Hello!
While I've never personally posted here specifically, I'm usually on the other end of help threads like this, so unfortunately, this is something that's legitimately serious and probably not something that has a quick fix.
I recently got a piece of adware that, while annoying, was nothing spectacular; however, this didn't last for long. The adware was elusive and difficult to remove, so I decided that I would deal with it later. Unfortunately, this adware operated by opening referral links and then clicking on the contents within them through some sort of clickjacking, which resulted in it clicking on an infected ad which then made the adware malicious via an "update". Things rapidly deteriorated from here, and the following symptoms arose:
-Somehow, it displayed a fake login screen over my real one. This was used to capture the auth key from my fingerprint scanner, which was subsequently used to automatically log into the laptop every boot, as well as privilege-escalate itself into creating a superuser account
-After this, it created a local proxy server and began re-routing all of my traffic through it. This also disabled HTTPS, although it was sneaky about it- https seems to be disabled on all outbound connections out of the proxy, but the connection is "secure" while it connects to the proxy itself. This SSL stripping resulted browsers incorrectly stating that connections were secure, when they were in fact not (this could be verified because websites that enforce SSL connections would not allow me to connect, and thank god they did because otherwise I would not have caught this). This proxy was managed via registry keys, again with the super-user access it had gained control to earlier
-Programs with auto-generated names began running and inserting themselves as startup items. Deleting these programs caused them to be created again somewhere random on my drive, including administrator-access-only locations. I have literally no idea what these programs are doing, as they seem to consume no resources. I think they're used to re-install any missing components of the core of the malware, but I'm not certain.
-Generalized, trashware adware was then installed, although this wasn't too hard to snuff out because the majority of the schlock came with uninstallers as they were semi-legit programs
-Finally, and this is what puts the nail in the coffin of all of this:
It completely disabled ALL antimalware as well as ALL software that could be used to determine what was happening. The following programs cannot run:
Hijack This
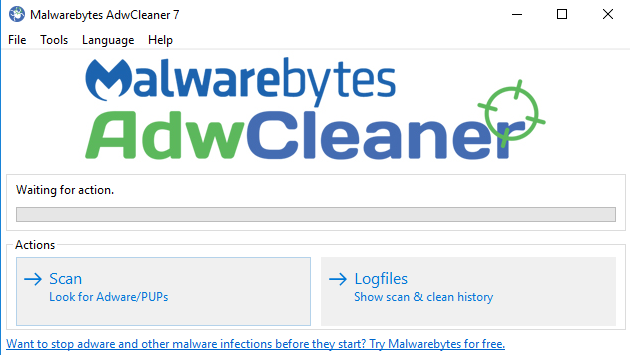
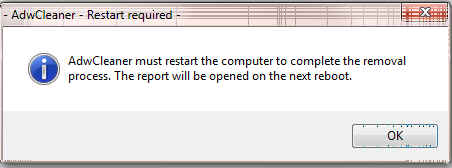
Malwarebytes (and Chameleon)
Procmon
Hitman Pro
rKill
Any name-brand antimalware software
Additionally, these programs cannot run in safe mode either.
I was finally able to make a very, very old version of procmon run, which let me inspect what was happening with the programs shutting off. It seems like the process starts, it launches successfully, and then almost immediately after that the main thread of the program is axed by something internally (not a regular application close, the thread is just terminated /w no indicator of how it was terminated and no error code).
The latter issue, as well as the auto-sign in, are present in safe mode.
Semi-successful scans included Windows Defender full scan, which picked up on some less malicious adware and malware, and a semi-broken install of Sophos (it couldn't fully fully complete install and failed right at the end, although I was able to still scan) which got rid of the thing that was causing the proxy server to be spawned.
My final try was with the Sophos Bootable CD, which successfully scans my boot record and partition table, but then goes on to scan 0 files and finish instantly.
On top of this, I cannot use the windows "fresh start" button (it does nothing).
pls help
If you need any more information, please feel free to ask for it. Also, if fixes are 'dangerous' in that incorrectly executing them could result in a bricked system if I mess up, fire away. I just want to fix this.
Edited by MsDoe, 16 October 2017 - 04:23 PM.


 This topic is locked
This topic is locked









![HP desktop - google.com is in Norwegian [Solved] - last post by wayneman50](https://www.geekstogo.com/forum/uploads/profile/photo-thumb-328601.jpg?_r=1546827512)









 Sign In
Sign In Create Account
Create Account

