INFECTED generic host process System and Browser after affect after Vi
Started by
poweradmin
, Dec 04 2010 07:05 PM
#31

 Posted 05 December 2010 - 03:33 PM
Posted 05 December 2010 - 03:33 PM

#32

 Posted 05 December 2010 - 03:35 PM
Posted 05 December 2010 - 03:35 PM

Proceeding there to complete now...
#33

 Posted 05 December 2010 - 03:43 PM
Posted 05 December 2010 - 03:43 PM

ok
#34

 Posted 05 December 2010 - 03:44 PM
Posted 05 December 2010 - 03:44 PM

I am on my other pc , that after this should be a breeze to correct lol. Combo fix is running.
#35

 Posted 05 December 2010 - 03:47 PM
Posted 05 December 2010 - 03:47 PM

Just to note: Wierd , told me need to install the MS recovery, but told me that I was not connected to the internet. Not true so, I clicked proceed and it installing now...
#36

 Posted 05 December 2010 - 03:51 PM
Posted 05 December 2010 - 03:51 PM

Scan is in process, but stopped. Warning box "Detected the presence of rootkit activity and needs to reboot" The reboot is in pocess. But bit worried about that
#37

 Posted 05 December 2010 - 03:53 PM
Posted 05 December 2010 - 03:53 PM

Combofix is running - but on a blue screen - Reboot did not come back with the GUI
#38

