pretty sure i have a virus but, scans don't find it [Solved]
Started by
death salad
, May 18 2010 02:37 AM
#1
![pretty sure i have a virus but, scans don't find it [Solved]: post #1](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 18 May 2010 - 02:37 AM
Posted 18 May 2010 - 02:37 AM

#2
![pretty sure i have a virus but, scans don't find it [Solved]: post #2](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 18 May 2010 - 09:47 AM
Posted 18 May 2010 - 09:47 AM

DO NOT use any TOOLS such as Combofix or HijackThis fixes without supervision.
Doing so could make your pc inoperatible and could require a full reinstall of your OS, losing all your programs and data.
Vista and Windows 7 users:
1. These tools MUST be run from the executable. (.exe) every time you run them
2. With Admin Rights (Right click, choose "Run as Administrator")
Stay with this topic until I give you the all clean post.
You might want to print these instructions out.
I suggest you do this:
XP Users
Double-click My Computer.
Click the Tools menu, and then click Folder Options.
Click the View tab.
Uncheck "Hide file extensions for known file types."
Under the "Hidden files" folder, select "Show hidden files and folders."
Uncheck "Hide protected operating system files."
Click Apply, and then click OK.
Vista Users
To enable the viewing of hidden and protected system files in Windows Vista please follow these steps:
Close all programs so that you are at your desktop.
Click on the Start button. This is the small round button with the Windows flag in the lower left corner.
Click on the Control Panel menu option.
When the control panel opens you can either be in Classic View or Control Panel Home view:
If you are in the Classic View do the following:
Double-click on the Folder Options icon.
Click on the View tab.
If you are in the Control Panel Home view do the following:
Click on the Appearance and Personalization link.
Click on Show Hidden Files or Folders.
Under the Hidden files and folders section select the radio button labeled Show hidden files and folders.
Remove the checkmark from the checkbox labeled Hide extensions for known file types.
Remove the checkmark from the checkbox labeled Hide protected operating system files.
Please do not delete anything unless instructed to.
We've been seeing some Java infections lately.
Go here and follow the instructions to clear your Java Cache
http://www.java.com/...lugin_cache.xml
Next:
Please download ATF Cleaner by Atribune.
Download - ATF Cleaner»
Double-click ATF-Cleaner.exe to run the program.
Under Main choose: Select All
Click the Empty Selected button.
[/list]If you use Firefox browserClick Firefox at the top and choose: Select All
Click the Empty Selected button.
NOTE: If you would like to keep your saved passwords, please click No at the prompt.
If you use Opera browserClick Opera at the top and choose: Select All
Click the Empty Selected button.
NOTE: If you would like to keep your saved passwords, please click No at the prompt.
Click Exit on the Main menu to close the program.
It's normal after running ATF cleaner that the PC will be slower to boot the first time or two.
Next:
Please download Malwarebytes' Anti-Malware to your desktop.
- Double-click mbam-setup.exe and follow the prompts to install the program.
- At the end, be sure a checkmark is placed next to Update Malwarebytes' Anti-Malware and Launch Malwarebytes' Anti-Malware, then click Finish.
- If an update is found, it will download and install the latest version.
- Once the program has loaded, select Perform quick scan, then click Scan.
- When the scan is complete, click OK, then Show Results to view the results.
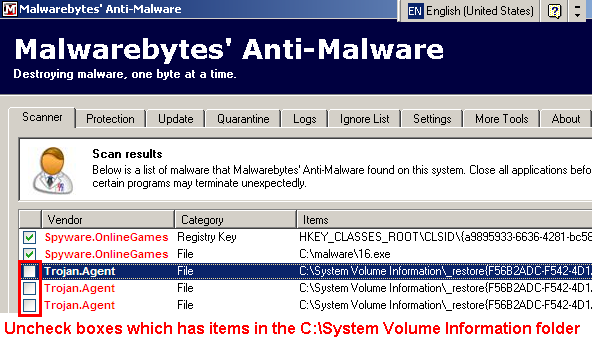
- Then click Remove Selected .
- When completed, a log will open in Notepad. Please save it to a convenient location and post the results.
- Note: If you receive a notice that some of the items couldn't be removed, that they have been added to the delete on reboot list, please reboot.
Also please describe how your computer behaves at the moment.
Please don't attach the scans / logs, use "copy/paste". .
#3
![pretty sure i have a virus but, scans don't find it [Solved]: post #3](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 18 May 2010 - 10:58 AM
Posted 18 May 2010 - 10:58 AM

first off thanks a lot for replying.
ok, so this morning it seems like the program went away and the antivirus didn't bring anything up, but here is the log anyway.
Malwarebytes' Anti-Malware 1.46
www.malwarebytes.org
Database version: 4111
Windows 6.0.6001 Service Pack 1
Internet Explorer 7.0.6001.18000
5/18/2010 9:53:35 AM
mbam-log-2010-05-18 (09-53-35).txt
Scan type: Quick scan
Objects scanned: 117951
Time elapsed: 4 minute(s), 10 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 0
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
(No malicious items detected)
ok, so this morning it seems like the program went away and the antivirus didn't bring anything up, but here is the log anyway.
Malwarebytes' Anti-Malware 1.46
www.malwarebytes.org
Database version: 4111
Windows 6.0.6001 Service Pack 1
Internet Explorer 7.0.6001.18000
5/18/2010 9:53:35 AM
mbam-log-2010-05-18 (09-53-35).txt
Scan type: Quick scan
Objects scanned: 117951
Time elapsed: 4 minute(s), 10 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 0
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
(No malicious items detected)
#4
![pretty sure i have a virus but, scans don't find it [Solved]: post #4](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 18 May 2010 - 11:13 AM
Posted 18 May 2010 - 11:13 AM

Nothing bad there.
I'll leave your topic open for a couple days.
If it comes back let me know.
I'll leave your topic open for a couple days.
If it comes back let me know.
#5
![pretty sure i have a virus but, scans don't find it [Solved]: post #5](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 26 May 2010 - 04:11 AM
Posted 26 May 2010 - 04:11 AM

i ran a malwarebytes quickscan again earlier and i got four infections. i deleted them but when i restarted my computer it said malwarebytes was being prevented from opening at startup and my computer is still acting funny
Malwarebytes' Anti-Malware 1.46
www.malwarebytes.org
Database version: 4111
Windows 6.0.6001 Service Pack 1 (Safe Mode)
Internet Explorer 7.0.6001.18000
5/25/2010 6:27:50 PM
mbam-log-2010-05-25 (18-27-50).txt
Scan type: Quick scan
Objects scanned: 115156
Time elapsed: 4 minute(s), 37 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 2
Registry Values Infected: 1
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 1
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
HKEY_CURRENT_USER\Software\avsuite (Rogue.AntivirusSuite) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\avsoft (Trojan.Fraudpack) -> Quarantined and deleted successfully.
Registry Values Infected:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\nxgpivyq (Rogue.AntivirusSuite.Gen) -> Quarantined and deleted successfully.
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
C:\Users\computer\AppData\Local\xgbeijmjo\rfhuehhtssd.exe (Rogue.AntivirusSuite.Gen) -> Quarantined and deleted successfully.
Malwarebytes' Anti-Malware 1.46
www.malwarebytes.org
Database version: 4111
Windows 6.0.6001 Service Pack 1 (Safe Mode)
Internet Explorer 7.0.6001.18000
5/25/2010 6:27:50 PM
mbam-log-2010-05-25 (18-27-50).txt
Scan type: Quick scan
Objects scanned: 115156
Time elapsed: 4 minute(s), 37 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 2
Registry Values Infected: 1
Registry Data Items Infected: 0
Folders Infected: 0
Files Infected: 1
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
HKEY_CURRENT_USER\Software\avsuite (Rogue.AntivirusSuite) -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\Software\avsoft (Trojan.Fraudpack) -> Quarantined and deleted successfully.
Registry Values Infected:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\nxgpivyq (Rogue.AntivirusSuite.Gen) -> Quarantined and deleted successfully.
Registry Data Items Infected:
(No malicious items detected)
Folders Infected:
(No malicious items detected)
Files Infected:
C:\Users\computer\AppData\Local\xgbeijmjo\rfhuehhtssd.exe (Rogue.AntivirusSuite.Gen) -> Quarantined and deleted successfully.
#6
![pretty sure i have a virus but, scans don't find it [Solved]: post #6](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 26 May 2010 - 03:32 PM
Posted 26 May 2010 - 03:32 PM

