As you have seen many times before, I am another Windows user going insane with advertisement pop up windows. I have tried everything for a week and am at the point of no return with this garbage. I believe the low lifes that advertise through these malicious programs should be burned as well as the folks that write/distribute this trash.
Logfile of HijackThis v1.99.1
Scan saved at 11:35:16 PM, on 8/7/2005
Platform: Windows XP SP1 (WinNT 5.01.2600)
MSIE: Internet Explorer v6.00 SP1 (6.00.2800.1106)
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\system32\spoolsv.exe
C:\WINDOWS\system32\rundll32.exe
C:\WINDOWS\Explorer.EXE
C:\WINDOWS\System32\ZoneLabs\isafe.exe
C:\WINDOWS\SYSTEM32\ZONELABS\vsmon.exe
C:\Program Files\Zone Labs\ZoneAlarm\zlclient.exe
C:\Program Files\Java\jre1.5.0_04\bin\jusched.exe
C:\Program Files\Spybot - Search & Destroy\TeaTimer.exe
C:\Program Files\Nikon\NkView6\NkvMon.exe
C:\Program Files\Microsoft Office\Office\OSA.EXE
C:\Program Files\Microsoft Office\Office\FINDFAST.EXE
C:\WINDOWS\System32\svchost.exe
C:\Program Files\Internet Explorer\IEXPLORE.EXE
C:\Program Files\Yahoo!\Messenger\YPager.exe
C:\Documents and Settings\default\My Documents\Programs\HiJack This\hijackthis\HijackThis.exe
R1 - HKCU\Software\Microsoft\Internet Explorer\Main,Search Page = http://us.rd.yahoo.c...//www.yahoo.com
R0 - HKLM\Software\Microsoft\Internet Explorer\Main,Local Page = C:\WINDOWS\SYSTEM\blank.htm
O3 - Toolbar: Pa&nicware Pop-Up Stopper Pro - {B1E741E7-1E77-40D4-9FD8-51949B9CCBD0} - C:\PROGRAM FILES\PANICWARE\POP-UP STOPPER PRO\POPUPPRO.DLL
O4 - HKLM\..\Run: [SystemTray] SysTray.Exe
O4 - HKLM\..\Run: [Microsoft Works Update Detection] C:\Program Files\Microsoft Works\WkDetect.exe
O4 - HKLM\..\Run: [NeroFilterCheck] C:\WINDOWS\system32\NeroCheck.exe
O4 - HKLM\..\Run: [Zone Labs Client] C:\Program Files\Zone Labs\ZoneAlarm\zlclient.exe
O4 - HKLM\..\Run: [SunJavaUpdateSched] C:\Program Files\Java\jre1.5.0_04\bin\jusched.exe
O4 - HKCU\..\Run: [SpybotSD TeaTimer] C:\Program Files\Spybot - Search & Destroy\TeaTimer.exe
O4 - Global Startup: NkvMon.exe.lnk = C:\Program Files\Nikon\NkView6\NkvMon.exe
O4 - Global Startup: Adobe Gamma Loader.lnk = C:\Program Files\Common Files\Adobe\Calibration\Adobe Gamma Loader.exe
O4 - Global Startup: Office Startup.lnk = C:\Program Files\Microsoft Office\Office\OSA.EXE
O4 - Global Startup: Microsoft Find Fast.lnk = C:\Program Files\Microsoft Office\Office\FINDFAST.EXE
O8 - Extra context menu item: &Define - C:\Program Files\Common Files\Microsoft Shared\Reference 2001\A\ERS_DEF.HTM
O8 - Extra context menu item: Display All Images with Full Quality - res://C:\PROGRAM FILES\NETZERO\QSACC\appres.dll/228