 Posted 05 December 2010 - 03:53 PM
Posted 05 December 2010 - 03:53 PM

Okay. Let ComboFix reboot, and it should proceed with running its scan.
#39

 Posted 05 December 2010 - 04:00 PM
Posted 05 December 2010 - 04:00 PM

Okay. ComboFix should still be running through a number of steps.
#40

 Posted 05 December 2010 - 04:05 PM
Posted 05 December 2010 - 04:05 PM

ok- noticing - Thank you
#41

 Posted 05 December 2010 - 04:21 PM
Posted 05 December 2010 - 04:21 PM

ComboFix 10-12-04.02 - Libia 12/05/2010 16:53:43.1.1 - x86
Microsoft Windows XP Professional 5.1.2600.3.1252.1.1033.18.1271.914 [GMT -5:00]
Running from: c:\documents and settings\Libia\Desktop\ComboFix.exe
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
c:\documents and settings\Libia\Application Data\Adobe\AdobeUpdate .exe
c:\documents and settings\Libia\Application Data\Adobe\plugs
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}\chrome.manifest
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}\chrome\content\_cfg.js
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}\chrome\content\overlay.xul
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}\install.rdf
c:\documents and settings\Libia\Recent\Thumbs.db
c:\windows\ocuzozaw.dll
E:\install.exe
.
\\.\PhysicalDrive0 - Bootkit TDL4 was found and disinfected
.
((((((((((((((((((((((((( Files Created from 2010-11-05 to 2010-12-05 )))))))))))))))))))))))))))))))
.
2010-12-05 18:45 . 2010-12-05 18:45 -------- dc----w- C:\_OTL
2010-12-04 03:37 . 2010-11-29 22:42 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2010-12-04 03:37 . 2010-11-29 22:42 20952 ----a-w- c:\windows\system32\drivers\mbam.sys
2010-12-04 02:49 . 2010-12-04 02:49 -------- d-sh--w- c:\documents and settings\NetworkService\IETldCache
2010-11-06 16:37 . 2010-11-06 16:37 103864 ----a-w- c:\program files\Mozilla Firefox\plugins\nppdf32.dll
2010-11-06 16:37 . 2010-11-06 16:37 103864 ----a-w- c:\program files\Internet Explorer\PLUGINS\nppdf32.dll
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2010-09-18 16:23 . 2004-08-04 07:56 974848 ----a-w- c:\windows\system32\mfc42u.dll
2010-09-18 06:53 . 2004-08-04 07:56 974848 ----a-w- c:\windows\system32\mfc42.dll
2010-09-18 06:53 . 2001-08-18 05:36 954368 ----a-w- c:\windows\system32\mfc40.dll
2010-09-18 06:53 . 2001-08-18 05:36 953856 ----a-w- c:\windows\system32\mfc40u.dll
2010-09-10 05:58 . 2004-08-04 07:56 916480 ----a-w- c:\windows\system32\wininet.dll
2010-09-10 05:58 . 2004-08-04 07:56 1469440 ------w- c:\windows\system32\inetcpl.cpl
2010-09-10 05:58 . 2004-08-04 07:56 43520 ----a-w- c:\windows\system32\licmgr10.dll
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"Adobe Version Cue CS2"="c:\program files\Adobe\Adobe Version Cue CS2\ControlPanel\VersionCueCS2Tray.exe" [2005-04-04 856064]
"igfxtray"="c:\windows\system32\igfxtray.exe" [2005-09-20 94208]
"igfxhkcmd"="c:\windows\system32\hkcmd.exe" [2005-09-20 77824]
"igfxpers"="c:\windows\system32\igfxpers.exe" [2005-09-20 114688]
"Adobe Reader Speed Launcher"="e:\program files\Adobe\adobereader92\theinstalledreader\Reader\Reader_sl.exe" [2010-09-23 35760]
c:\documents and settings\All Users\Start Menu\Programs\Startup\
Adobe Acrobat Speed Launcher.lnk - c:\windows\Installer\{AC76BA86-1033-0000-7760-000000000002}\SC_Acrobat.exe [2006-6-20 25214]
Adobe Gamma.lnk - c:\program files\Common Files\Adobe\Calibration\Adobe Gamma Loader.exe [2005-3-16 113664]
QuickBooks Update Agent.lnk - c:\program files\Common Files\Intuit\QuickBooks\QBUpdate\qbupdate.exe [2009-9-16 972064]
Windows Search.lnk - c:\program files\Windows Desktop Search\WindowsSearch.exe [2008-5-26 123904]
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecAntiVirus]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecFirewall]
"DisableMonitoring"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"c:\\Program Files\\Adobe\\Adobe Version Cue CS2\\bin\\VersionCueCS2.exe"=
"c:\\Program Files\\Macromedia\\Dreamweaver 8\\Dreamweaver.exe"=
"c:\\Program Files\\GlobalSCAPE\\CuteFTP 7 Home\\ftpte.exe"=
"%windir%\\Network Diagnostic\\xpnetdiag.exe"=
"c:\\Program Files\\Microsoft Office\\Office12\\OUTLOOK.EXE"=
"e:\\Program Files\\Intuit\\QuickBooks 2008\\QBDBMgrN.exe"=
"c:\\WINDOWS\\system32\\LEXPPS.EXE"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"3389:TCP"= 3389:TCP:*:Disabled:@xpsp2res.dll,-22009
R2 FreeAgentGoNext Service;Seagate Service;e:\seagate\Sync\FreeAgentService.exe [9/25/2009 10:32 PM 189736]
R3 seehcri;Sony Ericsson seehcri Device Driver;c:\windows\system32\drivers\seehcri.sys [9/5/2009 10:53 AM 27632]
[HKEY_LOCAL_MACHINE\software\microsoft\active setup\installed components\{A509B1FF-37FF-4bFF-8CFF-4F3A747040FF}]
2009-03-08 09:32 128512 ----a-w- c:\windows\system32\advpack.dll
.
.
------- Supplementary Scan -------
.
uSearchMigratedDefaultURL = hxxp://search.yahoo.com/search?p={searchTerms}&ei=utf-8&fr=b1ie7
uStart Page = hxxp://www.google.com/
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~2\Office12\EXCEL.EXE/3000
FF - ProfilePath - c:\documents and settings\Libia\Application Data\Mozilla\Firefox\Profiles\rfsy8jmh.default\
FF - prefs.js: browser.startup.homepage - hxxp://www.google.com/
FF - plugin: c:\program files\Mozilla Firefox\plugins\npOGAPlugin.dll
FF - plugin: e:\program files\Adobe\adobereader92\theinstalledreader\Reader\browser\nppdf32.dll
FF - HiddenExtension: Microsoft .NET Framework Assistant: {20a82645-c095-46ed-80e3-08825760534b} - c:\windows\Microsoft.NET\Framework\v3.5\Windows Presentation Foundation\DotNetAssistantExtension\
FF - Extension: Default: {972ce4c6-7e08-4474-a285-3208198ce6fd} - c:\program files\Mozilla Firefox\extensions\{972ce4c6-7e08-4474-a285-3208198ce6fd}
FF - Extension: Java Console: {CAFEEFAC-0016-0000-0012-ABCDEFFEDCBA} - c:\program files\Mozilla Firefox\extensions\{CAFEEFAC-0016-0000-0012-ABCDEFFEDCBA}
FF - Extension: Java Console: {CAFEEFAC-0016-0000-0013-ABCDEFFEDCBA} - c:\program files\Mozilla Firefox\extensions\{CAFEEFAC-0016-0000-0013-ABCDEFFEDCBA}
FF - Extension: Microsoft .NET Framework Assistant: {20a82645-c095-46ed-80e3-08825760534b} - c:\documents and settings\Libia\Application Data\Mozilla\Firefox\Profiles\rfsy8jmh.default\extensions\{20a82645-c095-46ed-80e3-08825760534b}
FF - Extension: Microsoft .NET Framework Assistant: {20a82645-c095-46ed-80e3-08825760534b} - c:\windows\Microsoft.NET\Framework\v3.5\Windows Presentation Foundation\DotNetAssistantExtension
.
- - - - ORPHANS REMOVED - - - -
HKCU-Run-BgMonitor_{79662E04-7C6C-4d9f-84C7-88D8A56B10AA} - c:\program files\Common Files\Ahead\lib\NMBgMonitor.exe
HKLM-Run-Mcocixatabivepa - c:\windows\ocuzozaw.dll
**************************************************************************
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2010-12-05 17:08
Windows 5.1.2600 Service Pack 3 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
Stealth MBR rootkit/Mebroot/Sinowal/TDL4 detector 0.4.2 by Gmer, http://www.gmer.net
Windows 5.1.2600 Disk: ST340015A rev.3.15 -> Harddisk0\DR0 -> \Device\Ide\IdeDeviceP0T1L0-c
device: opened successfully
user: MBR read successfully
Disk trace:
called modules: ntoskrnl.exe catchme.sys CLASSPNP.SYS disk.sys ACPI.sys hal.dll >>UNKNOWN [0x8A37E555]<<
c:\docume~1\Libia\LOCALS~1\Temp\catchme.sys
_asm { PUSH EBP; MOV EBP, ESP; PUSH ECX; MOV EAX, [EBP+0x8]; CMP EAX, [0x8a3847b0]; MOV EAX, [0x8a38482c]; PUSH EBX; PUSH ESI; MOV ESI, [EBP+0xc]; MOV EBX, [ESI+0x60]; PUSH EDI; JNZ 0x20; MOV [EBP+0x8], EAX; }
1 nt!IofCallDriver[0x804E37D5] -> \Device\Harddisk0\DR0[0x8A3F2AB8]
3 CLASSPNP[0xF7637FD7] -> nt!IofCallDriver[0x804E37D5] -> \Device\00000059[0x8A44C030]
5 ACPI[0xF75AE620] -> nt!IofCallDriver[0x804E37D5] -> [0x8A3FC030]
\Driver\atapi[0x8A434F38] -> IRP_MJ_CREATE -> 0x8A37E555
kernel: MBR read successfully
_asm { XOR AX, AX; MOV SS, AX; MOV SP, 0x7c00; STI ; PUSH AX; POP ES; PUSH AX; POP DS; CLD ; MOV SI, 0x7c1b; MOV DI, 0x61b; PUSH AX; PUSH DI; MOV CX, 0x1e5; REP MOVSB ; RETF ; MOV BP, 0x7be; MOV CL, 0x4; CMP [BP+0x0], CH; JL 0x2e; JNZ 0x3a; }
detected disk devices:
\Device\Ide\IdeDeviceP0T0L0-4 -> \??\IDE#DiskST340015A_______________________________3.15____#4c354e4153305a45202020202020202020202020#{53f56307-b6bf-11d0-94f2-00a0c91efb8b} device not found
detected hooks:
\Driver\atapi DriverStartIo -> 0x8A37E39B
user != kernel MBR !!!
sectors 78165358 (+255): user != kernel
Warning: possible TDL4 rootkit infection !
TDL4 rootkit infection detected ! Use: "mbr.exe -f" to fix.
**************************************************************************
.
--------------------- LOCKED REGISTRY KEYS ---------------------
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}]
@Denied: (A 2) (Everyone)
@="FlashBroker"
"LocalizedString"="@c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10l_ActiveX.exe,-101"
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\Elevation]
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\LocalServer32]
@="c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10l_ActiveX.exe"
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}]
@Denied: (A 2) (Everyone)
@="IFlashBroker4"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\ProxyStubClsid32]
@="{00020424-0000-0000-C000-000000000046}"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
"Version"="1.0"
.
--------------------- DLLs Loaded Under Running Processes ---------------------
- - - - - - - > 'winlogon.exe'(652)
c:\windows\system32\WININET.dll
- - - - - - - > 'lsass.exe'(712)
c:\windows\system32\WININET.dll
.
Completion time: 2010-12-05 17:14:35
ComboFix-quarantined-files.txt 2010-12-05 22:14
Pre-Run: 16,964,136,960 bytes free
Post-Run: 17,004,331,008 bytes free
WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
[boot loader]
timeout=2
default=multi(0)disk(0)rdisk(0)partition(1)\WINDOWS
[operating systems]
c:\cmdcons\BOOTSECT.DAT="Microsoft Windows Recovery Console" /cmdcons
UnsupportedDebug="do not select this" /debug
multi(0)disk(0)rdisk(0)partition(1)\WINDOWS="Microsoft Windows XP Professional" /noexecute=optin /fastdetect
- - End Of File - - 239EF85417E89DDD57A52872D9DE12EB
Microsoft Windows XP Professional 5.1.2600.3.1252.1.1033.18.1271.914 [GMT -5:00]
Running from: c:\documents and settings\Libia\Desktop\ComboFix.exe
.
((((((((((((((((((((((((((((((((((((((( Other Deletions )))))))))))))))))))))))))))))))))))))))))))))))))
.
c:\documents and settings\Libia\Application Data\Adobe\AdobeUpdate .exe
c:\documents and settings\Libia\Application Data\Adobe\plugs
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}\chrome.manifest
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}\chrome\content\_cfg.js
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}\chrome\content\overlay.xul
c:\documents and settings\Libia\Local Settings\Application Data\{FAB718ED-3E3A-43F8-8FEC-A1C0DEFD1C33}\install.rdf
c:\documents and settings\Libia\Recent\Thumbs.db
c:\windows\ocuzozaw.dll
E:\install.exe
.
\\.\PhysicalDrive0 - Bootkit TDL4 was found and disinfected
.
((((((((((((((((((((((((( Files Created from 2010-11-05 to 2010-12-05 )))))))))))))))))))))))))))))))
.
2010-12-05 18:45 . 2010-12-05 18:45 -------- dc----w- C:\_OTL
2010-12-04 03:37 . 2010-11-29 22:42 38224 ----a-w- c:\windows\system32\drivers\mbamswissarmy.sys
2010-12-04 03:37 . 2010-11-29 22:42 20952 ----a-w- c:\windows\system32\drivers\mbam.sys
2010-12-04 02:49 . 2010-12-04 02:49 -------- d-sh--w- c:\documents and settings\NetworkService\IETldCache
2010-11-06 16:37 . 2010-11-06 16:37 103864 ----a-w- c:\program files\Mozilla Firefox\plugins\nppdf32.dll
2010-11-06 16:37 . 2010-11-06 16:37 103864 ----a-w- c:\program files\Internet Explorer\PLUGINS\nppdf32.dll
.
(((((((((((((((((((((((((((((((((((((((( Find3M Report ))))))))))))))))))))))))))))))))))))))))))))))))))))
.
2010-09-18 16:23 . 2004-08-04 07:56 974848 ----a-w- c:\windows\system32\mfc42u.dll
2010-09-18 06:53 . 2004-08-04 07:56 974848 ----a-w- c:\windows\system32\mfc42.dll
2010-09-18 06:53 . 2001-08-18 05:36 954368 ----a-w- c:\windows\system32\mfc40.dll
2010-09-18 06:53 . 2001-08-18 05:36 953856 ----a-w- c:\windows\system32\mfc40u.dll
2010-09-10 05:58 . 2004-08-04 07:56 916480 ----a-w- c:\windows\system32\wininet.dll
2010-09-10 05:58 . 2004-08-04 07:56 1469440 ------w- c:\windows\system32\inetcpl.cpl
2010-09-10 05:58 . 2004-08-04 07:56 43520 ----a-w- c:\windows\system32\licmgr10.dll
.
((((((((((((((((((((((((((((((((((((( Reg Loading Points ))))))))))))))))))))))))))))))))))))))))))))))))))
.
.
*Note* empty entries & legit default entries are not shown
REGEDIT4
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"Adobe Version Cue CS2"="c:\program files\Adobe\Adobe Version Cue CS2\ControlPanel\VersionCueCS2Tray.exe" [2005-04-04 856064]
"igfxtray"="c:\windows\system32\igfxtray.exe" [2005-09-20 94208]
"igfxhkcmd"="c:\windows\system32\hkcmd.exe" [2005-09-20 77824]
"igfxpers"="c:\windows\system32\igfxpers.exe" [2005-09-20 114688]
"Adobe Reader Speed Launcher"="e:\program files\Adobe\adobereader92\theinstalledreader\Reader\Reader_sl.exe" [2010-09-23 35760]
c:\documents and settings\All Users\Start Menu\Programs\Startup\
Adobe Acrobat Speed Launcher.lnk - c:\windows\Installer\{AC76BA86-1033-0000-7760-000000000002}\SC_Acrobat.exe [2006-6-20 25214]
Adobe Gamma.lnk - c:\program files\Common Files\Adobe\Calibration\Adobe Gamma Loader.exe [2005-3-16 113664]
QuickBooks Update Agent.lnk - c:\program files\Common Files\Intuit\QuickBooks\QBUpdate\qbupdate.exe [2009-9-16 972064]
Windows Search.lnk - c:\program files\Windows Desktop Search\WindowsSearch.exe [2008-5-26 123904]
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecAntiVirus]
"DisableMonitoring"=dword:00000001
[HKEY_LOCAL_MACHINE\software\microsoft\security center\Monitoring\SymantecFirewall]
"DisableMonitoring"=dword:00000001
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\AuthorizedApplications\List]
"%windir%\\system32\\sessmgr.exe"=
"c:\\Program Files\\Adobe\\Adobe Version Cue CS2\\bin\\VersionCueCS2.exe"=
"c:\\Program Files\\Macromedia\\Dreamweaver 8\\Dreamweaver.exe"=
"c:\\Program Files\\GlobalSCAPE\\CuteFTP 7 Home\\ftpte.exe"=
"%windir%\\Network Diagnostic\\xpnetdiag.exe"=
"c:\\Program Files\\Microsoft Office\\Office12\\OUTLOOK.EXE"=
"e:\\Program Files\\Intuit\\QuickBooks 2008\\QBDBMgrN.exe"=
"c:\\WINDOWS\\system32\\LEXPPS.EXE"=
[HKLM\~\services\sharedaccess\parameters\firewallpolicy\standardprofile\GloballyOpenPorts\List]
"3389:TCP"= 3389:TCP:*:Disabled:@xpsp2res.dll,-22009
R2 FreeAgentGoNext Service;Seagate Service;e:\seagate\Sync\FreeAgentService.exe [9/25/2009 10:32 PM 189736]
R3 seehcri;Sony Ericsson seehcri Device Driver;c:\windows\system32\drivers\seehcri.sys [9/5/2009 10:53 AM 27632]
[HKEY_LOCAL_MACHINE\software\microsoft\active setup\installed components\{A509B1FF-37FF-4bFF-8CFF-4F3A747040FF}]
2009-03-08 09:32 128512 ----a-w- c:\windows\system32\advpack.dll
.
.
------- Supplementary Scan -------
.
uSearchMigratedDefaultURL = hxxp://search.yahoo.com/search?p={searchTerms}&ei=utf-8&fr=b1ie7
uStart Page = hxxp://www.google.com/
IE: E&xport to Microsoft Excel - c:\progra~1\MICROS~2\Office12\EXCEL.EXE/3000
FF - ProfilePath - c:\documents and settings\Libia\Application Data\Mozilla\Firefox\Profiles\rfsy8jmh.default\
FF - prefs.js: browser.startup.homepage - hxxp://www.google.com/
FF - plugin: c:\program files\Mozilla Firefox\plugins\npOGAPlugin.dll
FF - plugin: e:\program files\Adobe\adobereader92\theinstalledreader\Reader\browser\nppdf32.dll
FF - HiddenExtension: Microsoft .NET Framework Assistant: {20a82645-c095-46ed-80e3-08825760534b} - c:\windows\Microsoft.NET\Framework\v3.5\Windows Presentation Foundation\DotNetAssistantExtension\
FF - Extension: Default: {972ce4c6-7e08-4474-a285-3208198ce6fd} - c:\program files\Mozilla Firefox\extensions\{972ce4c6-7e08-4474-a285-3208198ce6fd}
FF - Extension: Java Console: {CAFEEFAC-0016-0000-0012-ABCDEFFEDCBA} - c:\program files\Mozilla Firefox\extensions\{CAFEEFAC-0016-0000-0012-ABCDEFFEDCBA}
FF - Extension: Java Console: {CAFEEFAC-0016-0000-0013-ABCDEFFEDCBA} - c:\program files\Mozilla Firefox\extensions\{CAFEEFAC-0016-0000-0013-ABCDEFFEDCBA}
FF - Extension: Microsoft .NET Framework Assistant: {20a82645-c095-46ed-80e3-08825760534b} - c:\documents and settings\Libia\Application Data\Mozilla\Firefox\Profiles\rfsy8jmh.default\extensions\{20a82645-c095-46ed-80e3-08825760534b}
FF - Extension: Microsoft .NET Framework Assistant: {20a82645-c095-46ed-80e3-08825760534b} - c:\windows\Microsoft.NET\Framework\v3.5\Windows Presentation Foundation\DotNetAssistantExtension
.
- - - - ORPHANS REMOVED - - - -
HKCU-Run-BgMonitor_{79662E04-7C6C-4d9f-84C7-88D8A56B10AA} - c:\program files\Common Files\Ahead\lib\NMBgMonitor.exe
HKLM-Run-Mcocixatabivepa - c:\windows\ocuzozaw.dll
**************************************************************************
catchme 0.3.1398 W2K/XP/Vista - rootkit/stealth malware detector by Gmer, http://www.gmer.net
Rootkit scan 2010-12-05 17:08
Windows 5.1.2600 Service Pack 3 NTFS
scanning hidden processes ...
scanning hidden autostart entries ...
scanning hidden files ...
scan completed successfully
hidden files: 0
**************************************************************************
Stealth MBR rootkit/Mebroot/Sinowal/TDL4 detector 0.4.2 by Gmer, http://www.gmer.net
Windows 5.1.2600 Disk: ST340015A rev.3.15 -> Harddisk0\DR0 -> \Device\Ide\IdeDeviceP0T1L0-c
device: opened successfully
user: MBR read successfully
Disk trace:
called modules: ntoskrnl.exe catchme.sys CLASSPNP.SYS disk.sys ACPI.sys hal.dll >>UNKNOWN [0x8A37E555]<<
c:\docume~1\Libia\LOCALS~1\Temp\catchme.sys
_asm { PUSH EBP; MOV EBP, ESP; PUSH ECX; MOV EAX, [EBP+0x8]; CMP EAX, [0x8a3847b0]; MOV EAX, [0x8a38482c]; PUSH EBX; PUSH ESI; MOV ESI, [EBP+0xc]; MOV EBX, [ESI+0x60]; PUSH EDI; JNZ 0x20; MOV [EBP+0x8], EAX; }
1 nt!IofCallDriver[0x804E37D5] -> \Device\Harddisk0\DR0[0x8A3F2AB8]
3 CLASSPNP[0xF7637FD7] -> nt!IofCallDriver[0x804E37D5] -> \Device\00000059[0x8A44C030]
5 ACPI[0xF75AE620] -> nt!IofCallDriver[0x804E37D5] -> [0x8A3FC030]
\Driver\atapi[0x8A434F38] -> IRP_MJ_CREATE -> 0x8A37E555
kernel: MBR read successfully
_asm { XOR AX, AX; MOV SS, AX; MOV SP, 0x7c00; STI ; PUSH AX; POP ES; PUSH AX; POP DS; CLD ; MOV SI, 0x7c1b; MOV DI, 0x61b; PUSH AX; PUSH DI; MOV CX, 0x1e5; REP MOVSB ; RETF ; MOV BP, 0x7be; MOV CL, 0x4; CMP [BP+0x0], CH; JL 0x2e; JNZ 0x3a; }
detected disk devices:
\Device\Ide\IdeDeviceP0T0L0-4 -> \??\IDE#DiskST340015A_______________________________3.15____#4c354e4153305a45202020202020202020202020#{53f56307-b6bf-11d0-94f2-00a0c91efb8b} device not found
detected hooks:
\Driver\atapi DriverStartIo -> 0x8A37E39B
user != kernel MBR !!!
sectors 78165358 (+255): user != kernel
Warning: possible TDL4 rootkit infection !
TDL4 rootkit infection detected ! Use: "mbr.exe -f" to fix.
**************************************************************************
.
--------------------- LOCKED REGISTRY KEYS ---------------------
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}]
@Denied: (A 2) (Everyone)
@="FlashBroker"
"LocalizedString"="@c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10l_ActiveX.exe,-101"
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\Elevation]
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\LocalServer32]
@="c:\\WINDOWS\\system32\\Macromed\\Flash\\FlashUtil10l_ActiveX.exe"
[HKEY_LOCAL_MACHINE\software\Classes\CLSID\{A483C63A-CDBC-426E-BF93-872502E8144E}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}]
@Denied: (A 2) (Everyone)
@="IFlashBroker4"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\ProxyStubClsid32]
@="{00020424-0000-0000-C000-000000000046}"
[HKEY_LOCAL_MACHINE\software\Classes\Interface\{E3F2C3CB-5EB8-4A04-B22C-7E3B4B6AF30F}\TypeLib]
@="{FAB3E735-69C7-453B-A446-B6823C6DF1C9}"
"Version"="1.0"
.
--------------------- DLLs Loaded Under Running Processes ---------------------
- - - - - - - > 'winlogon.exe'(652)
c:\windows\system32\WININET.dll
- - - - - - - > 'lsass.exe'(712)
c:\windows\system32\WININET.dll
.
Completion time: 2010-12-05 17:14:35
ComboFix-quarantined-files.txt 2010-12-05 22:14
Pre-Run: 16,964,136,960 bytes free
Post-Run: 17,004,331,008 bytes free
WindowsXP-KB310994-SP2-Pro-BootDisk-ENU.exe
[boot loader]
timeout=2
default=multi(0)disk(0)rdisk(0)partition(1)\WINDOWS
[operating systems]
c:\cmdcons\BOOTSECT.DAT="Microsoft Windows Recovery Console" /cmdcons
UnsupportedDebug="do not select this" /debug
multi(0)disk(0)rdisk(0)partition(1)\WINDOWS="Microsoft Windows XP Professional" /noexecute=optin /fastdetect
- - End Of File - - 239EF85417E89DDD57A52872D9DE12EB
#42

