Thanks again for the help.
FBI Moneypak and Subsequent Google Redirect [Solved]
#16
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #16](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 August 2013 - 12:45 PM
Posted 10 August 2013 - 12:45 PM

Thanks again for the help.
#17
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #17](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 10 August 2013 - 11:47 PM
Posted 10 August 2013 - 11:47 PM

- Double-click on the AVG tray icon to access the main interface.
- Click Tools > Advanced Settings > Antivirus > Resident Shield.
- Uncheck the box beside Enable Resident Shield.

- Click on Apply and then on OK to validate.
IF the OTL fix runs to completion after disabling AVG then go to Step 2. in post #15 and complete steps 2 through 4.
IF it still doesn't run, I have redone the OTL fix and removed the emptytemp directive. Please run the new OTL fix below.
Then we will download a stand alone Temporary File Cleaner and see if it will remove them. If it runs then you can continue with Step 2 through Step 4 in post #15.
Revised OTL fix
Be advised that when the fix commences it will shut down all running processes and you may lose the desktop and icons, they will return on reboot
1. Please copy all of the text in the quote box below (Do Not copy the word Quote. To do this, highlight everything
inside the quote box (except the word Quote) , right click and click Copy.
:COMMANDS
[createrestorepoint]
:OTL
C:\Users\Bruce\AppData\Local\Temp\AskSLib.dll
C:\Users\Bruce\AppData\Local\Temp\feumleviyabhoufngmh.bfg
C:\Users\Bruce\AppData\Local\Temp\jar_cache3466583319597352082.tmp
C:\Users\Bruce\AppData\Local\Temp\jar_cache5903818575124509270.tmp
C:\Users\Bruce\AppData\Local\Temp\jar_cache8139189273844289181.tmp
C:\Users\Bruce\AppData\Local\Temp\rsrctt\rsrctt.dll
C:\Users\Bruce\AppData\Local\Temp\urbylmnjm\urbylmnjm.dll
C:\Users\Bruce\AppData\LocalLow\Sun\Java\Deployment\cache\6.0\57\744ed939-129c4b61
C:\Users\Bruce\Documents\RCA easyRip\RCAeasyRipInstaller.exe
C:\Users\Bruce\Downloads\RCAEASYRIPINSTALLER2570 (1).EXE
C:\Users\Bruce\Downloads\RCAEASYRIPINSTALLER2570.EXE
:COMMANDS
[reboot]
Warning: This fix is relevant for this system and no other. If you are not this user, DO NOT follow these directions as they could damage the workings of your system.
2. Please re-open
- Vista and 7 users: Right click the icon and click Run as Administrator
 textbox, right click and click Paste. This will put the above script inside the textbox.
textbox, right click and click Paste. This will put the above script inside the textbox.4. Click the
 button.
button.5. Let the program run unhindered.
6. OTL may ask to reboot the machine. Please do so if asked.
7. Click the
 button.
button.8. A report will open. Copy and Paste that report in your next reply.
9. If the machine reboots, the log will be located at C:\_OTL\MovedFiles\mmddyyyy_hhmmss.log, (where mmddyyyy_hhmmss is the date of the tool run).
Clear Cache/TempFiles
- Please right click TFC icon on the desktop and click Run As Administrator. OK any UAC prompts.
- It will close all programs when run, so make sure you have saved all your work before you begin.
- Click the Start button to begin the process. Depending on how often you clean temp files, execution time should be anywhere from a few seconds to several minutes. Let it run uninterrupted to completion.
- Once it's finished it should reboot your machine. If it does not, please manually reboot the machine yourself to ensure a complete clean.
Now continue with steps 2 through 4 in post#15.
Things For Your Next Post:
Please post the logs in the order requested. Do Not attach the logs unless I request it.
1. Let me know if the original OTL fix ran after disabling AVG or if you had to run the revised OTL fix.
2. If you had to run TFC let me know if it ran successfully. (It doesn't create an log)
3. Let me know how the updates went.
4. The OTL fixes log
#18
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #18](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 11 August 2013 - 07:48 PM
Posted 11 August 2013 - 07:48 PM

I then ran the revised OTL Fix (with AVG disabled). The log is below. It doesn't appear to have done much. I confirmed the bad files were not moved. There is a new MovedFiles folder but it is empty as well.
========== COMMANDS ==========
Restore point Set: OTL Restore Point
========== OTL ==========
========== COMMANDS ==========
OTL by OldTimer - Version 3.2.69.0 log created on 08112013_181318
I ran TFC and it hung as well. I'm not sure where to look to confirm what it did but all the files in C:\Users\Bruce\AppData\Local\Temp are still there. The TFC screen read the following when it hung:
Getting user folders.
Stopping running processes.
Emptying Temp folders.
User: All Users
User: Bruce
I then went ahead and downloaded and installed Adobe Reader and Adobe Flash Player as instructed without any problems.
Thanks. Looking forward to what to try next.
#19
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #19](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 11 August 2013 - 09:44 PM
Posted 11 August 2013 - 09:44 PM

