Hello ginnyjoe,
I'm glad things have worked out for you. Resetting Internet Explorer may help with the slowness, and this step is entirely optional:
Reset Internet ExplorerNOTE: Your bookmarks/favorites should remain intact. If you wish to back them up, information on Exporting/Importing your IE bookmarks can be found
here.
- Open Internet Explorer
- Goto the Gear icon in the top right corner
- Select Internet Options
- Goto the Advanced tab
- Select the Reset button
- Enable "Delete personal Settings"
- Click the Reset button
- Close Internet Explorer
- Reboot
- The next time you open Internet Explorer, you will need to re-enable any add-ons you use, set your home page again, etc...
And now the best news of all:
Congratulations, your log is clean! 
Now, let's cover some additional steps to clean up your computer and help you avoid getting infected again...
Step 1Tools Cleanup and HousekeepingThe first thing we need to do is to remove all the tools that we have used. This is so that should you ever be re-infected, you will download updated versions. It will also remove the quarantined Malware from your computer.
Tool RemovalWe need to remove the tools we've used during cleaning your machine
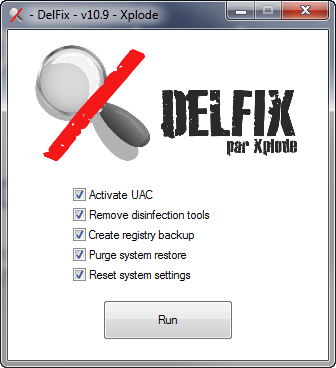
- Download DelFix from here
- Ensure Remove disinfection tools is ticked
- Also check these options:
- Activate UAC
- Create registry backup
- Purge system restore
- Reset System Settings
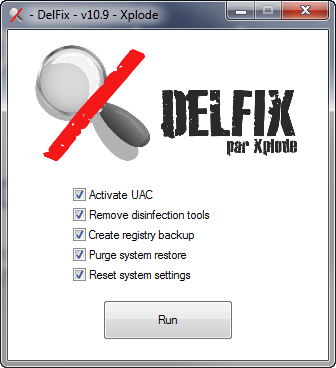
- Click Run
- The program will run for a few moments and then notepad will open with a log. Please paste the log in your next reply
And delete any
logs,
tools and
Microsoft FixIt files that you have left over on your desktop. For the FixIts they might be in your Downloads folder (or wherever else you may have saved them).
Now let's take a few preventative measures to reduce the risk of further infections.
 Step 2Automatic Updates for Windows Vista
Step 2Automatic Updates for Windows VistaAnother essential is to keep your computer updated with the latest operating system patches and security fixes. Windows Updates are constantly being revised to combat the newest hacks and threats, Microsoft releases security updates that help keep your computer from becoming vulnerable. It is best if you have these set to download automatically:
Turn ON Automatic Updates in Windows VistaStep 3Keep Java UpdatedWARNING: Java is the #1 exploited program at this time. The
Department of Homeland Security recommends that computer users disable
Java.
See
this articleI would recommend that you completely uninstall
Java unless you need it to run an important software.
In that instance I would recommend that you disable Java in your browsers until you need it for that software and then enable it. (See
How to disable Java in your web browser and
How to unplug Java from the browser).
If you do need to keep Java then download
JavaRa.
Run the program and select
Remove Java Runtime. Uninstall all versions of Java present.
Once done then run it again and select
Update Java runtime > Download and install Latest version.
 Step 4Web Browser security
Step 4Web Browser securityMost malware is exploiting
Internet Explorer's vulnerabilities, with
Firefox you will be more secure.
Note: If you are going to use
Firefox, I would suggest the use of these add-ons:
- NoScript - for blocking ads and other potential website attacks.
- McAfee SiteAdvisor - this tells you whether the sites you are about to visit are safe or not. A must if you do a lot of Googling.
Step 5Other Program updatesYou should get the latest versions of Adobe software and keep them updated. Best of all, they are FREE.
NOTE: Make sure to uncheck the check box labelled "Yes, install McAfee Security Scan Plus - optional", or any other optional "features".Step 6Anti Virus ProgramsOn to personal Anti Virus programs. One AV is a must have, but
never more than one, as this can and will cause conflicts, system slow-downs, and false readings.
If you wish to keep using your current program, always make sure it is up to date and enabled.
- OR -
These FREE ones are as good as any paid subscription AV, as long as you allow them to update themselves:
Step 7Anti SpywareYou already have an excellent preventative program that will help to keep the nasties away -
Malwarebytes Anti-Malware. I would advise running this at least once a month. If you need to download it again, you can get it from here:
Malwarebytes Anti-MalwareStep 8Personal FirewallsNext let's look at
Firewalls. These help to prevent unauthorized access both to and from the internet or your local network. A firewall is considered a first line of defense in protecting private information. Below are two free firewalls to choose from, if you do not already have one.
Note: You only want to use one firewall your system.
You can use your built-in
Windows Vista Firewall, OR use a third-party one, such as these:
Step 9Instant MessengersAlmost done! If you like to use chat,
MSN and
Yahoo have vulnerabilities that can leave you open to infections. There are however a couple of very good, malware-free Instant Messenger programs which allow you to connect to multiple IM services in one program! (AOL, Yahoo, ICQ, IRC, MSN):
Step 10File/System CleanersFinally, it is a good idea to clear out all your temp files every now and again. This will help keep your computer running optimally. It can detect registry errors, missing shortcuts, invalid files, etc. It also can assist in getting rid of files that may contain malicious code that could re-infect your computer.
Step 11CryptoLocker Warning CryptoLocker is a particularly nasty infection which is becoming more prevalent...
Go
here for information about CryptoLocker Ransomware. Learning about what is out there may help you prevent infection. The best protection against this infection is to backup your files often. If you're using an external drive, keep it unplugged from the computer when you're not backing up files or using it. This will prevent the infection from getting to your backed up files if you ever have the frustrating experience of contracting it.
It is suggested to Download
CryptoPrevent, which is free for home use. It will help prevent CryptoLocker infection.
Further ReadingTo find out more information about how you got infected in the first place and some great guidelines to follow to prevent future infections you can read
this excellent article, originally written by Tony Klein, and updated by SpySentinel.
I will keep this log open for the next couple of days, so if you have any further problems, you can post another reply here.
OK, happy computing, and stay safe!

Please reply again to this thread to acknowledge you have read my last post. If you have no further questions, this thread will be closed to prevent others from posting here.
Thanks!
![]()
![]()

 This topic is locked
This topic is locked














 Sign In
Sign In Create Account
Create Account

