364e35_6.1.7600.16385_none_381dabbceb60feb2\userinit.exe
[2010/11/20 09:25:24 | 000,030,720 | ---- | M] (Microsoft Corporation) MD5=BAFE84E637BF7388C96EF48D4D3FDD53 -- C:\Windows\SysNative\userinit.exe
[2010/11/20 09:25:24 | 000,030,720 | ---- | M] (Microsoft Corporation) MD5=BAFE84E637BF7388C96EF48D4D3FDD53 -- C:\Windows\winsxs\amd64_microsoft-windows-userinit_31bf3856ad364e35_6.1.7601.17514_none_3a4ebf84e84f824c\userinit.exe
< MD5 for: WINLOGON.EXE >
[2010/11/20 09:25:30 | 000,390,656 | ---- | M] (Microsoft Corporation) MD5=1151B1BAA6F350B1DB6598E0FEA7C457 -- C:\Windows\SysNative\winlogon.exe
[2010/11/20 09:25:30 | 000,390,656 | ---- | M] (Microsoft Corporation) MD5=1151B1BAA6F350B1DB6598E0FEA7C457 -- C:\Windows\winsxs\amd64_microsoft-windows-winlogon_31bf3856ad364e35_6.1.7601.17514_none_cde90685eb910636\winlogon.exe
[2009/07/13 21:39:52 | 000,389,120 | ---- | M] (Microsoft Corporation) MD5=132328DF455B0028F13BF0ABEE51A63A -- C:\Windows\winsxs\amd64_microsoft-windows-winlogon_31bf3856ad364e35_6.1.7600.16385_none_cbb7f2bdeea2829c\winlogon.exe
[2009/10/28 03:01:57 | 000,389,632 | ---- | M] (Microsoft Corporation) MD5=A93D41A4D4B0D91C072D11DD8AF266DE -- C:\Windows\winsxs\amd64_microsoft-windows-winlogon_31bf3856ad364e35_6.1.7600.20560_none_cc522fd507b468f8\winlogon.exe
[2009/10/28 02:24:40 | 000,389,632 | ---- | M] (Microsoft Corporation) MD5=DA3E2A6FA9660CC75B471530CE88453A -- C:\Windows\winsxs\amd64_microsoft-windows-winlogon_31bf3856ad364e35_6.1.7600.16447_none_cbe534e7ee8042ad\winlogon.exe
< %systemdrive%\$Recycle.Bin|@;true;true;true >
< HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\BITS /s >
"DisplayName" = @%SystemRoot%\system32\qmgr.dll,-1000
"ImagePath" = %SystemRoot%\System32\svchost.exe -k netsvcs -- [2009/07/13 21:14:41 | 000,020,992 | ---- | M] (Microsoft Corporation)
"Description" = @%SystemRoot%\system32\qmgr.dll,-1001
"ObjectName" = LocalSystem
"ErrorControl" = 1
"Start" = 2
"DelayedAutoStart" = 1
"Type" = 32
"DependOnService" = RpcSsEventSystem [binary data]
"ServiceSidType" = 1
"RequiredPrivileges" = SeCreateGlobalPrivilegeSeImperson [Binary data over 200 bytes]
"FailureActions" = 80 51 01 00 00 00 00 00 00 00 00 00 03 00 00 00 14 00 00 00 01 00 00 00 60 EA 00 00 01 00 00 00 C0 D4 01 00 00 00 00 00 00 00 00 00 [binary data]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\BITS\Parameters]
"ServiceDll" = %SystemRoot%\System32\qmgr.dll
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\BITS\Performance]
"Library" = bitsperf.dll -- [2010/11/20 08:18:07 | 000,019,456 | ---- | M] (Microsoft Corporation)
"Open" = PerfMon_Open
"Collect" = PerfMon_Collect
"Close" = PerfMon_Close
"InstallType" = 1
"PerfIniFile" = bitsctrs.ini
"First Counter" = 2156
"Last Counter" = 2172
"First Help" = 2157
"Last Help" = 2173
"Object List" = 2156
"PerfMMFileName" = Global\MMF_BITS_s
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\BITS\Security]
"Security" = 01 00 14 80 90 00 00 00 A0 00 00 00 14 00 00 00 34 00 00 00 02 00 20 00 01 00 00 00 02 C0 18 00 00 00 0C 00 01 02 00 00 00 00 00 05 20 00 00 00 20 02 00 00 02 00 5C 00 04 00 00 00 00 02 14 00 FF 01 0F 00 01 01 00 00 00 00 00 05 12 00 00 00 00 00 18 00 FF 01 0F 00 01 02 00 00 00 00 00 05 20 00 00 00 20 02 00 00 00 00 14 00 8D 01 02 00 01 01 00 00 00 00 00 05 04 00 00 00 00 00 14 00 8D 01 02 00 01 01 00 00 00 00 00 05 06 00 00 00 01 02 00 00 00 00 00 05 20 00 00 00 20 02 00 00 01 02 00 00 00 00 00 05 20 00 00 00 20 02 00 00 [Binary data over 200 bytes]
========== Alternate Data Streams ==========
@Alternate Data Stream - 169 bytes -> C:\ProgramData\Temp:0B4227B4
< End of report >
Attached Files
Edited by Essexboy, 09 September 2012 - 05:12 AM.
#4
![Massive Sality executable file infection [Solved]: post #4](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2012 - 05:22 AM
Posted 09 September 2012 - 05:22 AM

