Hello again,
Here is the info you asked for:
HJT-
StartupList report, 8/31/2005, 5:48:54 AM
StartupList version: 1.52.2
Started from : C:\Documents and Settings\KC\My Documents\My Computer Stuff\HijackThis.EXE
Detected: Windows XP SP1 (WinNT 5.01.2600)
Detected: Internet Explorer v6.00 SP1 (6.00.2800.1106)
* Using default options
==================================================
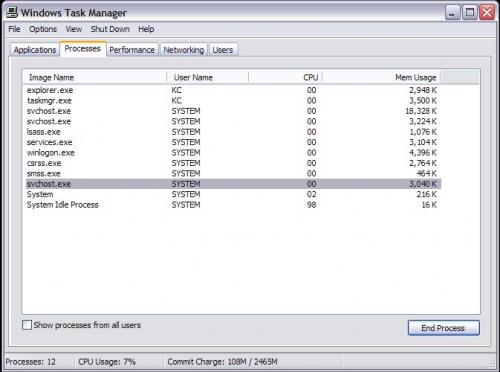
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\System32\Ati2evxx.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\system32\spoolsv.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\Explorer.EXE
C:\Program Files\ewido\security suite\ewidoctrl.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\System32\wuauclt.exe
C:\Program Files\Internet Explorer\iexplore.exe
C:\Documents and Settings\KC\My Documents\My Computer Stuff\HijackThis.exe
--------------------------------------------------
Checking Windows NT UserInit:
[HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon]
UserInit = C:\WINDOWS\system32\userinit.exe,
--------------------------------------------------
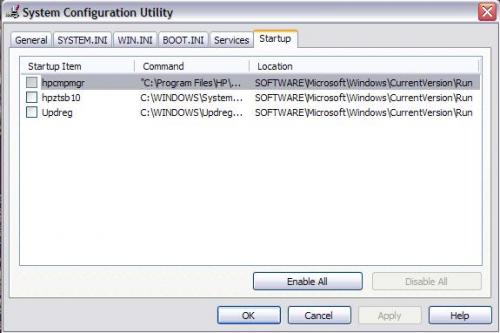
Autorun entries from Registry:
HKLM\Software\Microsoft\Windows\CurrentVersion\Run
UpdReg = C:\WINDOWS\Updreg.exe
NaturalPoint =
--------------------------------------------------
Shell & screensaver key from C:\WINDOWS\SYSTEM.INI:
Shell=*INI section not found*
SCRNSAVE.EXE=*INI section not found*
drivers=*INI section not found*
Shell & screensaver key from Registry:
Shell=Explorer.exe
SCRNSAVE.EXE=C:\WINDOWS\System32\sspipes.scr
drivers=*Registry value not found*
Policies Shell key:
HKCU\..\Policies: Shell=*Registry key not found*
HKLM\..\Policies: Shell=*Registry value not found*
--------------------------------------------------
Enumerating Browser Helper Objects:
(no name) - C:\Program Files\Adobe\Acrobat 7.0\ActiveX\AcroIEHelper.dll - {06849E9F-C8D7-4D59-B87D-784B7D6BE0B3}
(no name) - C:\PROGRA~1\SPYBOT~1\SDHelper.dll - {53707962-6F74-2D53-2644-206D7942484F}
--------------------------------------------------
Enumerating Download Program Files:
[SdcNetCheckCtl Class]
InProcServer32 = C:\Program Files\support.com\bin\sdcnetcheck.dll
CODEBASE =
http://activex.micro...jects/ocget.dll[UniInstaller Class]
InProcServer32 = C:\WINDOWS\Downloaded Program Files\UniInstaller.dll
CODEBASE =
http://www.webcamnow...e-installer.cab[HouseCall Control]
InProcServer32 = C:\WINDOWS\DOWNLO~1\xscan60.ocx
CODEBASE =
http://housecall60.t...all/xscan60.cab[Creative Software AutoUpdate]
InProcServer32 = C:\WINDOWS\DOWNLO~1\CTSUEng.ocx
CODEBASE =
http://www.creative....007/CTSUEng.cab[Windows Genuine Advantage Validation Tool]
InProcServer32 = C:\WINDOWS\System32\LegitCheckControl.DLL
CODEBASE =
http://go.microsoft....k/?linkid=39204[Symantec AntiVirus scanner]
InProcServer32 = C:\WINDOWS\Downloaded Program Files\avsniff.dll
CODEBASE =
http://security.syma...bin/AvSniff.cab[MSN Photo Upload Tool]
InProcServer32 = C:\WINDOWS\Downloaded Program Files\MsnPUpld.dll
CODEBASE =
http://by22fd.bay22....es/MsnPUpld.cab[WUWebControl Class]
InProcServer32 = C:\WINDOWS\System32\wuweb.dll
CODEBASE =
http://update.micros...b?1120645783281[Symantec RuFSI Utility Class]
InProcServer32 = C:\WINDOWS\Downloaded Program Files\rufsi.dll
CODEBASE =
http://security.syma...n/bin/cabsa.cab[MSN File Upload Control]