 Posted 05 December 2010 - 04:21 PM
Posted 05 December 2010 - 04:21 PM

I was able to load IE but getting pop ups now about winning crap
#43

 Posted 05 December 2010 - 04:24 PM
Posted 05 December 2010 - 04:24 PM

Hello,
Run this tool:
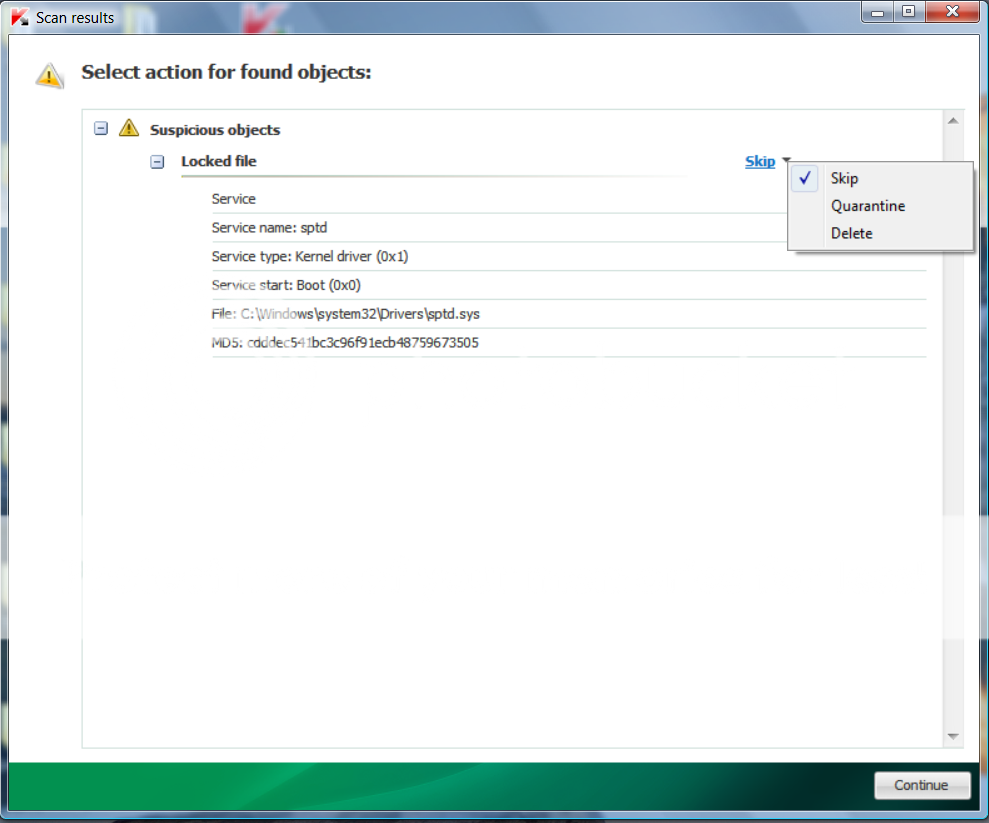
Running TDSSKiller
Please read carefully and follow these steps.
Run this tool:
Running TDSSKiller
Please read carefully and follow these steps.
- Download TDSSKiller and save it to your Desktop.
- Extract its contents to your desktop.
- Once extracted, open the TDSSKiller folder and doubleclick on TDSSKiller.exe to run the application, then on Start Scan.
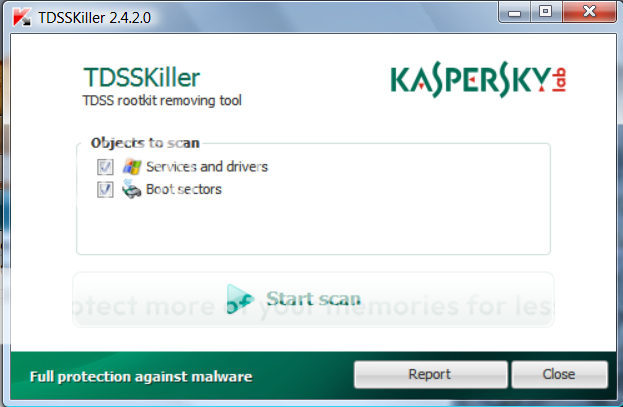
- If an infected file is detected, the default action will be Cure, click on Continue.

- If a suspicious file is detected, the default action will be Skip, click on Continue.
- It may ask you to reboot the computer to complete the process. Click on Reboot Now.

- If no reboot is require, click on Report. A log file should appear. Please copy and paste the contents of that file here.
- If a reboot is required, the report can also be found in your root directory, (usually C:\ folder) in the form of "TDSSKiller.[Version]_[Date]_[Time]_log.txt". Please copy and paste the contents of that file here.
#44

