OTL log:
OTL logfile created on: 11/12/2012 9:01:11 PM - Run 5
OTL by OldTimer - Version 3.2.69.0 Folder = C:\Users\Brian Hillard\Desktop
64bit- Home Premium Edition Service Pack 1 (Version = 6.1.7601) - Type = NTWorkstation
Internet Explorer (Version = 9.0.8112.16421)
Locale: 00000409 | Country: United States | Language: ENU | Date Format: M/d/yyyy
5.95 Gb Total Physical Memory | 4.19 Gb Available Physical Memory | 70.40% Memory free
11.90 Gb Paging File | 10.09 Gb Available in Paging File | 84.80% Paging File free
Paging file location(s): ?:\pagefile.sys [binary data]
%SystemDrive% = C: | %SystemRoot% = C:\windows | %ProgramFiles% = C:\Program Files (x86)
Drive C: | 682.64 Gb Total Space | 527.74 Gb Free Space | 77.31% Space Free | Partition Type: NTFS
Computer Name: BRIANHILLARD-PC | User Name: Brian Hillard | Logged in as Administrator.
Boot Mode: Normal | Scan Mode: Current user | Quick Scan | Include 64bit Scans
Company Name Whitelist: On | Skip Microsoft Files: On | No Company Name Whitelist: On | File Age = 30 Days
========== Processes (SafeList) ========== PRC - [2012/10/18 21:34:14 | 000,602,112 | ---- | M] (OldTimer Tools) -- C:\Users\Brian Hillard\Desktop\OTL.exe
PRC - [2012/07/27 15:51:26 | 000,063,960 | ---- | M] (Adobe Systems Incorporated) -- C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\armsvc.exe
PRC - [2012/06/15 21:24:19 | 000,138,272 | R--- | M] (Symantec Corporation) -- C:\Program Files (x86)\Norton Internet Security\Engine\19.9.0.9\ccsvchst.exe
PRC - [2012/06/15 18:07:23 | 000,686,280 | ---- | M] (Adobe Systems Incorporated) -- C:\Windows\SysWOW64\Macromed\Flash\FlashUtil32_11_3_300_257_ActiveX.exe
PRC - [2011/07/19 10:59:30 | 000,126,392 | R--- | M] (Symantec Corporation) -- C:\Program Files (x86)\Norton PC Checkup\Engine\2.0.13.11\ccSvcHst.exe
PRC - [2011/07/19 10:48:25 | 000,123,320 | R--- | M] (Symantec Corporation) -- C:\Program Files (x86)\Norton PC Checkup\Engine\2.0.13.11\SymcPCCULaunchSvc.exe
PRC - [2010/12/20 20:30:38 | 002,656,280 | ---- | M] (Intel Corporation) -- C:\Program Files (x86)\Intel\Intel® Management Engine Components\UNS\UNS.exe
PRC - [2010/12/20 20:30:36 | 000,325,656 | ---- | M] (Intel Corporation) -- C:\Program Files (x86)\Intel\Intel® Management Engine Components\LMS\LMS.exe
PRC - [2009/05/08 05:53:34 | 000,174,424 | ---- | M] (Yahoo! Inc.) -- C:\Program Files (x86)\Yahoo!\Common\YMailAdvisor.exe
PRC - [2008/11/09 15:48:14 | 000,602,392 | ---- | M] (Yahoo! Inc.) -- C:\Program Files (x86)\Yahoo!\SoftwareUpdate\YahooAUService.exe
PRC - [2008/07/17 16:12:24 | 000,161,064 | ---- | M] (Seagate Technology LLC) -- C:\Program Files (x86)\Seagate\SeagateManager\Sync\FreeAgentService.exe
PRC - [2008/07/17 16:12:04 | 000,177,448 | ---- | M] (Seagate LLC) -- C:\Program Files (x86)\Seagate\SeagateManager\FreeAgent Status\stxmenumgr.exe
========== Modules (No Company Name) ========== MOD - [2011/09/27 07:23:00 | 000,087,912 | ---- | M] () -- C:\Program Files (x86)\Common Files\Apple\Apple Application Support\zlib1.dll
MOD - [2011/09/27 07:22:40 | 001,242,472 | ---- | M] () -- C:\Program Files (x86)\Common Files\Apple\Apple Application Support\libxml2.dll
========== Services (SafeList) ========== SRV:
64bit: - [2011/07/01 13:46:14 | 000,828,856 | ---- | M] (TOSHIBA Corporation) [On_Demand | Running] -- C:\Program Files\Toshiba\TPHM\TPCHSrv.exe -- (TPCHSrv)
SRV:
64bit: - [2011/06/09 23:10:00 | 000,138,152 | ---- | M] (TOSHIBA Corporation) [On_Demand | Running] -- C:\Program Files\Toshiba\TOSHIBA HDD SSD Alert\TosSmartSrv.exe -- (TOSHIBA HDD SSD Alert Service)
SRV:
64bit: - [2011/05/24 11:58:12 | 000,294,848 | ---- | M] (TOSHIBA Corporation) [Auto | Running] -- C:\Program Files\Toshiba\TECO\TecoService.exe -- (TOSHIBA eco Utility Service)
SRV:
64bit: - [2011/05/17 16:34:18 | 000,574,896 | ---- | M] (TOSHIBA Corporation) [Auto | Running] -- C:\Program Files\Toshiba\Power Saver\TosCoSrv.exe -- (TosCoSrv)
SRV:
64bit: - [2010/10/20 16:41:00 | 000,138,656 | ---- | M] (TOSHIBA Corporation) [Auto | Running] -- C:\Windows\SysNative\TODDSrv.exe -- (TODDSrv)
SRV:
64bit: - [2010/09/22 20:10:10 | 000,057,184 | ---- | M] (Microsoft Corporation) [Disabled | Stopped] -- C:\Program Files\Windows Live\Mesh\wlcrasvc.exe -- (wlcrasvc)
SRV:
64bit: - [2009/07/13 20:41:27 | 001,011,712 | ---- | M] (Microsoft Corporation) [On_Demand | Stopped] -- C:\Program Files\Windows Defender\MpSvc.dll -- (WinDefend)
SRV - [2012/07/27 15:51:26 | 000,063,960 | ---- | M] (Adobe Systems Incorporated) [Auto | Running] -- C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\armsvc.exe -- (AdobeARMservice)
SRV - [2012/06/15 21:24:19 | 000,138,272 | R--- | M] (Symantec Corporation) [Auto | Running] -- C:\Program Files (x86)\Norton Internet Security\Engine\19.9.0.9\ccSvcHst.exe -- (NIS)
SRV - [2011/07/19 10:59:30 | 000,126,392 | R--- | M] (Symantec Corporation) [Auto | Running] -- C:\Program Files (x86)\Norton PC Checkup\Engine\2.0.13.11\ccSvcHst.exe -- (PCCUJobMgr)
