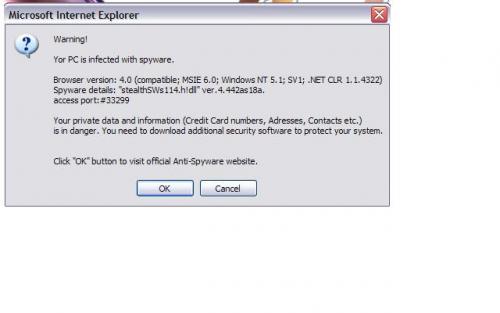
I get a spyware warning message whenever I start the computer.
The message snapshot is attached with this message (jpeg file).
The Hijackthis log is as follows:
Can you please help me out !!
--------------------
Logfile of HijackThis v1.99.1
Scan saved at 12:53:48 PM, on 12/4/2005
Platform: Windows XP SP2 (WinNT 5.01.2600)
MSIE: Internet Explorer v6.00 SP2 (6.00.2900.2180)
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\Ati2evxx.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\system32\ACS.exe
c:\Program Files\Common Files\Symantec Shared\ccSetMgr.exe
c:\Program Files\Common Files\Symantec Shared\ccEvtMgr.exe
C:\WINDOWS\system32\spoolsv.exe
C:\WINDOWS\Explorer.EXE
C:\PROGRA~1\COMMON~1\AOL\ACS\AOLacsd.exe
C:\WINDOWS\system32\mssearchnet.exe
C:\WINDOWS\system32\nvctrl.exe
C:\Program Files\TOSHIBA\E-KEY\CeEKey.exe
C:\Program Files\TOSHIBA\Power Management\CePMTray.exe
C:\Program Files\TOSHIBA\TouchPad\TPTray.exe
C:\WINDOWS\system32\dla\tfswctrl.exe
C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe
C:\Program Files\Toshiba\Power Management\CeEPwrSvc.exe
C:\Program Files\ltmoh\Ltmoh.exe
C:\WINDOWS\AGRSMMSG.exe
C:\Program Files\TOSHIBA\ConfigFree\CFSvcs.exe
C:\Program Files\Apoint2K\Apoint.exe
C:\Program Files\TOSHIBA\Touch and Launch\PadExe.exe
C:\Program Files\Common Files\Symantec Shared\ccApp.exe
C:\WINDOWS\system32\DVDRAMSV.exe
C:\Program Files\TOSHIBA\ConfigFree\NDSTray.exe
C:\toshiba\ivp\ism\pinger.exe
C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE
C:\Program Files\support.com\bin\tgcmd.exe
C:\Program Files\HP\HP Software Update\HPWuSchd2.exe
C:\Program Files\QuickTime\qttask.exe
C:\Program Files\Real\RealPlayer\RealPlay.exe
c:\Program Files\Norton AntiVirus\navapsvc.exe
C:\Program Files\TOSHIBA\TOSCDSPD\toscdspd.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\Messenger\msmsgs.exe
C:\Program Files\HP\Digital Imaging\bin\hpqtra08.exe
C:\Program Files\Apoint2K\Apntex.exe
C:\WINDOWS\system32\RAMASST.exe
c:\Program Files\Norton AntiVirus\SAVScan.exe
C:\WINDOWS\system32\svchost.exe
c:\Toshiba\Ivp\Swupdate\swupdtmr.exe
C:\Program Files\HP\Digital Imaging\bin\hpqgalry.exe
C:\Program Files\Linksys\Wireless-G Notebook Adapter\OdHost.exe
C:\Program Files\Common Files\Symantec Shared\Security Center\SymWSC.exe
C:\Program Files\Linksys\Wireless-G Notebook Adapter\WPC54Cfg.exe
C:\Program Files\Internet Explorer\iexplore.exe
C:\WINDOWS\system32\wuauclt.exe
C:\WINDOWS\system32\1024\ld6FC7.tmp
C:\DOCUME~1\Admin\LOCALS~1\Temp\mjgmjpmd.exe
C:\DOCUME~1\Admin\LOCALS~1\Temp\bnlbjpmd.exe
C:\Documents and Settings\Admin\Desktop\HijackThis.exe
R1 - HKCU\Software\Microsoft\Internet Explorer\Main,Search Bar = http://www.toshiba.com/search
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL = http://toshibadirect.com/
R0 - HKLM\Software\Microsoft\Internet Explorer\Main,Start Page = http://www.comcast.net/
R1 - HKCU\Software\Microsoft\Internet Connection Wizard,ShellNext = http://toshibadirect.com/
