You are absolutely right about there being ransomware on here. When I booted back up in normal mode and connected to the internet, 4 files were downloaded automatically, a Help_Decrpyt picture, .txt file .html file and .url file, the screen went purple and then it popped up saying my files had been encrypted and junk. I was able to alt+ctrl+delete and bring up task manager turned off some startup programs that didn't look familiar and was able to sign out and back in to do the scans. Thanks for the quick reply and attached are the requested logs!
1.| Possible CryptoWall Flag , HKCU\Software\D459277330F21B8C46B7BA72B04D3BE0\002344677ABBBBDE
Scan result of Farbar Recovery Scan Tool (FRST.txt) (x64) Version: 21-02-2015
Ran by Dorothy01 (administrator) on DOROTHY on 21-02-2015 22:39:57
Running from C:\Users\Dorothy01\Desktop
Loaded Profiles: Dorothy01 (Available profiles: Dorothy01)
Platform: Windows 8.1 (X64) OS Language: English (United States)
Internet Explorer Version 11 (Default browser: Chrome)
Boot Mode: Normal
==================== Processes (Whitelisted) =================
(If an entry is included in the fixlist, the process will be closed. The file will not be moved.)
(AMD) C:\Windows\System32\atiesrxx.exe
(AVAST Software) C:\Program Files\AVAST Software\Avast\AvastSvc.exe
(Andrea Electronics Corporation) C:\Program Files\Realtek\Audio\HDA\AERTSr64.exe
(Advanced Micro Devices, Inc.) C:\Program Files\ATI Technologies\ATI.ACE\Fuel\Fuel.Service.exe
(Apple Inc.) C:\Program Files (x86)\Common Files\Apple\Mobile Device Support\AppleMobileDeviceService.exe
(Apple Inc.) C:\Program Files\Bonjour\mDNSResponder.exe
(Microsoft Corporation) C:\Windows\System32\dasHost.exe
(Apple Inc.) C:\Program Files\iPod\bin\iPodService.exe
(Hewlett-Packard Company) C:\Program Files (x86)\Hewlett-Packard\HP Support Framework\HPSA_Service.exe
(Hewlett-Packard) C:\Program Files (x86)\Hewlett-Packard\HP Connected Remote\HPConnectedRemoteService.exe
(Realsil Microelectronics Inc.) C:\Program Files (x86)\Realtek\Realtek PCIE Card Reader\RIconMan.exe
(Symantec Corporation) C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\ccsvchst.exe
(AMD) C:\Windows\System32\atieclxx.exe
(Symantec Corporation) C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\ccsvchst.exe
(Microsoft Corporation) C:\Windows\System32\dllhost.exe
(Hewlett-Packard) C:\Program Files (x86)\Hewlett-Packard\HP Connected Remote\HPConnectedRemoteUser.exe
(Realtek Semiconductor) C:\Program Files\Realtek\Audio\HDA\RtkNGUI64.exe
(Microsoft Corporation) C:\Windows\SysWOW64\dllhost.exe
(Advanced Micro Devices Inc.) C:\Program Files (x86)\ATI Technologies\ATI.ACE\Core-Static\MOM.exe
(Apple Inc.) C:\Program Files (x86)\iTunes\iTunesHelper.exe
(AVAST Software) C:\Program Files\AVAST Software\Avast\avastui.exe
(ATI Technologies Inc.) C:\Program Files (x86)\ATI Technologies\ATI.ACE\Core-Static\CCC.exe
==================== Registry (Whitelisted) ==================
(If an entry is included in the fixlist, the registry item will be restored to default or removed. The file will not be moved.)
HKLM\...\Run: [RTHDVCPL] => C:\Program Files\Realtek\Audio\HDA\RtkNGUI64.exe [6549136 2012-07-02] (Realtek Semiconductor)
HKLM-x32\...\Run: [StartCCC] => C:\Program Files (x86)\ATI Technologies\ATI.ACE\Core-Static\amd64\CLIStart.exe [766688 2014-07-04] (Advanced Micro Devices, Inc.)
HKLM-x32\...\Run: [CLMLServer_For_P2G8] => c:\Program Files (x86)\CyberLink\Power2Go8\CLMLSvc_P2G8.exe [111120 2012-06-07] (CyberLink)
HKLM-x32\...\Run: [CLVirtualDrive] => c:\Program Files (x86)\CyberLink\Power2Go8\VirtualDrive.exe [491120 2012-07-02] (CyberLink Corp.)
HKLM-x32\...\Run: [iTunesHelper] => C:\Program Files (x86)\iTunes\iTunesHelper.exe [152392 2014-08-01] (Apple Inc.)
HKLM-x32\...\Run: [AvastUI.exe] => C:\Program Files\AVAST Software\Avast\AvastUI.exe [5227112 2015-02-19] (AVAST Software)
HKLM-x32\...\Run: [CrashReportSaver] => C:\WINDOWS\Installer\{4E61FB7C-E89A-4510-ADC1-B38572ADB03D}\msiexec.exe [1464320 2015-02-20] (EFD Software)
Winlogon\Notify\pckunie-x32: C:\Users\Dorothy01\AppData\Local\pckunie.dll ()
Winlogon\Notify\pgkunge-x32: C:\Users\Dorothy01\AppData\Local\pgkunge.dll ()
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\Run: [Driver Support] => C:\Program Files (x86)\Driver Support\Driver Support\DriverSupport.exe /applicationMode:systemTray /showWelcome:false
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\Run: [acikmao] => rundll32 "C:\Users\Dorothy01\AppData\Local\acikmao.dll",acikmao <===== ATTENTION
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\Run: [dccwmote] => C:\Users\Dorothy01\AppData\Local\Temp\getmhost.exe [406016 2015-02-21] () <===== ATTENTION
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\Run: [BluetoothS] => rundll32.exe "%appdata%\BtvStack.dll",BTHF_Register
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\MountPoints2: {5042c0a6-b247-11e4-bed4-089e013a632b} - "G:\AutoRun.exe"
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...A8F59079A8D5}\localserver32: rundll32.exe javascript:"\..\mshtml.dll,RunHTMLApplication ";eval("epdvnfou/xsjuf)(=tdsjqu!mbohvbhf> (the data entry has 243 more characters). <==== Poweliks!
Startup: C:\Users\Dorothy01\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\HELP_DECRYPT.HTML ()
Startup: C:\Users\Dorothy01\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\HELP_DECRYPT.PNG ()
Startup: C:\Users\Dorothy01\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\HELP_DECRYPT.TXT ()
InternetURL: C:\Users\Dorothy01\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\HELP_DECRYPT.URL -> hxxp://paytoc4gtpn5czl2.torconnectpaycom/1msme5i
ShellIconOverlayIdentifiers: [00avast] -> {472083B0-C522-11CF-8763-00608CC02F24} => C:\Program Files\AVAST Software\Avast\ashShA64.dll (AVAST Software)
==================== Internet (Whitelisted) ====================
(If an item is included in the fixlist, if it is a registry item it will be removed or restored to default.)
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\Software\Microsoft\Internet Explorer\Main,Start Page Redirect Cache =
http://www.msn.com/?ocid=iehpSearchScopes: HKU\.DEFAULT -> DefaultScope {0633EE93-D776-472f-A0FF-E1416B8B2E3A} URL =
SearchScopes: HKU\S-1-5-19 -> DefaultScope {0633EE93-D776-472f-A0FF-E1416B8B2E3A} URL =
SearchScopes: HKU\S-1-5-20 -> DefaultScope {0633EE93-D776-472f-A0FF-E1416B8B2E3A} URL =
BHO: No Name -> {7F96F190-09C4-4BEC-B7FB-A9E26151EAB0}} -> No File
BHO: No Name -> {AA58ED58-01DD-4d91-8333-CF10577473F7} -> No File
BHO-x32: Norton Identity Protection -> {602ADB0E-4AFF-4217-8AA1-95DAC4DFA408} -> C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\coIEPlg.dll (Symantec Corporation)
BHO-x32: Norton Vulnerability Protection -> {6D53EC84-6AAE-4787-AEEE-F4628F01010C} -> C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\IPS\IPSBHO.DLL (Symantec Corporation)
BHO-x32: Java™ Plug-In SSV Helper -> {761497BB-D6F0-462C-B6EB-D4DAF1D92D43} -> C:\Program Files (x86)\Java\jre1.8.0_31\bin\ssv.dll (Oracle Corporation)
BHO-x32: No Name -> {7F96F190-09C4-4BEC-B7FB-A9E26151EAB0}} -> No File
BHO-x32: Google Toolbar Helper -> {AA58ED58-01DD-4d91-8333-CF10577473F7} -> C:\Program Files (x86)\Google\Google Toolbar\GoogleToolbar_32.dll (Google Inc.)
BHO-x32: Java™ Plug-In 2 SSV Helper -> {DBC80044-A445-435b-BC74-9C25C1C588A9} -> C:\Program Files (x86)\Java\jre1.8.0_31\bin\jp2ssv.dll (Oracle Corporation)
BHO-x32: HP Network Check Helper -> {E76FD755-C1BA-4DCB-9F13-99BD91223ADE} -> C:\Program Files (x86)\Hewlett-Packard\HP Support Framework\Resources\HPNetworkCheck\HPNetworkCheckPlugin.dll (Hewlett-Packard)
Toolbar: HKLM - No Name - {2318C2B1-4965-11d4-9B18-009027A5CD4F} - No File
Toolbar: HKLM-x32 - Norton Toolbar - {7FEBEFE3-6B19-4349-98D2-FFB09D4B49CA} - C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\coIEPlg.dll (Symantec Corporation)
Toolbar: HKLM-x32 - Google Toolbar - {2318C2B1-4965-11d4-9B18-009027A5CD4F} - C:\Program Files (x86)\Google\Google Toolbar\GoogleToolbar_32.dll (Google Inc.)
Toolbar: HKU\.DEFAULT -> No Name - {7FEBEFE3-6B19-4349-98D2-FFB09D4B49CA} - No File
Hosts: There are more than one entry in Hosts. See Hosts section of Addition.txt
Tcpip\Parameters: [DhcpNameServer] 192.168.1.254
Tcpip\..\Interfaces\{0C5C3F02-879E-42E8-8113-9C0FA649DB90}: [NameServer] 8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8
Tcpip\..\Interfaces\{462105B1-AF78-47E3-AC0D-109F28027A93}: [NameServer] 8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8
Tcpip\..\Interfaces\{8718928D-CBEB-45EA-A621-800A9249001D}: [NameServer] 8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8
Tcpip\..\Interfaces\{9B004C7D-7A34-4A9C-BEDB-5212A582FAB1}: [NameServer] 8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8
Tcpip\..\Interfaces\{D24FA36B-6CD5-4603-8F72-73AC28D99F5B}: [NameServer] 8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8,8.8.8.8
FireFox:
========
FF Plugin-x32: @Apple.com/iTunes,version=1.0 -> C:\Program Files (x86)\iTunes\Mozilla Plugins\npitunes.dll ()
FF Plugin-x32: @java.com/DTPlugin,version=11.31.2 -> C:\Program Files (x86)\Java\jre1.8.0_31\bin\dtplugin\npDeployJava1.dll (Oracle Corporation)
FF Plugin-x32: @java.com/JavaPlugin,version=11.31.2 -> C:\Program Files (x86)\Java\jre1.8.0_31\bin\plugin2\npjp2.dll (Oracle Corporation)
FF Plugin-x32: @microsoft.com/WLPG,version=15.4.3502.0922 -> C:\Program Files (x86)\Windows Live\Photo Gallery\NPWLPG.dll (Microsoft Corporation)
FF Plugin-x32: @microsoft.com/WLPG,version=15.4.3555.0308 -> C:\Program Files (x86)\Windows Live\Photo Gallery\NPWLPG.dll (Microsoft Corporation)
FF Plugin-x32: @tools.google.com/Google Update;version=3 -> C:\Program Files (x86)\Google\Update\1.3.26.9\npGoogleUpdate3.dll (Google Inc.)
FF Plugin-x32: @tools.google.com/Google Update;version=9 -> C:\Program Files (x86)\Google\Update\1.3.26.9\npGoogleUpdate3.dll (Google Inc.)