That's good.I then went ahead and downloaded and installed Adobe Reader and Adobe Flash Player as instructed without any problems.
That's on me. I used the wrong command. I'm wondering if the malware files in the TEMP folder is what is causing OTL to hang on the emptytemp command. Please run the revised fix:I then ran the revised OTL Fix (with AVG disabled). The log is below. It doesn't appear to have done much.
Step-1.
Be advised that when the fix commences it will shut down all running processes and you may lose the desktop and icons, they will return on reboot
1. Please copy all of the text in the quote box below (Do Not copy the word Quote. To do this, highlight everything
inside the quote box (except the word Quote) , right click and click Copy.
:COMMANDS
[createrestorepoint]
:FILES
C:\Users\Bruce\AppData\Local\Temp\AskSLib.dll
C:\Users\Bruce\AppData\Local\Temp\feumleviyabhoufngmh.bfg
C:\Users\Bruce\AppData\Local\Temp\jar_cache3466583319597352082.tmp
C:\Users\Bruce\AppData\Local\Temp\jar_cache5903818575124509270.tmp
C:\Users\Bruce\AppData\Local\Temp\jar_cache8139189273844289181.tmp
C:\Users\Bruce\AppData\Local\Temp\rsrctt\rsrctt.dll
C:\Users\Bruce\AppData\Local\Temp\urbylmnjm\urbylmnjm.dll
C:\Users\Bruce\AppData\LocalLow\Sun\Java\Deployment\cache\6.0\57\744ed939-129c4b61
C:\Users\Bruce\Documents\RCA easyRip\RCAeasyRipInstaller.exe
C:\Users\Bruce\Downloads\RCAEASYRIPINSTALLER2570 (1).EXE
C:\Users\Bruce\Downloads\RCAEASYRIPINSTALLER2570.EXE
:COMMANDS
[reboot]
Warning: This fix is relevant for this system and no other. If you are not this user, DO NOT follow these directions as they could damage the workings of your system.
2. Please re-open
- Vista and 7 users: Right click the icon and click Run as Administrator
 textbox, right click and click Paste. This will put the above script inside the textbox.
textbox, right click and click Paste. This will put the above script inside the textbox.4. Click the
 button.
button.5. Let the program run unhindered.
6. OTL may ask to reboot the machine. Please do so if asked.
7. Click the
 button.
button.8. A report will open. Copy and Paste that report in your next reply.
9. If the machine reboots, the log will be located at C:\_OTL\MovedFiles\mmddyyyy_hhmmss.log, (where mmddyyyy_hhmmss is the date of the tool run).
Step-2.
***Read through this entire procedure and if you have any questions, please ask them before you begin. Then either print out, or copy this page to Notepad and save to your desktop for reference as you will not have any browsers open while you are carrying out portions of these instructions.***
If you have a previous version of Combofix.exe, delete it and download a fresh copy.
* IMPORTANT - Disable your AntiVirus and AntiSpyware applications before downloading ComboFix. This is usually done via a right click on the System Tray icon. They may otherwise interfere with our tools. If you have difficulty properly disabling your protective programs, refer to this link here
The list is not all inclusive. If yours is not listed and you don't know how to disable it, please ask.
VERY IMPORTANT !!! Save ComboFix.exe to your Desktop
Download ComboFix from one of the following locations:
Link 1
Link 2
- Double click on ComboFix.exe & follow the prompts.
- Accept the disclaimer and allow to update if it asks
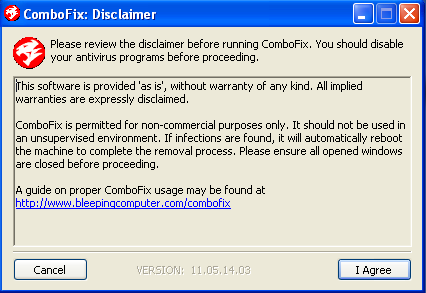
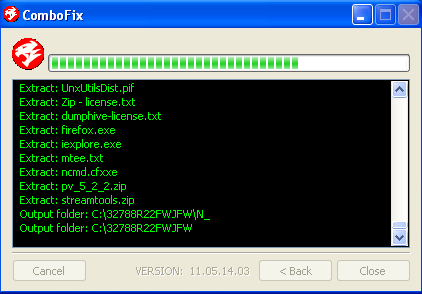
- When finished, it shall produce a log for you.
- Please include the C:\ComboFix.txt in your next reply.
1. Do not mouse-click Combofix's window while it is running. That may cause it to stall.
2. Do not "re-run" ComboFix. If you have a problem, reply back for further instructions.
3. If you recieve an error "Illegal operation attempted on a registry key that has been marked for deletion". Please restart the computer. That will cure it.
A word of warning: Neither I nor sUBs are responsible for any damage you may have caused your machine by running ComboFix on your own.
This tool is not a toy and not for everyday use. ComboFix Should Not be used unless requested by a forum helper
Please make sure you include the combo fix log in your next reply as well as describe how your computer is running now
Don't forget to re-enable your Anti-Virus
Step-3.
Things For Your Next Post:
Please post the logs in the order requested. Do Not attach the logs unless I request it.
1. The OTL fixes log
2. The ComboFix.txt log
#20
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #20](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 12 August 2013 - 08:56 PM
Posted 12 August 2013 - 08:56 PM

========== COMMANDS ==========
Restore point Set: OTL Restore Point
========== FILES ==========
C:\Users\Bruce\AppData\Local\Temp\AskSLib.dll moved successfully.
C:\Users\Bruce\AppData\Local\Temp\feumleviyabhoufngmh.bfg moved successfully.
C:\Users\Bruce\AppData\Local\Temp\jar_cache3466583319597352082.tmp moved successfully.
C:\Users\Bruce\AppData\Local\Temp\jar_cache5903818575124509270.tmp moved successfully.
C:\Users\Bruce\AppData\Local\Temp\jar_cache8139189273844289181.tmp moved successfully.
C:\Users\Bruce\AppData\Local\Temp\rsrctt\rsrctt.dll moved successfully.
C:\Users\Bruce\AppData\Local\Temp\urbylmnjm\urbylmnjm.dll moved successfully.
C:\Users\Bruce\AppData\LocalLow\Sun\Java\Deployment\cache\6.0\57\744ed939-129c4b61 moved successfully.
C:\Users\Bruce\Documents\RCA easyRip\RCAeasyRipInstaller.exe moved successfully.
C:\Users\Bruce\Downloads\RCAEASYRIPINSTALLER2570 (1).EXE moved successfully.
C:\Users\Bruce\Downloads\RCAEASYRIPINSTALLER2570.EXE moved successfully.
========== COMMANDS ==========
OTL by OldTimer - Version 3.2.69.0 log created on 08122013_211831
ComboFix on the other hand did not run completely. I disabled AVG like you instructed but after ComboFix had completed stage 4, AVG popped up reporting suspicious behavior and shut it down even though I selected to allow it. There was no log.
#21
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #21](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 13 August 2013 - 12:18 AM
Posted 13 August 2013 - 12:18 AM

That's good.The OTL Fix seems to have worked. Here is the log.
Yeah, unfortunately AVG can be a real pain when running some of our tools. But I want to clear the Temp files. Now that the malware files have been removed let's disable AVG again and re-run TFC using the instructions to Clear Cache/Temp Files in this post and let me know how that went.ComboFix on the other hand did not run completely. I disabled AVG like you instructed but after ComboFix had completed stage 4, AVG popped up reporting suspicious behavior and shut it down even though I selected to allow it.
#22
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #22](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 13 August 2013 - 07:06 AM
Posted 13 August 2013 - 07:06 AM

#23
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #23](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 13 August 2013 - 07:57 AM
Posted 13 August 2013 - 07:57 AM

Run RogueKiller
NOTE: If using IE8 or better the Smartscreen Filter will need to be disabled. Directions for disabling the SmartScreen Filter in IE 8, 9 and 10 can be found: here
- Click here to go to the RogueKiller download page.
- Click the Build 32 bits (x86): download button and save the RogueKiller.exe file to the desktop.
- Quit all programs and close all browsers.
- Right click the RogueKiller icon and click Run as Administrator to run the program.
NOTE: If this is the first time you have used the program you will need to accept the User Agreement. - Wait until Prescan has finished ...This may take a few minutes, especially if it is the first time you have used the program.
- Click on Scan
- Wait for the end of the scan.
- DO NOT delete anything at this time.
- The report has been created on the desktop.
All RKreport.txt text files located on your desktop.
NOTE: If RogueKiller has been blocked, do not hesitate to try a few times more. If it really won't run, rename it to winlogon.exe (or winlogon.com) and try again
#24
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #24](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 13 August 2013 - 05:51 PM
Posted 13 August 2013 - 05:51 PM

