What is Ginemo?
The Malwarebytes research team has determined that Ginemo is ransomware. These so-called "ransomware" try to trick you into paying a ransom to get back control over your system.
How do I know if my computer is affected by Ginemo?
You may see this screen that keeps refreshing itself, effectively locking up your computer:
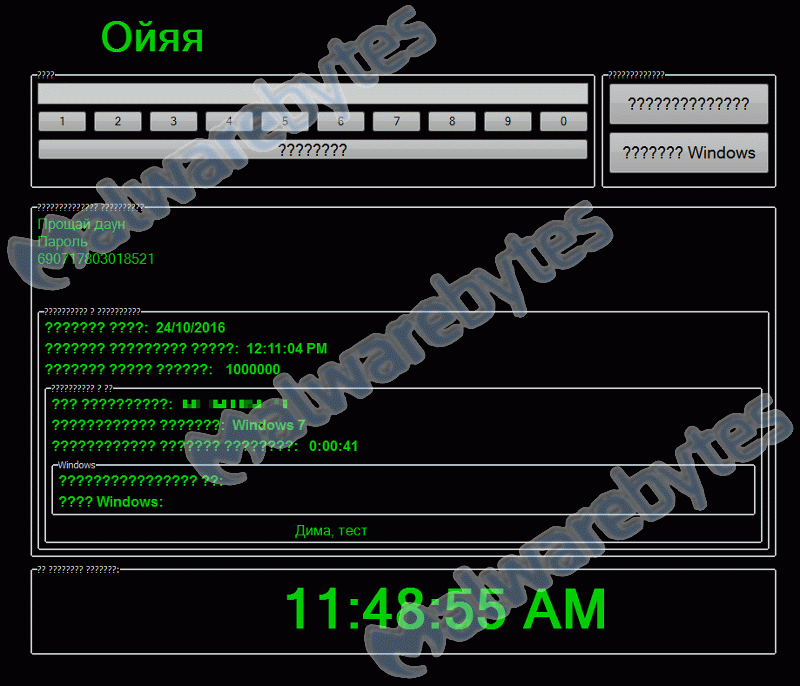
The ransomware may be targeted at people who can't read Russian as the text on the screen says:
Good bye stupid password 690717803018521How did Ginemo get on my computer?
Ransomwares use different methods for distributing themselves. This particular one was installed by a trojan.
How do I remove Ginemo?
Our program Malwarebytes Anti-Malware can detect and remove this potentially unwanted application, but due to the nature of the infection this will require some extra actions.
Method 1:
- In the screen use the buttons to enter the displayed password "690717803018521"
- The button below the numbers can be used to clear the input box, in case you made a mistake.
- Use the upper right hand button to enter the password
- The desktop will be accessible again and you can continue using the instructions below (under "Scan")
To use this method you will need a second user profile.
- Use the keyboard combination Ctrl-Alt-Del and choose "Switch User" from the menu
- Continue using the instructions below (under "Scan")
- Please download Malwarebytes Anti-Malware to your desktop.
- Double-click mbam-setup-{version}.exe and follow the prompts to install the program.
- At the end, be sure a check-mark is placed next to:
Launch Malwarebytes Anti-Malware - Then click Finish.
- Once the program has loaded, select Scan Now. Or select the Threat Scan from the Scan menu.
- If an update is available, it will be implemented before the rest of the scanning procedure.
- When the scan is complete, make sure that all Threats are selected, and click Remove Selected.
- Restart your computer when prompted to do so.
- No, Malwarebytes' Anti-Malware removes Ginemo completely.
We hope our application and this guide have helped you eradicate this hijacker.
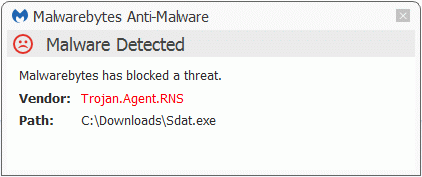
As you can see below the full version of Malwarebytes Anti-Malware would have protected you against the Tech Supprt Scam.
Technical details for experts
You may see these entries in FRST logs:
HKCU\..\RunOnce: [userini] C:\Users\{username}\AppData\Roaming\Sdat.exe [446464 2016-10-24] ()
HKCU\...\Winlogon: [Shell] C:\Users\{username}\AppData\Roaming\Sdat.exe <==== ATTENTIONMalwarebytes Anti-Malware log:Malwarebytes Anti-Malware
www.malwarebytes.org
Scan Date: 10/24/2016
Scan Time: 10:26 AM
Logfile: mbamGinero.txt
Administrator: Yes
Version: 2.2.1.1043
Malware Database: v2016.10.24.01
Rootkit Database: v2016.09.26.02
License: Premium
Malware Protection: Enabled
Malicious Website Protection: Enabled
Self-protection: Enabled
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: {username}
Scan Type: Threat Scan
Result: Completed
Objects Scanned: 325974
Time Elapsed: 9 min, 12 sec
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Enabled
Heuristics: Enabled
PUP: Enabled
PUM: Enabled
Processes: 0
(No malicious items detected)
Modules: 0
(No malicious items detected)
Registry Keys: 0
(No malicious items detected)
Registry Values: 0
(No malicious items detected)
Registry Data: 0
(No malicious items detected)
Folders: 0
(No malicious items detected)
Files: 1
Trojan.Agent.RNS, C:\Users\{username}\AppData\Roaming\Sdat.exe, Quarantined, [04fd5c41d3c795a1de6ac43dcd37748c],
Physical Sectors: 0
(No malicious items detected)
(end)As mentioned before the full version of Malwarebytes Anti-Malware could have protected your computer against this threat.We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

