Hi,
My home network got super crazy last year as a tool for harassment. I know almost nothing about Networking but here this is:
The ISP is Cox in Arizona
Router was a Netgear R7000 which my brother installed DDWrt firmware on to maybe help stem the "shutdowns"
Modem was a CIsco DPQ3212
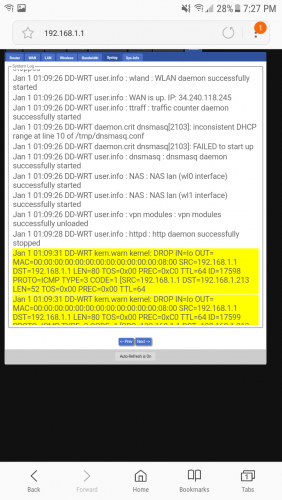
So I went through log after log and found something peculiar. With the old network being located in the Phoenix suburbs in Arizona we generally would have the WAN IP in that range, with San Diego being thrown in from time to time. I figured the mistake was Cox Communications based as opposed to a network intrusion. But this time there was an IP address from Ireland showing in the syslog under "WAN is up: 34.240.118.245".
Why would this happen? Is it related to the attack and could it possibly be used, in conjunction with Date and Time to point to the hacker? Again, I know nothing...obviously. But Cox was really skittish about providing me with the serial number they had on file for my modem when I wanted to make sure it matched with our In-Home modem. Again, why? It didn't match. And there was mystery online charges on our statement showing our service one week going from the 100 mb/s to 30 mb/s and then back again...just for one week. With all attached charges zeroed out.
I have reason to suspect that it is either the work of some crazy telecommunications employee messing with people's stuff OR...and try to stay with me here...OR its law enforcement. I'm not sure how the official "handover" of data is usually carried out between an ISP and a law enforcement agency. Just take my word that I had good reasons to consider that an option, and due to the amount of time since the attacks were taking place, the "handover" yielded nothing.
Thanks in advance for any networking insight into this. I have attached a screen shot of the syslog entry. Keep in mind that these logs were captured during the boot process and there was nothing connected to the WiFi or by ethernet.
















 Sign In
Sign In Create Account
Create Account