I ran RogueKiller. The log is below.
RogueKiller V8.6.5 [Aug 5 2013] by Tigzy
mail : tigzyRK<at>gmail<dot>com
Feedback : http://www.adlice.com/forum/
Website : http://www.adlice.co...es/roguekiller/
Blog : http://tigzyrk.blogspot.com/
Operating System : Windows Vista (6.0.6002 Service Pack 2) 32 bits version
Started in : Normal mode
User : Bruce [Admin rights]
Mode : Scan -- Date : 08/13/2013 18:45:46
| ARK || FAK || MBR |
¤¤¤ Bad processes : 1 ¤¤¤
[SUSP PATH] nexdef.exe -- C:\Users\Bruce\AppData\Local\Autobahn\nexdef.exe [-] -> KILLED [TermProc]
¤¤¤ Registry Entries : 3 ¤¤¤
[HJ POL] HKCU\[...]\System : DisableRegistryTools (0) -> FOUND
[HJ DESK] HKLM\[...]\NewStartPanel : {59031a47-3f72-44a7-89c5-5595fe6b30ee} (1) -> FOUND
[HJ DESK] HKLM\[...]\NewStartPanel : {20D04FE0-3AEA-1069-A2D8-08002B30309D} (1) -> FOUND
¤¤¤ Scheduled tasks : 2 ¤¤¤
[V1][SUSP PATH] AVG-Secure-Search-Update_JUNE2013_TB_rmv.job : C:\Windows\TEMP\{8B5E664F-BE39-4352-AECC-948F3F62E35F}.exe - --uninstall=1 [x] -> FOUND
[V2][SUSP PATH] AVG-Secure-Search-Update_JUNE2013_TB_rmv : C:\Windows\TEMP\{8B5E664F-BE39-4352-AECC-948F3F62E35F}.exe - --uninstall=1 [x] -> FOUND
¤¤¤ Startup Entries : 1 ¤¤¤
[Bruce][SUSP PATH] NexDef Plug-in.lnk : C:\Users\Bruce\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\NexDef Plug-in.lnk @C:\Users\Bruce\AppData\Local\Autobahn\nexdef.exe [-][-] -> FOUND
¤¤¤ Web browsers : 0 ¤¤¤
¤¤¤ Particular Files / Folders: ¤¤¤
¤¤¤ Driver : [LOADED] ¤¤¤
¤¤¤ External Hives: ¤¤¤
¤¤¤ Infection : ¤¤¤
¤¤¤ HOSTS File: ¤¤¤
--> %SystemRoot%\System32\drivers\etc\hosts
127.0.0.1 localhost
::1 localhost
¤¤¤ MBR Check: ¤¤¤
+++++ PhysicalDrive0: ST9320320AS ATA Device +++++
--- User ---
[MBR] 6602eda926d3c9230879da00ec6705e7
[BSP] c6bf521abd2dc45389bbfcbd6fb5529a : Toshiba MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 63 | Size: 294096 Mo
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 602310656 | Size: 11145 Mo
User = LL1 ... OK!
User = LL2 ... OK!
Finished : << RKreport[0]_S_08132013_184546.txt >>
#25
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #25](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 14 August 2013 - 09:18 AM
Posted 14 August 2013 - 09:18 AM

The consensus is that it is either AVG or the ZoneAlarm firewall causing this. Since AVG also caused ComboFix to hang we will start with it but first we will take care of the things that RogueKiller found.Any news on emptying the temp folders?
NOTE: After AVG is uninstalled you will need to disconnect the computer from the internet (except for coming here to post the results) until the antivirus program has been reinstalled.
Step-1.
Re-Run RogueKiller
Quit all programs and close all browsers.
- Right click the RogueKiller icon and click Run as Administrator to run the program.
- Wait until Prescan has finished ...
- Click the Scan button and wait for the scan to complete.
- After the scan has completed click the Registry tab and remove the check mark in all of the boxes except the following:
- [V1][SUSP PATH] AVG-Secure-Search-Update_JUNE2013_TB_rmv.job : C:\Windows\TEMP\{8B5E664F-BE39-4352-AECC-948F3F62E35F}.exe - --uninstall=1 [x] -> FOUND
- [V2][SUSP PATH] AVG-Secure-Search-Update_JUNE2013_TB_rmv : C:\Windows\TEMP\{8B5E664F-BE39-4352-AECC-948F3F62E35F}.exe - --uninstall=1 [x] -> FOUND
- Click on the Delete button.
- The report has been created on the desktop.
- Next click on the ShortcutsFix
- The report has been created on the desktop.
The RKreport.txt files located on your desktop.
NOTE: If RogueKiller has been blocked, do not hesitate to try a few times more. If it really won't run, rename it to winlogon.exe (or winlogon.com) and try again
Now let's uninstall AVG and see if we can empty the TEMP files.
Download AVG Free
Click here to go to the AVG download page.
- Under the Installation files section click the AVG for Windows (32bBit) link to download the avg free x86 all 2013 3392a6523.exe file and save it to the desktop.
- Download the AVG Remover tool and save it to the desktop.
Uninstall AVG Free
- Click the Start Orb and click Control Panel.
- Under the Programs section click Uninstall a program. The list of installed programs will populate.
- Locate AVG 2013, right click it and click Uninstall.
- Follow the instructions on the screen to complete the uninstall.
- Close the Control Panel.
- Reboot the computer.
AVG Remover eliminates all the parts of your AVG installation from your computer, including registry items, installation files, user files, etc.
- Right click the avg_remover_stf_x86_2013_3341.exe file on the desktop and click Run as Administrator and accept any UAC prompts to run the tool. Follow the on screen instructions.
- You will be asked during the removal process to restart the computer, please do so.
Step-2.
Be advised that when the fix commences it will shut down all running processes and you may lose the desktop and icons, they will return on reboot
1. Please copy all of the text in the quote box below (Do Not copy the word Quote. To do this, highlight everything
inside the quote box (except the word Quote) , right click and click Copy.
:COMMANDS
[createrestorepoint]
[emptytemp]
Warning: This fix is relevant for this system and no other. If you are not this user, DO NOT follow these directions as they could damage the workings of your system.
2. Please re-open
- Vista and 7 users: Right click the icon and click Run as Administrator
 textbox, right click and click Paste. This will put the above script inside the textbox.
textbox, right click and click Paste. This will put the above script inside the textbox.4. Click the
 button.
button.5. Let the program run unhindered.
6. OTL may ask to reboot the machine. Please do so if asked.
7. Click the
 button.
button.8. A report will open. Copy and Paste that report in your next reply.
9. If the machine reboots, the log will be located at C:\_OTL\MovedFiles\mmddyyyy_hhmmss.log, (where mmddyyyy_hhmmss is the date of the tool run).
NOTE: Depending on the number of TEMP files on the computer this can take several minutes to complete so let it run for 20 min or so.
IF the OTL fix ran to completion go to Step 3. IF it got hung again try re-running TFC using the instructions in this post and then go on to Step 3.
Step-3.
Re-run ComboFix using the instructions (except for the downloading part) in Step 2. of post #19
Step-4.
IF the OTL fix or TFC and ComboFix were able to run to completion, make sure that you can locate the log files and then you can reinstall the AVG antivirus program.
IF they did not run to completion don't reinstall the AV program yet and let me know.
Step-5.
Things For Your Next Post:
Please post the logs in the order requested. Do Not attach the logs unless I request it.
1. The RKReport [D]_xxxxxxxx_xxxxxx.txt log. (The Remove log)
2. The RKReport [SC]_xxxxxxxx.xxxx.log. (The Shortcut Fix log)
3. The The OTL fixes log if it ran to completion OR let me know if TFC was able to run.
4. The ComboFix.txt log
#26
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #26](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 14 August 2013 - 07:29 PM
Posted 14 August 2013 - 07:29 PM

