What is Groover?
The Malwarebytes research team has determined that Groover is a browser hijacker. These so-called "hijackers" manipulate your browser(s), for example to change your startpage or searchscopes, so that the affected browser visits their site or one of their choice. This one also displays advertisements.
How do I know if my computer is affected by Groover?
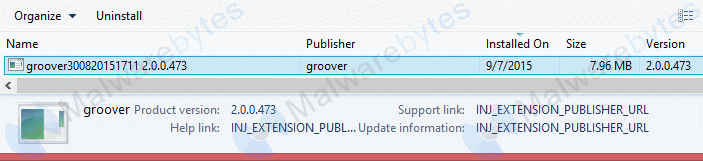
You may see this entry in your list of installed software:
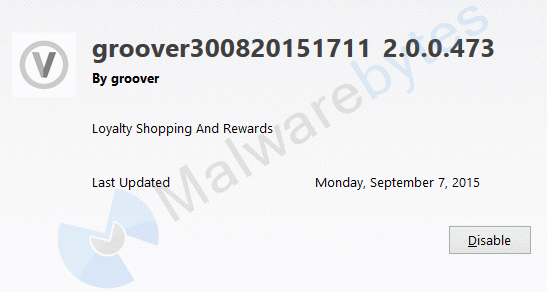
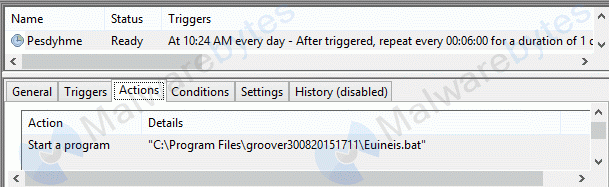
these browser add-ons:
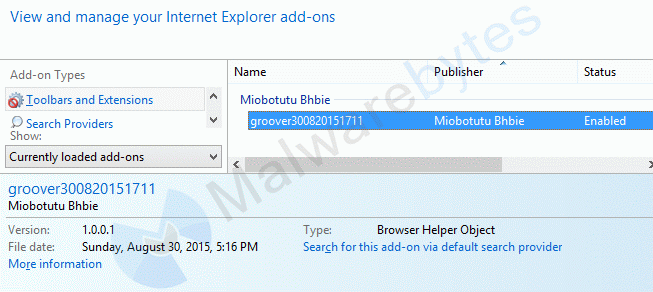
this Scheduled Task:
and this type of advertisements:

How did Groover get on my computer?
Browser hijackers use different methods for distributing themselves. This particular one was bundled with other software.
How do I remove Groover?
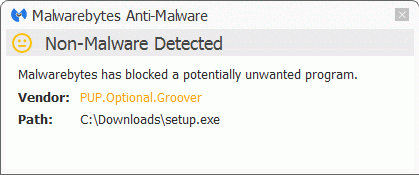
Our program Malwarebytes Anti-Malware can detect and remove this potentially unwanted program.
- Please download Malwarebytes Anti-Malware to your desktop.
- Double-click mbam-setup-version.exe and follow the prompts to install the program.
- At the end, be sure a check-mark is placed next to the following:
- Enable free trial of Malwarebytes Anti-Malware Premium
- Launch Malwarebytes Anti-Malware
- Then click Finish.
- If an update is found, you will be prompted to download and install the latest version.
- Once the program has loaded, select Scan Now. Or select the Threat Scan from the Scan menu.
- When the scan is complete, make sure that all Threats are selected, and click Remove Selected.
- Restart your computer when prompted to do so.
- You may be prompted twice to reboot after removal. Malwarebytes Anti-Malware needs to restore your connection after removing this LSP-hijacker.
- Please also run Windows System File Checker to undo some of the changes done by this PUP.
- This PUP creates some scheduled tasks. You can read here how to check for and, if necessary, remove Scheduled Tasks.
How would the full version of Malwarebytes Anti-Malware help protect me?
We hope our application and this guide have helped you eradicate this hijacker.
As you can see below the full version of Malwarebytes Anti-Malware would have protected you against the Groover hijacker. It would have warned you before the application could install itself, giving you a chance to stop it before it became too late.