SRV - [2011/07/19 10:48:25 | 000,123,320 | R--- | M] (Symantec Corporation) [Auto | Running] -- C:\Program Files (x86)\Norton PC Checkup\Engine\2.0.13.11\SymcPCCULaunchSvc.exe -- (Norton PC Checkup Application Launcher)
SRV - [2011/07/11 19:16:06 | 000,057,216 | ---- | M] (TOSHIBA Corporation) [On_Demand | Running] -- C:\Program Files (x86)\TOSHIBA\TOSHIBA Service Station\TMachInfo.exe -- (TMachInfo)
SRV - [2010/12/20 20:30:38 | 002,656,280 | ---- | M] (Intel Corporation) [Auto | Running] -- C:\Program Files (x86)\Intel\Intel® Management Engine Components\UNS\UNS.exe -- (UNS)
SRV - [2010/12/20 20:30:36 | 000,325,656 | ---- | M] (Intel Corporation) [Auto | Running] -- C:\Program Files (x86)\Intel\Intel® Management Engine Components\LMS\LMS.exe -- (LMS)
SRV - [2010/10/12 12:59:12 | 000,206,072 | ---- | M] (WildTangent, Inc.) [On_Demand | Stopped] -- C:\Program Files (x86)\WildTangent Games\App\GamesAppService.exe -- (GamesAppService)
SRV - [2010/03/18 13:16:28 | 000,130,384 | ---- | M] (Microsoft Corporation) [Auto | Stopped] -- C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -- (clr_optimization_v4.0.30319_32)
SRV - [2009/06/10 16:23:09 | 000,066,384 | ---- | M] (Microsoft Corporation) [Disabled | Stopped] -- C:\Windows\Microsoft.NET\Framework\v2.0.50727\mscorsvw.exe -- (clr_optimization_v2.0.50727_32)
SRV - [2008/11/09 15:48:14 | 000,602,392 | ---- | M] (Yahoo! Inc.) [Auto | Running] -- C:\Program Files (x86)\Yahoo!\SoftwareUpdate\YahooAUService.exe -- (YahooAUService)
SRV - [2008/07/17 16:12:24 | 000,161,064 | ---- | M] (Seagate Technology LLC) [Auto | Running] -- C:\Program Files (x86)\Seagate\SeagateManager\Sync\FreeAgentService.exe -- (FreeAgentGoNext Service)
========== Driver Services (SafeList) ========== DRV:
64bit: - [2012/08/21 12:01:20 | 000,033,240 | ---- | M] (GEAR Software Inc.) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\GEARAspiWDM.sys -- (GEARAspiWDM)
DRV:
64bit: - [2012/07/09 12:42:54 | 000,052,736 | ---- | M] (Apple, Inc.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\usbaapl64.sys -- (USBAAPL64)
DRV:
64bit: - [2012/07/05 21:17:58 | 000,037,536 | ---- | M] (Symantec Corporation) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\NISx64\1309000.009\srtspx64.sys -- (SRTSPX)
DRV:
64bit: - [2012/07/05 21:17:57 | 000,737,952 | ---- | M] (Symantec Corporation) [File_System | On_Demand | Running] -- C:\Windows\SysNative\drivers\NISx64\1309000.009\srtsp64.sys -- (SRTSP)
DRV:
64bit: - [2012/06/06 23:43:38 | 000,167,072 | ---- | M] (Symantec Corporation) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\NISx64\1309000.009\ccsetx64.sys -- (ccSet_NIS)
DRV:
64bit: - [2012/05/21 20:37:12 | 001,129,120 | ---- | M] (Symantec Corporation) [File_System | Boot | Running] -- C:\Windows\SysNative\drivers\NISx64\1309000.009\symefa64.sys -- (SymEFA)
DRV:
64bit: - [2012/04/17 21:13:32 | 000,405,624 | ---- | M] (Symantec Corporation) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\NISx64\1309000.009\symnets.sys -- (SymNetS)
DRV:
64bit: - [2012/04/17 20:42:14 | 000,190,072 | ---- | M] (Symantec Corporation) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\NISx64\1309000.009\ironx64.sys -- (SymIRON)
DRV:
64bit: - [2012/03/29 01:28:34 | 000,043,640 | R--- | M] (Symantec Corporation) [Kernel | System | Running] -- C:\Windows\SysNative\drivers\SymIMV.sys -- (SymIM)
DRV:
64bit: - [2012/03/23 21:47:34 | 000,175,736 | ---- | M] (Symantec Corporation) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\SYMEVENT64x86.SYS -- (SymEvent)
DRV:
64bit: - [2012/03/01 01:46:16 | 000,023,408 | ---- | M] (Microsoft Corporation) [Recognizer | Boot | Unknown] -- C:\windows\SysNative\drivers\fs_rec.sys -- (Fs_Rec)
DRV:
64bit: - [2011/08/01 15:59:06 | 000,045,416 | ---- | M] (Microsoft Corporation) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\point64.sys -- (Point64)
DRV:
64bit: - [2011/07/28 18:37:10 | 000,052,584 | ---- | M] (Microsoft Corporation) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\dc3d.sys -- (dc3d)
DRV:
64bit: - [2011/07/25 21:18:36 | 000,451,192 | R--- | M] (Symantec Corporation) [Kernel | Boot | Running] -- C:\Windows\SysNative\drivers\NISx64\1309000.009\symds64.sys -- (SymDS)
DRV:
64bit: - [2011/07/08 19:06:08 | 000,307,304 | ---- | M] (Realtek Semiconductor Corp.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\rtsuvstor.sys -- (RSUSBVSTOR)
DRV:
64bit: - [2011/07/07 17:02:16 | 001,576,576 | ---- | M] (Conexant Systems Inc.) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\CHDRT64.sys -- (CnxtHdAudService)
DRV:
64bit: - [2011/04/04 22:10:14 | 012,262,624 | ---- | M] (Intel Corporation) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\igdkmd64.sys -- (igfx)
DRV:
64bit: - [2011/03/11 01:41:12 | 000,107,904 | ---- | M] (Advanced Micro Devices) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\amdsata.sys -- (amdsata)
