UNSUPPORTED OPERATING SYSTEM! ABORTED!
Win32:Malware-gen trojan infection
#91

 Posted 04 October 2013 - 07:57 PM
Posted 04 October 2013 - 07:57 PM

UNSUPPORTED OPERATING SYSTEM! ABORTED!
#92

 Posted 05 October 2013 - 12:17 AM
Posted 05 October 2013 - 12:17 AM

Right click on (My) Computer and select Manage (Continue) Then click on the arrow in front of Event Viewer. Next Click on the arrow in front of Windows Logs Right click on System and Clear Log, Clear. Repeat for Application.
Reboot.
Start, All Programs, Accessories then right click on Command Prompt and Run as Administrator. Then type (with an Enter after each line).
sfc /scannow
(This will check your critical system files. Does this finish without complaint? IF it says it couldn't fix everything then:
Copy the next two lines:
findstr /c:"[SR]" \windows\logs\cbs\cbs.log > \windows\logs\cbs\junk.txt
notepad \windows\logs\cbs\junk.txt
Start, All Programs, Accessories, right click on Command Prompt and Run as Administrator, Continue. Right click and Paste or Edit then Paste and the copied line should appear.
Hit Enter. Copy and paste the text from notepad or if it is too big, just attach the file.)
1. Please download the Event Viewer Tool by Vino Rosso
http://images.malwar...om/vino/VEW.exe
and save it to your Desktop:
2. Right-click VEW.exe and Run AS Administrator
3. Under 'Select log to query', select:
* System
4. Under 'Select type to list', select:
* Error
* Warning
Then use the 'Number of events' as follows:
1. Click the radio button for 'Number of events'
Type 20 in the 1 to 20 box
Then click the Run button.
Notepad will open with the output log.
Please post the Output log in your next reply then repeat but select Application.
IF it is still locking up when you close the lid
see if you wait one minute after plugging it in if it will then go to sleep when the lid is closed and wake up when you open it. It could be that it gets caught switching between battery and AC mode.
IF you don't plug it in first does it go to sleep when you close the lid and awaken OK when you open it?
Does it go to Sleep and come out of it if you put it to sleep from the Start, Shutdown arrow, Sleep option?
You can go into Control Panel, Power Options, One of the plans should be checked. Click on its Change Plan Settings then on Change Advanced Power Settings. Find Power Buttons and Lid and click on the + in front of it. There should be an option for what happens when the lid is closed. Try changing it to something else.
#93

 Posted 05 October 2013 - 05:27 AM
Posted 05 October 2013 - 05:27 AM

sfc /scannow ran no problems. windows resource protection did not find any integrity violations.
#94

 Posted 05 October 2013 - 05:31 AM
Posted 05 October 2013 - 05:31 AM

Vino's Event Viewer v01c run on Windows 2008 in English
Report run at 05/10/2013 6:30:03 AM
Note: All dates below are in the format dd/mm/yyyy
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
'System' Log - Critical Type
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
'System' Log - Error Type
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
'System' Log - Warning Type
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Log: 'System' Date/Time: 05/10/2013 11:06:03 AM
Type: Warning Category: 212
Event: 219 Source: Microsoft-Windows-Kernel-PnP
The driver \Driver\WUDFRd failed to load for the device USB\VID_138A&PID_0018\04a4745dff40.
Log: 'System' Date/Time: 05/10/2013 11:05:25 AM
Type: Warning Category: 0
Event: 4001 Source: Microsoft-Windows-WLAN-AutoConfig
WLAN AutoConfig service has successfully stopped.
Log: 'System' Date/Time: 05/10/2013 11:05:25 AM
Type: Warning Category: 0
Event: 10002 Source: Microsoft-Windows-WLAN-AutoConfig
WLAN Extensibility Module has stopped. Module Path: C:\Windows\System32\IWMSSvc.dll
Vino's Event Viewer v01c run on Windows 2008 in English
Report run at 05/10/2013 6:31:34 AM
Note: All dates below are in the format dd/mm/yyyy
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
'Application' Log - Critical Type
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
'Application' Log - Error Type
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Log: 'Application' Date/Time: 05/10/2013 11:06:33 AM
Type: Error Category: 0
Event: 10 Source: Microsoft-Windows-WMI
Event filter with query "SELECT * FROM __InstanceModificationEvent WITHIN 60 WHERE TargetInstance ISA "Win32_Processor" AND TargetInstance.LoadPercentage > 99" could not be reactivated in namespace "//./root/CIMV2" because of error 0x80041003. Events cannot be delivered through this filter until the problem is corrected.
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
'Application' Log - Warning Type
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
Log: 'Application' Date/Time: 05/10/2013 11:16:46 AM
Type: Warning Category: 3
Event: 3036 Source: Microsoft-Windows-Search
The content source <ONEINDEX14://{S-1-5-21-2271316084-460775634-2034437219-1000}/> cannot be accessed.
Context: Application, SystemIndex Catalog
Details:
(HRESULT : 0x80004005) (0x80004005)
Log: 'Application' Date/Time: 05/10/2013 11:05:21 AM
Type: Warning Category: 0
Event: 1530 Source: Microsoft-Windows-User Profiles Service
Windows detected your registry file is still in use by other applications or services. The file will be unloaded now. The applications or services that hold your registry file may not function properly afterwards. DETAIL - 16 user registry handles leaked from \Registry\User\S-1-5-21-2271316084-460775634-2034437219-1000:
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Microsoft\SystemCertificates\trust
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Microsoft\SystemCertificates\SmartCardRoot
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Microsoft\SystemCertificates\Root
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Microsoft\SystemCertificates\TrustedPeople
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Policies\Microsoft\SystemCertificates
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Policies\Microsoft\SystemCertificates
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Policies\Microsoft\SystemCertificates
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Policies\Microsoft\SystemCertificates
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Microsoft\SystemCertificates\My
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Microsoft\SystemCertificates\CA
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000\Software\Microsoft\SystemCertificates\Disallowed
#95