RKreport[0]_S
RogueKiller V8.6.5 [Aug 5 2013] by Tigzy
mail : tigzyRK<at>gmail<dot>com
Feedback : http://www.adlice.com/forum/
Website : http://www.adlice.co...es/roguekiller/
Blog : http://tigzyrk.blogspot.com/
Operating System : Windows Vista (6.0.6002 Service Pack 2) 32 bits version
Started in : Normal mode
User : Bruce [Admin rights]
Mode : Scan -- Date : 08/14/2013 16:03:40
| ARK || FAK || MBR |
¤¤¤ Bad processes : 0 ¤¤¤
¤¤¤ Registry Entries : 3 ¤¤¤
[HJ POL] HKCU\[...]\System : DisableRegistryTools (0) -> FOUND
[HJ DESK] HKLM\[...]\NewStartPanel : {59031a47-3f72-44a7-89c5-5595fe6b30ee} (1) -> FOUND
[HJ DESK] HKLM\[...]\NewStartPanel : {20D04FE0-3AEA-1069-A2D8-08002B30309D} (1) -> FOUND
¤¤¤ Scheduled tasks : 2 ¤¤¤
[V1][SUSP PATH] AVG-Secure-Search-Update_JUNE2013_TB_rmv.job : C:\Windows\TEMP\{8B5E664F-BE39-4352-AECC-948F3F62E35F}.exe - --uninstall=1 [x] -> FOUND
[V2][SUSP PATH] AVG-Secure-Search-Update_JUNE2013_TB_rmv : C:\Windows\TEMP\{8B5E664F-BE39-4352-AECC-948F3F62E35F}.exe - --uninstall=1 [x] -> FOUND
¤¤¤ Startup Entries : 1 ¤¤¤
[Bruce][SUSP PATH] NexDef Plug-in.lnk : C:\Users\Bruce\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\NexDef Plug-in.lnk @C:\Users\Bruce\AppData\Local\Autobahn\nexdef.exe [-][-] -> FOUND
¤¤¤ Web browsers : 0 ¤¤¤
¤¤¤ Particular Files / Folders: ¤¤¤
¤¤¤ Driver : [LOADED] ¤¤¤
¤¤¤ External Hives: ¤¤¤
¤¤¤ Infection : ¤¤¤
¤¤¤ HOSTS File: ¤¤¤
--> %SystemRoot%\System32\drivers\etc\hosts
127.0.0.1 localhost
::1 localhost
¤¤¤ MBR Check: ¤¤¤
+++++ PhysicalDrive0: ST9320320AS ATA Device +++++
--- User ---
[MBR] 6602eda926d3c9230879da00ec6705e7
[BSP] c6bf521abd2dc45389bbfcbd6fb5529a : Toshiba MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 63 | Size: 294096 Mo
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 602310656 | Size: 11145 Mo
User = LL1 ... OK!
User = LL2 ... OK!
Finished : << RKreport[0]_S_08142013_160340.txt >>
RKreport[0]_S_08132013_184546.txt
RKreport[0]_D
RogueKiller V8.6.5 [Aug 5 2013] by Tigzy
mail : tigzyRK<at>gmail<dot>com
Feedback : http://www.adlice.com/forum/
Website : http://www.adlice.co...es/roguekiller/
Blog : http://tigzyrk.blogspot.com/
Operating System : Windows Vista (6.0.6002 Service Pack 2) 32 bits version
Started in : Normal mode
User : Bruce [Admin rights]
Mode : Remove -- Date : 08/14/2013 16:04:04
| ARK || FAK || MBR |
¤¤¤ Bad processes : 0 ¤¤¤
¤¤¤ Registry Entries : 3 ¤¤¤
[HJ POL] HKCU\[...]\System : DisableRegistryTools (0) -> NOT SELECTED
[HJ DESK] HKLM\[...]\NewStartPanel : {59031a47-3f72-44a7-89c5-5595fe6b30ee} (1) -> NOT SELECTED
[HJ DESK] HKLM\[...]\NewStartPanel : {20D04FE0-3AEA-1069-A2D8-08002B30309D} (1) -> NOT SELECTED
¤¤¤ Scheduled tasks : 2 ¤¤¤
[V1][SUSP PATH] AVG-Secure-Search-Update_JUNE2013_TB_rmv.job : C:\Windows\TEMP\{8B5E664F-BE39-4352-AECC-948F3F62E35F}.exe - --uninstall=1 [x] -> DELETED
[V2][SUSP PATH] AVG-Secure-Search-Update_JUNE2013_TB_rmv : C:\Windows\TEMP\{8B5E664F-BE39-4352-AECC-948F3F62E35F}.exe - --uninstall=1 [x] -> DELETED
¤¤¤ Startup Entries : 1 ¤¤¤
[Bruce][SUSP PATH] NexDef Plug-in.lnk : C:\Users\Bruce\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\NexDef Plug-in.lnk @C:\Users\Bruce\AppData\Local\Autobahn\nexdef.exe [-][-] -> NOT SELECTED
¤¤¤ Web browsers : 0 ¤¤¤
¤¤¤ Particular Files / Folders: ¤¤¤
¤¤¤ Driver : [LOADED] ¤¤¤
¤¤¤ External Hives: ¤¤¤
¤¤¤ Infection : ¤¤¤
¤¤¤ HOSTS File: ¤¤¤
--> %SystemRoot%\System32\drivers\etc\hosts
127.0.0.1 localhost
::1 localhost
¤¤¤ MBR Check: ¤¤¤
+++++ PhysicalDrive0: ST9320320AS ATA Device +++++
--- User ---
[MBR] 6602eda926d3c9230879da00ec6705e7
[BSP] c6bf521abd2dc45389bbfcbd6fb5529a : Toshiba MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 63 | Size: 294096 Mo
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 602310656 | Size: 11145 Mo
User = LL1 ... OK!
User = LL2 ... OK!
Finished : << RKreport[0]_D_08142013_160404.txt >>
RKreport[0]_S_08132013_184546.txt;RKreport[0]_S_08142013_160340.txt
RKreport[0]_SC
RogueKiller V8.6.5 [Aug 5 2013] by Tigzy
mail : tigzyRK<at>gmail<dot>com
Feedback : http://www.adlice.com/forum/
Website : http://www.adlice.co...es/roguekiller/
Blog : http://tigzyrk.blogspot.com/
Operating System : Windows Vista (6.0.6002 Service Pack 2) 32 bits version
Started in : Normal mode
User : Bruce [Admin rights]
Mode : Shortcuts HJfix -- Date : 08/14/2013 16:04:30
| ARK || FAK || MBR |
¤¤¤ Bad processes : 0 ¤¤¤
¤¤¤ Driver : [LOADED] ¤¤¤
¤¤¤ External Hives: ¤¤¤
¤¤¤ File attributes restored: ¤¤¤
Desktop: Success 0 / Fail 0
Quick launch: Success 0 / Fail 0
Programs: Success 0 / Fail 0
Start menu: Success 0 / Fail 0
User folder: Success 9 / Fail 0
My documents: Success 0 / Fail 0
My favorites: Success 0 / Fail 0
My pictures: Success 0 / Fail 0
My music: Success 42 / Fail 0
My videos: Success 0 / Fail 0
Local drives: Success 197 / Fail 0
Backup: [NOT FOUND]
Drives:
[C:] \Device\HarddiskVolume1 -- 0x3 --> Restored
[D:] \Device\HarddiskVolume2 -- 0x3 --> Restored
[E:] \Device\CdRom0 -- 0x5 --> Skipped
¤¤¤ Infection : ¤¤¤
Finished : << RKreport[0]_SC_08142013_160430.txt >>
RKreport[0]_D_08142013_160404.txt;RKreport[0]_S_08132013_184546.txt;RKreport[0]_S_08142013_160340.txt
ComboFix.txt
ComboFix 13-08-14.02 - Bruce 08/14/2013 19:56:59.2.2 - x86
Microsoft® Windows Vista Home Premium 6.0.6002.2.1252.1.1033.18.3002.1985 [GMT -5:00]
Running from: c:\users\Bruce\Desktop\ComboFix.exe
FW: ZoneAlarm Free Firewall Firewall *Disabled* {E6380B7E-D4B2-19F1-083E-56486607704B}
SP: Windows Defender *Disabled/Outdated* {D68DDC3A-831F-4fae-9E44-DA132C1ACF46}
.
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
.
C:\DFR1083.tmp
.
.
((((((((((((((((((((((((( Files Created from 2013-07-15 to 2013-08-15 )))))))))))))))))))))))))))))))
.
.
2013-08-15 01:09 . 2013-08-15 01:09 -------- d-----w- c:\users\Default\AppData\Local\temp
2013-08-12 01:13 . 2013-08-12 01:20 71048 ----a-w- c:\windows\system32\FlashPlayerCPLApp.cpl
2013-08-12 01:13 . 2013-08-12 01:20 692104 ----a-w- c:\windows\system32\FlashPlayerApp.exe
2013-08-12 01:02 . 2013-08-12 01:03 -------- d-----w- c:\program files\Common Files\Adobe
2013-08-10 04:04 . 2013-08-10 04:04 -------- d-----w- c:\users\Bruce\AppData\Roaming\Malwarebytes
2013-08-10 04:03 . 2013-08-10 04:03 -------- d-----w- c:\programdata\Malwarebytes
2013-08-10 04:03 . 2013-08-10 04:03 -------- d-----w- c:\program files\Malwarebytes' Anti-Malware
2013-08-10 04:03 . 2013-04-04 19:50 22856 ----a-w- c:\windows\system32\drivers\mbam.sys
2013-08-09 03:14 . 2013-08-09 03:14 -------- d-----w- c:\windows\ERUNT
2013-08-09 02:50 . 2013-08-09 02:57 115 ----a-w- c:\windows\DeleteOnReboot.bat
2013-08-08 03:53 . 2013-08-08 03:53 -------- d-----w- C:\_OTL
2013-08-08 03:42 . 2013-08-08 03:44 -------- d-----w- c:\windows\system32\MRT
2013-08-07 01:23 . 2013-08-07 01:24 -------- d-----w- c:\users\Bruce\.autobahn
2013-08-06 00:36 . 2013-08-06 00:36 1069032 ----a-w- c:\programdata\Microsoft\Windows\DRM\install_flashplayer.exe
