Hi
Here is the CFScript results and Hijackthis log results respectively
please suggest next plan of action
best regards
Jaswant
ComboFix 08-08-21.02 - singhpur 2008-08-22 18:04:19.3 - NTFSx86
Microsoft Windows XP Professional 5.1.2600.2.1252.1.1033.18.1523 [GMT 2:00]
Running from: C:\Documents and Settings\singhpur\Desktop\ComboFix.exe
Command switches used :: C:\Documents and Settings\singhpur\Desktop\CFScript.txt
* Created a new restore point
FILE ::
C:\\WINDOWS\\system32\\kdvic.exe
.
((((((((((((((((((((((((( Files Created from 2008-07-22 to 2008-08-22 )))))))))))))))))))))))))))))))
.
2008-08-21 20:26 . 2008-08-21 20:26 59 --a------ C:\WINDOWS\ANS2000.INI
2008-08-21 20:26 . 2008-08-21 20:26 20 --ah----- C:\WINDOWS\akebook.ini
2008-08-21 20:26 . 2008-08-21 20:26 4 --ah----- C:\WINDOWS\a3kebook.ini
2008-08-21 11:20 . 2008-08-21 11:20 <DIR> d-------- C:\Program Files\Malwarebytes' Anti-Malware
2008-08-21 11:20 . 2008-08-21 11:20 <DIR> d-------- C:\Documents and Settings\singhpur\Application Data\Malwarebytes
2008-08-21 11:20 . 2008-08-21 11:20 <DIR> d-------- C:\Documents and Settings\All Users\Application Data\Malwarebytes
2008-08-21 11:20 . 2008-08-17 15:01 38,472 --a------ C:\WINDOWS\system32\drivers\mbamswissarmy.sys
2008-08-21 11:20 . 2008-08-17 15:01 17,144 --a------ C:\WINDOWS\system32\drivers\mbam.sys
2008-08-21 11:19 . 2008-08-21 11:19 <DIR> d-------- C:\Program Files\Common Files\Download Manager
2008-08-21 11:15 . 2008-08-21 11:15 <DIR> d-------- C:\Program Files\ERUNT
2008-08-20 18:48 . 2008-08-20 18:48 <DIR> d-------- C:\Program Files\Trend Micro
2008-08-11 14:08 . 2008-08-11 14:08 172 --a------ C:\WINDOWS\el.ini
2008-08-03 13:47 . 2008-08-03 13:48 <DIR> d-------- C:\Program Files\HP
2008-08-03 13:47 . 2008-08-03 13:47 <DIR> d-------- C:\Program Files\Common Files\HP
2008-08-03 13:47 . 2008-08-03 13:48 107,440 --a------ C:\WINDOWS\hpqins13.dat
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2008-08-22 16:01 --------- d-----w C:\Documents and Settings\singhpur\Application Data\Skype
2008-08-22 15:39 --------- d-----w C:\Documents and Settings\singhpur\Application Data\BitTorrent
2008-08-22 14:06 --------- d-----w C:\Documents and Settings\All Users\Application Data\Google Updater
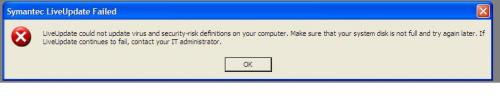
2008-08-21 12:16 --------- d-----w C:\Program Files\symantec antivirus
2008-08-20 16:15 --------- d-----w C:\Documents and Settings\All Users\Application Data\pdf995
2008-08-03 11:47 --------- d-----w C:\Documents and Settings\All Users\Application Data\HP
2008-06-28 11:30 --------- d-----w C:\Documents and Settings\singhpur\Application Data\dvdcss
2008-06-25 18:24 --------- d-----w C:\Program Files\Common Files\Real
2007-04-02 10:46 13,248 ----a-w C:\WINDOWS\system32\config\systemprofile\createprof.vbs
2007-04-02 10:46 13,248 ----a-w C:\Documents and Settings\hpadmin\createprof.vbs
2007-04-02 10:46 13,248 ----a-w C:\Documents and Settings\Default User\createprof.vbs
2007-02-23 14:43 851 ----a-w C:\WINDOWS\system32\config\systemprofile\enablecoe.vbs
2007-02-23 14:43 851 ----a-w C:\Documents and Settings\hpadmin\enablecoe.vbs
.