 Posted 05 December 2010 - 04:36 PM
Posted 05 December 2010 - 04:36 PM

Not finding the log file here
#45

 Posted 05 December 2010 - 04:40 PM
Posted 05 December 2010 - 04:40 PM

Found it duhhhhhhh sorry you told me...
2010/12/05 17:28:38.0093 TDSS rootkit removing tool 2.4.10.1 Dec 2 2010 12:28:01
2010/12/05 17:28:38.0093 ================================================================================
2010/12/05 17:28:38.0093 SystemInfo:
2010/12/05 17:28:38.0093
2010/12/05 17:28:38.0093 OS Version: 5.1.2600 ServicePack: 3.0
2010/12/05 17:28:38.0093 Product type: Workstation
2010/12/05 17:28:38.0093 ComputerName: TBBS02
2010/12/05 17:28:38.0093 UserName: Libia
2010/12/05 17:28:38.0093 Windows directory: C:\WINDOWS
2010/12/05 17:28:38.0093 System windows directory: C:\WINDOWS
2010/12/05 17:28:38.0093 Processor architecture: Intel x86
2010/12/05 17:28:38.0093 Number of processors: 1
2010/12/05 17:28:38.0093 Page size: 0x1000
2010/12/05 17:28:38.0093 Boot type: Normal boot
2010/12/05 17:28:38.0093 ================================================================================
2010/12/05 17:28:38.0343 Initialize success
2010/12/05 17:28:51.0359 ================================================================================
2010/12/05 17:28:51.0359 Scan started
2010/12/05 17:28:51.0359 Mode: Manual;
2010/12/05 17:28:51.0359 ================================================================================
2010/12/05 17:28:55.0437 a016bus (b021d0ae4605ce5df67f06e741278cdf) C:\WINDOWS\system32\DRIVERS\a016bus.sys
2010/12/05 17:28:56.0250 a016mdfl (5b6bc2de851012906d4aae84c802e3f2) C:\WINDOWS\system32\DRIVERS\a016mdfl.sys
2010/12/05 17:28:56.0921 a016mdm (c80cffb5819ccfc97f2b09e2259dfde6) C:\WINDOWS\system32\DRIVERS\a016mdm.sys
2010/12/05 17:28:57.0500 a016mgmt (415243177ff67d3cfba44d931b809bf3) C:\WINDOWS\system32\DRIVERS\a016mgmt.sys
2010/12/05 17:28:57.0796 a016obex (3a853f9b8b69541cde714a83a0a6434e) C:\WINDOWS\system32\DRIVERS\a016obex.sys
2010/12/05 17:28:58.0703 ac97intc (0f2d66d5f08ebe2f77bb904288dcf6f0) C:\WINDOWS\system32\drivers\ac97intc.sys
2010/12/05 17:28:58.0921 ACPI (8fd99680a539792a30e97944fdaecf17) C:\WINDOWS\system32\DRIVERS\ACPI.sys
2010/12/05 17:28:59.0187 ACPIEC (9859c0f6936e723e4892d7141b1327d5) C:\WINDOWS\system32\drivers\ACPIEC.sys
2010/12/05 17:28:59.0421 adpu160m (9a11864873da202c996558b2106b0bbc) C:\WINDOWS\system32\DRIVERS\adpu160m.sys
2010/12/05 17:28:59.0671 adpu320 (0ea9b1f0c6c90a509c8603775366adb7) C:\WINDOWS\system32\DRIVERS\adpu320.sys
2010/12/05 17:28:59.0890 aeaudio (11c04b17ed2abbb4833694bcd644ac90) C:\WINDOWS\system32\drivers\aeaudio.sys
2010/12/05 17:29:00.0125 aec (8bed39e3c35d6a489438b8141717a557) C:\WINDOWS\system32\drivers\aec.sys
2010/12/05 17:29:00.0359 AFD (7e775010ef291da96ad17ca4b17137d7) C:\WINDOWS\System32\drivers\afd.sys
2010/12/05 17:29:00.0640 AgereSoftModem (593aefc67283d409f34cc1245d00a509) C:\WINDOWS\system32\DRIVERS\AGRSM.sys
2010/12/05 17:29:01.0093 aic78u2 (19dd0fb48b0c18892f70e2e7d61a1529) C:\WINDOWS\system32\DRIVERS\aic78u2.sys
2010/12/05 17:29:01.0343 aic78xx (b7fe594a7468aa0132deb03fb8e34326) C:\WINDOWS\system32\DRIVERS\aic78xx.sys
2010/12/05 17:29:02.0593 AsyncMac (b153affac761e7f5fcfa822b9c4e97bc) C:\WINDOWS\system32\DRIVERS\asyncmac.sys
2010/12/05 17:29:02.0812 atapi (9f3a2f5aa6875c72bf062c712cfa2674) C:\WINDOWS\system32\DRIVERS\atapi.sys
2010/12/05 17:29:03.0234 Atmarpc (9916c1225104ba14794209cfa8012159) C:\WINDOWS\system32\DRIVERS\atmarpc.sys
2010/12/05 17:29:04.0250 audstub (d9f724aa26c010a217c97606b160ed68) C:\WINDOWS\system32\DRIVERS\audstub.sys
2010/12/05 17:29:04.0562 Beep (da1f27d85e0d1525f6621372e7b685e9) C:\WINDOWS\system32\drivers\Beep.sys
2010/12/05 17:29:04.0984 cbidf2k (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\drivers\cbidf2k.sys
2010/12/05 17:29:05.0390 Cdaudio (c1b486a7658353d33a10cc15211a873b) C:\WINDOWS\system32\drivers\Cdaudio.sys
2010/12/05 17:29:05.0656 Cdfs (c885b02847f5d2fd45a24e219ed93b32) C:\WINDOWS\system32\drivers\Cdfs.sys
2010/12/05 17:29:05.0937 Cdrom (1f4260cc5b42272d71f79e570a27a4fe) C:\WINDOWS\system32\DRIVERS\cdrom.sys
2010/12/05 17:29:07.0515 DgiVecp (a5034f77b278f07e224fe07cf98a8b76) C:\WINDOWS\system32\Drivers\DgiVecp.sys
2010/12/05 17:29:08.0171 Disk (044452051f3e02e7963599fc8f4f3e25) C:\WINDOWS\system32\DRIVERS\disk.sys
2010/12/05 17:29:08.0468 dmboot (d992fe1274bde0f84ad826acae022a41) C:\WINDOWS\system32\drivers\dmboot.sys
2010/12/05 17:29:08.0750 dmio (7c824cf7bbde77d95c08005717a95f6f) C:\WINDOWS\system32\drivers\dmio.sys
2010/12/05 17:29:08.0984 dmload (e9317282a63ca4d188c0df5e09c6ac5f) C:\WINDOWS\system32\drivers\dmload.sys
2010/12/05 17:29:09.0500 DMusic (8a208dfcf89792a484e76c40e5f50b45) C:\WINDOWS\system32\drivers\DMusic.sys
2010/12/05 17:29:09.0734 dpti2o (40f3b93b4e5b0126f2f5c0a7a5e22660) C:\WINDOWS\system32\DRIVERS\dpti2o.sys
2010/12/05 17:29:10.0000 drmkaud (8f5fcff8e8848afac920905fbd9d33c8) C:\WINDOWS\system32\drivers\drmkaud.sys
2010/12/05 17:29:10.0312 E1000 (1dc189cd47ad4c8ca214b234b84ca228) C:\WINDOWS\system32\DRIVERS\e1000325.sys
2010/12/05 17:29:10.0625 E100B (afee15c5b16317ebf17f79cc1843465a) C:\WINDOWS\system32\DRIVERS\e100b325.sys
2010/12/05 17:29:10.0921 Fastfat (38d332a6d56af32635675f132548343e) C:\WINDOWS\system32\drivers\Fastfat.sys
2010/12/05 17:29:11.0187 Fdc (92cdd60b6730b9f50f6a1a0c1f8cdc81) C:\WINDOWS\system32\DRIVERS\fdc.sys
2010/12/05 17:29:11.0500 Fips (d45926117eb9fa946a6af572fbe1caa3) C:\WINDOWS\system32\drivers\Fips.sys
2010/12/05 17:29:11.0734 Flpydisk (9d27e7b80bfcdf1cdd9b555862d5e7f0) C:\WINDOWS\system32\DRIVERS\flpydisk.sys
2010/12/05 17:29:12.0031 FltMgr (b2cf4b0786f8212cb92ed2b50c6db6b0) C:\WINDOWS\system32\drivers\fltmgr.sys
2010/12/05 17:29:12.0421 Fs_Rec (3e1e2bd4f39b0e2b7dc4f4d2bcc2779a) C:\WINDOWS\system32\drivers\Fs_Rec.sys
2010/12/05 17:29:12.0671 Ftdisk (6ac26732762483366c3969c9e4d2259d) C:\WINDOWS\system32\DRIVERS\ftdisk.sys
2010/12/05 17:29:12.0937 Gpc (0a02c63c8b144bd8c86b103dee7c86a2) C:\WINDOWS\system32\DRIVERS\msgpc.sys
2010/12/05 17:29:13.0437 HidUsb (ccf82c5ec8a7326c3066de870c06daf1) C:\WINDOWS\system32\DRIVERS\hidusb.sys
2010/12/05 17:29:13.0937 HTTP (f80a415ef82cd06ffaf0d971528ead38) C:\WINDOWS\system32\Drivers\HTTP.sys
2010/12/05 17:29:14.0843 i8042prt (4a0b06aa8943c1e332520f7440c0aa30) C:\WINDOWS\system32\DRIVERS\i8042prt.sys
2010/12/05 17:29:15.0093 i81x (06b7ef73ba5f302eecc294cdf7e19702) C:\WINDOWS\system32\DRIVERS\i81xnt5.sys
2010/12/05 17:29:15.0328 iAimFP0 (7b5b44efe5eb9dadfb8ee29700885d23) C:\WINDOWS\system32\DRIVERS\wADV01nt.sys
2010/12/05 17:29:15.0906 iAimFP1 (eb1f6bab6c22ede0ba551b527475f7e9) C:\WINDOWS\system32\DRIVERS\wADV02NT.sys
2010/12/05 17:29:16.0859 iAimFP2 (03ce989d846c1aa81145cb22fcb86d06) C:\WINDOWS\system32\DRIVERS\wADV05NT.sys
2010/12/05 17:29:17.0125 iAimFP3 (525849b4469de021d5d61b4db9be3a9d) C:\WINDOWS\system32\DRIVERS\wSiINTxx.sys
2010/12/05 17:29:17.0343 iAimFP4 (589c2bcdb5bd602bf7b63d210407ef8c) C:\WINDOWS\system32\DRIVERS\wVchNTxx.sys
2010/12/05 17:29:17.0562 iAimFP5 (0308aef61941e4af478fa1a0f83812f5) C:\WINDOWS\system32\DRIVERS\wADV07nt.sys
2010/12/05 17:29:17.0796 iAimFP6 (714038a8aa5de08e12062202cd7eaeb5) C:\WINDOWS\system32\DRIVERS\wADV08nt.sys
2010/12/05 17:29:18.0109 iAimFP7 (7bb3aa595e4507a788de1cdc63f4c8c4) C:\WINDOWS\system32\DRIVERS\wADV09nt.sys
2010/12/05 17:29:18.0375 iAimTV0 (d83bdd5c059667a2f647a6be5703a4d2) C:\WINDOWS\system32\DRIVERS\wATV01nt.sys
2010/12/05 17:29:18.0625 iAimTV1 (ed968d23354daa0d7c621580c012a1f6) C:\WINDOWS\system32\DRIVERS\wATV02NT.sys
2010/12/05 17:29:18.0859 iAimTV3 (d738273f218a224c1ddac04203f27a84) C:\WINDOWS\system32\DRIVERS\wATV04nt.sys
2010/12/05 17:29:19.0093 iAimTV4 (0052d118995cbab152daabe6106d1442) C:\WINDOWS\system32\DRIVERS\wCh7xxNT.sys
2010/12/05 17:29:19.0343 iAimTV5 (791cc45de6e50445be72e8ad6401ff45) C:\WINDOWS\system32\DRIVERS\wATV10nt.sys