 Posted 05 October 2013 - 09:26 AM
Posted 05 October 2013 - 09:26 AM

Type: Warning Category: 212
Event: 219 Source: Microsoft-Windows-Kernel-PnP
The driver \Driver\WUDFRd failed to load for the device USB\VID_138A&PID_0018\04a4745dff40.
This is supposed to be your fingerprint reader. Perhaps a reinstall of the fingerprint reader driver would help:
Look on the PC maker's website for the latest driver for it or if they don't have anything you can try:
http://h10025.www1.h...118737&sw_lang=
Event: 10 Source: Microsoft-Windows-WMI
Event filter with query "SELECT * FROM __InstanceModificationEvent WITHIN 60 WHERE TargetInstance ISA "Win32_Processor" AND TargetInstance.LoadPercentage > 99" could not be reactivated in namespace "//./root/CIMV2" because of error 0x80041003. Events cannot be delivered through this filter until the problem is corrected.
Run the FixIt here:
http://support.micro...b;en-US;2545227
Type: Warning Category: 3
Event: 3036 Source: Microsoft-Windows-Search
The content source <ONEINDEX14://{S-1-5-21-2271316084-460775634-2034437219-1000}/> cannot be accessed.
Context: Application, SystemIndex Catalog
Details:
(HRESULT : 0x80004005) (0x80004005)
a. Go to Start > Control Panel.
b. Double click on the Indexing Options.
c. Click on the Advanced button.
d. Click on on Restore Defaults.
or you can just turn it off:
http://www.howtogeek...h-in-windows-7/
Event: 1530 Source: Microsoft-Windows-User Profiles Service
Windows detected your registry file is still in use by other applications or services. The file will be unloaded now. The applications or services that hold your registry file may not function properly afterwards. DETAIL - 16 user registry handles leaked from \Registry\User\S-1-5-21-2271316084-460775634-2034437219-1000:
Process 2784 (\Device\HarddiskVolume2\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Virus 2013\avp.exe) has opened key \REGISTRY\USER\S-1-5-21-2271316084-460775634-2034437219-1000
Hopefully a newer version of Kaspersky will fix these errors. This could cause problems with Kaspersky and with shutdown so you should at least try to get a newer install.
#96