O8 - Extra context menu item: Display Image with Full Quality - res://C:\PROGRAM FILES\NETZERO\QSACC\appres.dll/227
O8 - Extra context menu item: Look Up in &Encyclopedia - C:\Program Files\Common Files\Microsoft Shared\Reference 2001\A\ERS_ENC.HTM
O9 - Extra button: Encarta Encyclopedia - {2FDEF853-0759-11D4-A92E-006097DBED37} - C:\Program Files\Common Files\Microsoft Shared\Reference 2001\A\ERS_ENC.HTM
O9 - Extra 'Tools' menuitem: Encarta Encyclopedia - {2FDEF853-0759-11D4-A92E-006097DBED37} - C:\Program Files\Common Files\Microsoft Shared\Reference 2001\A\ERS_ENC.HTM
O9 - Extra button: Define - {5DA9DE80-097A-11D4-A92E-006097DBED37} - C:\Program Files\Common Files\Microsoft Shared\Reference 2001\A\ERS_DEF.HTM
O9 - Extra 'Tools' menuitem: Define - {5DA9DE80-097A-11D4-A92E-006097DBED37} - C:\Program Files\Common Files\Microsoft Shared\Reference 2001\A\ERS_DEF.HTM
O9 - Extra button: Yahoo! Messenger - {E5D12C4E-7B4F-11D3-B5C9-0050045C3C96} - C:\PROGRAM FILES\YAHOO!\MESSENGER\YPAGER.EXE
O9 - Extra 'Tools' menuitem: Yahoo! Messenger - {E5D12C4E-7B4F-11D3-B5C9-0050045C3C96} - C:\PROGRAM FILES\YAHOO!\MESSENGER\YPAGER.EXE
O16 - DPF: {200B3EE9-7242-4EFD-B1E4-D97EE825BA53} (VerifyGMN Class) - http://h20270.www2.h...staller_gmn.cab
O16 - DPF: {4C39376E-FA9D-4349-BACC-D305C1750EF3} (EPUImageControl Class) - http://tools.ebayimg...l_v1-0-3-24.cab
O16 - DPF: {6414512B-B978-451D-A0D8-FCFDF33E833C} (WUWebControl Class) - http://update.micros...b?1121918189004
O16 - DPF: {6E32070A-766D-4EE6-879C-DC1FA91D2FC3} (MUWebControl Class) - http://update.micros...b?1123469099918
O16 - DPF: {9B03C5F1-F5AB-47EE-937D-A8EDA626F876} (Anonymizer Anti-Spyware Scanner) - http://download.zone...ctor/WebAAS.cab
O16 - DPF: {D719897A-B07A-4C0C-AEA9-9B663A28DFCB} (iTunesDetector Class) - http://ax.phobos.app.../ITDetector.cab
O16 - DPF: {E9348280-2D74-4933-BE25-73D946926795} (DeviceEnum Class) - http://h20270.www2.h...cdetection3.cab
O16 - DPF: {EB387D2F-E27B-4D36-979E-847D1036C65D} (QDiagHUpdateObj Class) - http://h30043.www3.h.../qdiagh.cab?326
O20 - Winlogon Notify: OEMRunOnce - C:\WINDOWS\system32\uarvpa.dll
O23 - Service: CA ISafe (CAISafe) - Computer Associates International, Inc. - C:\WINDOWS\System32\ZoneLabs\isafe.exe
O23 - Service: TrueVector Internet Monitor (vsmon) - Zone Labs, LLC - C:\WINDOWS\SYSTEM32\ZONELABS\vsmon.exe
ewido security suite - Scan report
---------------------------------------------------------
+ Created on: 1:09:58 AM, 8/8/2005
+ Report-Checksum: 8B1B4762
+ Scan result:
HKU\.DEFAULT\Software\Need2Find -> Spyware.Need2Find : Cleaned with backup
HKU\.DEFAULT\Software\Need2Find\bar -> Spyware.Need2Find : Cleaned with backup
HKU\S-1-5-19\Software\Need2Find -> Spyware.Need2Find : Cleaned with backup
