What is nerta TSS?
The Malwarebytes research team has determined that nerta TSS is a Tech Support Scam. These so-called "Tech Support Scammers" try to trick you into calling their phone number for various reasons, all of which turn out to be fraudulent in the end.
How do I know if my computer is affected by nerta TSS?
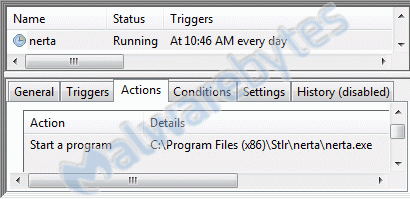
You may see this task in your Task Scheduler:
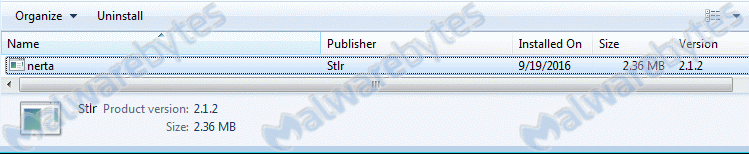
and this entry in your list of installed programs:
How did nerta TSS get on my computer?
Tech Support Scammers use different methods for distributing themselves. This particular one was bundled with other software.
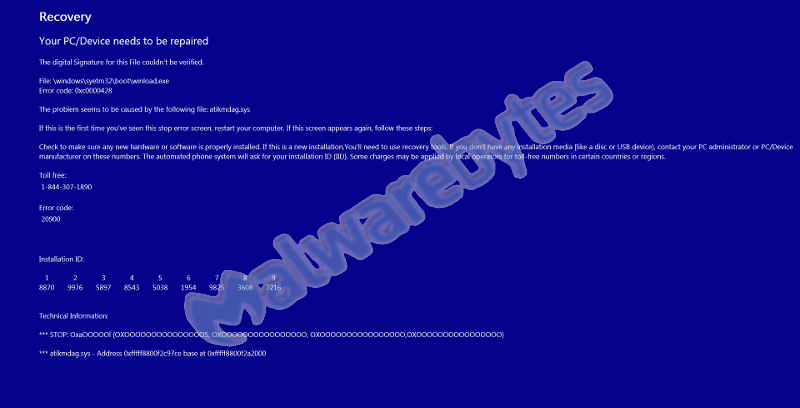
It installs files that will produce a fake Windows Activation screen with the Tech Support Scammers number. It can take a while before this actually happens, so you might be unaware of which install was the trigger.
It shows this fake error screen on top of your other applications, constantly refreshing so it's hard to stop.
How do I remove nerta TSS?
Our program Malwarebytes Anti-Malware can detect and remove this potentially unwanted application. Due to the nature of the infection, you will need to stop the malware process from running.
- When confronted with the fake blue error screen, use the Ctrl-Alt-Del key combination and run Task Manager.
- In the list of processes find nerta.exe.
- Select the nerta.exe process and click on the End Process button.
- Now you should have access to your desktop and other programs.
- Please download Malwarebytes Anti-Malware to your desktop.
- Double-click mbam-setup-{version}.exe and follow the prompts to install the program.
- At the end, be sure a check-mark is placed next to:
Launch Malwarebytes Anti-Malware - Then click Finish.
- Once the program has loaded, select Scan Now. Or select the Threat Scan from the Scan menu.
- If an update is available, it will be implemented before the rest of the scanning procedure.
- When the scan is complete, make sure that all Threats are selected, and click Remove Selected.
- Restart your computer when prompted to do so.
- No, Malwarebytes' Anti-Malware removes nerta TSS completely.
We hope our application and this guide have helped you eradicate this hijacker.
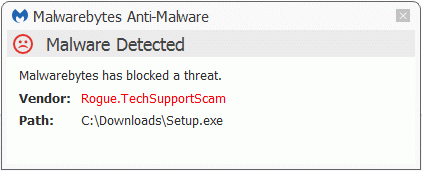
As you can see below the full version of Malwarebytes Anti-Malware would have protected you against the Tech Support Scam.