 Posted 05 October 2013 - 03:57 PM
Posted 05 October 2013 - 03:57 PM

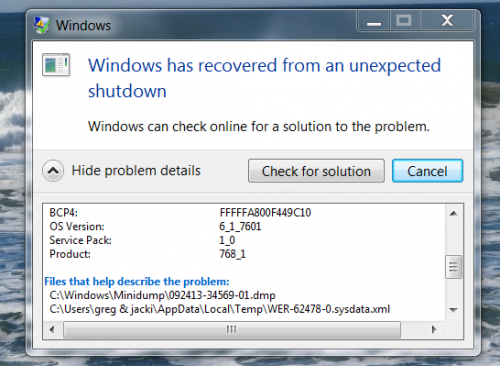
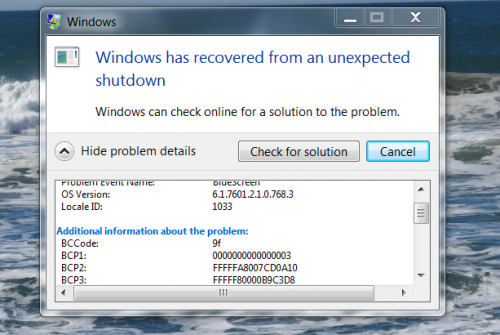
would any of this cause web pages or start up to be really slow? also, can any of this contribute to the blue pscreen i gat a little while back?
i captured a snip of it in two parts
#97

 Posted 05 October 2013 - 05:27 PM
Posted 05 October 2013 - 05:27 PM

Download BlueScreenView
http://www.nirsoft.n...creen_view.html
Double click on BlueScreenView.exe file to run the program.
When scanning is done, go Edit, Select All.
Go File, Save Selected Items, and save the report as BSOD.txt.
Open BSOD.txt in Notepad, copy all content, and paste it into your next reply.
#98

 Posted 05 October 2013 - 09:04 PM
Posted 05 October 2013 - 09:04 PM

==================================================
Dump File : 100413-22916-01.dmp
Crash Time : 10/3/2013 9:24:42 PM
Bug Check String : DRIVER_POWER_STATE_FAILURE
Bug Check Code : 0x0000009f
Parameter 1 : 00000000`00000003
Parameter 2 : fffffa80`080b5060
Parameter 3 : fffff800`00b9c3d8
Parameter 4 : fffffa80`11340010
Caused By Driver : ntoskrnl.exe
Caused By Address : ntoskrnl.exe+72f40
File Description : NT Kernel & System
Product Name : Microsoft® Windows® Operating System
Company : Microsoft Corporation
File Version : 6.1.7601.22411 (win7sp1_ldr.130801-1934)
Processor : x64
Crash Address : ntoskrnl.exe+72f40
Stack Address 1 :
Stack Address 2 :
Stack Address 3 :
Computer Name :
Full Path : C:\Windows\Minidump\100413-22916-01.dmp
Processors Count : 4
Major Version : 15
Minor Version : 7601
Dump File Size : 985,136
Dump File Time : 10/4/2013 6:06:01 AM
==================================================
==================================================
Dump File : 093013-21933-01.dmp
Crash Time : 9/30/2013 6:37:13 AM
Bug Check String : DRIVER_POWER_STATE_FAILURE
Bug Check Code : 0x0000009f
Parameter 1 : 00000000`00000003
Parameter 2 : fffffa80`07d31a10
Parameter 3 : fffff800`00b9c3d8
Parameter 4 : fffffa80`0f523b40
Caused By Driver : ntoskrnl.exe
Caused By Address : ntoskrnl.exe+72f40
File Description : NT Kernel & System
Product Name : Microsoft® Windows® Operating System
Company : Microsoft Corporation
File Version : 6.1.7601.22411 (win7sp1_ldr.130801-1934)
Processor : x64
Crash Address : ntoskrnl.exe+72f40
Stack Address 1 :
Stack Address 2 :
Stack Address 3 :
Computer Name :
Full Path : C:\Windows\Minidump\093013-21933-01.dmp
Processors Count : 4
Major Version : 15
Minor Version : 7601
Dump File Size : 980,472
Dump File Time : 9/30/2013 6:50:32 PM
==================================================
#99

 Posted 05 October 2013 - 10:29 PM
Posted 05 October 2013 - 10:29 PM

#100

 Posted 05 October 2013 - 11:12 PM
Posted 05 October 2013 - 11:12 PM

#101

 Posted 06 October 2013 - 06:43 AM
Posted 06 October 2013 - 06:43 AM

#102

 Posted 06 October 2013 - 06:54 AM
Posted 06 October 2013 - 06:54 AM

#103

 Posted 06 October 2013 - 09:25 AM
Posted 06 October 2013 - 09:25 AM

#104

 Posted 06 October 2013 - 09:39 AM
Posted 06 October 2013 - 09:39 AM

#105

 Posted 06 October 2013 - 09:44 AM
Posted 06 October 2013 - 09:44 AM

Similar Topics
0 user(s) are reading this topic
0 members, 0 guests, 0 anonymous users
As Featured On:














 Sign In
Sign In Create Account
Create Account