Warning This fix is only relevant for this system and no other, using on another computer may cause problems
Be advised that when the fix commences it will shut down all running processes and you may lose the desktop and icons, they will return on reboot
Run OTL
- Under the Custom Scans/Fixes box at the bottom, paste in the following
:OTL IE - HKLM\..\SearchScopes\{8A96AF9E-4074-43b7-BEA3-87217BDA7406}: "URL" = http://www.searchqu....q={searchTerms} IE - HKLM\..\SearchScopes\{ac2e4ae7-2d16-45ea-991c-2441dfd05696}: "URL" = http://search.mywebs...r={searchTerms} IE - HKLM\..\SearchScopes\{afdbddaa-5d3f-42ee-b79c-185a7020515b}: "URL" = http://search.condui...&ctid=CT2786678 IE - HKU\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyOverride" = 127.0.0.1:9421;<local> IE - HKU\S-1-5-18\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyOverride" = 127.0.0.1:9421;<local> IE - HKLM\..\URLSearchHook: {97bceb59-cfcd-4b16-a863-b3f72cf9f196} - SOFTWARE\Classes\CLSID\{97bceb59-cfcd-4b16-a863-b3f72cf9f196}\InprocServer32 File not found IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes\{0ECDF796-C2DC-4d79-A620-CCE0C0A66CC9}: "URL" = http://search.babylo...000701a04849685 IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\SearchScopes\{ac2e4ae7-2d16-45ea-991c-2441dfd05696}: "URL" = http://search.mywebs...r={searchTerms} IE - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyOverride" = 127.0.0.1:9421;<local> FF - prefs.js..browser.search.defaultenginename: "Search the web (Babylon)" FF - prefs.js..browser.search.defaulturl: "http://search.conduit.com/ResultsExt.aspx?ctid=CT3072253&SearchSource=3&q={searchTerms}" FF - prefs.js..browser.search.order.1: "Search the web (Babylon)" FF - prefs.js..extensions.enabledAddons: [email protected]:1.20.00 FF - prefs.js..extensions.enabledAddons: {EB9394A3-4AD6-4918-9537-31A1FD8E8EDF}:2.0 FF - prefs.js..extensions.enabledAddons: [email protected]:0.83.32 FF - prefs.js..extensions.enabledAddons: [email protected]:0.6.20120813 [2012/08/13 06:39:37 | 000,000,000 | ---D | M] (DealPly) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\{EB9394A3-4AD6-4918-9537-31A1FD8E8EDF} [2012/09/07 04:19:55 | 000,000,000 | ---D | M] ("Coupon Companion") -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\[email protected] [2012/06/19 22:25:17 | 000,000,000 | ---D | M] (Babylon) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\[email protected] [2012/07/08 22:10:58 | 000,000,000 | ---D | M] (Yontoo) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\Firefox\Profiles\9opbbadv.default\extensions\[email protected] [2012/08/16 23:01:42 | 002,282,511 | ---- | M] () (No name found) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\firefox\profiles\9opbbadv.default\extensions\[email protected] [2012/07/24 23:52:09 | 000,741,958 | ---- | M] () (No name found) -- C:\Users\joeniqua c\AppData\Roaming\mozilla\firefox\profiles\9opbbadv.default\extensions\{d10d0bf8-f5b5-c8b4-a8b2-2b9879e08c5d}.xpi [2012/06/19 22:25:00 | 000,002,352 | ---- | M] () -- C:\Program Files (x86)\mozilla firefox\searchplugins\babylon.xml O2 - BHO: (Coupon Companion) - {11111111-1111-1111-1111-110011441193} - Reg Error: Value error. File not found O2 - BHO: (2YourFace Addon) - {1185823F-F22F-4027-80E5-4F68ACD5DE5E} - C:\Users\joeniqua c\AppData\Roaming\2YourFace\bho.dll () O2 - BHO: (BitZipperSearch Toolbar) - {97bceb59-cfcd-4b16-a863-b3f72cf9f196} - C:\Program Files (x86)\BitZipperSearch\prxtbBit0.dll File not found O2 - BHO: (Searchqu Toolbar) - {99079a25-328f-4bd4-be04-00955acaa0a7} - C:\PROGRA~2\WI3C8A~1\ToolBar\searchqudtx.dll File not found O2 - BHO: (DealPly) - {A6174F27-1FFF-E1D6-A93F-BA48AD5DD448} - C:\Program Files (x86)\DealPly\DealPlyIE.dll (DealPly Technologies Ltd) O2 - BHO: (Yontoo) - {FD72061E-9FDE-484D-A58A-0BAB4151CAD8} - Reg Error: Value error. File not found O3:64bit: - HKLM\..\Toolbar: (no name) - !{2318C2B1-4965-11d4-9B18-009027A5CD4F} - No CLSID value found. O3:64bit: - HKLM\..\Toolbar: (no name) - !{687578b9-7132-4a7a-80e4-30ee31099e03} - No CLSID value found. O3:64bit: - HKLM\..\Toolbar: (no name) - !{95B7759C-8C7F-4BF1-B163-73684A933233} - No CLSID value found. O3:64bit: - HKLM\..\Toolbar: (no name) - !