Phishing Malware Issue? (Stolen personal information) [Closed]
#31
![Phishing Malware Issue? (Stolen personal information) [Closed]: post #31](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2013 - 07:28 AM
Posted 09 September 2013 - 07:28 AM

#32
![Phishing Malware Issue? (Stolen personal information) [Closed]: post #32](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2013 - 08:13 AM
Posted 09 September 2013 - 08:13 AM

#33
![Phishing Malware Issue? (Stolen personal information) [Closed]: post #33](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2013 - 09:08 PM
Posted 09 September 2013 - 09:08 PM

Ran by Melanie (administrator) on 09-09-2013 at 22:32:58
Running from "C:\Users\Melanie\Desktop"
Microsoft® Windows Vista Home Basic Service Pack 2 (X86)
Boot Mode: Normal
****************************************************************
Internet Services:
============
Connection Status:
==============
Localhost is accessible.
LAN connected.
Google IP is accessible.
Google.com is accessible.
Yahoo.com is accessible.
Windows Firewall:
=============
Firewall Disabled Policy:
==================
System Restore:
============
System Restore Disabled Policy:
========================
Security Center:
============
Security Center Notification Icon =====> HKLM\...\ShellServiceObjects\{FD6905CE-952F-41F1-9A6F-135D9C6622CC}\\"AutoStart" value does not exist.
Windows Update:
============
Windows Autoupdate Disabled Policy:
============================
Windows Defender:
==============
WinDefend Service is not running. Checking service configuration:
The start type of WinDefend service is OK.
The ImagePath of WinDefend service is OK.
The ServiceDll of WinDefend service is OK.
Windows Defender Disabled Policy:
==========================
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender]
"DisableAntiSpyware"=DWORD:1
Other Services:
==============
File Check:
========
C:\Windows\system32\nsisvc.dll => MD5 is legit
C:\Windows\system32\Drivers\nsiproxy.sys => MD5 is legit
C:\Windows\system32\dhcpcsvc.dll => MD5 is legit
C:\Windows\system32\Drivers\afd.sys => MD5 is legit
C:\Windows\system32\Drivers\tdx.sys => MD5 is legit
C:\Windows\system32\Drivers\tcpip.sys => MD5 is legit
C:\Windows\system32\dnsrslvr.dll => MD5 is legit
C:\Windows\system32\mpssvc.dll => MD5 is legit
C:\Windows\system32\bfe.dll => MD5 is legit
C:\Windows\system32\Drivers\mpsdrv.sys => MD5 is legit
C:\Windows\system32\SDRSVC.dll => MD5 is legit
C:\Windows\system32\vssvc.exe => MD5 is legit
C:\Windows\system32\wscsvc.dll => MD5 is legit
C:\Windows\system32\wbem\WMIsvc.dll => MD5 is legit
C:\Windows\system32\wuaueng.dll => MD5 is legit
C:\Windows\system32\qmgr.dll => MD5 is legit
C:\Windows\system32\es.dll => MD5 is legit
C:\Windows\system32\cryptsvc.dll => MD5 is legit
C:\Program Files\Windows Defender\MpSvc.dll => MD5 is legit
C:\Windows\system32\ipnathlp.dll => MD5 is legit
C:\Windows\system32\iphlpsvc.dll => MD5 is legit
C:\Windows\system32\svchost.exe => MD5 is legit
C:\Windows\system32\rpcss.dll => MD5 is legit
**** End of log ****
#34
![Phishing Malware Issue? (Stolen personal information) [Closed]: post #34](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 09 September 2013 - 11:21 PM
Posted 09 September 2013 - 11:21 PM