FF Plugin-x32: @WildTangent.com/GamesAppPresenceDetector,Version=1.0 -> C:\Program Files (x86)\WildTangent Games\App\BrowserIntegration\Registered\0\NP_wtapp.dll ()
FF HKLM-x32\...\Firefox\Extensions: [{BBDA0591-3099-440a-AA10-41764D9DB4DB}] - C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_20.0.0.136\IPSFF
FF Extension: Norton Vulnerability Protection - C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_20.0.0.136\IPSFF [2014-07-23]
FF HKLM-x32\...\Firefox\Extensions: [{2D3F3651-74B9-4795-BDEC-6DA2F431CB62}] - C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_20.0.0.136\coFFPlgn
FF Extension: Norton Toolbar - C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_20.0.0.136\coFFPlgn [2015-02-20]
Chrome:
=======
CHR StartupUrls: Default -> "hxxp://www.google.com/"
CHR Profile: C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default
CHR Extension: (Google Slides) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\aapocclcgogkmnckokdopfmhonfmgoek [2015-02-19]
CHR Extension: (Google Docs) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\aohghmighlieiainnegkcijnfilokake [2015-02-19]
CHR Extension: (Google Drive) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\apdfllckaahabafndbhieahigkjlhalf [2015-02-19]
CHR Extension: (Google Voice Search Hotword (Beta)) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\bepbmhgboaologfdajaanbcjmnhjmhfn [2015-02-19]
CHR Extension: (YouTube) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\blpcfgokakmgnkcojhhkbfbldkacnbeo [2015-02-19]
CHR Extension: (Google Search) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\coobgpohoikkiipiblmjeljniedjpjpf [2015-02-19]
CHR Extension: (Google Sheets) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\felcaaldnbdncclmgdcncolpebgiejap [2015-02-19]
CHR Extension: (Norton Identity Safe) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\iikflkcanblccfahdhdonehdalibjnif [2015-02-19]
CHR Extension: (Google Wallet) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\nmmhkkegccagdldgiimedpiccmgmieda [2015-02-19]
CHR Extension: (Gmail) - C:\Users\Dorothy01\AppData\Local\Google\Chrome\User Data\Default\Extensions\pjkljhegncpnkpknbcohdijeoejaedia [2015-02-19]
CHR HKLM\...\Chrome\Extension: [bejnhdlplbjhffionohbdnpcbobfejcc] - C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\Exts\Chrome.crx [2014-12-09]
CHR HKLM-x32\...\Chrome\Extension: [bejnhdlplbjhffionohbdnpcbobfejcc] - C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\Exts\Chrome.crx [2014-12-09]
==================== Services (Whitelisted) =================
(If an entry is included in the fixlist, the service will be removed from the registry. The file will not be moved unless listed separately.)
R2 AMD FUEL Service; C:\Program Files\ATI Technologies\ATI.ACE\Fuel\Fuel.Service.exe [344064 2014-07-04] (Advanced Micro Devices, Inc.) [File not signed]
R2 avast! Antivirus; C:\Program Files\AVAST Software\Avast\AvastSvc.exe [50344 2015-02-19] (AVAST Software)
R2 HP Support Assistant Service; C:\Program Files (x86)\Hewlett-Packard\HP Support Framework\hpsa_service.exe [85504 2012-08-15] (Hewlett-Packard Company) [File not signed]
R2 HPConnectedRemote; c:\Program Files (x86)\Hewlett-Packard\HP Connected Remote\HPConnectedRemoteService.exe [35232 2012-07-19] (Hewlett-Packard)
R2 IconMan_R; C:\Program Files (x86)\Realtek\Realtek PCIE Card Reader\RIconMan.exe [2451456 2012-07-13] (Realsil Microelectronics Inc.) [File not signed]
R2 NIS; C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\ccSvcHst.exe [144368 2013-05-20] (Symantec Corporation)
S3 w3logsvc; C:\Windows\system32\inetsrv\w3logsvc.dll [76800 2014-10-14] (Microsoft Corporation)
S3 WdNisSvc; C:\Program Files\Windows Defender\NisSrv.exe [347880 2014-09-24] (Microsoft Corporation)
S3 WinDefend; C:\Program Files\Windows Defender\MsMpEng.exe [23824 2014-09-24] (Microsoft Corporation)
==================== Drivers (Whitelisted) ====================
(If an entry is included in the fixlist, the service will be removed from the registry. The file will not be moved unless listed separately.)
R2 aswHwid; C:\Windows\system32\drivers\aswHwid.sys [29208 2015-02-19] ()
R2 aswMonFlt; C:\Windows\system32\drivers\aswMonFlt.sys [83280 2015-02-19] (AVAST Software)
R0 aswRvrt; C:\Windows\System32\Drivers\aswRvrt.sys [65776 2015-02-19] ()
R1 aswSnx; C:\Windows\system32\drivers\aswSnx.sys [1050432 2015-02-19] (AVAST Software)
R1 aswSP; C:\Windows\system32\drivers\aswSP.sys [436624 2015-02-19] (AVAST Software)
R0 aswVmm; C:\Windows\System32\Drivers\aswVmm.sys [267632 2015-02-19] ()
R3 BHDrvx64; C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_20.0.0.136\Definitions\BASHDefs\20140912.003\BHDrvx64.sys [1586904 2014-09-12] (Symantec Corporation)
S3 BS1924802738; C:\Users\Dorothy01\AppData\Local\Temp\NTFS.sys [13192 2015-02-21] (Sysinternals) [File not signed]
R3 ccSet_NIS; C:\Windows\system32\drivers\NISx64\1406000.01B\ccSetx64.sys [169048 2013-04-15] (Symantec Corporation)
R1 CLVirtualDrive; C:\Windows\system32\DRIVERS\CLVirtualDrive.sys [92536 2012-06-25] (CyberLink)
R3 eeCtrl; C:\Program Files (x86)\Common Files\Symantec Shared\EENGINE\eeCtrl64.sys [487216 2014-09-09] (Symantec Corporation)
R3 EraserUtilRebootDrv; C:\Program Files (x86)\Common Files\Symantec Shared\EENGINE\EraserUtilRebootDrv.sys [142640 2014-09-09] (Symantec Corporation)
R3 IDSVia64; C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_20.0.0.136\Definitions\IPSDefs\20140919.001\IDSvia64.sys [633560 2014-08-29] (Symantec Corporation)
S3 massfilter_hs; C:\WINDOWS\system32\drivers\massfilter_hs.sys [20232 2012-06-20] (HandSet Incorporated)
S3 MBAMSwissArmy; C:\WINDOWS\system32\drivers\MBAMSwissArmy.sys [129752 2015-02-19] (Malwarebytes Corporation)
S3 NAVENG; C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_20.0.0.136\Definitions\VirusDefs\20140920.001\ENG64.SYS [129752 2014-09-01] (Symantec Corporation)
S3 NAVEX15; C:\ProgramData\Norton\{0C55C096-0F1D-4F28-AAA2-85EF591126E7}\NIS_20.0.0.136\Definitions\VirusDefs\20140920.001\EX64.SYS [2137304 2014-09-01] (Symantec Corporation)
S3 SRTSP; C:\Windows\System32\Drivers\NISx64\1406000.01B\SRTSP64.SYS [796760 2013-05-15] (Symantec Corporation)
R3 SRTSPX; C:\Windows\system32\drivers\NISx64\1406000.01B\SRTSPX64.SYS [36952 2013-03-04] (Symantec Corporation)
R3 SymDS; C:\Windows\system32\drivers\NISx64\1406000.01B\SYMDS64.SYS [493656 2013-05-20] (Symantec Corporation)
R3 SymEFA; C:\Windows\system32\drivers\NISx64\1406000.01B\SYMEFA64.SYS [1139800 2013-05-22] (Symantec Corporation)
S4 SymELAM; C:\Windows\system32\drivers\NISx64\1406000.01B\SymELAM.sys [23448 2012-06-20] (Symantec Corporation)
R3 SymEvent; C:\windows\system32\Drivers\SYMEVENT64x86.SYS [177312 2014-07-23] (Symantec Corporation)
R3 SymIRON; C:\Windows\system32\drivers\NISx64\1406000.01B\Ironx64.SYS [224416 2013-03-04] (Symantec Corporation)
R3 SymNetS; C:\Windows\System32\Drivers\NISx64\1406000.01B\SYMNETS.SYS [433752 2013-04-24] (Symantec Corporation)
U3 TrueSight; C:\Windows\System32\drivers\TrueSight.sys [37624 2015-02-20] ()
S3 WdNisDrv; C:\Windows\System32\Drivers\WdNisDrv.sys [123224 2014-09-24] (Microsoft Corporation)
==================== NetSvcs (Whitelisted) ===================
(If an item is included in the fixlist, it will be removed from the registry. Any associated file could be listed separately to be moved.)
==================== One Month Created Files and Folders ========
(If an entry is included in the fixlist, the file\folder will be moved.)
2015-02-21 22:39 - 2015-02-21 22:40 - 00018356 _____ () C:\Users\Dorothy01\Desktop\FRST.txt
2015-02-21 22:39 - 2015-02-21 22:40 - 00000000 ____D () C:\FRST
2015-02-21 22:38 - 2015-02-21 22:38 - 00000383 _____ () C:\Users\Dorothy01\Desktop\idtool.txt
2015-02-21 22:24 - 2015-02-21 22:24 - 00008630 _____ () C:\Users\Dorothy01\HELP_DECRYPT.HTML
2015-02-21 22:24 - 2015-02-21 22:24 - 00008630 _____ () C:\Users\Dorothy01\Downloads\HELP_DECRYPT.HTML
2015-02-21 22:24 - 2015-02-21 22:24 - 00008630 _____ () C:\Users\Dorothy01\Desktop\HELP_DECRYPT.HTML
2015-02-21 22:24 - 2015-02-21 22:24 - 00004258 _____ () C:\Users\Dorothy01\HELP_DECRYPT.TXT
2015-02-21 22:24 - 2015-02-21 22:24 - 00004258 _____ () C:\Users\Dorothy01\Downloads\HELP_DECRYPT.TXT
2015-02-21 22:24 - 2015-02-21 22:24 - 00004258 _____ () C:\Users\Dorothy01\Desktop\HELP_DECRYPT.TXT
2015-02-21 22:24 - 2015-02-21 22:24 - 00000292 _____ () C:\Users\Dorothy01\HELP_DECRYPT.URL
2015-02-21 22:24 - 2015-02-21 22:24 - 00000292 _____ () C:\Users\Dorothy01\Downloads\HELP_DECRYPT.URL