{bf7380fa-e3b4-4db2-af3e-9d8783a45bfc} - No CLSID value found. O3:64bit: - HKLM\..\Toolbar: (no name) - 10 - No CLSID value found. O3:64bit: - HKLM\..\Toolbar: (no name) - Locked - No CLSID value found. O3 - HKLM\..\Toolbar: (BitZipperSearch Toolbar) - {97bceb59-cfcd-4b16-a863-b3f72cf9f196} - C:\Program Files (x86)\BitZipperSearch\prxtbBit0.dll File not found O3 - HKLM\..\Toolbar: (Searchqu Toolbar) - {99079a25-328f-4bd4-be04-00955acaa0a7} - C:\PROGRA~2\WI3C8A~1\ToolBar\searchqudtx.dll File not found O3 - HKLM\..\Toolbar: (no name) - 10 - No CLSID value found. O3 - HKLM\..\Toolbar: (no name) - Locked - No CLSID value found. O3 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\..\Toolbar\WebBrowser: (BitZipperSearch Toolbar) - {97BCEB59-CFCD-4B16-A863-B3F72CF9F196} - C:\Program Files (x86)\BitZipperSearch\prxtbBit0.dll File not found O4 - HKLM..\Run: [PC Cleaners] C:\Program Files (x86)\PC Cleaners\PCCleaners.exe (PC Cleaners Inc.) O4 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001..\Run: [bqyfq] C:\Users\JOENIQ~1\AppData\Local\Temp\Bash2.exe File not found O4 - Startup: C:\Users\joeniqua c\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Full glass.exe () O7 - HKU\.DEFAULT\Software\Policies\Microsoft\Internet Explorer\Restrictions present O7 - HKU\S-1-5-18\Software\Policies\Microsoft\Internet Explorer\Restrictions present O7 - HKU\S-1-5-19\Software\Policies\Microsoft\Internet Explorer\Restrictions present O7 - HKU\S-1-5-20\Software\Policies\Microsoft\Internet Explorer\Restrictions present O7 - HKU\S-1-5-21-1311796233-3422863359-2725502379-1001\Software\Policies\Microsoft\Internet Explorer\Restrictions present O20:64bit: - AppInit_DLLs: (C:\PROGRA~2\WI3C8A~1\Datamngr\x64\datamngr.dll) - File not found O20:64bit: - AppInit_DLLs: (C:\PROGRA~2\WI3C8A~1\Datamngr\x64\IEBHO.dll) - File not found [2012/09/08 07:07:11 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\PC Cleaners [2012/09/08 07:07:06 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\PC Cleaners [2012/09/08 07:07:05 | 004,571,960 | ---- | C] (PC Cleaners) -- C:\Windows\uninst.exe [2012/09/08 07:07:03 | 000,000,000 | ---D | C] -- C:\Users\joeniqua c\AppData\Roaming\PCPro [2012/09/08 07:07:03 | 000,000,000 | ---D | C] -- C:\ProgramData\PC1Data [2012/09/08 07:07:03 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\PC Cleaners [2012/08/13 06:33:32 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DealPly [2012/08/13 06:33:24 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\DealPly [2012/06/19 22:25:49 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\2YourFace [2012/06/19 22:24:39 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\Babylon [2010/06/10 17:21:11 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\BitZipper [2012/09/08 07:07:11 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\PC Cleaners [2012/09/08 07:07:14 | 000,000,000 | ---D | M] -- C:\Users\joeniqua c\AppData\Roaming\PCPro :Files ipconfig /flushdns /c netsh int ip reset c:\resetlog.txt /c ipconfig /release /c ipconfig /renew /c :Commands [purity] [resethosts] [emptytemp] [CREATERESTOREPOINT] [Reboot] - Then click the Run Fix button at the top
- Let the program run unhindered, reboot the PC when it is done
- Open OTL again and click the Quick Scan button. Post the log it produces in your next reply.
THEN
Download the latest version of TDSSKiller from here and save it to your Desktop.
- Doubleclick on TDSSKiller.exe to run the application
- Then click on Change parameters.
- Check the boxes beside Verify Driver Digital Signature and Detect TDLFS file system, then click OK.
- Click the Start Scan button.
- If a suspicious object is detected, the default action will be Skip, click on Continue.
- If malicious objects are found, they will show in the Scan results and offer three (3) options.
- Ensure Cure is selected, then click Continue => Reboot now to finish the cleaning process.
- Get the report by selecting Reports
- Note: If Cure is not available, please choose Skip instead, do not choose Delete unless instructed.
Please copy and paste its contents on your next reply.
#5
![Massive Sality executable file infection [Solved]: post #5](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2012 - 06:22 AM
Posted 09 September 2012 - 06:22 AM