Looks like you found an infected website.
Please do not delete anything unless instructed to.
We've been seeing some Java infections lately.
Go here and follow the instructions to clear your Java Cache
Please download DeFogger to your desktop.
Double click DeFogger to run the tool.
Do not re-enable these drivers until otherwise instructed.
To re-enable your Emulation drivers once you're clean, double click DeFogger to run the tool.
Your Emulation drivers are now re-enabled.
Next:
Please download GMER from one of the following locations and save it to your desktop:
Before scanning, make sure all other running programs are closed and no other actions like a scheduled antivirus scan will occur while the scan is being performed. Do not use your computer for anything else during the scan.
Rootkit scans often produce false positives. Do NOT take any action on any "<--- ROOKIT" entries
Please copy and paste the report into your Post.
Please do not delete anything unless instructed to.
We've been seeing some Java infections lately.
Go here and follow the instructions to clear your Java Cache
Please download DeFogger to your desktop.
Double click DeFogger to run the tool.
- The application window will appear
- Click the Disable button to disable your CD Emulation drivers
- Click Yes to continue
- A 'Finished!' message will appear
- Click OK
- DeFogger will now ask to reboot the machine - click OK
Do not re-enable these drivers until otherwise instructed.
To re-enable your Emulation drivers once you're clean, double click DeFogger to run the tool.
- The application window will appear
- Click the Re-enable button to re-enable your CD Emulation drivers
- Click Yes to continue
- A 'Finished!' message will appear
- Click OK
- DeFogger will now ask to reboot the machine - click OK
Your Emulation drivers are now re-enabled.
Next:
Please download GMER from one of the following locations and save it to your desktop:
- Main Mirror
This version will download a randomly named file (Recommended) - Zipped Mirror
This version will download a zip file you will need to extract first. If you use this mirror, please extract the zip file to your desktop.
Before scanning, make sure all other running programs are closed and no other actions like a scheduled antivirus scan will occur while the scan is being performed. Do not use your computer for anything else during the scan.
- Double click GMER.exe.

- If it gives you a warning about rootkit activity and asks if you want to run a full scan...click on NO, then use the following settings for a more complete scan..
- In the right panel, you will see several boxes that have been checked. Ensure the following are UNCHECKED ...
- Then click the Scan button & wait for it to finish.
- Once done click on the [Save..] button, and in the File name area, type in "ark.txt"
- Save the log where you can easily find it, such as your desktop.
Rootkit scans often produce false positives. Do NOT take any action on any "<--- ROOKIT" entries
Please copy and paste the report into your Post.
#7
![pretty sure i have a virus but, scans don't find it [Solved]: post #7](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 27 May 2010 - 01:17 AM
Posted 27 May 2010 - 01:17 AM

so i went ahead and attempted to follow your instructions and whenever i tried the gmer program my computer would freeze and i would have to restart it. i tried it 4 times and then i performed a system restore, but i am not so sure that was a good idea after all.
GMER 1.0.15.15281 - http://www.gmer.net
Rootkit scan 2010-05-27 00:13:45
Windows 6.0.6001 Service Pack 1
Running: x3yszr6x.exe; Driver: C:\Users\computer\AppData\Local\Temp\pwrirkoc.sys
---- Devices - GMER 1.0.15 ----
AttachedDevice \Driver\tdx \Device\Tcp Mpfp.sys (McAfee Personal Firewall Plus Driver/McAfee, Inc.)
AttachedDevice \Driver\tdx \Device\Udp Mpfp.sys (McAfee Personal Firewall Plus Driver/McAfee, Inc.)
AttachedDevice \Driver\tdx \Device\RawIp Mpfp.sys (McAfee Personal Firewall Plus Driver/McAfee, Inc.)
---- Files - GMER 1.0.15 ----
File C:\Users\computer\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\MYC0YJZD\GetXML[2].xml 321 bytes
---- EOF - GMER 1.0.15 ----
GMER 1.0.15.15281 - http://www.gmer.net
Rootkit scan 2010-05-27 00:13:45
Windows 6.0.6001 Service Pack 1
Running: x3yszr6x.exe; Driver: C:\Users\computer\AppData\Local\Temp\pwrirkoc.sys
---- Devices - GMER 1.0.15 ----
AttachedDevice \Driver\tdx \Device\Tcp Mpfp.sys (McAfee Personal Firewall Plus Driver/McAfee, Inc.)
AttachedDevice \Driver\tdx \Device\Udp Mpfp.sys (McAfee Personal Firewall Plus Driver/McAfee, Inc.)
AttachedDevice \Driver\tdx \Device\RawIp Mpfp.sys (McAfee Personal Firewall Plus Driver/McAfee, Inc.)
---- Files - GMER 1.0.15 ----
File C:\Users\computer\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\MYC0YJZD\GetXML[2].xml 321 bytes
---- EOF - GMER 1.0.15 ----
#8
![pretty sure i have a virus but, scans don't find it [Solved]: post #8](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 27 May 2010 - 05:35 AM
Posted 27 May 2010 - 05:35 AM