Technical details for experts
You may see these entries in FRST logs:
() C:\Program Files (x86)\Stlr\nerta\nerta.exe
() C:\Program Files (x86)\Stlr\nerta\nertacs.exe
Startup: C:\Users\{username}\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Nerta.lnk [2016-09-19]
ShortcutTarget: Nerta.lnk -> C:\Windows\System32\schtasks.exe (Microsoft Corporation)
R2 nrtService; C:\Program Files (x86)\Stlr\nerta\nertacs.exe [12288 2016-08-16] () [File not signed]
C:\Windows\System32\Tasks\nerta
C:\Users\{username}\AppData\Roaming\st
C:\Program Files (x86)\Stlr
nerta (HKLM-x32\...\nerta) (Version: 2.1.2 - Stlr)
Task: {0767AA60-4FDF-457C-9D2B-D132747A2416} - System32\Tasks\nerta => C:\Program Files (x86)\Stlr\nerta\nerta.exe [2016-08-29] ()Alterations made by the installer:File system details [View: All details] (Selection)
---------------------------------------------------
Adds the folder C:\Program Files (x86)\Stlr\nerta
Adds the file bto.ico"="8/12/2016 3:23 AM, 2462 bytes, A
Adds the file Caliburn.Micro.dll"="8/9/2016 10:37 PM, 104448 bytes, A
Adds the file Caliburn.Micro.pdb"="8/9/2016 10:37 PM, 296448 bytes, A
Adds the file Caliburn.Micro.xml"="8/9/2016 10:37 PM, 141115 bytes, A
Adds the file Comparers.dll"="4/17/2015 11:00 PM, 6144 bytes, A
Adds the file Garlic.dll"="8/9/2016 10:38 PM, 15360 bytes, A
Adds the file Garlic.pdb"="8/9/2016 10:38 PM, 40448 bytes, A
Adds the file InstallUtil.InstallLog"="9/19/2016 10:46 AM, 632 bytes, A
Adds the file Ionic.Zip.Reduced.dll"="7/14/2014 5:36 PM, 253440 bytes, A
Adds the file LedControl.dll"="3/6/2012 7:14 PM, 13824 bytes, A
Adds the file log.txt"="9/19/2016 10:46 AM, 743 bytes, A
Adds the file LoggingControl.dll"="1/22/2016 12:26 AM, 34816 bytes, A
Adds the file Microsoft.Win32.TaskScheduler.dll"="12/17/2015 3:24 AM, 185856 bytes, A
Adds the file Microsoft.Windows.Shell.dll"="10/19/2010 9:00 PM, 167808 bytes, A
Adds the file nerta.exe"="8/29/2016 12:41 PM, 30720 bytes, A
Adds the file nerta.exe.config"="8/9/2016 3:09 AM, 588 bytes, A
Adds the file nertacs.exe"="8/16/2016 4:00 AM, 12288 bytes, A
Adds the file nertacs.exe.config"="12/11/2015 2:26 AM, 597 bytes, A
Adds the file nertacs.InstallLog"="9/19/2016 10:46 AM, 645 bytes, A
Adds the file nertacs.InstallState"="9/19/2016 10:46 AM, 7466 bytes, A
Adds the file nertastarter.exe"="8/12/2016 6:12 AM, 6656 bytes, A
Adds the file nertastarter.exe.config"="12/11/2015 2:27 AM, 174 bytes, A
Adds the file Newtonsoft.Json.dll"="8/9/2016 10:37 PM, 489472 bytes, A
Adds the file Newtonsoft.Json.xml"="8/9/2016 10:37 PM, 523221 bytes, A
Adds the file nrtupdates.exe"="8/12/2016 6:11 AM, 11264 bytes, A
Adds the file nrtupdates.exe.config"="3/11/2015 10:26 PM, 174 bytes, A
Adds the file PDSA.Common.dll"="12/17/2015 3:24 AM, 9728 bytes, A
Adds the file System.Windows.Interactivity.dll"="8/9/2016 10:37 PM, 39936 bytes, A
Adds the file System.Windows.Interactivity.xml"="8/9/2016 10:37 PM, 62128 bytes, A
Adds the file testwcf.exe"="8/12/2016 4:18 AM, 6656 bytes, A
Adds the file testwcf.exe.config"="8/12/2016 3:59 AM, 174 bytes, A
Adds the file UrlHistoryLibrary.dll"="2/3/2015 11:12 PM, 24576 bytes, A
In the existing folder C:\Users\{username}\AppData\Roaming
Adds the file st"="9/19/2016 10:46 AM, 53 bytes, A
In the existing folder C:\Users\{username}\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
Adds the file Nerta.lnk"="9/19/2016 10:46 AM, 1825 bytes, A
In the existing folder C:\Windows\System32\Tasks
Adds the file nerta"="9/19/2016 10:46 AM, 3252 bytes, A
Registry details [View: All details] (Selection)
