The Malwarebytes research team has determined that AV Guard Online is a fake anti-malware application. These so-called "rogues" use intentional false positives to convince users that their systems have been compromised. Then they try to sell you their software, claiming it will remove these threats. In extreme cases the false threats are actually the very trojans that advertise or even directly install the rogue. You are strongly advised to follow our removal instructions below.
How do I know if I am infected with AV Guard Online?
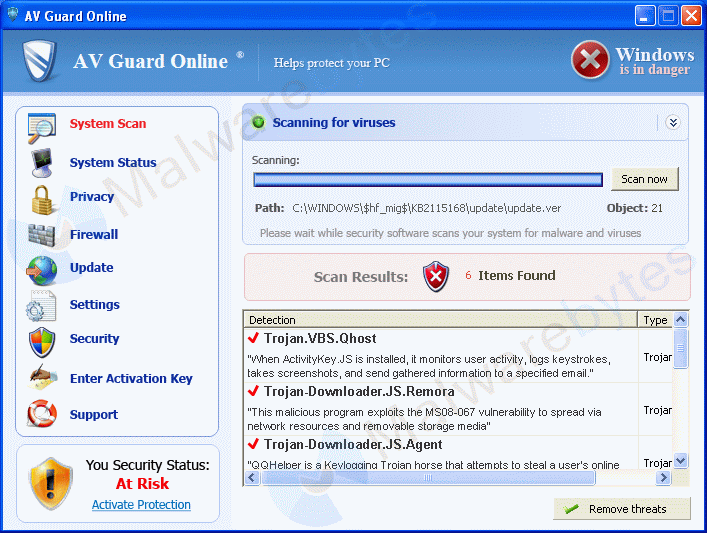
This is how the main screen of the rogue application looks:
You will find these icons on your desktop and in your taskbar:
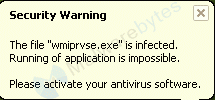
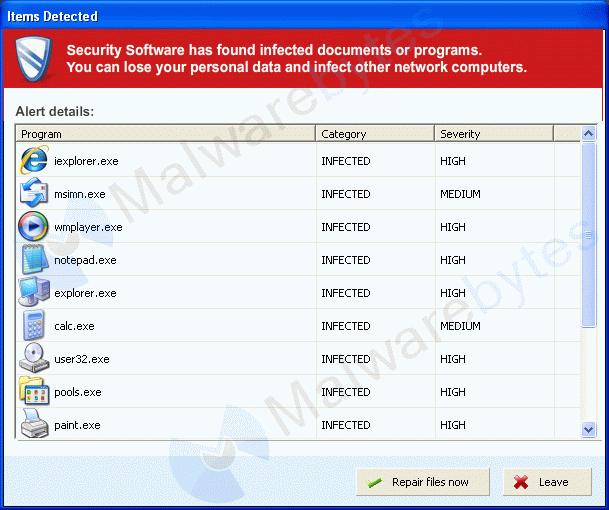
And see these warnings:
How did AV Guard Online get on my computer?
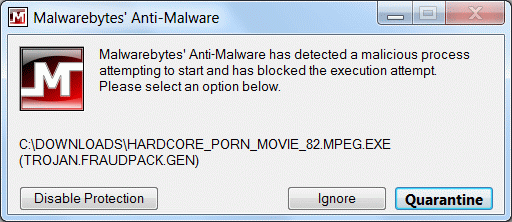
Rogue programs use different methods for spreading themselves. This particular one was offered as a movie with explicit content.
How do I remove AV Guard Online?
Our program Malwarebytes' Anti-Malware can detect and remove this rogue application.
- Please download Malwarebytes' Anti-Malware from here
If you are unable to do this from the infected computer directly, transfer the file from another computer. - Download the mbam-setup.exe to your desktop.
- Now make sure extensions are shown. To do this, please look here
- Then rename the mbam-setup.exe:
 to iexplore.exe
to iexplore.exe - Then launch iexplore.exe in order to install Malwarebytes' Anti-malware
- Once Malwarebytes' Anti-Malware is installed, navigate to your Program Files\Malwarebytes' Anti-Malware folder and locate the mbam.exe in there:

rename it to iexplore.exe
- Now doubleclick iexplore.exe to launch Malwarebytes' Anti-malware.
- Click the "Update" tab and click the "Check For updates" button.
- Once the program has loaded and updates were downloaded, select "Perform Quick Scan", then click Scan.
- The scan may take some time to finish,so please be patient.
- When the scan is complete, click OK, then Show Results to view the results.
- Make sure that everything is checked, and click Remove Selected.
- When disinfection is completed, a log will open in Notepad and you may be prompted to Restart, so please allow MBAM to restart.
