What is SMedia?
The Malwarebytes research team has determined that SMedia is a search hijacker. These so-called "hijackers" manipulate your browser(s), for example to change your startpage or searchscopes, so that the affected browser visits their site or one of their choice.
How do I know if my computer is affected by SMedia?
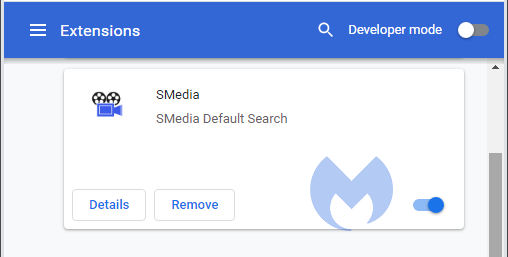
You may see this entry in your list of installed Chrome extensions:
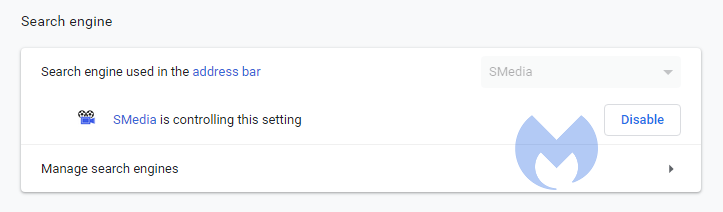
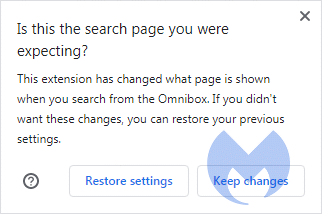
and this changed setting:
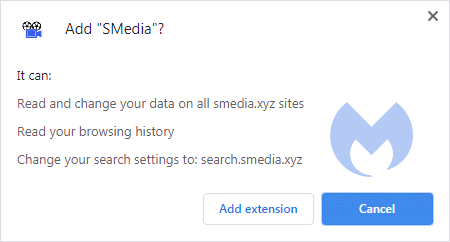
You may have noticed these warnings during install:
How did SMedia get on my computer?
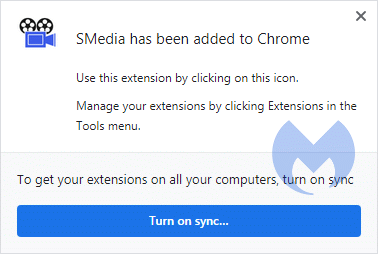
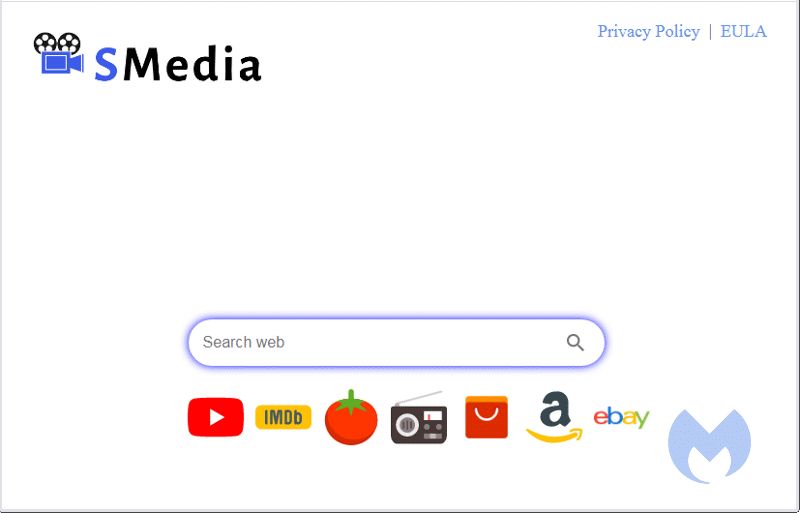
Browser hijackers use different methods for distributing themselves. This particular one was downloaded from the webstore:
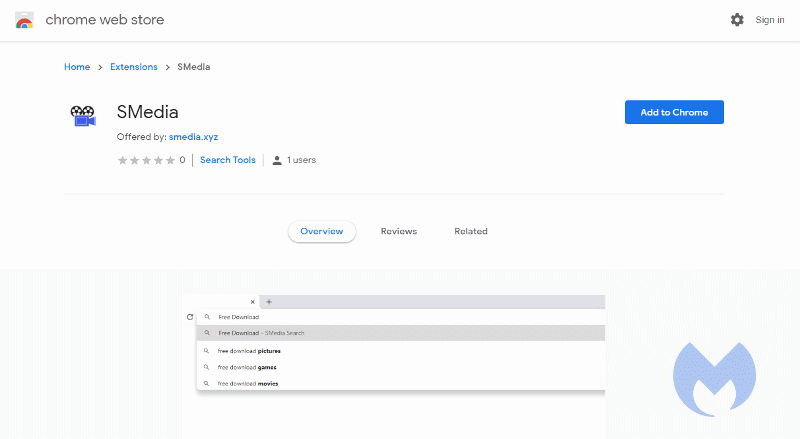
after a redirect from their website:
How do I remove SMedia?