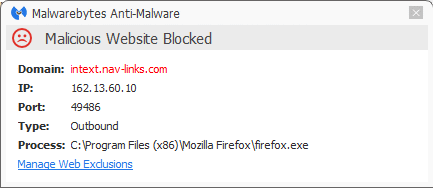
And it will block a lot of the advertisements:
Technical details for experts
Signs in a HijackThis log:
O2 - BHO: groover300820151711 Helper - {36D83219-421C-436D-87A7-0682A3781DE1} - C:\Program Files\groover300820151711\Colmugt.dll
O4 - HKLM\..\RunOnce: [cmdrun] cmd.exe /C ipconfig /flushdns
O10 - Unknown file in Winsock LSP: c:\windows\system32\zoegceato.dll
O10 - Unknown file in Winsock LSP: c:\windows\system32\zoegceato.dll
O10 - Unknown file in Winsock LSP: c:\windows\system32\zoegceato.dll
O10 - Unknown file in Winsock LSP: c:\windows\system32\zoegceato.dll
O10 - Unknown file in Winsock LSP: c:\windows\system32\zoegceato.dll
O23 - Service: 21C49BB6-7CDB-478F-8D05-44C6F236D73A - Unknown owner - C:\Program Files\groover300820151711\Gujrijo.exe
O23 - Service: CectuCibi - Unknown owner - C:\Program Files\groover300820151711\HarsyUoufyf.exe
O23 - Service: csrcc - Unknown owner - C:\Program Files\groover300820151711\csrcc.exe
O23 - Service: groover300820151711 Updater - Unknown owner - C:\Program Files\groover300820151711\Zhyyoqam.exe
O23 - Service: Zoegceato - Unknown owner - C:\Program Files\groover300820151711\Zoegceato.exe
Possible signs in FRST logs: () C:\Program Files\groover300820151711\csrcc.exe
() C:\Program Files\groover300820151711\Gujrijo.exe
() C:\Program Files\groover300820151711\Zhyyoqam.exe
() C:\Program Files\groover300820151711\Lotbi.exe
() C:\Program Files\groover300820151711\Lotbi64.exe
() C:\Program Files\groover300820151711\Zoegceato.EXE
() C:\Program Files\groover300820151711\HarsyUoufyf.exe
HKLM\...\Run: [groover300820151711] => C:\Program Files\groover300820151711\Lotbi.exe [428712 2015-08-30] ()
HKLM\...\Run: [groover30082015171164] => C:\Program Files\groover300820151711\Lotbi64.exe [459944 2015-08-30] ()
HKLM-x32\...\RunOnce: [cmdrun] => cmd.exe /C ipconfig /flushdns
Winsock: Catalog9 01 C:\Windows\SysWOW64\Zoegceato.dll [283472 2015-09-07] ()
Winsock: Catalog9 02 C:\Windows\SysWOW64\Zoegceato.dll [283472 2015-09-07] ()
Winsock: Catalog9 03 C:\Windows\SysWOW64\Zoegceato.dll [283472 2015-09-07] ()
Winsock: Catalog9 04 C:\Windows\SysWOW64\Zoegceato.dll [283472 2015-09-07] ()
Winsock: Catalog9 16 C:\Windows\SysWOW64\Zoegceato.dll [283472 2015-09-07] ()
Winsock: Catalog9-x64 01 C:\Windows\system32\Zoegceato64.dll [353616 2015-09-07] ()
Winsock: Catalog9-x64 02 C:\Windows\system32\Zoegceato64.dll [353616 2015-09-07] ()
Winsock: Catalog9-x64 03 C:\Windows\system32\Zoegceato64.dll [353616 2015-09-07] ()
Winsock: Catalog9-x64 04 C:\Windows\system32\Zoegceato64.dll [353616 2015-09-07] ()
Winsock: Catalog9-x64 16 C:\Windows\system32\Zoegceato64.dll [353616 2015-09-07] ()
BHO: groover300820151711 -> {36D83219-421C-436D-87A7-0682A3781DE1} -> C:\Program Files\groover300820151711\Colmugt64.dll [2015-08-30] ()
BHO-x32: groover300820151711 -> {36D83219-421C-436D-87A7-0682A3781DE1} -> C:\Program Files\groover300820151711\Colmugt.dll [2015-08-30] ()
FF HKLM\...\Firefox\Extensions: [{36D83219-421C-436D-87A7-0682A3781DE1}] - C:\Program Files\groover300820151711\Firefox
FF Extension: groover300820151711 - C:\Program Files\groover300820151711\Firefox [2015-09-07]
FF HKLM-x32\...\Firefox\Extensions: [{36D83219-421C-436D-87A7-0682A3781DE1}] - C:\Program Files\groover300820151711\Firefox
R3 21C49BB6-7CDB-478F-8D05-44C6F236D73A; C:\Program Files\groover300820151711\Gujrijo.exe [280744 2015-08-30] ()
R2 CectuCibi; C:\Program Files\groover300820151711\HarsyUoufyf.exe [171856 2015-08-30] ()
R3 csrcc; C:\Program Files\groover300820151711\csrcc.exe [1444008 2015-08-30] ()
R2 groover300820151711 Updater; C:\Program Files\groover300820151711\Zhyyoqam.exe [170664 2015-08-30] ()
R3 Zoegceato; C:\Program Files\groover300820151711\Zoegceato.exe [2044240 2015-08-30] ()
R1 cherimoya; C:\Windows\System32\drivers\cherimoya.sys [56736 2015-08-20] (Windows (R) Win 7 DDK provider)
C:\Program Files\groover300820151711
C:\Windows\SysWOW64\Zoegceato.ini
C:\Windows\System32\Tasks\Pesdyhme
C:\Windows\SysWOW64\ZoegceatoOff.ini
C:\Windows\system32\ZoegceatoOff.ini
C:\Windows\system32\abis
C:\Windows\system32\Zoegceato64.dll
C:\Windows\SysWOW64\Zoegceato.dll
(Windows (R) Win 7 DDK provider) C:\Windows\system32\Drivers\cherimoya.sys
C:\Users\{username}\AppData\Local\Temp\oprun2139.exe
C:\Users\{username}\AppData\Local\Temp\oprun25420.exe
groover300820151711 2.0.0.473 (HKLM\...\{36D83219-421C-436D-87A7-0682A3781DE1}_is1) (Version: 2.0.0.473 - groover)
Task: {44C1F6D0-FBC8-4285-882E-700FFFB2151E} - System32\Tasks\Pesdyhme => C:\Program Files\groover300820151711\Euineis.bat [2015-08-30] ()Malwarebytes Anti-Malware log:Malwarebytes Anti-Malware
