With wireless internet taking over our lives, internet cables have become a rare sight. Today, what has been a breakthrough, cutting edge discovery just several years ago, is being utilized by most of us every day. It’s called Wireless LAN (otherwise referred to as WiFi, or WLAN) and while it did bring about a revolution in the way we access the internet, it doesn’t come without drawbacks.
Unlike a traditional, wired internet connection, Wireless LAN is transmitted through the air – and thus, anyone with the proper equipment can intercept it. In the best case scenario, someone steals your internet connection. But in the worst case, sensitive data may be intercepted and stolen.
So, just how do you make your wireless internet activity safer? How do you secure your connection? Here’s how.
Secure your wireless connection
If you connect to the internet wirelessly, you have a router. This device allows several wireless connections at a time. There are several methods to secure your home or business connection. They can be used separately or best – together, for ultimate protection. Note: Refer to your router’s user manual to determine the exact procedures needed to change the various settings mentioned in this article. They may vary from router to router.
MAC filtering
MAC, not to confuse with Apple’s operating system, is an acronym which stands for Media Access Control. A unique MAC address is assigned to network adapters, in our case, in order to identify the computer. Most routers allow filtering MAC addresses, so only specific addresses can connect to the network. This is a rather simple method, which has several drawbacks. First, even a not particularly seasoned hacker can spoof a MAC address and gain access to the router. Second, this system proves to be inefficient over time, as any device or computer you might want to add to the trusted list, needs to be manually entered into the system.
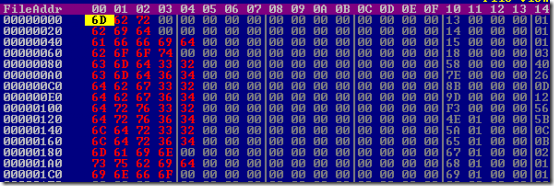
To find out your network adapter’s MAC address in Windows, you first need to open a command prompt – in Windows 98/2000/XP, click Start > Run > type “cmd” (without the quotes) then hit OK. In Windows Vista, click Start > All Programs > Accessories > Command Prompt. In the window that appears, type “ipconfig/all” (without the quotes) and hit Enter. You will see a plethora of information on the screen – we’re looking for Physical Address under Ethernet Adapter.
After you’ve found out the relevant MAC address, open up your router’s interface through a browser (see the manual). You will then need to look for an option called MAC Filtering or similar. There, enable MAC filtering and add the address we’ve just found to the list. Note that you will need to do the same procedure for every additional computer, as well as when changing network adapters.
Secret Access Point name
Every wireless connection – or Access Point -– has a Service Set Identifier (SSID), which translates to the name of the wireless network you’re connecting to. By default, the SSID will automatically show when one searches for a wireless network. However, most routers allow you to hide the SSID, so it’s only possible to connect to the network by entering the exact SSID. This is where you come in – you can give the connection a particularly nasty or long name, essentially serving as a password. The major disadvantage here, like with MAC filtering, is that any average hacker will be able to sniff out a hidden SSID’s name, and effortlessly connect to your network if it’s not encrypted.
To make a hidden SSID, search for this option in the router’s menu – it can usually be found under Wireless Setup or similar. After this, you will need to enter the exact SSID when connecting to this network.
Encryption
This is by far the most popular and secure method of protecting your wireless connection. Wireless Network encryption means that you have to enter a password to gain access to a WLAN or the information streamed through the connection.
There are two main encryption protocols in use today. The first is called WEP – which stands for Wired Equivalent Protection. WEP is an aged technology, having been developed in the early days of WLAN. Therefore, although it still remains a very popular encryption method, it is the most insecure – it’s very easy to crack this encryption protocol with no technical knowledge and simply with a few minutes to spare. WEP is offered in several degrees of complexity: 64, 128 and 256 bits, which directly influence the encryption key’s length. The more complex the cipher is, the better.
To answer the disadvantages of WEP, a new protocol – called WPA (WiFi Protected Access) – was developed by the Wi-Fi Alliance. It utilizes a more complex algorithm which is far more secure than WEP. Unfortunately, WPA and WPA2 – the newest iteration of the protocol – are not readily available on all routers on sale today, so if you’re shopping for a router in the lower price range, make sure it supports WPA for ultimate security. The encryption key, in WPA’s case, can be entered as 8-63 characters – but generally speaking, a random, 13 character WPA key is nearly impossible to crack.
Which protocol to use is your decision – however, using WPA is highly recommended, as it provides a much better layer of security than WEP. Whichever you choose, remember to use a random combination of letters and numbers as your password – if your router has a ‘Generate Password’ feature, use it.
To set up encryption, enter your router’s menu and look for Wireless Security. Choose the appropriate protocol and follow the instructions.
Additional tips on wireless security
- When using public wireless networks, like in a café or restaurant, pay extra attention to online security. Avoid entering your banking information, or credit card number, while connected in public networks, as it’s very easy for hackers to intercept this information and steal it.

 A recent
A recent 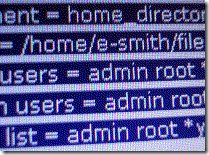 Chances are you know the rules for creating a secure password. Don’t use a dictionary word. Use upper and lowercase letters. Use at least one special character. Unfortunately, most people don’t follow even these basic rules. Recently, advances in computational power have made them as obsolete as your AOL account. Say goodbye to the old rules, and the concept of a password. Hello passphrase.
Chances are you know the rules for creating a secure password. Don’t use a dictionary word. Use upper and lowercase letters. Use at least one special character. Unfortunately, most people don’t follow even these basic rules. Recently, advances in computational power have made them as obsolete as your AOL account. Say goodbye to the old rules, and the concept of a password. Hello passphrase.

 Google CEO Eric Schmidt has set the Internet on fire with his
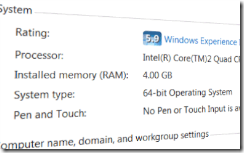
Google CEO Eric Schmidt has set the Internet on fire with his  It seems as though the entire world is abuzz with talk of Windows 7 being released today. Everywhere you look online, someone is discussing it. They talk about how fast it is, how cool some of the features are. However, you only really read about the security side of the new operating system if you look on the various tech sites. It’s as though the general population has forgotten about that important component… or have they simply written Microsoft off when it comes to security?
It seems as though the entire world is abuzz with talk of Windows 7 being released today. Everywhere you look online, someone is discussing it. They talk about how fast it is, how cool some of the features are. However, you only really read about the security side of the new operating system if you look on the various tech sites. It’s as though the general population has forgotten about that important component… or have they simply written Microsoft off when it comes to security?