If you still have ATF cleaner you don't need to download it again, just run it.
Please download ATF Cleaner by Atribune.
Download - ATF Cleaner»
Double-click ATF-Cleaner.exe to run the program.
Under Main choose: Select All
Click the Empty Selected button.
[/list]If you use Firefox browserClick Firefox at the top and choose: Select All
Click the Empty Selected button.
NOTE: If you would like to keep your saved passwords, please click No at the prompt.
If you use Opera browserClick Opera at the top and choose: Select All
Click the Empty Selected button.
NOTE: If you would like to keep your saved passwords, please click No at the prompt.
Click Exit on the Main menu to close the program.
It's normal after running ATF cleaner that the PC will be slower to boot the first time.
Next:
Download ComboFix from one of these locations:
Link 1
Link 2 If using this link, Right Click and select Save As.
* IMPORTANT !!! Save ComboFix.exe to your Desktop
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
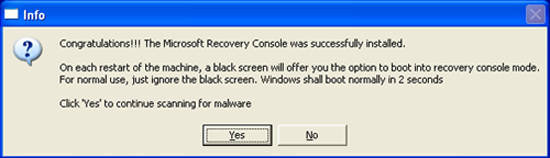
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt using Copy / Paste in your next reply.
Notes:
1.Do not mouse-click Combofix's window while it is running. That may cause it to stall.
2. ComboFix may reset a number of Internet Explorer's settings, including making I-E the default browser.
3. Combofix prevents autorun of ALL CD, floppy and USB devices to assist with malware removal & increase security. If this is an issue or makes it difficult for you -- please tell your helper.
4. CF disconnects your machine from the internet. The connection is automatically restored before CF completes its run. If CF runs into difficulty and terminates prematurely, the connection can be manually restored by restarting your machine.
Give it atleast 20-30 minutes to finish if needed.
Please do not attach the scan results from Combofx. Use copy/paste.
Also please describe how your computer behaves at the moment.
Please download ATF Cleaner by Atribune.
Download - ATF Cleaner»
Double-click ATF-Cleaner.exe to run the program.
Under Main choose: Select All
Click the Empty Selected button.
[/list]If you use Firefox browserClick Firefox at the top and choose: Select All
Click the Empty Selected button.
NOTE: If you would like to keep your saved passwords, please click No at the prompt.
If you use Opera browserClick Opera at the top and choose: Select All
Click the Empty Selected button.
NOTE: If you would like to keep your saved passwords, please click No at the prompt.
Click Exit on the Main menu to close the program.
It's normal after running ATF cleaner that the PC will be slower to boot the first time.
Next:
Download ComboFix from one of these locations:
Link 1
Link 2 If using this link, Right Click and select Save As.
* IMPORTANT !!! Save ComboFix.exe to your Desktop
- Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools. Note: If you are having difficulty properly disabling your protective programs, or are unsure as to what programs need to be disabled, please refer to the information available through this link : Protective Programs
- Double click on ComboFix.exe & follow the prompts.
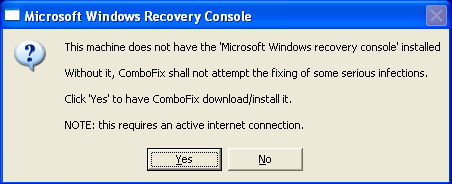
Notes: Combofix will run without the Recovery Console installed. Skip the Recovery Console part if you're running Vista or Windows 7.
Note: If you have SP3, use the SP2 package.If Vista or Windows 7, skip the Recovery Console part
- As part of it's process, ComboFix will check to see if the Microsoft Windows Recovery Console is installed. With malware infections being as they are today, it's strongly recommended to have this pre-installed on your machine before doing any malware removal. It will allow you to boot up into a special recovery/repair mode that will allow us to more easily help you should your computer have a problem after an attempted removal of malware.
- Follow the prompts to allow ComboFix to download and install the Microsoft Windows Recovery Console, and when prompted, agree to the End-User License Agreement to install the Microsoft Windows Recovery Console.
**Please note: If the Microsoft Windows Recovery Console is already installed, ComboFix will continue it's malware removal procedures.
Once the Microsoft Windows Recovery Console is installed using ComboFix, you should see the following message:
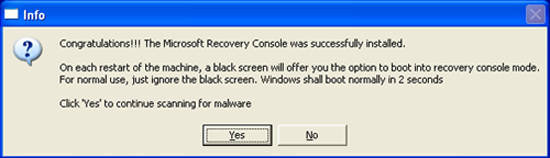
Click on Yes, to continue scanning for malware.
When finished, it shall produce a log for you. Please include the C:\ComboFix.txt using Copy / Paste in your next reply.
Notes:
1.Do not mouse-click Combofix's window while it is running. That may cause it to stall.
2. ComboFix may reset a number of Internet Explorer's settings, including making I-E the default browser.
3. Combofix prevents autorun of ALL CD, floppy and USB devices to assist with malware removal & increase security. If this is an issue or makes it difficult for you -- please tell your helper.
4. CF disconnects your machine from the internet. The connection is automatically restored before CF completes its run. If CF runs into difficulty and terminates prematurely, the connection can be manually restored by restarting your machine.
Give it atleast 20-30 minutes to finish if needed.
Please do not attach the scan results from Combofx. Use copy/paste.
Also please describe how your computer behaves at the moment.
#9
![pretty sure i have a virus but, scans don't find it [Solved]: post #9](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 27 May 2010 - 04:32 PM
Posted 27 May 2010 - 04:32 PM

