This log is from a coworkers computer. Had Antivirus XP Pro. Had taken over the computer. When ever I tried to run and antivirus program or try to run defrag, it would pop up floating point error message. I was finally able to run Malwarebytes in safe mode and get it out. Question I have is after I run Malwarebytes it still shows two entries in the registry. (at the end of Hijack log is the Malwarebyters log) I went into registry and do not see the files. Could they be false positives. Computer is running fine now.
Thanks, Doug
Logfile of Trend Micro HijackThis v2.0.2
Scan saved at 8:31:57 PM, on 2/1/2009
Platform: Windows XP SP3 (WinNT 5.01.2600)
MSIE: Internet Explorer v7.00 (7.00.6000.16762)
Boot mode: Normal
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\AVG\AVG8\avgrsx.exe
C:\WINDOWS\system32\LEXBCES.EXE
C:\WINDOWS\system32\spoolsv.exe
C:\WINDOWS\system32\LEXPPS.EXE
C:\Program Files\Java\jre6\bin\jqs.exe
C:\Program Files\Common Files\Microsoft Shared\VS7DEBUG\MDM.EXE
C:\WINDOWS\BCMSMMSG.exe
C:\WINDOWS\system32\nvsvc32.exe
C:\Program Files\CyberLink\PowerDVD\PDVDServ.exe
C:\Program Files\Java\jre6\bin\jusched.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\system32\ctfmon.exe
C:\Program Files\Messenger\msmsgs.exe
C:\WINDOWS\system32\RUNDLL32.EXE
C:\Program Files\Kodak\Kodak EasyShare software\bin\EasyShare.exe
C:\Program Files\Creative\SBLive\Diagnostics\diagent.exe
C:\WINDOWS\explorer.exe
C:\Documents and Settings\User\Desktop\HijackThis.exe
R0 - HKCU\Software\Microsoft\Internet Explorer\Main,Start Page = http://www.yahoo.com/
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL = http://go.microsoft....k/?LinkId=69157
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Search_URL = http://go.microsoft....k/?LinkId=54896
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Search Page = http://go.microsoft....k/?LinkId=54896
R0 - HKLM\Software\Microsoft\Internet Explorer\Main,Start Page = http://go.microsoft....k/?LinkId=69157
R1 - HKCU\Software\Microsoft\Internet Connection Wizard,ShellNext = http://windowsupdate.microsoft.com/
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,ProxyOverride = localhost
O2 - BHO: Adobe PDF Reader Link Helper - {06849E9F-C8D7-4D59-B87D-784B7D6BE0B3} - C:\Program Files\Common Files\Adobe\Acrobat\ActiveX\AcroIEHelper.dll
O2 - BHO: Spybot-S&D IE Protection - {53707962-6F74-2D53-2644-206D7942484F} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O2 - BHO: SSVHelper Class - {761497BB-D6F0-462C-B6EB-D4DAF1D92D43} - C:\Program Files\Java\jre6\bin\ssv.dll
O2 - BHO: Java™ Plug-In 2 SSV Helper - {DBC80044-A445-435b-BC74-9C25C1C588A9} - C:\Program Files\Java\jre6\bin\jp2ssv.dll
O4 - HKLM\..\Run: [Adobe Reader Speed Launcher] "C:\Program Files\Adobe\Reader 8.0\Reader\Reader_sl.exe"
O4 - HKLM\..\Run: [BCMSMMSG] BCMSMMSG.exe
O4 - HKLM\..\Run: [RemoteControl] "C:\Program Files\CyberLink\PowerDVD\PDVDServ.exe"
O4 - HKLM\..\Run: [NeroFilterCheck] C:\WINDOWS\system32\NeroCheck.exe
O4 - HKLM\..\Run: [UpdReg] C:\WINDOWS\UpdReg.EXE
O4 - HKLM\..\Run: [diagent] "C:\Program Files\Creative\SBLive\Diagnostics\diagent.exe" startup
O4 - HKLM\..\Run: [SunJavaUpdateSched] "C:\Program Files\Java\jre6\bin\jusched.exe"
O4 - HKLM\..\Run: [NvCplDaemon] RUNDLL32.EXE C:\WINDOWS\system32\NvCpl.dll,NvStartup