HKU\S-1-5-19\Software\Need2Find\bar -> Spyware.Need2Find : Cleaned with backup
HKU\S-1-5-19\Software\RX Toolbar -> Spyware.RXToolbar : Cleaned with backup
HKU\S-1-5-20\Software\Need2Find -> Spyware.Need2Find : Cleaned with backup
HKU\S-1-5-20\Software\Need2Find\bar -> Spyware.Need2Find : Cleaned with backup
HKU\S-1-5-20\Software\RX Toolbar -> Spyware.RXToolbar : Cleaned with backup
HKU\S-1-5-18\Software\Need2Find -> Spyware.Need2Find : Cleaned with backup
HKU\S-1-5-18\Software\Need2Find\bar -> Spyware.Need2Find : Cleaned with backup
::Report End
---------------------------------------------------------
ewido security suite - Connection report
---------------------------------------------------------
+ Created on: 1:13:16 AM, 8/8/2005
+ Report-Checksum: B1236D6C
TCP 0.0.0.0:135 0.0.0.0:0 LISTENING
TCP 0.0.0.0:445 0.0.0.0:0 LISTENING
TCP 0.0.0.0:1025 0.0.0.0:0 LISTENING
TCP 0.0.0.0:1032 0.0.0.0:0 LISTENING
TCP 0.0.0.0:1033 0.0.0.0:0 LISTENING
TCP 0.0.0.0:1034 0.0.0.0:0 LISTENING
TCP 0.0.0.0:1187 0.0.0.0:0 LISTENING
TCP 0.0.0.0:2675 0.0.0.0:0 LISTENING
TCP 0.0.0.0:2677 0.0.0.0:0 LISTENING
TCP 0.0.0.0:2682 0.0.0.0:0 LISTENING
TCP 0.0.0.0:5000 0.0.0.0:0 LISTENING
TCP 0.0.0.0:5101 0.0.0.0:0 LISTENING
TCP 127.0.0.1:1029 0.0.0.0:0 LISTENING
TCP 127.0.0.1:1029 127.0.0.1:1034 ESTABLISHED
TCP 127.0.0.1:1030 0.0.0.0:0 LISTENING
TCP 127.0.0.1:1030 127.0.0.1:1033 ESTABLISHED
TCP 127.0.0.1:1033 127.0.0.1:1030 ESTABLISHED
TCP 127.0.0.1:1034 127.0.0.1:1029 ESTABLISHED
TCP 192.168.1.96:139 0.0.0.0:0 LISTENING
TCP 192.168.1.96:1187 69.45.79.144:80 CLOSE_WAIT
TCP 192.168.1.96:2671 69.45.79.152:80 TIME_WAIT
TCP 192.168.1.96:2673 69.45.79.152:80 TIME_WAIT
TCP 192.168.1.96:2675 216.155.193.151:5050 ESTABLISHED
TCP 192.168.1.96:2677 69.45.79.152:80 ESTABLISHED
TCP 192.168.1.96:2682 216.136.232.45:80 SYN_SENT
UDP 0.0.0.0:135
UDP 0.0.0.0:445
UDP 0.0.0.0:500
UDP 0.0.0.0:1026
UDP 0.0.0.0:1028
UDP 0.0.0.0:1064
UDP 0.0.0.0:1071
UDP 0.0.0.0:1761
UDP 0.0.0.0:2058
UDP 0.0.0.0:2109
UDP 0.0.0.0:2119
UDP 0.0.0.0:2334
UDP 127.0.0.1:123
UDP 127.0.0.1:1045
UDP 127.0.0.1:1655
UDP 127.0.0.1:1900
UDP 192.168.1.96:123
UDP 192.168.1.96:137
UDP 192.168.1.96:138
UDP 192.168.1.96:1900
Please, before I <shotgun>my computer</shotgun>, someone please give me guidance.
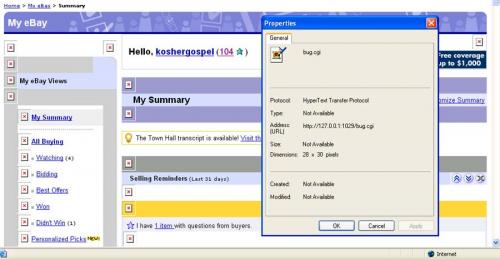
Zone Alarm Security Suite catches a Canbede.J virus running. If I end the process rundll32.exe it goes crazy catching this thing.
ANy help in killing this is so greatly appreciated. Many thanks in advance - Chris
Edited by rhythmco, 07 August 2005 - 11:21 PM.

 This topic is locked
This topic is locked













 Sign In
Sign In Create Account
Create Account

