What is WindowsActivationError?
The Malwarebytes research team has determined that WindowsActivationError is a Tech Support Scam. These so-called "Tech Support Scammers" try to trick you into calling their phone number for various reasons, all of which turn out to be fraudulent in the end.
For more information on this particular type of Windows Shell hijackers please read this blogpost.
How do I know if my computer is affected by WindowsActivationError?
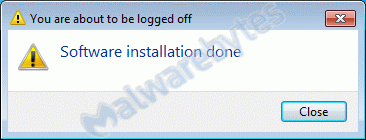
You may see this warning during install:
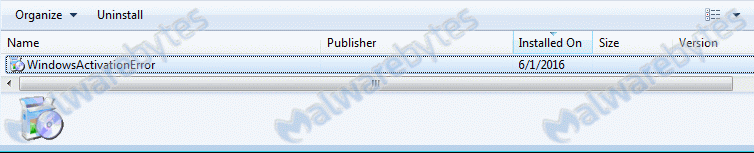
and this entry in your list of installed programs:
How did WindowsActivationError get on my computer?
Tech Support Scammers use different methods to get users to contact them. This on uses the Winlogon-Shell registry value.
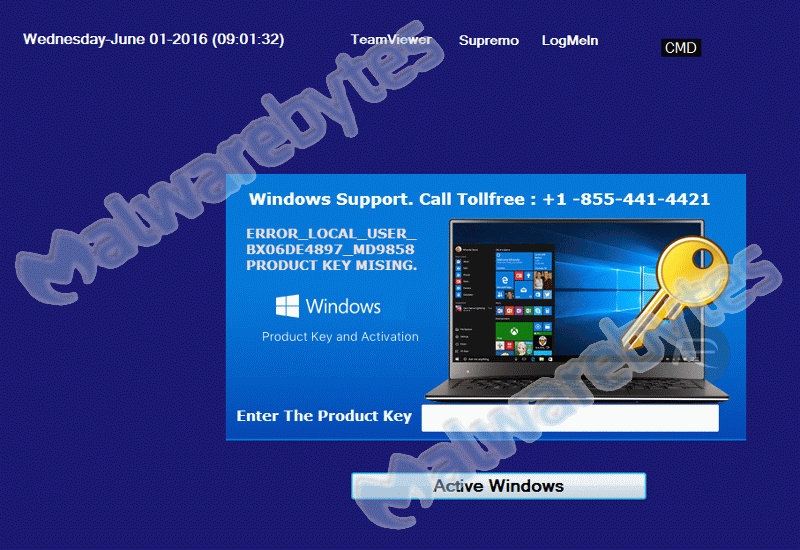
And shows the users this screen after logging on:
How do I remove WindowsActivationError?
Our program Malwarebytes Anti-Malware can detect and remove this potentially unwanted application, but due to the nature of the infection we will need a way to bypass the shell replacement.
If you already have Malwarebytes Anti-Malware installed, you can use Chameleon to get rid of this infection.
- In the TechSupportScam screen click on the "Cmd" button which will open a command prompt.
- In the command prompt type "explorer" and press "Enter".
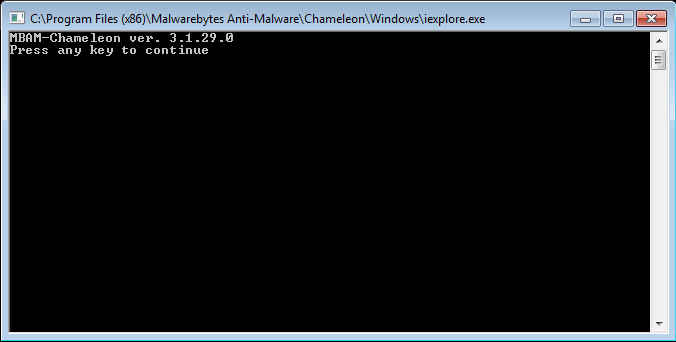
- In the resulting explorer window navigate to the Chameleon folder, usually "C:\Program Files (x86)\Malwarebytes Anti-Malware\Chameleon\Windows" and doubleclick on "iexplore(.exe)".
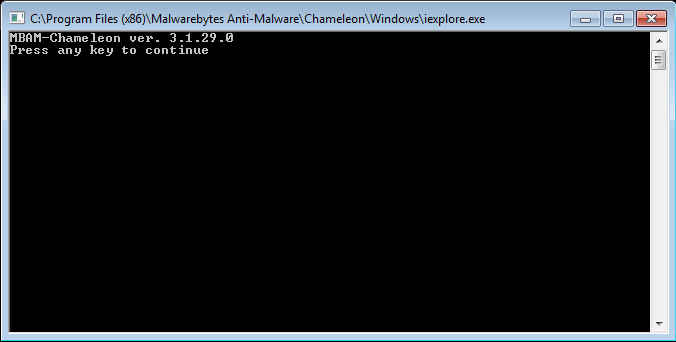
- and follow the instructions ("Press any key to continue"). Chameleon will kill the process and start Malwarebytes Anti-Malware to finish it up.
- Reboot when prompted to do so and evrything should be fine.
- In the TechSupportScam screen click on the "Cmd" button which will open a command prompt.
- In the command prompt type "taskmgr" and press "Enter".
- In the list of running "Applications" select "WindowsActivation".

- Then click on "End Task". The Techs Support Scam screen should disappear and you should be able to access your desktop again.
- Please download Malwarebytes Anti-Malware to your desktop.