((((((((((((((((((((((((((((( snapshot@2008-08-21_13.59.09.35 )))))))))))))))))))))))))))))))))))))))))
.
+ 2005-10-20 18:02:28 163,328 ----a-w C:\WINDOWS\erdnt\subs\ERDNT.EXE
- 2007-01-26 16:19:17 25,214 ----a-r C:\WINDOWS\Installer\{A011A1DC-7F1D-4EA8-BD11-0C5F9718E428}\ARPPRODUCTICON.exe
+ 2008-08-21 12:21:41 25,214 ----a-r C:\WINDOWS\Installer\{A011A1DC-7F1D-4EA8-BD11-0C5F9718E428}\ARPPRODUCTICON.exe
- 2007-01-26 16:19:17 40,960 ----a-r C:\WINDOWS\Installer\{A011A1DC-7F1D-4EA8-BD11-0C5F9718E428}\DTIcon.ECFEE69D_DA66_4F00_ABE5_54E931059C01.exe
+ 2008-08-21 12:21:41 40,960 ----a-r C:\WINDOWS\Installer\{A011A1DC-7F1D-4EA8-BD11-0C5F9718E428}\DTIcon.ECFEE69D_DA66_4F00_ABE5_54E931059C01.exe
- 2007-01-26 16:19:17 40,960 ----a-r C:\WINDOWS\Installer\{A011A1DC-7F1D-4EA8-BD11-0C5F9718E428}\NewShortcut1.ECFEE69D_DA66_4F00_ABE5_54E931059C01.exe
+ 2008-08-21 12:21:41 40,960 ----a-r C:\WINDOWS\Installer\{A011A1DC-7F1D-4EA8-BD11-0C5F9718E428}\NewShortcut1.ECFEE69D_DA66_4F00_ABE5_54E931059C01.exe
- 2008-08-21 09:32:38 63,590 ----a-w C:\WINDOWS\system32\perfc009.dat
+ 2008-08-22 15:55:47 63,590 ----a-w C:\WINDOWS\system32\perfc009.dat
- 2008-08-21 09:32:38 404,536 ----a-w C:\WINDOWS\system32\perfh009.dat
+ 2008-08-22 15:55:47 404,536 ----a-w C:\WINDOWS\system32\perfh009.dat
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"ctfmon.exe"="C:\WINDOWS\system32\ctfmon.exe" [2004-08-04 02:56 15360]
[HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Run]
"CTFMON.EXE"="C:\WINDOWS\system32\CTFMON.EXE" [2004-08-04 02:56 15360]
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\policies\system]
"SynchronousMachineGroupPolicy"= 0 (0x0)
"SynchronousUserGroupPolicy"= 0 (0x0)
"DisableNT4Policy"= 1 (0x1)
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\policies\explorer]
"NoMSAppLogo5ChannelNotify"= 1 (0x1)
"NoBandCustomize"= 0 (0x0)
[HKEY_CURRENT_USER\software\microsoft\windows\currentversion\policies\explorer]
"Btn_Back"= 0 (0x0)
"Btn_Forward"= 0 (0x0)
"Btn_Stop"= 0 (0x0)
"Btn_Refresh"= 0 (0x0)
"Btn_Home"= 0 (0x0)
"Btn_Search"= 0 (0x0)
"Btn_History"= 0 (0x0)
"Btn_Favorites"= 0 (0x0)
"Btn_Media"= 0 (0x0)
"Btn_Folders"= 0 (0x0)
"Btn_Fullscreen"= 0 (0x0)
"Btn_Tools"= 0 (0x0)
"Btn_MailNews"= 0 (0x0)
"Btn_Size"= 0 (0x0)
"Btn_Print"= 0 (0x0)
"Btn_Edit"= 0 (0x0)
"Btn_Discussions"= 0 (0x0)
"Btn_Cut"= 0 (0x0)
"Btn_Copy"= 0 (0x0)
"Btn_Paste"= 0 (0x0)
"Btn_Encoding"= 0 (0x0)
"Btn_PrintPreview"= 0 (0x0)
"NoFavoritesMenu"= 0 (0x0)
"NoLogoff"= 0 (0x0)
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\group policy\state\Machine\Scripts\Startup\
0\
0]
"Script"=NOITSCAN.bat
[HKEY_LOCAL_MACHINE\software\microsoft\windows\currentversion\group policy\state\S-1-5-21-1343024091-879983540-725345543-753218\Scripts\Logon\
0\
0]
"Script"=NOITSCAN.bat
[HKEY_LOCAL_MACHINE\system\currentcontrolset\control\securityproviders]
SecurityProviders msapsspc.dllschannel.dlldigest.dllmsnsspc.dll
HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\c:
HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\c:\windows
HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\c:\windows\system32
