What is ActSys?
The Malwarebytes research team has determined that ActSys is adware. These adware applications display advertisements not originating from the sites you are browsing.
How do I know if my computer is affected by ActSys?
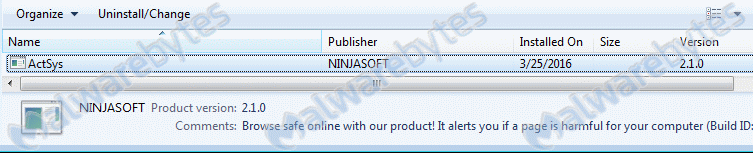
You may see this entry in your list of installed programs:
How did ActSys get on my computer?
Adware applications use different methods for distributing themselves. This particular one was bundled with other software.
How do I remove ActSys?
Our program Malwarebytes Anti-Malware can detect and remove this potentially unwanted program.
- Please download Malwarebytes Anti-Malware to your desktop.
- Double-click mbam-setup-version.exe and follow the prompts to install the program.
- At the end, be sure a check-mark is placed next to the following:
- Enable free trial of Malwarebytes Anti-Malware Premium
- Launch Malwarebytes Anti-Malware
- Then click Finish.
- If an update is found, you will be prompted to download and install the latest version.
- Once the program has loaded, select Scan now. Or select the Threat Scan from the Scan menu.
- When the scan is complete , make sure that everything is set to "Quarantine", and click Apply Actions.
- Reboot your computer if prompted.
- No, Malwarebytes' Anti-Malware removes ActSys completely.
We hope our application and this guide have helped you eradicate this adware.
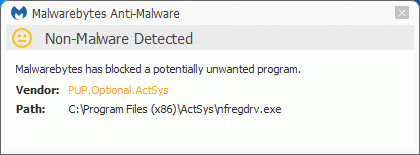
As you can see below the full version of Malwarebytes Anti-Malware would have protected you against the ActSys adware. It would have warned you before the rogue could install itself, giving you a chance to stop it before it became too late.
Technical details for experts
Possible signs in FRST logs:
() C:\Program Files (x86)\ActSys\ActSys.exe R2 ActSys; C:\Program Files (x86)\ActSys\ActSys.exe [452664 2016-02-24] () R1 asfilterdrv; C:\Windows\System32\drivers\asfilterdrv.sys [57656 2016-02-24] (Windows (R) Win 7 DDK provider) C:\Program Files (x86)\ActSys (Windows (R) Win 7 DDK provider) C:\Windows\system32\Drivers\asfilterdrv.sys ActSys (HKLM-x32\...\ActSys) (Version: 2.1.0 - NINJASOFT) () C:\Program Files (x86)\ActSys\ActSys.exe () C:\Program Files (x86)\ActSys\nfapi.dll () C:\Program Files (x86)\ActSys\ProtocolFilters.dllAlterations made by the installer:
File system details [View: All details] (Selection)
---------------------------------------------------
Adds the folder C:\Program Files (x86)\ActSys
Adds the file ActSys.exe"="2/24/2016 11:09 PM, 452664 bytes, A
Adds the file libeay32.dll"="2/24/2016 11:09 PM, 1499136 bytes, A
Adds the file nfapi.dll"="2/24/2016 11:09 PM, 126976 bytes, A
Adds the file nfregdrv.exe"="2/24/2016 11:09 PM, 49152 bytes, A
Adds the file ProtocolFilters.dll"="2/24/2016 11:09 PM, 1413120 bytes, A
Adds the file remove_ActSys.exe"="3/25/2016 8:14 AM, 34782 bytes, A
Adds the file ssleay32.dll"="2/24/2016 11:09 PM, 376832 bytes, A
In the existing folder C:\Windows\System32\drivers
Adds the file asfilterdrv.sys"="2/24/2016 11:10 PM, 57656 bytes, A
Registry details [View: All details] (Selection)
------------------------------------------------
[HKEY_LOCAL_MACHINE\SOFTWARE\ActSys]
"InstID"="REG_SZ", "AKeMrOsZjSuhzCnEkxfKdoKKZa3q3mn1"
"Version"="REG_SZ", "2.1.0"
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\ActSys]
"Comments"="REG_SZ", "Browse safe online with our product! It alerts you if a page is harmful for your computer (Build ID: tO8kyrdAFHApzvcfzVvji4NnQsP9)"
"DisplayName"="REG_SZ", "ActSys"
"DisplayVersion"="REG_SZ", "2.1.0"
"Publisher"="REG_SZ", "NINJASOFT"
"QuietUninstallString"="REG_SZ", ""C:\Program Files (x86)\ActSys\remove_ActSys.exe" /S"
"UninstallString"="REG_SZ", ""C:\Program Files (x86)\ActSys\remove_ActSys.exe" /S"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\ActSys]
"DisplayName"="REG_SZ", "ActSys"
"ErrorControl"="REG_DWORD", 1
"ImagePath"="REG_EXPAND_SZ, "C:\Program Files (x86)\ActSys\ActSys.exe"
"ObjectName"="REG_SZ", "LocalSystem"
"Start"="REG_DWORD", 2
"Type"="REG_DWORD", 16
"WOW64"="REG_DWORD", 1
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\asfilterdrv]
"DisplayName"="REG_SZ", "asfilterdrv"
"ErrorControl"="REG_DWORD", 1
"Group"="REG_SZ", "PNP_TDI"
"ImagePath"="REG_EXPAND_SZ, "system32\drivers\asfilterdrv.sys"
"Start"="REG_DWORD", 1
"Tag"="REG_DWORD", 11
"Type"="REG_DWORD", 1
"WOW64"="REG_DWORD", 1
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\asfilterdrv\Enum]
"0"="REG_SZ", "Root\LEGACY_ASFILTERDRV\0000"
"Count"="REG_DWORD", 1
"NextInstance"="REG_DWORD", 1
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings]