Step-1.
Be advised that when the fix commences it will shut down all running processes and you may lose the desktop and icons, they will return on reboot
1. Please copy all of the text in the quote box below (Do Not copy the word Quote. To do this, highlight everything
inside the quote box (except the word Quote) , right click and click Copy.
:COMMANDS
[createrestorepoint]
:REG
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ShellServiceObjects\{FD6905CE-952F-41F1-9A6F-135D9C6622CC}]
"AutoStart" = ""
:COMMANDS
[emptytemp]
Warning: This fix is relevant for this system and no other. If you are not this user, DO NOT follow these directions as they could damage the workings of your system.
2. Please re-open
- Vista and 7 users: Right click the icon and click Run as Administrator
 textbox, right click and click Paste. This will put the above script inside the textbox.
textbox, right click and click Paste. This will put the above script inside the textbox.4. Click the
 button.
button.5. Let the program run unhindered.
6. OTL may ask to reboot the machine. Please do so if asked.
7. Click the
 button.
button.8. A report will open. Copy and Paste that report in your next reply.
9. If the machine reboots, the log will be located at C:\_OTL\MovedFiles\mmddyyyy_hhmmss.log, (where mmddyyyy_hhmmss is the date of the tool run).
Before you complete Steps 2 and 3 I want you to disable any screen saver you might have running.
Step-2.
 Malwarebytes' Anti-Malware
Malwarebytes' Anti-MalwareClose all programs and browsers on your computer and disable any screen saver you might have running.
- Right click the MalwareBytes icon on the desktop. Click Run As Administrator, then click the Continue button on the UAC window. You will now be at the main program as shown below.
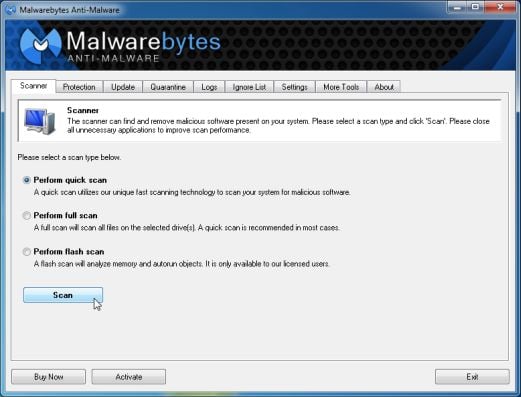
- Click the Update tab and update the program if required.
- Click the Scanner tab, make sure the the Perform full scan option is selected and then click on the Scan button to start scanning your computer.
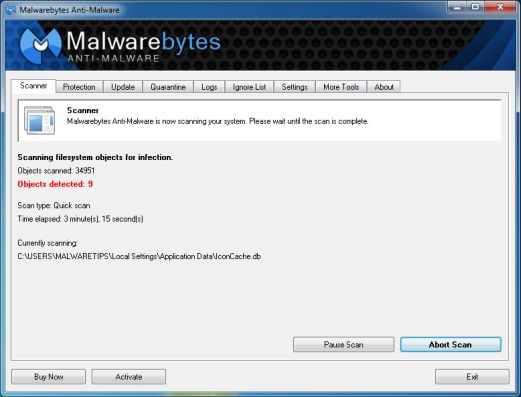
MBAM will now start scanning your computer for malware. This process can take quite a while, so I suggest you go and do something else and periodically check on the status of the scan. When MBAM is scanning it will look like the image below.
- When the scan is finished a message box will appear as shown in the image below.

You should click on the OK button to close the message box and continue with the removal process.
- You will now be back at the main Scanner screen. At this point you should click on the Show Results button.
- A screen displaying all the malware that the program found will be shown as seen in the image below. Please note that the infections found may be different than what is shown in the image.
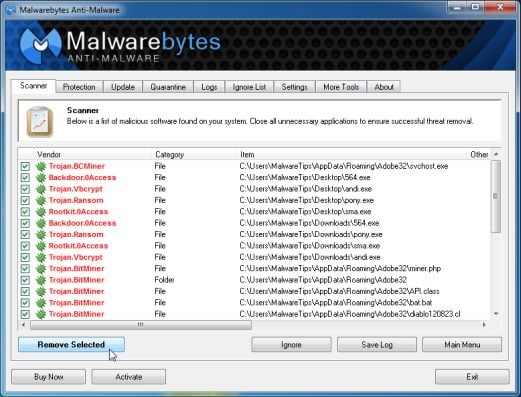
- Make sure that everything is checked EXCEPT items in System Restore (see the image below), and click Remove Selected<---Very Important.

- When disinfection is completed, a log will open in Notepad and you may be prompted to Restart.(See Extra Note)
- The log is automatically saved by MBAM and can be viewed by clicking the Logs tab in MBAM.
- Copy&Paste the entire report in your next reply.
Step-3.
Run ESET Online Scanner:
Note: You can use either Internet Explorer or Mozilla FireFox for this scan. You will however need to disable your current installed Anti-Virus, how to do so can be read here.
Vista / 7 users: You will need to to right-click on the either the IE or FF icon in the Start Menu or Quick Launch Bar on the Taskbar and select Run as Administrator from the context menu.
- Please go here then click on:

Note: If using Mozilla Firefox you will need to download the ESET Smart Installer. Click on esetsmartinstaller_enu.exe to download the Smart Installer. Save it to the desktop.
When prompted double click on the icon on the desktop.
icon on the desktop.
All of the below instructions are compatible with either Internet Explorer or Mozilla FireFox. - Select the option YES, I accept the Terms of Use then click on:

- When prompted allow the Add-On/Active X to install.
- Uncheck the box beside Remove Found Threats
- Make sure that the option Scan archives is checked.
- Now click on Advanced Settings and select the following:
- Scan for potentially unwanted applications
- Scan for potentially unsafe applications
- Enable Anti-Stealth Technology
- Now click on:

- The virus signature database... will begin to download. Be patient this make take some time depending on the speed of your Internet Connection.
- When completed the Online Scan will begin automatically. The scan may take several hours.
- Wait for the scan to finish. Do not touch either the Mouse or keyboard during the scan. Otherwise it may stall.
- If No Threats Were Found:
- Put a checkmark in "Uninstall application on close"
- Close the program
- Report to me that nothing was found
- If Threats Were Found:
- Click on "list of threats found"
- Click on "export to text file" and save it to the desktop as ESET SCAN.txt
- Click on Back
- Put a checkmark in "Uninstall application on close" (Be sure you have saved the file first)
- Click on Finish
- Close the program
- Copy and paste the report here
Step-4.
Install AV Program
- Please click here to go to our Free Antivirus and Antispyware Software page.
- Under the Free Antivirus Software section choose one antivirus program. Download it to the desktop, close the browser and all open windows.
- Right click the setup file, click Run as Administrator and OK any UAC prompts to start the installation. Follow any on screen prompts.
Step-5.
Things For Your Next Post:
Please post the logs in the order requested. Do Not attach the logs unless I request it.
1. Let me know if you successfully got an antivirus installed.
2. How is the computer running now?
3. The OTL fix log
4. The MalwareBytes log
5. The ESET log (If it found anything). If it didn't just let me know.
#35
![Phishing Malware Issue? (Stolen personal information) [Closed]: post #35](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 13 September 2013 - 06:46 AM
Posted 13 September 2013 - 06:46 AM

#36
![Phishing Malware Issue? (Stolen personal information) [Closed]: post #36](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 13 September 2013 - 12:01 PM
Posted 13 September 2013 - 12:01 PM

#37
![Phishing Malware Issue? (Stolen personal information) [Closed]: post #37](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 17 September 2013 - 08:33 AM
Posted 17 September 2013 - 08:33 AM