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\accelerometersystrayapplet]
--a------ 2007-01-24 10:58 124928 C:\WINDOWS\system32\accelerometerST.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\ccapp]
--a------ 2006-03-07 20:02 53408 C:\Program Files\Common Files\Symantec Shared\ccApp.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\coemsgdisplay]
--a------ 2007-04-11 18:14 26624 C:\Program Files\Hewlett-Packard\PC COE\COEMsgDisplay.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\ctfmon.exe]
--a------ 2004-08-04 02:56 15360 C:\WINDOWS\system32\ctfmon.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\getit]
--a------ 2007-12-04 02:12 286720 C:\Program Files\Hewlett-Packard\GetIT\GetIT.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\googletalk]
--a------ 2007-01-01 23:22 3739648 C:\Program Files\Google\Google Talk\googletalk.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\hotkeyscmds]
--a------ 2007-02-26 12:34 155648 C:\WINDOWS\system32\hkcmd.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\hpqsrmon]
--a------ 2008-03-13 09:34 81920 C:\Program Files\HP\Digital Imaging\bin\HpqSRmon.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\hpwirelessassistant]
--a------ 2007-01-10 11:43 472776 C:\Program Files\Hewlett-Packard\HP Wireless Assistant\HPWAMain.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\ida]
--a------ 2008-01-03 20:24 176128 C:\Program Files\Hewlett-Packard\PC COE\Ida.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\igfxtray]
--a------ 2007-02-26 12:34 131072 C:\WINDOWS\system32\igfxtray.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\imekrmig7.0]
--a------ 2003-07-15 06:57 19520 C:\Program Files\Common Files\Microsoft Shared\IME\IMKR7\IMEKRMIG.EXE
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\imjpmig8.1]
--a------ 2004-08-03 23:32 208952 C:\WINDOWS\ime\imjp8_1\imjpmig.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\imjpmig9.0]
--a------ 2004-02-17 23:51 33992 C:\Program Files\Common Files\Microsoft Shared\IME\IMJP9\IMJPRMZB.EXE
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\mspy2002]
--a------ 2004-08-03 23:31 59392 C:\WINDOWS\system32\IME\PINTLGNT\IMSCINST.EXE
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\persistence]
--a------ 2007-02-26 12:33 131072 C:\WINDOWS\system32\igfxpers.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\phime2002a]
--a------ 2004-08-03 23:32 455168 C:\WINDOWS\system32\IME\TINTLGNT\TINTSETP.EXE
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\phime2002async]
--a------ 2004-08-03 23:32 455168 C:\WINDOWS\system32\IME\TINTLGNT\TINTSETP.EXE
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\qlbctrl]
--a------ 2007-03-05 12:24 159744 C:\Program Files\Hewlett-Packard\HP Quick Launch Buttons\QLBCTRL.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\quickpassword]
--a------ 2007-06-27 00:06 225280 C:\Program Files\ActivCard\ActivCard Gold\agquickp.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\smcservice]
--a------ 2005-08-05 19:22 2582240 C:\PROGRA~1\sygate\ssa\Smc.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\soundmaxpnp]