DRV:
64bit: - [2011/03/11 01:41:12 | 000,027,008 | ---- | M] (Advanced Micro Devices) [Kernel | Boot | Running] -- C:\Windows\SysNative\drivers\amdxata.sys -- (amdxata)
DRV:
64bit: - [2011/02/08 21:07:00 | 000,038,096 | ---- | M] (TOSHIBA Corporation) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\PGEffect.sys -- (PGEffect)
DRV:
64bit: - [2011/02/03 21:59:06 | 001,413,680 | ---- | M] (Synaptics Incorporated) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\SynTP.sys -- (SynTP)
DRV:
64bit: - [2011/01/12 19:51:44 | 000,439,320 | ---- | M] (Intel Corporation) [Kernel | Boot | Running] -- C:\Windows\SysNative\drivers\iaStor.sys -- (iaStor)
DRV:
64bit: - [2011/01/05 03:08:58 | 001,109,096 | ---- | M] (Realtek Semiconductor Corporation ) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\rtl8192ce.sys -- (RTL8192Ce)
DRV:
64bit: - [2010/12/01 18:12:06 | 000,250,984 | ---- | M] (Realtek Semiconductor Corp.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\RtsUStor.sys -- (RSUSBSTOR)
DRV:
64bit: - [2010/11/20 22:24:33 | 000,059,392 | ---- | M] (Microsoft Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\TsUsbFlt.sys -- (TsUsbFlt)
DRV:
64bit: - [2010/11/20 22:23:47 | 000,078,720 | ---- | M] (Hewlett-Packard Company) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\HpSAMD.sys -- (HpSAMD)
DRV:
64bit: - [2010/11/20 22:23:47 | 000,031,232 | ---- | M] (Microsoft Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\TsUsbGD.sys -- (TsUsbGD)
DRV:
64bit: - [2010/11/08 14:44:40 | 000,076,912 | ---- | M] (Atheros Communications, Inc.) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\L1C62x64.sys -- (L1C)
DRV:
64bit: - [2010/10/19 18:34:26 | 000,056,344 | ---- | M] (Intel Corporation) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\HECIx64.sys -- (MEIx64)
DRV:
64bit: - [2010/10/15 03:28:16 | 000,317,440 | ---- | M] (Intel® Corporation) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\IntcDAud.sys -- (IntcDAud)
DRV:
64bit: - [2009/07/30 22:22:04 | 000,027,784 | ---- | M] (TOSHIBA Corporation.) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\tdcmdpst.sys -- (tdcmdpst)
DRV:
64bit: - [2009/07/14 17:31:18 | 000,026,840 | ---- | M] (TOSHIBA Corporation) [Kernel | Boot | Running] -- C:\Windows\SysNative\drivers\TVALZ_O.SYS -- (TVALZ)
DRV:
64bit: - [2009/07/13 20:52:20 | 000,194,128 | ---- | M] (AMD Technologies Inc.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\amdsbs.sys -- (amdsbs)
DRV:
64bit: - [2009/07/13 20:48:04 | 000,065,600 | ---- | M] (LSI Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\lsi_sas2.sys -- (LSI_SAS2)
DRV:
64bit: - [2009/07/13 20:45:55 | 000,024,656 | ---- | M] (Promise Technology) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\stexstor.sys -- (stexstor)
DRV:
64bit: - [2009/06/24 17:36:48 | 000,482,384 | ---- | M] (TOSHIBA Corporation) [Kernel | Boot | Running] -- C:\Windows\SysNative\drivers\tos_sps64.sys -- (tos_sps64)
DRV:
64bit: - [2009/06/19 21:15:22 | 000,014,472 | ---- | M] (TOSHIBA Corporation) [Kernel | Auto | Running] -- C:\Windows\SysNative\drivers\TVALZFL.sys -- (TVALZFL)
DRV:
64bit: - [2009/06/15 15:58:50 | 000,012,800 | ---- | M] (TOSHIBA) [Kernel | On_Demand | Running] -- C:\Windows\SysNative\drivers\QIOMem.sys -- (QIOMem)
DRV:
64bit: - [2009/06/10 16:01:11 | 001,485,312 | ---- | M] (Conexant Systems, Inc.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\VSTDPV6.SYS -- (SrvHsfV92)
DRV:
64bit: - [2009/06/10 16:01:11 | 000,740,864 | ---- | M] (Conexant Systems, Inc.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\VSTCNXT6.SYS -- (SrvHsfWinac)
DRV:
64bit: - [2009/06/10 16:01:11 | 000,292,864 | ---- | M] (Conexant Systems, Inc.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\VSTAZL6.SYS -- (SrvHsfHDA)
DRV:
64bit: - [2009/06/10 15:34:33 | 003,286,016 | ---- | M] (Broadcom Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\evbda.sys -- (ebdrv)
DRV:
64bit: - [2009/06/10 15:34:28 | 000,468,480 | ---- | M] (Broadcom Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\bxvbda.sys -- (b06bdrv)
DRV:
64bit: - [2009/06/10 15:34:23 | 000,270,848 | ---- | M] (Broadcom Corporation) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\b57nd60a.sys -- (b57nd60a)
DRV:
64bit: - [2009/06/10 15:31:59 | 000,031,232 | ---- | M] (Hauppauge Computer Works, Inc.) [Kernel | On_Demand | Stopped] -- C:\Windows\SysNative\drivers\hcw85cir.sys -- (hcw85cir)
DRV - [2012/11/12 01:14:04 | 002,084,000 | ---- | M] (Symantec Corporation) [Kernel | On_Demand | Running] -- C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_19.1.0.28\Definitions\VirusDefs\20121111.008\ex64.sys -- (NAVEX15)
DRV - [2012/11/12 01:14:04 | 000,126,112 | ---- | M] (Symantec Corporation) [Kernel | On_Demand | Running] -- C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_19.1.0.28\Definitions\VirusDefs\20121111.008\eng64.sys -- (NAVENG)
