What is ExtenBro?
The Malwarebytes research team has determined that ExtenBro is adware. These adware applications display advertisements not originating from the sites you are browsing.
This particular one blocks access to domains related to security software to hinder victims from installing a remediation.
How do I know if my computer is affected by ExtenBro?
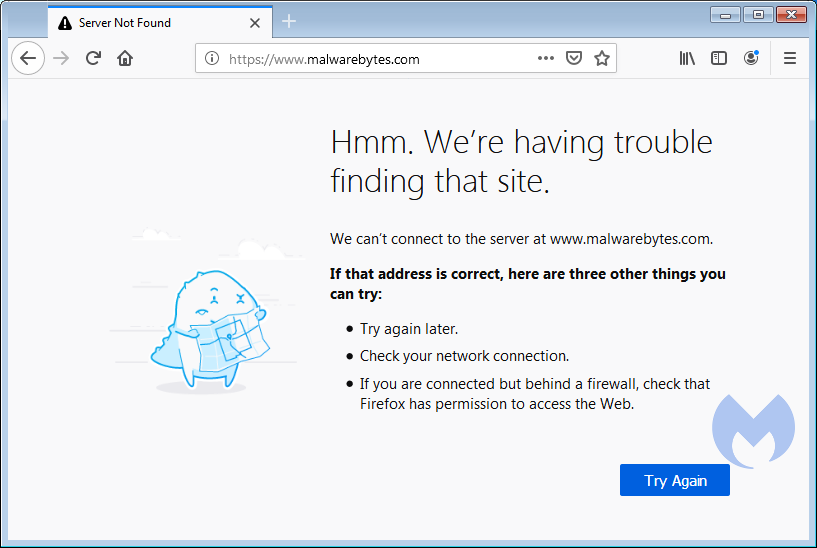
Users may complain about being unable to reach malwarebytes.com and other AV related domains:
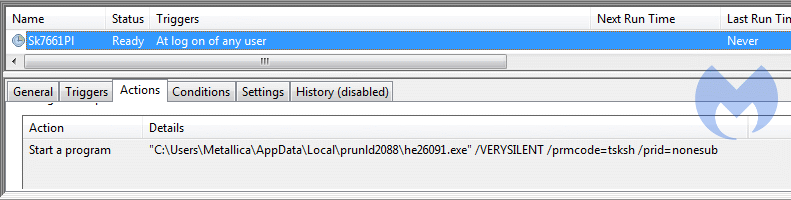
You may see this type of task in your Scheduled Tasks:
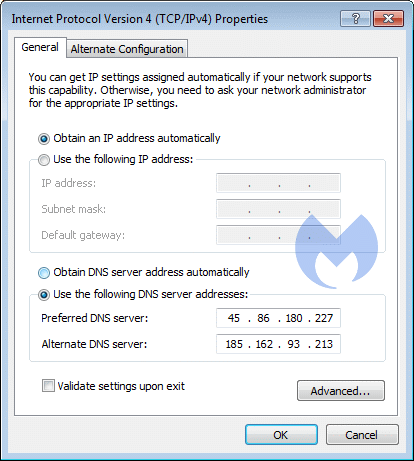
these changed DNS settings:
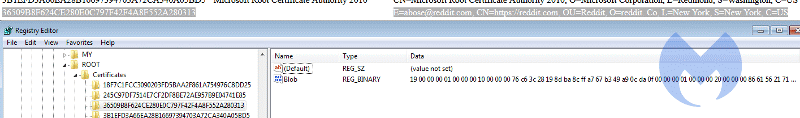
and this entry in your list of Root certificates:
How did ExtenBro get on my computer?
Adware applications use different methods for distributing themselves. This particular one was installed by a bundler.
How do I remove ExtenBro?
Our program Malwarebytes can detect and remove this potentially unwanted program.
- Due to the nature of this DNS changer you may have to change your DNS settings first.
- If you can't find the preferred settings on the website of your internet-service provider (ISP), you can follow the appropiate instructions on the OpenDNS site.
- When you are looking at the DNS settings, make sure to click Advanced and look at the DNS tab
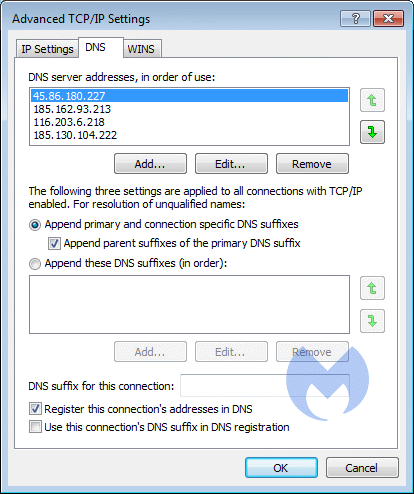
- Make sure that only two of those entries are left and that they match the preferred settings that you found, before you close the Internet Connection settings menu's.
- Do not reboot your system yet, because the Scheduled Task will re-instate the malicious DNS settings.
- You may have to restart your browser to make it use the new settings.
- Please download Malwarebytes to your desktop.
- Double-click mb3-setup-consumer-{version}.exe and follow the prompts to install the program.
- Then click Finish.
- Once the program has fully updated, select Scan Now on the Dashboard. Or select the Threat Scan from the Scan menu.
- If another update of the definitions is available, it will be implemented before the rest of the scanning procedure.
- When the scan is complete, make sure that all Threats are selected, and click Remove Selected.
- Restart your computer when prompted to do so.
- No, Malwarebytes removes ExtenBro completely.
- This PUP creates a scheduled task. You can read here how to check for and, if necessary, remove Scheduled Tasks.
We hope our application and this guide have helped you eradicate this adware.