--a------ 2007-01-05 18:36 872448 C:\Program Files\Analog Devices\Core\smax4pnp.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\swg]
--a------ 2008-06-19 19:38 68856 C:\Program Files\Google\GoogleToolbarNotifier\GoogleToolbarNotifier.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\syntpenh]
--a------ 2007-01-12 15:36 827392 C:\Program Files\Synaptics\SynTP\SynTPEnh.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\vptray]
--a------ 2006-05-27 03:01 124656 C:\PROGRA~1\SYMANT~1\VPTray.exe
[HKEY_LOCAL_MACHINE\software\microsoft\shared tools\msconfig\startupreg\watchdog]
--a------ 2006-09-05 15:32 184320 C:\Program Files\InterVideo\DVD Check\DVDCheck.exe
[HKEY_LOCAL_MACHINE\software\microsoft\security center]
"AntiVirusDisableNotify"=dword:00000001
"UpdatesDisableNotify"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecAntiVirus]
"DisableMonitoring"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile]
"DisableNotifications"= 1 (0x1)
"DisableUnicastResponsesToMulticastBroadcast"= 0 (0x0)
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"C:\\Program Files\\Hewlett-Packard\\PC COE 3\\OV CMS\\radexecd.exe"=
"C:\\Program Files\\Hewlett-Packard\\PC COE 3\\OV CMS\\RADUISHELL.exe"=
"C:\\Program Files\\Hewlett-Packard\\PC COE 3\\OV CMS\\RadTray.exe"=
"C:\\Program Files\\Google\\Google Talk\\googletalk.exe"=
"C:\\Program Files\\BitTorrent\\bittorrent.exe"=
"%windir%\\Network Diagnostic\\xpnetdiag.exe"=
"C:\\Program Files\\Skype\\Phone\\Skype.exe"=
R2 acautoreg;ActivCard Gold Autoregister;C:\Program Files\Common Files\ActivCard\acautoreg.exe [2007-06-27 00:06]
R2 Accoca;ActivCard Gold service;C:\Program Files\Common Files\ActivCard\accoca.exe [2007-06-27 00:06]
R2 HPSygControl;HP Sygate Icon Control;C:\PROGRA~1\sygate\ssa\syg_hp.exe [2006-01-25 23:25]
R2 msralinkmonitor;MSRA Link Monitor;C:\Program Files\Remote tools\msraLinkMonitor.exe [2007-11-29 07:39]
R2 radexecd;HP OVCM Notify Daemon;C:\Program Files\Hewlett-Packard\PC COE 3\OV CMS\radexecd.exe [2007-02-20 10:29]
R2 radsched;HP OVCM Scheduler Daemon;C:\Program Files\Hewlett-Packard\PC COE 3\OV CMS\radsched.exe [2007-03-22 13:49]
R2 Radstgms;HP OVCM MSI Redirector;C:\Program Files\Hewlett-Packard\PC COE 3\OV CMS\Radstgms.exe [2007-03-20 08:33]
R3 aksbus;ActivIdentity Virtual Reader Enumerator;C:\WINDOWS\system32\DRIVERS\aksbus.sys [2007-04-06 08:16]
R3 akspcsc;ActivIdentity Virtual PC/SC Device Driver;C:\WINDOWS\system32\DRIVERS\akspcsc.sys [2007-06-27 00:06]
R3 IFXTPM;IFXTPM;C:\WINDOWS\system32\DRIVERS\IFXTPM.SYS [2006-09-19 18:58]
R3 RadiaMsi;RadiaMsi;C:\WINDOWS\system32\DRIVERS\radiamsi.sys [2007-08-03 10:31]
S1 a701effd;a701effd;C:\WINDOWS\system32\drivers\a701effd.sys []
S3 actccid;ActivCard USB Reader V2;C:\WINDOWS\system32\DRIVERS\actccid.sys [2007-06-27 00:06]
S3 AKSIM;ActivKey Sim;C:\WINDOWS\system32\drivers\aksim.sys [2007-06-27 00:06]
S3 magaService;Lan Discover Agent;C:\Program Files\Sygate\SSA\maga\maga.exe [2005-08-05 19:18]
[HKEY_LOCAL_MACHINE\software\microsoft\active setup\installed components\{8E9DB7EF-5DD3-499E-BA2A-A1F3153A4DF8}]
msiexec.exe /fomus {8E9DB7EF-5DD3-499E-BA2A-A1F3153A4DF8} /qb!
.