2015-02-21 22:24 - 2015-02-21 22:24 - 00000292 _____ () C:\Users\Dorothy01\Desktop\HELP_DECRYPT.URL
2015-02-21 22:15 - 2015-02-21 22:15 - 02086912 _____ (Farbar) C:\Users\Dorothy01\Desktop\FRST64.exe
2015-02-21 22:12 - 2015-02-21 22:12 - 02745248 _____ () C:\Users\Dorothy01\Downloads\idtool.zip
2015-02-21 19:12 - 2015-02-21 19:12 - 00101120 _____ () C:\Users\Dorothy01\Downloads\Extras.Txt
2015-02-21 19:07 - 2015-02-21 19:14 - 00137792 _____ () C:\Users\Dorothy01\Downloads\OTL.Txt
2015-02-21 18:42 - 2015-02-21 18:42 - 00602112 _____ (OldTimer Tools) C:\Users\Dorothy01\Downloads\OTL.exe
2015-02-21 18:33 - 2015-02-21 18:33 - 00001616 _____ () C:\WINDOWS\PFRO.log
2015-02-21 03:30 - 2015-02-21 03:30 - 00023552 _____ () C:\Users\Dorothy01\AppData\Local\pgkunge.dll
2015-02-20 19:35 - 2015-02-20 19:35 - 02347384 _____ (ESET) C:\Users\Dorothy01\Downloads\esetsmartinstaller_enu.exe
2015-02-20 19:35 - 2015-02-20 19:35 - 02347384 _____ (ESET) C:\Users\Dorothy01\Downloads\esetsmartinstaller_enu (1).exe
2015-02-20 19:33 - 2015-02-20 19:33 - 00190152 _____ (ESET) C:\Users\Dorothy01\Downloads\ESETPoweliksCleaner (2).exe
2015-02-20 19:33 - 2015-02-20 19:33 - 00190152 _____ (ESET) C:\Users\Dorothy01\Downloads\ESETPoweliksCleaner (1).exe
2015-02-20 19:33 - 2015-02-20 19:33 - 00002814 _____ () C:\Users\Dorothy01\Downloads\ESETPoweliksCleaner (1).exe_20150220.193324.1664.log
2015-02-20 06:45 - 2015-02-21 22:40 - 00000000 ____D () C:\Users\Dorothy01\AppData\Local\CrashDumps
2015-02-20 06:41 - 2015-02-20 18:46 - 00000922 _____ () C:\WINDOWS\Tasks\GoogleUpdateTaskMachineUA.job
2015-02-20 06:41 - 2015-02-20 06:41 - 00003894 _____ () C:\WINDOWS\System32\Tasks\GoogleUpdateTaskMachineUA
2015-02-20 06:41 - 2015-02-20 06:41 - 00003658 _____ () C:\WINDOWS\System32\Tasks\GoogleUpdateTaskMachineCore
2015-02-20 06:07 - 2015-02-20 19:18 - 00037624 _____ () C:\WINDOWS\system32\Drivers\TrueSight.sys
2015-02-20 06:07 - 2015-02-20 06:07 - 00000000 ____D () C:\ProgramData\RogueKiller
2015-02-19 22:07 - 2015-02-19 22:09 - 18683992 _____ () C:\Users\Dorothy01\Downloads\RogueKillerX64.exe
2015-02-19 22:04 - 2015-02-19 22:04 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\AVAST Software
2015-02-19 21:41 - 2015-02-19 21:41 - 00002814 _____ () C:\Users\Dorothy01\Downloads\ESETPoweliksCleaner.exe_20150219.214114.592.log
2015-02-19 21:33 - 2015-02-21 03:14 - 00000000 ____D () C:\AdwCleaner
2015-02-19 21:33 - 2015-02-19 21:33 - 00002814 _____ () C:\Users\Dorothy01\Downloads\ESETPoweliksCleaner.exe_20150219.213330.1188.log
2015-02-19 21:33 - 2015-02-19 21:33 - 00002814 _____ () C:\Users\Dorothy01\Downloads\ESETPoweliksCleaner.exe_20150219.213304.1212.log
2015-02-19 21:32 - 2015-02-19 21:33 - 02126848 _____ () C:\Users\Dorothy01\Downloads\adwcleaner_4.111.exe
2015-02-19 21:32 - 2015-02-19 21:32 - 00190152 _____ (ESET) C:\Users\Dorothy01\Downloads\ESETPoweliksCleaner.exe
2015-02-19 21:32 - 2015-02-19 21:32 - 00002814 _____ () C:\Users\Dorothy01\Downloads\ESETPoweliksCleaner.exe_20150219.213253.1128.log
2015-02-19 21:27 - 2015-02-19 21:27 - 00001982 _____ () C:\Users\Public\Desktop\Avast Free Antivirus.lnk
2015-02-19 21:27 - 2015-02-19 21:27 - 00000000 ____D () C:\ProgramData\Microsoft\Windows\Start Menu\Programs\AVAST Software
2015-02-19 21:27 - 2015-02-19 21:17 - 00364512 _____ (AVAST Software) C:\WINDOWS\system32\aswBoot.exe
2015-02-19 21:23 - 2015-02-19 21:23 - 05006864 _____ (AVAST Software) C:\Users\Dorothy01\Downloads\avast_free_antivirus_setup_online.exe
2015-02-19 21:20 - 2015-02-19 21:27 - 00000350 ____H () C:\WINDOWS\Tasks\avast! Emergency Update.job
2015-02-19 21:20 - 2015-02-19 21:20 - 00002281 _____ () C:\Users\Public\Desktop\Google Chrome.lnk
2015-02-19 21:20 - 2015-02-19 21:20 - 00000000 ____D () C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Google Chrome
2015-02-19 21:20 - 2015-02-19 21:20 - 00000000 ____D () C:\ProgramData\Google
2015-02-19 21:20 - 2015-02-19 21:20 - 00000000 ____D () C:\Program Files\Google
2015-02-19 21:18 - 2015-02-21 22:34 - 00000918 _____ () C:\WINDOWS\Tasks\GoogleUpdateTaskMachineCore.job
2015-02-19 21:18 - 2015-02-19 21:21 - 00000000 ____D () C:\Users\Dorothy01\AppData\Local\Google
2015-02-19 21:18 - 2015-02-19 21:20 - 00000000 ____D () C:\Program Files (x86)\Google
2015-02-19 21:17 - 2015-02-19 21:27 - 01050432 _____ (AVAST Software) C:\WINDOWS\system32\Drivers\aswsnx.sys
2015-02-19 21:17 - 2015-02-19 21:27 - 00083280 _____ (AVAST Software) C:\WINDOWS\system32\Drivers\aswmonflt.sys
2015-02-19 21:17 - 2015-02-19 21:17 - 00436624 _____ (AVAST Software) C:\WINDOWS\system32\Drivers\aswSP.sys
2015-02-19 21:17 - 2015-02-19 21:17 - 00267632 _____ () C:\WINDOWS\system32\Drivers\aswVmm.sys
2015-02-19 21:17 - 2015-02-19 21:17 - 00065776 _____ () C:\WINDOWS\system32\Drivers\aswRvrt.sys
2015-02-19 21:17 - 2015-02-19 21:17 - 00043152 _____ (AVAST Software) C:\WINDOWS\avastSS.scr
2015-02-19 21:17 - 2015-02-19 21:17 - 00029208 _____ () C:\WINDOWS\system32\Drivers\aswHwid.sys
2015-02-19 21:15 - 2015-02-19 21:15 - 00000000 ____D () C:\ProgramData\AVAST Software
2015-02-19 21:15 - 2015-02-19 21:15 - 00000000 ____D () C:\Program Files\AVAST Software
2015-02-19 21:13 - 2015-02-19 21:14 - 00000000 ____D () C:\Program Files (x86)\Mozilla Firefox
2015-02-19 21:10 - 2015-02-21 03:14 - 00000292 _____ () C:\HELP_DECRYPT.URL
2015-02-19 21:07 - 2015-02-19 21:07 - 00023552 _____ () C:\Users\Dorothy01\AppData\Local\pckunie.dll
2015-02-19 18:15 - 2015-02-19 18:15 - 00003180 _____ () C:\WINDOWS\SysWOW64\InstallUtil.InstallLog
2015-02-18 16:53 - 2015-02-19 21:49 - 00129752 _____ (Malwarebytes Corporation) C:\WINDOWS\system32\Drivers\MBAMSwissArmy.sys
2015-02-18 16:52 - 2015-02-18 16:52 - 00001120 _____ () C:\Users\Public\Desktop\Malwarebytes Anti-Malware.lnk
2015-02-18 16:52 - 2015-02-18 16:52 - 00000000 ____D () C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Malwarebytes Anti-Malware
2015-02-18 16:52 - 2015-02-18 16:52 - 00000000 ____D () C:\ProgramData\Malwarebytes
2015-02-18 16:52 - 2015-02-18 16:52 - 00000000 ____D () C:\Program Files (x86)\Malwarebytes Anti-Malware
2015-02-18 16:52 - 2014-11-21 06:14 - 00093400 _____ (Malwarebytes Corporation) C:\WINDOWS\system32\Drivers\mbamchameleon.sys
2015-02-18 16:52 - 2014-11-21 06:14 - 00064216 _____ (Malwarebytes Corporation) C:\WINDOWS\system32\Drivers\mwac.sys
2015-02-18 16:52 - 2014-11-21 06:14 - 00025816 _____ (Malwarebytes Corporation) C:\WINDOWS\system32\Drivers\mbam.sys
2015-02-18 16:48 - 2015-02-18 16:48 - 00000836 _____ () C:\Users\Public\Desktop\CCleaner.lnk
2015-02-18 16:48 - 2015-02-18 16:48 - 00000000 ____D () C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CCleaner
2015-02-18 16:48 - 2015-02-18 16:48 - 00000000 ____D () C:\Program Files\CCleaner
2015-02-18 16:39 - 2015-02-21 22:17 - 00000000 ____D () C:\WINDOWS\pss
2015-02-11 17:53 - 2015-02-11 17:53 - 00000000 ____D () C:\ProgramData\Microsoft\Windows\Start Menu\Programs\ZTE Handset USB Driver
2015-02-11 17:53 - 2015-02-11 17:53 - 00000000 ____D () C:\Program Files\ZTE_Handset_USB_Driver
2015-02-11 17:53 - 2013-09-11 16:27 - 00134976 _____ (ZTE Corporation) C:\WINDOWS\system32\Drivers\zghsser.sys
2015-02-11 17:53 - 2013-09-11 16:26 - 00175808 _____ (ZTE Corporation) C:\WINDOWS\system32\Drivers\zghsnet.sys
2015-02-11 17:53 - 2013-03-19 18:38 - 00821544 _____ () C:\WINDOWS\adb.exe
2015-02-11 17:53 - 2012-11-09 17:14 - 00062728 _____ (VIA Telecom) C:\WINDOWS\system32\Drivers\viahsser.sys
2015-02-11 17:53 - 2012-10-31 18:02 - 00032136 _____ (Via Telecom, Inc.) C:\WINDOWS\system32\Drivers\viahsets.sys
2015-02-11 17:53 - 2012-06-20 13:51 - 00020232 _____ (HandSet Incorporated) C:\WINDOWS\system32\Drivers\massfilter_hs.sys
2015-02-11 17:53 - 2012-06-08 16:56 - 01721576 _____ () C:\WINDOWS\system32\WdfCoInstaller01009.dll
2015-02-11 17:53 - 2012-06-08 16:56 - 01002728 _____ () C:\WINDOWS\system32\WinUSBCoInstaller2.dll
2015-02-11 17:53 - 2011-10-26 17:31 - 00067608 _____ (Google, inc) C:\WINDOWS\AdbWinUsbApi.dll
2015-02-11 17:53 - 2011-08-15 18:43 - 00102936 _____ (Google, inc) C:\WINDOWS\AdbWinApi.dll
2015-02-09 16:56 - 2015-02-09 16:56 - 00000000 ____H () C:\WINDOWS\system32\Drivers\Msft_User_WpdMtpDr_01_11_00.Wdf
2015-01-24 16:45 - 2015-02-19 07:41 - 00000000 ____D () C:\Users\Dorothy01\AppData\Local\{294523ef-b8b6-59cc-fe37-7cd365b2a599}
2015-01-22 10:52 - 2015-01-22 10:52 - 00003296 ____N () C:\bootsqm.dat
==================== One Month Modified Files and Folders =======
(If an entry is included in the fixlist, the file\folder will be moved.)