DRV - [2012/11/10 19:45:29 | 000,138,912 | ---- | M] (Symantec Corporation) [Kernel | On_Demand | Running] -- C:\Program Files (x86)\Common Files\Symantec Shared\EENGINE\EraserUtilRebootDrv.sys -- (EraserUtilRebootDrv)
DRV - [2012/11/04 20:35:59 | 000,484,512 | ---- | M] (Symantec Corporation) [Kernel | System | Running] -- C:\Program Files (x86)\Common Files\Symantec Shared\EENGINE\eeCtrl64.sys -- (eeCtrl)
DRV - [2012/10/05 13:23:26 | 001,385,632 | ---- | M] (Symantec Corporation) [Kernel | System | Running] -- C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_19.1.0.28\Definitions\BASHDefs\20121030.002\BHDrvx64.sys -- (BHDrvx64)
DRV - [2012/08/31 19:27:23 | 000,513,184 | ---- | M] (Symantec Corporation) [Kernel | System | Running] -- C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_19.1.0.28\Definitions\IPSDefs\20121109.001\IDSviA64.sys -- (IDSVia64)
DRV - [2009/07/13 20:19:10 | 000,019,008 | ---- | M] (Microsoft Corporation) [File_System | On_Demand | Stopped] -- C:\Windows\SysWOW64\drivers\wimmount.sys -- (WIMMount)
========== Standard Registry (SafeList) ========== ========== Internet Explorer ========== IE:
64bit: - HKLM\..\SearchScopes,DefaultScope =
IE:
64bit: - HKLM\..\SearchScopes\{270DCF97-4042-44CC-BE0B-DF668B4A80D4}: "URL" =
http://www.google.co...ng}&rlz=1I7TSNPIE - HKLM\SOFTWARE\Microsoft\Internet Explorer\Main,Local Page = C:\Windows\SysWOW64\blank.htm
IE - HKLM\..\SearchScopes,DefaultScope =
IE - HKLM\..\SearchScopes\{270DCF97-4042-44CC-BE0B-DF668B4A80D4}: "URL" =
http://www.google.co...ng}&rlz=1I7TSNP IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Default_Page_URL =
http://start.toshiba.comIE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Search Bar =
IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,SearchDefaultBranded = 1
IE - HKCU\SOFTWARE\Microsoft\Internet Explorer\Main,Start Page =
http://www.yahoo.com/IE - HKCU\..\SearchScopes,DefaultScope = {0633EE93-D776-472f-A0FF-E1416B8B2E3A}
IE - HKCU\..\SearchScopes\{270DCF97-4042-44CC-BE0B-DF668B4A80D4}: "URL" =
http://www.google.co...ng}&rlz=1I7TSNPIE - HKCU\..\SearchScopes\{81F5F0B8-320F-4D33-9B73-3ED145016BD3}: "URL" =
http://www.google.co...1I7TSNP_enUS459IE - HKCU\..\SearchScopes\{AFBCB7E0-F91A-4951-9F31-58FEE57A25C4}: "URL" =
http://www.ask.com/w...l&geo=US&ver=19IE - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyEnable" = 0
IE - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings: "ProxyOverride" = *.local
========== FireFox ========== FF:
64bit: - HKLM\Software\MozillaPlugins\@microsoft.com/GENUINE: disabled File not found
FF:
64bit: - HKLM\Software\MozillaPlugins\@Microsoft.com/NpCtrl,version=1.0: c:\Program Files\Microsoft Silverlight\5.1.10411.0\npctrl.dll ( Microsoft Corporation)
FF:
64bit: - HKLM\Software\MozillaPlugins\@microsoft.com/OfficeAuthz,version=14.0: C:\PROGRA~1\MICROS~2\Office14\NPAUTHZ.DLL (Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@adobe.com/FlashPlayer: C:\windows\SysWOW64\Macromed\Flash\NPSWF32.dll ()
FF - HKLM\Software\MozillaPlugins\@Apple.com/iTunes,version=: File not found
FF - HKLM\Software\MozillaPlugins\@Apple.com/iTunes,version=1.0: C:\Program Files (x86)\iTunes\Mozilla Plugins\npitunes.dll ()
FF - HKLM\Software\MozillaPlugins\@Google.com/GoogleEarthPlugin: C:\Program Files (x86)\Google\Google Earth\plugin\npgeplugin.dll (Google)
FF - HKLM\Software\MozillaPlugins\@java.com/JavaPlugin: C:\Program Files (x86)\Java\jre6\bin\new_plugin\npjp2.dll (Sun Microsystems, Inc.)
FF - HKLM\Software\MozillaPlugins\@microsoft.com/GENUINE: disabled File not found
FF - HKLM\Software\MozillaPlugins\@Microsoft.com/NpCtrl,version=1.0: c:\Program Files (x86)\Microsoft Silverlight\5.1.10411.0\npctrl.dll ( Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@microsoft.com/OfficeAuthz,version=14.0: C:\PROGRA~2\MICROS~3\Office14\NPAUTHZ.DLL (Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@microsoft.com/SharePoint,version=14.0: C:\PROGRA~2\MICROS~3\Office14\NPSPWRAP.DLL (Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@microsoft.com/WLPG,version=15.4.3502.0922: C:\Program Files (x86)\Windows Live\Photo Gallery\NPWLPG.dll (Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@microsoft.com/WLPG,version=15.4.3538.0513: C:\Program Files (x86)\Windows Live\Photo Gallery\NPWLPG.dll (Microsoft Corporation)
FF - HKLM\Software\MozillaPlugins\@tools.google.com/Google Update;version=3: C:\Program Files (x86)\Google\Update\1.3.21.123\npGoogleUpdate3.dll (Google Inc.)
FF - HKLM\Software\MozillaPlugins\@tools.google.com/Google Update;version=9: C:\Program Files (x86)\Google\Update\1.3.21.123\npGoogleUpdate3.dll (Google Inc.)
FF - HKLM\Software\MozillaPlugins\@WildTangent.com/GamesAppPresenceDetector,Version=1.0: C:\Program Files (x86)\WildTangent Games\App\BrowserIntegration\Registered\0\NP_wtapp.dll ()
FF - HKLM\Software\MozillaPlugins\Adobe Reader: C:\Program Files (x86)\Adobe\Reader 10.0\Reader\AIR\nppdf32.dll (Adobe Systems Inc.)