O4 - HKLM\..\Run: [nwiz] nwiz.exe /install
O4 - HKLM\..\Run: [MSConfig] C:\WINDOWS\PCHealth\HelpCtr\Binaries\MSConfig.exe /auto
O4 - HKCU\..\Run: [ctfmon.exe] C:\WINDOWS\system32\ctfmon.exe
O4 - HKCU\..\Run: [MSMSGS] "C:\Program Files\Messenger\msmsgs.exe" /background
O4 - HKCU\..\Run: [NvMediaCenter] RUNDLL32.EXE C:\WINDOWS\system32\NVMCTRAY.DLL,NvTaskbarInit
O4 - Global Startup: Kodak EasyShare software.lnk = C:\Program Files\Kodak\Kodak EasyShare software\bin\EasyShare.exe
O4 - Global Startup: KODAK Software Updater.lnk = C:\Program Files\Kodak\KODAK Software Updater\7288971\Program\backWeb-7288971.exe
O8 - Extra context menu item: E&xport to Microsoft Excel - res://C:\PROGRA~1\MICROS~2\OFFICE11\EXCEL.EXE/3000
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre6\bin\jp2iexp.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\jre6\bin\jp2iexp.dll
O9 - Extra button: Research - {92780B25-18CC-41C8-B9BE-3C9C571A8263} - C:\PROGRA~1\MICROS~2\OFFICE11\REFIEBAR.DLL
O9 - Extra button: (no name) - {DFB852A3-47F8-48C4-A200-58CAB36FD2A2} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O9 - Extra 'Tools' menuitem: Spybot - Search & Destroy Configuration - {DFB852A3-47F8-48C4-A200-58CAB36FD2A2} - C:\PROGRA~1\SPYBOT~1\SDHelper.dll
O9 - Extra button: (no name) - {e2e2dd38-d088-4134-82b7-f2ba38496583} - C:\WINDOWS\Network Diagnostic\xpnetdiag.exe
O9 - Extra 'Tools' menuitem: @xpsp3res.dll,-20001 - {e2e2dd38-d088-4134-82b7-f2ba38496583} - C:\WINDOWS\Network Diagnostic\xpnetdiag.exe
O9 - Extra button: Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O9 - Extra 'Tools' menuitem: Windows Messenger - {FB5F1910-F110-11d2-BB9E-00C04F795683} - C:\Program Files\Messenger\msmsgs.exe
O18 - Protocol: linkscanner - {F274614C-63F8-47D5-A4D1-FBDDE494F8D1} - C:\Program Files\AVG\AVG8\avgpp.dll
O20 - Winlogon Notify: avgrsstarter - C:\WINDOWS\SYSTEM32\avgrsstx.dll
O23 - Service: Java Quick Starter (JavaQuickStarterService) - Sun Microsystems, Inc. - C:\Program Files\Java\jre6\bin\jqs.exe
O23 - Service: LexBce Server (LexBceS) - Lexmark International, Inc. - C:\WINDOWS\system32\LEXBCES.EXE
O23 - Service: NVIDIA Driver Helper Service (NVSvc) - NVIDIA Corporation - C:\WINDOWS\system32\nvsvc32.exe
--
End of file - 5414 bytes
Malwarebytes' Anti-Malware 1.33
Database version: 1712
Windows 5.1.2600 Service Pack 3
2/1/2009 8:29:54 PM
mbam-log-2009-02-01 (20-29-54).txt
Scan type: Full Scan (C:\|)
Objects scanned: 73171
Time elapsed: 22 minute(s), 34 second(s)
Memory Processes Infected: 0
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 0
Registry Data Items Infected: 2
Folders Infected: 0
Files Infected: 0
Memory Processes Infected:
(No malicious items detected)
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
(No malicious items detected)
Registry Data Items Infected:
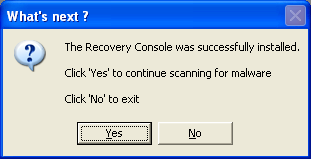
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit (Trojan.Agent) -> Data: c:\windows\system32\userinit.exe -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit (Trojan.Agent) -> Data: system32\userinit.exe -> Quarantined and deleted successfully.
Folders Infected:
(No malicious items detected)
Files Infected:
(No malicious items detected)















 Sign In
Sign In Create Account
Create Account