2015-02-21 22:38 - 2014-07-23 09:19 - 00003598 _____ () C:\WINDOWS\System32\Tasks\Optimize Start Menu Cache Files-S-1-5-21-1427692388-1042374531-2795145444-1001
2015-02-21 22:37 - 2014-09-24 01:15 - 00006428 _____ () C:\WINDOWS\system32\PerfStringBackup.INI
2015-02-21 22:33 - 2014-12-09 19:03 - 00000000 ___HD () C:\ProgramData\{F66CB4EE-546F-4D54-9332-216DE189AAB0}
2015-02-21 22:33 - 2014-10-14 09:44 - 00000000 ____D () C:\Users\Dorothy01
2015-02-21 22:31 - 2012-08-31 22:56 - 00000000 ____D () C:\ProgramData\Hewlett-Packard
2015-02-21 22:30 - 2013-08-22 09:36 - 00000000 ____D () C:\WINDOWS\system32\sru
2015-02-21 22:28 - 2013-08-22 08:45 - 00000006 ____H () C:\WINDOWS\Tasks\SA.DAT
2015-02-21 22:13 - 2014-10-23 11:14 - 04012982 _____ (NathanScott Apps) C:\Users\Dorothy01\Desktop\IDTool.exe
2015-02-21 19:37 - 2013-08-22 07:25 - 01048576 ___SH () C:\WINDOWS\system32\config\BBI
2015-02-21 03:31 - 2014-11-11 19:11 - 00000761 _____ () C:\WINDOWS\system32\Drivers\etc\hosts.txt
2015-02-21 03:14 - 2014-07-23 16:07 - 00000000 ____D () C:\StarmIRC v3.0
2015-02-21 03:14 - 2014-07-23 16:05 - 00000000 ____D () C:\StarPircH
2015-02-21 03:14 - 2012-08-01 21:15 - 00000000 ____D () C:\SWSETUP
2015-02-21 03:14 - 2012-08-01 03:57 - 00000000 _RSHD () C:\SYSTEM.SAV
2015-02-20 06:09 - 2014-07-23 16:00 - 00000000 ____D () C:\ProgramData\Oracle
2015-02-20 06:09 - 2014-07-23 15:56 - 00000000 ____D () C:\Program Files (x86)\Java
2015-02-20 06:07 - 2014-07-23 15:56 - 00272296 _____ (Oracle Corporation) C:\WINDOWS\SysWOW64\javaws.exe
2015-02-20 06:07 - 2014-07-23 15:56 - 00176552 _____ (Oracle Corporation) C:\WINDOWS\SysWOW64\javaw.exe
2015-02-20 06:07 - 2014-07-23 15:56 - 00176552 _____ (Oracle Corporation) C:\WINDOWS\SysWOW64\java.exe
2015-02-20 06:07 - 2014-07-23 15:56 - 00098216 _____ (Oracle Corporation) C:\WINDOWS\SysWOW64\WindowsAccessBridge-32.dll
2015-02-20 02:17 - 2014-10-14 10:30 - 00000000 ____D () C:\Windows.old
2015-02-19 23:30 - 2014-09-07 12:01 - 00000000 ____D () C:\Users\Public\CyberLink
2015-02-19 23:28 - 2014-11-14 15:44 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Adhoxi
2015-02-19 23:28 - 2014-07-23 15:49 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\unpacked23206
2015-02-19 23:28 - 2014-07-23 09:13 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Adobe
2015-02-19 23:28 - 2014-07-23 09:09 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Hewlett-Packard
2015-02-19 23:23 - 2014-11-10 16:42 - 00000000 ____D () C:\Users\Dorothy01\AppData\Local\Ovics
2015-02-19 23:21 - 2014-10-14 13:14 - 00000000 ____D () C:\Users\Dorothy01\AppData\Local\AMD
2015-02-19 23:21 - 2014-08-11 11:56 - 00000000 ____D () C:\Users\Dorothy01\AppData\Local\Apple Computer
2015-02-19 22:45 - 2014-11-26 18:24 - 00000000 ____D () C:\ProgramData\bamgaq
2015-02-19 22:11 - 2014-11-07 11:27 - 00000000 ____D () C:\Users\Dorothy01\AppData\Local\{30112b75-e574-a6db-560c-8103291a0838}
2015-02-19 21:07 - 2014-12-03 17:38 - 00000000 ____D () C:\ProgramData\PenulErhig
2015-02-19 07:40 - 2015-01-13 16:26 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Kuseyd
2015-02-19 07:40 - 2015-01-13 16:26 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Guhyanmo
2015-02-19 07:40 - 2015-01-06 13:58 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Veepme
2015-02-19 07:40 - 2015-01-05 20:36 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Kybeuv
2015-02-19 07:40 - 2015-01-05 15:02 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Wiudiz
2015-02-19 07:40 - 2015-01-02 12:19 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Tapyara
2015-02-19 07:40 - 2014-12-26 17:52 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Rifiewyn
2015-02-19 07:40 - 2014-12-25 17:44 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ynopqual
2015-02-19 07:40 - 2014-12-25 15:54 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ihywkead
2015-02-19 07:40 - 2014-12-25 15:43 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ekmiys
2015-02-19 07:40 - 2014-12-23 15:28 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Maypyz
2015-02-19 07:40 - 2014-12-22 15:27 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Fuwutee
2015-02-19 07:40 - 2014-12-22 14:56 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Fyarxy
2015-02-19 07:40 - 2014-12-21 15:20 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Zekubuab
2015-02-19 07:40 - 2014-12-15 16:15 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Wuwuec
2015-02-19 07:40 - 2014-12-14 15:11 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Byloaq
2015-02-19 07:40 - 2014-12-12 15:35 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Yhohybe
2015-02-19 07:40 - 2014-12-11 21:23 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Hovoote
2015-02-19 07:40 - 2014-12-11 16:09 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Amcyocut
2015-02-19 07:40 - 2014-12-11 09:47 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Itsefo
2015-02-19 07:40 - 2014-12-08 17:45 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Tumiexcu
2015-02-19 07:40 - 2014-12-08 16:37 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ziqeexew
2015-02-19 07:40 - 2014-12-04 15:16 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Mawywopo
2015-02-19 07:40 - 2014-12-03 17:42 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Icxeewhu
2015-02-19 07:40 - 2014-12-03 13:46 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ucucni
2015-02-19 07:40 - 2014-12-02 18:10 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Edutsoix
2015-02-19 07:40 - 2014-12-01 10:45 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ruyxku
2015-02-19 07:40 - 2014-12-01 10:45 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Huqokayx
2015-02-19 07:40 - 2014-12-01 10:42 - 00000000 ____D () C:\ProgramData\TifwIdyo
2015-02-19 07:40 - 2014-12-01 10:42 - 00000000 ____D () C:\ProgramData\BolsiWelug
2015-02-19 07:40 - 2014-11-28 08:56 - 00000000 ____D () C:\ProgramData\PeboZnoli
2015-02-19 07:40 - 2014-11-28 08:56 - 00000000 ____D () C:\ProgramData\CecuSefki
2015-02-19 07:40 - 2014-11-24 20:33 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Itufefv
2015-02-19 07:40 - 2014-11-24 20:28 - 00000000 ____D () C:\ProgramData\FapziGguzq
2015-02-19 07:40 - 2014-11-23 15:14 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Senyzayr
2015-02-19 07:40 - 2014-11-23 15:09 - 00000000 ____D () C:\ProgramData\QiktiWuffu
2015-02-19 07:40 - 2014-11-23 15:09 - 00000000 ____D () C:\ProgramData\FadyOdyu
2015-02-19 07:40 - 2014-11-23 08:58 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Zacosia
2015-02-19 07:40 - 2014-11-23 08:53 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ecqootfi
2015-02-19 07:40 - 2014-11-23 08:43 - 00000000 ____D () C:\ProgramData\TixoZuwu
2015-02-19 07:40 - 2014-11-20 15:57 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ymqiuky
2015-02-19 07:40 - 2014-11-20 15:57 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Qaedxa
2015-02-19 07:40 - 2014-11-20 15:54 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Hyipfy
2015-02-19 07:40 - 2014-11-20 15:49 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\FrameworkUpdate
2015-02-19 07:40 - 2014-11-20 15:49 - 00000000 ____D () C:\ProgramData\EiniHubex
2015-02-19 07:40 - 2014-11-19 16:07 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Woakduwa
2015-02-19 07:40 - 2014-11-19 16:07 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Obmukany
2015-02-19 07:40 - 2014-11-19 16:03 - 00000000 ____D () C:\ProgramData\GuxeXowi
2015-02-19 07:40 - 2014-11-18 15:30 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Gynika
2015-02-19 07:40 - 2014-11-18 15:30 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Egewtoi
2015-02-19 07:40 - 2014-11-18 15:26 - 00000000 ____D () C:\ProgramData\MokeVike
2015-02-19 07:40 - 2014-11-17 19:11 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Pevyliu
2015-02-19 07:40 - 2014-11-17 19:11 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ciokov
2015-02-19 07:40 - 2014-11-17 19:07 - 00000000 ____D () C:\ProgramData\MesmAyof
2015-02-19 07:40 - 2014-11-17 10:10 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ohvyev
2015-02-19 07:40 - 2014-11-17 10:10 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Esisgyl
2015-02-19 07:40 - 2014-11-17 10:05 - 00000000 ____D () C:\ProgramData\LuqePana
2015-02-19 07:40 - 2014-11-16 11:38 - 00000000 ____D () C:\ProgramData\YuctAren
2015-02-19 07:40 - 2014-11-16 11:38 - 00000000 ____D () C:\ProgramData\GiqyoCxuko
2015-02-19 07:40 - 2014-11-16 11:02 - 00000000 ____D () C:\ProgramData\JoheMsum
2015-02-19 07:40 - 2014-11-16 11:02 - 00000000 ____D () C:\ProgramData\JahebSuhvo
2015-02-19 07:40 - 2014-11-15 11:27 - 00000000 ____D () C:\ProgramData\HozbEzpud
2015-02-19 07:40 - 2014-11-15 11:27 - 00000000 ____D () C:\ProgramData\FasuTuhu
2015-02-19 07:40 - 2014-11-14 15:44 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ytbynede
2015-02-19 07:40 - 2014-11-14 15:40 - 00000000 ____D () C:\ProgramData\NeheQiri
2015-02-19 07:40 - 2014-11-14 15:40 - 00000000 ____D () C:\ProgramData\KaseJolmi
2015-02-19 07:40 - 2014-11-13 18:25 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ezrydu
2015-02-19 07:40 - 2014-11-13 18:21 - 00000000 ____D () C:\ProgramData\UardiNdeca
2015-02-19 07:40 - 2014-11-13 10:22 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Sequefb
2015-02-19 07:40 - 2014-11-13 10:22 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Onpyym
2015-02-19 07:40 - 2014-11-13 10:17 - 00000000 ____D () C:\ProgramData\UopiJowv
2015-02-19 07:40 - 2014-11-13 10:17 - 00000000 ____D () C:\ProgramData\DervUvon
2015-02-19 07:40 - 2014-11-12 17:45 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Ezupuhaf
2015-02-19 07:40 - 2014-11-12 17:40 - 00000000 ____D () C:\ProgramData\PokuGehos
2015-02-19 07:40 - 2014-11-12 17:40 - 00000000 ____D () C:\ProgramData\NerxElyo
2015-02-19 07:40 - 2014-11-11 20:48 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Upvukyy
2015-02-19 07:40 - 2014-11-11 20:47 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\Olaqduqo
2015-02-19 07:40 - 2014-11-11 20:42 - 00000000 ____D () C:\ProgramData\PapoSutul
2015-02-19 07:40 - 2014-11-11 20:42 - 00000000 ____D () C:\ProgramData\MoruYemq
2015-02-19 07:40 - 2014-11-11 18:14 - 00000000 ____D () C:\ProgramData\JufhEnusi
2015-02-19 07:40 - 2014-11-10 16:29 - 00000000 ____D () C:\Users\Dorothy01\AppData\Roaming\FrameworkUpdate7
2015-02-19 07:40 - 2014-11-10 16:29 - 00000000 ____D () C:\ProgramData\YansAjfir
2015-02-19 07:40 - 2014-11-10 16:29 - 00000000 ____D () C:\ProgramData\KitpUxijo
2015-02-19 07:40 - 2014-11-07 17:00 - 00000000 ____D () C:\Users\Dorothy01\AppData\Local\Ugmedia
2015-02-19 07:40 - 2014-11-07 16:59 - 00000000 ____D () C:\ProgramData\XiceNnar
2015-02-19 07:40 - 2014-11-07 16:59 - 00000000 ____D () C:\ProgramData\TobaFisa
2015-02-19 07:40 - 2014-10-02 15:49 - 00000000 ____D () C:\Users\Dorothy01\AppData\Local\tmp1461
2015-02-19 01:24 - 2014-10-14 10:31 - 00000000 ___DC () C:\WINDOWS\Panther
2015-02-19 01:18 - 2014-11-11 16:55 - 00000000 ____D () C:\WINDOWS\Minidump
2015-02-15 08:13 - 2013-08-22 07:25 - 00262144 ___SH () C:\WINDOWS\system32\config\ELAM
2015-02-01 20:32 - 2014-11-10 16:30 - 00000648 _____ () C:\ProgramData\@system.temp
2015-02-01 20:32 - 2014-11-10 16:30 - 00000384 ____H () C:\ProgramData\@system3.att
2015-02-01 15:57 - 2015-01-14 07:56 - 00020480 ___SH () C:\Users\Dorothy01\Desktop\Thumbs.db
==================== Files in the root of some directories =======
2014-11-13 18:51 - 2015-01-07 09:58 - 0000288 _____ () C:\Users\Dorothy01\AppData\Roaming\1B477081.reg
2014-11-21 18:59 - 2014-11-21 18:59 - 0022327 _____ () C:\Users\Dorothy01\AppData\Roaming\893686b8
2011-07-11 21:06 - 2011-07-11 21:06 - 0212304 _____ (Microsoft Corporation) C:\Users\Dorothy01\AppData\Roaming\BtvStack.dll
2015-01-05 14:15 - 2015-01-05 14:15 - 0015872 _____ () C:\Users\Dorothy01\AppData\Roaming\cowitches.d
2014-11-12 18:01 - 2014-11-12 18:01 - 0008542 _____ () C:\Users\Dorothy01\AppData\Roaming\DECRYPT_INSTRUCTION.HTML
2014-11-12 18:01 - 2014-11-12 18:01 - 0004214 _____ () C:\Users\Dorothy01\AppData\Roaming\DECRYPT_INSTRUCTION.TXT
2015-01-12 15:11 - 2015-01-12 15:11 - 0008562 _____ () C:\Users\Dorothy01\AppData\Roaming\HELP_DECRYPT.HTML
2015-01-12 15:11 - 2015-01-12 15:11 - 0001270 _____ () C:\Users\Dorothy01\AppData\Roaming\HELP_DECRYPT.PNG
2015-01-12 15:11 - 2015-01-12 15:11 - 0004224 _____ () C:\Users\Dorothy01\AppData\Roaming\HELP_DECRYPT.TXT
2014-11-13 18:51 - 2015-01-07 09:58 - 0009728 _____ () C:\Users\Dorothy01\AppData\Roaming\mcp.ico
2014-07-23 15:49 - 2014-07-23 15:49 - 0000043 _____ () C:\Users\Dorothy01\AppData\Roaming\WB.CFG
2014-11-10 16:30 - 2014-11-10 16:30 - 0000448 ____H () C:\Users\Dorothy01\AppData\Roaming\麽鎒駓覜
2014-11-21 18:59 - 2014-11-21 18:59 - 0037439 _____ () C:\Users\Dorothy01\AppData\Local\893686b8
2014-11-12 18:01 - 2014-11-12 18:01 - 0008542 _____ () C:\Users\Dorothy01\AppData\Local\DECRYPT_INSTRUCTION.HTML
2014-11-12 18:01 - 2014-11-12 18:01 - 0004214 _____ () C:\Users\Dorothy01\AppData\Local\DECRYPT_INSTRUCTION.TXT
2014-12-11 09:44 - 2014-12-11 21:24 - 0929536 _____ () C:\Users\Dorothy01\AppData\Local\f5e83w4ef.dat
2015-01-12 15:10 - 2015-01-12 15:10 - 0008562 _____ () C:\Users\Dorothy01\AppData\Local\HELP_DECRYPT.HTML
2015-01-12 15:10 - 2015-01-12 15:10 - 0001270 _____ () C:\Users\Dorothy01\AppData\Local\HELP_DECRYPT.PNG
2015-01-12 15:10 - 2015-01-12 15:10 - 0004224 _____ () C:\Users\Dorothy01\AppData\Local\HELP_DECRYPT.TXT
2015-02-19 21:07 - 2015-02-19 21:07 - 0023552 _____ () C:\Users\Dorothy01\AppData\Local\pckunie.dll
2015-02-21 03:30 - 2015-02-21 03:30 - 0023552 _____ () C:\Users\Dorothy01\AppData\Local\pgkunge.dll
2014-11-21 18:59 - 2014-11-21 18:59 - 0026477 _____ () C:\ProgramData\893686b8
2014-11-10 16:30 - 2015-02-01 20:32 - 0000648 _____ () C:\ProgramData\@system.temp
2014-11-10 16:30 - 2015-02-01 20:32 - 0000384 ____H () C:\ProgramData\@system3.att
2015-01-12 15:09 - 2015-01-12 15:09 - 0008562 _____ () C:\ProgramData\HELP_DECRYPT.HTML
2015-01-12 15:09 - 2015-01-12 15:09 - 0001270 _____ () C:\ProgramData\HELP_DECRYPT.PNG
2015-01-12 15:09 - 2015-01-12 15:09 - 0004224 _____ () C:\ProgramData\HELP_DECRYPT.TXT
2012-09-01 00:08 - 2012-09-01 00:08 - 0000141 _____ () C:\ProgramData\Microsoft.SqlServer.Compact.351.64.bc
Files to move or delete:
====================
C:\Users\Dorothy01\AppData\Local\Temp\getmhost.exe
Some content of TEMP:
====================
C:\Users\Dorothy01\AppData\Local\Temp\ARS.exe
C:\Users\Dorothy01\AppData\Local\Temp\dllnt_dump.dll
C:\Users\Dorothy01\AppData\Local\Temp\getmhost.exe
C:\Users\Dorothy01\AppData\Local\Temp\ivbhim.exe
C:\Users\Dorothy01\AppData\Local\Temp\jre-8u31-windows-au.exe
C:\Users\Dorothy01\AppData\Local\Temp\Quarantine.exe
C:\Users\Dorothy01\AppData\Local\Temp\sqlite3.dll
C:\Users\Dorothy01\AppData\Local\Temp\tmp7A9C.tmp.exe
==================== Bamital & volsnap Check =================
(There is no automatic fix for files that do not pass verification.)