O2 - BHO: HomepageBHO - {3e9b951e-6f72-431b-82cf-4a9fbf2f53bc} - C:\WINDOWS\system32\hpB9DA.tmp
O3 - Toolbar: AOL Toolbar - {4982D40A-C53B-4615-B15B-B5B5E98D167C} - C:\Program Files\AOL Toolbar\toolbar.dll
O3 - Toolbar: Norton AntiVirus - {42CDD1BF-3FFB-4238-8AD1-7859DF00B1D6} - c:\Program Files\Norton AntiVirus\NavShExt.dll (file missing)
O3 - Toolbar: &Google - {2318C2B1-4965-11d4-9B18-009027A5CD4F} - c:\program files\google\googletoolbar2.dll
O3 - Toolbar: SecurityToolbar - {736b5468-bdad-41be-92d0-22ae2ddf7bcb} - C:\Program Files\Security Toolbar\Security Toolbar.dll
O4 - HKLM\..\Run: [CeEKEY] C:\Program Files\TOSHIBA\E-KEY\CeEKey.exe
O4 - HKLM\..\Run: [CeEPOWER] C:\Program Files\TOSHIBA\Power Management\CePMTray.exe
O4 - HKLM\..\Run: [TPNF] C:\Program Files\TOSHIBA\TouchPad\TPTray.exe
O4 - HKLM\..\Run: [dla] C:\WINDOWS\system32\dla\tfswctrl.exe
O4 - HKLM\..\Run: [ATIPTA] C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe
O4 - HKLM\..\Run: [LtMoh] C:\Program Files\ltmoh\Ltmoh.exe
O4 - HKLM\..\Run: [AGRSMMSG] AGRSMMSG.exe
O4 - HKLM\..\Run: [Apoint] C:\Program Files\Apoint2K\Apoint.exe
O4 - HKLM\..\Run: [PadTouch] C:\Program Files\TOSHIBA\Touch and Launch\PadExe.exe
O4 - HKLM\..\Run: [ccApp] "c:\Program Files\Common Files\Symantec Shared\ccApp.exe"
O4 - HKLM\..\Run: [NDSTray.exe] NDSTray.exe
O4 - HKLM\..\Run: [Pinger] c:\toshiba\ivp\ism\pinger.exe /run
O4 - HKLM\..\Run: [Symantec NetDriver Monitor] C:\PROGRA~1\SYMNET~1\SNDMon.exe /Consumer
O4 - HKLM\..\Run: [tgcmd] "C:\Program Files\support.com\bin\tgcmd.exe" /server
O4 - HKLM\..\Run: [HP Software Update] "C:\Program Files\HP\HP Software Update\HPWuSchd2.exe"
O4 - HKLM\..\Run: [QuickTime Task] "C:\Program Files\QuickTime\qttask.exe" -atboottime
O4 - HKLM\..\Run: [RealTray] C:\Program Files\Real\RealPlayer\RealPlay.exe SYSTEMBOOTHIDEPLAYER
O4 - HKCU\..\Run: [TOSCDSPD] C:\Program Files\TOSHIBA\TOSCDSPD\toscdspd.exe
O4 - HKCU\..\Run: [ctfmon.exe] C:\WINDOWS\system32\ctfmon.exe
O4 - HKCU\..\Run: [MSMSGS] "C:\Program Files\Messenger\msmsgs.exe" /background
O4 - Global Startup: HP Digital Imaging Monitor.lnk = C:\Program Files\HP\Digital Imaging\bin\hpqtra08.exe
O4 - Global Startup: HP Image Zone Fast Start.lnk = C:\Program Files\HP\Digital Imaging\bin\hpqthb08.exe
O4 - Global Startup: RAMASST.lnk = C:\WINDOWS\system32\RAMASST.exe
O4 - Global Startup: Wireless-G Notebook Adapter Utility.lnk = C:\Program Files\Linksys\Wireless-G Notebook Adapter\Startup.exe
O8 - Extra context menu item: &AOL Toolbar search - res://C:\Program Files\AOL Toolbar\toolbar.dll/SEARCH.HTML
O8 - Extra context menu item: E&xport to Microsoft Excel - res://C:\PROGRA~1\MICROS~2\OFFICE11\EXCEL.EXE/3000
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\j2re1.4.2_05\bin\npjpi142_05.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\j2re1.4.2_05\bin\npjpi142_05.dll
O9 - Extra button: AOL Toolbar - {4982D40A-C53B-4615-B15B-B5B5E98D167C} - C:\Program Files\AOL Toolbar\toolbar.dll