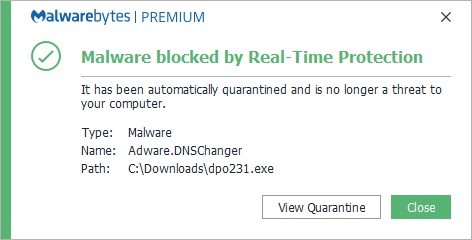
As you can see below the full version of Malwarebytes would have protected you against the ExtenBro adware. It would have blocked the installer before it became too late.
Technical details for experts
Possible signs in FRST logs:
Task: {50620101-C554-48D3-BAC6-0E9FF5466289} - System32\Tasks\Sk7661Pl => C:\Users\{username}\AppData\Local\prunld2088\he26091.exe [1387864 2019-07-10] ( ) [File not signed]
Tcpip\..\Interfaces\{DCC6FDFC-344E-465D-A1F5-77B8161CA4FB}: [NameServer] 45.86.180.227,185.162.93.213,116.203.6.218,185.130.104.222,77.234.40.79
Tcpip\..\Interfaces\{EDB0D6D8-B1F7-496F-A023-44DF7155F1CD}: [NameServer] 45.86.180.227,185.162.93.213,116.203.6.218,185.130.104.222
FF user.js: detected! => C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\vkq9erdv.default-1519559592148-1560329836028\user.js [2019-07-10]
C:\Windows\System32\Tasks\Sk7661Pl
( ) C:\Users\{username}\Desktop\dpo231.exe
( ) C:\Users\{username}\AppData\Local\prunld2088\he26091.exeSignificant changes made by the installer:File system details [View: All details] (Selection)
---------------------------------------------------
Adds the folder C:\Users\{username}\AppData\Local\prunld2088
Adds the file he26091.exe"="7/10/2019 8:59 AM, 1387864 bytes, A
In the existing folder C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\vkq9erdv.default-1519559592148-1560329836028
Adds the file user.js"="7/10/2019 8:59 AM, 53 bytes, A
In the existing folder C:\Windows\System32\Tasks
Adds the file Sk7661Pl"="7/10/2019 8:59 AM, 3194 bytes, A
Registry details [View: All details] (Selection)
------------------------------------------------
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\36509B8F624CE280E0C797F42F4A8F552A280313]
"Blob"="REG_BINARY, .................. ................................................. ..........................................
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\TCPIP6\Parameters]
"DisabledComponents"="REG_DWORD", 255
[HKEY_CURRENT_USER\Software\UniversalCadast]
"InstRes"="REG_SZ", "1"Malwarebytes log:Malwarebytes
www.malwarebytes.com
-Log Details-
Scan Date: 7/10/19
Scan Time: 1:15 PM
Log File: 0e88437a-a304-11e9-a395-00ffdcc6fdfc.json
-Software Information-
Version: 3.7.1.2839
Components Version: 1.0.586
Update Package Version: 1.0.11482
License: Premium
-System Information-
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: METALLICA-PC\Metallica
-Scan Summary-
Scan Type: Threat Scan
Scan Initiated By: Manual
Result: Completed
Objects Scanned: 236345
Threats Detected: 11
Threats Quarantined: 11
Time Elapsed: 5 min, 23 sec
-Scan Options-
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Enabled
Heuristics: Enabled
PUP: Detect
PUM: Detect
-Scan Details-
Process: 0
(No malicious items detected)
Module: 0
(No malicious items detected)
Registry Key: 5
Adware.ExtenBro, HKLM\SOFTWARE\MICROSOFT\SYSTEMCERTIFICATES\ROOT\CERTIFICATES\36509B8F624CE280E0C797F42F4A8F552A280313, Quarantined, [2068], [706129],1.0.11482
Adware.ExtenBro, HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\SYSTEMCERTIFICATES\ROOT\CERTIFICATES\36509B8F624CE280E0C797F42F4A8F552A280313, Quarantined, [2068], [706129],1.0.11482
Trojan.Agent, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\Sk9239Pl, Quarantined, [442], [698502],1.0.11482
Trojan.Agent, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{03EAD71D-807C-49EE-922B-A4F7F554D25B}, Quarantined, [442], [698502],1.0.11482
Trojan.Agent, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\LOGON\{03EAD71D-807C-49EE-922B-A4F7F554D25B}, Quarantined, [442], [698502],1.0.11482
Registry Value: 0
(No malicious items detected)
Registry Data: 3
Trojan.DNSChanger, HKLM\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters\Interfaces\{DCC6FDFC-344E-465D-A1F5-77B8161CA4FB}|NameServer, Replaced, [3068], [706134],1.0.11482
Trojan.DNSChanger, HKLM\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters\Interfaces\{DCC6FDFC-344E-465D-A1F5-77B8161CA4FB}|NameServer, Replaced, [3068], [706135],1.0.11482
Trojan.DNSChanger, HKLM\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters\Interfaces\{DCC6FDFC-344E-465D-A1F5-77B8161CA4FB}|NameServer, Replaced, [3068], [706136],1.0.11482
Data Stream: 0
(No malicious items detected)
Folder: 0
(No malicious items detected)
File: 3
Trojan.Agent, C:\WINDOWS\SYSTEM32\TASKS\Sk9239Pl, Quarantined, [442], [698502],1.0.11482
Adware.DNSChanger, C:\USERS\METALLICA\APPDATA\LOCAL\PRUNLD8747\HE88127.EXE, Quarantined, [695], [706144],1.0.11482
Adware.DNSChanger, C:\USERS\METALLICA\DESKTOP\DPO231.EXE, Quarantined, [695], [706158],1.0.11482
Physical Sector: 0
(No malicious items detected)
WMI: 0
(No malicious items detected)
(end)As mentioned before the full version of Malwarebytes could have protected your computer against this threat.We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