FF - HKEY_LOCAL_MACHINE\software\mozilla\Firefox\Extensions\\{BBDA0591-3099-440a-AA10-41764D9DB4DB}: C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_19.1.0.28\IPSFFPlgn\ [2012/02/03 08:51:32 | 000,000,000 | ---D | M]
FF - HKEY_LOCAL_MACHINE\software\mozilla\Firefox\Extensions\\{2D3F3651-74B9-4795-BDEC-6DA2F431CB62}: C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_19.1.0.28\coFFPlgn\ [2012/11/12 20:50:58 | 000,000,000 | ---D | M]
========== Chrome ========== CHR - homepage:
http://www.google.com/CHR - default_search_provider: Search Results ()
CHR - default_search_provider: search_url = {google:baseURL}search?q={searchTerms}&{google:RLZ}{google:acceptedSuggestion}{google:originalQueryForSuggestion}{google:searchFieldtrialParameter}sourceid=chrome&ie={inputEncoding}
CHR - default_search_provider: suggest_url =
CHR - homepage:
http://www.google.com/CHR - plugin: Shockwave Flash (Enabled) = C:\Program Files (x86)\Google\Chrome\Application\22.0.1229.94\gcswf32.dll
CHR - plugin: Shockwave Flash (Enabled) = C:\windows\SysWOW64\Macromed\Flash\NPSWF32.dll
CHR - plugin: Java Deployment Toolkit 6.0.250.6 (Enabled) = C:\Program Files (x86)\Java\jre6\bin\new_plugin\npdeployJava1.dll
CHR - plugin: Java™ Platform SE 6 U25 (Enabled) = C:\Program Files (x86)\Java\jre6\bin\new_plugin\npjp2.dll
CHR - plugin: Adobe Acrobat (Disabled) = C:\Program Files (x86)\Adobe\Reader 10.0\Reader\Browser\nppdf32.dll
CHR - plugin: Silverlight Plug-In (Enabled) = c:\Program Files (x86)\Microsoft Silverlight\4.0.60831.0\npctrl.dll
CHR - plugin: Microsoft Office 2010 (Enabled) = C:\PROGRA~2\MICROS~3\Office14\NPAUTHZ.DLL
CHR - plugin: Microsoft Office 2010 (Enabled) = C:\PROGRA~2\MICROS~3\Office14\NPSPWRAP.DLL
CHR - plugin: Remoting Viewer (Enabled) = internal-remoting-viewer
CHR - plugin: Native Client (Enabled) = C:\Program Files (x86)\Google\Chrome\Application\22.0.1229.94\ppGoogleNaClPluginChrome.dll
CHR - plugin: Chrome PDF Viewer (Enabled) = C:\Program Files (x86)\Google\Chrome\Application\22.0.1229.94\pdf.dll
CHR - plugin: Norton Confidential (Enabled) = C:\Users\Brian Hillard\AppData\Local\Google\Chrome\User Data\Default\Extensions\mkfokfffehpeedafpekjeddnmnjhmcmk\2012.2.1.6_0\npcoplgn.dll
CHR - plugin: Google Update (Enabled) = C:\Program Files (x86)\Google\Update\1.3.21.79\npGoogleUpdate3.dll
CHR - plugin: WildTangent Games App Presence Detector (Enabled) = C:\Program Files (x86)\WildTangent Games\App\BrowserIntegration\Registered\0\NP_wtapp.dll
CHR - plugin: Windows Live\u0099 Photo Gallery (Enabled) = C:\Program Files (x86)\Windows Live\Photo Gallery\NPWLPG.dll
CHR - plugin: iTunes Application Detector (Enabled) = C:\Program Files (x86)\iTunes\Mozilla Plugins\npitunes.dll
CHR - plugin: Default Plug-in (Enabled) = default_plugin
CHR - Extension: Norton Identity Protection = C:\Users\Brian Hillard\AppData\Local\Google\Chrome\User Data\Default\Extensions\mkfokfffehpeedafpekjeddnmnjhmcmk\2012.5.3.7_0\
CHR - Extension: Norton Identity Protection = C:\Users\Brian Hillard\AppData\Local\Google\Chrome\User Data\Default\Extensions\mkfokfffehpeedafpekjeddnmnjhmcmk\2012.5.6.10_0\
O1 HOSTS File: ([2009/06/10 16:00:26 | 000,000,824 | ---- | M]) - C:\Windows\SysNative\drivers\etc\hosts
O2:
64bit: - BHO: (TOSHIBA Media Controller Plug-in) - {F3C88694-EFFA-4d78-B409-54B7B2535B14} - C:\Program Files (x86)\TOSHIBA\TOSHIBA Media Controller Plug-in\x64\TOSHIBAMediaControllerIE.dll (<TOSHIBA>)
O2 - BHO: (&Yahoo! Toolbar Helper) - {02478D38-C3F9-4efb-9B51-7695ECA05670} - C:\Program Files (x86)\Yahoo!\Companion\Installs\cpn0\yt.dll (Yahoo! Inc.)
O2 - BHO: (Norton Identity Protection) - {602ADB0E-4AFF-4217-8AA1-95DAC4DFA408} - C:\Program Files (x86)\Norton Internet Security\Engine\19.9.0.9\coieplg.dll (Symantec Corporation)
O2 - BHO: (Norton Vulnerability Protection) - {6D53EC84-6AAE-4787-AEEE-F4628F01010C} - C:\Program Files (x86)\Norton Internet Security\Engine\19.9.0.9\ips\ipsbho.dll (Symantec Corporation)
O2 - BHO: (TOSHIBA Media Controller Plug-in) - {F3C88694-EFFA-4d78-B409-54B7B2535B14} - C:\Program Files (x86)\TOSHIBA\TOSHIBA Media Controller Plug-in\TOSHIBAMediaControllerIE.dll (<TOSHIBA>)
O3:
64bit: - HKLM\..\Toolbar: (no name) - Locked - No CLSID value found.
O3 - HKLM\..\Toolbar: (Norton Toolbar) - {7FEBEFE3-6B19-4349-98D2-FFB09D4B49CA} - C:\Program Files (x86)\Norton Internet Security\Engine\19.9.0.9\coieplg.dll (Symantec Corporation)
O3 - HKLM\..\Toolbar: (Yahoo! Toolbar) - {EF99BD32-C1FB-11D2-892F-0090271D4F88} - C:\Program Files (x86)\Yahoo!\Companion\Installs\cpn0\yt.dll (Yahoo! Inc.)
O3 - HKLM\..\Toolbar: (no name) - Locked - No CLSID value found.
O3 - HKCU\..\Toolbar\WebBrowser: (Norton Toolbar) - {7FEBEFE3-6B19-4349-98D2-FFB09D4B49CA} - C:\Program Files (x86)\Norton Internet Security\Engine\19.9.0.9\coieplg.dll (Symantec Corporation)
O4:
64bit: - HKLM..\Run: [] File not found
O4:
64bit: - HKLM..\Run: [cAudioFilterAgent] C:\Program Files\CONEXANT\cAudioFilterAgent\cAudioFilterAgent64.exe (Conexant Systems, Inc.)
O4:
64bit: - HKLM..\Run: [HotKeysCmds] C:\Windows\SysNative\hkcmd.exe (Intel Corporation)
O4:
64bit: - HKLM..\Run: [HSON] C:\Program Files\Toshiba\TBS\HSON.exe (TOSHIBA Corporation)
O4:
64bit: - HKLM..\Run: [IgfxTray] C:\Windows\SysNative\igfxtray.exe (Intel Corporation)
O4:
64bit: - HKLM..\Run: [IntelliPoint] c:\Program Files\Microsoft IntelliPoint\ipoint.exe (Microsoft Corporation)
O4:
64bit: - HKLM..\Run: [Persistence] C:\Windows\SysNative\igfxpers.exe (Intel Corporation)
O4:
64bit: - HKLM..\Run: [SmartAudio] C:\Program Files\CONEXANT\SAII\SAIICpl.exe (Conexant Systems, Inc.)
O4:
64bit: - HKLM..\Run: [TCrdMain] C:\Program Files\Toshiba\FlashCards\TCrdMain.exe (TOSHIBA Corporation)
O4:
64bit: - HKLM..\Run: [Teco] C:\Program Files\TOSHIBA\TECO\Teco.exe (TOSHIBA Corporation)
O4:
64bit: - HKLM..\Run: [TosNC] C:\Program Files\Toshiba\BulletinBoard\TosNcCore.exe (TOSHIBA Corporation)
O4:
64bit: - HKLM..\Run: [TosReelTimeMonitor] C:\Program Files\Toshiba\ReelTime\TosReelTimeMonitor.exe (TOSHIBA Corporation)
O4:
64bit: - HKLM..\Run: [TosSENotify] C:\Program Files\Toshiba\TOSHIBA HDD SSD Alert\TosWaitSrv.exe (TOSHIBA Corporation)
O4:
64bit: - HKLM..\Run: [TosVolRegulator] C:\Program Files\Toshiba\TosVolRegulator\TosVolRegulator.exe (TOSHIBA Corporation)
O4:
64bit: - HKLM..\Run: [TosWaitSrv] C:\Program Files\Toshiba\TPHM\TosWaitSrv.exe (TOSHIBA Corporation)
O4:
64bit: - HKLM..\Run: [TPwrMain] C:\Program Files\Toshiba\Power Saver\TPwrMain.exe (TOSHIBA Corporation)
O4 - HKLM..\Run: [APSDaemon] C:\Program Files (x86)\Common Files\Apple\Apple Application Support\APSDaemon.exe (Apple Inc.)