**************************************************************************
catchme 0.3.1361 W2K/XP/Vista - rootkit/stealth malware detector by Gmer,
http://www.gmer.netRootkit scan 2008-08-22 18:05:15
Windows 5.1.2600 Service Pack 2 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
[HKEY_LOCAL_MACHINE\system\ControlSet001\Services\vsdatant]
"ImagePath"=""
.
Completion time: 2008-08-22 18:05:52
ComboFix-quarantined-files.txt 2008-08-22 16:05:49
ComboFix2.txt 2008-08-22 15:55:29
ComboFix3.txt 2008-08-21 12:07:52
Pre-Run: 40,198,725,632 bytes free
Post-Run: 40,188,624,896 bytes free
212
Logfile of Trend Micro HijackThis v2.0.2
Scan saved at 18:22, on 2008-08-22
Platform: Windows XP SP2 (WinNT 5.01.2600)
MSIE: Internet Explorer v7.00 (7.00.6000.16674)
Boot mode: Normal
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
c:\Program Files\WIDCOMM\Bluetooth Software\bin\btwdins.exe
C:\Program Files\Sygate\SSA\smc.exe
C:\Program Files\Common Files\Symantec Shared\ccSetMgr.exe
C:\Program Files\Common Files\Symantec Shared\ccEvtMgr.exe
C:\Program Files\Common Files\Symantec Shared\SPBBC\SPBBCSvc.exe
C:\WINDOWS\system32\spoolsv.exe
C:\Program Files\Common Files\ActivCard\acautoreg.exe
C:\Program Files\Common Files\ActivCard\accoca.exe
C:\Program Files\Symantec AntiVirus\DefWatch.exe
C:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
C:\PROGRA~1\sygate\ssa\syg_hp.exe
C:\Program Files\Common Files\InterVideo\RegMgr\iviRegMgr.exe
C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE
C:\Program Files\Remote tools\msraLinkMonitor.exe
C:\WINDOWS\SYSTEM32\SPOOL\DRIVERS\W32X86\3\HPZipm12.exe
C:\Program Files\Hewlett-Packard\PC COE 3\OV CMS\radexecd.exe
C:\Program Files\Hewlett-Packard\PC COE 3\OV CMS\radsched.exe
C:\Program Files\Hewlett-Packard\PC COE 3\OV CMS\Radstgms.exe
C:\Program Files\Symantec AntiVirus\SavRoam.exe
C:\Program Files\UPHClean\uphclean.exe
C:\Program Files\Hewlett-Packard\Shared\hpqWmiEx.exe
C:\Program Files\Citrix\ICA Client\ssonsvr.exe
C:\WINDOWS\system32\ctfmon.exe
C:\WINDOWS\explorer.exe
C:\Program Files\internet explorer\iexplore.exe
C:\Program Files\Trend Micro\HijackThis\HijackThis.exe
R0 - HKCU\Software\Microsoft\Internet Explorer\Main,Start Page = about:blank
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL =
http://go.microsoft....k/?LinkId=69157R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Search_URL =
http://go.microsoft....k/?LinkId=54896R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Page =
http://go.microsoft....k/?LinkId=54896R0 - HKLM\Software\Microsoft\Internet Explorer\Main,Start Page =
http://athp.hp.comO2 - BHO: Plugin Class - {56CD20F0-7C09-11D5-A768-0050042307CE} - C:\PlayerIE\playerIE.dll
O2 - BHO: Google Toolbar Notifier BHO - {AF69DE43-7D58-4638-B6FA-CE66B5AD205D} - C:\Program Files\Google\GoogleToolbarNotifier\3.0.1225.9868\swg.dll
O4 - HKCU\..\Run: [ctfmon.exe] C:\WINDOWS\system32\ctfmon.exe
O4 - HKUS\S-1-5-18\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\CTFMON.EXE (User 'SYSTEM')
O4 - HKUS\.DEFAULT\..\Run: [CTFMON.EXE] C:\WINDOWS\system32\CTFMON.EXE (User 'Default user')
