Download ESET's Service Repair
http://kb.eset.com/l...vicesRepair.exe and Save it then right click on it and Run As Admin.
I think it reboots when done. IF not, reboot it.
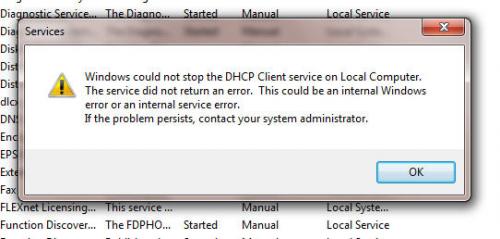
If that doesn't help then go back into Services, DHCP Client and change the Startup Type: to Automatic (Delayed Start). Apply. Reboot.
If it won't let you change the Startup Type let me know.
Copy the next 4 lines:
reg query HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\afd > \junk.txt
reg query HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\tdx >> \junk.txt
reg query HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\nsi >> \junk.txt
reg query HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\dhcp >> \junk.txt
notepad \junk.txt
Start, All Programs, Accessories, right click on Command Prompt and Run as Administrator, Continue. Right click and Paste or Edit then Paste and the copied line should appear.
Hit Enter. Notepad should open. Copy and paste the text from notepad. (Close the Command Window)















 Sign In
Sign In Create Account
Create Account