InProcServer32 = C:\WINDOWS\DOWNLO~1\MsnUpld.dll
CODEBASE =
http://sc.groups.msn...eUC/MsnUpld.cab[WebCam Control]
InProcServer32 = C:\WINDOWS\DOWNLO~1\ACTIVE~1.OCX
CODEBASE =
http://www.webcamnow...tiveXWebCam.cab[{9F1C11AA-197B-4942-BA54-47A8489BB47F}]
CODEBASE =
http://v4.windowsupd...8135.6785069444[MsnMessengerSetupDownloadControl Class]
InProcServer32 = C:\WINDOWS\Downloaded Program Files\MsnMessengerSetupDownloader.ocx
CODEBASE =
http://messenger.msn...pDownloader.cab[Shockwave Flash Object]
InProcServer32 = C:\WINDOWS\System32\macromed\flash\Flash.ocx
CODEBASE =
http://download.macr...ash/swflash.cab[McFreeScan Class]
InProcServer32 = C:\WINDOWS\McAfee.com\FreeScan\mcfscan.dll
CODEBASE =
http://download.mcaf...566/mcfscan.cab[MSN Chat Control 4.5]
InProcServer32 = C:\WINDOWS\Downloaded Program Files\MSNChat45.ocx
CODEBASE =
http://chat.msn.com/bin/msnchat45.cab[Creative Software AutoUpdate Support Package]
InProcServer32 = C:\WINDOWS\DOWNLO~1\CTPID.ocx
CODEBASE =
http://www.creative....15008/CTPID.cab--------------------------------------------------
Enumerating ShellServiceObjectDelayLoad items:
PostBootReminder: C:\WINDOWS\system32\SHELL32.dll
CDBurn: C:\WINDOWS\system32\SHELL32.dll
WebCheck: C:\WINDOWS\System32\webcheck.dll
SysTray: C:\WINDOWS\System32\stobject.dll
--------------------------------------------------
End of report, 5,921 bytes
Report generated in 0.062 seconds
Command line options:
/verbose - to add additional info on each section
/complete - to include empty sections and unsuspicious data
/full - to include several rarely-important sections
/force9x - to include Win9x-only startups even if running on WinNT
/forcent - to include WinNT-only startups even if running on Win9x
/forceall - to include all Win9x and WinNT startups, regardless of platform
/history - to list version history only
SR-
"Silent Runners.vbs", revision 40.1,
http://www.silentrunners.org/Operating System: Windows XP
Output limited to non-default values, except where indicated by "{++}"
Startup items buried in registry:
---------------------------------
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\ {++}
"UpdReg" = "C:\WINDOWS\Updreg.exe" ["Creative Technology Ltd."]
"NaturalPoint" = (empty string)
HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\Browser Helper Objects\
{06849E9F-C8D7-4D59-B87D-784B7D6BE0B3}\(Default) = "AcroIEHlprObj Class" [from CLSID]
-> {CLSID}\InProcServer32\(Default) = "C:\Program Files\Adobe\Acrobat 7.0\ActiveX\AcroIEHelper.dll" ["Adobe Systems Incorporated"]
{53707962-6F74-2D53-2644-206D7942484F}\(Default) = (no title provided)
-> {CLSID}\InProcServer32\(Default) = "C:\PROGRA~1\SPYBOT~1\SDHelper.dll" ["Safer Networking Limited"]
HKLM\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Approved\
"{42071714-76d4-11d1-8b24-00a0c9068ff3}" = "Display Panning CPL Extension"
-> {CLSID}\InProcServer32\(Default) = "deskpan.dll" [file not found]
"{88895560-9AA2-1069-930E-00AA0030EBC8}" = "HyperTerminal Icon Ext"
-> {CLSID}\InProcServer32\(Default) = "C:\WINDOWS\System32\hticons.dll" ["Hilgraeve, Inc."]
"{5E44E225-A408-11CF-B581-008029601108}" = "Adaptec DirectCD Shell Extension"
-> {CLSID}\InProcServer32\(Default) = "C:\PROGRA~1\Adaptec\EASYCD~1\DirectCD\Shellex.dll" ["Roxio"]
"{eb9ebda0-b3e7-11cf-81c9-0000c0aa665f}" = "FTP Explorer Shell Extension"
-> {CLSID}\InProcServer32\(Default) = "ftpxext.dll" ["FTPx Corp."]
