Step 1.Download the enclosed file.
 fixlist.txt 770bytes
633 downloads
fixlist.txt 770bytes
633 downloadsSave it in the USB drive.
Insert the
USB drive into the ailing computer. Run
FRST as you did before,
except that this time around
click on the
Fix button.
The tool will make a log on the flashdrive (
Fixlog.txt) please post it it your reply.
Step 2.On the good computer download a fresh copy of the following tools and put them on the USB drive.
RogueKillerComboFix.Boot the ailing computer into normal mode.
Insert the USB drive in the ailing computer and copy
RogueKiller to the desktop.
Try to run it. If it does not run post the log above, skip the remaining steps, and let me know.
If it runs do these steps:
- Quit all programs
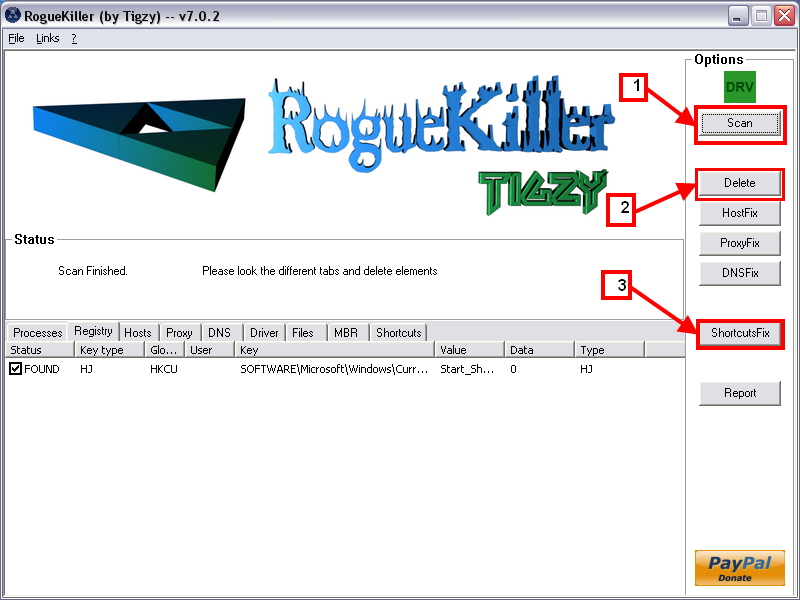
- Start RogueKiller.exe.
- Wait until Prescan has finished ...
- Click on the Scan button Step 1 in the picture.
- Note: If RogueKiller will not run please try it several times, if it still does not run rename it winlogon.com and try it several times.
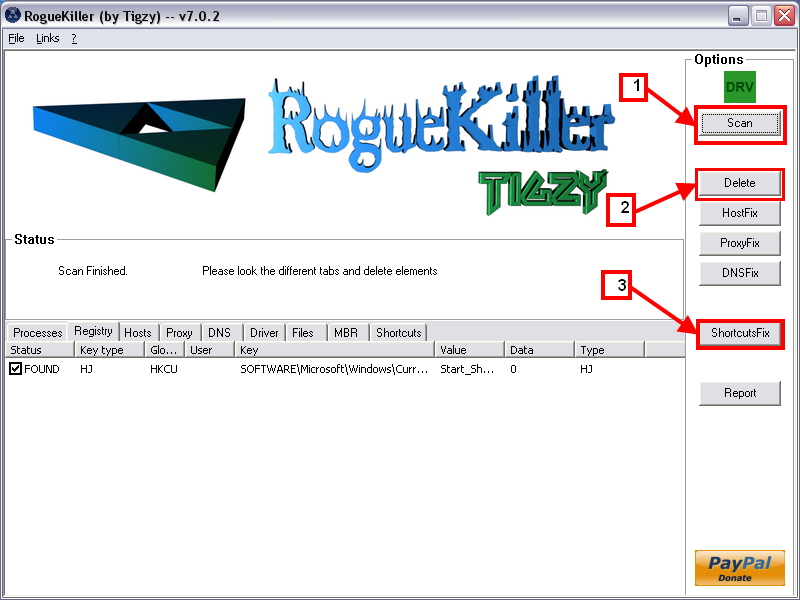
- Wait for the end of the scan.
- The first report will be created on the desktop.
- Click on the Delete button step 2 in the picture.
- The second report will be created on the desktop.
- Next click on ShortcutsFix step 3 in the picture.
- The third report will be created on the desktop.
Please post:
All RKreport.txt text files located on your desktop.
Step 3.Copy Combofix from the USB drive to the ailing computer desktop.
*
IMPORTANT -
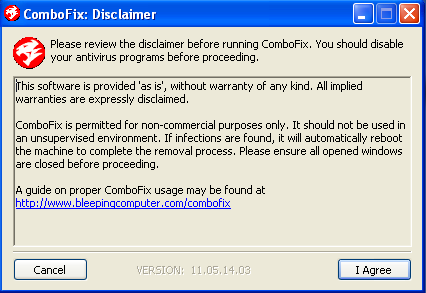
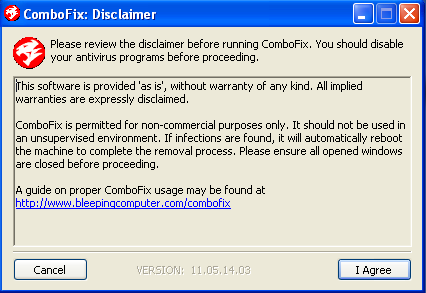
Disable your AntiVirus and AntiSpyware applications, usually via a right click on the System Tray icon. They may otherwise interfere with our tools. If you have difficulty properly disabling your protective programs, refer to this link
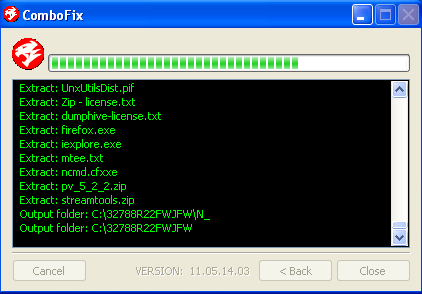
here - Double click on ComboFix.exe & follow the prompts.
- Accept the disclaimer and allow to update if it asks
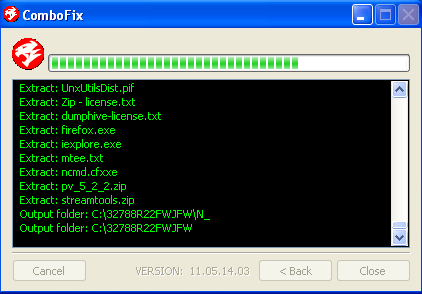
- When finished, it shall produce a log for you.
- Please include the C:\ComboFix.txt in your next reply.
Notes:
1. Do not mouse-click Combofix's window while it is running. That may cause it to stall.
2. Do not "re-run" Combofix. If you have a problem, reply back for further instructions.
3. If after the reboot you get errors about programmes being marked for deletion then reboot, that will cure it.
Please make sure you include the Combofix log in your next reply as well as describe how your computer is running nowStep 4.Please post:FixLog.txtif they can run post:All RKreport.txt files
ComboFix.txtGive me an update on how the computer is running
Edited by CompCav, 18 March 2012 - 07:46 PM.

 This topic is locked
This topic is locked














 Sign In
Sign In Create Account
Create Account