2010/12/05 17:29:19.0781 iAimTV6 (352fa0e98bc461ce1ce5d41f64db558d) C:\WINDOWS\system32\DRIVERS\wATV06nt.sys
2010/12/05 17:29:20.0171 ialm (9a883c3c4d91292c0d09de7c728e781c) C:\WINDOWS\system32\DRIVERS\ialmnt5.sys
2010/12/05 17:29:20.0406 Imapi (083a052659f5310dd8b6a6cb05edcf8e) C:\WINDOWS\system32\DRIVERS\imapi.sys
2010/12/05 17:29:21.0515 IntelIde (b5466a9250342a7aa0cd1fba13420678) C:\WINDOWS\system32\DRIVERS\intelide.sys
2010/12/05 17:29:21.0765 intelppm (8c953733d8f36eb2133f5bb58808b66b) C:\WINDOWS\system32\DRIVERS\intelppm.sys
2010/12/05 17:29:22.0031 Ip6Fw (3bb22519a194418d5fec05d800a19ad0) C:\WINDOWS\system32\drivers\ip6fw.sys
2010/12/05 17:29:22.0359 IpFilterDriver (731f22ba402ee4b62748adaf6363c182) C:\WINDOWS\system32\DRIVERS\ipfltdrv.sys
2010/12/05 17:29:22.0750 IpInIp (b87ab476dcf76e72010632b5550955f5) C:\WINDOWS\system32\DRIVERS\ipinip.sys
2010/12/05 17:29:23.0312 IpNat (cc748ea12c6effde940ee98098bf96bb) C:\WINDOWS\system32\DRIVERS\ipnat.sys
2010/12/05 17:29:23.0546 IPSec (23c74d75e36e7158768dd63d92789a91) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2010/12/05 17:29:23.0781 IRENUM (c93c9ff7b04d772627a3646d89f7bf89) C:\WINDOWS\system32\DRIVERS\irenum.sys
2010/12/05 17:29:24.0000 isapnp (05a299ec56e52649b1cf2fc52d20f2d7) C:\WINDOWS\system32\DRIVERS\isapnp.sys
2010/12/05 17:29:24.0406 Kbdclass (463c1ec80cd17420a542b7f36a36f128) C:\WINDOWS\system32\DRIVERS\kbdclass.sys
2010/12/05 17:29:24.0734 kbdhid (9ef487a186dea361aa06913a75b3fa99) C:\WINDOWS\system32\DRIVERS\kbdhid.sys
2010/12/05 17:29:24.0937 kmixer (692bcf44383d056aed41b045a323d378) C:\WINDOWS\system32\drivers\kmixer.sys
2010/12/05 17:29:25.0390 KSecDD (b467646c54cc746128904e1654c750c1) C:\WINDOWS\system32\drivers\KSecDD.sys
2010/12/05 17:29:25.0859 mnmdd (4ae068242760a1fb6e1a44bf4e16afa6) C:\WINDOWS\system32\drivers\mnmdd.sys
2010/12/05 17:29:26.0515 Modem (dfcbad3cec1c5f964962ae10e0bcc8e1) C:\WINDOWS\system32\drivers\Modem.sys
2010/12/05 17:29:26.0734 Mouclass (35c9e97194c8cfb8430125f8dbc34d04) C:\WINDOWS\system32\DRIVERS\mouclass.sys
2010/12/05 17:29:26.0968 mouhid (b1c303e17fb9d46e87a98e4ba6769685) C:\WINDOWS\system32\DRIVERS\mouhid.sys
2010/12/05 17:29:27.0531 MountMgr (a80b9a0bad1b73637dbcbba7df72d3fd) C:\WINDOWS\system32\drivers\MountMgr.sys
2010/12/05 17:29:27.0984 MREMPR5 (2bc9e43f55de8c30fc817ed56d0ee907) C:\PROGRA~1\COMMON~1\Motive\MREMPR5.SYS
2010/12/05 17:29:28.0203 MRENDIS5 (594b9d8194e3f4ecbf0325bd10bbeb05) C:\PROGRA~1\COMMON~1\Motive\MRENDIS5.SYS
2010/12/05 17:29:28.0421 MRxDAV (11d42bb6206f33fbb3ba0288d3ef81bd) C:\WINDOWS\system32\DRIVERS\mrxdav.sys
2010/12/05 17:29:28.0671 MRxSmb (f3aefb11abc521122b67095044169e98) C:\WINDOWS\system32\DRIVERS\mrxsmb.sys
2010/12/05 17:29:28.0968 Msfs (c941ea2454ba8350021d774daf0f1027) C:\WINDOWS\system32\drivers\Msfs.sys
2010/12/05 17:29:29.0328 MSKSSRV (d1575e71568f4d9e14ca56b7b0453bf1) C:\WINDOWS\system32\drivers\MSKSSRV.sys
2010/12/05 17:29:29.0546 MSPCLOCK (325bb26842fc7ccc1fcce2c457317f3e) C:\WINDOWS\system32\drivers\MSPCLOCK.sys
2010/12/05 17:29:29.0812 MSPQM (bad59648ba099da4a17680b39730cb3d) C:\WINDOWS\system32\drivers\MSPQM.sys
2010/12/05 17:29:30.0093 mssmbios (af5f4f3f14a8ea2c26de30f7a1e17136) C:\WINDOWS\system32\DRIVERS\mssmbios.sys
2010/12/05 17:29:30.0359 Mup (2f625d11385b1a94360bfc70aaefdee1) C:\WINDOWS\system32\drivers\Mup.sys
2010/12/05 17:29:30.0671 NDIS (1df7f42665c94b825322fae71721130d) C:\WINDOWS\system32\drivers\NDIS.sys
2010/12/05 17:29:30.0859 NdisTapi (1ab3d00c991ab086e69db84b6c0ed78f) C:\WINDOWS\system32\DRIVERS\ndistapi.sys
2010/12/05 17:29:31.0140 Ndisuio (f927a4434c5028758a842943ef1a3849) C:\WINDOWS\system32\DRIVERS\ndisuio.sys
2010/12/05 17:29:31.0359 NdisWan (edc1531a49c80614b2cfda43ca8659ab) C:\WINDOWS\system32\DRIVERS\ndiswan.sys
2010/12/05 17:29:31.0609 NDProxy (6215023940cfd3702b46abc304e1d45a) C:\WINDOWS\system32\drivers\NDProxy.sys
2010/12/05 17:29:31.0828 NetBIOS (5d81cf9a2f1a3a756b66cf684911cdf0) C:\WINDOWS\system32\DRIVERS\netbios.sys
2010/12/05 17:29:32.0343 NetBT (74b2b2f5bea5e9a3dc021d685551bd3d) C:\WINDOWS\system32\DRIVERS\netbt.sys
2010/12/05 17:29:32.0734 Npfs (3182d64ae053d6fb034f44b6def8034a) C:\WINDOWS\system32\drivers\Npfs.sys
2010/12/05 17:29:32.0984 Ntfs (78a08dd6a8d65e697c18e1db01c5cdca) C:\WINDOWS\system32\drivers\Ntfs.sys
2010/12/05 17:29:33.0375 NuidFltr (cf7e041663119e09d2e118521ada9300) C:\WINDOWS\system32\DRIVERS\NuidFltr.sys
2010/12/05 17:29:33.0609 Null (73c1e1f395918bc2c6dd67af7591a3ad) C:\WINDOWS\system32\drivers\Null.sys
2010/12/05 17:29:34.0187 NwlnkFlt (b305f3fad35083837ef46a0bbce2fc57) C:\WINDOWS\system32\DRIVERS\nwlnkflt.sys
2010/12/05 17:29:34.0468 NwlnkFwd (c99b3415198d1aab7227f2c88fd664b9) C:\WINDOWS\system32\DRIVERS\nwlnkfwd.sys
2010/12/05 17:29:34.0859 P3 (c90018bafdc7098619a4a95b046b30f3) C:\WINDOWS\system32\DRIVERS\p3.sys
2010/12/05 17:29:35.0265 Parport (5575faf8f97ce5e713d108c2a58d7c7c) C:\WINDOWS\system32\DRIVERS\parport.sys
2010/12/05 17:29:35.0500 PartMgr (beb3ba25197665d82ec7065b724171c6) C:\WINDOWS\system32\drivers\PartMgr.sys
2010/12/05 17:29:35.0750 ParVdm (70e98b3fd8e963a6a46a2e6247e0bea1) C:\WINDOWS\system32\drivers\ParVdm.sys
2010/12/05 17:29:35.0984 PCI (a219903ccf74233761d92bef471a07b1) C:\WINDOWS\system32\DRIVERS\pci.sys
2010/12/05 17:29:36.0515 PCIIde (ccf5f451bb1a5a2a522a76e670000ff0) C:\WINDOWS\system32\DRIVERS\pciide.sys
2010/12/05 17:29:36.0765 Pcmcia (9e89ef60e9ee05e3f2eef2da7397f1c1) C:\WINDOWS\system32\drivers\Pcmcia.sys
2010/12/05 17:29:37.0218 Point32 (3b6973d60bde757c53bb76842d31318e) C:\WINDOWS\system32\DRIVERS\point32.sys
2010/12/05 17:29:37.0515 PptpMiniport (efeec01b1d3cf84f16ddd24d9d9d8f99) C:\WINDOWS\system32\DRIVERS\raspptp.sys
2010/12/05 17:29:37.0921 PSched (09298ec810b07e5d582cb3a3f9255424) C:\WINDOWS\system32\DRIVERS\psched.sys
2010/12/05 17:29:38.0375 Ptilink (80d317bd1c3dbc5d4fe7b1678c60cadd) C:\WINDOWS\system32\DRIVERS\ptilink.sys
2010/12/05 17:29:40.0171 RasAcd (fe0d99d6f31e4fad8159f690d68ded9c) C:\WINDOWS\system32\DRIVERS\rasacd.sys
2010/12/05 17:29:40.0968 Rasl2tp (11b4a627bc9614b885c4969bfa5ff8a6) C:\WINDOWS\system32\DRIVERS\rasl2tp.sys
2010/12/05 17:29:41.0531 RasPppoe (5bc962f2654137c9909c3d4603587dee) C:\WINDOWS\system32\DRIVERS\raspppoe.sys
2010/12/05 17:29:42.0000 Raspti (fdbb1d60066fcfbb7452fd8f9829b242) C:\WINDOWS\system32\DRIVERS\raspti.sys
2010/12/05 17:29:42.0250 Rdbss (7ad224ad1a1437fe28d89cf22b17780a) C:\WINDOWS\system32\DRIVERS\rdbss.sys
2010/12/05 17:29:42.0484 RDPCDD (4912d5b403614ce99c28420f75353332) C:\WINDOWS\system32\DRIVERS\RDPCDD.sys
2010/12/05 17:29:42.0718 rdpdr (15cabd0f7c00c47c70124907916af3f1) C:\WINDOWS\system32\DRIVERS\rdpdr.sys
2010/12/05 17:29:43.0187 RDPWD (6728e45b66f93c08f11de2e316fc70dd) C:\WINDOWS\system32\drivers\RDPWD.sys
2010/12/05 17:29:43.0562 redbook (f828dd7e1419b6653894a8f97a0094c5) C:\WINDOWS\system32\DRIVERS\redbook.sys
2010/12/05 17:29:43.0968 Secdrv (90a3935d05b494a5a39d37e71f09a677) C:\WINDOWS\system32\DRIVERS\secdrv.sys
2010/12/05 17:29:44.0234 seehcri (e5b56569a9f79b70314fede6c953641e) C:\WINDOWS\system32\DRIVERS\seehcri.sys
2010/12/05 17:29:44.0468 Ser2pl (b490ad520257dda26c1d587a71e527b5) C:\WINDOWS\system32\DRIVERS\ser2pl.sys
2010/12/05 17:29:44.0703 serenum (0f29512ccd6bead730039fb4bd2c85ce) C:\WINDOWS\system32\DRIVERS\serenum.sys
2010/12/05 17:29:45.0140 Serial (cca207a8896d4c6a0c9ce29a4ae411a7) C:\WINDOWS\system32\DRIVERS\serial.sys
2010/12/05 17:29:45.0437 Sfloppy (8e6b8c671615d126fdc553d1e2de5562) C:\WINDOWS\system32\drivers\Sfloppy.sys
2010/12/05 17:29:46.0015 smwdm (bf208c85119770e6a9b6577019a3d810) C:\WINDOWS\system32\drivers\smwdm.sys
2010/12/05 17:29:46.0437 splitter (ab8b92451ecb048a4d1de7c3ffcb4a9f) C:\WINDOWS\system32\drivers\splitter.sys
2010/12/05 17:29:46.0671 sr (76bb022c2fb6902fd5bdd4f78fc13a5d) C:\WINDOWS\system32\DRIVERS\sr.sys
2010/12/05 17:29:47.0046 Srv (0f6aefad3641a657e18081f52d0c15af) C:\WINDOWS\system32\DRIVERS\srv.sys