Our program Malwarebytes can detect and remove this potentially unwanted program.
- Please download Malwarebytes for Windows to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- When the scan is finished click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
- No, Malwarebytes removes SMedia completely.
We hope our application and this guide have helped you eradicate this hijacker.
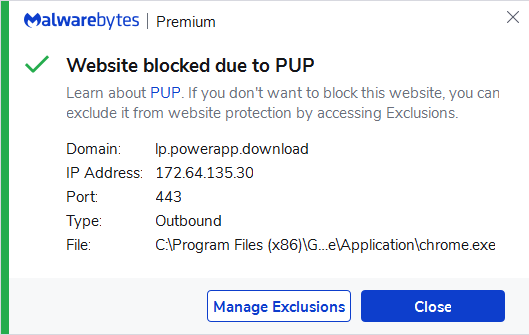
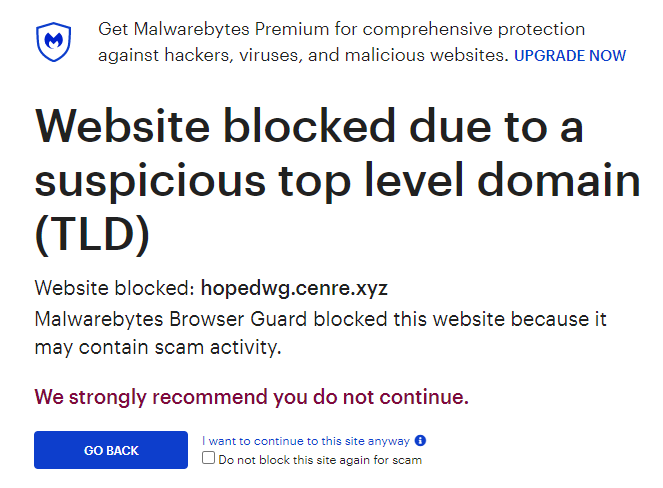
As you can see below Malwarebytes Browser Guard, and the full version of Malwarebytes would have protected you against the SMedia hijacker. It would have blocked their website, giving you a chance to stop it before it became too late.
Technical details for experts
Possible signs in FRST logs:
CHR DefaultSearchURL: Default -> hxxps://search.smedia.xyz/chrome/newtab/search.aspx?q={searchTerms}&src=ds&pid=ismedia&v=1.6#chrome://newtab
CHR DefaultSearchKeyword: Default -> hxxps://www.smedia.xyz/search.aspx
CHR DefaultSuggestURL: Default -> hxxps://www.smedia.xyz/ntapi/suggestions/rd?q={searchTerms}
CHR Extension: (SMedia) - C:\Users\Metallica\AppData\Local\Google\Chrome\User Data\Default\Extensions\hmpmalngfnhbmbdkdnlehcfpdmpaidim [2020-07-14]Alterations made by the installer:File system details [View: All details] (Selection)
---------------------------------------------------
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\hmpmalngfnhbmbdkdnlehcfpdmpaidim\1.6_0
Adds the file manifest.json"="7/14/2020 7:15 PM, 1769 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\hmpmalngfnhbmbdkdnlehcfpdmpaidim\1.6_0\_metadata
Adds the file computed_hashes.json"="7/14/2020 7:15 PM, 981 bytes, A
Adds the file verified_contents.json"="7/12/2020 4:05 PM, 2257 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\hmpmalngfnhbmbdkdnlehcfpdmpaidim\1.6_0\common
Adds the file contentscript.js"="7/12/2020 4:05 PM, 637 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\hmpmalngfnhbmbdkdnlehcfpdmpaidim\1.6_0\img
Adds the file logo.png"="7/12/2020 4:05 PM, 5849 bytes, A
Adds the file logo_128x.png"="7/14/2020 7:15 PM, 6657 bytes, A
Adds the file logo_16x.png"="7/14/2020 7:15 PM, 509 bytes, A
Adds the file logo_48x.png"="7/14/2020 7:15 PM, 1806 bytes, A
Adds the file search.png"="7/12/2020 4:05 PM, 646 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\hmpmalngfnhbmbdkdnlehcfpdmpaidim\1.6_0\release
Adds the file browseraction_release.js"="7/12/2020 4:05 PM, 31707 bytes, A
Adds the file script_release.js"="7/12/2020 4:05 PM, 1388 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\hmpmalngfnhbmbdkdnlehcfpdmpaidim
Adds the file 000003.log"="7/14/2020 7:19 PM, 686 bytes, A
Adds the file CURRENT"="7/14/2020 7:15 PM, 16 bytes, A
Adds the file LOCK"="7/14/2020 7:15 PM, 0 bytes, A
Adds the file LOG"="7/14/2020 7:20 PM, 184 bytes, A
Adds the file MANIFEST-000001"="7/14/2020 7:15 PM, 41 bytes, A
Registry details [View: All details] (Selection)
------------------------------------------------
[HKEY_CURRENT_USER\Software\Google\Chrome\PreferenceMACs\Default\extensions.settings]