i wasn't able to turn off spybot s+d i don't know if that affected the scan or not
ComboFix 10-05-27.01 - computer 05/27/2010 15:15:24.1.2 - x86
Microsoft® Windows Vista Home Premium 6.0.6001.1.1252.1.1033.18.3062.2021 [GMT -7:00]
Running from: c:\users\computer\Desktop\ComboFix.exe
SP: Lavasoft Ad-Watch Live! *disabled* (Updated) {67844DAE-4F77-4D69-9457-98E8CFFDAA22}
SP: Spybot - Search and Destroy *enabled* (Outdated) {ED588FAF-1B8F-43B4-ACA8-8E3C85DADBE9}
SP: Windows Defender *enabled* (Updated) {D68DDC3A-831F-4FAE-9E44-DA132C1ACF46}
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
c:\windows\system32\AbaleZip.dll
.
((((((((((((((((((((((((( Files Created from 2010-04-27 to 2010-05-27 )))))))))))))))))))))))))))))))
.
2010-05-27 22:21 . 2010-05-27 22:21 -------- d-----w- c:\users\Default\AppData\Local\temp
2010-05-27 07:35 . 2010-04-13 00:29 411368 ----a-w- c:\windows\system32\deployJava1.dll
2010-05-27 01:26 . 2010-04-23 13:55 2048 ----a-w- c:\windows\system32\tzres.dll
2010-05-26 05:23 . 2010-05-26 05:25 -------- d-----w- c:\program files\Common Files\Mcafee(1)
2010-05-26 05:23 . 2010-05-26 05:23 -------- d-----w- c:\program files\McAfee(3).com
2010-05-26 05:23 . 2010-05-26 09:59 -------- d-----w- c:\program files\McAfee(2)
2010-05-26 01:14 . 2010-05-26 01:27 -------- d-----w- c:\users\computer\AppData\Local\xgbeijmjo
2010-05-25 17:18 . 2010-05-25 17:18 -------- d-----w- c:\programdata\Office Genuine Advantage
2010-05-24 20:32 . 2008-01-31 01:36 90112 ----a-w- c:\windows\unvise32.exe
2010-05-21 08:37 . 2010-05-22 05:17 -------- d-----w- c:\users\computer\AppData\Roaming\Auslogics
2010-05-21 08:37 . 2010-05-21 08:40 -------- d-----w- c:\program files\Auslogics
2010-05-19 10:01 . 2010-05-19 10:01 -------- d-----w- c:\windows\CheckSur
2010-05-18 10:21 . 2010-04-29 22:39 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2010-05-18 10:20 . 2010-04-29 22:39 20952 ----a-w- c:\windows\system32\drivers\mbam.sys
2010-05-18 10:01 . 2010-01-29 16:21 738304 ----a-w- c:\windows\system32\inetcomm.dll
2010-05-18 10:00 . 2010-05-12 18:21 221568 ------w- c:\windows\system32\MpSigStub.exe
2010-05-18 08:22 . 2010-05-18 08:22 -------- d-----w- c:\programdata\Kaspersky Lab Setup Files
2010-05-18 07:58 . 2010-05-18 07:58 -------- d-----w- c:\users\computer\AppData\Roaming\Malwarebytes
2010-05-18 07:58 . 2010-05-18 07:58 -------- d-----w- c:\programdata\Malwarebytes
2010-05-18 07:58 . 2010-05-18 10:21 -------- d-----w- c:\program files\Malwarebytes' Anti-Malware
2010-05-18 07:18 . 2010-05-18 07:18 -------- d-----w- c:\program files\AVG
2010-05-18 07:18 . 2010-05-18 07:18 -------- d-----w- c:\programdata\avg9
2010-05-18 06:53 . 2010-05-18 06:55 -------- d-----w- c:\program files\Common Files\Mcafee(25)
2010-05-18 06:53 . 2010-05-18 06:53 -------- d-----w- c:\program files\McAfee(79).com
2010-05-18 06:53 . 2010-05-18 09:11 -------- d-----w- c:\program files\McAfee(78)
2010-05-16 05:40 . 2010-05-16 05:42 -------- d-----w- c:\program files\Common Files\Mcafee(2)
2010-05-16 05:40 . 2010-05-16 05:40 -------- d-----w- c:\program files\McAfee(22).com
2010-05-16 05:40 . 2010-05-16 05:42 -------- d-----w- c:\program files\McAfee(21)
2010-05-09 13:14 . 2010-05-26 04:31 -------- d-----w- C:\PERRLA
2010-04-29 02:40 . 2010-04-29 02:40 -------- d--h--w- c:\windows\system32\CanonIJ Uninstaller Information
2010-04-29 02:38 . 2010-05-18 09:37 -------- d--h--w- c:\program files\CanonBJ
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2010-05-27 07:35 . 2008-04-09 04:45 -------- d-----w- c:\program files\Java
2010-05-27 07:34 . 2009-09-12 10:15 -------- d-----w- c:\programdata\Spybot - Search & Destroy
2010-05-27 00:47 . 2009-09-11 09:45 -------- d-----w- c:\programdata\McAfee
2010-05-27 00:45 . 2009-09-12 07:24 -------- d-----w- c:\program files\McAfee
2010-05-27 00:44 . 2009-09-12 07:24 -------- d-----w- c:\program files\McAfee.com
2010-05-27 00:44 . 2009-09-12 07:24 -------- d-----w- c:\program files\Common Files\McAfee
2010-05-27 00:44 . 2009-09-16 08:03 -------- d-----w- c:\programdata\Yahoo! Companion
2010-05-27 00:30 . 2009-09-11 11:51 1356 ----a-w- c:\users\computer\AppData\Local\d3d9caps.dat
2010-05-23 23:57 . 2009-09-20 06:43 -------- d-----w- c:\programdata\Soulseek
2010-05-23 06:30 . 2009-09-11 06:53 -------- d-----w- c:\program files\Common Files\AOL
2010-05-21 18:55 . 2009-09-11 06:41 77928 ----a-w- c:\users\computer\AppData\Local\GDIPFONTCACHEV1.DAT
2010-05-21 09:13 . 2006-11-02 06:37 20480 ----a-w- c:\windows\system32\drivers\secdrv.sys
2010-05-21 09:13 . 2010-01-19 07:58 819200 ----a-w- c:\windows\system32\xvidcore.dll
2010-05-21 09:13 . 2010-01-19 07:58 180224 ----a-w- c:\windows\system32\xvidvfw.dll
2010-05-21 09:13 . 2008-04-29 12:49 237568 ----a-w- c:\windows\system32\UCI32M29.dll
2010-05-21 09:13 . 2008-04-09 05:22 221184 ----a-w- c:\windows\system32\UCI32M22.dll
2010-05-21 09:09 . 2009-11-15 05:06 1196032 ----a-w- c:\windows\RtlUpd.exe
2010-05-21 09:09 . 2009-11-15 05:06 520192 ----a-w- c:\windows\RtlExUpd.dll
2010-05-21 09:08 . 2009-11-15 05:06 315392 ----a-w- c:\windows\HideWin.exe
2010-05-21 09:08 . 2008-04-09 04:47 24576 ----a-w- c:\windows\Help\OEM\scripts\taskMgrPrefs.exe
2010-05-21 09:08 . 2008-04-09 04:47 81920 ----a-w- c:\windows\Help\OEM\scripts\HPPhoneNumbers.exe
2010-05-21 09:08 . 2008-04-09 04:47 53248 ----a-w- c:\windows\Help\OEM\scripts\HPASL.exe
2010-05-21 09:08 . 2008-04-09 04:47 4096 ----a-w- c:\windows\Help\OEM\scripts\Interop.HelpPane.dll
2010-05-21 09:08 . 2008-04-09 04:47 24576 ----a-w- c:\windows\Help\OEM\scripts\launchAP.exe
2010-05-21 09:04 . 2009-10-25 22:30 81920 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0419\CNMsr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 413696 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0419\CNMur9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 401408 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\041D\CNMur9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 147456 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\041E\CNMlr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 397312 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0414\CNMur9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 282624 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0411\CNMur9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 196608 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0410\CNMlr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 176128 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\040e\CNMlr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 73728 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\040b\CNMsr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 94208 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0408\CNMsr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 253952 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0404\CNMur9I.dll
2010-05-19 18:27 . 2006-11-02 11:18 -------- d-----w- c:\program files\Windows Mail
2010-05-18 09:58 . 2009-09-11 06:53 -------- d-----w- c:\programdata\Viewpoint
2010-05-18 09:46 . 2009-09-16 01:55 -------- d-----w- c:\programdata\Microsoft Help
2010-05-18 09:38 . 2009-09-12 10:15 -------- d-----w- c:\program files\Spybot - Search & Destroy
2010-05-18 09:38 . 2009-11-11 03:34 -------- d-----w- c:\program files\iTunes
2010-05-18 09:38 . 2009-09-20 07:57 -------- d-----w- c:\program files\Bonjour
2010-04-24 05:30 . 2010-04-24 05:30 -------- d-----w- c:\users\computer\AppData\Roaming\muvee Technologies