2010/12/05 17:29:47.0343 swenum (3941d127aef12e93addf6fe6ee027e0f) C:\WINDOWS\system32\DRIVERS\swenum.sys
2010/12/05 17:29:47.0578 swmidi (8ce882bcc6cf8a62f2b2323d95cb3d01) C:\WINDOWS\system32\drivers\swmidi.sys
2010/12/05 17:29:47.0906 symc810 (1ff3217614018630d0a6758630fc698c) C:\WINDOWS\system32\DRIVERS\symc810.sys
2010/12/05 17:29:48.0281 symc8xx (070e001d95cf725186ef8b20335f933c) C:\WINDOWS\system32\DRIVERS\symc8xx.sys
2010/12/05 17:29:48.0453 Symmpi (f2b7e8416f508368ac6730e2ae1c614f) C:\WINDOWS\system32\DRIVERS\symmpi.sys
2010/12/05 17:29:48.0656 sym_hi (80ac1c4abbe2df3b738bf15517a51f2c) C:\WINDOWS\system32\DRIVERS\sym_hi.sys
2010/12/05 17:29:48.0875 sym_u3 (bf4fab949a382a8e105f46ebb4937058) C:\WINDOWS\system32\DRIVERS\sym_u3.sys
2010/12/05 17:29:49.0375 sysaudio (8b83f3ed0f1688b4958f77cd6d2bf290) C:\WINDOWS\system32\drivers\sysaudio.sys
2010/12/05 17:29:49.0718 Tcpip (9aefa14bd6b182d61e3119fa5f436d3d) C:\WINDOWS\system32\DRIVERS\tcpip.sys
2010/12/05 17:29:50.0265 TDPIPE (6471a66807f5e104e4885f5b67349397) C:\WINDOWS\system32\drivers\TDPIPE.sys
2010/12/05 17:29:50.0468 TDTCP (c56b6d0402371cf3700eb322ef3aaf61) C:\WINDOWS\system32\drivers\TDTCP.sys
2010/12/05 17:29:50.0718 TermDD (88155247177638048422893737429d9e) C:\WINDOWS\system32\DRIVERS\termdd.sys
2010/12/05 17:29:51.0281 Udfs (5787b80c2e3c5e2f56c2a233d91fa2c9) C:\WINDOWS\system32\drivers\Udfs.sys
2010/12/05 17:29:51.0718 Update (402ddc88356b1bac0ee3dd1580c76a31) C:\WINDOWS\system32\DRIVERS\update.sys
2010/12/05 17:29:52.0046 usbaudio (e919708db44ed8543a7c017953148330) C:\WINDOWS\system32\drivers\usbaudio.sys
2010/12/05 17:29:52.0687 usbccgp (173f317ce0db8e21322e71b7e60a27e8) C:\WINDOWS\system32\DRIVERS\usbccgp.sys
2010/12/05 17:29:52.0890 usbehci (65dcf09d0e37d4c6b11b5b0b76d470a7) C:\WINDOWS\system32\DRIVERS\usbehci.sys
2010/12/05 17:29:53.0203 usbhub (1ab3cdde553b6e064d2e754efe20285c) C:\WINDOWS\system32\DRIVERS\usbhub.sys
2010/12/05 17:29:53.0437 usbprint (a717c8721046828520c9edf31288fc00) C:\WINDOWS\system32\DRIVERS\usbprint.sys
2010/12/05 17:29:53.0750 usbscan (a0b8cf9deb1184fbdd20784a58fa75d4) C:\WINDOWS\system32\DRIVERS\usbscan.sys
2010/12/05 17:29:54.0171 USBSTOR (a32426d9b14a089eaa1d922e0c5801a9) C:\WINDOWS\system32\DRIVERS\USBSTOR.SYS
2010/12/05 17:29:55.0265 usbuhci (26496f9dee2d787fc3e61ad54821ffe6) C:\WINDOWS\system32\DRIVERS\usbuhci.sys
2010/12/05 17:29:55.0515 VgaSave (0d3a8fafceacd8b7625cd549757a7df1) C:\WINDOWS\System32\drivers\vga.sys
2010/12/05 17:29:56.0078 ViaIde (3b3efcda263b8ac14fdf9cbdd0791b2e) C:\WINDOWS\system32\DRIVERS\viaide.sys
2010/12/05 17:29:56.0515 VolSnap (4c8fcb5cc53aab716d810740fe59d025) C:\WINDOWS\system32\drivers\VolSnap.sys
2010/12/05 17:29:56.0781 Wanarp (e20b95baedb550f32dd489265c1da1f6) C:\WINDOWS\system32\DRIVERS\wanarp.sys
2010/12/05 17:29:57.0062 Wdf01000 (fd47474bd21794508af449d9d91af6e6) C:\WINDOWS\system32\DRIVERS\Wdf01000.sys
2010/12/05 17:29:57.0296 wdmaud (6768acf64b18196494413695f0c3a00f) C:\WINDOWS\system32\drivers\wdmaud.sys
2010/12/05 17:29:57.0687 WudfPf (f15feafffbb3644ccc80c5da584e6311) C:\WINDOWS\system32\DRIVERS\WudfPf.sys
2010/12/05 17:29:58.0109 {6080A529-897E-4629-A488-ABA0C29B635E} (1a301c3c65a3d119803fbac5ab65897f) C:\WINDOWS\system32\drivers\ialmsbw.sys
2010/12/05 17:29:58.0562 {D31A0762-0CEB-444e-ACFF-B049A1F6FE91} (4afee4b1625d5146b16526e48953d7a6) C:\WINDOWS\system32\drivers\ialmkchw.sys
2010/12/05 17:29:58.0734 \HardDisk1 - detected Rootkit.Win32.TDSS.tdl4 (0)
2010/12/05 17:29:58.0734 ================================================================================
2010/12/05 17:29:58.0734 Scan finished
2010/12/05 17:29:58.0734 ================================================================================
2010/12/05 17:29:58.0750 Detected object count: 1
2010/12/05 17:30:05.0703 \HardDisk1 - will be cured after reboot
2010/12/05 17:30:05.0703 Rootkit.Win32.TDSS.tdl4(\HardDisk1) - User select action: Cure
2010/12/05 17:30:14.0390 Deinitialize success
2010/12/05 17:28:38.0093 TDSS rootkit removing tool 2.4.10.1 Dec 2 2010 12:28:01
2010/12/05 17:28:38.0093 ================================================================================
2010/12/05 17:28:38.0093 SystemInfo:
2010/12/05 17:28:38.0093
2010/12/05 17:28:38.0093 OS Version: 5.1.2600 ServicePack: 3.0
2010/12/05 17:28:38.0093 Product type: Workstation
2010/12/05 17:28:38.0093 ComputerName: TBBS02
2010/12/05 17:28:38.0093 UserName: Libia
2010/12/05 17:28:38.0093 Windows directory: C:\WINDOWS
2010/12/05 17:28:38.0093 System windows directory: C:\WINDOWS
2010/12/05 17:28:38.0093 Processor architecture: Intel x86
2010/12/05 17:28:38.0093 Number of processors: 1
2010/12/05 17:28:38.0093 Page size: 0x1000
2010/12/05 17:28:38.0093 Boot type: Normal boot
2010/12/05 17:28:38.0093 ================================================================================
2010/12/05 17:28:38.0343 Initialize success
2010/12/05 17:28:51.0359 ================================================================================
2010/12/05 17:28:51.0359 Scan started
2010/12/05 17:28:51.0359 Mode: Manual;
2010/12/05 17:28:51.0359 ================================================================================
2010/12/05 17:28:55.0437 a016bus (b021d0ae4605ce5df67f06e741278cdf) C:\WINDOWS\system32\DRIVERS\a016bus.sys
2010/12/05 17:28:56.0250 a016mdfl (5b6bc2de851012906d4aae84c802e3f2) C:\WINDOWS\system32\DRIVERS\a016mdfl.sys
2010/12/05 17:28:56.0921 a016mdm (c80cffb5819ccfc97f2b09e2259dfde6) C:\WINDOWS\system32\DRIVERS\a016mdm.sys
2010/12/05 17:28:57.0500 a016mgmt (415243177ff67d3cfba44d931b809bf3) C:\WINDOWS\system32\DRIVERS\a016mgmt.sys
2010/12/05 17:28:57.0796 a016obex (3a853f9b8b69541cde714a83a0a6434e) C:\WINDOWS\system32\DRIVERS\a016obex.sys
2010/12/05 17:28:58.0703 ac97intc (0f2d66d5f08ebe2f77bb904288dcf6f0) C:\WINDOWS\system32\drivers\ac97intc.sys
2010/12/05 17:28:58.0921 ACPI (8fd99680a539792a30e97944fdaecf17) C:\WINDOWS\system32\DRIVERS\ACPI.sys
2010/12/05 17:28:59.0187 ACPIEC (9859c0f6936e723e4892d7141b1327d5) C:\WINDOWS\system32\drivers\ACPIEC.sys
2010/12/05 17:28:59.0421 adpu160m (9a11864873da202c996558b2106b0bbc) C:\WINDOWS\system32\DRIVERS\adpu160m.sys
2010/12/05 17:28:59.0671 adpu320 (0ea9b1f0c6c90a509c8603775366adb7) C:\WINDOWS\system32\DRIVERS\adpu320.sys
2010/12/05 17:28:59.0890 aeaudio (11c04b17ed2abbb4833694bcd644ac90) C:\WINDOWS\system32\drivers\aeaudio.sys
2010/12/05 17:29:00.0125 aec (8bed39e3c35d6a489438b8141717a557) C:\WINDOWS\system32\drivers\aec.sys
2010/12/05 17:29:00.0359 AFD (7e775010ef291da96ad17ca4b17137d7) C:\WINDOWS\System32\drivers\afd.sys
2010/12/05 17:29:00.0640 AgereSoftModem (593aefc67283d409f34cc1245d00a509) C:\WINDOWS\system32\DRIVERS\AGRSM.sys
2010/12/05 17:29:01.0093 aic78u2 (19dd0fb48b0c18892f70e2e7d61a1529) C:\WINDOWS\system32\DRIVERS\aic78u2.sys
2010/12/05 17:29:01.0343 aic78xx (b7fe594a7468aa0132deb03fb8e34326) C:\WINDOWS\system32\DRIVERS\aic78xx.sys
2010/12/05 17:29:02.0593 AsyncMac (b153affac761e7f5fcfa822b9c4e97bc) C:\WINDOWS\system32\DRIVERS\asyncmac.sys
2010/12/05 17:29:02.0812 atapi (9f3a2f5aa6875c72bf062c712cfa2674) C:\WINDOWS\system32\DRIVERS\atapi.sys
2010/12/05 17:29:03.0234 Atmarpc (9916c1225104ba14794209cfa8012159) C:\WINDOWS\system32\DRIVERS\atmarpc.sys
2010/12/05 17:29:04.0250 audstub (d9f724aa26c010a217c97606b160ed68) C:\WINDOWS\system32\DRIVERS\audstub.sys
2010/12/05 17:29:04.0562 Beep (da1f27d85e0d1525f6621372e7b685e9) C:\WINDOWS\system32\drivers\Beep.sys
2010/12/05 17:29:04.0984 cbidf2k (90a673fc8e12a79afbed2576f6a7aaf9) C:\WINDOWS\system32\drivers\cbidf2k.sys
2010/12/05 17:29:05.0390 Cdaudio (c1b486a7658353d33a10cc15211a873b) C:\WINDOWS\system32\drivers\Cdaudio.sys
2010/12/05 17:29:05.0656 Cdfs (c885b02847f5d2fd45a24e219ed93b32) C:\WINDOWS\system32\drivers\Cdfs.sys
2010/12/05 17:29:05.0937 Cdrom (1f4260cc5b42272d71f79e570a27a4fe) C:\WINDOWS\system32\DRIVERS\cdrom.sys
