Dawn of the 64-bit Rootkit Era
 A recent Prevx blogpost details information on the new TDL3 rootkit, which they have deemed, “the first x64 compatible kernel mode rootkit infection in the wild.” Followed with more information in a post today.
A recent Prevx blogpost details information on the new TDL3 rootkit, which they have deemed, “the first x64 compatible kernel mode rootkit infection in the wild.” Followed with more information in a post today.
While much of the information presented by Prevx is highly technical, there are some takeaways for the average user. Most importantly, this 64-bit infection requires administrator privileges. The best option is to run as a standard user, but it also won’t run if User Account Control (or UAC) is activated. I run as standard user, and there is really no reason for your account to run as administrator.
Second, this infection is being spread mostly through porn sites, and exploited sites. While it may seem easy to avoid porn sites, almost any site can be exploited. However, exploited sites almost always rely on a unpatched system vulnerabilities to download and run their payload. A common method relies on unpatched Internet Explorer to download, and unpatched Adobe Acrobat to run. Run Windows Update. Update Adobe products (Reader, Flash). Don’t be a Microsoft rebel who refuses to run updates out of fear for what they may do. You should be fearing what may happen without them. In the past few weeks, Microsoft has patched an unusually large number of critical bugs.
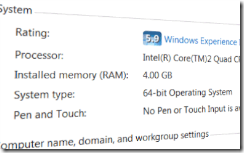
While 64-bit versions of Windows Vista and Windows 7 are more secure, we are seeing more malware designed to work with 64-bit operating systems. This is because 64-bit operating system have reached the mainstream, and their market share makes them an attractive target. According to Steam, 35% of hardware surveyed runs a 64-bit Windows OS. The majority of systems sold at retail are now 64-bit. Windows Vista and Windows 7 have advanced security features like Digital Signature Checking, Kernel Patch Protection, and PatchGuard. The preferred method for bypassing these protections is to infect the Master Boot Record, or MBR. These MBR infections (including TDSS, Whistler and Stoned v2) can be difficult to remove, and sometimes evolve almost daily. It’s best to avoid them in the first place.
Are you infected with a TDL3 rootkit? Because of the nature of rootkits, they hide well, and can be difficult to identify. The most common symptom is search redirects (Google, Bing, Yahoo). Free help is available our virus, spyware & malware removal forum. We recommend you start with our Malware Cleaning Guide.

