State Sponsored Malware, the New Normal?
Computer security is hard. Stopping state-sponsored malware might prove impossible. Consider this recent example of a security breach that hasn’t yet been reported to be state-sponsored, but has the hallmarks. Cloudflare is a service that promises to make sites faster and more secure. Recently one of their clients had their DNS records changed. The incident report reveals a lengthy and complex attack involving redirected voicemail, tricked email account recovery, and a flaw in Google Apps two-factor authentication. What if the ultimate target was not in fact the CloudFlare client, but rather some victim who could be vulnerable to exploitation through the CloudFlare customer compromise? How could this victim have prevented the attack, or even known about it?
The first viruses were written as a prank. Later virus writers were motivated by the attention they received. More recently, malware has been written for profit, often with the support of organized crime. With the increased organization and support, has come some impressive pieces of malware. TDSS/TDL4, and ZeroAccess rootkits are invasive, widespread and difficult to remove. While for-profit malware uses some clever tricks, state-sponsored Stuxnet and Flame bring malware development to an entirely new level.
Stuxnet and Flame are large, complex programs requiring thousands of man hours and millions of dollars to develop. Maybe most impressive is their use of zero-day, or unknown vulnerabilities. A couple of days ago, Flame prompted Microsoft to issue an emergency security update. Not because of what Flame might do, but what other attackers and malware might do with this door opened by Flame’s method of attack. 900 million computers are connect to Windows Update, and this vulnerability could have allowed malware to spread via it.
Despite collateral damage potential to almost one billion Windows users in this example, state-sponsored malware remains attractive to governments because there are no boots on the ground, no civilian casualties, and the cost is lower than a single cruise missile. When done correctly, it should also be undetectable, and leave no trace. Stuxnet and Flame were only discovered because of mistakes.
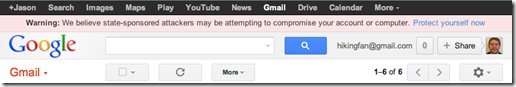
Just how common is state-sponsored malware and attack? Apparently, widespread enough that Google started issuing security warnings for it today (image at top of post):
Warning: We believe state-sponsored attackers may be attempting to compromise your account or computer. Protect yourself now.
What does Google mean by “state-sponsored attackers”? Most likely it means, “we’re pretty sure it’s China, but it could be Iran or Syria”. Or in other words, a foreign government is trying to gain access to your account.
How can you secure your account now? Google recommends you have a good password, use 2-factor authentication, and be careful about clicking on any log in links. If you use Gmail, or Google Apps, you really should take advantage of 2-step verification – today. If you’ve supplied Google with a backup email, be sure that account also has 2-step verification. Google Authenticator even allows you to create codes on Android, iPhone and Blackberry devices whether or not you have an internet connection, or mobile service.
Are we entering a new cold war era of sustained tension with the internet as the potential battlefield? Stuxnet’s high value target was a nuclear plant. More recently, Flame appears targeted toward general espionage. Many state-sponsored attacks have been reported against US Fortune 500 companies. There were likely many more attacks unreported. Is your company, or your data the next target of a state-sponsored attack?
“My greatest fear,” Clarke says, “is that, rather than having a cyber-Pearl Harbor event, we will instead have this death of a thousand cuts. Where we lose our competitiveness by having all of our research and development stolen by the Chinese. And we never really see the single event that makes us do something about it. That it’s always just below our pain threshold. That company after company in the United States spends millions, hundreds of millions, in some cases billions of dollars on R&D and that information goes free to China….After a while you can’t compete.”
Richard Clarke via Smithsonian Magazine