What is Flash Video Downloader?
The Malwarebytes research team has determined that Flash Video Downloader is a browser hijacker. These so-called "hijackers" manipulate your browser(s), for example to change your startpage or searchscopes, so that the affected browser visits their site or one of their choice. This one also displays advertisements.
How do I know if my computer is affected by Flash Video Downloader?
You may see these warnings:
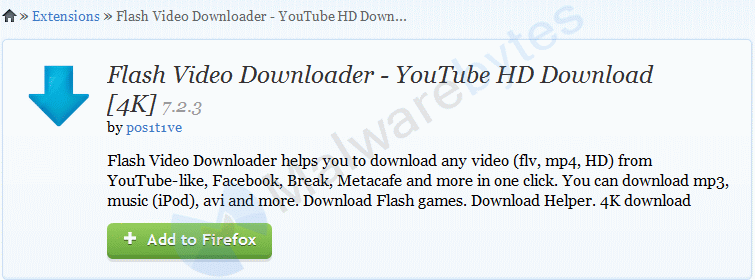
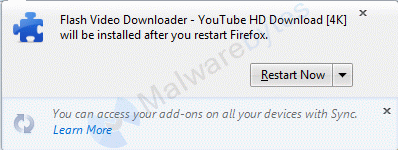
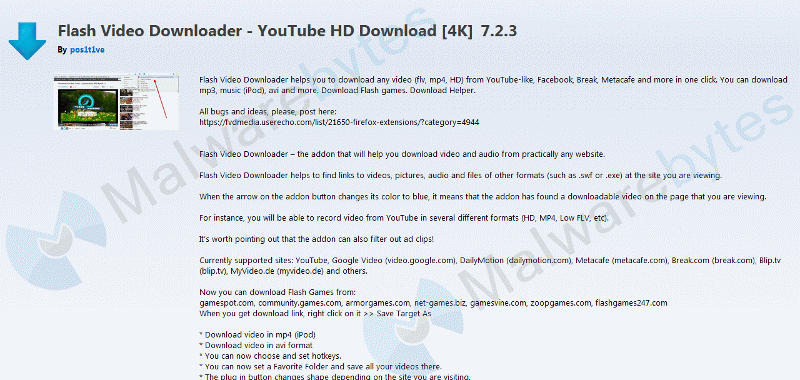
and this Firefox add-on:
How did Flash Video Downloader get on my computer?
Browser hijackers use different methods for distributing themselves. This particular one was offered as a video downloader.
How do I remove Flash Video Downloader?
Our program Malwarebytes Anti-Malware can detect and remove this potentially unwanted program.
- Please download Malwarebytes Anti-Malware to your desktop.
- Double-click mbam-setup-version.exe and follow the prompts to install the program.
- At the end, be sure a check-mark is placed next to the following:
- Enable free trial of Malwarebytes Anti-Malware Premium
- Launch Malwarebytes Anti-Malware
- Then click Finish.
- If an update is found, you will be prompted to download and install the latest version.
- Once the program has loaded, select Scan Now. Or select the Threat Scan from the Scan menu.
- When the scan is complete, make sure that all Threats are selected, and click Remove Selected.
- Restart your computer when prompted to do so.
- No, Malwarebytes' Anti-Malware removes Flash Video Downloader completely.
Technical details for experts
No visible signs in a HijackThis log
Possible signs in a FRST log:
HKCU\Software\Microsoft\Internet Explorer\Main,Start Page Redirect Cache = http://nl.msn.com/?rd=1&ucc=NL&dcc=NL&opt=0&ocid=iehp FF Extension: No Name - C:\Users\Malwarebytes\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\extensions\74979c91-c812-44d6-90e1-1ff0491351e5@e3e0c78c-dd15-4ac4-b6a0-08cad184bd23.com [Not Found] FF Extension: No Name - C:\Users\Malwarebytes\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\Extensions\[email protected] [2015-04-16]Alterations made by the installer:
File system details
---------------------------------------------
Adds the folder C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\extensions\[email protected]
Adds the file chrome.manifest"="4/16/2015 4:09 PM, 1804 bytes, A
Adds the file install.rdf"="4/16/2015 4:09 PM, 1665 bytes, A
Adds the folder C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\extensions\[email protected]\chrome
Adds the folder C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\extensions\[email protected]\components
Adds the folder C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\extensions\[email protected]\defaults
Adds the folder C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\extensions\[email protected]\modules
Adds the file ad.js"="4/16/2015 4:09 PM, 1979 bytes, A
Adds the file async.js"="4/16/2015 4:09 PM, 816 bytes, A
Adds the file config.js"="4/16/2015 4:09 PM, 227 bytes, A
Adds the file downloads.js"="4/16/2015 4:09 PM, 8629 bytes, A
Adds the file misc.js"="4/16/2015 4:09 PM, 8357 bytes, A
Adds the file settings.js"="4/16/2015 4:09 PM, 3862 bytes, A
Adds the file superfish.js"="4/16/2015 4:09 PM, 42877 bytes, A
Adds the file superfish_titles.txt"="4/16/2015 4:09 PM, 140588 bytes, A
Adds the file welcome.js"="4/16/2015 4:09 PM, 5224 bytes, A
Adds the folder C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\extensions\[email protected]\modules\ffmpeg
Adds the file avcodec-55.dll"="4/16/2015 4:09 PM, 10146890 bytes, A
Adds the file avfilter-3.dll"="4/16/2015 4:09 PM, 1158947 bytes, A
Adds the file avformat-55.dll"="4/16/2015 4:09 PM, 2134348 bytes, A
Adds the file avutil-52.dll"="4/16/2015 4:09 PM, 542107 bytes, A
Adds the file ffmpeg.exe"="4/16/2015 4:09 PM, 428889 bytes, A
Adds the file swresample-0.dll"="4/16/2015 4:09 PM, 159175 bytes, A
Adds the folder C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\extensions\[email protected]\modules\ffmpeg\macos
Adds the file ffmpeg"="4/16/2015 4:09 PM, 15144732 bytes, A
Adds the folder C:\Users\{username}\AppData\Roaming\Mozilla\Firefox\Profiles\6qeoodjs.default-1401006518835\FVD Single
Adds the file ad_signs.txt"="4/16/2015 4:10 PM, 233 bytes, A
