What is HDConverterSearch?
The Malwarebytes research team has determined that HDConverterSearch is a search hijacker. These so-called "hijackers" manipulate your browser(s), for example to change your startpage or searchscopes, so that the affected browser visits their site or one of their choice.
How do I know if my computer is affected by HDConverterSearch?
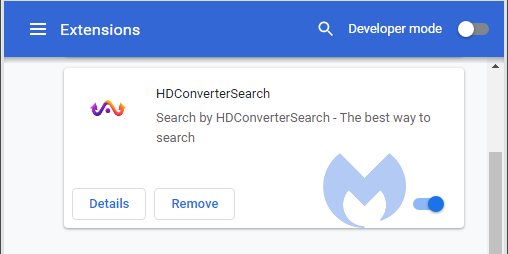
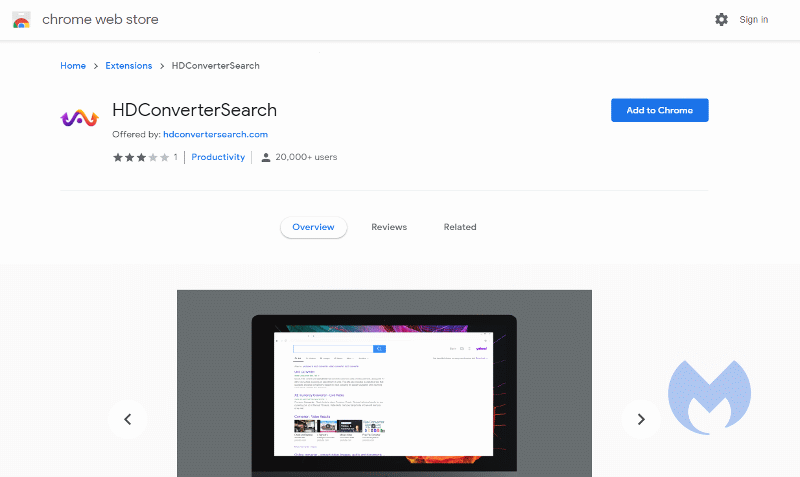
You may see this entry in your list of installed Chrome extensions:
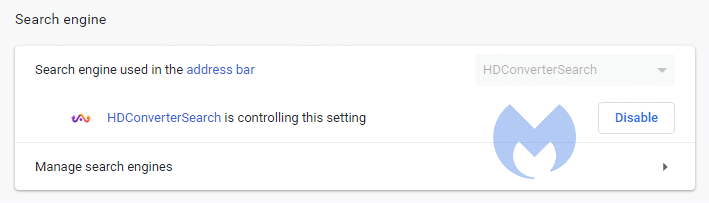
and this changed setting:
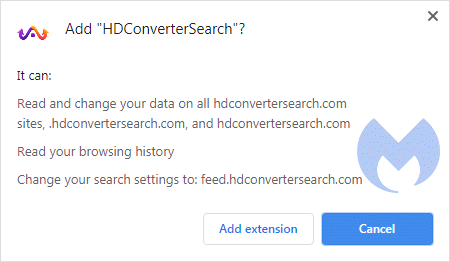
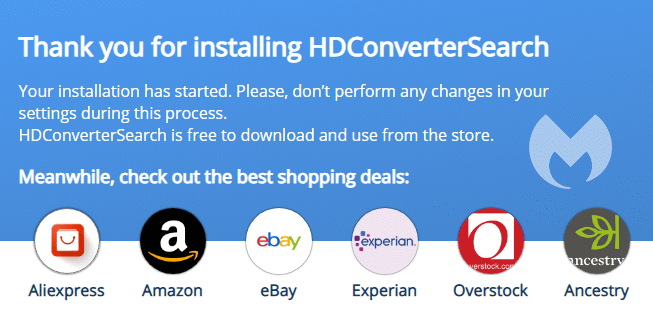
You may have noticed these warnings during install:
How did HDConverterSearch get on my computer?
