---------------------------------------------------------
ewido security suite - Scan report
---------------------------------------------------------
+ Created on: 6:45:55 PM, 7/28/2005
+ Report-Checksum: 69C703D
+ Scan result:
C:\Documents and Settings\Owner\Cookies\[email protected][2].txt -> Spyware.Cookie.2o7 : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@2o7[1].txt -> Spyware.Cookie.2o7 : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][2].txt -> Spyware.Cookie.Yieldmanager : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@advertising[2].txt -> Spyware.Cookie.Advertising : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][1].txt -> Spyware.Cookie.Falkag : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@atdmt[1].txt -> Spyware.Cookie.Atdmt : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@bluestreak[2].txt -> Spyware.Cookie.Bluestreak : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][2].txt -> Spyware.Cookie.Serving-sys : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@casalemedia[1].txt -> Spyware.Cookie.Casalemedia : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][1].txt -> Spyware.Cookie.Coremetrics : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@doubleclick[1].txt -> Spyware.Cookie.Doubleclick : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][1].txt -> Spyware.Cookie.Esomniture : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][1].txt -> Spyware.Cookie.Esomniture : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][2].txt -> Spyware.Cookie.Esomniture : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][2].txt -> Spyware.Cookie.Hitbox : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@fastclick[1].txt -> Spyware.Cookie.Fastclick : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@hitbox[1].txt -> Spyware.Cookie.Hitbox : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@mediaplex[1].txt -> Spyware.Cookie.Mediaplex : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][1].txt -> Spyware.Cookie.Overture : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@qksrv[2].txt -> Spyware.Cookie.Qksrv : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@questionmarket[1].txt -> Spyware.Cookie.Questionmarket : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][2].txt -> Spyware.Cookie.Advertising : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][2].txt -> Spyware.Cookie.Liveperson : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@serving-sys[1].txt -> Spyware.Cookie.Serving-sys : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@trafficmp[2].txt -> Spyware.Cookie.Trafficmp : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@tribalfusion[1].txt -> Spyware.Cookie.Tribalfusion : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\owner@valueclick[2].txt -> Spyware.Cookie.Valueclick : Cleaned with backup
C:\Documents and Settings\Owner\Cookies\[email protected][1].txt -> Spyware.Cookie.Adserver : Cleaned with backup
C:\Documents and Settings\Owner\Local Settings\Temporary Internet Files\Content.IE5\4XIBODUR\popcaploader_v6[1].cab/PopCapLoader.dll -> Not-A-Virus.PornWare.PopCap.b : Error during cleaning
C:\WINDOWS\fgtygsa.exe -> Adware.BetterInternet : Cleaned with backup
::Report End
Logfile of HijackThis v1.99.1
Scan saved at 6:49:27 PM, on 7/28/2005