"ProxyEnable"="REG_DWORD", 0
Malwarebytes Anti-Malware log:Malwarebytes Anti-Malware
www.malwarebytes.org
Scan Date: 3/25/2016
Scan Time: 8:41 AM
Logfile: mbamActSys.txt
Administrator: Yes
Version: 2.2.1.1043
Malware Database: v2016.03.25.01
Rootkit Database: v2016.03.12.01
License: Premium
Malware Protection: Disabled
Malicious Website Protection: Enabled
Self-protection: Enabled
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: {username}
Scan Type: Threat Scan
Result: Completed
Objects Scanned: 372382
Time Elapsed: 10 min, 7 sec
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Enabled
Heuristics: Enabled
PUP: Enabled
PUM: Enabled
Processes: 2
Adware.BrAppWare, C:\Program Files (x86)\ActSys\ActSys.exe, 3516, Delete-on-Reboot, [46af0f7cbadfd561f44b0be241c03ec2]
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\ActSys.exe, 3516, Delete-on-Reboot, [25d03259cccdef475c2ab244ad561de3]
Modules: 2
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\nfapi.dll, Delete-on-Reboot, [b73e6823c0d94ee86cb10bf63cc823dd],
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\ProtocolFilters.dll, Delete-on-Reboot, [b73e6823c0d94ee86cb10bf63cc823dd],
Registry Keys: 5
Adware.BrAppWare, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\ActSys, Quarantined, [46af0f7cbadfd561f44b0be241c03ec2],
PUP.Optional.ActSys, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\ActSys, Quarantined, [25d03259cccdef475c2ab244ad561de3],
PUP.Optional.ActSys, HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\ActSys, Quarantined, [b73e6823c0d94ee86cb10bf63cc823dd],
PUP.Optional.ASFilter, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\asfilterdrv, Quarantined, [4ea76229eeab1026ee517192659fc53b],
PUP.Optional.BrAdware, HKLM\SOFTWARE\ACTSYS, Quarantined, [28cd1a71d9c0b97d655a8e00d43048b8],
Registry Values: 2
PUP.Optional.BrAdware, HKLM\SOFTWARE\ACTSYS|InstID, AKeMrOsZjSuhzCnEkxfKdoKKZa3q3mn1, Quarantined, [28cd1a71d9c0b97d655a8e00d43048b8]
PUP.Optional.BrAdware, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\ACTSYS|ImagePath, C:\Program Files (x86)\ActSys\ActSys.exe, Quarantined, [62930f7ccfca1620566a06883bc936ca]
Registry Data: 0
(No malicious items detected)
Folders: 4
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys, Delete-on-Reboot, [b73e6823c0d94ee86cb10bf63cc823dd],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\nss, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
Files: 20
PUP.Optional.ASFilter, C:\Windows\System32\drivers\asfilterdrv.sys, Delete-on-Reboot, [3ba8b7859ad35cdbb9049d1261801928],
Adware.BrAppWare, C:\Program Files (x86)\ActSys\ActSys.exe, Delete-on-Reboot, [46af0f7cbadfd561f44b0be241c03ec2],
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\ActSys.exe, Delete-on-Reboot, [25d03259cccdef475c2ab244ad561de3],
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\nfregdrv.exe, Quarantined, [b73e6823c0d94ee86cb10bf63cc823dd],
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\libeay32.dll, Quarantined, [b73e6823c0d94ee86cb10bf63cc823dd],
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\nfapi.dll, Delete-on-Reboot, [b73e6823c0d94ee86cb10bf63cc823dd],
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\ProtocolFilters.dll, Delete-on-Reboot, [b73e6823c0d94ee86cb10bf63cc823dd],
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\remove_ActSys.exe, Quarantined, [b73e6823c0d94ee86cb10bf63cc823dd],
PUP.Optional.ActSys, C:\Program Files (x86)\ActSys\ssleay32.dll, Quarantined, [b73e6823c0d94ee86cb10bf63cc823dd],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\actssl.cer, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\import.bat, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\import_root_cert.exe, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\nss\certutil.exe, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\nss\mozcrt19.dll, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\nss\nspr4.dll, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\nss\nss3.dll, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\nss\plc4.dll, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\nss\plds4.dll, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\nss\smime3.dll, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
PUP.Optional.BrAdware, C:\Users\{username}\AppData\Local\Temp\ActSys\SSL\nss\softokn3.dll, Quarantined, [668f1d6e3e5b1f1713abd4ba749058a8],
Physical Sectors: 0
(No malicious items detected)
(end)As mentioned before the full version of Malwarebytes Anti-Malware could have protected your computer against this threat.We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