www.malwarebytes.org
Scan Date: 9/7/2015
Scan Time: 10:42 AM
Logfile: mbamGroover.txt
Administrator: Yes
Version: 2.1.8.1057
Malware Database: v2015.09.07.01
Rootkit Database: v2015.08.16.01
License: Premium
Malware Protection: Disabled
Malicious Website Protection: Enabled
Self-protection: Disabled
OS: Windows 8.1
CPU: x64
File System: NTFS
User: {username}
Scan Type: Threat Scan
Result: Completed
Objects Scanned: 349172
Time Elapsed: 31 min, 26 sec
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Enabled
Heuristics: Enabled
PUP: Enabled
PUM: Enabled
Processes: 8
PUP.Optional.Perion, C:\Program Files\groover300820151711\csrcc.exe, 2144, Delete-on-Reboot, [709d939a44478aac0561b2013cc548b8]
PUP.Optional.Perion, C:\Program Files\groover300820151711\Gujrijo.exe, 5044, Delete-on-Reboot, [15f882ab0289ac8a9ad103b00cf5817f]
PUP.Optional.Perion, C:\Program Files\groover300820151711\Lotbi.exe, 888, Delete-on-Reboot, [b15ccf5e692247efaac0743fb44d3fc1]
PUP.Optional.Perion, C:\Program Files\groover300820151711\Lotbi64.exe, 980, Delete-on-Reboot, [9e6f06275536d0661c11745ae8193bc5]
Adware.Agent, C:\Program Files\groover300820151711\Zoegceato.EXE, 800, Delete-on-Reboot, [ef1ee24b2269aa8c6824ab088879ba46]
PUP.Optional.Komodia, C:\Program Files\groover300820151711\HarsyUoufyf.exe, 3460, Delete-on-Reboot, [e12ce04da7e4da5c5d2c426c70918779]
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Zhyyoqam.exe, 3308, Delete-on-Reboot, [c14c101d4843979fd119ed89699b916f]
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Zoegceato.EXE, 800, Delete-on-Reboot, [b855022bdbb0be7819d16c0ac143847c]
Modules: 13
PUP.Optional.Perion, C:\Program Files\groover300820151711\Misnhl.dll, Delete-on-Reboot, [c14caa8391fa1521f1a2377cf50c29d7],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Misnhl.dll, Delete-on-Reboot, [c14caa8391fa1521f1a2377cf50c29d7],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Misnhl.dll, Delete-on-Reboot, [c14caa8391fa1521f1a2377cf50c29d7],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Teweg.dll, Delete-on-Reboot, [ca43ec417f0ce254e781e5cebc4530d0],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Ukoslu.dll, Delete-on-Reboot, [0c016bc26e1da393204742719968738d],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Bodtykra.dll, Delete-on-Reboot, [cc4140edddaedf57048dd4df21e0c33d],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\freebl3.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\libnspr4.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\libplc4.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\libplds4.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\nss3.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\nssutil3.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\smime3.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
Registry Keys: 118
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\TYPELIB\{14EF423E-3EE8-44AE-9337-07AC3F27B744}, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\INTERFACE\{A9582D7B-F24A-441D-9D26-450D58F3CD17}, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\INTERFACE\{EE0D8859-2ED4-4B0D-9812-16865B9AFD65}, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{A9582D7B-F24A-441D-9D26-450D58F3CD17}, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{EE0D8859-2ED4-4B0D-9812-16865B9AFD65}, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{A9582D7B-F24A-441D-9D26-450D58F3CD17}, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{EE0D8859-2ED4-4B0D-9812-16865B9AFD65}, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\TYPELIB\{14EF423E-3EE8-44AE-9337-07AC3F27B744}, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\TYPELIB\{14EF423E-3EE8-44AE-9337-07AC3F27B744}, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\csrcc, Quarantined, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\TYPELIB\{13B77022-DB7B-4112-9B33-FA1F3F6D04B5}, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\INTERFACE\{545A0A06-3DA4-41E1-BD2B-6F3604DD762B}, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\INTERFACE\{61FE27E6-82A6-402E-BEC9-7DC46B9D139A}, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{545A0A06-3DA4-41E1-BD2B-6F3604DD762B}, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{61FE27E6-82A6-402E-BEC9-7DC46B9D139A}, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{545A0A06-3DA4-41E1-BD2B-6F3604DD762B}, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{61FE27E6-82A6-402E-BEC9-7DC46B9D139A}, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\TYPELIB\{13B77022-DB7B-4112-9B33-FA1F3F6D04B5}, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\TYPELIB\{13B77022-DB7B-4112-9B33-FA1F3F6D04B5}, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\21C49BB6-7CDB-478F-8D05-44C6F236D73A, Quarantined, [15f882ab0289ac8a9ad103b00cf5817f],