O6 - HKCU\Software\Policies\Microsoft\Internet Explorer\Control Panel present
O9 - Extra button: Skype - {77BF5300-1474-4EC7-9980-D32B190E9B07} - C:\Program Files\Skype\Toolbars\Internet Explorer\SkypeIEPlugin.dll
O9 - Extra button: Research - {92780B25-18CC-41C8-B9BE-3C9C571A8263} - C:\PROGRA~1\MICROS~2\OFFICE11\REFIEBAR.DLL
O9 - Extra button: (no name) - {c95fe080-8f5d-11d2-a20b-00aa003c157a} - (no file)
O9 - Extra button: Fix Common Internet Explorer Problems - {E270AB82-96D5-45DB-ABE3-0BC038B92334} - C:\Program Files\Hewlett-Packard\IEToolBar\HP IE Fix.exe
O9 - Extra 'Tools' menuitem: Fix Common Internet Explorer Problems - {E270AB82-96D5-45DB-ABE3-0BC038B92334} - C:\Program Files\Hewlett-Packard\IEToolBar\HP IE Fix.exe
O9 - Extra button: (no name) - {e2e2dd38-d088-4134-82b7-f2ba38496583} - C:\WINDOWS\Network Diagnostic\xpnetdiag.exe
O9 - Extra 'Tools' menuitem: @xpsp3res.dll,-20001 - {e2e2dd38-d088-4134-82b7-f2ba38496583} - C:\WINDOWS\Network Diagnostic\xpnetdiag.exe
O9 - Extra button: Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O9 - Extra 'Tools' menuitem: Windows Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O14 - IERESET.INF: START_PAGE_URL=http://athp.hp.com
O15 - Trusted Zone:
http://ie.config.asia.compaq.comO15 - Trusted Zone:
http://ie.config.eur.compaq.comO15 - Trusted Zone:
http://ie.config.im.hou.compaq.comO15 - Trusted Zone:
http://ie.config.jp.compaq.comO15 - Trusted Zone:
http://ie.config.ecom.dec.comO15 - Trusted Zone:
http://www.geekstogo.comO15 - Trusted Zone:
http://ie.config.tandem.comO15 - Trusted Zone:
http://ie.config.asia.compaq.com (HKLM)
O15 - Trusted Zone:
http://ie.config.eur.compaq.com (HKLM)
O15 - Trusted Zone:
http://ie.config.im.hou.compaq.com (HKLM)
O15 - Trusted Zone:
http://ie.config.jp.compaq.com (HKLM)
O15 - Trusted Zone:
http://ie.config.ecom.dec.com (HKLM)
O15 - Trusted Zone:
http://ie.config.tandem.com (HKLM)
O16 - DPF: {00000021-9593-4264-8B29-930B3E4EDCCD} (HPVirtualRooms21 Class) -
https://www.rooms.hp...VCInstall21.cabO16 - DPF: {10E0E75E-6701-4134-9D95-C0942ED1F1C8} (Snapfish Outlook Import ActiveX Control) -
http://www4.snapfish...tlookImport.cabO16 - DPF: {406B5949-7190-4245-91A9-30A17DE16AD0} (Snapfish Activia) -
http://www4.snapfish...fishActivia.cabO16 - DPF: {67DABFBF-D0AB-41FA-9C46-CC0F21721616} -
http://go.divx.com/p...owserPlugin.cabO16 - DPF: {857ABA85-8AB2-4C9E-8FAA-D2A963739859} (HPPKI Control) -
https://g4t0070.hous...om/hp/HPPKI.cabO16 - DPF: {A996E48C-D3DC-4244-89F7-AFA33EC60679} (Settings Class) -
https://digitalbadge.../hp/capicom.cabO17 - HKLM\System\CCS\Services\Tcpip\Parameters: Domain = asiapacific.cpqcorp.net
O17 - HKLM\Software\..\Telephony: DomainName = asiapacific.hpqcorp.net
O17 - HKLM\System\CS1\Services\Tcpip\Parameters: Domain = asiapacific.cpqcorp.net
O17 - HKLM\System\CS1\Services\Tcpip\Parameters: SearchList = ASIAPACIFIC.cpqcorp.net,ASIAPACIFIC.hpqcorp.net,hpqcorp.net,cpqcorp.net
O17 - HKLM\System\CCS\Services\Tcpip\Parameters: SearchList = ASIAPACIFIC.cpqcorp.net,ASIAPACIFIC.hpqcorp.net,hpqcorp.net,cpqcorp.net