------------------------------------------------
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\nerta_RASAPI32]
"ConsoleTracingMask"="REG_DWORD", -65536
"EnableConsoleTracing"="REG_DWORD", 0
"EnableFileTracing"="REG_DWORD", 0
"FileDirectory"="REG_EXPAND_SZ, "%windir%\tracing"
"FileTracingMask"="REG_DWORD", -65536
"MaxFileSize"="REG_DWORD", 1048576
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\nerta_RASMANCS]
"ConsoleTracingMask"="REG_DWORD", -65536
"EnableConsoleTracing"="REG_DWORD", 0
"EnableFileTracing"="REG_DWORD", 0
"FileDirectory"="REG_EXPAND_SZ, "%windir%\tracing"
"FileTracingMask"="REG_DWORD", -65536
"MaxFileSize"="REG_DWORD", 1048576
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Uninstall\nerta]
"DisplayIcon"="REG_SZ", "C:\Program Files (x86)\Stlr\nerta\Uninstall.exe"
"DisplayName"="REG_SZ", "nerta"
"DisplayVersion"="REG_SZ", "2.1.2"
"EstimatedSize"="REG_DWORD", 2423
"InstallDate"="REG_SZ", "20160919"
"InstallLocation"="REG_SZ", "C:\Program Files (x86)\Stlr\nerta\"
"InstallSource"="REG_SZ", "C:\Users\{username}\Desktop\"
"Language"="REG_DWORD", 1033
"NoModify"="REG_DWORD", 1
"NoRepair"="REG_DWORD", 1
"Publisher"="REG_SZ", "Stlr"
"UninstallString"="REG_SZ", "C:\Program Files (x86)\Stlr\nerta\Uninstall.exe"
"VersionMajor"="REG_DWORD", 2
"VersionMinor"="REG_DWORD", 1
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\eventlog\Application\nrtService]
"EventMessageFile"="REG_EXPAND_SZ, "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\EventLogMessages.dll"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\nrtService]
"DelayedAutostart"="REG_DWORD", 0
"Description"="REG_SZ", "this will update the gas"
"DisplayName"="REG_SZ", "Btior New"
"ErrorControl"="REG_DWORD", 1
"ImagePath"="REG_EXPAND_SZ, ""C:\Program Files (x86)\Stlr\nerta\nertacs.exe""
"ObjectName"="REG_SZ", "LocalSystem"
"Start"="REG_DWORD", 2
"Type"="REG_DWORD", 16
Malwarebytes Anti-Malware log:Malwarebytes Anti-Malware
www.malwarebytes.org
Scan Date: 9/19/2016
Scan Time: 10:54 AM
Logfile: mbamNerta.txt
Administrator: Yes
Version: 2.2.1.1043
Malware Database: v2016.09.19.03
Rootkit Database: v2016.08.15.01
License: Premium
Malware Protection: Disabled
Malicious Website Protection: Enabled
Self-protection: Enabled
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: {username}
Scan Type: Threat Scan
Result: Completed
Objects Scanned: 321010
Time Elapsed: 9 min, 46 sec
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Enabled
Heuristics: Enabled
PUP: Enabled
PUM: Enabled
Processes: 2
Rogue.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nerta.exe, 3184, Delete-on-Reboot, [4db2b6bd97039a9c4683608fcd3711ef]
Rogue.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nertacs.exe, 3360, Delete-on-Reboot, [08f7da993b5f280efad03ab54db7857b]
Modules: 0
(No malicious items detected)
Registry Keys: 4
Rogue.TechSupportScam, HKLM\SYSTEM\CURRENTCONTROLSET\SERVICES\nrtService, Quarantined, [08f7da993b5f280efad03ab54db7857b],
Trojan.TechSupportScam, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{0767AA60-4FDF-457C-9D2B-D132747A2416}, Delete-on-Reboot, [af50d79c9109ad8989a340af8b79a957],
Trojan.TechSupportScam, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TREE\nerta, Delete-on-Reboot, [a15e96dd1585c571af7edc130103a759],
Trojan.TechSupportScam, HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\UNINSTALL\nerta, Quarantined, [fc03b1c222784bebfc2ed21de222fa06],
Registry Values: 1
Trojan.TechSupportScam, HKLM\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\SCHEDULE\TASKCACHE\TASKS\{0767AA60-4FDF-457C-9D2B-D132747A2416}|Path, \nerta, Delete-on-Reboot, [af50d79c9109ad8989a340af8b79a957]