2010-04-23 17:32 . 2010-04-23 17:32 690952 ----a-w- c:\programdata\Microsoft\eHome\Packages\MCESpotlight\MCESpotlight\SpotlightResources.dll
2010-03-28 23:48 . 2010-03-28 23:48 652296 ----a-w- c:\programdata\Microsoft\eHome\Packages\SportsTemplate\SportsTemplateCore\Microsoft.MediaCenter.Sports.UI.dll
2010-03-28 23:47 . 2010-03-28 23:47 416128 ----a-w- c:\programdata\Microsoft\eHome\Packages\NetTV\Browse\NetTVResources.dll
2010-03-09 16:28 . 2010-03-31 17:32 833024 ----a-w- c:\windows\system32\wininet.dll
2010-03-09 16:25 . 2010-03-31 17:32 78336 ----a-w- c:\windows\system32\ieencode.dll
2010-03-09 14:01 . 2010-03-31 17:32 26624 ----a-w- c:\windows\system32\ieUnatt.exe
2010-03-04 18:54 . 2010-04-14 17:49 430080 ----a-w- c:\windows\system32\vbscript.dll
2010-02-28 03:10 . 2009-11-08 01:51 95024 ----a-w- c:\windows\system32\drivers\SBREDrv.sys
2010-02-28 03:10 . 2009-09-12 08:11 15880 ----a-w- c:\windows\system32\lsdelete.exe
2009-10-24 19:00 . 2009-10-24 19:00 22 --sha-w- c:\windows\SMINST\HPCD.sys
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"Sidebar"="c:\program files\Windows Sidebar\sidebar.exe" [2008-01-21 1233920]
"HPAdvisor"="c:\program files\Hewlett-Packard\HP Advisor\HPAdvisor.exe" [2009-08-05 1644088]
"SpybotSD TeaTimer"="c:\program files\Spybot - Search & Destroy\TeaTimer.exe" [2009-03-05 2260480]
"WMPNSCFG"="c:\program files\Windows Media Player\WMPNSCFG.exe" [2008-01-21 202240]
"ehTray.exe"="c:\windows\ehome\ehTray.exe" [2008-01-21 125952]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"Windows Defender"="c:\program files\Windows Defender\MSASCui.exe" [2008-01-21 1008184]
"RtHDVCpl"="RtHDVCpl.exe" [2008-07-03 6266880]
"hpsysdrv"="c:\hp\support\hpsysdrv.exe" [2007-04-18 65536]
"KBD"="c:\hp\KBD\KbdStub.EXE" [2010-05-21 65536]
"OsdMaestro"="c:\program files\Hewlett-Packard\On-Screen OSD Indicator\OSD.exe" [2007-02-15 118784]
"Adobe Reader Speed Launcher"="c:\program files\Adobe\Reader 8.0\Reader\Reader_sl.exe" [2007-05-11 40048]
"HP Software Update"="c:\program files\HP\HP Software Update\HPWuSchd2.exe" [2007-05-08 54840]
"mcagent_exe"="c:\program files\McAfee.com\Agent\mcagent.exe" [2009-09-17 645328]
"QuickTime Task"="c:\program files\QuickTime\QTTask.exe" [2010-05-21 417792]
"iTunesHelper"="c:\program files\iTunes\iTunesHelper.exe" [2009-10-29 141600]
"IgfxTray"="c:\windows\system32\igfxtray.exe" [2008-04-01 141848]
"HotKeysCmds"="c:\windows\system32\hkcmd.exe" [2008-04-01 166424]
"Persistence"="c:\windows\system32\igfxpers.exe" [2008-04-01 133656]
"IAAnotif"="c:\program files\Intel\Intel Matrix Storage Manager\Iaanotif.exe" [2008-06-03 178712]
"SunJavaUpdateSched"="c:\program files\Java\jre1.6.0_01\bin\jusched.exe" [2007-04-07 132760]
c:\users\computer\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\
OneNote 2007 Screen Clipper and Launcher.lnk - c:\program files\Microsoft Office\Office12\ONENOTEM.EXE [2009-2-26 97680]
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\policies\system]
"EnableUIADesktopToggle"= 0 (0x0)
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\drivers32]
"aux"=wdmaud.drv
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\Lavasoft Ad-Aware Service]
@="Service"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\mcmscsvc]
@=""
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\WinDefend]
@="Service"
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecAntiVirus]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecFirewall]
"DisableMonitoring"=dword:00000001
R2 Lavasoft Ad-Aware Service;Lavasoft Ad-Aware Service;c:\program files\Lavasoft\Ad-Aware\AAWService.exe [2010-05-19 1314704]
S0 Lbd;Lbd;c:\windows\system32\DRIVERS\Lbd.sys [2010-02-04 64288]
S2 McAfee SiteAdvisor Service;McAfee SiteAdvisor Service;c:\program files\McAfee\SiteAdvisor\McSACore.exe [2009-12-23 93320]
S2 SBSDWSCService;SBSD Security Center Service;c:\program files\Spybot - Search & Destroy\SDWinSec.exe [2009-01-26 1153368]
.
Contents of the 'Scheduled Tasks' folder
2010-03-15 c:\windows\Tasks\McDefragTask.job
- c:\progra~1\mcafee\mqc\QcConsol.exe [2009-10-22 19:22]
2010-04-01 c:\windows\Tasks\McQcTask.job
- c:\progra~1\mcafee\mqc\QcConsol.exe [2009-10-22 19:22]
.
.
------- Supplementary Scan -------
.
uStart Page = hxxp://ie.redirect.hp.com/svs/rdr?TYPE=3&tp=iehome&locale=en_us&c=81&bd=Pavilion&pf=desktop
mStart Page = hxxp://ie.redirect.hp.com/svs/rdr?TYPE=3&tp=iehome&locale=en_us&c=81&bd=Pavilion&pf=desktop
uInternet Settings,ProxyOverride = *.local
uSearchURL,(Default) = hxxp://search.yahoo.com/search?fr=mcafee&p=%s
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~3\Office12\EXCEL.EXE/3000
FF - ProfilePath - c:\users\computer\AppData\Roaming\Mozilla\Firefox\Profiles\ttggtg9q.default\
FF - prefs.js: browser.startup.homepage - hxxp://www.yahoo.com/
FF - component: c:\program files\McAfee\SiteAdvisor\components\McFFPlg.dll
FF - plugin: c:\program files\DivX\DivX Plus Web Player\npdivx32.dll
FF - plugin: c:\program files\Mozilla Firefox\plugins\np-mswmp.dll
FF - plugin: c:\program files\Mozilla Firefox\plugins\npdeployJava1.dll
FF - plugin: c:\users\computer\AppData\Roaming\Move Networks\plugins\npqmp071505000010.dll
FF - plugin: c:\users\computer\AppData\Roaming\Move Networks\plugins\npqmp071505000011.dll
FF - HiddenExtension: Microsoft .NET Framework Assistant: {20a82645-c095-46ed-80e3-08825760534b} - c:\windows\Microsoft.NET\Framework\v3.5\Windows Presentation Foundation\DotNetAssistantExtension\
---- FIREFOX POLICIES ----
c:\program files\Mozilla Firefox\greprefs\all.js - pref("ui.use_native_colors", true);
c:\program files\Mozilla Firefox\greprefs\all.js - pref("network.auth.force-generic-ntlm", false);
c:\program files\Mozilla Firefox\greprefs\all.js - pref("svg.smil.enabled", false);
c:\program files\Mozilla Firefox\greprefs\security-prefs.js - pref("security.ssl.allow_unrestricted_renego_everywhere__temporarily_available_pr
ef", true);
c:\program files\Mozilla Firefox\greprefs\security-prefs.js - pref("security.ssl.renego_unrestricted_hosts", "");
c:\program files\Mozilla Firefox\greprefs\security-prefs.js - pref("security.ssl.treat_unsafe_negotiation_as_broken", false);
c:\program files\Mozilla Firefox\greprefs\security-prefs.js - pref("security.ssl.require_safe_negotiation", false);
c:\program files\Mozilla Firefox\defaults\pref\firefox.js - pref("extensions.{972ce4c6-7e08-4474-a285-3208198ce6fd}.name", "chrome://browser/locale/browser.properties");
c:\program files\Mozilla Firefox\defaults\pref\firefox.js - pref("extensions.{972ce4c6-7e08-4474-a285-3208198ce6fd}.description", "chrome://browser/locale/browser.properties");
c:\program files\Mozilla Firefox\defaults\pref\firefox.js - pref("plugins.update.notifyUser", false);
.
- - - - ORPHANS REMOVED - - - -
SafeBoot-MCODS
**************************************************************************
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2010-05-27 15:21
Windows 6.0.6001 Service Pack 1 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
--------------------- LOCKED REGISTRY KEYS ---------------------
[HKEY_LOCAL_MACHINE\system\ControlSet001\Control\Class\{4D36E96D-E325-11CE-BFC1-08002BE10318}\0000\AllUserSettings]
@Denied: (A) (Users)
@Denied: (A) (Everyone)
@Allowed: (B 1 2 3 4 5) (S-1-5-20)
"BlindDial"=dword:00000000
.
Completion time: 2010-05-27 15:23:40
ComboFix-quarantined-files.txt 2010-05-27 22:23
Pre-Run: 494,712,270,848 bytes free
Post-Run: 494,653,386,752 bytes free
- - End Of File - - 9B2E10CC5F15560D66A2C986EA50D546
ComboFix 10-05-27.01 - computer 05/27/2010 15:15:24.1.2 - x86