Platform: Windows XP SP1 (WinNT 5.01.2600)
MSIE: Internet Explorer v6.00 SP1 (6.00.2800.1106)
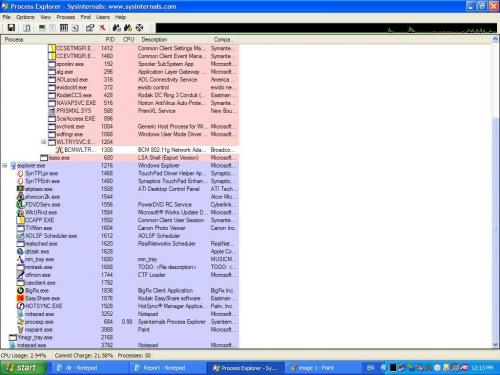
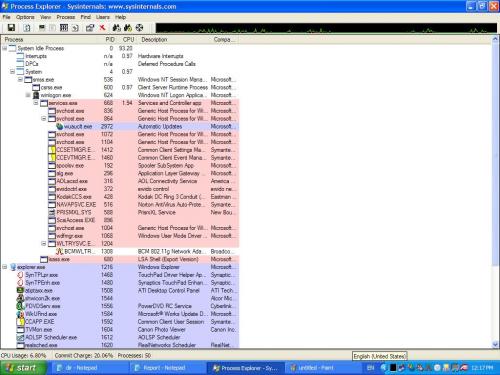
Running processes:
C:\WINDOWS\System32\smss.exe
C:\WINDOWS\system32\csrss.exe
C:\WINDOWS\system32\winlogon.exe
C:\WINDOWS\system32\services.exe
C:\WINDOWS\system32\lsass.exe
C:\WINDOWS\system32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\System32\svchost.exe
C:\Program Files\Common Files\Symantec Shared\ccSetMgr.exe
C:\WINDOWS\Explorer.EXE
C:\Program Files\Common Files\Symantec Shared\ccEvtMgr.exe
C:\WINDOWS\system32\spoolsv.exe
C:\Program Files\Synaptics\SynTP\SynTPLpr.exe
C:\Program Files\Synaptics\SynTP\SynTPEnh.exe
C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe
C:\WINDOWS\System32\alg.exe
C:\Program Files\Common Files\Symantec Shared\Security Center\UsrPrmpt.exe
C:\Program Files\Digital Media Reader\shwicon2k.exe
C:\Program Files\CyberLink\PowerDVD\PDVDServ.exe
C:\PROGRA~1\COMMON~1\AOL\ACS\AOLacsd.exe
C:\Program Files\Common Files\Microsoft Shared\Works Shared\WkUFind.exe
C:\Program Files\Common Files\Symantec Shared\ccApp.exe
C:\Program Files\Canon\BJPV\TVMon.exe
C:\PROGRA~1\COMMON~1\AOL\AOLSPY~1\AOLSP Scheduler.exe
C:\Program Files\Common Files\Real\Update_OB\realsched.exe
C:\Program Files\QuickTime\qttask.exe
C:\Program Files\ewido\security suite\ewidoctrl.exe
C:\Program Files\MUSICMATCH\MUSICMATCH Jukebox\mm_tray.exe
C:\WINDOWS\system32\drivers\KodakCCS.exe
C:\Program Files\MusicMatch\MusicMatch Jukebox\mmtask.exe
C:\WINDOWS\System32\ctfmon.exe
C:\Program Files\Cas\Client\casclient.exe
C:\Program Files\Norton AntiVirus\navapsvc.exe
C:\Program Files\BigFix\BigFix.exe
C:\Program Files\Kodak\Kodak EasyShare software\bin\EasyShare.exe
C:\Program Files\Common Files\New Boundary\PrismXL\PRISMXL.SYS
C:\Program Files\Palm\HOTSYNC.EXE
C:\WINDOWS\System32\ScsiAccess.EXE
C:\WINDOWS\System32\svchost.exe
C:\WINDOWS\System32\wdfmgr.exe
C:\WINDOWS\System32\wltrysvc.exe
C:\WINDOWS\System32\bcmwltry.exe
C:\Program Files\Yahoo!\Messenger\ymsgr_tray.exe
C:\WINDOWS\System32\wuauclt.exe
C:\Documents and Settings\Owner\Desktop\hijack this\HijackThis.exe
R0 - HKCU\Software\Microsoft\Internet Explorer\Main,Start Page = http://www.yahoo.com/
R1 - HKLM\Software\Microsoft\Internet Explorer\Main,Default_Page_URL = http://red.clientapp...//www.yahoo.com
R0 - HKLM\Software\Microsoft\Internet Explorer\Main,Start Page = http://red.clientapp...//www.yahoo.com
R1 - HKCU\Software\Microsoft\Internet Connection Wizard,ShellNext = wmplayer.exe //ICWLaunch
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,ProxyOverride = localhost
O2 - BHO: (no name) - {53707962-6F74-2D53-2644-206D7942484F} - C:\Program Files\Spybot - Search & Destroy\SDHelper.dll
O2 - BHO: PCTools Site Guard - {5C8B2A36-3DB1-42A4-A3CB-D426709BBFEB} - C:\PROGRA~1\SPYWAR~1\tools\iesdsg.dll
O2 - BHO: PCTools Browser Monitor - {B56A7D7D-6927-48C8-A975-17DF180C71AC} - C:\PROGRA~1\SPYWAR~1\tools\iesdpb.dll
O3 - Toolbar: Yahoo! Toolbar - {EF99BD32-C1FB-11D2-892F-0090271D4F88} - C:\Program Files\Yahoo!\Companion\Installs\cpn2\yt.dll
O4 - HKLM\..\Run: [SynTPLpr] C:\Program Files\Synaptics\SynTP\SynTPLpr.exe
O4 - HKLM\..\Run: [SynTPEnh] C:\Program Files\Synaptics\SynTP\SynTPEnh.exe
