Ready when you are

Trojan.downloader9.55030 [Solved]
#16
![Trojan.downloader9.55030 [Solved]: post #16](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 14 February 2014 - 11:33 PM
Posted 14 February 2014 - 11:33 PM

Ready when you are
#17
![Trojan.downloader9.55030 [Solved]: post #17](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 14 February 2014 - 11:35 PM
Posted 14 February 2014 - 11:35 PM

LOL! I'm not going anywhere till you say it's safe to do so.
Ready when you are
#18
![Trojan.downloader9.55030 [Solved]: post #18](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 15 February 2014 - 06:40 AM
Posted 15 February 2014 - 06:40 AM

I'm so glad everything looks good!
You did a great job...thank you!!!!
You are welcome, I'm glad we were able to help you, which leads me to this:
Great news, your logs are CLEAN!
- I need to remove the tools we installed on your machine.
- We also have some programs on your machine that need updating to help protect you in the future.
Step 1: Delete Old Restore Points and Create a New Clean One.
We're going to delete your old restore points and create a new one. We do this in case you need to do a system restore, you will have a clean restore point.
Please follow the instructions below:
- Start OTL and copy the text in the quote box below.
- Paste the contents into the Custom Scans/Fixes box and click the Run Fix button.
- OTL will delete the old restore points and create a new one.
:Files
%systemroot%\system32\vssadmin delete shadows /for=c: /all /quiet /c
:Commands
[CreateRestorePoint]
Step 2: Update Adobe Reader and Install FileHippo
Updating Adobe Reader
- Malware will exploit any vulnerabilities it can find in outdated software. If you are using Adobe Reader for reading pdf files, try using FoxIt Reader. It is a very capable alternative to Adobe.
- Please click here to download FoxIt Reader.
- If you wish to continue to use Adobe Reader, then please update it by clicking here.
- Please remember to uncheck the option to install McAfee's Security Suite.
Keeping your software updated
Another weapon against malicious programs and viruses is to keeping other programs updated. There are several programs out there that can check for out of date programs on your computer. One is Filehippo. You can run this on a weekly or monthly basis to check your programs for updates and then it will provide a link for you to download them.
Download Filehippo Updatechecker
Step 3: Tool Removal
You can delete SystemLook from your desktop.
You can uninstall ESET Online Scanner at this time.
I recommend keeping Malwarebytes Anti-Malware installed. Make sure to update it and run it at least once a week.
Start OTL and click the Cleanup button. OTL will delete it's quarantined files and then uninstall itself.
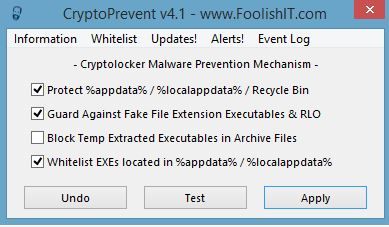
Step 4: Information and Protecting your machine against CryptoLocker
- Watch what you open in your emails. If you get an email from an unknown source with any attached files, do not open it.
- Be careful of the websites you visit.
- When installing new programs, don't be "click happy" and click through the screens. Many programs come with adware in them and are set to install them by default. Several programs require that you uncheck or select no to prevent the installation. Take you time and read each screen as you go.

- To help protect yourself while on the web, I recommend you read How did I get infected in the first place?
A warning about CryptoLocker
CryptoLocker is a ransomware program that was released around the beginning of September 2013 that targets all versions of Windows including Windows XP, Windows Vista, Windows 7, and Windows 8. This ransomware will encrypt certain files using a mixture of RSA & AES encryption. When it has finished encrypting your files, it will display a CryptoLocker payment program that prompts you to send a ransom of either $100 or $300 in order to decrypt the files. This screen will also display a timer stating that you have 72 hours, or 4 days, to pay the ransom or it will delete your encryption key and you will not have any way to decrypt your files. This ransom must be paid using MoneyPak vouchers or Bitcoins. Once you send the payment and it is verified, the program will decrypt the files that it encrypted.
Please download and install CryptoPrevent to lock your machine down from this infection.
Are there any further issues I can assist you with?
#19
![Trojan.downloader9.55030 [Solved]: post #19](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 15 February 2014 - 10:10 PM
Posted 15 February 2014 - 10:10 PM

When I tried to set a new restore point via OTL,
Kaspersky sent an alert stating it was malicious
activity detected:
PDM: Trojan.Win32.Generic
I figured this may be a false alert, but I terminated
the process anyway to be sure. Please advise and let me
know if I should ignore this alert next time and proceed.
Edited by mango_nj, 15 February 2014 - 10:10 PM.
#20
![Trojan.downloader9.55030 [Solved]: post #20](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 15 February 2014 - 10:52 PM
Posted 15 February 2014 - 10:52 PM

Hi Rusty!
When I tried to set a new restore point via OTL,
Kaspersky sent an alert stating it was malicious
activity detected:
PDM: Trojan.Win32.Generic
I figured this may be a false alert, but I terminated
the process anyway to be sure. Please advise and let me
know if I should ignore this alert next time and proceed.
Hello
Disable Kaspersky before running that restore point creation. That should allow the new restore point to be created.
#21
![Trojan.downloader9.55030 [Solved]: post #21](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 16 February 2014 - 03:03 AM
Posted 16 February 2014 - 03:03 AM

I also decided to try FoxIt Reader and see if I like it better than Adobe
and I installed CryptoLocker. Thank you for everything!!!!
I guess I should be on my way. You did an excellent job! Hard
to believe you're still in training. You have a great teacher.
appreciate your patience...
YOU ARE AWESOME!!!
#22
![Trojan.downloader9.55030 [Solved]: post #22](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 16 February 2014 - 07:02 AM
Posted 16 February 2014 - 07:02 AM

Hi Rusty! ALL DONE

I also decided to try FoxIt Reader and see if I like it better than Adobe
and I installed CryptoLocker. Thank you for everything!!!!
I guess I should be on my way. You did an excellent job! Hard
to believe you're still in training. You have a great teacher.
appreciate your patience...
YOU ARE AWESOME!!!
Thank you
Safe surfing!
#23
![Trojan.downloader9.55030 [Solved]: post #23](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 16 February 2014 - 03:21 PM
Posted 16 February 2014 - 03:21 PM

If you're the topic starter, and need this topic reopened, please contact a staff member with the address of the thread.
Everyone else please begin a New Topic.
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked






 Sign In
Sign In Create Account
Create Account