C:\Windows\System32\winlogon.exe => File is digitally signed
C:\Windows\System32\wininit.exe => File is digitally signed
C:\Windows\explorer.exe => File is digitally signed
C:\Windows\SysWOW64\explorer.exe => File is digitally signed
C:\Windows\System32\svchost.exe => File is digitally signed
C:\Windows\SysWOW64\svchost.exe => File is digitally signed
C:\Windows\System32\services.exe => File is digitally signed
C:\Windows\System32\User32.dll => File is digitally signed
C:\Windows\SysWOW64\User32.dll => File is digitally signed
C:\Windows\System32\userinit.exe => File is digitally signed
C:\Windows\SysWOW64\userinit.exe => File is digitally signed
C:\Windows\System32\rpcss.dll => File is digitally signed
C:\Windows\System32\Drivers\volsnap.sys => File is digitally signed
LastRegBack: 2014-10-14 09:32
==================== End Of Log ============================
ADDITIONAL SCAN
Additional scan result of Farbar Recovery Scan Tool (x64) Version: 21-02-2015
Ran by Dorothy01 at 2015-02-21 22:42:35
Running from C:\Users\Dorothy01\Desktop
Boot Mode: Normal
==========================================================
==================== Security Center ========================
(If an entry is included in the fixlist, it will be removed.)
AV: Norton Internet Security (Disabled - Up to date) {53C7D717-52E2-B95E-FA61-6F32ECC805DB}
AV: Windows Defender (Disabled - Up to date) {D68DDC3A-831F-4fae-9E44-DA132C1ACF46}
AS: Windows Defender (Disabled - Up to date) {D68DDC3A-831F-4fae-9E44-DA132C1ACF46}
AS: Norton Internet Security (Disabled - Up to date) {E8A636F3-74D8-B6D0-C0D1-5440974F4F66}
FW: Norton Internet Security (Disabled) {6BFC5632-188D-B806-D13E-C607121B42A0}
==================== Installed Programs ======================
(Only the adware programs with "hidden" flag could be added to the fixlist to unhide them. The adware programs should be uninstalled manually.)
4 Elements II (x32 Version: 2.2.0.98 - WildTangent) Hidden
AMD Catalyst Install Manager (HKLM\...\{5F769CF4-5263-4C7B-AEB2-C06A73AE4428}) (Version: 8.0.881.0 - Advanced Micro Devices, Inc.)
Apple Application Support (HKLM-x32\...\{78002155-F025-4070-85B3-7C0453561701}) (Version: 3.0.6 - Apple Inc.)
Apple Mobile Device Support (HKLM\...\{6AF2AC2A-3532-43FD-9F4D-BDC9C0D724C7}) (Version: 7.1.2.6 - Apple Inc.)
Apple Software Update (HKLM-x32\...\{789A5B64-9DD9-4BA5-915A-F0FC0A1B7BFE}) (Version: 2.1.3.127 - Apple Inc.)
Avast Free Antivirus (HKLM-x32\...\Avast) (Version: 10.0.2208 - AVAST Software)
Bejeweled 3 (x32 Version: 2.2.0.98 - WildTangent) Hidden
Bonjour (HKLM\...\{6E3610B2-430D-4EB0-81E3-2B57E8B9DE8D}) (Version: 3.0.0.10 - Apple Inc.)
Build-a-lot 4 - Power Source (x32 Version: 2.2.0.98 - WildTangent) Hidden
Catalyst Control Center (HKLM-x32\...\WUCCCApp) (Version: 1.00.0000 - AMD)
CCleaner (HKLM\...\CCleaner) (Version: 5.02 - Piriform)
Chuzzle Deluxe (x32 Version: 2.2.0.95 - WildTangent) Hidden
Cradle Of Egypt Collector's Edition (x32 Version: 2.2.0.98 - WildTangent) Hidden
Cradle of Rome 2 (x32 Version: 2.2.0.98 - WildTangent) Hidden
CyberLink LabelPrint (HKLM-x32\...\InstallShield_{C59C179C-668D-49A9-B6EA-0121CCFC1243}) (Version: 2.5.1.5510 - CyberLink Corp.)
CyberLink Media Suite 10 (HKLM-x32\...\InstallShield_{1FBF6C24-C1fD-4101-A42B-0C564F9E8E79}) (Version: 10.0.1.1916 - CyberLink Corp.)
CyberLink PhotoDirector (HKLM-x32\...\InstallShield_{4862344A-A39C-4897-ACD4-A1BED5163C5A}) (Version: 2.0.1.3109 - CyberLink Corp.)
CyberLink Power2Go 8 (HKLM-x32\...\InstallShield_{2A87D48D-3FDF-41fd-97CD-A1E370EFFFE2}) (Version: 8.0.1.1902 - CyberLink Corp.)
CyberLink PowerDirector 10 (HKLM-x32\...\InstallShield_{B0B4F6D2-F2AE-451A-9496-6F2F6A897B32}) (Version: 10.0.1.1925 - CyberLink Corp.)
CyberLink PowerDVD (HKLM-x32\...\InstallShield_{DEC235ED-58A4-4517-A278-C41E8DAEAB3B}) (Version: 10.0.1.4407 - CyberLink Corp.)
CyberLink YouCam (HKLM-x32\...\InstallShield_{01FB4998-33C4-4431-85ED-079E3EEFE75D}) (Version: 3.5.4.5527 - CyberLink Corp.)
D3DX10 (x32 Version: 15.4.2368.0902 - Microsoft) Hidden
Energy Star (HKLM\...\{0FA995CC-C849-4755-B14B-5404CC75DC24}) (Version: 1.0.8 - Hewlett-Packard)
Farm Frenzy (x32 Version: 2.2.0.98 - WildTangent) Hidden
FATE: The Cursed King (x32 Version: 2.2.0.97 - WildTangent) Hidden
Final Drive Fury (x32 Version: 2.2.0.95 - WildTangent) Hidden
FlatOut 2 (x32 Version: 2.2.0.98 - WildTangent) Hidden
Google Chrome (HKLM-x32\...\Google Chrome) (Version: 40.0.2214.115 - Google Inc.)
Google Toolbar for Internet Explorer (HKLM-x32\...\{2318C2B1-4965-11d4-9B18-009027A5CD4F}) (Version: 7.5.5111.1712 - Google Inc.)
Google Update Helper (x32 Version: 1.3.21.169 - Google Inc.) Hidden
Google Update Helper (x32 Version: 1.3.26.9 - Google Inc.) Hidden
Governor of Poker 2 Premium Edition (x32 Version: 2.2.0.95 - WildTangent) Hidden
Hewlett-Packard ACLM.NET v1.2.0.0 (x32 Version: 1.00.0000 - Hewlett-Packard Company) Hidden
Hoyle Card Games (x32 Version: 2.2.0.95 - WildTangent) Hidden
HP Connected Music (Meridian - installer) (HKLM-x32\...\StartHPConnectedMusic) (Version: v1.0 - Meridian Audio Ltd)
HP Connected Remote (HKLM-x32\...\{F243A34B-AB7F-4065-B770-B85B767C247C}) (Version: 1.0.1202 - Hewlett-Packard)
HP Games (HKLM-x32\...\WildTangent hp Master Uninstall) (Version: 1.0.3.0 - WildTangent)
HP MyRoom (HKLM-x32\...\{9C35EDE5-4B0F-45E7-A438-314BA889948E}) (Version: 9.0.0.0 - Hewlett-Packard Company)
HP Registration Service (HKLM\...\{E4D6CCF2-0AAF-4B9C-9DE5-893EDC9B4BAA}) (Version: 1.0.5976.4186 - Hewlett-Packard)
HP Support Assistant (HKLM-x32\...\{FF27F674-821E-4BA2-985B-DDF539C2CD03}) (Version: 7.0.33.6 - Hewlett-Packard Company)
HP Support Information (HKLM-x32\...\{B2B7B1C8-7C8B-476C-BE2C-049731C55992}) (Version: 12.00.0000 - Hewlett-Packard)
iscsicli (HKLM\...\{f48a0c57-7c48-461c-9957-ab255ddc986e}.sdb) (Version: - )
iTunes (HKLM\...\{77DE5105-D05E-448C-96CB-7FA381903753}) (Version: 11.3.1.2 - Apple Inc.)