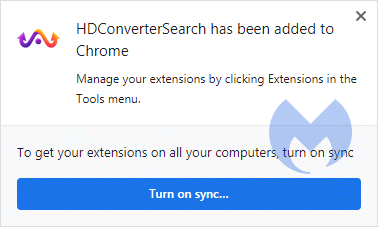
Browser hijackers use different methods for distributing themselves. This particular one was downloaded from the webstore:
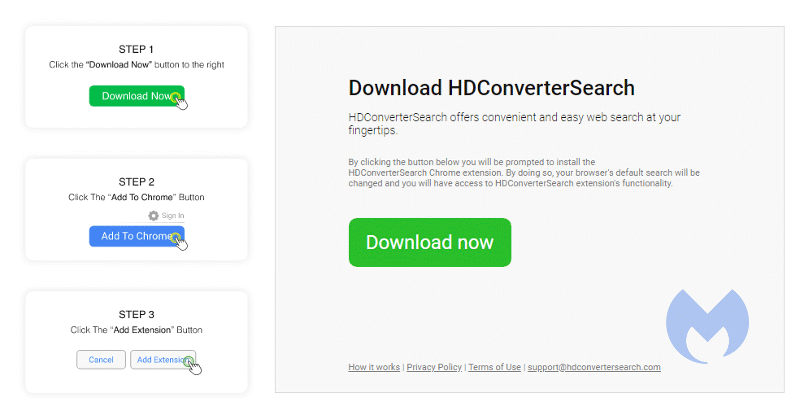
after a redirect from their website:
How do I remove HDConverterSearch?
Our program Malwarebytes can detect and remove this potentially unwanted program.
- Please download Malwarebytes for Windows to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- When the scan is finished click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
- No, Malwarebytes removes HDConverterSearch completely.
We hope our application and this guide have helped you eradicate this hijacker.
Malwarebytes Browser Guard, as well as the full version of Malwarebytes will protect you against the HDConverterSearch hijacker. It will block their website, giving you a chance to stop it before it became too late.
Technical details for experts
Possible signs in FRST logs:
CHR DefaultSearchURL: Default -> hxxps://feed.hdconvertersearch.com/?q={searchTerms}&publisher=hdconvertersearch&barcodeid=577310000000000
CHR DefaultSearchKeyword: Default -> HDConverterSearch
CHR DefaultSuggestURL: Default -> hxxps://api.hdconvertersearch.com/suggest/get?q={searchTerms}
CHR Extension: (HDConverterSearch) - C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\bjpadccgendgmeccahhmkllpmkemmmem [2020-08-17]Alterations made by the installer:File system details [View: All details] (Selection)
---------------------------------------------------
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\bjpadccgendgmeccahhmkllpmkemmmem\1.1.0_0
Adds the file manifest.json"="8/17/2020 10:20 AM, 2144 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\bjpadccgendgmeccahhmkllpmkemmmem\1.1.0_0\_metadata
Adds the file computed_hashes.json"="8/17/2020 10:20 AM, 6255 bytes, A
Adds the file verified_contents.json"="7/16/2020 3:53 PM, 2049 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\bjpadccgendgmeccahhmkllpmkemmmem\1.1.0_0\images
Adds the file logo-white-text.png"="7/16/2020 3:53 PM, 0 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\bjpadccgendgmeccahhmkllpmkemmmem\1.1.0_0\images\icons
Adds the file 128x128.png"="8/17/2020 10:20 AM, 7169 bytes, A
Adds the file 16x16.png"="8/17/2020 10:20 AM, 464 bytes, A
Adds the file 64x64.png"="8/17/2020 10:20 AM, 2883 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Extensions\bjpadccgendgmeccahhmkllpmkemmmem\1.1.0_0\scripts
Adds the file background.js"="7/16/2020 3:53 PM, 514658 bytes, A
Adds the file sitecontent.js"="7/16/2020 3:53 PM, 77 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\bjpadccgendgmeccahhmkllpmkemmmem
Adds the file 000003.log"="8/17/2020 10:20 AM, 0 bytes, A
Adds the file CURRENT"="8/17/2020 10:20 AM, 16 bytes, A
Adds the file LOCK"="8/17/2020 10:20 AM, 0 bytes, A
Adds the file LOG"="8/17/2020 10:20 AM, 0 bytes, A
Adds the file MANIFEST-000001"="8/17/2020 10:20 AM, 41 bytes, A
Adds the folder C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Web Applications\_crx_bjpadccgendgmeccahhmkllpmkemmmem
Adds the file HDConverterSearch.ico"="8/17/2020 10:20 AM, 183865 bytes, A
Adds the file HDConverterSearch.ico.md5"="8/17/2020 10:20 AM, 16 bytes, A
Registry details [View: All details] (Selection)
------------------------------------------------
[HKEY_CURRENT_USER\Software\Google\Chrome\PreferenceMACs\Default\extensions.settings]
"bjpadccgendgmeccahhmkllpmkemmmem"="REG_SZ", "E53D4560B152C5779907FA50100C610577357201611A9F01A153CACDF95CDF9F"Malwarebytes log:Malwarebytes
www.malwarebytes.com
-Log Details-
Scan Date: 8/17/20
Scan Time: 10:31 AM
Log File: 1c8f61a8-e064-11ea-843f-00ffdcc6fdfc.json