Microsoft® Windows Vista Home Premium 6.0.6001.1.1252.1.1033.18.3062.2021 [GMT -7:00]
Running from: c:\users\computer\Desktop\ComboFix.exe
SP: Lavasoft Ad-Watch Live! *disabled* (Updated) {67844DAE-4F77-4D69-9457-98E8CFFDAA22}
SP: Spybot - Search and Destroy *enabled* (Outdated) {ED588FAF-1B8F-43B4-ACA8-8E3C85DADBE9}
SP: Windows Defender *enabled* (Updated) {D68DDC3A-831F-4FAE-9E44-DA132C1ACF46}
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
c:\windows\system32\AbaleZip.dll
.
((((((((((((((((((((((((( Files Created from 2010-04-27 to 2010-05-27 )))))))))))))))))))))))))))))))
.
2010-05-27 22:21 . 2010-05-27 22:21 -------- d-----w- c:\users\Default\AppData\Local\temp
2010-05-27 07:35 . 2010-04-13 00:29 411368 ----a-w- c:\windows\system32\deployJava1.dll
2010-05-27 01:26 . 2010-04-23 13:55 2048 ----a-w- c:\windows\system32\tzres.dll
2010-05-26 05:23 . 2010-05-26 05:25 -------- d-----w- c:\program files\Common Files\Mcafee(1)
2010-05-26 05:23 . 2010-05-26 05:23 -------- d-----w- c:\program files\McAfee(3).com
2010-05-26 05:23 . 2010-05-26 09:59 -------- d-----w- c:\program files\McAfee(2)
2010-05-26 01:14 . 2010-05-26 01:27 -------- d-----w- c:\users\computer\AppData\Local\xgbeijmjo
2010-05-25 17:18 . 2010-05-25 17:18 -------- d-----w- c:\programdata\Office Genuine Advantage
2010-05-24 20:32 . 2008-01-31 01:36 90112 ----a-w- c:\windows\unvise32.exe
2010-05-21 08:37 . 2010-05-22 05:17 -------- d-----w- c:\users\computer\AppData\Roaming\Auslogics
2010-05-21 08:37 . 2010-05-21 08:40 -------- d-----w- c:\program files\Auslogics
2010-05-19 10:01 . 2010-05-19 10:01 -------- d-----w- c:\windows\CheckSur
2010-05-18 10:21 . 2010-04-29 22:39 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2010-05-18 10:20 . 2010-04-29 22:39 20952 ----a-w- c:\windows\system32\drivers\mbam.sys
2010-05-18 10:01 . 2010-01-29 16:21 738304 ----a-w- c:\windows\system32\inetcomm.dll
2010-05-18 10:00 . 2010-05-12 18:21 221568 ------w- c:\windows\system32\MpSigStub.exe
2010-05-18 08:22 . 2010-05-18 08:22 -------- d-----w- c:\programdata\Kaspersky Lab Setup Files
2010-05-18 07:58 . 2010-05-18 07:58 -------- d-----w- c:\users\computer\AppData\Roaming\Malwarebytes
2010-05-18 07:58 . 2010-05-18 07:58 -------- d-----w- c:\programdata\Malwarebytes
2010-05-18 07:58 . 2010-05-18 10:21 -------- d-----w- c:\program files\Malwarebytes' Anti-Malware
2010-05-18 07:18 . 2010-05-18 07:18 -------- d-----w- c:\program files\AVG
2010-05-18 07:18 . 2010-05-18 07:18 -------- d-----w- c:\programdata\avg9
2010-05-18 06:53 . 2010-05-18 06:55 -------- d-----w- c:\program files\Common Files\Mcafee(25)
2010-05-18 06:53 . 2010-05-18 06:53 -------- d-----w- c:\program files\McAfee(79).com
2010-05-18 06:53 . 2010-05-18 09:11 -------- d-----w- c:\program files\McAfee(78)
2010-05-16 05:40 . 2010-05-16 05:42 -------- d-----w- c:\program files\Common Files\Mcafee(2)
2010-05-16 05:40 . 2010-05-16 05:40 -------- d-----w- c:\program files\McAfee(22).com
2010-05-16 05:40 . 2010-05-16 05:42 -------- d-----w- c:\program files\McAfee(21)
2010-05-09 13:14 . 2010-05-26 04:31 -------- d-----w- C:\PERRLA
2010-04-29 02:40 . 2010-04-29 02:40 -------- d--h--w- c:\windows\system32\CanonIJ Uninstaller Information
2010-04-29 02:38 . 2010-05-18 09:37 -------- d--h--w- c:\program files\CanonBJ
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2010-05-27 07:35 . 2008-04-09 04:45 -------- d-----w- c:\program files\Java
2010-05-27 07:34 . 2009-09-12 10:15 -------- d-----w- c:\programdata\Spybot - Search & Destroy
2010-05-27 00:47 . 2009-09-11 09:45 -------- d-----w- c:\programdata\McAfee
2010-05-27 00:45 . 2009-09-12 07:24 -------- d-----w- c:\program files\McAfee
2010-05-27 00:44 . 2009-09-12 07:24 -------- d-----w- c:\program files\McAfee.com
2010-05-27 00:44 . 2009-09-12 07:24 -------- d-----w- c:\program files\Common Files\McAfee
2010-05-27 00:44 . 2009-09-16 08:03 -------- d-----w- c:\programdata\Yahoo! Companion
2010-05-27 00:30 . 2009-09-11 11:51 1356 ----a-w- c:\users\computer\AppData\Local\d3d9caps.dat
2010-05-23 23:57 . 2009-09-20 06:43 -------- d-----w- c:\programdata\Soulseek
2010-05-23 06:30 . 2009-09-11 06:53 -------- d-----w- c:\program files\Common Files\AOL
2010-05-21 18:55 . 2009-09-11 06:41 77928 ----a-w- c:\users\computer\AppData\Local\GDIPFONTCACHEV1.DAT
2010-05-21 09:13 . 2006-11-02 06:37 20480 ----a-w- c:\windows\system32\drivers\secdrv.sys
2010-05-21 09:13 . 2010-01-19 07:58 819200 ----a-w- c:\windows\system32\xvidcore.dll
2010-05-21 09:13 . 2010-01-19 07:58 180224 ----a-w- c:\windows\system32\xvidvfw.dll
2010-05-21 09:13 . 2008-04-29 12:49 237568 ----a-w- c:\windows\system32\UCI32M29.dll
2010-05-21 09:13 . 2008-04-09 05:22 221184 ----a-w- c:\windows\system32\UCI32M22.dll
2010-05-21 09:09 . 2009-11-15 05:06 1196032 ----a-w- c:\windows\RtlUpd.exe
2010-05-21 09:09 . 2009-11-15 05:06 520192 ----a-w- c:\windows\RtlExUpd.dll
2010-05-21 09:08 . 2009-11-15 05:06 315392 ----a-w- c:\windows\HideWin.exe
2010-05-21 09:08 . 2008-04-09 04:47 24576 ----a-w- c:\windows\Help\OEM\scripts\taskMgrPrefs.exe
2010-05-21 09:08 . 2008-04-09 04:47 81920 ----a-w- c:\windows\Help\OEM\scripts\HPPhoneNumbers.exe
2010-05-21 09:08 . 2008-04-09 04:47 53248 ----a-w- c:\windows\Help\OEM\scripts\HPASL.exe
2010-05-21 09:08 . 2008-04-09 04:47 4096 ----a-w- c:\windows\Help\OEM\scripts\Interop.HelpPane.dll
2010-05-21 09:08 . 2008-04-09 04:47 24576 ----a-w- c:\windows\Help\OEM\scripts\launchAP.exe
2010-05-21 09:04 . 2009-10-25 22:30 81920 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0419\CNMsr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 413696 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0419\CNMur9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 401408 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\041D\CNMur9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 147456 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\041E\CNMlr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 397312 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0414\CNMur9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 282624 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0411\CNMur9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 196608 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0410\CNMlr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 176128 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\040e\CNMlr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 73728 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\040b\CNMsr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 94208 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0408\CNMsr9I.dll
2010-05-21 09:04 . 2009-10-25 22:30 253952 ----a-w- c:\programdata\CanonBJ\IJPrinter\CNMWindows\Canon MP190 series Printer\LanguageModules\0404\CNMur9I.dll
2010-05-19 18:27 . 2006-11-02 11:18 -------- d-----w- c:\program files\Windows Mail
2010-05-18 09:58 . 2009-09-11 06:53 -------- d-----w- c:\programdata\Viewpoint
2010-05-18 09:46 . 2009-09-16 01:55 -------- d-----w- c:\programdata\Microsoft Help
2010-05-18 09:38 . 2009-09-12 10:15 -------- d-----w- c:\program files\Spybot - Search & Destroy
2010-05-18 09:38 . 2009-11-11 03:34 -------- d-----w- c:\program files\iTunes
2010-05-18 09:38 . 2009-09-20 07:57 -------- d-----w- c:\program files\Bonjour
2010-04-24 05:30 . 2010-04-24 05:30 -------- d-----w- c:\users\computer\AppData\Roaming\muvee Technologies
2010-04-23 17:32 . 2010-04-23 17:32 690952 ----a-w- c:\programdata\Microsoft\eHome\Packages\MCESpotlight\MCESpotlight\SpotlightResources.dll