Java 8 Update 31 (HKLM-x32\...\{26A24AE4-039D-4CA4-87B4-2F83218031F0}) (Version: 8.0.310 - Oracle Corporation)
Jewel Match 3 (x32 Version: 2.2.0.98 - WildTangent) Hidden
John Deere Drive Green (x32 Version: 2.2.0.95 - WildTangent) Hidden
Luxor Evolved (x32 Version: 2.2.0.98 - WildTangent) Hidden
Mahjongg Dimensions Deluxe: Tiles in Time (x32 Version: 2.2.0.98 - WildTangent) Hidden
Malwarebytes Anti-Malware version 2.0.4.1028 (HKLM-x32\...\Malwarebytes Anti-Malware_is1) (Version: 2.0.4.1028 - Malwarebytes Corporation)
Microsoft Office (HKLM-x32\...\{95140000-0070-0000-0000-0000000FF1CE}) (Version: 14.0.6120.5004 - Microsoft Corporation)
Microsoft SQL Server 2005 Compact Edition [ENU] (HKLM-x32\...\{F0B430D1-B6AA-473D-9B06-AA3DD01FD0B8}) (Version: 3.1.0000 - Microsoft Corporation)
Microsoft Visual C++ 2005 Redistributable (HKLM-x32\...\{710f4c1c-cc18-4c49-8cbf-51240c89a1a2}) (Version: 8.0.61001 - Microsoft Corporation)
Microsoft Visual C++ 2005 Redistributable (HKLM-x32\...\{837b34e3-7c30-493c-8f6a-2b0f04e2912c}) (Version: 8.0.59193 - Microsoft Corporation)
Microsoft Visual C++ 2008 Redistributable - x64 9.0.30729.4148 (HKLM\...\{4B6C7001-C7D6-3710-913E-5BC23FCE91E6}) (Version: 9.0.30729.4148 - Microsoft Corporation)
Microsoft Visual C++ 2008 Redistributable - x86 9.0.30729.17 (HKLM-x32\...\{9A25302D-30C0-39D9-BD6F-21E6EC160475}) (Version: 9.0.30729 - Microsoft Corporation)
Microsoft Visual C++ 2008 Redistributable - x86 9.0.30729.4148 (HKLM-x32\...\{1F1C2DFC-2D24-3E06-BCB8-725134ADF989}) (Version: 9.0.30729.4148 - Microsoft Corporation)
Microsoft Visual C++ 2010 x64 Redistributable - 10.0.40219 (HKLM\...\{1D8E6291-B0D5-35EC-8441-6616F567A0F7}) (Version: 10.0.40219 - Microsoft Corporation)
Microsoft Visual C++ 2010 x86 Redistributable - 10.0.40219 (HKLM-x32\...\{F0C3E5D1-1ADE-321E-8167-68EF0DE699A5}) (Version: 10.0.40219 - Microsoft Corporation)
Microsoft Visual C++ 2012 Redistributable (x64) - 11.0.50727 (HKLM-x32\...\{15134cb0-b767-4960-a911-f2d16ae54797}) (Version: 11.0.50727.1 - Microsoft Corporation)
Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.50727 (HKLM-x32\...\{22154f09-719a-4619-bb71-5b3356999fbf}) (Version: 11.0.50727.1 - Microsoft Corporation)
Mortimer Beckett and the Crimson Thief Premium Edition (x32 Version: 2.2.0.98 - WildTangent) Hidden
Mystery P.I. - Curious Case of Counterfeit Cove (x32 Version: 2.2.0.98 - WildTangent) Hidden
Norton Internet Security (HKLM-x32\...\NIS) (Version: 20.6.0.27 - Symantec Corporation)
Peggle Nights (x32 Version: 2.2.0.98 - WildTangent) Hidden
Penguins! (x32 Version: 2.2.0.98 - WildTangent) Hidden
Polar Bowler (x32 Version: 2.2.0.97 - WildTangent) Hidden
Polar Golfer (x32 Version: 2.2.0.98 - WildTangent) Hidden
Ralink RT5390R 802.11bgn Wi-Fi Adapter (HKLM-x32\...\{8FC4F1DD-F7FD-4766-804D-3C8FF1D309AF}) (Version: 5.0.0.0 - Ralink)
Realtek High Definition Audio Driver (HKLM-x32\...\{F132AF7F-7BCA-4EDE-8A7C-958108FE7DBC}) (Version: 6.0.1.6675 - Realtek Semiconductor Corp.)
Realtek PCIE Card Reader (HKLM-x32\...\{C1594429-8296-4652-BF54-9DBE4932A44C}) (Version: 6.2.8400.28123 - Realtek Semiconductor Corp.)
Recovery Manager (x32 Version: 5.5.0.5530 - CyberLink Corp.) Hidden
Roads of Rome 3 (x32 Version: 2.2.0.98 - WildTangent) Hidden
StarmIRC 3.0 (HKLM-x32\...\StarmIRC 3.0) (Version: - )
StarPircH v3.0 (HKLM-x32\...\StarPircH v3.0) (Version: - )
Tales of Lagoona (x32 Version: 2.2.0.110 - WildTangent) Hidden
Update Installer for WildTangent Games App (x32 Version: - WildTangent) Hidden
Vacation Quest™ - Australia (x32 Version: 2.2.0.98 - WildTangent) Hidden
WildTangent Games (HKLM-x32\...\WildTangent wildgames Master Uninstall) (Version: 1.0.3.0 - WildTangent)
WildTangent Games App (x32 Version: 4.0.9.6 - WildTangent) Hidden
Windows Live Essentials (HKLM-x32\...\WinLiveSuite) (Version: 15.4.3555.0308 - Microsoft Corporation)
ZTE Handset USB Driver (HKLM\...\{01D42BF0-ED08-463f-8A28-99EB6FEE962B}) (Version: - ZTE Corporation)
ZTE Handset USB Driver (HKLM\...\{D2D77DC2-8299-11D1-8949-444553540000}_is1) (Version: 5.2104.1.01B01 - ZTE Corporation)
Zuma's Revenge (x32 Version: 2.2.0.98 - WildTangent) Hidden
==================== Custom CLSID (selected items): ==========================
(If an entry is included in the fixlist, it will be removed from registry. Any eventual file will not be moved.)
CustomCLSID: HKU\S-1-5-21-1427692388-1042374531-2795145444-1001_Classes\CLSID\{AB8902B4-09CA-4bb6-B78D-A8F59079A8D5}\localserver32 -> rundll32.exe javascript:"\..\mshtml.dll,RunHTMLApplication ";eval("epdvnfou/xsjuf)(=tdsjqu!mbohvbhf> (the data entry has 251 more characters). <==== Poweliks?
==================== Restore Points =========================
==================== Hosts content: ==========================
(If needed Hosts: directive could be included in the fixlist to reset Hosts.)
2013-08-22 07:25 - 2015-02-21 03:31 - 00001509 _RASH C:\WINDOWS\system32\Drivers\etc\hosts
127.0.0.1 localhost
195.162.68.59 www.google-analytics.com.
195.162.68.59 google-analytics.com.
195.162.68.59 connect.facebook.net.
162.247.13.54 www.google-analytics.com.
162.247.13.54 google-analytics.com.
162.247.13.54 connect.facebook.net.
195.162.69.252 www.google-analytics.com.
195.162.69.252 google-analytics.com.
195.162.69.252 connect.facebook.net.
==================== Scheduled Tasks (whitelisted) =============
(If an entry is included in the fixlist, it will be removed from registry. Any associated file could be listed separately to be moved.)
Task: {0AF68A16-8BB9-4884-9B4E-15D4F360BB7B} - System32\Tasks\Security Center Update - 2036164130 => C:\Users\Dorothy01\AppData\Roaming\Yhohybe\odhie.exe <==== ATTENTION
Task: {0C23B36F-F62C-434F-AA02-5ADBADF1858B} - System32\Tasks\Security Center Update - 2231539794 => C:\Users\Dorothy01\AppData\Roaming\Qaedxa\uwywweo.exe <==== ATTENTION
Task: {10DBF29F-9C03-4CB6-9169-375E42E32964} - System32\Tasks\Norton WSC Integration => C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\WSCStub.exe [2014-12-06] (Symantec Corporation)
Task: {11313470-E7D3-43C8-A7F7-5F76D072D93D} - System32\Tasks\Norton Internet Security\Norton Error Processor => C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\SymErr.exe [2013-06-03] (Symantec Corporation)
Task: {14653784-6568-4765-B81E-19CEB2C29EEF} - System32\Tasks\Security Center Update - 304447838 => C:\Users\Dorothy01\AppData\Roaming\Fyarxy\odrakal.exe <==== ATTENTION
Task: {14B872C9-ED54-4ACC-A2E9-1A45CAD02CCE} - System32\Tasks\MirageAgent => C:\Program Files (x86)\CyberLink\YouCam\YCMMirage.exe [2012-07-27] (CyberLink)
Task: {1DE689D1-D5D6-4E99-9906-A33502FF48FF} - System32\Tasks\Security Center Update - 3156874879 => C:\Users\Dorothy01\AppData\Roaming\Ziqeexew\peisomr.exe <==== ATTENTION
Task: {29FD53A0-B0E0-4AC5-A535-A77BDBAB7300} - System32\Tasks\Security Center Update - 1511213846 => C:\Users\Dorothy01\AppData\Roaming\Ynopqual\epeht.exe <==== ATTENTION
Task: {348D35BE-0530-4438-9C00-FA4E457087F1} - System32\Tasks\GoogleUpdateTaskMachineUA => C:\Program Files (x86)\Google\Update\GoogleUpdate.exe [2015-02-19] (Google Inc.)
Task: {34D40EAE-6659-4B8C-8F0E-5D9D8F76EE87} - System32\Tasks\Security Center Update - 3665910781 => C:\Users\Dorothy01\AppData\Roaming\Ekmiys\edanuzh.exe <==== ATTENTION
Task: {38AD3EE9-89B1-4FE8-BD3A-C268041E30AB} - System32\Tasks\Security Center Update - 3379427597 => C:\Users\Dorothy01\AppData\Roaming\Obmukany\otipky.exe <==== ATTENTION
Task: {45D84C00-2A3B-4698-945A-BD5F046DE8C1} - System32\Tasks\Hewlett-Packard\HP Support Assistant\PC Health Analysis => C:\Program Files (x86)\Hewlett-Packard\HP Support Framework\HPSF.exe [2012-08-15] (Hewlett-Packard Company)
Task: {46591690-E2C7-4AB5-90B8-0807BF83FA2E} - System32\Tasks\Security Center Update - 1219234967 => C:\Users\Dorothy01\AppData\Roaming\Hovoote\viywyke.exe <==== ATTENTION
Task: {4FE7F4B5-6216-4BF5-B69B-AE6DCAB85ACC} - System32\Tasks\Security Center Update - 951185298 => C:\Users\Dorothy01\AppData\Roaming\Tumiexcu\esinwii.exe <==== ATTENTION
Task: {506490F7-3376-4EFC-A901-586AA3303B44} - System32\Tasks\Security Center Update - 2325803103 => C:\Users\Dorothy01\AppData\Roaming\Adhoxi\vywipir.exe <==== ATTENTION
Task: {516E887F-D9AA-43E6-A51E-2905BC435DC3} - System32\Tasks\Security Center Update - 1528112639 => C:\Users\Dorothy01\AppData\Roaming\Kuseyd\ihnoxa.exe <==== ATTENTION
Task: {58DBAADD-4BFC-48F9-A19E-02A3DBE8DB7A} - System32\Tasks\Security Center Update - 2901739987 => C:\Users\Dorothy01\AppData\Roaming\Icxeewhu\avazx.exe <==== ATTENTION
Task: {62015E40-868F-450C-BB00-4F2987356F87} - System32\Tasks\Security Center Update - 3903236305 => C:\Users\Dorothy01\AppData\Roaming\Itufefv\qusieny.exe <==== ATTENTION
Task: {636CB7B6-8835-4A64-A923-ED55EB0D8640} - System32\Tasks\Security Center Update - 2512843633 => C:\Users\Dorothy01\AppData\Roaming\Ohvyev\yketpyu.exe <==== ATTENTION
Task: {6378A9C8-1406-4725-9242-44BFD048B5CE} - System32\Tasks\Security Center Update - 331106455 => C:\Users\Dorothy01\AppData\Roaming\Ymqiuky\mipiims.exe <==== ATTENTION
Task: {639A2A23-A522-40F7-AD5D-9F1245DF1A82} - System32\Tasks\Security Center Update - 2487970780 => C:\Users\Dorothy01\AppData\Roaming\Pevyliu\adelre.exe <==== ATTENTION
Task: {6BB0DD4F-FC46-49AF-B590-4F9F44C7E1A7} - System32\Tasks\rspahma => C:\Users\DOROTH~1\AppData\Local\Temp\utyczdi.exe <==== ATTENTION
Task: {70C6EC5A-CD9A-41DE-8073-EBF9E70D4E54} - System32\Tasks\Security Center Update - 3838766864 => C:\Users\Dorothy01\AppData\Roaming\Ezrydu\xyelefq.exe <==== ATTENTION
Task: {72165FBF-954D-4040-B5B5-BC5F9EED3A0E} - System32\Tasks\Security Center Update - 3216473386 => C:\Users\Dorothy01\AppData\Roaming\Zacosia\geulby.exe <==== ATTENTION
Task: {7430F638-B12A-445A-BBEF-5E8F514DF753} - System32\Tasks\Security Center Update - 699896687 => C:\Users\Dorothy01\AppData\Roaming\Itsefo\zyyzpii.exe <==== ATTENTION