O4 - HKLM..\Run: [MaxMenuMgr] C:\Program Files (x86)\Seagate\SeagateManager\FreeAgent Status\StxMenuMgr.exe (Seagate LLC)
O4 - HKLM..\Run: [NortonOnlineBackupReminder] C:\Program Files (x86)\Toshiba\Toshiba Online Backup\Activation\TOBuActivation.exe (Toshiba)
O4 - HKLM..\Run: [SecureW2 Tray] C:\Program Files (x86)\SecureW2\sw2_tray.exe (SecureW2 B.V.)
O4 - HKLM..\Run: [ToshibaAppPlace] C:\Program Files (x86)\Toshiba\Toshiba App Place\ToshibaAppPlace.exe (Toshiba)
O4 - HKLM..\Run: [ToshibaServiceStation] C:\Program Files (x86)\TOSHIBA\TOSHIBA Service Station\ToshibaServiceStation.exe (TOSHIBA Corporation)
O4 - HKLM..\Run: [TSleepSrv] C:\Program Files (x86)\TOSHIBA\TOSHIBA Sleep Utility\TSleepSrv.exe (TOSHIBA)
O4 - HKLM..\Run: [YMailAdvisor] C:\Program Files (x86)\Yahoo!\Common\YMailAdvisor.exe (Yahoo! Inc.)
O4 - HKCU..\Run: [MobileDocuments] C:\Program Files (x86)\Common Files\Apple\Internet Services\ubd.exe File not found
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoActiveDesktop = 1
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\Explorer: NoActiveDesktopChanges = 1
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: ConsentPromptBehaviorAdmin = 5
O6 - HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\policies\System: ConsentPromptBehaviorUser = 3
O9 - Extra Button: Add to Wish List - {76c5fb99-dd0a-4186-9e75-65d1bf3da283} - C:\Program Files (x86)\Amazon\Add to Wish List IE Extension\run.htm ()
O10:
64bit: - NameSpace_Catalog5\Catalog_Entries64\000000000009 [] - C:\Program Files\Bonjour\mdnsNSP.dll (Apple Inc.)
O10 - NameSpace_Catalog5\Catalog_Entries\000000000009 [] - C:\Program Files (x86)\Bonjour\mdnsNSP.dll (Apple Inc.)
O13
64bit: - gopher Prefix: missing
O13 - gopher Prefix: missing
O15 - HKCU\..Trusted Domains: ecollege.com ([]* in Trusted sites)
O15 - HKCU\..Trusted Domains: ecollege.com ([ph] * in Trusted sites)
O15 - HKCU\..Trusted Domains: https ([]* in Trusted sites)
O15 - HKCU\..Trusted Domains: mathxl.com ([]* in Trusted sites)
O15 - HKCU\..Trusted Domains: myitlab.com ([]* in Trusted sites)
O15 - HKCU\..Trusted Domains: pearsoncmg.com ([]* in Trusted sites)
O15 - HKCU\..Trusted Domains: pearsoned.com ([]* in Trusted sites)
O15 - HKCU\..Trusted Domains: psu.edu ([*.cms] * in Trusted sites)
O15 - HKCU\..Trusted Domains: psu.edu ([*.courses.worldcampus] * in Trusted sites)
O15 - HKCU\..Trusted Domains: psu.edu ([*.webaccess] * in Trusted sites)
O15 - HKCU\..Trusted Domains: psu.edu ([courses.worldcampus] * in Trusted sites)
O15 - HKCU\..Trusted Domains: psu.edu ([elion] https in Trusted sites)
O16 - DPF: {02BF25D5-8C17-4B23-BC80-D3488ABDDC6B}
http://appldnld.appl...ex/qtplugin.cab (QuickTime Object)
O16 - DPF: {30528230-99f7-4bb4-88d8-fa1d4f56a2ab} C:\Program Files (x86)\Yahoo!\Common\Yinsthelper.dll (Installation Support)
O16 - DPF: {7530BFB8-7293-4D34-9923-61A11451AFC5}
http://download.eset...lineScanner.cab (Reg Error: Key error.)
O16 - DPF: {8AD9C840-044E-11D1-B3E9-00805F499D93}
http://java.sun.com/...indows-i586.cab (Java Plug-in 1.6.0_25)
O16 - DPF: {CAFEEFAC-0016-0000-0025-ABCDEFFEDCBA}
http://java.sun.com/...indows-i586.cab (Java Plug-in 1.6.0_25)
O16 - DPF: {CAFEEFAC-FFFF-FFFF-FFFF-ABCDEFFEDCBA}
http://java.sun.com/...indows-i586.cab (Java Plug-in 1.6.0_25)
O17 - HKLM\System\CCS\Services\Tcpip\Parameters: DhcpNameServer = 208.59.247.45 208.59.247.46
O17 - HKLM\System\CCS\Services\Tcpip\Parameters\Interfaces\{B2EE03B5-815D-457B-84C5-1D9A0F9BF600}: DhcpNameServer = 208.59.247.45 208.59.247.46
O17 - HKLM\System\CCS\Services\Tcpip\Parameters\Interfaces\{ED326837-8CB6-4B2C-B089-B81B261A6F91}: DhcpNameServer = 208.59.247.45 208.59.247.46
O18:
64bit: - Protocol\Handler\livecall - No CLSID value found
O18:
64bit: - Protocol\Handler\ms-help - No CLSID value found
O18:
64bit: - Protocol\Handler\msnim - No CLSID value found
O18:
64bit: - Protocol\Handler\wlmailhtml - No CLSID value found
O18:
64bit: - Protocol\Handler\wlpg - No CLSID value found
O20:
64bit: - HKLM Winlogon: Shell - (explorer.exe) - C:\windows\explorer.exe (Microsoft Corporation)
O20:
64bit: - HKLM Winlogon: UserInit - (C:\Windows\system32\userinit.exe) - C:\Windows\SysNative\userinit.exe (Microsoft Corporation)
O20 - HKLM Winlogon: Shell - (explorer.exe) - C:\windows\SysWow64\explorer.exe (Microsoft Corporation)
O20 - HKLM Winlogon: UserInit - (userinit.exe) - C:\windows\SysWow64\userinit.exe (Microsoft Corporation)
O20:
64bit: - Winlogon\Notify\igfxcui: DllName - (igfxdev.dll) - C:\windows\SysNative\igfxdev.dll (Intel Corporation)
O21:
64bit: - SSODL: WebCheck - {E6FB5E20-DE35-11CF-9C87-00AA005127ED} - No CLSID value found.