2010-03-28 23:48 . 2010-03-28 23:48 652296 ----a-w- c:\programdata\Microsoft\eHome\Packages\SportsTemplate\SportsTemplateCore\Microsoft.MediaCenter.Sports.UI.dll
2010-03-28 23:47 . 2010-03-28 23:47 416128 ----a-w- c:\programdata\Microsoft\eHome\Packages\NetTV\Browse\NetTVResources.dll
2010-03-09 16:28 . 2010-03-31 17:32 833024 ----a-w- c:\windows\system32\wininet.dll
2010-03-09 16:25 . 2010-03-31 17:32 78336 ----a-w- c:\windows\system32\ieencode.dll
2010-03-09 14:01 . 2010-03-31 17:32 26624 ----a-w- c:\windows\system32\ieUnatt.exe
2010-03-04 18:54 . 2010-04-14 17:49 430080 ----a-w- c:\windows\system32\vbscript.dll
2010-02-28 03:10 . 2009-11-08 01:51 95024 ----a-w- c:\windows\system32\drivers\SBREDrv.sys
2010-02-28 03:10 . 2009-09-12 08:11 15880 ----a-w- c:\windows\system32\lsdelete.exe
2009-10-24 19:00 . 2009-10-24 19:00 22 --sha-w- c:\windows\SMINST\HPCD.sys
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"Sidebar"="c:\program files\Windows Sidebar\sidebar.exe" [2008-01-21 1233920]
"HPAdvisor"="c:\program files\Hewlett-Packard\HP Advisor\HPAdvisor.exe" [2009-08-05 1644088]
"SpybotSD TeaTimer"="c:\program files\Spybot - Search & Destroy\TeaTimer.exe" [2009-03-05 2260480]
"WMPNSCFG"="c:\program files\Windows Media Player\WMPNSCFG.exe" [2008-01-21 202240]
"ehTray.exe"="c:\windows\ehome\ehTray.exe" [2008-01-21 125952]
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"Windows Defender"="c:\program files\Windows Defender\MSASCui.exe" [2008-01-21 1008184]
"RtHDVCpl"="RtHDVCpl.exe" [2008-07-03 6266880]
"hpsysdrv"="c:\hp\support\hpsysdrv.exe" [2007-04-18 65536]
"KBD"="c:\hp\KBD\KbdStub.EXE" [2010-05-21 65536]
"OsdMaestro"="c:\program files\Hewlett-Packard\On-Screen OSD Indicator\OSD.exe" [2007-02-15 118784]
"Adobe Reader Speed Launcher"="c:\program files\Adobe\Reader 8.0\Reader\Reader_sl.exe" [2007-05-11 40048]
"HP Software Update"="c:\program files\HP\HP Software Update\HPWuSchd2.exe" [2007-05-08 54840]
"mcagent_exe"="c:\program files\McAfee.com\Agent\mcagent.exe" [2009-09-17 645328]
"QuickTime Task"="c:\program files\QuickTime\QTTask.exe" [2010-05-21 417792]
"iTunesHelper"="c:\program files\iTunes\iTunesHelper.exe" [2009-10-29 141600]
"IgfxTray"="c:\windows\system32\igfxtray.exe" [2008-04-01 141848]
"HotKeysCmds"="c:\windows\system32\hkcmd.exe" [2008-04-01 166424]
"Persistence"="c:\windows\system32\igfxpers.exe" [2008-04-01 133656]
"IAAnotif"="c:\program files\Intel\Intel Matrix Storage Manager\Iaanotif.exe" [2008-06-03 178712]
"SunJavaUpdateSched"="c:\program files\Java\jre1.6.0_01\bin\jusched.exe" [2007-04-07 132760]
c:\users\computer\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\
OneNote 2007 Screen Clipper and Launcher.lnk - c:\program files\Microsoft Office\Office12\ONENOTEM.EXE [2009-2-26 97680]
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\policies\system]
"EnableUIADesktopToggle"= 0 (0x0)
[HKEY_LOCAL_MACHINE\software\microsoft\windows nt\currentversion\drivers32]
"aux"=wdmaud.drv
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\Lavasoft Ad-Aware Service]
@="Service"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\mcmscsvc]
@=""
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\WinDefend]
@="Service"
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecAntiVirus]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecFirewall]
"DisableMonitoring"=dword:00000001
R2 Lavasoft Ad-Aware Service;Lavasoft Ad-Aware Service;c:\program files\Lavasoft\Ad-Aware\AAWService.exe [2010-05-19 1314704]
S0 Lbd;Lbd;c:\windows\system32\DRIVERS\Lbd.sys [2010-02-04 64288]
S2 McAfee SiteAdvisor Service;McAfee SiteAdvisor Service;c:\program files\McAfee\SiteAdvisor\McSACore.exe [2009-12-23 93320]
S2 SBSDWSCService;SBSD Security Center Service;c:\program files\Spybot - Search & Destroy\SDWinSec.exe [2009-01-26 1153368]
.
Contents of the 'Scheduled Tasks' folder
2010-03-15 c:\windows\Tasks\McDefragTask.job
- c:\progra~1\mcafee\mqc\QcConsol.exe [2009-10-22 19:22]
2010-04-01 c:\windows\Tasks\McQcTask.job
- c:\progra~1\mcafee\mqc\QcConsol.exe [2009-10-22 19:22]
.
.
------- Supplementary Scan -------
.
uStart Page = hxxp://ie.redirect.hp.com/svs/rdr?TYPE=3&tp=iehome&locale=en_us&c=81&bd=Pavilion&pf=desktop
mStart Page = hxxp://ie.redirect.hp.com/svs/rdr?TYPE=3&tp=iehome&locale=en_us&c=81&bd=Pavilion&pf=desktop
uInternet Settings,ProxyOverride = *.local
uSearchURL,(Default) = hxxp://search.yahoo.com/search?fr=mcafee&p=%s
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~3\Office12\EXCEL.EXE/3000
FF - ProfilePath - c:\users\computer\AppData\Roaming\Mozilla\Firefox\Profiles\ttggtg9q.default\
FF - prefs.js: browser.startup.homepage - hxxp://www.yahoo.com/
FF - component: c:\program files\McAfee\SiteAdvisor\components\McFFPlg.dll
FF - plugin: c:\program files\DivX\DivX Plus Web Player\npdivx32.dll
FF - plugin: c:\program files\Mozilla Firefox\plugins\np-mswmp.dll
FF - plugin: c:\program files\Mozilla Firefox\plugins\npdeployJava1.dll
FF - plugin: c:\users\computer\AppData\Roaming\Move Networks\plugins\npqmp071505000010.dll
FF - plugin: c:\users\computer\AppData\Roaming\Move Networks\plugins\npqmp071505000011.dll
FF - HiddenExtension: Microsoft .NET Framework Assistant: {20a82645-c095-46ed-80e3-08825760534b} - c:\windows\Microsoft.NET\Framework\v3.5\Windows Presentation Foundation\DotNetAssistantExtension\
---- FIREFOX POLICIES ----
c:\program files\Mozilla Firefox\greprefs\all.js - pref("ui.use_native_colors", true);
c:\program files\Mozilla Firefox\greprefs\all.js - pref("network.auth.force-generic-ntlm", false);
c:\program files\Mozilla Firefox\greprefs\all.js - pref("svg.smil.enabled", false);
c:\program files\Mozilla Firefox\greprefs\security-prefs.js - pref("security.ssl.allow_unrestricted_renego_everywhere__temporarily_available_pr
ef", true);
c:\program files\Mozilla Firefox\greprefs\security-prefs.js - pref("security.ssl.renego_unrestricted_hosts", "");
c:\program files\Mozilla Firefox\greprefs\security-prefs.js - pref("security.ssl.treat_unsafe_negotiation_as_broken", false);
c:\program files\Mozilla Firefox\greprefs\security-prefs.js - pref("security.ssl.require_safe_negotiation", false);
c:\program files\Mozilla Firefox\defaults\pref\firefox.js - pref("extensions.{972ce4c6-7e08-4474-a285-3208198ce6fd}.name", "chrome://browser/locale/browser.properties");
c:\program files\Mozilla Firefox\defaults\pref\firefox.js - pref("extensions.{972ce4c6-7e08-4474-a285-3208198ce6fd}.description", "chrome://browser/locale/browser.properties");
c:\program files\Mozilla Firefox\defaults\pref\firefox.js - pref("plugins.update.notifyUser", false);
.
- - - - ORPHANS REMOVED - - - -
SafeBoot-MCODS
**************************************************************************
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2010-05-27 15:21
Windows 6.0.6001 Service Pack 1 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
.
--------------------- LOCKED REGISTRY KEYS ---------------------
[HKEY_LOCAL_MACHINE\system\ControlSet001\Control\Class\{4D36E96D-E325-11CE-BFC1-08002BE10318}\0000\AllUserSettings]
@Denied: (A) (Users)
@Denied: (A) (Everyone)
@Allowed: (B 1 2 3 4 5) (S-1-5-20)
"BlindDial"=dword:00000000
.
Completion time: 2010-05-27 15:23:40
ComboFix-quarantined-files.txt 2010-05-27 22:23
Pre-Run: 494,712,270,848 bytes free
Post-Run: 494,653,386,752 bytes free
- - End Of File - - 9B2E10CC5F15560D66A2C986EA50D546
#10
![pretty sure i have a virus but, scans don't find it [Solved]: post #10](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 30 May 2010 - 05:57 PM
Posted 30 May 2010 - 05:57 PM