Adware.Agent, HKLM\SOFTWARE\CLASSES\TYPELIB\{C1AF885F-E1A4-477A-B7D1-3B91F948EB3C}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\INTERFACE\{06AFC378-3A58-440F-89B7-BC8E1D542811}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\INTERFACE\{2CCF9955-CAB4-45AA-8CBA-0DA051870EA2}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\INTERFACE\{312C28A0-E1F7-4408-8454-BE10A2580856}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\INTERFACE\{34EB02C9-D7BD-4347-A370-53844307E000}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\INTERFACE\{49027476-6383-4815-8EA9-E9FFC6B54A03}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\INTERFACE\{FCE19D66-6135-49C8-8D72-A8AE495BDA15}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{06AFC378-3A58-440F-89B7-BC8E1D542811}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{2CCF9955-CAB4-45AA-8CBA-0DA051870EA2}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{312C28A0-E1F7-4408-8454-BE10A2580856}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{34EB02C9-D7BD-4347-A370-53844307E000}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{49027476-6383-4815-8EA9-E9FFC6B54A03}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{FCE19D66-6135-49C8-8D72-A8AE495BDA15}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{06AFC378-3A58-440F-89B7-BC8E1D542811}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{2CCF9955-CAB4-45AA-8CBA-0DA051870EA2}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{312C28A0-E1F7-4408-8454-BE10A2580856}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{34EB02C9-D7BD-4347-A370-53844307E000}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{49027476-6383-4815-8EA9-E9FFC6B54A03}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{FCE19D66-6135-49C8-8D72-A8AE495BDA15}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\WOW6432NODE\CLASSES\TYPELIB\{C1AF885F-E1A4-477A-B7D1-3B91F948EB3C}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SOFTWARE\CLASSES\WOW6432NODE\TYPELIB\{C1AF885F-E1A4-477A-B7D1-3B91F948EB3C}, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
Adware.Agent, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\Zoegceato, Quarantined, [ef1ee24b2269aa8c6824ab088879ba46],
PUP.Optional.Komodia, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\CectuCibi, Quarantined, [e12ce04da7e4da5c5d2c426c70918779],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\CLSID\{36D83219-421C-436D-87A7-0682A3781DE1}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\CLSID\{36D83219-421C-436D-87A7-0682A3781DE1}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\TYPELIB\{9AE7A6AE-162E-44c4-9A2B-A6B4EF19909D}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\INTERFACE\{E4C3E50F-5761-4BF8-95A0-939A819DF1C3}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{E4C3E50F-5761-4BF8-95A0-939A819DF1C3}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{E4C3E50F-5761-4BF8-95A0-939A819DF1C3}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\TYPELIB\{9AE7A6AE-162E-44c4-9A2B-A6B4EF19909D}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\TYPELIB\{9AE7A6AE-162E-44c4-9A2B-A6B4EF19909D}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\Extension.Maqyjam.1, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\Extension.Maqyjam, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\Extension.Maqyjam, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\Extension.Maqyjam, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\BROWSER HELPER OBJECTS\{36D83219-421C-436D-87A7-0682A3781DE1}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\EXPLORER\BROWSER HELPER OBJECTS\{36D83219-421C-436D-87A7-0682A3781DE1}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\CLASSES\Extension.Maqyjam.1, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\Extension.Maqyjam.1, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\WOW6432NODE\CLSID\{36D83219-421C-436D-87A7-0682A3781DE1}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKCU\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXT\SETTINGS\{36D83219-421C-436D-87A7-0682A3781DE1}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKCU\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\EXT\STATS\{36D83219-421C-436D-87A7-0682A3781DE1}, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, HKLM\SOFTWARE\CLASSES\CLSID\{36D83219-421C-436D-87A7