O18 - Protocol: skype4com - {FFC8B962-9B40-4DFF-9458-1830C7DD7F5D} - C:\PROGRA~1\COMMON~1\Skype\SKYPE4~1.DLL
O23 - Service: ActivCard Gold Autoregister (acautoreg) - ActivIdentity - C:\Program Files\Common Files\ActivCard\acautoreg.exe
O23 - Service: ActivCard Gold service (Accoca) - ActivCard - C:\Program Files\Common Files\ActivCard\accoca.exe
O23 - Service: Bluetooth Service (btwdins) - Broadcom Corporation. - c:\Program Files\WIDCOMM\Bluetooth Software\bin\btwdins.exe
O23 - Service: Symantec Event Manager (ccEvtMgr) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\ccEvtMgr.exe
O23 - Service: Symantec Settings Manager (ccSetMgr) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\ccSetMgr.exe
O23 - Service: Symantec AntiVirus Definition Watcher (DefWatch) - Symantec Corporation - C:\Program Files\Symantec AntiVirus\DefWatch.exe
O23 - Service: Google Updater Service (gusvc) - Google - C:\Program Files\Google\Common\Google Updater\GoogleUpdaterService.exe
O23 - Service: hpqwmiex - Hewlett-Packard Development Company, L.P. - C:\Program Files\Hewlett-Packard\Shared\hpqWmiEx.exe
O23 - Service: HP Sygate Icon Control (HPSygControl) - Hewlett-Packard Company - C:\PROGRA~1\sygate\ssa\syg_hp.exe
O23 - Service: IviRegMgr - InterVideo - C:\Program Files\Common Files\InterVideo\RegMgr\iviRegMgr.exe
O23 - Service: LiveUpdate - Symantec Corporation - C:\PROGRA~1\Symantec\LIVEUP~1\LUCOMS~1.EXE
O23 - Service: Lan Discover Agent (magaService) - Sygate Technologies, Inc. - C:\Program Files\Sygate\SSA\maga\maga.exe
O23 - Service: MSRA Link Monitor (msralinkmonitor) - Unknown owner - C:\Program Files\Remote tools\msraLinkMonitor.exe
O23 - Service: PictureTaker - LANovation - C:\WINDOWS\system32\PCTKRNT.SYS
O23 - Service: Pml Driver HPZ12 - HP - C:\WINDOWS\SYSTEM32\SPOOL\DRIVERS\W32X86\3\HPZipm12.exe
O23 - Service: HP OVCM Notify Daemon (radexecd) - Hewlett-Packard - C:\Program Files\Hewlett-Packard\PC COE 3\OV CMS\radexecd.exe
O23 - Service: HP OVCM Scheduler Daemon (radsched) - Hewlett-Packard - C:\Program Files\Hewlett-Packard\PC COE 3\OV CMS\radsched.exe
O23 - Service: HP OVCM MSI Redirector (Radstgms) - Hewlett-Packard - C:\Program Files\Hewlett-Packard\PC COE 3\OV CMS\Radstgms.exe
O23 - Service: SAVRoam (SavRoam) - symantec - C:\Program Files\Symantec AntiVirus\SavRoam.exe
O23 - Service: Sygate Security Agent (SmcService) - Sygate Technologies, Inc. - C:\Program Files\Sygate\SSA\smc.exe
O23 - Service: Symantec Network Drivers Service (SNDSrvc) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\SNDSrvc.exe
O23 - Service: Symantec SPBBCSvc (SPBBCSvc) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\SPBBC\SPBBCSvc.exe
O23 - Service: Symantec AntiVirus - Symantec Corporation - C:\Program Files\Symantec AntiVirus\Rtvscan.exe
O24 - Desktop Component 0: (no name) - file:///C:/DOCUME~1/singhpur/LOCALS~1/Temp/msohtml1/01/clip_image001.jpg
--
End of file - 9027 bytes
Edited by jaswantpurba, 22 August 2008 - 10:24 AM.

 This topic is locked
This topic is locked















 Sign In
Sign In Create Account
Create Account