- Double-click mbam-setup-version.exe and follow the prompts to install the program.
- At the end, be sure a check-mark is placed next to the following:
- Enable free trial of Malwarebytes Anti-Malware Premium
- Launch Malwarebytes Anti-Malware
- Then click Finish.
- If an update is found, you will be prompted to download and install the latest version.
- Once the program has loaded, select Scan Now. Or select the Threat Scan from the Scan menu.
- When the scan is complete, make sure that all Threats are selected, and click Remove Selected.
- Restart your computer when prompted to do so.
- No, Malwarebytes' Anti-Malware removes WindowsActivationError completely.
We hope our application and this guide have helped you eradicate this hijacker.
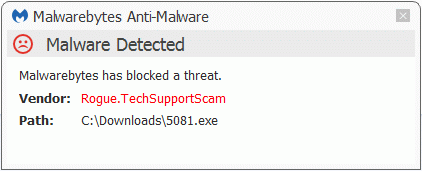
As you can see below the full version of Malwarebytes Anti-Malware would have protected you against the Tech Supprt Scam.
Technical details for experts
You may see these entries in FRST logs:
HKLM-x32\...\Run: [LicenceError] => C:\Program Files (x86)\{System-name}\error.exe [196096 2016-04-12] ()
HKLM-x32\...\Winlogon: [Shell] C:\Program Files (x86)\{System-name}\error.exe [196096 ] () <=== ATTENTION
C:\Program Files (x86)\WindowsActivationError
C:\Program Files (x86)\{System-name}
WindowsActivationError (HKLM-x32\...\WindowsActivationError) (Version: - )Alterations made by the installer:
File system details [View: All details] (Selection)
---------------------------------------------------
Adds the folder C:\Program Files (x86)\{System-name}
Adds the file error.exe"="4/12/2016 4:45 AM, 196096 bytes, A
Adds the file rst30.bat"="4/11/2016 9:26 PM, 190 bytes, A
Adds the folder C:\Program Files (x86)\WindowsActivationError
Adds the file Uninstall.exe"="6/1/2016 8:58 AM, 75325 bytes, A
Adds the file Uninstall.ini"="6/1/2016 8:58 AM, 1587 bytes, A
Registry details [View: All details] (Selection)
------------------------------------------------
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
"LicenceError"="REG_SZ", "C:\Program Files (x86)\{System-name}\error.exe"
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\WindowsActivationError]
"DisplayIcon"="REG_SZ", "C:\Program Files (x86)\WindowsActivationError\Uninstall.exe"
"DisplayName"="REG_SZ", "WindowsActivationError"
"NoModify"="REG_DWORD", 1
"NoRepair"="REG_DWORD", 1
"UninstallString"="REG_SZ", "C:\Program Files (x86)\WindowsActivationError\Uninstall.exe"
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows NT\CurrentVersion\Winlogon]
"Shell"= REG_SZ, "C:\Program Files (x86)\{System-name}\error.exe"Malwarebytes Anti-Malware log:Malwarebytes Anti-Malware
www.malwarebytes.org
Scan Date: 6/1/2016
Scan Time: 9:14 AM
Logfile: mbamWindowsActivationError.txt
Administrator: Yes
Version: 2.2.1.1043
Malware Database: v2016.06.01.02
Rootkit Database: v2016.05.27.01
License: Premium
Malware Protection: Enabled
Malicious Website Protection: Enabled
Self-protection: Enabled
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: {username}
Scan Type: Threat Scan
Result: Completed
Objects Scanned: 312433
Time Elapsed: 9 min, 6 sec
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Enabled
Heuristics: Enabled
PUP: Enabled
PUM: Enabled
Processes: 0
(No malicious items detected)
Modules: 0
(No malicious items detected)
Registry Keys: 1
Rogue.TechSupportScam, HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\WindowsActivationError, Quarantined, [f8ce589fefaa1026b031a30f36cca858],
Registry Values: 1
Rogue.TechSupportScam, HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN|LicenceError, C:\Program Files (x86)\{System-name}\error.exe, Quarantined, [f6d025d24b4ef2448b3120b4ee136a96]
Registry Data: 1
Hijack.Shell, HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS NT\CURRENTVERSION\WINLOGON|Shell, C:\Program Files (x86)\{System-name}\error.exe, Good: (Explorer.exe), Bad: (C:\Program Files (x86)\{System-name}\error.exe),Replaced,[5373d1261386211513dcb9a263a1926e]
Folders: 1
Rogue.TechSupportScam, C:\Program Files (x86)\WindowsActivationError, Quarantined, [f8ce589fefaa1026b031a30f36cca858],
Files: 4
Rogue.TechSupportScam, C:\Program Files (x86)\{System-name}\error.exe, Quarantined, [f6d025d24b4ef2448b3120b4ee136a96],
Rogue.TechSupportScam, C:\Users\{username}\Desktop\5081.exe, Quarantined, [ebdb24d37b1efa3ce1dc9143af526e92],
Rogue.TechSupportScam, C:\Program Files (x86)\WindowsActivationError\Uninstall.exe, Quarantined, [f8ce589fefaa1026b031a30f36cca858],
Rogue.TechSupportScam, C:\Program Files (x86)\WindowsActivationError\Uninstall.ini, Quarantined, [f8ce589fefaa1026b031a30f36cca858],
Physical Sectors: 0
(No malicious items detected)
(end)As mentioned before the full version of Malwarebytes Anti-Malware could have protected your computer against this threat.We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