2013-08-05 23:01 . 2013-08-08 03:40 -------- d-----w- c:\users\Bruce\AppData\Local\a469e699-64a9-40e7-9471-53f0beca95a8ad
.
.
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2013-07-29 19:27 . 2012-12-14 23:46 37664 ----a-w- c:\windows\system32\drivers\avgtpx86.sys
2013-06-13 21:34 . 2011-05-07 23:51 452120 ----a-w- c:\windows\system32\drivers\vsdatant.sys
2013-06-04 01:50 . 2013-07-10 03:36 2049024 ----a-w- c:\windows\system32\win32k.sys
2013-06-01 04:06 . 2013-07-10 03:36 505344 ----a-w- c:\windows\system32\qedit.dll
2013-05-29 01:50 . 2013-07-10 08:13 1800704 ----a-w- c:\windows\system32\jscript9.dll
2013-05-29 01:41 . 2013-07-10 08:13 1427968 ----a-w- c:\windows\system32\inetcpl.cpl
2013-05-29 01:41 . 2013-07-10 08:13 1129472 ----a-w- c:\windows\system32\wininet.dll
2013-05-29 01:37 . 2013-07-10 08:13 142848 ----a-w- c:\windows\system32\ieUnatt.exe
2013-05-29 01:36 . 2013-07-10 08:13 420864 ----a-w- c:\windows\system32\vbscript.dll
2013-05-29 01:33 . 2013-07-10 08:13 2382848 ----a-w- c:\windows\system32\mshtml.tlb
.
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
.
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"MoneyAgent"="c:\program files\Microsoft Money\System\mnyexpr.exe" [2002-07-17 200767]
"WMPNSCFG"="c:\program files\Windows Media Player\WMPNSCFG.exe" [2008-01-21 202240]
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"SynTPEnh"="c:\program files\Synaptics\SynTP\SynTPEnh.exe" [2008-04-17 1049896]
"QPService"="c:\program files\HP\QuickPlay\QPService.exe" [2008-09-24 468264]
"UpdateLBPShortCut"="c:\program files\CyberLink\LabelPrint\MUITransfer\MUIStartMenu.exe" [2008-06-14 210216]
"UpdatePSTShortCut"="c:\program files\CyberLink\DVD Suite\MUITransfer\MUIStartMenu.exe" [2008-10-07 210216]
"UCam_Menu"="c:\program files\CyberLink\YouCam\MUITransfer\MUIStartMenu.exe" [2007-12-24 222504]
"QlbCtrl.exe"="c:\program files\Hewlett-Packard\HP Quick Launch Buttons\QlbCtrl.exe" [2008-08-01 202032]
"UpdateP2GoShortCut"="c:\program files\CyberLink\Power2Go\MUITransfer\MUIStartMenu.exe" [2008-06-14 210216]
"UpdatePDIRShortCut"="c:\program files\CyberLink\PowerDirector\MUITransfer\MUIStartMenu.exe" [2008-06-14 210216]
"HP Health Check Scheduler"="c:\program files\Hewlett-Packard\HP Health Check\HPHC_Scheduler.exe" [2008-10-09 75008]
"hpWirelessAssistant"="c:\program files\Hewlett-Packard\HP Wireless Assistant\HPWAMain.exe" [2008-04-15 488752]
"IgfxTray"="c:\windows\system32\igfxtray.exe" [2010-08-26 136216]
"HotKeysCmds"="c:\windows\system32\hkcmd.exe" [2010-08-26 171032]
"Persistence"="c:\windows\system32\igfxpers.exe" [2010-08-26 170520]
"HP Software Update"="c:\program files\Hp\HP Software Update\HPWuSchd2.exe" [2011-02-18 49208]
"CanonMyPrinter"="c:\program files\Canon\MyPrinter\BJMyPrt.exe" [2010-07-26 2569616]
"CanonSolutionMenuEx"="c:\program files\Canon\Solution Menu EX\CNSEMAIN.EXE" [2010-09-15 1213848]
"IJNetworkScannerSelectorEX"="c:\program files\Canon\IJ Network Scanner Selector EX\CNMNSST.exe" [2010-09-09 452016]
"ZoneAlarm"="c:\program files\CheckPoint\ZoneAlarm\zatray.exe" [2013-06-20 73832]
"BCSSync"="c:\program files\Microsoft Office\Office14\BCSSync.exe" [2010-03-13 91520]
"Adobe ARM"="c:\program files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" [2012-07-27 919008]
.
c:\users\Bruce\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\
NexDef Plug-in.lnk - c:\users\Bruce\AppData\Local\Autobahn\nexdef.exe [2011-8-11 15490560]
RCA Detective.lnk - c:\users\Bruce\Documents\RCA Detective\RCADetective.exe [2011-12-25 868864]
.
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\policies\system]
"EnableUIADesktopToggle"= 0 (0x0)
.
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\Wdf01000.sys]
@="Driver"
.
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\WudfSvc]
@="Service"
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\ZoneLabsFirewall]
"DisableMonitoring"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Svc]
"FirewallOverride"=dword:00000001
.
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\svchost]
LocalServiceAndNoImpersonation REG_MULTI_SZ FontCache
.
.
------- Supplementary Scan -------
.
uStart Page = hxxp://www.google.com/
mStart Page = hxxp://www.google.com
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~3\Office14\EXCEL.EXE/3000
IE: Se&nd to OneNote - c:\progra~1\MICROS~3\Office14\ONBttnIE.dll/105
TCP: DhcpNameServer = 192.168.1.254
DPF: {12545791-AC9A-44B2-8964-0DA216C4A4E5} - hxxp://www.partserver.de/partserver/viewer/cnsweb3d/cnsweb3d.cab
.
- - - - ORPHANS REMOVED - - - -
.
WebBrowser-{91DA5E8A-3318-4F8C-B67E-5964DE3AB546} - (no file)
HKCU-Run-Start WingMan Profiler - (no file)
HKCU-Run-Easy Dock - (no file)
HKLM-Run-Easy Dock - (no file)
SafeBoot-WudfPf
SafeBoot-WudfRd
AddRemove-Applet - c:\windows\system32\javaws.exe
.
.
.
**************************************************************************
.
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2013-08-14 20:11
Windows 6.0.6002 Service Pack 2 NTFS
.
scanning hidden processes ...
.
scanning hidden autostart entries ...
.
scanning hidden files ...
.
scan completed successfully
hidden files: 0
.
**************************************************************************
.
--------------------- LOCKED REGISTRY KEYS ---------------------
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{73C9DFA0-750D-11E1-B0C4-0800200C9A66}]
@Denied: (A 2) (Everyone)
@="FlashBroker"
"LocalizedString"="@c:\\Windows\\system32\\Macromed\\Flash\\FlashUtil32_11_8_800_94_ActiveX.exe,-101"
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{73C9DFA0-750D-11E1-B0C4-0800200C9A66}\Elevation]
"Enabled"=dword:00000001
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{73C9DFA0-750D-11E1-B0C4-0800200C9A66}\LocalServer32]
@="c:\\Windows\\system32\\Macromed\\Flash\\FlashUtil32_11_8_800_94_ActiveX.exe"
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{73C9DFA0-750D-11E1-B0C4-0800200C9A66}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{6AE38AE0-750C-11E1-B0C4-0800200C9A66}]
@Denied: (A 2) (Everyone)
@="IFlashBroker5"
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{6AE38AE0-750C-11E1-B0C4-0800200C9A66}\ProxyStubClsid32]
@="{00020424-0000-0000-C000-000000000046}"
.
[HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{6AE38AE0-750C-11E1-B0C4-0800200C9A66}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
"Version"="1.0"
.
[HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{4D36E96D-E325-11CE-BFC1-08002BE10318}\0000\AllUserSettings]
@Denied: (A) (Users)
@Denied: (A) (Everyone)
@Allowed: (B 1 2 3 4 5) (S-1-5-20)
"BlindDial"=dword:00000000
.
Completion time: 2013-08-14 20:14:14
ComboFix-quarantined-files.txt 2013-08-15 01:14
.
Pre-Run: 211,086,741,504 bytes free
Post-Run: 212,309,106,688 bytes free
.
- - End Of File - - 2AE1034DC8D2AD1BD0D67810C82A92D0
588AE8F0C685C02BA11F30D9CD7E61A0
#27
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #27](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 15 August 2013 - 07:23 AM
Posted 15 August 2013 - 07:23 AM