Task: {7444E2A1-12CB-40A5-B56A-3E21543B4514} - System32\Tasks\Security Center Update - 3204526539 => C:\Users\Dorothy01\AppData\Roaming\Huqokayx\cazol.exe <==== ATTENTION
Task: {797B7B84-6E57-4129-A6A9-7A7099782A48} - System32\Tasks\Security Center Update - 242654636 => C:\Users\Dorothy01\AppData\Roaming\Maypyz\acoxv.exe <==== ATTENTION
Task: {7BB4C936-AFE9-405B-8288-876487348757} - System32\Tasks\Security Center Update - 116467704 => C:\Users\Dorothy01\AppData\Roaming\Zekubuab\usloe.exe <==== ATTENTION
Task: {7E32FCE3-C859-49A2-8E75-598B56230006} - System32\Tasks\Security Center Update - 4028262528 => C:\Users\Dorothy01\AppData\Roaming\Byloaq\uzodzay.exe <==== ATTENTION
Task: {833517E7-60C9-4EBA-B5E2-E1A24D86CE1A} - System32\Tasks\Security Center Update - 2519066445 => C:\Users\Dorothy01\AppData\Roaming\Ruyxku\vyfyr.exe <==== ATTENTION
Task: {86BAB3C1-BEB4-4F5B-9723-D319FC15EB44} - System32\Tasks\Security Center Update - 1810362612 => C:\Users\Dorothy01\AppData\Roaming\Senyzayr\ynval.exe <==== ATTENTION
Task: {86C013A6-B536-4DF0-BEDC-656D87A1D6D5} - System32\Tasks\Hewlett-Packard\HP Support Assistant\Update Check => C:\ProgramData\Hewlett-Packard\HP Support Framework\Resources\Updater7\HPSFUpdater.exe [2012-08-07] (Hewlett-Packard Company)
Task: {8A4EFB2F-EFF1-4B4C-A1E0-641064B8C832} - System32\Tasks\Security Center Update - 3747167081 => C:\Users\Dorothy01\AppData\Roaming\Kybeuv\zywefu.exe <==== ATTENTION
Task: {91474FF9-C8FF-4F7E-B671-C5BAA856571C} - System32\Tasks\Security Center Update - 513270047 => C:\Users\Dorothy01\AppData\Roaming\Veepme\mearabi.exe <==== ATTENTION
Task: {9A50C6A9-6D3C-4A7F-B237-D2E34D535BAF} - System32\Tasks\Security Center Update - 4149247359 => C:\Users\Dorothy01\AppData\Roaming\Tapyara\ehubzy.exe <==== ATTENTION
Task: {9BD8C08F-7F0B-430E-AD7D-12988F4D4D76} - System32\Tasks\Security Center Update - 1179286971 => C:\Users\Dorothy01\AppData\Roaming\Ciokov\ekypu.exe <==== ATTENTION
Task: {9CD254AC-60CC-41FE-B8C7-884BAC0FA4A3} - System32\Tasks\Security Center Update - 1285267939 => C:\Users\Dorothy01\AppData\Roaming\Ytbynede\ebusfe.exe <==== ATTENTION
Task: {9DB27102-BD01-4DBA-AA72-192BAC09BFE7} - System32\Tasks\Security Center Update - 3201999599 => C:\Users\Dorothy01\AppData\Roaming\Ihywkead\olypozo.exe <==== ATTENTION
Task: {A24B621A-54AB-4FAF-9C35-FB0D87321DD4} - System32\Tasks\Security Center Update - 1259602875 => C:\Users\Dorothy01\AppData\Roaming\Egewtoi\kumysio.exe <==== ATTENTION
Task: {A31D10D4-B4CF-4475-B02B-0A9BEB4E6617} - System32\Tasks\Security Center Update - 2329648882 => C:\Users\Dorothy01\AppData\Roaming\Ecqootfi\inecimy.exe <==== ATTENTION
Task: {A3FB09EC-C469-45ED-8A04-7E9497A4358B} - System32\Tasks\Security Center Update - 532629427 => C:\Users\Dorothy01\AppData\Roaming\Mawywopo\yhrog.exe <==== ATTENTION
Task: {A589DDED-A1E5-4832-A451-604AADF76C94} - System32\Tasks\Norton Internet Security\Norton Error Analyzer => C:\Program Files (x86)\Norton Internet Security\Engine\20.6.0.27\SymErr.exe [2013-06-03] (Symantec Corporation)
Task: {ACE571AA-4750-4BA4-9AB7-285B651F13E4} - System32\Tasks\Security Center Update - 578871115 => C:\Users\Dorothy01\AppData\Roaming\Wiudiz\areta.exe <==== ATTENTION
Task: {B1AE1850-9814-4733-A837-1BCFDCA93C2F} - System32\Tasks\Security Center Update - 1433702555 => C:\Users\Dorothy01\AppData\Roaming\Olaqduqo\oxico.exe <==== ATTENTION
Task: {B2111A5C-17C6-42AC-8232-C4BFBD5CEAE2} - System32\Tasks\Security Center Update - 2786531556 => C:\Users\Dorothy01\AppData\Roaming\Guhyanmo\usukrau.exe <==== ATTENTION
Task: {B31AB263-6E64-4AE6-9131-F03F3EB11C96} - System32\Tasks\Security Center Update - 2649167008 => C:\Users\Dorothy01\AppData\Roaming\Amcyocut\seovado.exe <==== ATTENTION
Task: {B69D26CC-F736-43EF-8678-4047B1182B5E} - System32\Tasks\Security Center Update - 4109173847 => C:\Users\Dorothy01\AppData\Roaming\Ezupuhaf\ziexepo.exe <==== ATTENTION
Task: {BA2069FF-78E4-45BC-B55E-CD0ACD43F066} - System32\Tasks\Security Center Update - 2002689914 => C:\Users\Dorothy01\AppData\Roaming\Hyipfy\eheqqu.exe <==== ATTENTION
Task: {BB68D13D-D1D6-492F-8D8C-218D8F32F366} - System32\Tasks\Security Center Update - 3566967998 => C:\Users\Dorothy01\AppData\Roaming\Sequefb\apxuyb.exe <==== ATTENTION
Task: {C0214B00-381D-48C6-8657-2096534B77ED} - System32\Tasks\Security Center Update - 2047020247 => C:\Users\Dorothy01\AppData\Roaming\Woakduwa\vyvefiy.exe <==== ATTENTION
Task: {C8F0BD03-484C-4EA4-B730-E73FCF57C579} - System32\Tasks\Security Center Update - 1058146964 => C:\Users\Dorothy01\AppData\Roaming\Esisgyl\hupoto.exe <==== ATTENTION
Task: {CCE07978-A743-41CE-84CE-1E73B09468DB} - System32\Tasks\Security Center Update - 4056442320 => C:\Users\Dorothy01\AppData\Roaming\Ucucni\qyhyg.exe <==== ATTENTION
Task: {D042FFB9-18A6-451E-A0B3-D8F8FDB41F2E} - System32\Tasks\Apple\AppleSoftwareUpdate => C:\Program Files (x86)\Apple Software Update\SoftwareUpdate.exe [2011-06-01] (Apple Inc.)
Task: {D272D6E1-FF48-4D29-8FED-3859A8299DC8} - System32\Tasks\Security Center Update - 446489216 => C:\Users\Dorothy01\AppData\Roaming\Gynika\daboop.exe <==== ATTENTION
Task: {D7DFAC78-DC9A-420F-9905-9654F37432EC} - System32\Tasks\GoogleUpdateTaskMachineCore => C:\Program Files (x86)\Google\Update\GoogleUpdate.exe [2015-02-19] (Google Inc.)
Task: {D8A8741F-AFA1-45BC-8531-65E4136E8CD5} - System32\Tasks\Hewlett-Packard\HP Support Assistant\HP Support Assistant Quick Start => C:\Program Files (x86)\Hewlett-Packard\HP Support Framework\HPSF.exe [2012-08-15] (Hewlett-Packard Company)
Task: {DAF472B5-87C9-4EB7-BD1F-23897D28E7CF} - System32\Tasks\Security Center Update - 4131681425 => C:\Users\Dorothy01\AppData\Roaming\Upvukyy\qikoiqp.exe <==== ATTENTION
Task: {DD416C59-DA11-4673-95DF-6CCB71853F43} - System32\Tasks\Security Center Update - 2300971329 => C:\Users\Dorothy01\AppData\Roaming\Fuwutee\kikiap.exe <==== ATTENTION
Task: {F0BDD635-04A8-43FD-B541-D9182F90415D} - System32\Tasks\Security Center Update - 4105554909 => C:\Users\Dorothy01\AppData\Roaming\Wuwuec\xeabac.exe <==== ATTENTION
Task: {F70673BE-9DA6-4FE7-93FB-32DE754FBB81} - System32\Tasks\Microsoft\Windows\RemovalTools\MRT_HB => C:\windows\system32\MRT.exe [2014-09-12] (Microsoft Corporation)
Task: {F9426B1C-C5B8-43C1-9B81-F5F6932587E9} - System32\Tasks\Security Center Update - 700698430 => C:\Users\Dorothy01\AppData\Roaming\Edutsoix\idyzsya.exe <==== ATTENTION
Task: {FA7D302B-25B4-4938-976B-AFD59ED105BC} - System32\Tasks\Security Center Update - 3992158093 => C:\Users\Dorothy01\AppData\Roaming\Onpyym\puzyril.exe <==== ATTENTION
Task: {FDF8C72F-4705-4C83-B0F3-47690D02FCBE} - System32\Tasks\Security Center Update - 4183678770 => C:\Users\Dorothy01\AppData\Roaming\Rifiewyn\puyrdo.exe <==== ATTENTION
Task: C:\WINDOWS\Tasks\avast! Emergency Update.job => C:\Program Files\AVAST Software\Avast\AvastEmUpdate.exe
Task: C:\WINDOWS\Tasks\GoogleUpdateTaskMachineCore.job => C:\Program Files (x86)\Google\Update\GoogleUpdate.exe
Task: C:\WINDOWS\Tasks\GoogleUpdateTaskMachineUA.job => C:\Program Files (x86)\Google\Update\GoogleUpdate.exe
==================== Loaded Modules (whitelisted) ==============
2014-07-04 22:33 - 2014-07-04 22:33 - 00127488 _____ () C:\Program Files\ATI Technologies\ATI.ACE\Fuel\Fuel.Container.Wlan.dll
2012-07-19 19:06 - 2012-07-19 19:06 - 00120224 _____ () c:\Program Files (x86)\Hewlett-Packard\HP Connected Remote\HPItunesModule.dll
2012-07-19 19:06 - 2012-07-19 19:06 - 00048544 _____ () c:\Program Files (x86)\Hewlett-Packard\HP Connected Remote\HPItunesProxy.dll
2012-07-19 19:07 - 2012-07-19 19:07 - 00180224 _____ () c:\Program Files (x86)\Hewlett-Packard\HP Connected Remote\zxing.dll
2014-10-14 13:10 - 2014-10-14 13:10 - 00120224 _____ () C:\Users\Dorothy01\AppData\Local\assembly\dl3\N1ZEJ5WT.E21\Y8VKR1P8.4QP\edb32bf5\0038bcf4_1366cd01\HPItunesModule.DLL
2014-07-04 22:33 - 2014-07-04 22:33 - 00102400 _____ () C:\Program Files\ATI Technologies\ATI.ACE\Fuel\Fuel.Proxy.Native.dll
2012-05-04 17:42 - 2012-05-04 17:42 - 00098304 _____ () C:\Program Files (x86)\ATI Technologies\ATI.ACE\Branding\BrandingNet4.dll
2015-02-19 21:17 - 2015-02-19 21:17 - 02911744 _____ () C:\Program Files\AVAST Software\Avast\defs\15021901\algo.dll
2014-07-31 13:16 - 2014-07-31 13:16 - 00073544 _____ () C:\Program Files (x86)\Common Files\Apple\Apple Application Support\zlib1.dll
2014-07-31 13:16 - 2014-07-31 13:16 - 01044776 _____ () C:\Program Files (x86)\Common Files\Apple\Apple Application Support\libxml2.dll
2014-12-09 18:31 - 2012-05-30 00:51 - 00699280 ____R () C:\PROGRAM FILES (X86)\NORTON INTERNET SECURITY\ENGINE\20.6.0.27\wincfi39.dll
2015-02-19 21:17 - 2015-02-19 21:17 - 38562088 _____ () C:\Program Files\AVAST Software\Avast\libcef.dll
==================== Alternate Data Streams (whitelisted) =========
(If an entry is included in the fixlist, only the Alternate Data Streams will be removed.)
==================== Safe Mode (whitelisted) ===================
(If an item is included in the fixlist, it will be removed from the registry. The "AlternateShell" will be restored.)
HKLM\SYSTEM\CurrentControlSet\Control\SafeBoot\Minimal\MBAMSwissArmy => ""="Driver"
HKLM\SYSTEM\CurrentControlSet\Control\SafeBoot\Network\MBAMSwissArmy => ""="Driver"
==================== EXE Association (whitelisted) ===============
(If an entry is included in the fixlist, the default will be restored. None default entries will be removed.)
==================== Other Areas ============================
(Currently there is no automatic fix for this section.)
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\Control Panel\Desktop\\Wallpaper -> C:\windows\web\wallpaper\HP\HP_Svinoya_Norway_Sunset.jpg
DNS Servers: Media is not connected to internet.
==================== MSCONFIG/TASK MANAGER disabled items ==
(Currently there is no automatic fix for this section.)