2010/12/05 17:29:07.0515 DgiVecp (a5034f77b278f07e224fe07cf98a8b76) C:\WINDOWS\system32\Drivers\DgiVecp.sys
2010/12/05 17:29:08.0171 Disk (044452051f3e02e7963599fc8f4f3e25) C:\WINDOWS\system32\DRIVERS\disk.sys
2010/12/05 17:29:08.0468 dmboot (d992fe1274bde0f84ad826acae022a41) C:\WINDOWS\system32\drivers\dmboot.sys
2010/12/05 17:29:08.0750 dmio (7c824cf7bbde77d95c08005717a95f6f) C:\WINDOWS\system32\drivers\dmio.sys
2010/12/05 17:29:08.0984 dmload (e9317282a63ca4d188c0df5e09c6ac5f) C:\WINDOWS\system32\drivers\dmload.sys
2010/12/05 17:29:09.0500 DMusic (8a208dfcf89792a484e76c40e5f50b45) C:\WINDOWS\system32\drivers\DMusic.sys
2010/12/05 17:29:09.0734 dpti2o (40f3b93b4e5b0126f2f5c0a7a5e22660) C:\WINDOWS\system32\DRIVERS\dpti2o.sys
2010/12/05 17:29:10.0000 drmkaud (8f5fcff8e8848afac920905fbd9d33c8) C:\WINDOWS\system32\drivers\drmkaud.sys
2010/12/05 17:29:10.0312 E1000 (1dc189cd47ad4c8ca214b234b84ca228) C:\WINDOWS\system32\DRIVERS\e1000325.sys
2010/12/05 17:29:10.0625 E100B (afee15c5b16317ebf17f79cc1843465a) C:\WINDOWS\system32\DRIVERS\e100b325.sys
2010/12/05 17:29:10.0921 Fastfat (38d332a6d56af32635675f132548343e) C:\WINDOWS\system32\drivers\Fastfat.sys
2010/12/05 17:29:11.0187 Fdc (92cdd60b6730b9f50f6a1a0c1f8cdc81) C:\WINDOWS\system32\DRIVERS\fdc.sys
2010/12/05 17:29:11.0500 Fips (d45926117eb9fa946a6af572fbe1caa3) C:\WINDOWS\system32\drivers\Fips.sys
2010/12/05 17:29:11.0734 Flpydisk (9d27e7b80bfcdf1cdd9b555862d5e7f0) C:\WINDOWS\system32\DRIVERS\flpydisk.sys
2010/12/05 17:29:12.0031 FltMgr (b2cf4b0786f8212cb92ed2b50c6db6b0) C:\WINDOWS\system32\drivers\fltmgr.sys
2010/12/05 17:29:12.0421 Fs_Rec (3e1e2bd4f39b0e2b7dc4f4d2bcc2779a) C:\WINDOWS\system32\drivers\Fs_Rec.sys
2010/12/05 17:29:12.0671 Ftdisk (6ac26732762483366c3969c9e4d2259d) C:\WINDOWS\system32\DRIVERS\ftdisk.sys
2010/12/05 17:29:12.0937 Gpc (0a02c63c8b144bd8c86b103dee7c86a2) C:\WINDOWS\system32\DRIVERS\msgpc.sys
2010/12/05 17:29:13.0437 HidUsb (ccf82c5ec8a7326c3066de870c06daf1) C:\WINDOWS\system32\DRIVERS\hidusb.sys
2010/12/05 17:29:13.0937 HTTP (f80a415ef82cd06ffaf0d971528ead38) C:\WINDOWS\system32\Drivers\HTTP.sys
2010/12/05 17:29:14.0843 i8042prt (4a0b06aa8943c1e332520f7440c0aa30) C:\WINDOWS\system32\DRIVERS\i8042prt.sys
2010/12/05 17:29:15.0093 i81x (06b7ef73ba5f302eecc294cdf7e19702) C:\WINDOWS\system32\DRIVERS\i81xnt5.sys
2010/12/05 17:29:15.0328 iAimFP0 (7b5b44efe5eb9dadfb8ee29700885d23) C:\WINDOWS\system32\DRIVERS\wADV01nt.sys
2010/12/05 17:29:15.0906 iAimFP1 (eb1f6bab6c22ede0ba551b527475f7e9) C:\WINDOWS\system32\DRIVERS\wADV02NT.sys
2010/12/05 17:29:16.0859 iAimFP2 (03ce989d846c1aa81145cb22fcb86d06) C:\WINDOWS\system32\DRIVERS\wADV05NT.sys
2010/12/05 17:29:17.0125 iAimFP3 (525849b4469de021d5d61b4db9be3a9d) C:\WINDOWS\system32\DRIVERS\wSiINTxx.sys
2010/12/05 17:29:17.0343 iAimFP4 (589c2bcdb5bd602bf7b63d210407ef8c) C:\WINDOWS\system32\DRIVERS\wVchNTxx.sys
2010/12/05 17:29:17.0562 iAimFP5 (0308aef61941e4af478fa1a0f83812f5) C:\WINDOWS\system32\DRIVERS\wADV07nt.sys
2010/12/05 17:29:17.0796 iAimFP6 (714038a8aa5de08e12062202cd7eaeb5) C:\WINDOWS\system32\DRIVERS\wADV08nt.sys
2010/12/05 17:29:18.0109 iAimFP7 (7bb3aa595e4507a788de1cdc63f4c8c4) C:\WINDOWS\system32\DRIVERS\wADV09nt.sys
2010/12/05 17:29:18.0375 iAimTV0 (d83bdd5c059667a2f647a6be5703a4d2) C:\WINDOWS\system32\DRIVERS\wATV01nt.sys
2010/12/05 17:29:18.0625 iAimTV1 (ed968d23354daa0d7c621580c012a1f6) C:\WINDOWS\system32\DRIVERS\wATV02NT.sys
2010/12/05 17:29:18.0859 iAimTV3 (d738273f218a224c1ddac04203f27a84) C:\WINDOWS\system32\DRIVERS\wATV04nt.sys
2010/12/05 17:29:19.0093 iAimTV4 (0052d118995cbab152daabe6106d1442) C:\WINDOWS\system32\DRIVERS\wCh7xxNT.sys
2010/12/05 17:29:19.0343 iAimTV5 (791cc45de6e50445be72e8ad6401ff45) C:\WINDOWS\system32\DRIVERS\wATV10nt.sys
2010/12/05 17:29:19.0781 iAimTV6 (352fa0e98bc461ce1ce5d41f64db558d) C:\WINDOWS\system32\DRIVERS\wATV06nt.sys
2010/12/05 17:29:20.0171 ialm (9a883c3c4d91292c0d09de7c728e781c) C:\WINDOWS\system32\DRIVERS\ialmnt5.sys
2010/12/05 17:29:20.0406 Imapi (083a052659f5310dd8b6a6cb05edcf8e) C:\WINDOWS\system32\DRIVERS\imapi.sys
2010/12/05 17:29:21.0515 IntelIde (b5466a9250342a7aa0cd1fba13420678) C:\WINDOWS\system32\DRIVERS\intelide.sys
2010/12/05 17:29:21.0765 intelppm (8c953733d8f36eb2133f5bb58808b66b) C:\WINDOWS\system32\DRIVERS\intelppm.sys
2010/12/05 17:29:22.0031 Ip6Fw (3bb22519a194418d5fec05d800a19ad0) C:\WINDOWS\system32\drivers\ip6fw.sys
2010/12/05 17:29:22.0359 IpFilterDriver (731f22ba402ee4b62748adaf6363c182) C:\WINDOWS\system32\DRIVERS\ipfltdrv.sys
2010/12/05 17:29:22.0750 IpInIp (b87ab476dcf76e72010632b5550955f5) C:\WINDOWS\system32\DRIVERS\ipinip.sys
2010/12/05 17:29:23.0312 IpNat (cc748ea12c6effde940ee98098bf96bb) C:\WINDOWS\system32\DRIVERS\ipnat.sys
2010/12/05 17:29:23.0546 IPSec (23c74d75e36e7158768dd63d92789a91) C:\WINDOWS\system32\DRIVERS\ipsec.sys
2010/12/05 17:29:23.0781 IRENUM (c93c9ff7b04d772627a3646d89f7bf89) C:\WINDOWS\system32\DRIVERS\irenum.sys
2010/12/05 17:29:24.0000 isapnp (05a299ec56e52649b1cf2fc52d20f2d7) C:\WINDOWS\system32\DRIVERS\isapnp.sys
2010/12/05 17:29:24.0406 Kbdclass (463c1ec80cd17420a542b7f36a36f128) C:\WINDOWS\system32\DRIVERS\kbdclass.sys
2010/12/05 17:29:24.0734 kbdhid (9ef487a186dea361aa06913a75b3fa99) C:\WINDOWS\system32\DRIVERS\kbdhid.sys
2010/12/05 17:29:24.0937 kmixer (692bcf44383d056aed41b045a323d378) C:\WINDOWS\system32\drivers\kmixer.sys
2010/12/05 17:29:25.0390 KSecDD (b467646c54cc746128904e1654c750c1) C:\WINDOWS\system32\drivers\KSecDD.sys
2010/12/05 17:29:25.0859 mnmdd (4ae068242760a1fb6e1a44bf4e16afa6) C:\WINDOWS\system32\drivers\mnmdd.sys
2010/12/05 17:29:26.0515 Modem (dfcbad3cec1c5f964962ae10e0bcc8e1) C:\WINDOWS\system32\drivers\Modem.sys
2010/12/05 17:29:26.0734 Mouclass (35c9e97194c8cfb8430125f8dbc34d04) C:\WINDOWS\system32\DRIVERS\mouclass.sys
2010/12/05 17:29:26.0968 mouhid (b1c303e17fb9d46e87a98e4ba6769685) C:\WINDOWS\system32\DRIVERS\mouhid.sys
2010/12/05 17:29:27.0531 MountMgr (a80b9a0bad1b73637dbcbba7df72d3fd) C:\WINDOWS\system32\drivers\MountMgr.sys
2010/12/05 17:29:27.0984 MREMPR5 (2bc9e43f55de8c30fc817ed56d0ee907) C:\PROGRA~1\COMMON~1\Motive\MREMPR5.SYS
2010/12/05 17:29:28.0203 MRENDIS5 (594b9d8194e3f4ecbf0325bd10bbeb05) C:\PROGRA~1\COMMON~1\Motive\MRENDIS5.SYS
2010/12/05 17:29:28.0421 MRxDAV (11d42bb6206f33fbb3ba0288d3ef81bd) C:\WINDOWS\system32\DRIVERS\mrxdav.sys
2010/12/05 17:29:28.0671 MRxSmb (f3aefb11abc521122b67095044169e98) C:\WINDOWS\system32\DRIVERS\mrxsmb.sys
2010/12/05 17:29:28.0968 Msfs (c941ea2454ba8350021d774daf0f1027) C:\WINDOWS\system32\drivers\Msfs.sys
2010/12/05 17:29:29.0328 MSKSSRV (d1575e71568f4d9e14ca56b7b0453bf1) C:\WINDOWS\system32\drivers\MSKSSRV.sys
2010/12/05 17:29:29.0546 MSPCLOCK (325bb26842fc7ccc1fcce2c457317f3e) C:\WINDOWS\system32\drivers\MSPCLOCK.sys
2010/12/05 17:29:29.0812 MSPQM (bad59648ba099da4a17680b39730cb3d) C:\WINDOWS\system32\drivers\MSPQM.sys
2010/12/05 17:29:30.0093 mssmbios (af5f4f3f14a8ea2c26de30f7a1e17136) C:\WINDOWS\system32\DRIVERS\mssmbios.sys
2010/12/05 17:29:30.0359 Mup (2f625d11385b1a94360bfc70aaefdee1) C:\WINDOWS\system32\drivers\Mup.sys
2010/12/05 17:29:30.0671 NDIS (1df7f42665c94b825322fae71721130d) C:\WINDOWS\system32\drivers\NDIS.sys
2010/12/05 17:29:30.0859 NdisTapi (1ab3d00c991ab086e69db84b6c0ed78f) C:\WINDOWS\system32\DRIVERS\ndistapi.sys
2010/12/05 17:29:31.0140 Ndisuio (f927a4434c5028758a842943ef1a3849) C:\WINDOWS\system32\DRIVERS\ndisuio.sys
2010/12/05 17:29:31.0359 NdisWan (edc1531a49c80614b2cfda43ca8659ab) C:\WINDOWS\system32\DRIVERS\ndiswan.sys
2010/12/05 17:29:31.0609 NDProxy (6215023940cfd3702b46abc304e1d45a) C:\WINDOWS\system32\drivers\NDProxy.sys
2010/12/05 17:29:31.0828 NetBIOS (5d81cf9a2f1a3a756b66cf684911cdf0) C:\WINDOWS\system32\DRIVERS\netbios.sys
2010/12/05 17:29:32.0343 NetBT (74b2b2f5bea5e9a3dc021d685551bd3d) C:\WINDOWS\system32\DRIVERS\netbt.sys