O4 - HKLM\..\Run: [ATIModeChange] Ati2mdxx.exe
O4 - HKLM\..\Run: [ATIPTA] C:\Program Files\ATI Technologies\ATI Control Panel\atiptaxx.exe
O4 - HKLM\..\Run: [Symantec NetDriver Monitor] C:\PROGRA~1\SYMNET~1\SNDMon.exe /Consumer
O4 - HKLM\..\Run: [SSC_UserPrompt] C:\Program Files\Common Files\Symantec Shared\Security Center\UsrPrmpt.exe
O4 - HKLM\..\Run: [SunKist] C:\Program Files\Digital Media Reader\shwicon2k.exe
O4 - HKLM\..\Run: [RemoteControl] "C:\Program Files\CyberLink\PowerDVD\PDVDServ.exe"
O4 - HKLM\..\Run: [NAV CfgWiz] C:\Program Files\Common Files\Symantec Shared\CfgWiz.exe /GUID NAV /CMDLINE "REBOOT"
O4 - HKLM\..\Run: [Microsoft Works Update Detection] C:\Program Files\Common Files\Microsoft Shared\Works Shared\WkUFind.exe
O4 - HKLM\..\Run: [ccApp] "C:\Program Files\Common Files\Symantec Shared\ccApp.exe"
O4 - HKLM\..\Run: [BJPD HID Control] C:\Program Files\Canon\BJPV\TVMon.exe
O4 - HKLM\..\Run: [AOL Spyware Protection] "C:\PROGRA~1\COMMON~1\AOL\AOLSPY~1\AOLSP Scheduler.exe"
O4 - HKLM\..\Run: [TkBellExe] C:\Program Files\Common Files\Real\Update_OB\realsched.exe -osboot
O4 - HKLM\..\Run: [QuickTime Task] "C:\Program Files\QuickTime\qttask.exe" -atboottime
O4 - HKLM\..\Run: [NeroFilterCheck] C:\WINDOWS\system32\NeroCheck.exe
O4 - HKLM\..\Run: [MMTray] C:\Program Files\MUSICMATCH\MUSICMATCH Jukebox\mm_tray.exe
O4 - HKLM\..\Run: [mmtask] c:\Program Files\MusicMatch\MusicMatch Jukebox\mmtask.exe
O4 - HKLM\..\Run: [Gateway Extended Warranty] "C:\Program Files\Gateway\GWCares\GWCares.exe"
O4 - HKLM\..\Run: [winsync] C:\WINDOWS\System32\ojnapn.exe reg_run
O4 - HKCU\..\Run: [Yahoo! Pager] C:\Program Files\Yahoo!\Messenger\ypager.exe -quiet
O4 - HKCU\..\Run: [ctfmon.exe] C:\WINDOWS\System32\ctfmon.exe
O4 - HKCU\..\Run: [CAS Client] "C:\Program Files\Cas\Client\casclient.exe"
O4 - Startup: HotSync Manager.lnk = C:\Program Files\Palm\HOTSYNC.EXE
O4 - Global Startup: BigFix.lnk = C:\Program Files\BigFix\BigFix.exe
O4 - Global Startup: Kodak EasyShare software.lnk = C:\Program Files\Kodak\Kodak EasyShare software\bin\EasyShare.exe
O4 - Global Startup: Microsoft Office.lnk = C:\Program Files\Microsoft Office\Office\OSA9.EXE
O8 - Extra context menu item: &AOL Toolbar search - res://C:\Program Files\AOL Toolbar\toolbar.dll/SEARCH.HTML
O8 - Extra context menu item: &Google Search - res://c:\program files\google\GoogleToolbar1.dll/cmsearch.html
O8 - Extra context menu item: &Yahoo! Search - file:///C:\Program Files\Yahoo!\Common/ycsrch.htm
O8 - Extra context menu item: Backward Links - res://c:\program files\google\GoogleToolbar1.dll/cmbacklinks.html
O8 - Extra context menu item: Cached Snapshot of Page - res://c:\program files\google\GoogleToolbar1.dll/cmcache.html
O8 - Extra context menu item: Similar Pages - res://c:\program files\google\GoogleToolbar1.dll/cmsimilar.html
O8 - Extra context menu item: Translate into English - res://c:\program files\google\GoogleToolbar1.dll/cmtrans.html
O8 - Extra context menu item: Yahoo! &Dictionary - file:///C:\Program Files\Yahoo!\Common/ycdict.htm
O8 - Extra context menu item: Yahoo! &Maps - file:///C:\Program Files\Yahoo!\Common/ycdict.htm
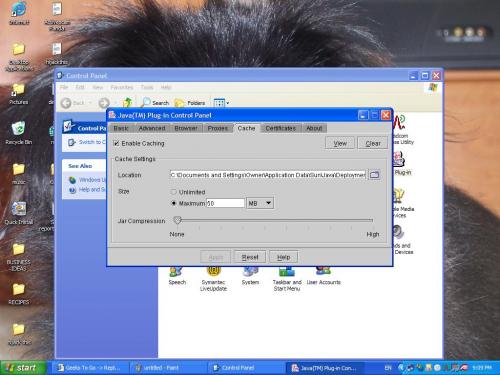
O9 - Extra button: (no name) - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\j2re1.4.2\bin\npjpi142.dll