HKLM\...\StartupApproved\Run32: => "{30112b75-e574-a6db-560c-8103291a0838}"
HKLM\...\StartupApproved\Run32: => "CrashReportSaver"
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\StartupApproved\StartupFolder: => "HELP_DECRYPT.URL"
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\StartupApproved\StartupFolder: => "HELP_DECRYPT.TXT"
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\StartupApproved\StartupFolder: => "HELP_DECRYPT.PNG"
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\StartupApproved\StartupFolder: => "HELP_DECRYPT.HTML"
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\StartupApproved\Run: => "acikmao"
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\StartupApproved\Run: => "BluetoothS"
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\StartupApproved\Run: => "dccwmote"
HKU\S-1-5-21-1427692388-1042374531-2795145444-1001\...\StartupApproved\Run: => "Driver Support"
==================== Accounts: =============================
Administrator (S-1-5-21-1427692388-1042374531-2795145444-500 - Administrator - Disabled)
Dorothy01 (S-1-5-21-1427692388-1042374531-2795145444-1001 - Administrator - Enabled) => C:\Users\Dorothy01
Guest (S-1-5-21-1427692388-1042374531-2795145444-501 - Limited - Disabled)
HomeGroupUser$ (S-1-5-21-1427692388-1042374531-2795145444-1006 - Limited - Enabled)
==================== Faulty Device Manager Devices =============
==================== Event log errors: =========================
Application errors:
==================
Error: (02/21/2015 10:40:49 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: Faulting application name: powershell.exe, version: 6.3.9600.16384, time stamp: 0x52158733
Faulting module name: unknown, version: 0.0.0.0, time stamp: 0x00000000
Exception code: 0xc0000005
Fault offset: 0x033c92b8
Faulting process id: 0x13f4
Faulting application start time: 0xpowershell.exe0
Faulting application path: powershell.exe1
Faulting module path: powershell.exe2
Report Id: powershell.exe3
Faulting package full name: powershell.exe4
Faulting package-relative application ID: powershell.exe5
Error: (02/21/2015 10:40:48 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
Error: (02/21/2015 10:40:35 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: Faulting application name: powershell.exe, version: 6.3.9600.16384, time stamp: 0x52158733
Faulting module name: unknown, version: 0.0.0.0, time stamp: 0x00000000
Exception code: 0xc0000005
Fault offset: 0x033878b0
Faulting process id: 0xf0c
Faulting application start time: 0xpowershell.exe0
Faulting application path: powershell.exe1
Faulting module path: powershell.exe2
Report Id: powershell.exe3
Faulting package full name: powershell.exe4
Faulting package-relative application ID: powershell.exe5
Error: (02/21/2015 10:40:35 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
Error: (02/21/2015 10:40:24 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: Faulting application name: powershell.exe, version: 6.3.9600.16384, time stamp: 0x52158733
Faulting module name: unknown, version: 0.0.0.0, time stamp: 0x00000000
Exception code: 0xc0000005
Fault offset: 0x039292b8
Faulting process id: 0x6e0
Faulting application start time: 0xpowershell.exe0
Faulting application path: powershell.exe1
Faulting module path: powershell.exe2
Report Id: powershell.exe3
Faulting package full name: powershell.exe4
Faulting package-relative application ID: powershell.exe5
Error: (02/21/2015 10:40:24 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
Error: (02/21/2015 10:38:01 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: Faulting application name: powershell.exe, version: 6.3.9600.16384, time stamp: 0x52158733
Faulting module name: unknown, version: 0.0.0.0, time stamp: 0x00000000
Exception code: 0xc0000005
Fault offset: 0x03048ce8
Faulting process id: 0x1378
Faulting application start time: 0xpowershell.exe0
Faulting application path: powershell.exe1
Faulting module path: powershell.exe2
Report Id: powershell.exe3
Faulting package full name: powershell.exe4
Faulting package-relative application ID: powershell.exe5
Error: (02/21/2015 10:38:00 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
Error: (02/21/2015 10:37:50 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: Faulting application name: powershell.exe, version: 6.3.9600.16384, time stamp: 0x52158733
Faulting module name: unknown, version: 0.0.0.0, time stamp: 0x00000000
Exception code: 0xc0000005
Fault offset: 0x035092a0
Faulting process id: 0xf3c
Faulting application start time: 0xpowershell.exe0
Faulting application path: powershell.exe1
Faulting module path: powershell.exe2
Report Id: powershell.exe3
Faulting package full name: powershell.exe4
Faulting package-relative application ID: powershell.exe5
Error: (02/21/2015 10:37:50 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
System errors:
=============
Error: (02/21/2015 10:42:55 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Error: (02/21/2015 10:42:13 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Error: (02/21/2015 10:40:13 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Error: (02/21/2015 10:39:30 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Error: (02/21/2015 10:38:47 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Error: (02/21/2015 10:36:54 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Error: (02/21/2015 10:36:07 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Error: (02/21/2015 10:35:25 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Error: (02/21/2015 10:34:38 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Error: (02/21/2015 10:32:39 PM) (Source: DCOM) (EventID: 10010) (User: Dorothy)
Description: {AB8902B4-09CA-4BB6-B78D-A8F59079A8D5}
Microsoft Office Sessions:
=========================
Error: (02/21/2015 10:40:49 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: powershell.exe6.3.9600.1638452158733unknown0.0.0.000000000c0000005033c92b813f401d04e59b4ea3f5eC:\WINDOWS\syswow64\windowspowershell\v1.0\powershell.exeunknownf8b04196-ba4c-11e4-bef0-089e013a632b
Error: (02/21/2015 10:40:48 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
Error: (02/21/2015 10:40:35 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: powershell.exe6.3.9600.1638452158733unknown0.0.0.000000000c0000005033878b0f0c01d04e59ad2f98abC:\WINDOWS\syswow64\windowspowershell\v1.0\powershell.exeunknownf0be6a1c-ba4c-11e4-bef0-089e013a632b
Error: (02/21/2015 10:40:35 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
Error: (02/21/2015 10:40:24 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: powershell.exe6.3.9600.1638452158733unknown0.0.0.000000000c0000005039292b86e001d04e59a6e1c57dC:\WINDOWS\syswow64\windowspowershell\v1.0\powershell.exeunknownea3b534c-ba4c-11e4-bef0-089e013a632b
Error: (02/21/2015 10:40:24 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
Error: (02/21/2015 10:38:01 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: powershell.exe6.3.9600.1638452158733unknown0.0.0.000000000c000000503048ce8137801d04e5950fbbed4C:\WINDOWS\syswow64\windowspowershell\v1.0\powershell.exeunknown94e77365-ba4c-11e4-bef0-089e013a632b
Error: (02/21/2015 10:38:00 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
Error: (02/21/2015 10:37:50 PM) (Source: Application Error) (EventID: 1000) (User: )
Description: powershell.exe6.3.9600.1638452158733unknown0.0.0.000000000c0000005035092a0f3c01d04e594b4c4144C:\WINDOWS\syswow64\windowspowershell\v1.0\powershell.exeunknown8e33772d-ba4c-11e4-bef0-089e013a632b
Error: (02/21/2015 10:37:50 PM) (Source: .NET Runtime) (EventID: 1026) (User: )
Description: Application: powershell.exe
Framework Version: v4.0.30319
Description: The process was terminated due to an unhandled exception.
Exception Info: System.AccessViolationException
Stack:
at DynamicClass.CallSite.Target(System.Runtime.CompilerServices.Closure, System.Runtime.CompilerServices.CallSite, System.Object, System.Object, System.Object, Int32, Int32, Int32)
at System.Dynamic.UpdateDelegates.UpdateAndExecute6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.Runtime.CompilerServices.CallSite, System.__Canon, System.__Canon, System.__Canon, Int32, Int32, Int32)
at System.Management.Automation.Interpreter.DynamicInstruction`7[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Int32, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.ScriptBlock.InvokeWithPipeImpl(System.Management.Automation.ScriptBlockClauseToInvoke, Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock+<>c__DisplayClassa.<InvokeWithPipe>b__8()
at System.Management.Automation.Runspaces.RunspaceBase.RunActionIfNoRunningPipelinesWithThreadCheck(System.Action)
at System.Management.Automation.ScriptBlock.InvokeWithPipe(Boolean, System.Collections.Generic.Dictionary`2<System.String,System.Management.Automation.ScriptBlock>, System.Collections.Generic.List`1<System.Management.Automation.PSVariable>, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Management.Automation.Internal.Pipe, System.Management.Automation.InvocationInfo, System.Object[])
at System.Management.Automation.ScriptBlock.InvokeUsingCmdlet(System.Management.Automation.Cmdlet, Boolean, ErrorHandlingBehavior, System.Object, System.Object, System.Object, System.Object[])
at Microsoft.PowerShell.Commands.InvokeExpressionCommand.ProcessRecord()
at System.Management.Automation.Cmdlet.DoProcessRecord()
at System.Management.Automation.CommandProcessor.ProcessRecord()
at System.Management.Automation.CommandProcessorBase.DoExecute()
at System.Management.Automation.Internal.PipelineProcessor.Inject(System.Object, Boolean)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.PipelineOps.InvokePipeline(System.Object, Boolean, System.Management.Automation.CommandParameterInternal[][], System.Management.Automation.Language.CommandBaseAst[], System.Management.Automation.CommandRedirection[][], System.Management.Automation.Language.FunctionContext)
at System.Management.Automation.Interpreter.ActionCallInstruction`6[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.Boolean, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089],[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]].Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.EnterTryCatchFinallyInstruction.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.Interpreter.Run(System.Management.Automation.Interpreter.InterpretedFrame)
at System.Management.Automation.Interpreter.LightLambda.RunVoid1[[System.__Canon, mscorlib, Version=4.0.0.0, Culture=neutral, PublicKeyToken=b77a5c561934e089]](System.__Canon)
at System.Management.Automation.DlrScriptCommandProcessor.RunClause(System.Action`1<System.Management.Automation.Language.FunctionContext>, System.Object, System.Object)
at System.Management.Automation.DlrScriptCommandProcessor.Complete()
at System.Management.Automation.CommandProcessorBase.DoComplete()
at System.Management.Automation.Internal.PipelineProcessor.DoCompleteCore(System.Management.Automation.CommandProcessorBase)
at System.Management.Automation.Internal.PipelineProcessor.SynchronousExecuteEnumerate(System.Object, System.Collections.Hashtable, Boolean)
at System.Management.Automation.Runspaces.LocalPipeline.InvokeHelper()
at System.Management.Automation.Runspaces.LocalPipeline.InvokeThreadProc()
at System.Management.Automation.Runspaces.PipelineThread.WorkerProc()
at System.Threading.ThreadHelper.ThreadStart_Context(System.Object)
at System.Threading.ExecutionContext.RunInternal(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object, Boolean)
at System.Threading.ExecutionContext.Run(System.Threading.ExecutionContext, System.Threading.ContextCallback, System.Object)
at System.Threading.ThreadHelper.ThreadStart()
==================== Memory info ===========================
Processor: AMD E1-1200 APU with Radeon™ HD Graphics
Percentage of memory in use: 33%
Total physical RAM: 3660.08 MB
Available physical RAM: 2427.64 MB
Total Pagefile: 4060.08 MB
Available Pagefile: 2657.52 MB
Total Virtual: 131072 MB
Available Virtual: 131071.8 MB
==================== Drives ================================
Drive c: (OS) (Fixed) (Total:444.06 GB) (Free:382.85 GB) NTFS ==>[System with boot components (obtained from reading drive)]
Drive d: (Recovery Image) (Fixed) (Total:19.78 GB) (Free:2.47 GB) NTFS ==>[System with boot components (obtained from reading drive)]
Drive f: () (Removable) (Total:7.44 GB) (Free:6.38 GB) FAT32
==================== MBR & Partition Table ==================
========================================================
Disk: 0 (Size: 465.8 GB) (Disk ID: D370BA94)
Partition: GPT Partition Type.
========================================================
Disk: 1 (MBR Code: Windows 7 or 8) (Size: 7.5 GB) (Disk ID: 00000000)
Partition: GPT Partition Type.
==================== End Of Log ============================


 This topic is locked
This topic is locked




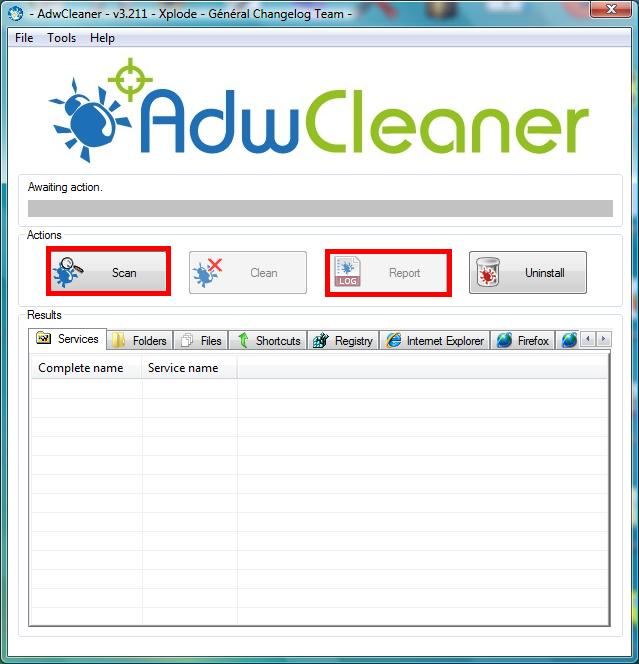





























 Sign In
Sign In Create Account
Create Account