Attached Files
#6
![Massive Sality executable file infection [Solved]: post #6](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2012 - 06:24 AM
Posted 09 September 2012 - 06:24 AM

Download and Install Combofix
Download ComboFix from one of the following locations:
Link 1
Link 2
VERY IMPORTANT !!! Save ComboFix.exe to your Desktop
* IMPORTANT - Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools. If you have difficulty properly disabling your protective programs, refer to this link here
- Double click on ComboFix.exe & follow the prompts.
- Accept the disclaimer and allow to update if it asks
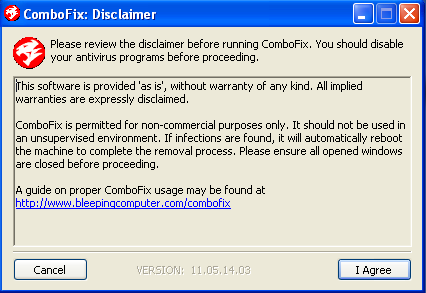
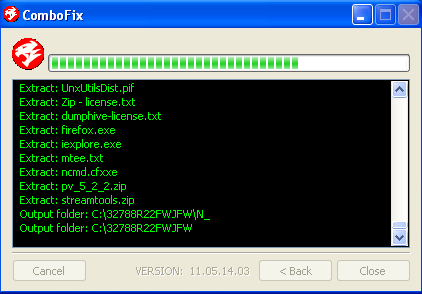
- When finished, it shall produce a log for you.
- Please include the C:\ComboFix.txt in your next reply.
Notes:
1. Do not mouse-click Combofix's window while it is running. That may cause it to stall.
2. Do not "re-run" Combofix. If you have a problem, reply back for further instructions.
3. If after the reboot you get errors about programmes being marked for deletion then reboot, that will cure it.
Please make sure you include the combo fix log in your next reply as well as describe how your computer is running now
#7
![Massive Sality executable file infection [Solved]: post #7](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2012 - 06:49 AM
Posted 09 September 2012 - 06:49 AM

Attached Files
Edited by insecure5082, 09 September 2012 - 06:53 AM.
#8
![Massive Sality executable file infection [Solved]: post #8](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2012 - 07:11 AM
Posted 09 September 2012 - 07:11 AM

#9
![Massive Sality executable file infection [Solved]: post #9](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2012 - 07:19 AM
Posted 09 September 2012 - 07:19 AM

Edited by insecure5082, 09 September 2012 - 07:20 AM.
#10
![Massive Sality executable file infection [Solved]: post #10](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2012 - 07:51 AM
Posted 09 September 2012 - 07:51 AM