- The log is automatically saved by MBAM and can be viewed by clicking the Logs tab in MBAM.
Is there anything else I need to do to get rid of AV Guard Online?
- The shortcut called AV Guard Online on the desktop can be deleted if it belonged to the rogue. If you are unsure, compare the icon to the one posted above.
How would the full version of Malwarebytes' Anti-Malware help protect me?
We hope our application has helped you eradicate this malicious software. If your current security solution let this infection through, you might please consider purchasing the FULL version of Malwarebytes' Anti-Malware for additional protection.
As you can see below the full version of Malwarebytes' Anti-Malware would have protected you against the AV Guard Online rogue. It would have warned you before the rogue could install itself, giving you a chance to stop it before it became too late.
Signs in a HijackThis log:
C:\DOCUME~1\{username}1\LOCALS~1\Temp\9.tmp
C:\WINDOWS\system32\dC6ujAXym.exe
C:\Documents and Settings\{username}\Application Data\conhost.exe
C:\WINDOWS\system32\lvvm.exe
C:\Documents and Settings\{username}\Desktop\iexplore.exe
R1 - HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings,ProxyServer = http=127.0.0.1:60970
F3 - REG:win.ini: load=C:\WINDOWS\system32\lvvm.exe
O4 - HKLM\..\Run: [conhost] C:\Documents and Settings\{username}\Application Data\Microsoft\csrss.exe
O4 - HKLM\..\Run: [G4tgnL3fI2dUwYq8234A] C:\WINDOWS\system32\dC6ujAXym.exe
O4 - HKLM\..\Run: [AyhmP4tnLrbKdJs8234A] C:\WINDOWS\system32\REDV7kWCuQX.exe
O4 - HKCU\..\Policies\Explorer\Run: [MartS] C:\Documents and Settings\{username}\Application Data\csrss.exe
Note: filenames and Runkey-names are (semi-)random
Alterations made by the installer:
File System
===============
In the existing folder C:\Documents and Settings\{username}\Application Data
Adds the file A1BA.EEF"="11:35 06/10/11 2136 bytes
Adds the file BscYHqaTNpRBlVkAV Guard Online.ico"="11:32 06/10/11 15086 bytes
Adds the file conhost.exe"="11:32 06/10/11 184320 bytes
Adds the file csrss.exe"="14:10 09/02/09 31744 bytes
Adds the file ldr.ini"="11:32 06/10/11 1213 bytes
Adds the folder C:\Documents and Settings\{username}\Application Data\bgnOLrfO3fI2v1c
Adds the folder C:\Documents and Settings\{username}\Application Data\BscYHqaTNpRBlVk
Adds the folder C:\Documents and Settings\{username}\Application Data\dtgnO3rbKevJ
Adds the folder C:\Documents and Settings\{username}\Application Data\r1wscH0aTNpR8E7
Adds the folder C:\Documents and Settings\{username}\Application Data\XpzRF8oRBoEVk
In the existing folder C:\Documents and Settings\{username}\Application Data\Microsoft
Adds the file csrss.exe"="11:31 06/10/11 180224 bytes
In the existing folder C:\Documents and Settings\{username}\Desktop
Adds the file AV Guard Online.lnk"="11:32 06/10/11 1705 bytes
In the existing folder C:\Documents and Settings\{username}\Local Settings\Temp
Adds the file 9.tmp"="11:31 06/10/11 180224 bytes
Adds the file A.tmp"="11:31 06/10/11 66560 bytes
Adds the file B.tmp"="11:32 06/10/11 5 bytes
Adds the file C.tmp"="11:32 06/10/11 0 bytes
Adds the file D.tmp"="11:32 06/10/11 0 bytes
Adds the file E.exe"="11:35 06/10/11 2413056 bytes
Adds the file E.tmp"="11:35 06/10/11 0 bytes
Adds the folder C:\Documents and Settings\{username}\Start Menu\Programs\AV Guard Online
Adds the file AV Guard Online.lnk"="11:32 06/10/11 1717 bytes
In the existing folder C:\Program Files\Internet Explorer
Adds the file rasadhlp.dll"="11:31 06/10/11 66560 bytes
In the existing folder C:\Program Files\Outlook Express
Adds the file rasadhlp.dll"="11:31 06/10/11 66560 bytes
In the existing folder C:\WINDOWS\system32
Adds the file dC6ujAXym.exe"="11:31 06/10/11 2412032 bytes
Adds the file lvvm.exe"="11:32 06/10/11 196608 bytes
Adds the file REDV7kWCuQX.exe"="11:35 06/10/11 2413056 bytes
Registry
===============
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run]
"AyhmP4tnLrbKdJs8234A"="'C:\WINDOWS\system32\REDV7kWCuQX.exe'"
"conhost"="'C:\Documents and Settings\{username}\Application Data\Microsoft\csrss.exe'"
"G4tgnL3fI2dUwYq8234A"="'C:\WINDOWS\system32\dC6ujAXym.exe'"