Malwarebytes Anti-Malware log:Malwarebytes Anti-Malware www.malwarebytes.org Scan Date: 4/16/2015 Scan Time: 3:04:44 PM Logfile: mbamFVD.txt Administrator: Yes Version: 2.01.0.1004 Malware Database: v2015.04.16.03 Rootkit Database: v2015.03.31.01 License: Free Malware Protection: Disabled Malicious Website Protection: Disabled Self-protection: Disabled OS: Windows 7 Service Pack 1 CPU: x86 File System: NTFS User: Malwarebytes Scan Type: Threat Scan Result: Completed Objects Scanned: 288515 Time Elapsed: 10 min, 38 sec Memory: Enabled Startup: Enabled Filesystem: Enabled Archives: Enabled Rootkits: Disabled Heuristics: Enabled PUP: Enabled PUM: Enabled Processes: 0 (No malicious items detected) Modules: 0 (No malicious items detected) Registry Keys: 27 PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdate.OneClickProcessLauncherMachine, Quarantined, [390ac9a42862cd694cb0cb8951b409f7], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdate.OneClickProcessLauncherMachine.1.0, Quarantined, [ee5581ec3d4dca6cad4f98bc9d682ed2], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.CoCreateAsync, Quarantined, [0142165721694de96499d28227de06fa], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.CoCreateAsync.1.0, Quarantined, [281b4b224347f3430df082d230d5e61a], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.CoreClass, Quarantined, [01422746cdbd37ffe31a094bc83d43bd], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.CoreClass.1, Quarantined, [c182d19c464401350af386ce0bfae61a], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.CoreMachineClass, Quarantined, [0f34f479d3b7ce68847979db5ea78977], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.CoreMachineClass.1, Quarantined, [5ee592db61294bebb449da7aeb1ae11f], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.CredentialDialogMachine, Quarantined, [380b88e55b2f2c0a738a144012f357a9], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.CredentialDialogMachine.1.0, Quarantined, [67dc1a53f991f83e9c6177dd22e3d42c], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.OnDemandCOMClassMachine, Quarantined, [a69d7df00486e74f2fce9fb506ff8c74], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.OnDemandCOMClassMachine.1.0, Quarantined, [2023ec810a8037ffd4294f05c93cd42c], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.OnDemandCOMClassMachineFallback, Quarantined, [02411f4eabdfd06658a585cf7a8b7b85], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.OnDemandCOMClassMachineFallback.1.0, Quarantined, [053e73faa8e21521bf3e0d475ea720e0], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.OnDemandCOMClassSvc, Quarantined, [9ea5c1acb4d61e18ed105ef611f47987], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.OnDemandCOMClassSvc.1.0, Quarantined, [a3a0e786404a2c0a0df0183c52b3d729], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.ProcessLauncher, Quarantined, [ef548fde4c3e1620fa031a3a58adbf41], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.ProcessLauncher.1.0, Quarantined, [d76c5e0fe5a51620f20ba4b065a0e020], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.Update3COMClassService, Quarantined, [dc670964a1e9ed49ac51b3a1b1548a76], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.Update3COMClassService.1.0, Quarantined, [7ac9ee7f5238c67015e864f048bd19e7], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.Update3WebMachine, Quarantined, [8cb7195466242f07e815c094ad5854ac], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.Update3WebMachine.1.0, Quarantined, [76cd1b52ff8b171fae4fc094f510d828], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.Update3WebMachineFallback, Quarantined, [cb78224be2a87fb77f7e32223ec7738d], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.Update3WebMachineFallback.1.0, Quarantined, [96ad26476c1ec5718d70b59f669f0000], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.Update3WebSvc, Quarantined, [053ebbb2c5c50b2be6170a4a5fa65aa6], PUP.Optional.GlobalUpdate.A, HKLM\SOFTWARE\CLASSES\globalUpdateUpdate.Update3WebSvc.1.0, Quarantined, [0340fd70dcaec86e8a73f85c36cf37c9], PUP.Optional.GlobalUpdate.C, HKCU\SOFTWARE\GLOBALUPDATE\UPDATE\PROXY, Quarantined, [a49f7fee1a7052e482429b24cd3614ec], Registry Values: 2 PUP.Optional.GlobalUpdate.C, HKLM\SOFTWARE\GLOBALUPDATE\UPDATEDEV|AuCheckPeriodMs, 21600000, Quarantined, [85be26473654d85e1b10b807838005fb] PUP.Optional.GlobalUpdate.C, HKCU\SOFTWARE\GLOBALUPDATE\UPDATE\PROXY|source, IE, Quarantined, [a49f7fee1a7052e482429b24cd3614ec] Registry Data: 0 (No malicious items detected) Folders: 0 (No malicious items detected) Files: 0 (No malicious items detected) Physical Sectors: 0 (No malicious items detected) (end)We recommend using the full version of Malwarebytes Anti-Malware.
We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

