What is Windows AntiVirus Adviser?
The Malwarebytes research team has determined that Windows AntiVirus Adviser is a fake anti-malware application. These so-called "rogues" use intentional false positives to convince users that their systems have been compromised. Then they try to sell you their software, claiming it will remove these threats. In extreme cases the false threats are actually the very trojans that advertise or even directly install the rogue. You are strongly advised to follow our removal instructions below.
How do I know if I am infected with Windows AntiVirus Adviser?
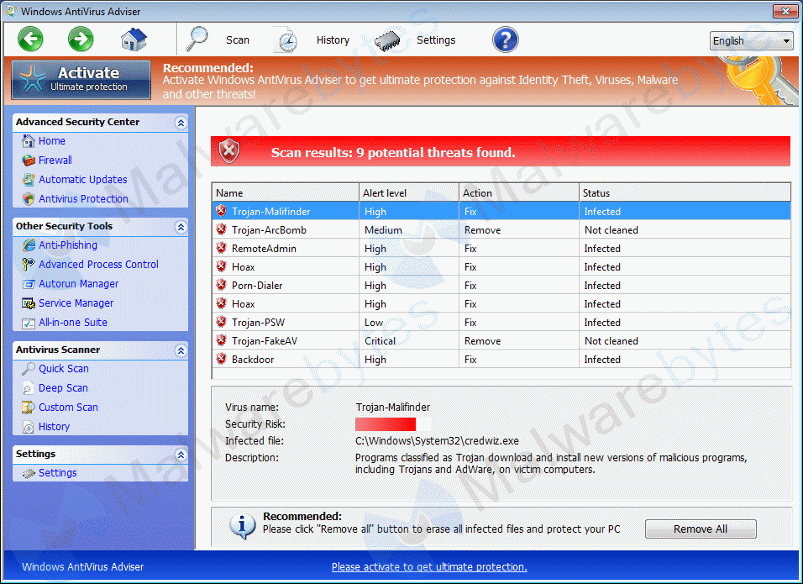
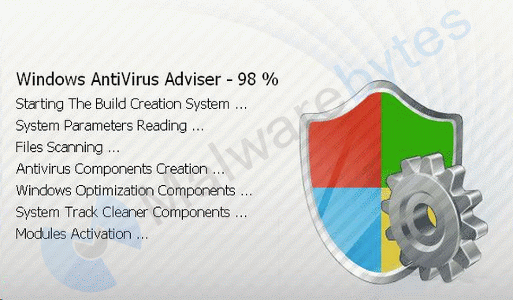
This is how the main screen of the rogue application looks:
You will find this icon in your taskbar:
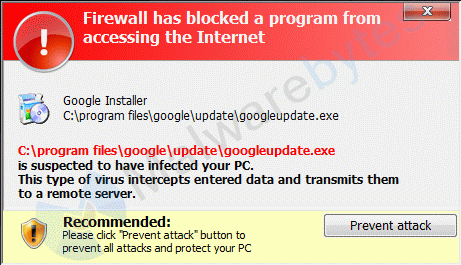
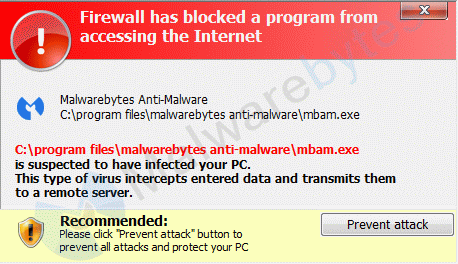
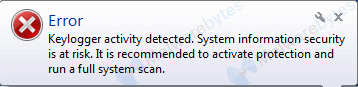
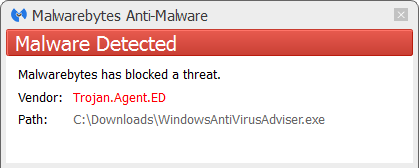
And see these warnings:
How did Windows AntiVirus Adviser get on my computer?
Rogue programs use different methods for spreading themselves. This particular one was installed by a trojan.
How do I remove Windows AntiVirus Adviser?
Our program Malwarebytes Anti-Malware can detect and remove this rogue application.
Because this rogue blocks the normal use of programs we will use Chameleon to remove it. During removal your taskbar may disappear. This is normal and necessary for removal. It will be back after the reboot.
- If Malwarebytes Anti-Malware is not installed on the infected computer.
- In order for this to work, you will need a second PC which is not infected and a USB flash drive or blank CD and CD burner or some other means to transfer files from one computer to the other.