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections]
"DefaultConnectionSettings"="http=127.0.0.1:60970"
"SavedLegacySettings"="http=127.0.0.1:60970"
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run]
"MartS"="'C:\Documents and Settings\{username}\Application Data\csrss.exe'"
[HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows]
"load"="'C:\WINDOWS\system32\lvvm.exe'"
[HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon]
"Shell"="'explorer.exe,C:\Documents and Settings\{username}\Application Data\conhost.exe'"
Malwarebytes' Anti-Malware log:
Malwarebytes' Anti-Malware 1.51.2.1300
www.malwarebytes.org
Database version: 7883
Windows 5.1.2600 Service Pack 3
Internet Explorer 8.0.6001.18702
10/6/2011 11:40:04 AM
mbam-log-2011-10-06 (11-40-04).txt
Scan type: Quick scan
Objects scanned: 147497
Time elapsed: 1 minute(s), 5 second(s)
Memory Processes Infected: 3
Memory Modules Infected: 0
Registry Keys Infected: 0
Registry Values Infected: 5
Registry Data Items Infected: 1
Folders Infected: 0
Files Infected: 12
Memory Processes Infected:
c:\WINDOWS\system32\dc6ujaxym.exe (Backdoor.Bot) -> 1152 -> Unloaded process successfully.
c:\documents and settings\{username}\application data\conhost.exe (Backdoor.Bot) -> 1756 -> Unloaded process successfully.
c:\WINDOWS\system32\lvvm.exe (Backdoor.Bot) -> 1948 -> Unloaded process successfully.
Memory Modules Infected:
(No malicious items detected)
Registry Keys Infected:
(No malicious items detected)
Registry Values Infected:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\G4tgnL3fI2dUwYq8234A (Backdoor.Bot) -> Value: G4tgnL3fI2dUwYq8234A -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\conhost (Backdoor.Bot) -> Value: conhost -> Quarantined and deleted successfully.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\AyhmP4tnLrbKdJs8234A (Backdoor.Bot) -> Value: AyhmP4tnLrbKdJs8234A -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer\Run\MartS (Trojan.Downloader) -> Value: MartS -> Quarantined and deleted successfully.
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Shell (Hijack.Shell.Gen) -> Value: Shell -> Quarantined and deleted successfully.
Registry Data Items Infected:
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows\Load (Backdoor.Bot) -> Bad: (C:\WINDOWS\system32\lvvm.exe) Good: () -> Quarantined and deleted successfully.
Folders Infected:
(No malicious items detected)
Files Infected:
c:\Documents and Settings\{username}\Local Settings\Temp\9.tmp (Backdoor.Bot) -> Delete on reboot.
c:\WINDOWS\system32\dc6ujaxym.exe (Backdoor.Bot) -> Quarantined and deleted successfully.
c:\documents and settings\{username}\application data\conhost.exe (Backdoor.Bot) -> Quarantined and deleted successfully.
c:\WINDOWS\system32\lvvm.exe (Backdoor.Bot) -> Quarantined and deleted successfully.
c:\documents and settings\{username}\application data\microsoft\csrss.exe (Backdoor.Bot) -> Quarantined and deleted successfully.
c:\WINDOWS\system32\redv7kwcuqx.exe (Backdoor.Bot) -> Quarantined and deleted successfully.
c:\documents and settings\{username}\application data\csrss.exe (Trojan.Downloader) -> Quarantined and deleted successfully.
c:\documents and settings\{username}\Desktop\hardcore_porn_movie_82.mpeg.exe (Trojan.FraudPack.Gen) -> Quarantined and deleted successfully.
c:\documents and settings\{username}\local settings\Temp\E.exe (Backdoor.Bot) -> Quarantined and deleted successfully.
c:\program files\internet explorer\rasadhlp.dll (Spyware.Passwords) -> Quarantined and deleted successfully.
c:\program files\outlook express\rasadhlp.dll (Trojan.PWS) -> Quarantined and deleted successfully.
c:\documents and settings\{username}\application data\ldr.ini (Malware.Trace) -> Quarantined and deleted successfully.
As mentioned before the full version of Malwarebytes' Anti-Malware could have protected your computer against this threat.
We use different ways of protecting your computer(s):
- Dynamically Blocks Malware Sites & Servers
- Malware Execution Prevention







 Back to top
Back to top




 Sign In
Sign In Create Account
Create Account