O9 - Extra 'Tools' menuitem: Sun Java Console - {08B0E5C0-4FCB-11CF-AAA5-00401C608501} - C:\Program Files\Java\j2re1.4.2\bin\npjpi142.dll
O9 - Extra button: Spyware Doctor - {2D663D1A-8670-49D9-A1A5-4C56B4E14E84} - C:\PROGRA~1\SPYWAR~1\tools\iesdpb.dll
O9 - Extra button: Messenger - {4528BBE0-4E08-11D5-AD55-00010333D0AD} - C:\Program Files\Yahoo!\Messenger\yhexbmes0521.dll
O9 - Extra 'Tools' menuitem: Yahoo! Messenger - {4528BBE0-4E08-11D5-AD55-00010333D0AD} - C:\Program Files\Yahoo!\Messenger\yhexbmes0521.dll
O9 - Extra button: AOL Toolbar - {4982D40A-C53B-4615-B15B-B5B5E98D167C} - C:\Program Files\AOL Toolbar\toolbar.dll
O9 - Extra 'Tools' menuitem: AOL Toolbar - {4982D40A-C53B-4615-B15B-B5B5E98D167C} - C:\Program Files\AOL Toolbar\toolbar.dll
O9 - Extra button: AIM - {AC9E2541-2814-11d5-BC6D-00B0D0A1DE45} - C:\Program Files\AIM\aim.exe
O9 - Extra button: Real.com - {CD67F990-D8E9-11d2-98FE-00C0F0318AFE} - C:\WINDOWS\System32\Shdocvw.dll
O16 - DPF: {30528230-99F7-4BB4-88D8-FA1D4F56A2AB} (YInstStarter Class) - http://us.dl1.yimg.c...nst20040510.cab
O16 - DPF: {4F1E5B1A-2A80-42CA-8532-2D05CB959537} (MSN Photo Upload Tool) - http://by107fd.bay10...es/MsnPUpld.cab
O16 - DPF: {6414512B-B978-451D-A0D8-FCFDF33E833C} (WUWebControl Class) - http://update.micros...b?1121748673693
O16 - DPF: {74D05D43-3236-11D4-BDCD-00C04F9A3B61} (HouseCall Control) - http://a840.g.akamai...all/xscan53.cab
O16 - DPF: {7E980B9B-8AE5-466A-B6D6-DA8CF814E78A} (MJLauncherCtrl Class) - http://www.shockwave...mjolauncher.cab
O16 - DPF: {DF780F87-FF2B-4DF8-92D0-73DB16A1543A} (PopCapLoader Object) - http://download.game...aploader_v6.cab
O23 - Service: AOL Connectivity Service (AOL ACS) - America Online, Inc. - C:\PROGRA~1\COMMON~1\AOL\ACS\AOLacsd.exe
O23 - Service: Symantec Event Manager (ccEvtMgr) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\ccEvtMgr.exe
O23 - Service: Symantec Password Validation (ccPwdSvc) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\ccPwdSvc.exe
O23 - Service: Symantec Settings Manager (ccSetMgr) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\ccSetMgr.exe
O23 - Service: ewido security suite control - ewido networks - C:\Program Files\ewido\security suite\ewidoctrl.exe
O23 - Service: Kodak Camera Connection Software (KodakCCS) - Eastman Kodak Company - C:\WINDOWS\system32\drivers\KodakCCS.exe
O23 - Service: Norton AntiVirus Auto Protect Service (navapsvc) - Symantec Corporation - C:\Program Files\Norton AntiVirus\navapsvc.exe
O23 - Service: PrismXL - New Boundary Technologies, Inc. - C:\Program Files\Common Files\New Boundary\PrismXL\PRISMXL.SYS
O23 - Service: SAVScan - Symantec Corporation - C:\Program Files\Norton AntiVirus\SAVScan.exe
O23 - Service: ScriptBlocking Service (SBService) - Symantec Corporation - C:\PROGRA~1\COMMON~1\SYMANT~1\SCRIPT~1\SBServ.exe
O23 - Service: ScsiAccess - Unknown owner - C:\WINDOWS\System32\ScsiAccess.EXE
O23 - Service: Symantec Network Drivers Service (SNDSrvc) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\SNDSrvc.exe
O23 - Service: SymWMI Service (SymWSC) - Symantec Corporation - C:\Program Files\Common Files\Symantec Shared\Security Center\SymWSC.exe
O23 - Service: WLTRYSVC - Unknown owner - C:\WINDOWS\System32\wltrysvc.exe
There you go!!!















 Sign In
Sign In Create Account
Create Account