I should have mentioned this is my last post. I neglected to disable the IE SmartScreen Filter when I ran RogueKiller the last time. I was looking at previous posts and realized that I probably should have. Also, when ComboFix ran, I did get one message that it was not able to completely delete all of the files in a folder. I believe it was C:\ERUNT. I clicked OK and it continued to what I believe was a successful run.
Bruce
#28
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #28](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 15 August 2013 - 08:58 AM
Posted 15 August 2013 - 08:58 AM

Step-1.
Disable the Zone Alarm Firewall. To do that:
- On the Windows taskbar, next to the clock, right-click the ZoneAlarm icon, and then click Shutdown ZoneAlarm.
Note: If you don't see the icon next to the clock, click the arrow next to the clock to reveal the hidden icons.
- You will get a Zone Alarm warning asking if you are sure. Click Yes
Step-2.
Run the OTL fix in Step 2. of post #25. IF it runs this time go to Step 4. IF it still won't run try running TFC again. IF TFC runs then go to Step 4. IF it won't run then complete the following:
Step-3.
Run CCleaner
Click here to go to the CCleaner download page.
In the CCleaner Free cloumn under the Download from: heading click the Piriform link to download CCleaner and save it to the desktop.
Close the browser and all open windows.
Right click the ccsetupXXX.exe file, click Run as Administrator and OK any UAC prompts to install the program.
NOTE: When it gives you the option to install Yahoo toolbar uncheck the box next to it.
After the program is installed:
- Right click the CCleaner icon on the desktop, click Run as Administrator and OK any UAC prompts to run the program. You will see the following console:

- Click the Cleaner icon in the left column and make sure the Windows tab is selected.
- Under the Internet Explorer section check the boxes beside:
- Temporary Internet Files
- History
- Cookies
- Recently Typed URLs
- Index.dat files
- Last Downloaded Location
- Under the Windows Explorer section check all boxes except Network Passwords unless you want to clear them also.
- Under the System section check the boxes beside:
- Empty Recycle Bin
- Temporary Files
- Click the Application tab.
- If there are any browsers listed, like Firefox, Chrome, Safari etc;, check all boxes for all listed browsers except Saved Passwords unless you want to clear them also.
- Under the Applications section check all boxes. This will clear the TEMP files for each application listed.
- You don't need to check anything in the rest of the sections.
- Click the Run Cleaner button.
NOTE: IF CCleaner prompts you to backup your registry to a .REG file before CCleaner runs. Please allow this. - When the program has finished you will see a screen showing you what was deleted. You can now close CCleaner.
Step-4.
- Re-enable the Zone Alarm firewall.(But you might want to seriously consider getting rid of Zone Alarm and replacing it. There are alternatives we can recommend that don't cause nearly the headaches.)
- Reinstall the AVG antivirus program using the avg free x86 all 2013 3392a6523.exe file you downloaded earlier.
- Let me know how things went.
#29
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #29](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 15 August 2013 - 06:03 PM
Posted 15 August 2013 - 06:03 PM

A few questions...what firewall would you recommend? Why do you recommend not using Zone Alarm? Also, what do you recommend for general malware prevention and maintenance? I thought a firewall and an AV would be enought but I was obviously wrong. What about key loggers? How would you recommend setting up a PC for children's use? They've been using the administrator logon and I wonder if this was a significant part of my problem.
Thanks for all your help.
Bruce
#30
![FBI Moneypak and Subsequent Google Redirect [Solved]: post #30](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 16 August 2013 - 10:51 AM
Posted 16 August 2013 - 10:51 AM