"hmpmalngfnhbmbdkdnlehcfpdmpaidim"="REG_SZ", "5FD2DA61DC0B0AFE23AA73921038B0C6BAAB857EB3F043D09E1AA9905C6279CB"Malwarebytes log:Malwarebytes
www.malwarebytes.com
-Log Details-
Scan Date: 7/15/20
Scan Time: 8:43 AM
Log File: 71a06db2-c666-11ea-b07f-00ffdcc6fdfc.json
-Software Information-
Version: 4.1.2.73
Components Version: 1.0.979
Update Package Version: 1.0.26847
License: Premium
-System Information-
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: {computername}\{username}
-Scan Summary-
Scan Type: Threat Scan
Scan Initiated By: Manual
Result: Completed
Objects Scanned: 231923
Threats Detected: 11
Threats Quarantined: 11
Time Elapsed: 4 min, 50 sec
-Scan Options-
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Disabled
Heuristics: Enabled
PUP: Detect
PUM: Detect
-Scan Details-
Process: 0
(No malicious items detected)
Module: 0
(No malicious items detected)
Registry Key: 0
(No malicious items detected)
Registry Value: 1
PUP.Optional.SMedia, HKCU\SOFTWARE\GOOGLE\CHROME\PREFERENCEMACS\Default\extensions.settings|hmpmalngfnhbmbdkdnlehcfpdmpaidim, Quarantined, 15314, 840645, , , ,
Registry Data: 0
(No malicious items detected)
Data Stream: 0
(No malicious items detected)
Folder: 2
PUP.Optional.SMedia, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\Default\Local Extension Settings\hmpmalngfnhbmbdkdnlehcfpdmpaidim, Quarantined, 15314, 840645, , , ,
PUP.Optional.SMedia, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\DEFAULT\EXTENSIONS\HMPMALNGFNHBMBDKDNLEHCFPDMPAIDIM, Quarantined, 15314, 840645, 1.0.26847, , ame,
File: 8
PUP.Optional.SMedia, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\Default\Secure Preferences, Replaced, 15314, 840645, , , ,
PUP.Optional.SMedia, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\Default\Preferences, Replaced, 15314, 840645, , , ,
PUP.Optional.SMedia, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\hmpmalngfnhbmbdkdnlehcfpdmpaidim\000003.log, Quarantined, 15314, 840645, , , ,
PUP.Optional.SMedia, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\hmpmalngfnhbmbdkdnlehcfpdmpaidim\CURRENT, Quarantined, 15314, 840645, , , ,
PUP.Optional.SMedia, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\hmpmalngfnhbmbdkdnlehcfpdmpaidim\LOCK, Quarantined, 15314, 840645, , , ,
PUP.Optional.SMedia, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\hmpmalngfnhbmbdkdnlehcfpdmpaidim\LOG, Quarantined, 15314, 840645, , , ,
PUP.Optional.SMedia, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Local Extension Settings\hmpmalngfnhbmbdkdnlehcfpdmpaidim\MANIFEST-000001, Quarantined, 15314, 840645, , , ,
PUP.Optional.SMedia, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\DEFAULT\EXTENSIONS\HMPMALNGFNHBMBDKDNLEHCFPDMPAIDIM\1.6_0\MANIFEST.JSON, Quarantined, 15314, 840645, 1.0.26847, , ame,
Physical Sector: 0
(No malicious items detected)
WMI: 0
(No malicious items detected)
(end)As mentioned before the full version of Malwarebytes could have protected your computer against this threat.We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