Please download the following programmes to your desktop:
Dr Web Live CD
ImgBurn
Install IMGBurn
- Double click Dr Web
- IMGBurn will open
- Burn the ISO to a cd
- Reboot the infected computer with the CD in the drive
- Ensure that the first boot device is CD - If you are not sure about that then see this page for instructions
- As loading starts, a dialogue window will prompt you to choose between the standard and safe modes.
- Use arrow keys to select DrWeb-LiveCD (Default)
- When the system is loaded, check the disks or folders you want to scan, and click on Start.
- The programme will now scan for and cure/delete any malware that it finds. Allow it to do so
- Once completed reboot to normal windows
- No log is produced so once in normal windows run a fresh OTL scan and let me know if the problems persist
#11
![Massive Sality executable file infection [Solved]: post #11](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2012 - 04:12 PM
Posted 09 September 2012 - 04:12 PM

Attached Files
#12
![Massive Sality executable file infection [Solved]: post #12](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 September 2012 - 03:27 AM
Posted 10 September 2012 - 03:27 AM

Download and burn on a different system. This may be to deeply rooted to cure I am afraid, but lets give Dr Web a try
#13
![Massive Sality executable file infection [Solved]: post #13](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 September 2012 - 06:11 AM
Posted 10 September 2012 - 06:11 AM

#14
![Massive Sality executable file infection [Solved]: post #14](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 September 2012 - 07:27 AM
Posted 10 September 2012 - 07:27 AM

1. Close any open browsers.
2. Close/disable all anti virus and anti malware programs so they do not interfere with the running of ComboFix.
3. Open notepad and copy/paste the text in the quotebox below into it:
Save this as CFScript.txt, in the same location as ComboFix.exeRenv::
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A01 - easy - Identifying while-do Loops .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A02 - easy - Identifying for Loops .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A03 - easy - Identifying Local Variables .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A04 - easy - Identifying Register Variables .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A05 - easy - Identifying the - Operator .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A06 - easy - Identifying the + Operator .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A07 - easy - Identifying the Conditional Operator .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A08 - easy - Pass Global Variables Explicitly .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A09 - easy - Passing Arguments via Registers .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment A10 - easy - Passing Floating-Point Arguments to a Function .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment B01 - normal - Calling a Function Using a Pointer .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment B02 - normal - Elementary Integer-Float Relationships Using Visual C++ .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment B03 - normal - Identifying an Object and Its Structure .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment B04 - normal - Identifying the Asterisk Operator .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment B05 - normal - Identifying the continue Statement .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment B06 - normal - Passing the 'this' Implicit Argument .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment B07 - normal - The Result of Adding the Constant to the Pointer Is Written into the Pointer-Type Variable .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment B08 - normal - various 1 .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C01 - medium - A Constructor-Destructor for a Global Object .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C02 - medium - A Constructor-Destructor for an Object on the Stack .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C03 - medium - An Analysis of the Code That Manipulates Strings .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C04 - medium - Call a Virtual Function .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C05 - medium - Calling a Function Using a Pointer and a Complassessment Calculation of the Target Address .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C06 - medium - Distinguishing PASCAL from stdcall .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C07 - medium - Identifying the Division Operator .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C08 - medium - Identifying the Percent Operator .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C09 - medium - Passing a Structure Pointer to a Function .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment C10 - medium - Problem of Eliminating Structures at Compile Time .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment D01 - hard - Calling a Pure Virtual Function .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment D02 - hard - Calling a Static Virtual Function .exe
c:\windows\TacoFilez\Prams\binary-auditing-training-package\binary-auditing-training-package\003.02 - hll mapping\assessment D03 - hard - Distinguishing an Imitation from a True Virtual Table .exe

Refering to the picture above, drag CFScript into ComboFix.exeWhen finished, it shall produce a log for you at C:\ComboFix.txt which I will require in your next reply.
Notes:
1. Do not mouse-click Combofix's window while it is running. That may cause it to stall.
2. Do not "re-run" Combofix. If you have a problem, reply back for further instructions.
3. If after the reboot you get errors about programmes being marked for deletion then reboot, that will cure it.
#15
![Massive Sality executable file infection [Solved]: post #15](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 September 2012 - 04:43 PM
Posted 10 September 2012 - 04:43 PM

Attached Files
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked






 Sign In
Sign In Create Account
Create Account