O21 - SSODL: WebCheck - {E6FB5E20-DE35-11CF-9C87-00AA005127ED} - No CLSID value found.
O32 - HKLM CDRom: AutoRun - 1
O34 - HKLM BootExecute: (autocheck autochk *)
O35:
64bit: - HKLM\..comfile [open] -- "%1" %*
O35:
64bit: - HKLM\..exefile [open] -- "%1" %*
O35 - HKLM\..comfile [open] -- "%1" %*
O35 - HKLM\..exefile [open] -- "%1" %*
O37:
64bit: - HKLM\...com [@ = comfile] -- "%1" %*
O37:
64bit: - HKLM\...exe [@ = exefile] -- "%1" %*
O37 - HKLM\...com [@ = comfile] -- "%1" %*
O37 - HKLM\...exe [@ = exefile] -- "%1" %*
O38 - SubSystems\\Windows: (ServerDll=winsrv:UserServerDllInitialization,3)
O38 - SubSystems\\Windows: (ServerDll=winsrv:ConServerDllInitialization,2)
O38 - SubSystems\\Windows: (ServerDll=sxssrv,4)
========== Files/Folders - Created Within 30 Days ========== [2012/11/10 17:41:03 | 000,000,000 | ---D | C] -- C:\Users\Brian Hillard\AppData\Roaming\Malwarebytes
[2012/11/10 17:40:35 | 000,000,000 | ---D | C] -- C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Malwarebytes' Anti-Malware
[2012/11/10 17:40:34 | 000,025,928 | ---- | C] (Malwarebytes Corporation) -- C:\windows\SysNative\drivers\mbam.sys
[2012/11/10 17:40:34 | 000,000,000 | ---D | C] -- C:\Program Files (x86)\Malwarebytes' Anti-Malware
[2012/11/10 17:40:34 | 000,000,000 | ---D | C] -- C:\ProgramData\Malwarebytes
[2012/10/26 19:58:12 | 004,731,392 | ---- | C] (AVAST Software) -- C:\Users\Brian Hillard\Desktop\aswMBR.exe
[2012/10/23 21:53:35 | 000,000,000 | ---D | C] -- C:\_OTL
[2012/10/21 20:33:14 | 002,957,840 | ---- | C] (Symantec Corporation) -- C:\Users\Brian Hillard\Desktop\NPE.exe
[2012/10/21 20:32:10 | 000,000,000 | ---D | C] -- C:\Users\Brian Hillard\AppData\Local\NPE
[2012/10/18 21:34:07 | 000,602,112 | ---- | C] (OldTimer Tools) -- C:\Users\Brian Hillard\Desktop\OTL.exe
[2012/10/18 00:17:04 | 000,000,000 | ---D | C] -- C:\Users\Brian Hillard\AppData\Local\BVRP Software
[2012/10/15 16:18:17 | 000,000,000 | ---D | C] -- C:\Users\Brian Hillard\AppData\Local\ElevatedDiagnostics
[1 C:\Users\Brian Hillard\Documents\*.tmp files -> C:\Users\Brian Hillard\Documents\*.tmp -> ]
========== Files - Modified Within 30 Days ========== [2012/11/12 20:55:40 | 000,024,608 | -H-- | M] () -- C:\windows\SysNative\7B296FB0-376B-497e-B012-9C450E1B7327-5P-1.C7483456-A289-439d-8115-601632D005A0
[2012/11/12 20:55:40 | 000,024,608 | -H-- | M] () -- C:\windows\SysNative\7B296FB0-376B-497e-B012-9C450E1B7327-5P-0.C7483456-A289-439d-8115-601632D005A0
[2012/11/12 20:52:43 | 000,726,316 | ---- | M] () -- C:\windows\SysNative\PerfStringBackup.INI
[2012/11/12 20:52:43 | 000,624,178 | ---- | M] () -- C:\windows\SysNative\perfh009.dat
[2012/11/12 20:52:43 | 000,106,522 | ---- | M] () -- C:\windows\SysNative\perfc009.dat
[2012/11/12 20:48:32 | 000,000,908 | ---- | M] () -- C:\windows\tasks\GoogleUpdateTaskMachineCore.job
[2012/11/12 20:48:14 | 000,067,584 | --S- | M] () -- C:\windows\bootstat.dat
[2012/11/12 20:48:06 | 495,865,855 | -HS- | M] () -- C:\hiberfil.sys
[2012/11/12 01:08:00 | 000,000,912 | ---- | M] () -- C:\windows\tasks\GoogleUpdateTaskMachineUA.job
[2012/11/10 17:40:35 | 000,001,124 | ---- | M] () -- C:\Users\Public\Desktop\Malwarebytes Anti-Malware.lnk
[2012/10/27 13:38:04 | 000,000,098 | ---- | M] () -- C:\Users\Brian Hillard\Desktop\testhd.bat
[2012/10/26 20:08:55 | 000,538,941 | ---- | M] () -- C:\Users\Brian Hillard\Desktop\adwcleaner.exe
[2012/10/26 19:58:12 | 004,731,392 | ---- | M] (AVAST Software) -- C:\Users\Brian Hillard\Desktop\aswMBR.exe
[2012/10/26 19:51:22 | 000,022,460 | ---- | M] () -- C:\Users\Brian Hillard\Desktop\2012-10-26_205042.jpg
[2012/10/22 17:12:53 | 689,110,939 | ---- | M] () -- C:\windows\MEMORY.DMP
[2012/10/21 20:33:24 | 002,957,840 | ---- | M] (Symantec Corporation) -- C:\Users\Brian Hillard\Desktop\NPE.exe
[2012/10/18 23:28:05 | 000,023,852 | ---- | M] () -- C:\Users\Brian Hillard\Desktop\high disk usage.jpg
[2012/10/18 21:34:14 | 000,602,112 | ---- | M] (OldTimer Tools) -- C:\Users\Brian Hillard\Desktop\OTL.exe
[1 C:\Users\Brian Hillard\Documents\*.tmp files -> C:\Users\Brian Hillard\Documents\*.tmp -> ]
========== Files Created - No Company Name ========== [2012/11/10 17:40:35 | 000,001,124 | ---- | C] () -- C:\Users\Public\Desktop\Malwarebytes Anti-Malware.lnk
[2012/10/27 13:38:04 | 000,000,098 | ---- | C] () -- C:\Users\Brian Hillard\Desktop\testhd.bat
[2012/10/26 20:08:46 | 000,538,941 | ---- | C] () -- C:\Users\Brian Hillard\Desktop\adwcleaner.exe