-Software Information-
Version: 4.1.2.73
Components Version: 1.0.1003
Update Package Version: 1.0.28601
License: Premium
-System Information-
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: {computername}\{username}
-Scan Summary-
Scan Type: Threat Scan
Scan Initiated By: Manual
Result: Completed
Objects Scanned: 231077
Threats Detected: 11
Threats Quarantined: 11
Time Elapsed: 4 min, 14 sec
-Scan Options-
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Disabled
Heuristics: Enabled
PUP: Detect
PUM: Detect
-Scan Details-
Process: 0
(No malicious items detected)
Module: 0
(No malicious items detected)
Registry Key: 0
(No malicious items detected)
Registry Value: 1
Adware.SearchEngineHijack.Generic, HKCU\SOFTWARE\GOOGLE\CHROME\PREFERENCEMACS\Default\extensions.settings|bjpadccgendgmeccahhmkllpmkemmmem, Quarantined, 15192, 799722, , , , , ,
Registry Data: 0
(No malicious items detected)
Data Stream: 0
(No malicious items detected)
Folder: 2
Adware.SearchEngineHijack.Generic, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\Default\Sync Extension Settings\bjpadccgendgmeccahhmkllpmkemmmem, Quarantined, 15192, 799722, , , , , ,
Adware.SearchEngineHijack.Generic, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\DEFAULT\EXTENSIONS\BJPADCCGENDGMECCAHHMKLLPMKEMMMEM, Quarantined, 15192, 799722, 1.0.28601, , ame, , ,
File: 8
Adware.SearchEngineHijack.Generic, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\Default\Secure Preferences, Replaced, 15192, 799722, , , , , 5B8A5838B5B874E75CC99244ADE48D9F, 4E978A49C35B82F311B4CA98A448BC12997C536B399470300DE101093F8F4FE9
Adware.SearchEngineHijack.Generic, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\Default\Preferences, Replaced, 15192, 799722, , , , , 552CB167FE45ED3A8F4A5362CD51488D, 3432DF96D5A18376EA77B8174AB86CD234AFB19048AE5EF118F16FBF434CD5B0
Adware.SearchEngineHijack.Generic, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\bjpadccgendgmeccahhmkllpmkemmmem\000003.log, Quarantined, 15192, 799722, , , , , 612F8CB19B4796824AEFAAF9F0CC7D15, 072BD8CAD9EC376B2914C2A9699E0340BEA0E1B8E8B95A43561F61989F6D44ED
Adware.SearchEngineHijack.Generic, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\bjpadccgendgmeccahhmkllpmkemmmem\CURRENT, Quarantined, 15192, 799722, , , , , 46295CAC801E5D4857D09837238A6394, 0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443
Adware.SearchEngineHijack.Generic, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\bjpadccgendgmeccahhmkllpmkemmmem\LOCK, Quarantined, 15192, 799722, , , , , ,
Adware.SearchEngineHijack.Generic, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\bjpadccgendgmeccahhmkllpmkemmmem\LOG, Quarantined, 15192, 799722, , , , , 70AFA642DAD8F6F32DC41BB6A307D9F0, 4C3554C5F0096BDF6BDD98B214A8CC1C73FD6801367BAD4CC9E47117D5DE5EFA
Adware.SearchEngineHijack.Generic, C:\Users\{username}\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\bjpadccgendgmeccahhmkllpmkemmmem\MANIFEST-000001, Quarantined, 15192, 799722, , , , , 5AF87DFD673BA2115E2FCF5CFDB727AB, F9D31B278E215EB0D0E9CD709EDFA037E828F36214AB7906F612160FEAD4B2B4
Adware.SearchEngineHijack.Generic, C:\USERS\{username}\APPDATA\LOCAL\GOOGLE\CHROME\USER DATA\DEFAULT\EXTENSIONS\BJPADCCGENDGMECCAHHMKLLPMKEMMMEM\1.1.0_0\MANIFEST.JSON, Quarantined, 15192, 799722, 1.0.28601, , ame, , D74518D36D8840954903C29ED91F3E25, 8C87255D3DC3DE34765455D77F0F1D66878D757CDA18F786038C2D3E1318C33D
Physical Sector: 0
(No malicious items detected)
WMI: 0
(No malicious items detected)
(end)As mentioned before the full version of Malwarebytes could have protected your computer against this threat.We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