-0682A3781DE1}\INPROCSERVER32, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\groover300820151711, Quarantined, [987545e88cff83b3598ce294679dfa06],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.EgoaZelminus, Quarantined, [fe0fe746c1cab383bf2d7f447094aa56],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.EgoaZelminus.1, Quarantined, [48c550dd2368280e9953a51ed13344bc],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.EnaiAsijge, Quarantined, [fa131914d5b668ce727aa12218ecab55],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.EnaiAsijge.1, Quarantined, [e9245ad3a1ead363cb21982b7b89e21e],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.GyaKadsiti, Quarantined, [7b92c26b1f6cd561b23a9b28aa5a2dd3],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.GyaKadsiti.1, Quarantined, [a26baa83f398ae884aa2b211ec18d927],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.LetmViwbagnido, Quarantined, [b954c36aa8e36fc77c70a91a41c3cc34],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.LetmViwbagnido.1, Quarantined, [48c56bc2aedd6fc7da127d46bc48d030],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.UpirHatbijh, Quarantined, [2be2111cec9f84b20ae29d268d773cc4],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\ZoegceatoLib.UpirHatbijh.1, Quarantined, [3bd295983457aa8cdd0f9a29a95b31cf],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\APPID\Zoegceato.EXE, Quarantined, [8a83f835a9e2f34334b7438094707789],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\WOW6432NODE\APPID\Zoegceato.EXE, Quarantined, [18f5230a94f758de8b60725122e2d12f],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\Pesdyhme, Delete-on-Reboot, [b459f23bd7b468ce737a0cb7699b9c64],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\groover300820151711, Quarantined, [a46974b9e6a5d16528bde59160a49b65],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.EgoaZelminus, Quarantined, [b657ec410c7f1323b8347a4957adf010],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.EgoaZelminus.1, Quarantined, [16f7d7562c5fcd698369a51ed92beb15],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.EnaiAsijge, Quarantined, [ac610e1f06858caaeb01992a20e41ae6],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.EnaiAsijge.1, Quarantined, [62abc469f19a013568847a49db29f50b],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.GyaKadsiti, Quarantined, [b15c8aa30883eb4bdf0dd6eda361b050],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.GyaKadsiti.1, Quarantined, [33da69c436556dc94ba1d4efd33157a9],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.LetmViwbagnido, Quarantined, [a06d2c016a21a49299539c2726de0af6],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.LetmViwbagnido.1, Quarantined, [60ad70bd711aa98d3fad299a689ce917],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.UpirHatbijh, Quarantined, [db32d954cfbc2610f4f8f8cbc2429e62],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\ZoegceatoLib.UpirHatbijh.1, Quarantined, [d03dd558fa9190a6f4f8dde6d33139c7],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\APPID\Zoegceato.EXE, Quarantined, [2ae3b875f3980c2a8962fbc8ba4adc24],
Rootkit.cherimoya.A, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\cherimoya, Quarantined, [af5e46e786059f9705029f8b966deb15],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\GROOVER300820151711 UPDATER, Quarantined, [c14c101d4843979fd119ed89699b916f],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\ZOEGCEATO, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\TYPELIB\{C1AF885F-E1A4-477A-B7D1-3B91F948EB3C}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\INTERFACE\{06AFC378-3A58-440F-89B7-BC8E1D542811}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\INTERFACE\{2CCF9955-CAB4-45AA-8CBA-0DA051870EA2}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\INTERFACE\{312C28A0-E1F7-4408-8454-BE10A2580856}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\INTERFACE\{34EB02C9-D7BD-4347-A370-53844307E000}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\INTERFACE\{49027476-6383-4815-8EA9-E9FFC6B54A03}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\INTERFACE\{FCE19D66-6135-49C8-8D72-A8AE495BDA15}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{06AFC378-3A58-440F-89B7-BC8E1D542811}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{2CCF9955-CAB4-45AA-8CBA-0DA051870EA2}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{312C28A0-E1F7-4408-8454-BE10A2580856}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{34EB02C9-D7BD-4347-A370-53844307E000}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{49027476-6383