[2012/10/26 19:51:22 | 000,022,460 | ---- | C] () -- C:\Users\Brian Hillard\Desktop\2012-10-26_205042.jpg
[2012/10/18 23:28:05 | 000,023,852 | ---- | C] () -- C:\Users\Brian Hillard\Desktop\high disk usage.jpg
[2012/04/05 21:40:30 | 000,188,041 | ---- | C] () -- C:\Users\Brian Hillard\rjd2 3rd hand.jpg
[2012/03/24 23:56:33 | 000,107,924 | ---- | C] () -- C:\Users\Brian Hillard\tumblr post 2.jpg
[2012/03/24 23:56:10 | 000,182,681 | ---- | C] () -- C:\Users\Brian Hillard\tumblr coal post.jpg
[2011/12/04 01:17:08 | 000,000,043 | ---- | C] () -- C:\Users\Brian Hillard\.mjsync_en_US
[2011/09/07 00:46:50 | 000,451,072 | ---- | C] () -- C:\windows\SysWow64\ISSRemoveSP.exe
[2011/04/04 22:07:00 | 000,145,804 | ---- | C] () -- C:\windows\SysWow64\igcompkrng600.bin
[2011/04/04 22:06:58 | 000,963,116 | ---- | C] () -- C:\windows\SysWow64\igkrng600.bin
[2011/04/04 22:06:58 | 000,216,876 | ---- | C] () -- C:\windows\SysWow64\igfcg600m.bin
[2011/02/03 21:56:58 | 000,066,856 | ---- | C] () -- C:\windows\SysWow64\SynTPEnhPS.dll
========== ZeroAccess Check ========== [2009/07/13 23:55:00 | 000,000,227 | RHS- | M] () -- C:\windows\assembly\Desktop.ini
[HKEY_CURRENT_USER\Software\Classes\clsid\{42aedc87-2188-41fd-b9a3-0c966feabec1}\InProcServer32] /64
[HKEY_CURRENT_USER\Software\Classes\Wow6432node\clsid\{42aedc87-2188-41fd-b9a3-0c966feabec1}\InProcServer32]
[HKEY_CURRENT_USER\Software\Classes\clsid\{fbeb8a05-beee-4442-804e-409d6c4515e9}\InProcServer32] /64
[HKEY_CURRENT_USER\Software\Classes\Wow6432node\clsid\{fbeb8a05-beee-4442-804e-409d6c4515e9}\InProcServer32]
[HKEY_LOCAL_MACHINE\Software\Classes\clsid\{42aedc87-2188-41fd-b9a3-0c966feabec1}\InProcServer32] /64
"" = C:\Windows\SysNative\shell32.dll -- [2012/06/09 00:43:10 | 014,172,672 | ---- | M] (Microsoft Corporation)
"ThreadingModel" = Apartment
[HKEY_LOCAL_MACHINE\Software\Wow6432Node\Classes\clsid\{42aedc87-2188-41fd-b9a3-0c966feabec1}\InProcServer32]
"" = %SystemRoot%\system32\shell32.dll -- [2012/06/08 23:41:00 | 012,873,728 | ---- | M] (Microsoft Corporation)
"ThreadingModel" = Apartment
[HKEY_LOCAL_MACHINE\Software\Classes\clsid\{5839FCA9-774D-42A1-ACDA-D6A79037F57F}\InProcServer32] /64
"" = C:\Windows\SysNative\wbem\fastprox.dll -- [2009/07/13 20:40:51 | 000,909,312 | ---- | M] (Microsoft Corporation)
"ThreadingModel" = Free
[HKEY_LOCAL_MACHINE\Software\Wow6432Node\Classes\clsid\{5839FCA9-774D-42A1-ACDA-D6A79037F57F}\InProcServer32]
"" = %systemroot%\system32\wbem\fastprox.dll -- [2010/11/20 22:24:25 | 000,606,208 | ---- | M] (Microsoft Corporation)
"ThreadingModel" = Free
[HKEY_LOCAL_MACHINE\Software\Classes\clsid\{F3130CDB-AA52-4C3A-AB32-85FFC23AF9C1}\InProcServer32] /64
"" = C:\Windows\SysNative\wbem\wbemess.dll -- [2009/07/13 20:41:56 | 000,505,856 | ---- | M] (Microsoft Corporation)
"ThreadingModel" = Both
[HKEY_LOCAL_MACHINE\Software\Wow6432Node\Classes\clsid\{F3130CDB-AA52-4C3A-AB32-85FFC23AF9C1}\InProcServer32]
========== LOP Check ========== [2012/01/08 10:55:01 | 000,000,000 | ---D | M] -- C:\Users\Brian Hillard\AppData\Roaming\OverDrive
[2011/11/25 12:55:31 | 000,000,000 | ---D | M] -- C:\Users\Brian Hillard\AppData\Roaming\Tific
[2011/11/25 10:30:55 | 000,000,000 | ---D | M] -- C:\Users\Brian Hillard\AppData\Roaming\Toshiba
[2011/11/25 10:27:45 | 000,000,000 | ---D | M] -- C:\Users\Brian Hillard\AppData\Roaming\WinBatch
[2012/01/23 23:15:31 | 000,000,000 | ---D | M] -- C:\Users\Brian Hillard\AppData\Roaming\Windows Live Writer
========== Purity Check ========== < End of report >
Checkup log:
Results of screen317's Security Check version 0.99.54
Windows 7 Service Pack 1 x64 (UAC is enabled)
Internet Explorer 9
``````````````Antivirus/Firewall Check:`````````````` Windows Firewall Enabled!
Norton Internet Security
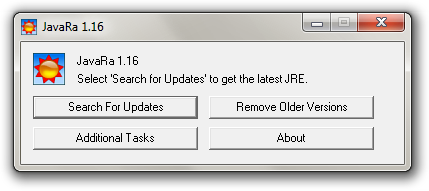
WMI entry may not exist for antivirus; attempting automatic update. `````````Anti-malware/Other Utilities Check:````````` Malwarebytes Anti-Malware version 1.65.1.1000
Java™ 6 Update 25
Java version out of Date! Adobe Flash Player 10
Flash Player out of Date! Adobe Reader X (10.1.4)
````````Process Check: objlist.exe by Laurent```````` Norton ccSvcHst.exe
`````````````````System Health check````````````````` Total Fragmentation on Drive C: 1%
````````````````````End of Log``````````````````````
 (this will copy the log).
(this will copy the log).

 This topic is locked
This topic is locked






















 Sign In
Sign In Create Account
Create Account