"{640167b4-59b0-47a6-b335-a6b3c0695aea}" = "Portable Media Devices"
-> {CLSID}\InProcServer32\(Default) = "C:\WINDOWS\System32\Audiodev.dll" [MS]
"{cc86590a-b60a-48e6-996b-41d25ed39a1e}" = "Portable Media Devices Menu"
-> {CLSID}\InProcServer32\(Default) = "C:\WINDOWS\System32\Audiodev.dll" [MS]
HKLM\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellExecuteHooks\
INFECTION WARNING! "{54D9498B-CF93-414F-8984-8CE7FDE0D391}" = "ewido shell guard"
-> {CLSID}\InProcServer32\(Default) = "C:\Program Files\ewido\security suite\shellhook.dll" ["TODO: <Firmenname>"]
HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Notify\
INFECTION WARNING! AtiExtEvent\DLLName = "Ati2evxx.dll" ["ATI Technologies Inc."]
HKLM\Software\Classes\*\shellex\ContextMenuHandlers\
TDS-3\(Default) = "{E8ADA3E1-CE9B-44A0-A165-997304EF4E18}"
-> {CLSID}\InProcServer32\(Default) = "C:\WINDOWS\System32\tds3shl.dll" [empty string]
HKLM\Software\Classes\Directory\shellex\ContextMenuHandlers\
TDS-3\(Default) = "{E8ADA3E1-CE9B-44A0-A165-997304EF4E18}"
-> {CLSID}\InProcServer32\(Default) = "C:\WINDOWS\System32\tds3shl.dll" [empty string]
Active Desktop and Wallpaper:
-----------------------------
Active Desktop is enabled at this entry:
HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\ShellState
HKCU\Software\Microsoft\Internet Explorer\Desktop\General\
"Wallpaper" = "C:\Documents and Settings\KC\Local Settings\Application Data\Microsoft\Wallpaper1.bmp"
Active Desktop web content:
HKCU\Software\Microsoft\Internet Explorer\Desktop\Components\0\
"FriendlyName" = ""
"Source" = "file:///C:/DOCUME~1/KC/LOCALS~1/Temp/msoclip1/01/clip_image002.jpg"
"SubscribedURL" = "file:///C:/DOCUME~1/KC/LOCALS~1/Temp/msoclip1/01/clip_image002.jpg"
Enabled Screen Saver:
---------------------
HKCU\Control Panel\Desktop\
HKCU\Software\Microsoft\Internet Explorer\Desktop\Components\1\
"SCRNSAVE.EXE" = "C:\WINDOWS\System32\sspipes.scr" [MS]
Winsock2 Service Provider DLLs:
-------------------------------
Namespace Service Providers
HKLM\System\CurrentControlSet\Services\Winsock2\Parameters\NameSpace_Catalog5\Catalog_Entries\ {++}
000000000001\LibraryPath = "%SystemRoot%\System32\mswsock.dll" [MS]
000000000002\LibraryPath = "%SystemRoot%\System32\winrnr.dll" [MS]
000000000003\LibraryPath = "%SystemRoot%\System32\mswsock.dll" [MS]
Transport Service Providers
HKLM\System\CurrentControlSet\Services\Winsock2\Parameters\Protocol_Catalog9\Catalog_Entries\ {++}
0000000000##\PackedCatalogItem (contains) DLL [Company Name], (at) ## range:
%SystemRoot%\system32\mswsock.dll [MS], 01 - 03, 06 - 13
%SystemRoot%\system32\rsvpsp.dll [MS], 04 - 05
Miscellaneous IE Hijack Points
------------------------------
C:\WINDOWS\INF\IERESET.INF (used to "Reset Web Settings")
Added lines (compared with English-language version):
[Strings]: START_PAGE_URL=http://www.falcon-nw.com
Missing lines (compared with English-language version):
[Strings]: 1 line
Running Services (Display Name, Service Name, Path {Service DLL}):
------------------------------------------------------------------
Ati HotKey Poller, Ati HotKey Poller, "C:\WINDOWS\System32\Ati2evxx.exe" ["ATI Technologies Inc."]
ewido security suite control, ewido security suite control, "C:\Program Files\ewido\security suite\ewidoctrl.exe" ["ewido networks"]
Windows User Mode Driver Framework, UMWdf, "C:\WINDOWS\System32\wdfmgr.exe" [MS]
----------
+ This report excludes default entries except where indicated.
+ To see *everywhere* the script checks and *everything* it finds,
launch it from a command prompt or a shortcut with the -all parameter.
+ To search all directories of local fixed drives for DESKTOP.INI
DLL launch points and all Registry CLSIDs for dormant Explorer Bars,
use the -supp parameter or answer "No" at the first message box.
---------- (total run time: 27 seconds, including 18 seconds for message boxes)
Thanks!

 This topic is locked
This topic is locked













 Sign In
Sign In Create Account
Create Account