O9 - Extra 'Tools' menuitem: AOL Toolbar - {4982D40A-C53B-4615-B15B-B5B5E98D167C} - C:\Program Files\AOL Toolbar\toolbar.dll
O9 - Extra button: ComcastHSI - {669B269B-0D4E-41FB-A3D8-FD67CA94F646} - http://www.comcast.net/ (file missing)
O9 - Extra button: Support - {8828075D-D097-4055-AA02-2DBFA9D85E8A} - http://www.comcastsupport.com/ (file missing)
O9 - Extra button: Badanie - {92780B25-18CC-41C8-B9BE-3C9C571A8263} - C:\PROGRA~1\MICROS~2\OFFICE11\REFIEBAR.DLL
O9 - Extra button: Help - {97809617-3937-4F84-B335-9BB05EF1A8D4} - http://online.comcast.net/help/ (file missing)
O9 - Extra button: Real.com - {CD67F990-D8E9-11d2-98FE-00C0F0318AFE} - C:\WINDOWS\system32\Shdocvw.dll
O9 - Extra button: Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O9 - Extra 'Tools' menuitem: Windows Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O12 - Plugin for .spop: C:\Program Files\Internet Explorer\Plugins\NPDocBox.dll
O14 - IERESET.INF: START_PAGE_URL=http://www.toshiba.com
O23 - Service: Atheros Configuration Service (ACS) - Unknown owner - C:\WINDOWS\system32\ACS.exe
O23 - Service: AOL Connectivity Service (AOL ACS) - America Online, Inc. - C:\PROGRA~1\COMMON~1\AOL\ACS\AOLacsd.exe
O23 - Service: Ati HotKey Poller - Unknown owner - C:\WINDOWS\system32\Ati2evxx.exe
O23 - Service: Symantec Event Manager (ccEvtMgr) - Symantec Corporation - c:\Program Files\Common Files\Symantec Shared\ccEvtMgr.exe
O23 - Service: Symantec Password Validation (ccPwdSvc) - Symantec Corporation - c:\Program Files\Common Files\Symantec Shared\ccPwdSvc.exe
O23 - Service: Symantec Settings Manager (ccSetMgr) - Symantec Corporation - c:\Program Files\Common Files\Symantec Shared\ccSetMgr.exe
O23 - Service: CeEPwrSvc - COMPAL ELECTRONIC INC. - C:\Program Files\Toshiba\Power Management\CeEPwrSvc.exe
O23 - Service: ConfigFree Service (CFSvcs) - TOSHIBA CORPORATION - C:\Program Files\TOSHIBA\ConfigFree\CFSvcs.exe
O23 - Service: DVD-RAM_Service - Matsushita Electric Industrial Co., Ltd. - C:\WINDOWS\system32\DVDRAMSV.exe
O23 - Service: Norton AntiVirus Auto Protect Service (navapsvc) - Symantec Corporation - c:\Program Files\Norton AntiVirus\navapsvc.exe
O23 - Service: NICSer_WPC54G - Unknown owner - C:\Program Files\Linksys\Wireless-G Notebook Adapter\NICServ.exe
O23 - Service: Pml Driver HPZ12 - HP - C:\WINDOWS\system32\HPZipm12.exe
O23 - Service: SAVScan - Symantec Corporation - c:\Program Files\Norton AntiVirus\SAVScan.exe
O23 - Service: ScriptBlocking Service (SBService) - Symantec Corporation - C:\PROGRA~1\COMMON~1\SYMANT~1\SCRIPT~1\SBServ.exe
O23 - Service: Symantec Network Drivers Service (SNDSrvc) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\SNDSrvc.exe
O23 - Service: Swupdtmr - Unknown owner - c:\Toshiba\Ivp\Swupdate\swupdtmr.exe
O23 - Service: SymWMI Service (SymWSC) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\Security Center\SymWSC.exe
----------------------------------

 This topic is locked
This topic is locked













 Sign In
Sign In Create Account
Create Account