-4815-8EA9-E9FFC6B54A03}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\INTERFACE\{FCE19D66-6135-49C8-8D72-A8AE495BDA15}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{06AFC378-3A58-440F-89B7-BC8E1D542811}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{2CCF9955-CAB4-45AA-8CBA-0DA051870EA2}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{312C28A0-E1F7-4408-8454-BE10A2580856}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{34EB02C9-D7BD-4347-A370-53844307E000}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{49027476-6383-4815-8EA9-E9FFC6B54A03}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\WOW6432NODE\INTERFACE\{FCE19D66-6135-49C8-8D72-A8AE495BDA15}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\CLASSES\TYPELIB\{C1AF885F-E1A4-477A-B7D1-3B91F948EB3C}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\CLASSES\WOW6432NODE\TYPELIB\{C1AF885F-E1A4-477A-B7D1-3B91F948EB3C}, Quarantined, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, HKU\S-1-5-18\SOFTWARE\{78427AE8-76E6-4C75-8C84-CB84491D626C}, Quarantined, [1bf2121b1477bd79984b2b4b9470da26],
PUP.Optional.Groover.BrwsrFlsh, HKU\S-1-5-19\SOFTWARE\{78427AE8-76E6-4C75-8C84-CB84491D626C}, Quarantined, [9e6fa68736556acc05de0274689c7e82],
PUP.Optional.Groover.BrwsrFlsh, HKU\S-1-5-20\SOFTWARE\{78427AE8-76E6-4C75-8C84-CB84491D626C}, Quarantined, [2be239f4355669cd598af5816e9649b7],
PUP.Optional.Groover.BrwsrFlsh, HKCU\SOFTWARE\{78427AE8-76E6-4C75-8C84-CB84491D626C}, Quarantined, [b35add50692203330dd676001aea2fd1],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\{36D83219-421C-436D-87A7-0682A3781DE1}_is1, Quarantined, [10fd61cc8407132339a99860f210a858],
Registry Values: 15
PUP.Optional.Perion, HKLM\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN|groover300820151711, C:\Program Files\groover300820151711\Lotbi.exe, Quarantined, [b15ccf5e692247efaac0743fb44d3fc1]
PUP.Optional.Perion, HKLM\SOFTWARE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN|groover30082015171164, C:\Program Files\groover300820151711\Lotbi64.exe, Quarantined, [9e6f06275536d0661c11745ae8193bc5]
PUP.Optional.Perion, HKLM\SOFTWARE\MOZILLA\FIREFOX\EXTENSIONS|{36D83219-421C-436D-87A7-0682A3781DE1}, C:\Program Files\groover300820151711\Firefox, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22]
PUP.Optional.Perion, HKLM\SOFTWARE\WOW6432NODE\MOZILLA\FIREFOX\EXTENSIONS|{36D83219-421C-436D-87A7-0682A3781DE1}, C:\Program Files\groover300820151711\Firefox, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22]
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\MOZILLA\FIREFOX\EXTENSIONS\{36D83219-421C-436D-87A7-0682A3781DE1}, Quarantined, [ee1f1d1074172d09b5b934ad38ca18e8],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SOFTWARE\WOW6432NODE\MOZILLA\FIREFOX\EXTENSIONS\{36D83219-421C-436D-87A7-0682A3781DE1}, Quarantined, [8588b7766c1fbc7ad99541a0e2209a66],
PUP.Optional.Groover.BrwsrFlsh, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\21C49BB6-7CDB-478F-8D05-44C6F236D73A|ImagePath, "C:\Program Files\groover300820151711\Gujrijo.exe", Quarantined, [22eb111ce3a8c670826890e6fa0aa55b]
PUP.Optional.Groover.BrwsrFlsh, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\CectuCibi|ImagePath, "C:\Program Files\groover300820151711\HarsyUoufyf.exe" -cmd, Quarantined, [50bd1c111477f640bb2f5d1980849868]
PUP.Optional.Groover.BrwsrFlsh, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\csrcc|ImagePath, "C:\Program Files\groover300820151711\csrcc.exe", Quarantined, [85888ba27c0fce68dc0ebabc18ec9a66]
PUP.Optional.Groover.BrwsrFlsh, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\groover300820151711 Updater|ImagePath, C:\Program Files\groover300820151711\Zhyyoqam.exe, Quarantined, [c14c101d4843979fd119ed89699b916f]
PUP.Optional.Groover.BrwsrFlsh, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\Zoegceato|ImagePath, C:\Program Files\groover300820151711\Zoegceato.exe, Quarantined, [b855022bdbb0be7819d16c0ac143847c]
PUP.Optional.Groover.BrwsrFlsh, HKU\S-1-5-18\SOFTWARE\{78427AE8-76E6-4C75-8C84-CB84491D626C}|Name, C:\Program Files\groover300820151711\Lotbi.exe, Quarantined, [1bf2121b1477bd79984b2b4b9470da26]
PUP.Optional.Groover.BrwsrFlsh, HKU\S-1-5-19\SOFTWARE\{78427AE8-76E6-4C75-8C84-CB84491D626C}|Name, C:\Program Files\groover300820151711\Lotbi.exe, Quarantined, [9e6fa68736556acc05de0274689c7e82]
PUP.Optional.Groover.BrwsrFlsh, HKU\S-1-5-20\SOFTWARE\{78427AE8-76E6-4C75-8C84-CB84491D626C}|Name, C:\Program Files\groover300820151711\Lotbi.exe, Quarantined, [2be239f4355669cd598af5816e9649b7]