Well at last we got to the bottom of it. That was a headache.Well, ZoneAlarm was the problem.
Depends on your Internet configuration. If you use a Router or Gateway you really don't need an inbound/outbound firewall (like Zone Alarm or the other 3rd party firewalls). Routers/Gateways have their own layer of protection so simply turning the Windows firewall on will do the job nicely. All I use is a Router, Microsoft Security Essentials for an antivirus program and the Windows firewall. But if you want to use a 3rd party firewall try Online Armor. It is much more reliable than Zone Alarm and doesn't cause all of the conflicts and hassles. Online Armor is recommended by GeeksToGo. If you want to install it click here to go to the Online Armor Free page and click the Download button under the Online Armor Free description....what firewall would you recommend?
NOTE: Uninstall the Zone Alarm firewall before installing the new firewall. And learn how to set up the 3rd party firewall. There is a good tutorial on Understanding and Using Firewalls here
Because of dumb stuff like what we just went through and other headaches that ZA has caused because of conflicts with other software. Zone Alarm is a good inbound/outbound firewall but it can cause more conflicts than other 3rd party firewalls.Why do you recommend not using Zone Alarm?
I don't use anything more than Microsoft Security Essentials for an antivirus (AVG is also a good AV and if you are happy with it I wouldn't change), the Windows firewall and MalwareBytes (the free version). The upside to MSE for me is that it's easy to setup. There aren't a lot of settings or modules that you need to configure. It updates the program version through Windows Updates and the malware definition files are automatically updated. And I don't run into a situation where MSE has caused a conflict with any other software very often. It is also just as effective as any other free AV software and some paid AV software. In my opinion it's better than a lot of them. MSE is one of the things that Microsoft got right. And it's a GeeksToGo Recommended AV.Also, what do you recommend for general malware prevention and maintenance?
Then I use MalwareBytes for a Quick scan several times a week and a Full scan at least once a month.
Nothing can catch everything. Having an up to date AV program and the firewall will prevent al lot, but malware writers are smart. They're always changing the entry point of the malware to places where the AV programs won't catch them...until it's noticed and the AV programs can be updated to find and stop it.I thought a firewall and an AV would be enought but I was obviously wrong.
I don't have any anti keylogger programs installed. I don't do on-line banking and I don't save passwords to sites like my credit card companies in any browsers. I keep them in an encrypted file with a strong password. If you use online banking there is a program that will help protect your security. I can research it and let you know what it is if you want.What about key loggers?
You hit the nail on the head. For security purposes you shouldn't ever log onto the computer with Administrator privileges. I have all user accounts set up as Standard (limited) users. And then I have one account set up as System Admin with Administrator privileges.How would you recommend setting up a PC for children's use? They've been using the administrator logon and I wonder if this was a significant part of my problem.
I would log into the computer using an Administrator account, then go into the User Accounts section in Control Panel and create a seperate account for each child and make it a Standard account. That way they will still be able to use most programs, like web browsers, and they will be able to change system settings that do not affect other users or the security of the computer. Next you should change the password on the Administrator account and don't let anyone else have it. When/if they come to you complaining that they can't install the latest/greatest software or toolbar, or the browser won't let them download or install certain things you can have them show it to you and then if it is appropriate you can download the program or file and then right click on it and click Run as Administrator and provide the Admin password and it will install.
And you can log on with the Admin account when you want to check for updates or do any other work that needs Admin privileges. It's more of a hassle, but it's safer and more secure.
OK! Well done.
The first thing we need to do is to remove all the tools that we have used. This is so that should you ever be re-infected, you will download updated versions.
If you didn't uninstall ESET after running the program we will do it now.
Step-1.
Uninstall ESET
1. Please click the Start Orb
 , click Control Panel. Under the Programs heading click Uninstall a program
, click Control Panel. Under the Programs heading click Uninstall a program1. Please click Start > Control Panel > Add/Remove Programs
2. In the list of programs installed, locate the following program(s):
ESET
3. Right click the program and click Uninstall
4. After the programs have been uninstalled, close the Installed Programs window and the Control Panel.
5. Reboot the computer.
Delete the folders associated with the uninstalled programs.(Only do this if you uninstalled the program)
1. Using Windows Explorer (to get there right-click your Start button and click "Explore"), please delete the following folders(s) (if present):
C:\Program Files\ESET
2. Close Windows Explorer.
Step-2.
Uninstall ComboFix
- Click the Start Orb and click Run. This will display the Run dialogue box .
- In the Run box, type in ComboFix /Uninstall (Notice the space between the "x" and "/") then click OK

- Follow the prompts on the screen.
- A message should appear confirming that ComboFix was uninstalled
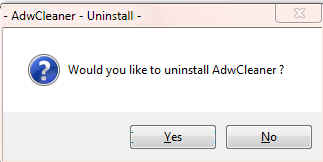
Uninstall AdwCleaner
Re-open AdwCleaner
- Click the Uninstall button
- Confirm with yes
Step-4.
OTL Cleanup
1. Please re-open
- Be sure all other programs are closed as this step will require a reboot.
- Click on

- You will be prompted to reboot your system. Please do so.
Step-5.
Delete the following Files and Folders (If Present):
MBR.dat
JRT.exe
JRT.txt
SecurityCheck.exe
checkup.txt
Adobe FlashPlayer setup file
Adobe Reader setup file
jre-7u25-Windows-i586.exe
ccsetupXXX.exe
avg free x86 all 2013 3392a6523.exe
avg_remover_stf_x86_2013_3341.exe
Delete any other .bat, .log, .reg, .txt, and any other files created during this process, and left on the desktop and empty the Recycle Bin.
Step-6.
Reset Hidden Files and Folders
1. Click Start,click Control Panel.
2. Click Folder Options.... NOTE: If you are in the Category view, click Appearance, then Folder Options
3. On the Folder Options window click the View tab.
4. In the Advanced settings: box, Under Hidden files and folders, click the Do not show hidden files and folders button.
5. Click the Hide protected operating system files (Recommended) box.
6. Click Apply and then OK
Step-7.
Make a Fresh Restore Point, Clear the Old Restore Points, and Re-enable System Restore
The files in System Restore are protected to prevent any programs from changing those files. This is the only way to clean these files: (You will lose all previous restore points which are likely to be infected, but that's good news).
Note: Do not clear infected/old System Restore points before creating a new System Restore point first!For Vista and Windows 7:
- Click the Start Orb. Click Control Panel. Click System and Maintenance
- Click System
- In the left column under Tasks, click Advance System Settings and accept the warning if you get one
- Click the System Protection Tab
- In the Available Disks box put a ckeck mark in the box next to OS (?:) (System). Your drive letter will be shown in place of the ?
Note: It may take some time for the system to populate the Available Disks box, so be patient.
- Click the Create button at the bottom
- Type in a name fo the restore point, i.e: Clean
- Click Create
- A small System Protection window will come up telling you a Restore Point is being created.
- Another System Protection window will come up telling you the Restore Point has been created, click OK
- Click OK again.
- Close the Control Panel
- Click Start(Windows 7 Orb), click Run (or press the Windows key and R together) to bring up the Run box.
- Copy and Paste the following in the Run box:
cleanmgr
- Click OK
A Disk Cleanup Options popup will open

- Click Files from all users on this computer
A Drive Selection popup will open
NOTE: You will not see this window unless you have more than one drive or partition on your computer.