Registry Data: 0
(No malicious items detected)
Folders: 2
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta, Delete-on-Reboot, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr, Delete-on-Reboot, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Files: 36
Rogue.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nerta.exe, Quarantined, [4db2b6bd97039a9c4683608fcd3711ef],
Rogue.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nertacs.exe, Delete-on-Reboot, [08f7da993b5f280efad03ab54db7857b],
Rogue.TechSupportScam, C:\Users\{username}\Desktop\Setup.exe, Quarantined, [c639adc6e1b95cda77540ce33acafa06],
Trojan.TechSupportScam, C:\Windows\System32\Tasks\nerta, Quarantined, [19e611629efce55152dcf0fff70dd828],
Trojan.TechSupportScam, C:\Users\{username}\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Nerta.lnk, Quarantined, [35ca4c27f9a180b6df51c32caa5aea16],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\log.txt, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\bto.ico, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Caliburn.Micro.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Caliburn.Micro.pdb, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Caliburn.Micro.xml, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Comparers.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Garlic.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Garlic.pdb, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\InstallUtil.InstallLog, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Ionic.Zip.Reduced.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\LedControl.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\LoggingControl.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Microsoft.Win32.TaskScheduler.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Microsoft.Windows.Shell.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nerta.exe.config, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nertacs.exe.config, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nertacs.InstallLog, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nertacs.InstallState, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nertastarter.exe, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nertastarter.exe.config, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Newtonsoft.Json.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\Newtonsoft.Json.xml, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nrtupdates.exe, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\nrtupdates.exe.config, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\PDSA.Common.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\System.Windows.Interactivity.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\System.Windows.Interactivity.xml, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\testwcf.exe, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\testwcf.exe.config, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Trojan.TechSupportScam, C:\Program Files (x86)\Stlr\nerta\UrlHistoryLibrary.dll, Quarantined, [34cb7300f8a2b87ecd6430bf1ee64ab6],
Rogue.TechSupportScam, C:\Users\{username}\AppData\Roaming\st, Quarantined, [08f7264dbedc45f168eb0ee208fc15eb],
Physical Sectors: 0
(No malicious items detected)
(end)As mentioned before the full version of Malwarebytes Anti-Malware could have protected your computer against this threat.We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