2010/12/05 17:29:32.0734 Npfs (3182d64ae053d6fb034f44b6def8034a) C:\WINDOWS\system32\drivers\Npfs.sys
2010/12/05 17:29:32.0984 Ntfs (78a08dd6a8d65e697c18e1db01c5cdca) C:\WINDOWS\system32\drivers\Ntfs.sys
2010/12/05 17:29:33.0375 NuidFltr (cf7e041663119e09d2e118521ada9300) C:\WINDOWS\system32\DRIVERS\NuidFltr.sys
2010/12/05 17:29:33.0609 Null (73c1e1f395918bc2c6dd67af7591a3ad) C:\WINDOWS\system32\drivers\Null.sys
2010/12/05 17:29:34.0187 NwlnkFlt (b305f3fad35083837ef46a0bbce2fc57) C:\WINDOWS\system32\DRIVERS\nwlnkflt.sys
2010/12/05 17:29:34.0468 NwlnkFwd (c99b3415198d1aab7227f2c88fd664b9) C:\WINDOWS\system32\DRIVERS\nwlnkfwd.sys
2010/12/05 17:29:34.0859 P3 (c90018bafdc7098619a4a95b046b30f3) C:\WINDOWS\system32\DRIVERS\p3.sys
2010/12/05 17:29:35.0265 Parport (5575faf8f97ce5e713d108c2a58d7c7c) C:\WINDOWS\system32\DRIVERS\parport.sys
2010/12/05 17:29:35.0500 PartMgr (beb3ba25197665d82ec7065b724171c6) C:\WINDOWS\system32\drivers\PartMgr.sys
2010/12/05 17:29:35.0750 ParVdm (70e98b3fd8e963a6a46a2e6247e0bea1) C:\WINDOWS\system32\drivers\ParVdm.sys
2010/12/05 17:29:35.0984 PCI (a219903ccf74233761d92bef471a07b1) C:\WINDOWS\system32\DRIVERS\pci.sys
2010/12/05 17:29:36.0515 PCIIde (ccf5f451bb1a5a2a522a76e670000ff0) C:\WINDOWS\system32\DRIVERS\pciide.sys
2010/12/05 17:29:36.0765 Pcmcia (9e89ef60e9ee05e3f2eef2da7397f1c1) C:\WINDOWS\system32\drivers\Pcmcia.sys
2010/12/05 17:29:37.0218 Point32 (3b6973d60bde757c53bb76842d31318e) C:\WINDOWS\system32\DRIVERS\point32.sys
2010/12/05 17:29:37.0515 PptpMiniport (efeec01b1d3cf84f16ddd24d9d9d8f99) C:\WINDOWS\system32\DRIVERS\raspptp.sys
2010/12/05 17:29:37.0921 PSched (09298ec810b07e5d582cb3a3f9255424) C:\WINDOWS\system32\DRIVERS\psched.sys
2010/12/05 17:29:38.0375 Ptilink (80d317bd1c3dbc5d4fe7b1678c60cadd) C:\WINDOWS\system32\DRIVERS\ptilink.sys
2010/12/05 17:29:40.0171 RasAcd (fe0d99d6f31e4fad8159f690d68ded9c) C:\WINDOWS\system32\DRIVERS\rasacd.sys
2010/12/05 17:29:40.0968 Rasl2tp (11b4a627bc9614b885c4969bfa5ff8a6) C:\WINDOWS\system32\DRIVERS\rasl2tp.sys
2010/12/05 17:29:41.0531 RasPppoe (5bc962f2654137c9909c3d4603587dee) C:\WINDOWS\system32\DRIVERS\raspppoe.sys
2010/12/05 17:29:42.0000 Raspti (fdbb1d60066fcfbb7452fd8f9829b242) C:\WINDOWS\system32\DRIVERS\raspti.sys
2010/12/05 17:29:42.0250 Rdbss (7ad224ad1a1437fe28d89cf22b17780a) C:\WINDOWS\system32\DRIVERS\rdbss.sys
2010/12/05 17:29:42.0484 RDPCDD (4912d5b403614ce99c28420f75353332) C:\WINDOWS\system32\DRIVERS\RDPCDD.sys
2010/12/05 17:29:42.0718 rdpdr (15cabd0f7c00c47c70124907916af3f1) C:\WINDOWS\system32\DRIVERS\rdpdr.sys
2010/12/05 17:29:43.0187 RDPWD (6728e45b66f93c08f11de2e316fc70dd) C:\WINDOWS\system32\drivers\RDPWD.sys
2010/12/05 17:29:43.0562 redbook (f828dd7e1419b6653894a8f97a0094c5) C:\WINDOWS\system32\DRIVERS\redbook.sys
2010/12/05 17:29:43.0968 Secdrv (90a3935d05b494a5a39d37e71f09a677) C:\WINDOWS\system32\DRIVERS\secdrv.sys
2010/12/05 17:29:44.0234 seehcri (e5b56569a9f79b70314fede6c953641e) C:\WINDOWS\system32\DRIVERS\seehcri.sys
2010/12/05 17:29:44.0468 Ser2pl (b490ad520257dda26c1d587a71e527b5) C:\WINDOWS\system32\DRIVERS\ser2pl.sys
2010/12/05 17:29:44.0703 serenum (0f29512ccd6bead730039fb4bd2c85ce) C:\WINDOWS\system32\DRIVERS\serenum.sys
2010/12/05 17:29:45.0140 Serial (cca207a8896d4c6a0c9ce29a4ae411a7) C:\WINDOWS\system32\DRIVERS\serial.sys
2010/12/05 17:29:45.0437 Sfloppy (8e6b8c671615d126fdc553d1e2de5562) C:\WINDOWS\system32\drivers\Sfloppy.sys
2010/12/05 17:29:46.0015 smwdm (bf208c85119770e6a9b6577019a3d810) C:\WINDOWS\system32\drivers\smwdm.sys
2010/12/05 17:29:46.0437 splitter (ab8b92451ecb048a4d1de7c3ffcb4a9f) C:\WINDOWS\system32\drivers\splitter.sys
2010/12/05 17:29:46.0671 sr (76bb022c2fb6902fd5bdd4f78fc13a5d) C:\WINDOWS\system32\DRIVERS\sr.sys
2010/12/05 17:29:47.0046 Srv (0f6aefad3641a657e18081f52d0c15af) C:\WINDOWS\system32\DRIVERS\srv.sys
2010/12/05 17:29:47.0343 swenum (3941d127aef12e93addf6fe6ee027e0f) C:\WINDOWS\system32\DRIVERS\swenum.sys
2010/12/05 17:29:47.0578 swmidi (8ce882bcc6cf8a62f2b2323d95cb3d01) C:\WINDOWS\system32\drivers\swmidi.sys
2010/12/05 17:29:47.0906 symc810 (1ff3217614018630d0a6758630fc698c) C:\WINDOWS\system32\DRIVERS\symc810.sys
2010/12/05 17:29:48.0281 symc8xx (070e001d95cf725186ef8b20335f933c) C:\WINDOWS\system32\DRIVERS\symc8xx.sys
2010/12/05 17:29:48.0453 Symmpi (f2b7e8416f508368ac6730e2ae1c614f) C:\WINDOWS\system32\DRIVERS\symmpi.sys
2010/12/05 17:29:48.0656 sym_hi (80ac1c4abbe2df3b738bf15517a51f2c) C:\WINDOWS\system32\DRIVERS\sym_hi.sys
2010/12/05 17:29:48.0875 sym_u3 (bf4fab949a382a8e105f46ebb4937058) C:\WINDOWS\system32\DRIVERS\sym_u3.sys
2010/12/05 17:29:49.0375 sysaudio (8b83f3ed0f1688b4958f77cd6d2bf290) C:\WINDOWS\system32\drivers\sysaudio.sys
2010/12/05 17:29:49.0718 Tcpip (9aefa14bd6b182d61e3119fa5f436d3d) C:\WINDOWS\system32\DRIVERS\tcpip.sys
2010/12/05 17:29:50.0265 TDPIPE (6471a66807f5e104e4885f5b67349397) C:\WINDOWS\system32\drivers\TDPIPE.sys
2010/12/05 17:29:50.0468 TDTCP (c56b6d0402371cf3700eb322ef3aaf61) C:\WINDOWS\system32\drivers\TDTCP.sys
2010/12/05 17:29:50.0718 TermDD (88155247177638048422893737429d9e) C:\WINDOWS\system32\DRIVERS\termdd.sys
2010/12/05 17:29:51.0281 Udfs (5787b80c2e3c5e2f56c2a233d91fa2c9) C:\WINDOWS\system32\drivers\Udfs.sys
2010/12/05 17:29:51.0718 Update (402ddc88356b1bac0ee3dd1580c76a31) C:\WINDOWS\system32\DRIVERS\update.sys
2010/12/05 17:29:52.0046 usbaudio (e919708db44ed8543a7c017953148330) C:\WINDOWS\system32\drivers\usbaudio.sys
2010/12/05 17:29:52.0687 usbccgp (173f317ce0db8e21322e71b7e60a27e8) C:\WINDOWS\system32\DRIVERS\usbccgp.sys
2010/12/05 17:29:52.0890 usbehci (65dcf09d0e37d4c6b11b5b0b76d470a7) C:\WINDOWS\system32\DRIVERS\usbehci.sys
2010/12/05 17:29:53.0203 usbhub (1ab3cdde553b6e064d2e754efe20285c) C:\WINDOWS\system32\DRIVERS\usbhub.sys
2010/12/05 17:29:53.0437 usbprint (a717c8721046828520c9edf31288fc00) C:\WINDOWS\system32\DRIVERS\usbprint.sys
2010/12/05 17:29:53.0750 usbscan (a0b8cf9deb1184fbdd20784a58fa75d4) C:\WINDOWS\system32\DRIVERS\usbscan.sys
2010/12/05 17:29:54.0171 USBSTOR (a32426d9b14a089eaa1d922e0c5801a9) C:\WINDOWS\system32\DRIVERS\USBSTOR.SYS
2010/12/05 17:29:55.0265 usbuhci (26496f9dee2d787fc3e61ad54821ffe6) C:\WINDOWS\system32\DRIVERS\usbuhci.sys
2010/12/05 17:29:55.0515 VgaSave (0d3a8fafceacd8b7625cd549757a7df1) C:\WINDOWS\System32\drivers\vga.sys
2010/12/05 17:29:56.0078 ViaIde (3b3efcda263b8ac14fdf9cbdd0791b2e) C:\WINDOWS\system32\DRIVERS\viaide.sys
2010/12/05 17:29:56.0515 VolSnap (4c8fcb5cc53aab716d810740fe59d025) C:\WINDOWS\system32\drivers\VolSnap.sys
2010/12/05 17:29:56.0781 Wanarp (e20b95baedb550f32dd489265c1da1f6) C:\WINDOWS\system32\DRIVERS\wanarp.sys
2010/12/05 17:29:57.0062 Wdf01000 (fd47474bd21794508af449d9d91af6e6) C:\WINDOWS\system32\DRIVERS\Wdf01000.sys
2010/12/05 17:29:57.0296 wdmaud (6768acf64b18196494413695f0c3a00f) C:\WINDOWS\system32\drivers\wdmaud.sys
2010/12/05 17:29:57.0687 WudfPf (f15feafffbb3644ccc80c5da584e6311) C:\WINDOWS\system32\DRIVERS\WudfPf.sys
2010/12/05 17:29:58.0109 {6080A529-897E-4629-A488-ABA0C29B635E} (1a301c3c65a3d119803fbac5ab65897f) C:\WINDOWS\system32\drivers\ialmsbw.sys
2010/12/05 17:29:58.0562 {D31A0762-0CEB-444e-ACFF-B049A1F6FE91} (4afee4b1625d5146b16526e48953d7a6) C:\WINDOWS\system32\drivers\ialmkchw.sys
2010/12/05 17:29:58.0734 \HardDisk1 - detected Rootkit.Win32.TDSS.tdl4 (0)
2010/12/05 17:29:58.0734 ================================================================================
2010/12/05 17:29:58.0734 Scan finished
2010/12/05 17:29:58.0734 ================================================================================
2010/12/05 17:29:58.0750 Detected object count: 1
2010/12/05 17:30:05.0703 \HardDisk1 - will be cured after reboot
2010/12/05 17:30:05.0703 Rootkit.Win32.TDSS.tdl4(\HardDisk1) - User select action: Cure
2010/12/05 17:30:14.0390 Deinitialize success
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked





 Sign In
Sign In Create Account
Create Account