PUP.Optional.Groover.BrwsrFlsh, HKCU\SOFTWARE\{78427AE8-76E6-4C75-8C84-CB84491D626C}|Name, C:\Program Files\groover300820151711\Lotbi.exe, Quarantined, [b35add50692203330dd676001aea2fd1]
Registry Data: 0
(No malicious items detected)
Folders: 13
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\content, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\content\libraries, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\content\resources, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\locale, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\locale\en-US, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\skin, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\defaults, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\defaults\preferences, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\libraries, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\resources, Quarantined, [10fd61cc8407132339a99860f210a858],
Files: 78
Rootkit.Agent.A, C:\WINDOWS\SYSTEM32\drivers\bsdriver.sys, Delete-on-Reboot, [4920a82f041ec05d87daf729e134aca4],
PUP.Optional.Shopperz.BrwsrFlsh, C:\WINDOWS\SYSTEM32\drivers\cherimoya.sys, Delete-on-Reboot, [6fecea2b9d3fab8e75b84eb9169273a2],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Misnhl.dll, Delete-on-Reboot, [c14caa8391fa1521f1a2377cf50c29d7],
PUP.Optional.Perion, C:\Program Files\groover300820151711\csrcc.exe, Delete-on-Reboot, [709d939a44478aac0561b2013cc548b8],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Gujrijo.exe, Delete-on-Reboot, [15f882ab0289ac8a9ad103b00cf5817f],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Lotbi.exe, Delete-on-Reboot, [b15ccf5e692247efaac0743fb44d3fc1],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Teweg.dll, Delete-on-Reboot, [ca43ec417f0ce254e781e5cebc4530d0],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Ukoslu.dll, Delete-on-Reboot, [0c016bc26e1da393204742719968738d],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Bodtykra.dll, Delete-on-Reboot, [cc4140edddaedf57048dd4df21e0c33d],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Lotbi64.exe, Delete-on-Reboot, [9e6f06275536d0661c11745ae8193bc5],
Adware.Agent, C:\Program Files\groover300820151711\Zoegceato.EXE, Delete-on-Reboot, [ef1ee24b2269aa8c6824ab088879ba46],
PUP.Optional.Komodia, C:\Program Files\groover300820151711\HarsyUoufyf.exe, Delete-on-Reboot, [e12ce04da7e4da5c5d2c426c70918779],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Colmugt64.dll, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Colmugt.dll, Quarantined, [63aa26074c3fd75f2d37b8fbbf42de22],
PUP.Optional.Groover, C:\Users\{username}\Desktop\setup.exe, Quarantined, [ee1fd35ad0bbb5815b7c7c5d4ab75fa1],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Bodtykra64.dll, Delete-on-Reboot, [0effb07d8a0165d12b67684b8e73d12f],
PUP.Optional.Perion, C:\Program Files\groover300820151711\dr_inst.exe, Quarantined, [9b72e14c414abd79117c6f4402ff649c],
PUP.Optional.Komodia, C:\Program Files\groover300820151711\eosowayhio.exe, Quarantined, [53bab07dc2c9f1451674703ea859926e],
PUP.Optional.Komodia, C:\Program Files\groover300820151711\eosowayhio64.exe, Quarantined, [d13c3bf2a4e76acc3b50ecc24fb29b65],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Misnhl64.dll, Delete-on-Reboot, [c8451e0f5f2c072f1381b8fb22df9b65],
PUP.Optional.Komodia, C:\Program Files\groover300820151711\rmvall.exe, Quarantined, [4ac3a588117a0f27a1e765494cb5b749],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Shbymqyl.dll, Quarantined, [709d72bb9dee9f971e4b793a758c0ff1],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Teweg64.dll, Delete-on-Reboot, [878669c4216af145355b21929d644db3],
PUP.Optional.Perion, C:\Program Files\groover300820151711\Ukoslu64.dll, Delete-on-Reboot, [16f7b479f19a5adcefa0288b34cde41c],
PUP.Optional.Perion, C:\Program Files\groover300820151711\wrapper.exe, Quarantined, [927b87a6f29969cdd0be11a228d938c8],
PUP.Optional.Winsock.HijackBoot, C:\Program Files\groover300820151711\Zoegceato.dll, Quarantined, [44c90c211f6c87aff795c0ee659c06fa],
PUP.Optional.Winsock.HijackBoot, C:\Program Files\groover300820151711\Zoegceato64.dll, Quarantined, [fe0f31fc97f4d3630885832b2ed3bb45],
PUP.Optional.Winsock.HijackBoot, C:\Windows\System32\Zoegceato64.dll, Delete-on-Reboot, [b9541419315aa88e8805991525dc5ba5],
PUP.Optional.Winsock.HijackBoot, C:\Windows\SysWOW64\Zoegceato.dll, Delete-on-Reboot, [b558cc612764ae88d9b36945c73ada26],
PUP.Optional.Komodia, C:\Users\{username}\AppData\Local\Temp\oprun2139.exe, Quarantined, [77969796f19a41f5bdcc0ba31de425db],
PUP.Optional.Perion, C:\Users\{username}\AppData\Local\Temp\is-N2KKE.tmp\Shbymqyl.dll, Quarantined, [a5685cd1acdfeb4b630660531ce5eb15],