If you chose Files from all users on this computer above, then click on Continue for UAC prompt. - Select the system drive, C:\ and click OK.
- For a few moments the system will make some calculations

- The Disk Cleanup Window will open:

- Click the More Options tab.
- Click the Clean up button under the System Restore and Shadow Copies section. (See screenshot below)

- In the Disk Cleanup dialog box, click Delete (See screenshot below).

- You will get a Disk Cleanup confirmation (See screenshot below)

- Click Delete Files, and then click OK.
Preventing Re-Infection
Below, I have included a number of recommendations for how to protect your computer against future malware infections.
:Keep Windows Updated:-Windows Updates are constantly being revised to combat the newest hacks and threats. Microsoft releases security updates that help your computer from becoming vulnerable.
Please either enable Automatic Updates or get into the habit of checking Windows Update regularly. They usually have security updates every month. You can set Windows to notify you of Updates so that you can choose, but only do this if you believe you are able to understand which ones are needed. This is a crucial security measure.
Vista and Windows 7 Users:
1. Click Start> All Programs, from the list find Windows Update and click it.
:Turn On Automatic Updates:
1. Click Start> Control Panel. Click Security. Under Windows Update, Click Turn automatic on or off.
2. On the next page, under Important Updates, Click the Drop down arrow on the right side of the box and Click Install Updates Automatically(recommended).
If you click this setting, click to select the day and time for scheduled updates to occur. You can schedule Automatic Updates for any time of day. Remember, your computer must be on at the scheduled time for updates to be installed. After you set this option, Windows recognizes when you are online and uses your Internet connection to find updates on the Windows Update Web site or on the Microsoft Update Web site that apply to your computer. Updates are downloaded automatically in the background, and you are not notified or interrupted during this process. An icon appears in the notification area of your task bar when the updates are being downloaded. You can point to the icon to view the download status. To pause or to resume the download, right-click the icon, and then click Pause or Resume. When the download is completed, another message appears in the notification area so that you can review the updates that are scheduled for installation. If you choose not to install at that time, Windows starts the installation on your set schedule.
: Keep Java Updated :
WARNING: Java is the #1 exploited program at this time. The Department of Homeland Security recommends that computer users disable Java
See this article and this article.
I would recommend that you completely uninstall Java unless you need it to run an important software or need it to play games on-line.
In that instance I would recommend that you only use Firefox or Chrome to visit those sites and do the following:
- For Firefox, install the NoScript add-on.
- For Chrome, install the Script-No add-on.
NOTE: After installing the add-ons you will need to tell them that the site you are visiting is allowed to run Java. - Disable Java in your browsers until you need it for that software and then enable it. (See How to disable Java in your web browser or How to unplug Java from the browser)
- Click the Start button
- Click Control Panel
- Double Click Java - Looks like a coffee cup. You may have to switch to Classical View on the upper left of the Control Panel to see it.
- Click the Update tab
- Click Update Now
- Allow any updates to be downloaded and installed
- Open Adobe Reader
- Click Help on the menu at the top
- Click Check for Updates
- Allow any updates to be downloaded and installed
NOTE: Many installers offer third-party downloads that are installed automatically when you do not uncheck certain checkboxes. While most of the time not being malicious you usually do not want these on your computer. Be careful during the installation process and you will avoid seeing tons of new unwanted toolbars in your favorite web browser.
:Web Browsers:
:Make your Internet Explorer more secure:
1. From within Internet Explorer click on the Tools menu and then click on Options.
2. Click once on the Security tab
3. Click once on the Internet icon so it becomes highlighted.
4. Click once on the Custom Level button.
5. Change the Download signed ActiveX controls to "Prompt"
6. Change the Download unsigned ActiveX controls to "Disable"
7. Change the Initialise and script ActiveX controls not marked as safe to "Disable"
8. Change the Installation of desktop items to "Prompt"
9. Change the Launching programs and files in an IFRAME to "Prompt"
10. When all these settings have been made, click on the OK button.
11. If it prompts you as to whether or not you want to save the settings, click the Yes button.
12. Next press the Apply button and then the OK to exit the Internet Properties page.
This webpage is worth bookmarking/reading for future reference:
Securing Your Web Browser
:Alternate Browsers:
If you use Firefox, I highly recommend these add-ons to keep your PC even more secure.
- NoScript - for blocking ads and other potential website attacks
- WebOfTrust - a safe surfing tool for your browser. Traffic-light rating symbols show which websites you can trust when you search, shop and surf on the Web.
- McAfee SiteAdvisor - this tells you whether the sites you are about to visit are safe or not. A must if you do a lot of Googling
- MVPS Hosts file-replaces your current HOSTS file with one containing well known ad sites and other bad sites. Basically, this prevents your computer from connecting to those sites by redirecting them to 127.0.0.1 which is your local computer, meaning it will be difficult to infect yourself in the future.
Preventative programs that will help to keep the nasties away! We will start with Anti Spyware programs. I would advise getting a couple of them at least, and running a full scan at least once a month. Run Quick Scans at least once a week. Download the Free versions. And update the definitions before running scans.
========Anti Spyware========
- Malwarebytes-Free Version- a powerful tool to search for and eliminate malware found on your computer.
- SUPERAntiSpyware Free Edition-another scanning tool to find and eliminate malware.
- SpywareBlaster-to help prevent spyware from installing in the first place. A tutorial can be found here.
- SpywareGuard-to catch and block spyware before it can execute. A tutorial can be found here.
- WinPatrol - will alert you to hijackings, malware attacks and critical changes made to your computer without your permission. Help file and tutorial can be found here.
========TEMP File Cleaners========
- TFC by OldTimer-A very powerful cleaning program for 32 and 64 bit OS. Note: You may have this already as part of the fixes you have run.
- CleanUP-Click the Download CleanUP! link. There is also a Learn how to use CleanUP! link on this page.
- Keep a backup of your important files.-Now, more than ever, it's especially important to protect your digital files and memories. This article is full of good information on alternatives for home backup solutions.
- ERUNT-(Emergency Recovery Utility NT) allows you to keep a complete backup of your registry and restore it when needed. The standard registry backup options that come with Windows back up most of the registry but not all of it. ERUNT however creates a complete backup set, including the Security hive and user related sections. ERUNT is easy to use and since it creates a full backup, there are no options or choices other than to select the location of the backup files. The backup set includes a small executable that will launch the registry restore if needed.
It is also possible for other programs on your computer to have security vulnerability that can allow malware to infect you. Therefore, it is also a good idea to check for the latest versions of commonly installed applications that are regularly patched to fix vulnerabilities.
A program that will do this is listed below. Download and install the program and run it monthly:
Filehippo Update Checker
Finally, please read How did I get infected in the first place? by Mr. Tony Cline
I'd be grateful if you could reply to this post so that I know you have read it and, if you've no other questions, the thread can then be closed.
IF I have helped you and you want to say "thanks", you can do that by clicking the Rep+ button at the bottom right of this post.
I Will Keep This Open For 24 hours or so. If Anything Comes Up - Just Come Back And Let Me Know
Stay Safe
godawgs
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked




 Sign In
Sign In Create Account
Create Account