- From your clean computer, download and install Malwarebytes Anti-Malware from here
- Once installed, open the folder where the program was installed (usually C:\Program Files\Malwarebytes' Anti-Malware or C:\Program Files (x86)\Malwarebytes' Anti-Malware)
- Once there, right-click on the Chameleon folder and choose Copy
- Close the Malwarebytes' Anti-Malware folder
- Right-click on your USB flash drive or blank CD and choose Paste and proceed to burn the CD if using a blank CD or remove your flash drive if using a flash drive
- Now, insert your USB flash drive or CD which should now contain the Chameleon folder into the infected PC
- Make certain that your infected PC is connected to the internet and then open the Chameleon folder which now resides on the desktop of your infected computer and double-click on firefox.exe.
- Follow the onscreen instructions to press a key to continue and Chameleon will proceed to download and install Malwarebytes Anti-Malware for you.
- Once it has done this, it will attempt to update Malwarebytes Anti-Malware, click OK when it says that the database was updated successfully
- Next, Malwarebytes Anti-Malware will automatically open and perform a Threat scan
- Upon completion of the scan, if anything has been detected, click on Apply Actions
- Malwarebytes Anti-Malware will now remove any threats that were detected. Please click Yes if prompted to reboot your computer to allow the removal process to complete
- After your computer restarts, open Malwarebytes Anti-Malware and perform one last Threat scan to verify that there are no remaining threats
- If Malwarebytes Anti-Malware is already installed on the infected computer.
- In order for this to work, you must already have Malwarebytes Anti-Malware version 2.0 or later already installed on your infected PC.
- Open the program folder for Malwarebytes Anti-Malware (normally C:\Program Files\Malwarebytes Anti-Malware or C:\Program Files (x86)\Malwarebytes Anti-Malware)
- Once there, open the Chameleon folder
- Next, double-click on firefox.exe. This should result in a black DOS/command prompt window opening up.
- Press any key to continue as it says in the window
- Malwarebytes Chameleon will proceed to update Malwarebytes Anti-Malware, so ensure that you are connected to the internet if possible
- Once the update completes and it says your database is updated, click on OK
- Malwarebytes Chameleon will then terminate any threats running in memory, which may take a while, so please be patient
- Upon completion, Malwarebytes Anti-Malware will open automatically and perform a Threat scan
- Once the scan is complete, click on Show Results and remove any threats that are found by clicking Apply Actions
- If prompted to restart your computer to complete the removal process, click Yes
- After your computer restarts, open Malwarebytes Anti-Malware and perform one last Threat scan to verify that there are no remaining threats
- No, Malwarebytes' Anti-Malware removes Windows AntiVirus Adviser completely.
We hope our application has helped you eradicate this malicious software. If your current security solution let this infection through, you might please consider purchasing the FULL version of Malwarebytes Anti-Malware for additional protection.
As you can see below the full version of Malwarebytes Anti-Malware would have protected you against the Windows AntiVirus Adviser rogue. It would have warned you before the rogue could install itself, giving you a chance to stop it before it became too late.
Technical details for experts
Signs in a HijackThis log:
O4 - HKLM\..\Run: [MSmpeNG] C:\Users\{username}\AppData\Roaming\svc-qmvx.exe
O4 - HKCU\..\Run: [MSmpeNG] C:\Users\{username}\AppData\Roaming\svc-qmvx.exeNote: the filename is semi-random and has the format svc-****.exe where the asterisks represent random lettersAlterations made by the installer:
File system details
---------------------------------------------
In the existing folder C:\Users\{username}\AppData\Roaming
Adds the file svc-qmvx.exe"="11/10/2014 12:28 PM, 1016832 bytes, A
Adds the file svc-qmvx.exe.bat"="11/10/2014 12:59 PM, 65 bytes, A
Registry details
------------------------------------------
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System]
"ConsentPromptBehaviorAdmin"="REG_DWORD", 0
"ConsentPromptBehaviorUser"="REG_DWORD", 0
"EnableLUA"="REG_DWORD", 0
"EnableVirtualization"="REG_DWORD", 0
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"MSmpeNG"="REG_SZ", "C:\Users\{username}\AppData\Roaming\svc-qmvx.exe"
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\k9filter.exe]
"Debugger"="REG_SZ", "c:\windows\wfg1.EXE"