Trojan.Agent, C:\Users\{username}\AppData\Local\Temp\oprun2139.exe, Quarantined, [aa63b875b4d79e981fe39dfc38cb53ad],
Trojan.Agent, C:\Users\{username}\AppData\Local\Temp\oprun25420.exe, Quarantined, [a26b2c01eba0b284be441b7e25ded42c],
PUP.Optional.PricePeep, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Storage\https_static.pricepeep00.pricepeep.net_0.localstorage, Quarantined, [de2f34f9dcaf41f521ecd1d65ca80af6],
PUP.Optional.PricePeep, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Storage\https_static.pricepeep00.pricepeep.net_0.localstorage-journal, Quarantined, [9d70939abbd0fa3c85884d5adf252dd3],
PUP.Optional.SelectNGo, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Storage\https_static.selectgo00.selectgo.net_0.localstorage, Quarantined, [8d8079b4d4b7e25494227c31fc080df3],
PUP.Optional.SelectNGo, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Storage\https_static.selectgo00.selectgo.net_0.localstorage-journal, Quarantined, [8d801b12c2c9152152640aa3a3611de3],
PUP.Optional.Groover.BrwsrFlsh, C:\Windows\System32\Tasks\Pesdyhme, Quarantined, [f01d7db0315ad95d28c109ba7d87916f],
PUP.Optional.Winsock.HijackBoot, C:\Windows\System32\ZoegceatoOff.ini, Quarantined, [e726e94475163df9749e7b49f4108f71],
PUP.Optional.Winsock.HijackBoot, C:\Windows\SysWOW64\Zoegceato.ini, Quarantined, [29e4c36a8ffc4de9070b51736a9a758b],
PUP.Optional.Winsock.HijackBoot, C:\Windows\SysWOW64\ZoegceatoOff.ini, Quarantined, [0a03d15ca5e686b0ee24b50f13f150b0],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Zhyyoqam.exe, Delete-on-Reboot, [c14c101d4843979fd119ed89699b916f],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Zoegceato.EXE, Delete-on-Reboot, [b855022bdbb0be7819d16c0ac143847c],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\brwbl.bin, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Euineis.bat, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\freebl3.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\gcpum.dll, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\libnspr4.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\libplc4.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\libplds4.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\nfregdrv64.exe, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\nss3.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\nssckbi.dll, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\nssdbm3.dll, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\nssutil3.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\prc.exe, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\prdt.bin, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\smime3.dll, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\softokn3.dll, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\sqlite3.dll, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\ssl3.dll, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\tree.js, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\unins000.dat, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\unins000.exe, Delete-on-Reboot, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome.manifest, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\icon.png, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\install.rdf, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\{36D83219-421C-436D-87A7-0682A3781DE1}.xpi, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\content\main.js, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\content\main.xul, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\content\libraries\DataExchangeScript.js, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\content\resources\LocalScript.js, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\locale\en-US\overlay.dtd, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\chrome\skin\overlay.css, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\Firefox\defaults\preferences\defaults.js, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\libraries\DataExchangeScript.js, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.Groover.BrwsrFlsh, C:\Program Files\groover300820151711\resources\LocalScript.js, Quarantined, [10fd61cc8407132339a99860f210a858],
PUP.Optional.HijackHosts.Gen, C:\Windows\System32\abis\cuuf\fah.dat, Quarantined, [a06d50dd4f3c0d29bd794d50aa5bc53b],
Physical Sectors: 0
(No malicious items detected)
(end)As mentioned before the full version of Malwarebytes Anti-Malware could have protected your computer against this threat.We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