Are you using McAfee or Symantec?
How's it running?
How's it running?
#11
![pretty sure i have a virus but, scans don't find it [Solved]: post #11](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 31 May 2010 - 04:47 AM
Posted 31 May 2010 - 04:47 AM

i have an expired trial version of mcafee still on my computer. i never got rid of it cause it has blocked a few trojans even after it expired
#12
![pretty sure i have a virus but, scans don't find it [Solved]: post #12](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 31 May 2010 - 05:15 AM
Posted 31 May 2010 - 05:15 AM

OK. In order to try and clean your computer I need to know which ONE anti-virus you want to use. I can suggest a free one if needed.i have an expired trial version of mcafee still on my computer. i never got rid of it cause it has blocked a few trojans even after it expired
You only want 1 anti-virus program active.
I see 4 different ones that are / were used at one time or another.
You already said McAfee is outdated so we need to get rid of it. Symantec looks like a leftover.
What about the Grisoft AVG's?
Mcafee
c:\program files\AVG
c:\programdata\avg9
SymantecAntiVirus
#13
![pretty sure i have a virus but, scans don't find it [Solved]: post #13](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 31 May 2010 - 03:02 PM
Posted 31 May 2010 - 03:02 PM

ok sounds good to me though i cant find any evidence of the avg program or symantec for that matter
#14
![pretty sure i have a virus but, scans don't find it [Solved]: post #14](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 31 May 2010 - 03:51 PM
Posted 31 May 2010 - 03:51 PM

OK. Lets start with this. Then well remove the leftover anti-virus programs.
Microsoft Security Essentials
Run a full scan and let us know what it finds.
Also please describe how your computer behaves at the moment
Microsoft Security Essentials
Run a full scan and let us know what it finds.
Also please describe how your computer behaves at the moment
#15
![pretty sure i have a virus but, scans don't find it [Solved]: post #15](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 31 May 2010 - 04:22 PM
Posted 31 May 2010 - 04:22 PM

Copy/paste the text in the Codebox below into notepad:
Here's how to do that:
Click Start > Run type Notepad click OK.
This will open an empty notepad file:
Take your mouse, and place your cursor at the beginning of the text in the box below, then click and hold the left mouse button, while pulling your mouse over the text. This should highlight the text. Now release the left mouse button. Now, with the cursor over the highlighted text, right click the mouse for options, and select 'copy'. Now over the empty Notepad box, right click your mouse again, and select 'paste' and you will have copied and pasted the text.
Save this file to your desktop, Save this as "CFScript"
Here's how to do that:
1.Click File;
2.Click Save As... Change the directory to your desktop;
3.Change the Save as type to "All Files";
4.Type in the file name: CFScript
5.Click Save ...

Drag CFScript.txt into ComboFix.exe
Then post the results log using Copy / Paste
Also please describe how your computer behaves at the moment.
Here's how to do that:
Click Start > Run type Notepad click OK.
This will open an empty notepad file:
Take your mouse, and place your cursor at the beginning of the text in the box below, then click and hold the left mouse button, while pulling your mouse over the text. This should highlight the text. Now release the left mouse button. Now, with the cursor over the highlighted text, right click the mouse for options, and select 'copy'. Now over the empty Notepad box, right click your mouse again, and select 'paste' and you will have copied and pasted the text.
File:: Folder:: c:\program files\Common Files\Mcafee(1) c:\program files\McAfee(3).com c:\program files\McAfee(2) c:\users\computer\AppData\Local\xgbeijmjo c:\program files\AVG c:\programdata\avg9 c:\program files\Common Files\Mcafee(25) c:\program files\McAfee(79).com c:\program files\McAfee(78) c:\program files\Common Files\Mcafee(2) c:\program files\McAfee(22).com c:\program files\McAfee(21) c:\programdata\Viewpoint c:\program files\Bonjour c:\program files\McAfee.com Registry:: [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] "mcagent_exe"=- [-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\mcmscsvc] [-HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecAntiVirus] [-HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecFirewall]
Save this file to your desktop, Save this as "CFScript"
Here's how to do that:
1.Click File;
2.Click Save As... Change the directory to your desktop;
3.Change the Save as type to "All Files";
4.Type in the file name: CFScript
5.Click Save ...

Drag CFScript.txt into ComboFix.exe
Then post the results log using Copy / Paste
Also please describe how your computer behaves at the moment.
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked






 Sign In
Sign In Create Account
Create Account