Computer seems alright.
ESET found nothing.
Malwarebytes Anti-Malware 1.75.0.1300
www.malwarebytes.org
Database version: v2013.09.13.02
Windows Vista Service Pack 2 x86 NTFS
Internet Explorer 7.0.6002.18005
Melanie :: MELANIE-PC [administrator]
2013-09-12 23:34:45
mbam-log-2013-09-12 (23-34-45).txt
Scan type: Full scan (C:\|D:\|)
Scan options enabled: Memory | Startup | Registry | File System | Heuristics/Extra | Heuristics/Shuriken | PUP | PUM
Scan options disabled: P2P
Objects scanned: 348512
Time elapsed: 22 hour(s), 48 minute(s), 42 second(s)
Memory Processes Detected: 0
(No malicious items detected)
Memory Modules Detected: 0
(No malicious items detected)
Registry Keys Detected: 0
(No malicious items detected)
Registry Values Detected: 0
(No malicious items detected)
Registry Data Items Detected: 0
(No malicious items detected)
Folders Detected: 1
C:\Program Files\PCHealthCenter (Trojan.FakeAlert) -> Quarantined and deleted successfully.
Files Detected: 14
C:\Users\Melanie\Downloads\CodecPerformerSetup(1).exe (Adware.InstallBrain) -> Quarantined and deleted successfully.
C:\Users\Melanie\Downloads\CodecPerformerSetup(2).exe (Adware.InstallBrain) -> Quarantined and deleted successfully.
C:\Users\Melanie\Downloads\CodecPerformerSetup.exe (Adware.InstallBrain) -> Quarantined and deleted successfully.
C:\_OTL\MovedFiles\04302013_123709\C_Users\Melanie\AppData\Local\{65382B45-7ADE-488A-36A8-32F7161ADBA6}\syshost.exe (Trojan.FakeMS) -> Quarantined and deleted successfully.
C:\Windows\System32\1.ico (Malware.Trace) -> Quarantined and deleted successfully.
C:\Windows\System32\2.ico (Malware.Trace) -> Quarantined and deleted successfully.
C:\Program Files\PCHealthCenter\0.gif (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Program Files\PCHealthCenter\1.gif (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Program Files\PCHealthCenter\1.ico (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Program Files\PCHealthCenter\2.gif (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Program Files\PCHealthCenter\2.ico (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Program Files\PCHealthCenter\3.gif (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Program Files\PCHealthCenter\5.exe (Trojan.FakeAlert) -> Quarantined and deleted successfully.
C:\Program Files\PCHealthCenter\sc.html (Trojan.FakeAlert) -> Quarantined and deleted successfully.
(end)
All processes killed
========== COMMANDS ==========
Restore point Set: OTL Restore Point
========== REGISTRY ==========
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ShellServiceObjects\{FD6905CE-952F-41F1-9A6F-135D9C6622CC}\\"AutoStart" | "" /E : value set successfully!
========== COMMANDS ==========
[EMPTYTEMP]
User: All Users
User: Default
->Temp folder emptied: 0 bytes
->Temporary Internet Files folder emptied: 0 bytes
->Flash cache emptied: 0 bytes
User: Default User
->Temp folder emptied: 0 bytes
->Temporary Internet Files folder emptied: 0 bytes
->Flash cache emptied: 0 bytes
User: Melanie
->Temp folder emptied: 2730919 bytes
->Temporary Internet Files folder emptied: 33170 bytes
->Java cache emptied: 0 bytes
->FireFox cache emptied: 355460845 bytes
->Google Chrome cache emptied: 0 bytes
->Apple Safari cache emptied: 0 bytes
->Flash cache emptied: 4234 bytes
User: Public
User: TESTFOLDER
%systemdrive% .tmp files removed: 0 bytes
%systemroot% .tmp files removed: 0 bytes
%systemroot%\System32 .tmp files removed: 0 bytes
%systemroot%\System32\drivers .tmp files removed: 0 bytes
Windows Temp folder emptied: 8677760 bytes
RecycleBin emptied: 0 bytes
Total Files Cleaned = 350,00 mb
OTL by OldTimer - Version 3.2.69.0 log created on 09122013_215119
Files\Folders moved on Reboot...
File move failed. C:\Windows\temp\hlktmp scheduled to be moved on reboot.
PendingFileRenameOperations files...
Registry entries deleted on Reboot...
#38
![Phishing Malware Issue? (Stolen personal information) [Closed]: post #38](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 17 September 2013 - 10:32 AM
Posted 17 September 2013 - 10:32 AM

Good news all around. The last thing we need to do is check for any programs that need to be updated. Then if there aren't any further issues we will be ready to clean up the tools and wrap this puppy upMSE successfully installed.
Computer seems alright.
ESET found nothing.
Run Security Check
Download Security Check from here or here and save it to the Desktop.
- Right click the SecurityCheck icon
 and click Run as Administrator to run the application. Allow any UAC warnings.
and click Run as Administrator to run the application. Allow any UAC warnings. - Follow the onscreen instructions inside of the black box.
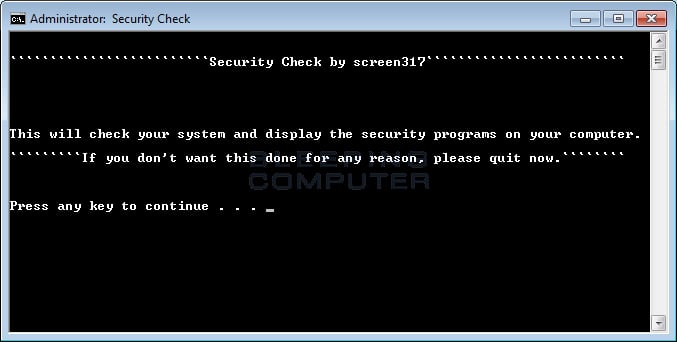
- A Notepad document should open automatically called checkup.txt; please post the contents of that document.
Things For Your Next Post:
Please post the logs in the order requested. Do Not attach the logs unless I request it.
1. The checkup.txt log
#39
![Phishing Malware Issue? (Stolen personal information) [Closed]: post #39](https://www.geekstogo.com/forum/public/style_images/shift/icon_share.png)
 Posted 21 September 2013 - 01:07 PM
Posted 21 September 2013 - 01:07 PM

If you need this topic reopened, please contact a staff member. This applies only to the original topic starter. Everyone else please begin a New Topic.
Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:








 This topic is locked
This topic is locked




 Sign In
Sign In Create Account
Create Account