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mpcmdrun]
"Debugger"="REG_SZ", "c:\windows\wfg1.EXE"]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mpsvc.dll]
"Debugger"="REG_SZ", "c:\windows\wfg1.EXE"
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\mpuxsrv.exe]
"Debugger"="REG_SZ", "c:\windows\wfg1.EXE"
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msascui]
"Debugger"="REG_SZ", "c:\windows\wfg1.EXE"
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCUI.exe]
"dEbUGgEr"="REG_SZ", ""wdn.ssd" /z "
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSconfig.exe]
"Debugger"="REG_SZ", "c:\windows\wfg1.EXE"
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSseces]
"Debugger"="REG_SZ", "c:\windows\wfg1.EXE"
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations]
"LowRiskFileTypes"="REG_SZ", ".zip;.rar;.nfo;.txt;.exe;.bat;.com;.cmd;.reg;.msi;.htm;.html;.gif;.bmp;.jpg;.avi;.mpg;.mpeg;.mov;.mp3;.m3u;.wav;"
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments]
"SaveZoneInformation"="REG_DWORD", 1
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run]
"MSmpeNG"="REG_SZ", "C:\Users\{username}\AppData\Roaming\svc-qmvx.exe" Malwarebytes Anti-Malware log:
Malwarebytes Anti-Malware
www.malwarebytes.org
Scan Date: 11/10/2014
Scan Time: 12:45:50 PM
Logfile: mbamWindowsAntivirusAdviser.txt
Administrator: Yes
Version: 2.00.3.1025
Malware Database: v2014.11.10.03
Rootkit Database: v2014.11.08.01
License: Free
Malware Protection: Disabled
Malicious Website Protection: Disabled
Self-protection: Enabled
OS: Windows 7 Service Pack 1
CPU: x86
File System: NTFS
User: Malwarebytes
Scan Type: Threat Scan
Result: Completed
Objects Scanned: 274531
Time Elapsed: 3 min, 36 sec
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Disabled
Heuristics: Enabled
PUP: Enabled
PUM: Enabled
Processes: 0
(No malicious items detected)
Modules: 0
(No malicious items detected)
Registry Keys: 9
Security.Hijack, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\k9filter.exe, Quarantined, [1b002614f389a88e87d9524414f0659b],
Security.Hijack, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\mpcmdrun, Quarantined, [ab7018227804092d769374f0669d4bb5],
Security.Hijack, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\mpsvc.dll, Quarantined, [37e459e11765c0761af085dfdc2759a7],
Security.Hijack, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\mpuxsrv.exe, Quarantined, [d84345f5a7d5e0563622adbf17ec8878],
Security.Hijack, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\msascui, Quarantined, [b96283b7cfadea4c55b603617e857090],
Security.Hijack, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\MSASCUI.exe, Quarantined, [1efd26141c60c07679eb8c5f11f2d927],
Security.Hijack, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\MSconfig.exe, Quarantined, [5cbf5fdb225a79bdc0ab1ccf8083738d],
Security.Hijack, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\IMAGE FILE EXECUTION OPTIONS\MSseces, Quarantined, [c4573bffe8942e082fdd6ef6df247f81],
Trojan.Agent, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\BCKD, Quarantined, [d2498eac205cf3437387e67d778cca36],
Registry Values: 4
Trojan.Agent.ED, HKLM\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN|MSmpeNG, C:\Users\{username}\AppData\Roaming\svc-qmvx.exe, Quarantined, [908bd1692b51ec4acd1f44975ba621df]
Trojan.Agent.ED, HKCU\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN|MSmpeNG, C:\Users\{username}\AppData\Roaming\svc-qmvx.exe, Quarantined, [908bd1692b51ec4acd1f44975ba621df]
Trojan.Agent, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\BCKD|ImagePath, 33.sys, Quarantined, [d2498eac205cf3437387e67d778cca36]
PUM.LowRiskFileTypes, HKCU\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\POLICIES\ASSOCIATIONS|LowRiskFileTypes, .zip;.rar;.nfo;.txt;.exe;.bat;.com;.cmd;.reg;.msi;.htm;.html;.gif;.bmp;.jpg;.avi;.mpg;.mpeg;.mov;.mp3;.m3u;.wav;, Quarantined, [a57668d2ec90df570ce18ea6c83b52ae]
Registry Data: 0
(No malicious items detected)
Folders: 0
(No malicious items detected)
Files: 3
Trojan.Agent.ED, C:\Users\{username}\AppData\Roaming\svc-qmvx.exe, Delete-on-Reboot, [908bd1692b51ec4acd1f44975ba621df],
Rogue.WindowsAntiVirus, C:\Users\{username}\Desktop\WindowsAntiVirusAdviser.exe.bat, Quarantined, [d744ec4e3f3da492e590dbc67d86c43c],
Malware.Trace.E, C:\Users\{username}\AppData\Roaming\data.sec, Quarantined, [b06b5cde384447efd7825d39a55fa25e],
Physical Sectors: 0
(No malicious items detected)
(end) As mentioned before the full version of Malwarebytes Anti-Malware could have protected your computer against this threat.
We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

